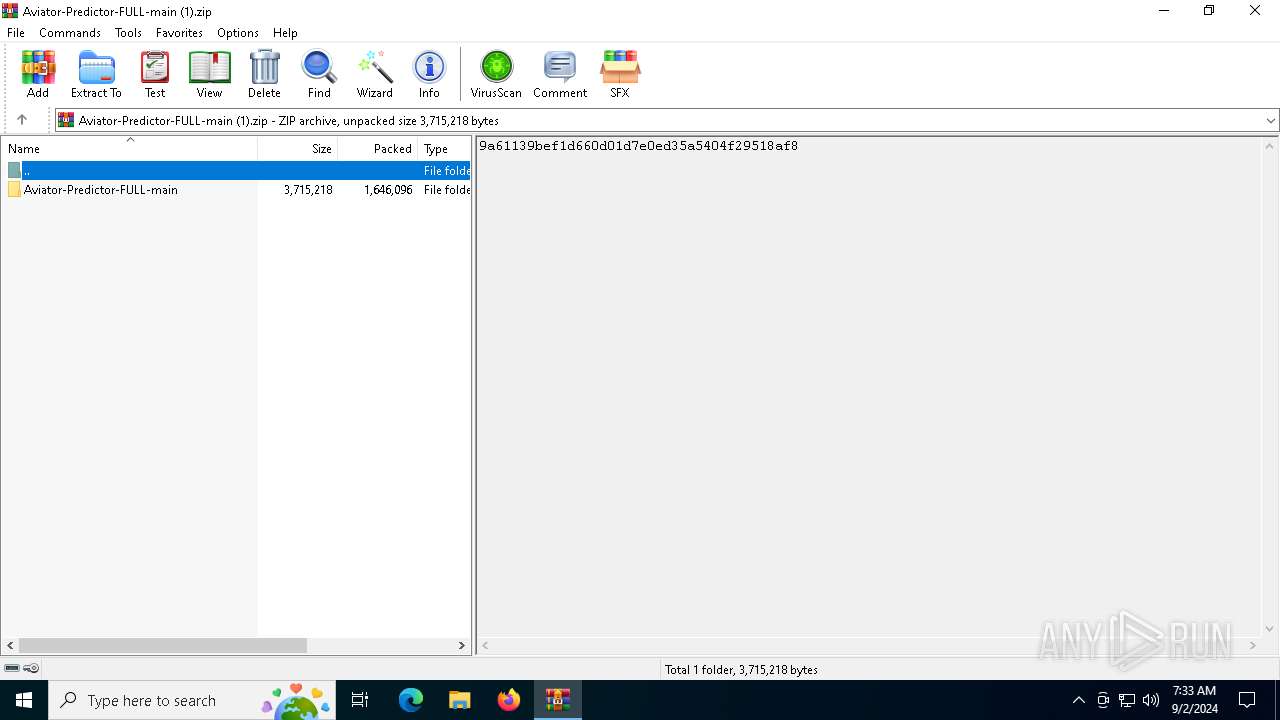
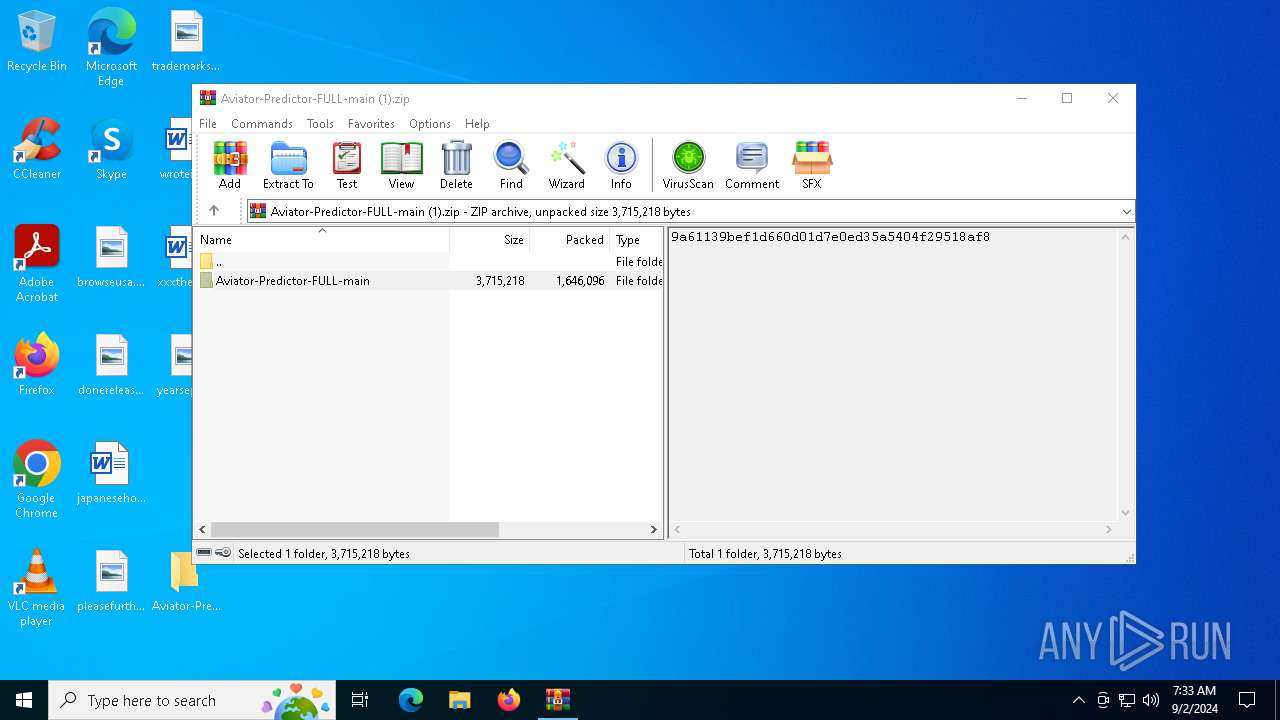
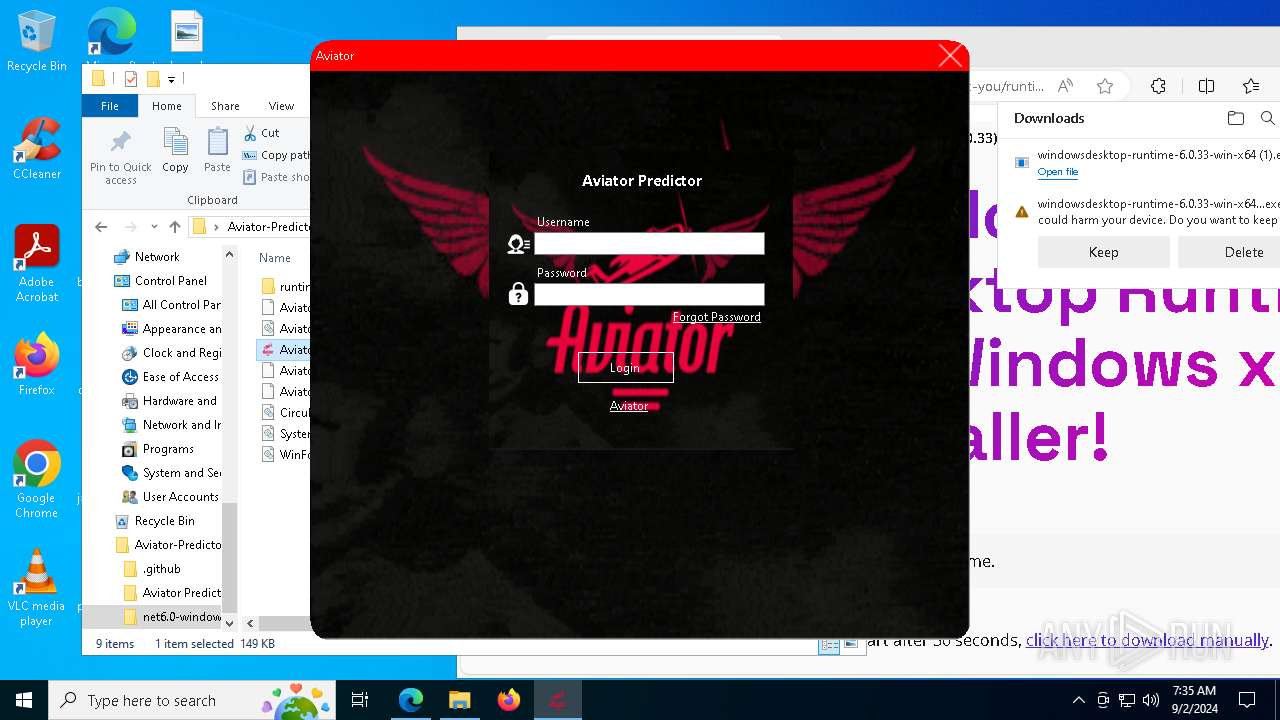
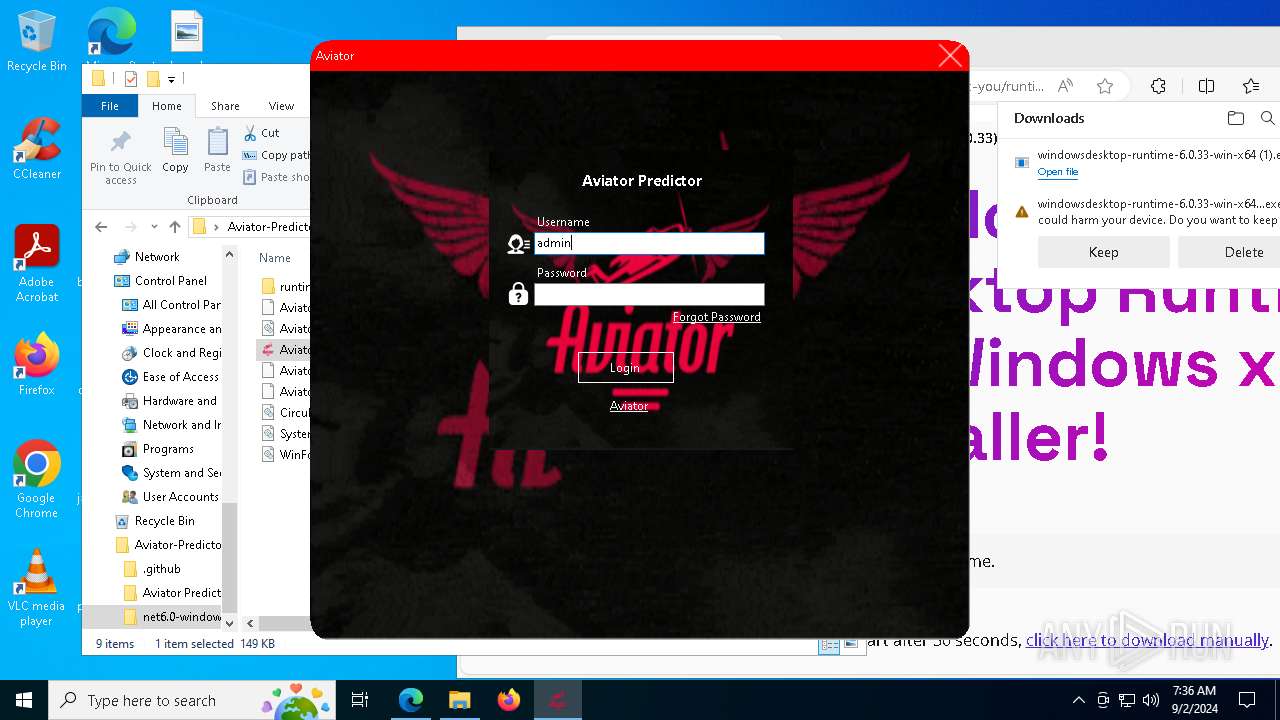
| File name: | Aviator-Predictor-FULL-main (1).zip |
| Full analysis: | https://app.any.run/tasks/5a43a5a9-bfec-4cb3-b2b4-48b2d7f1e176 |
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2024, 07:32:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 2AD477B9C4FE0AC1F42E8D3FDBB5568A |
| SHA1: | 6DEAEEF8409DCCD218EAA4C69CB1B52E104F7D84 |
| SHA256: | 05C3F1186CE7E2E82F2D6CE4770FFDC1D170CDABC1298595D8A6EA26BC230829 |
| SSDEEP: | 49152:ZJR8Em3mNAIhOR+wwehGP/bzLFfolk/Ml753S7BOuW6R5TR54tPa9m8ES0A5K4/v:zR8TmNAIhORhdM/LFfEk/Ml13A1PTRSo |
MALICIOUS
Changes the autorun value in the registry
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6168)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 940)
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
- msiexec.exe (PID: 3028)
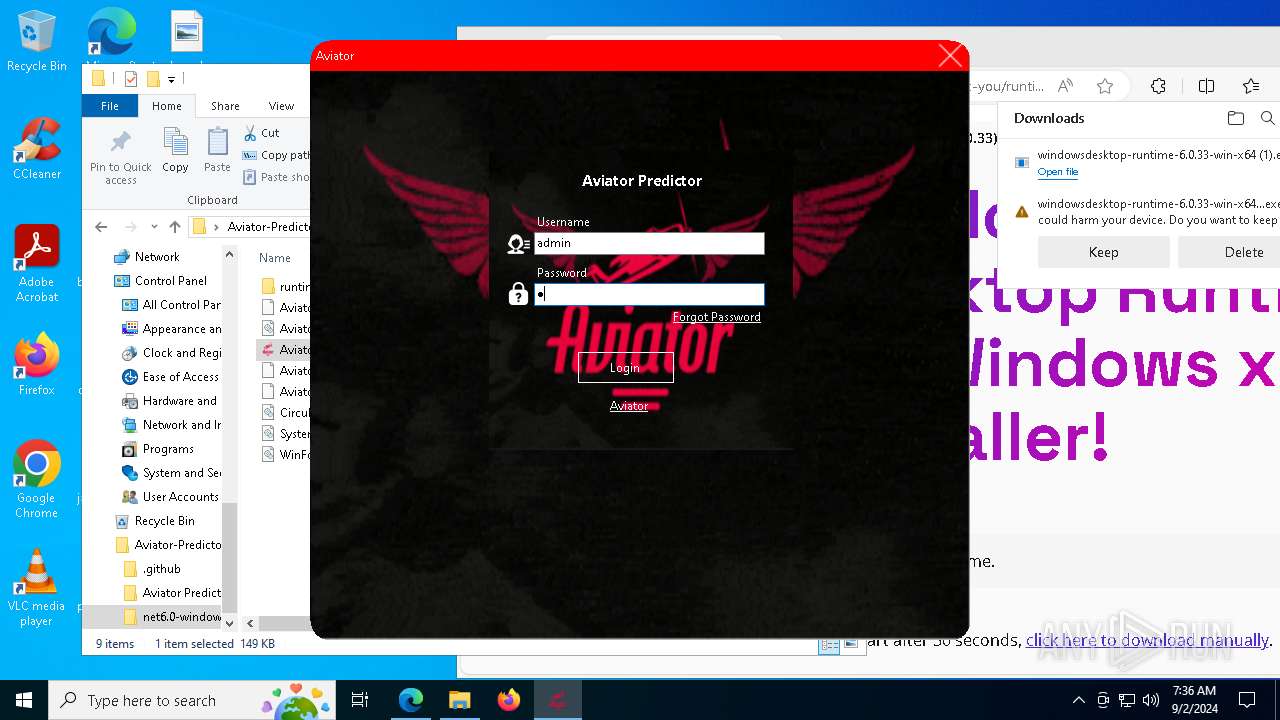
Reads security settings of Internet Explorer
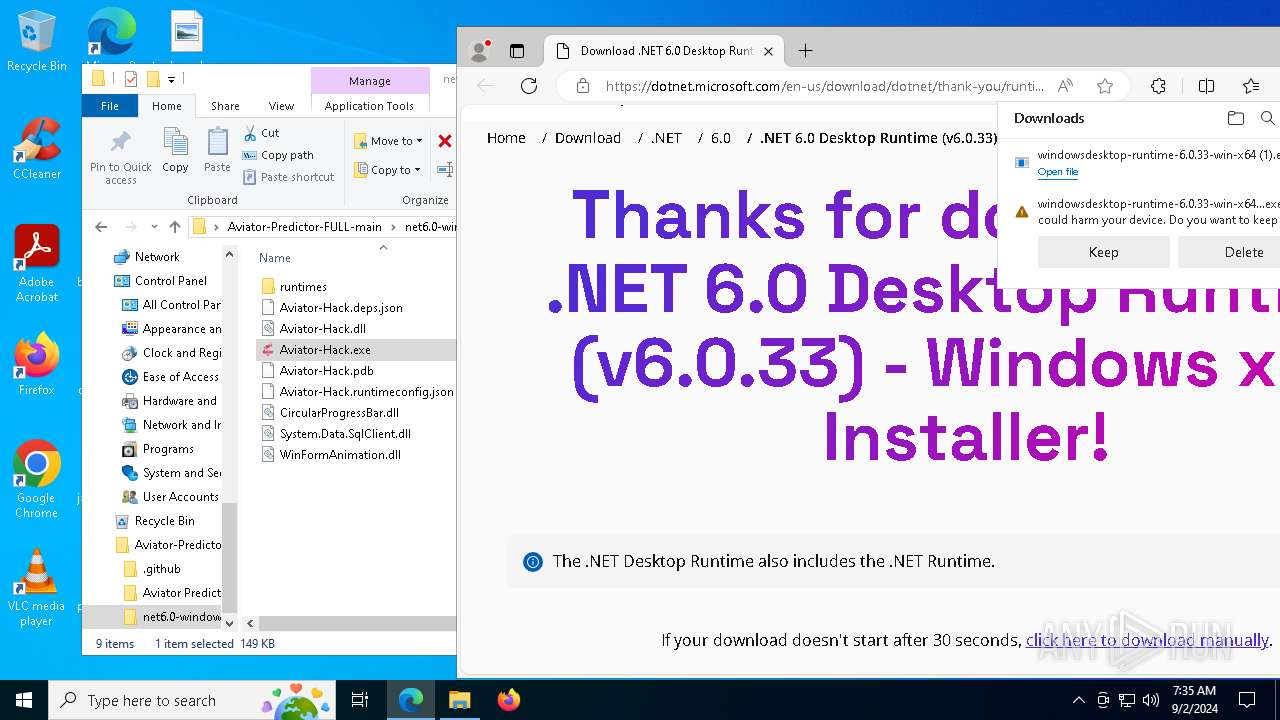
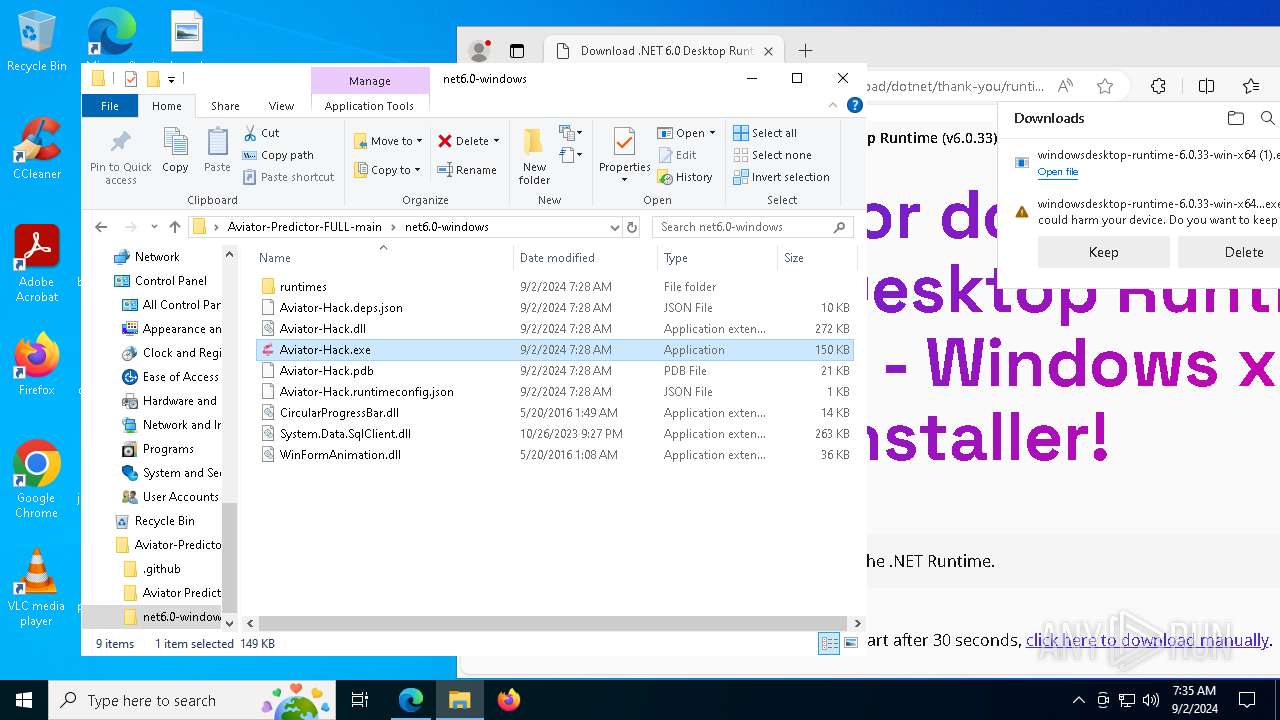
- Aviator-Hack.exe (PID: 6748)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
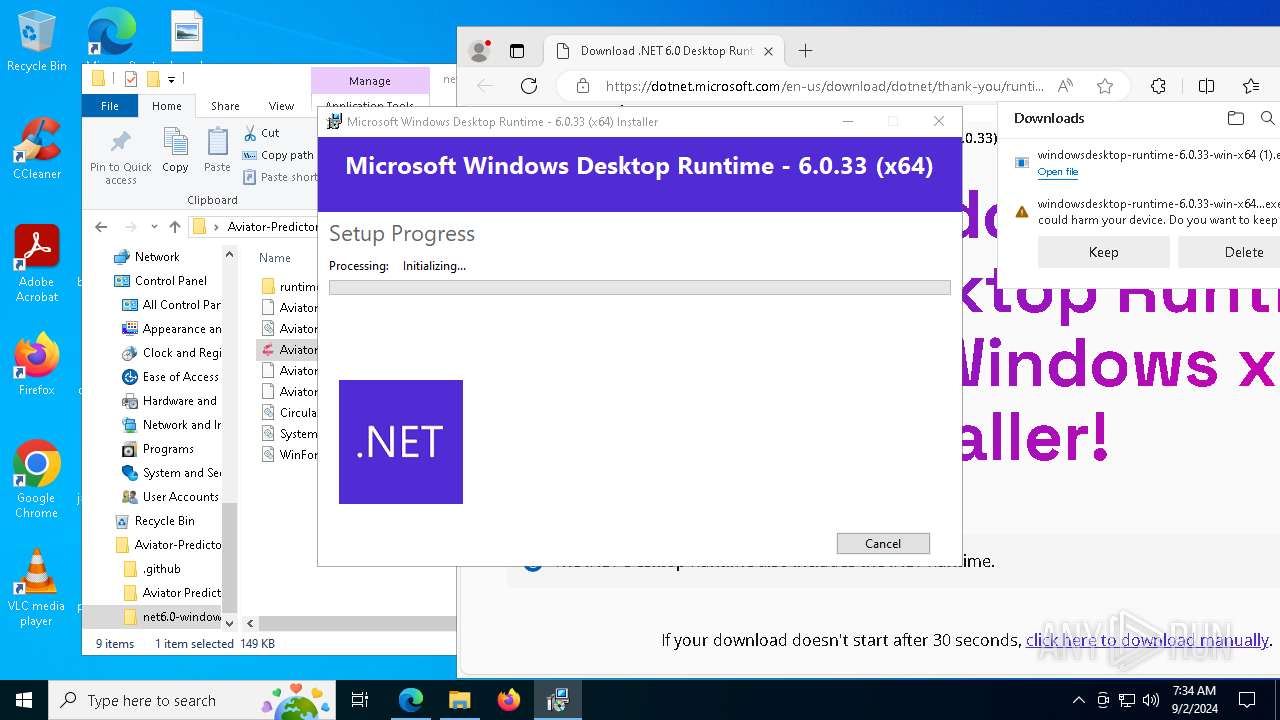
Executable content was dropped or overwritten
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 940)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
Drops the executable file immediately after the start
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 940)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
- msiexec.exe (PID: 3028)
Starts itself from another location
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
Starts a Microsoft application from unusual location
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
Searches for installed software
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
Reads the date of Windows installation
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
Creates a software uninstall entry
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
The process creates files with name similar to system file names
- msiexec.exe (PID: 3028)
Checks Windows Trust Settings
- msiexec.exe (PID: 3028)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3028)
The process drops C-runtime libraries
- msiexec.exe (PID: 3028)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6168)
- msedge.exe (PID: 6308)
- msiexec.exe (PID: 3028)
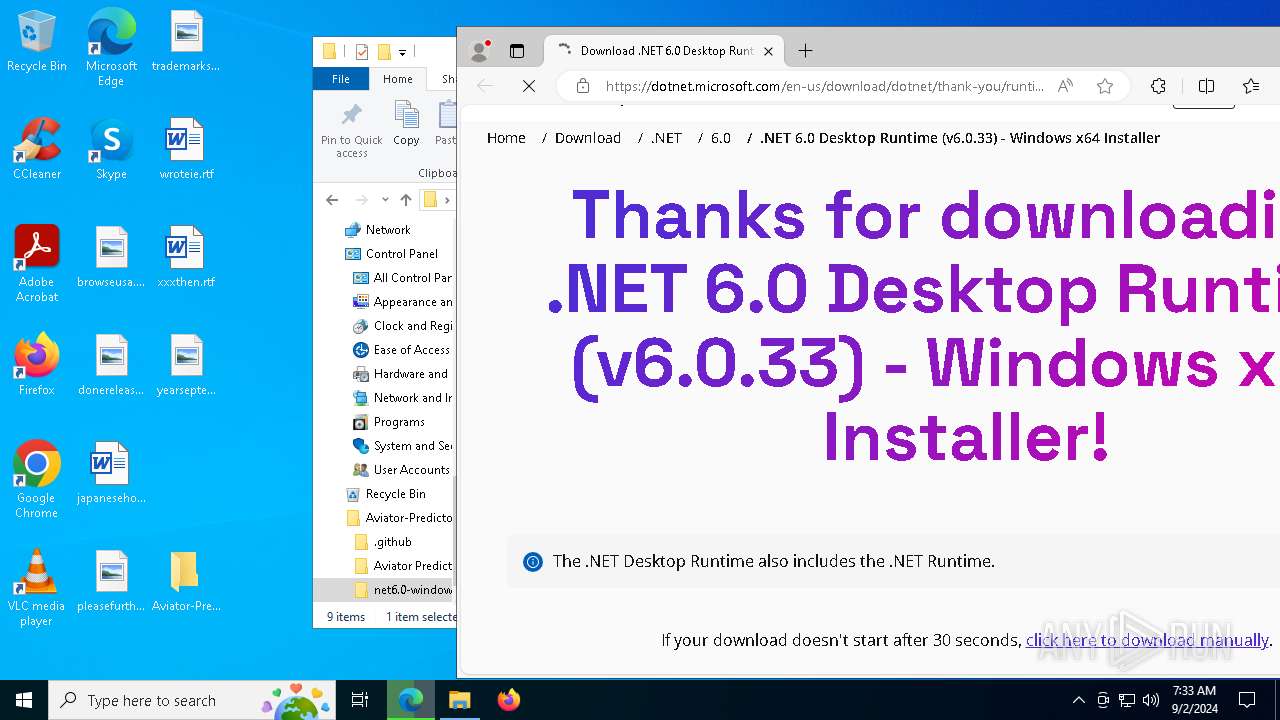
The process uses the downloaded file
- WinRAR.exe (PID: 6168)
- msedge.exe (PID: 7772)
- msedge.exe (PID: 6308)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
Checks supported languages
- Aviator-Hack.exe (PID: 6748)
- identity_helper.exe (PID: 7472)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 940)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
- msiexec.exe (PID: 3028)
- msiexec.exe (PID: 5692)
- msiexec.exe (PID: 6948)
- msiexec.exe (PID: 2360)
- msiexec.exe (PID: 2132)
- Aviator-Hack.exe (PID: 5712)
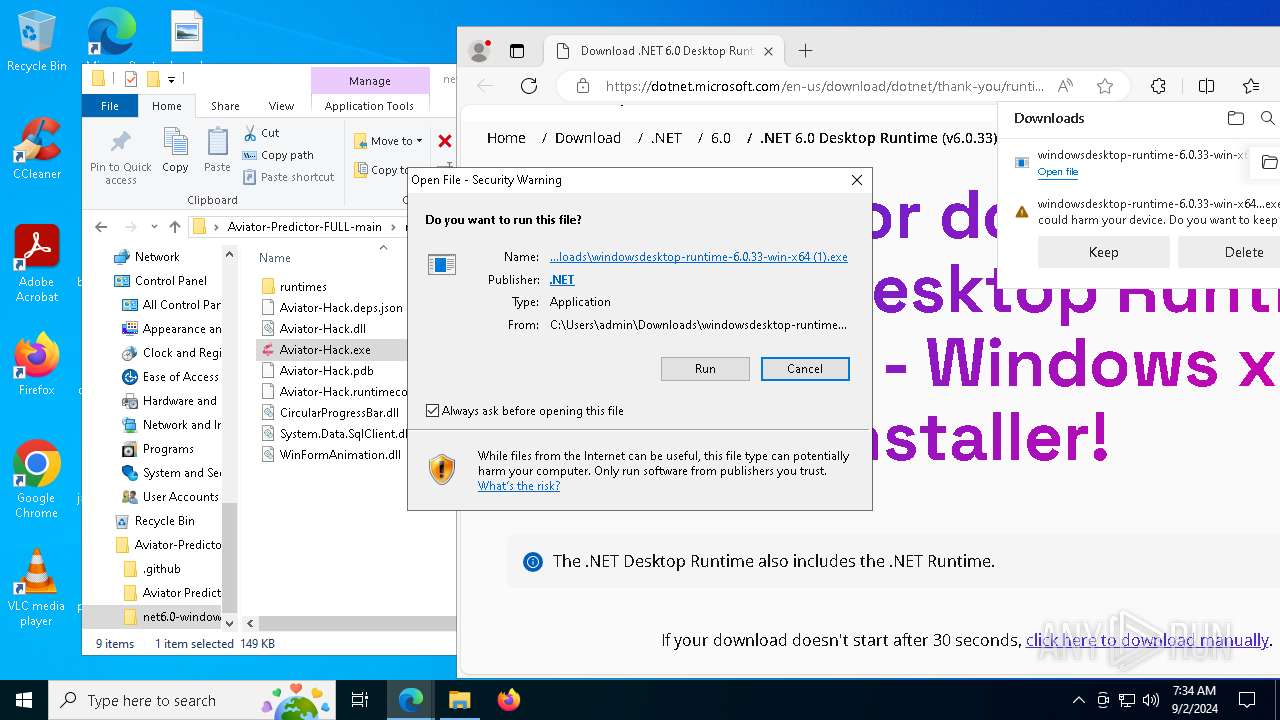
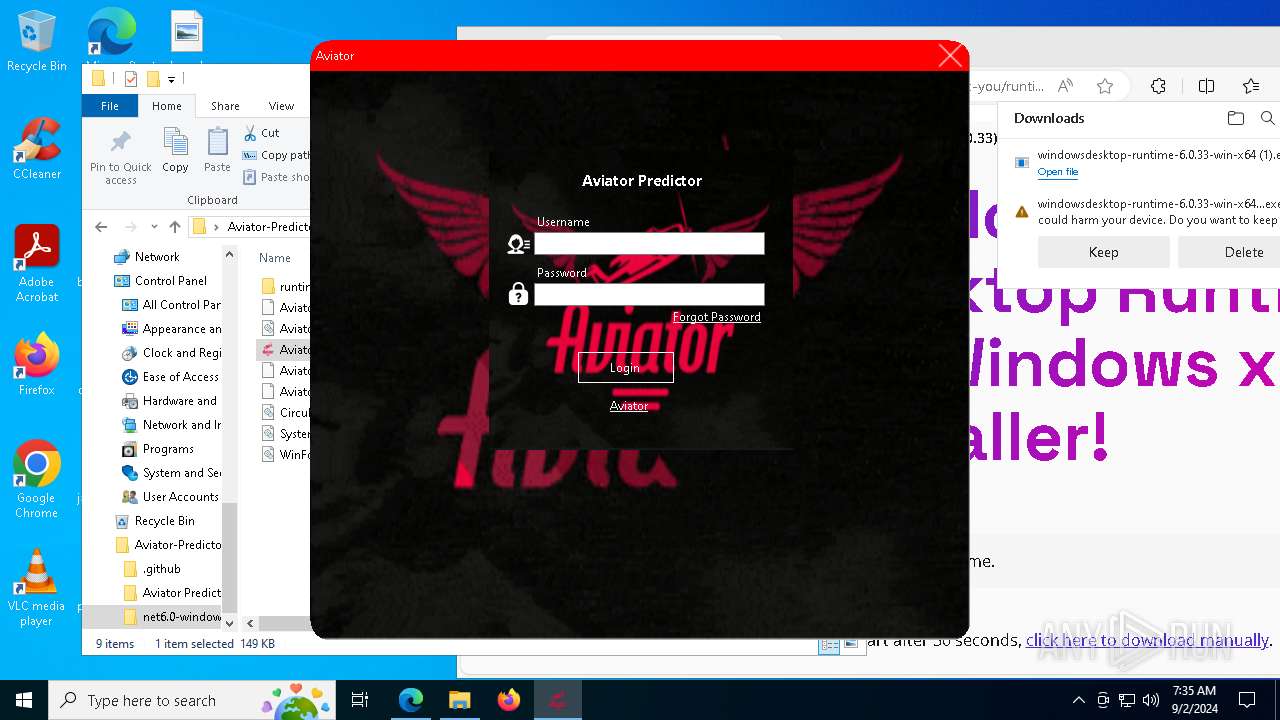
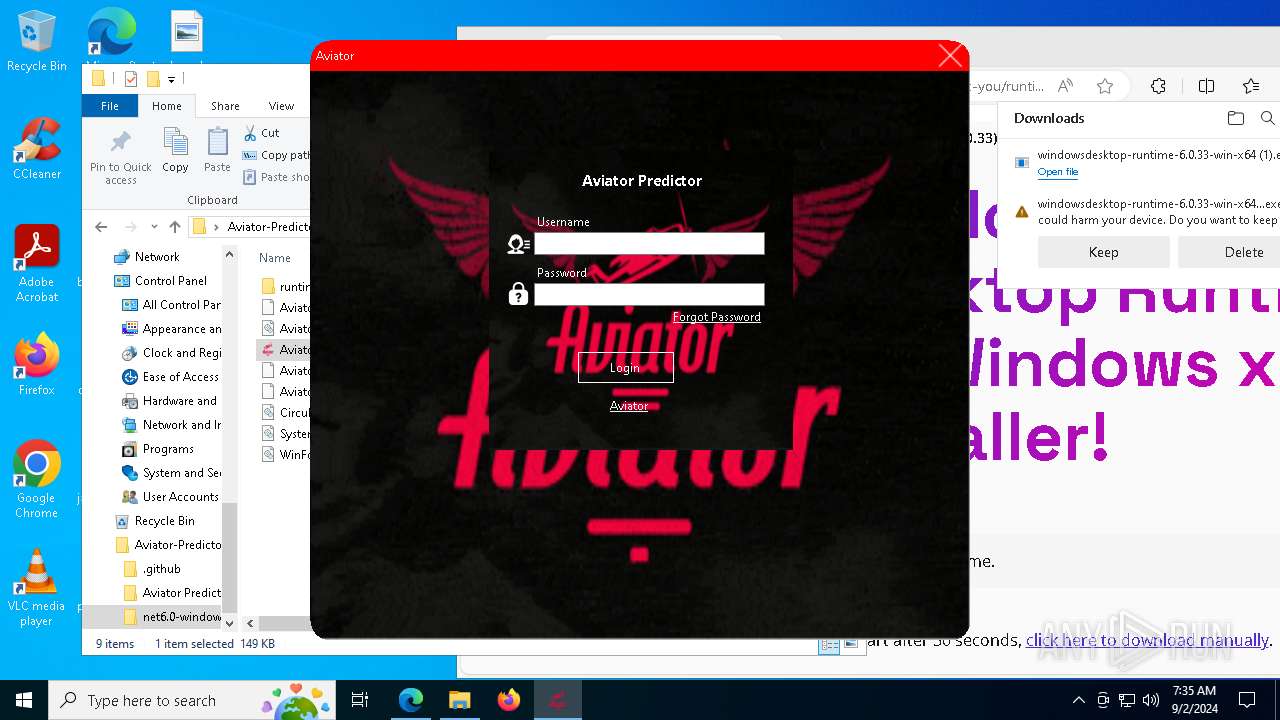
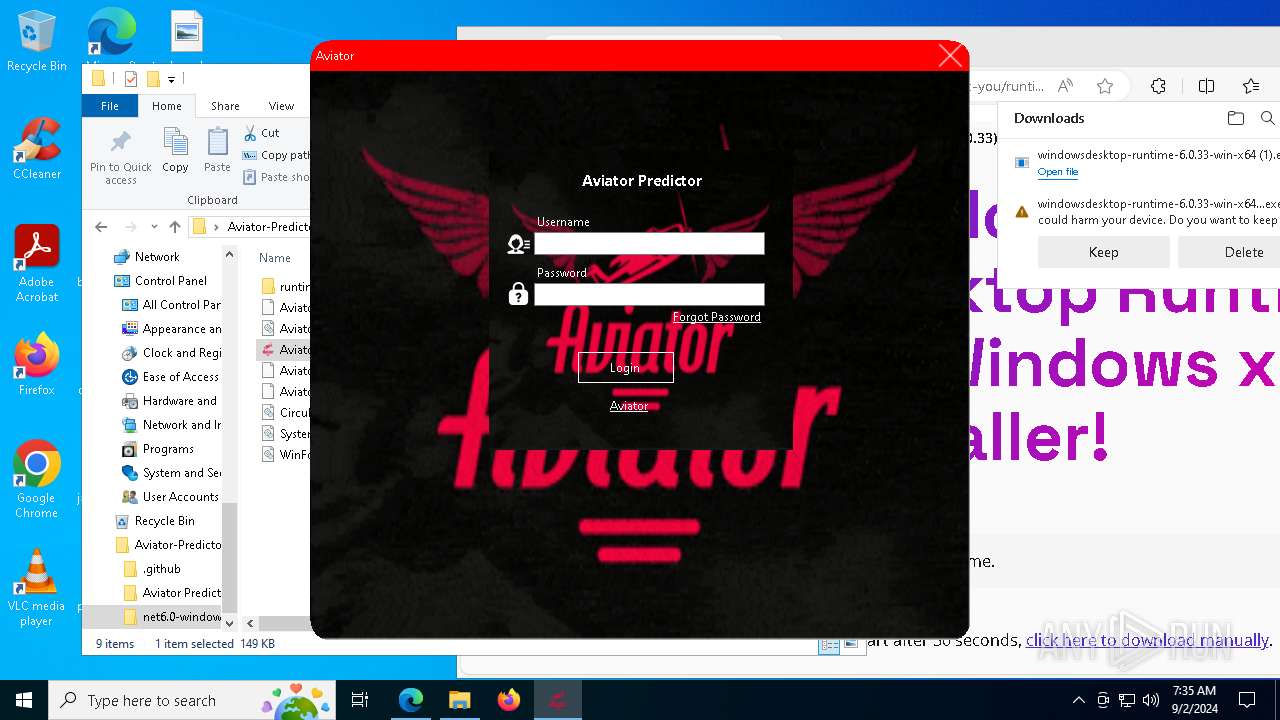
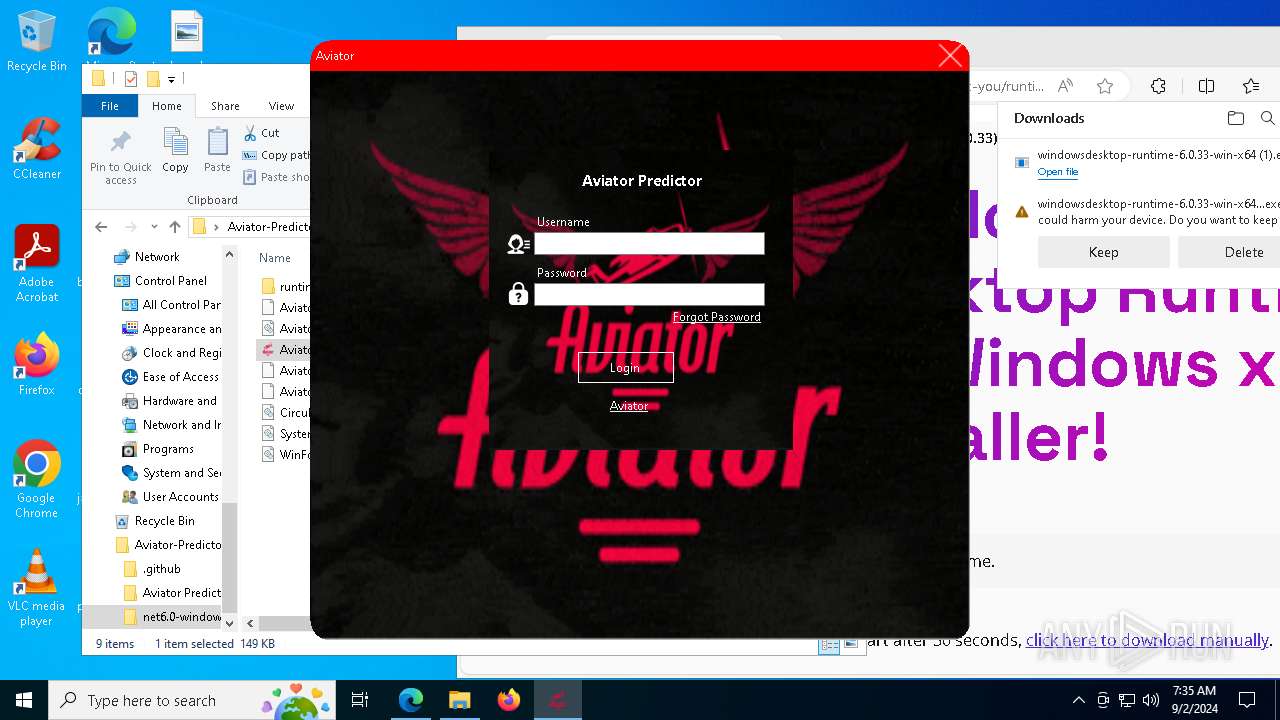
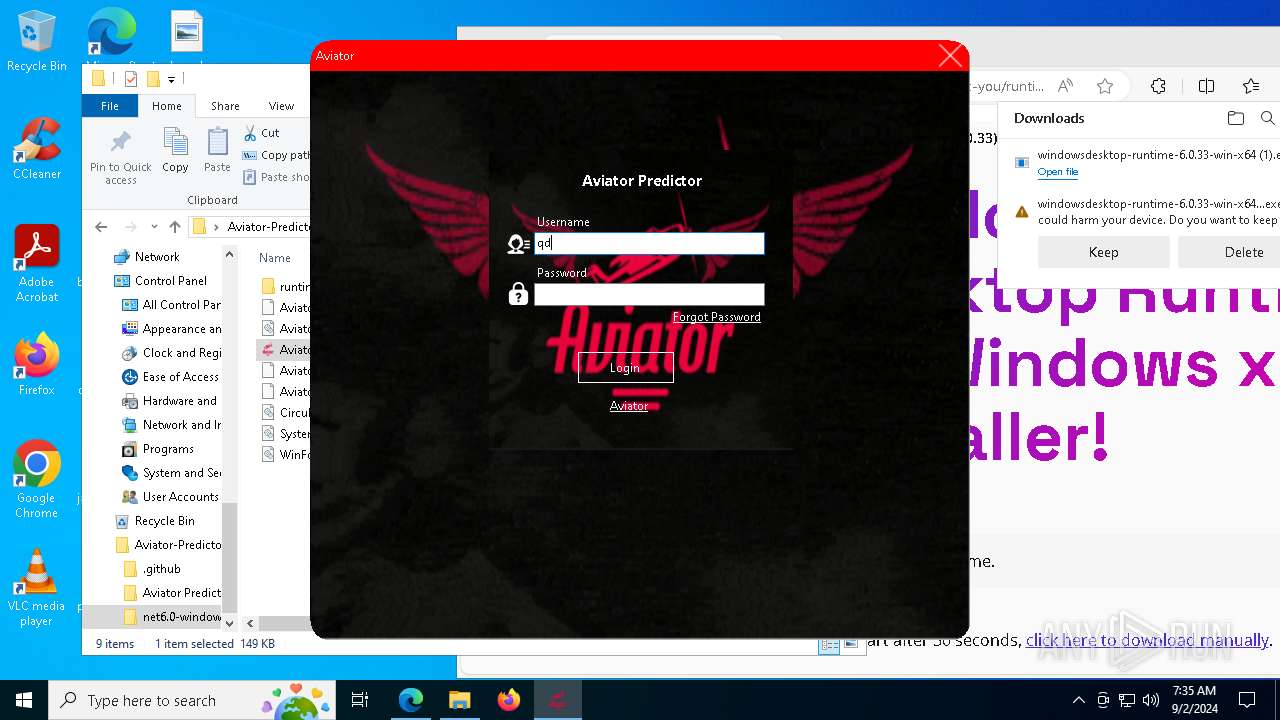
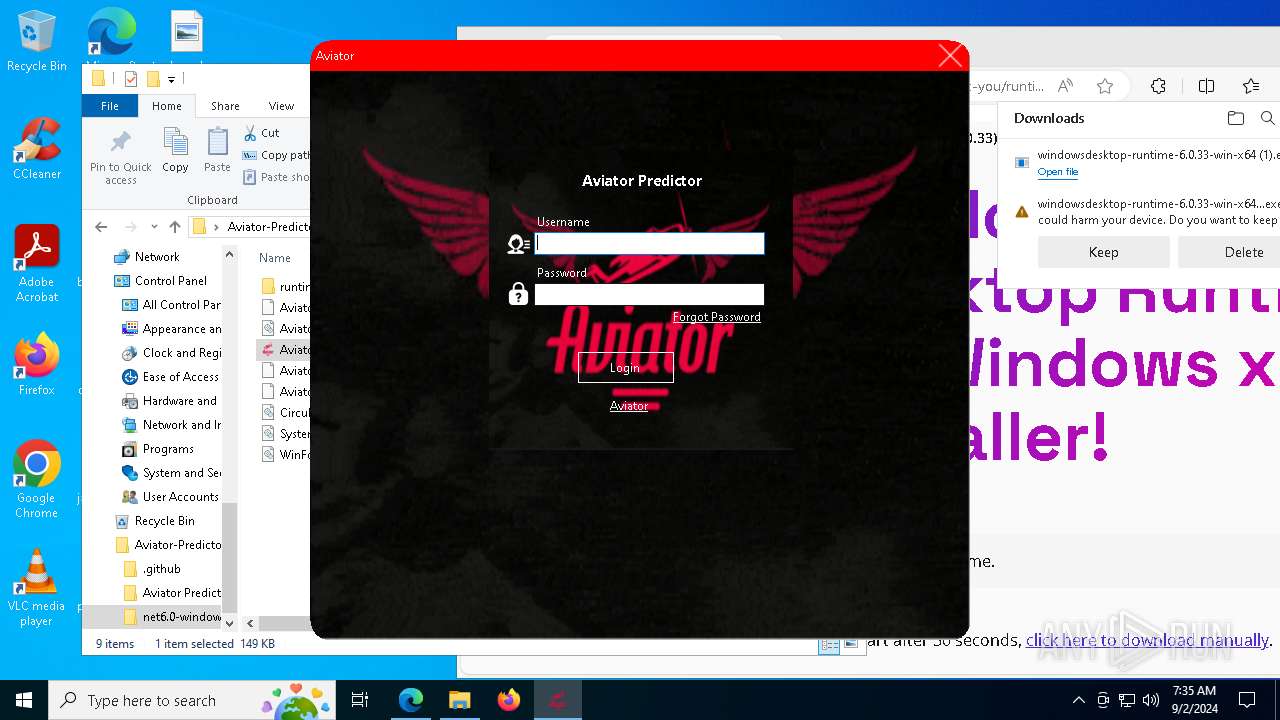
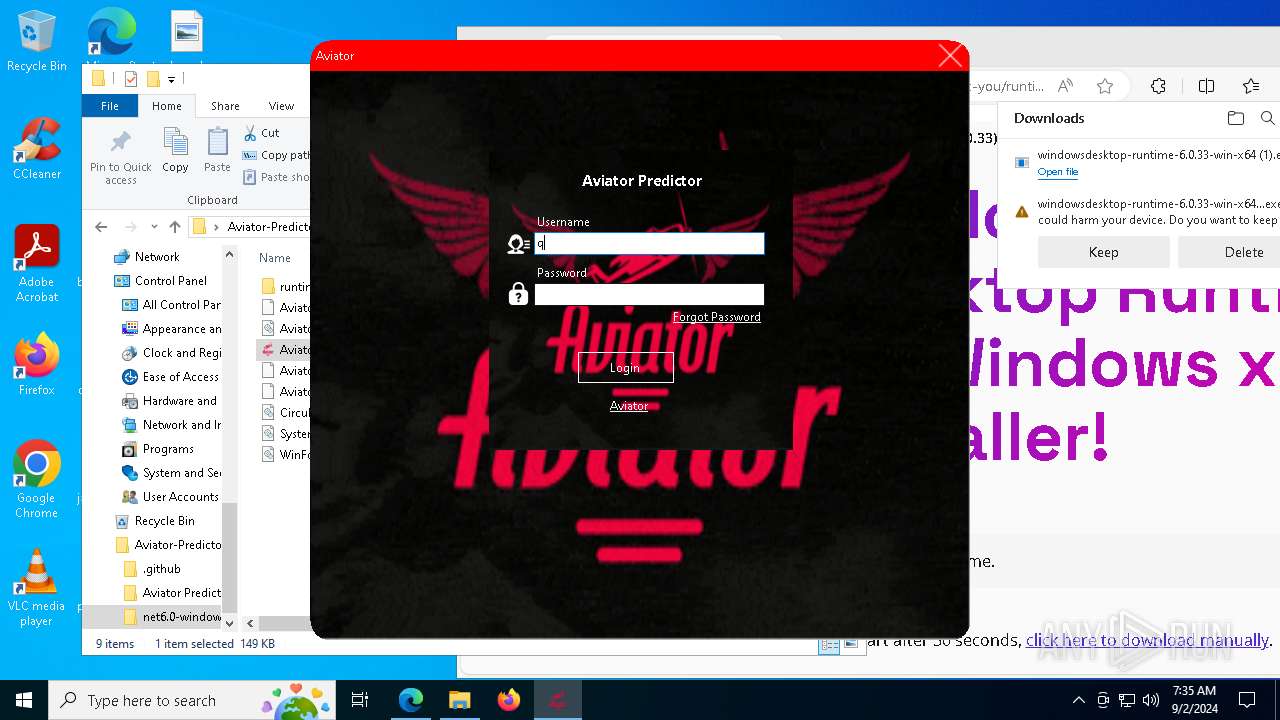
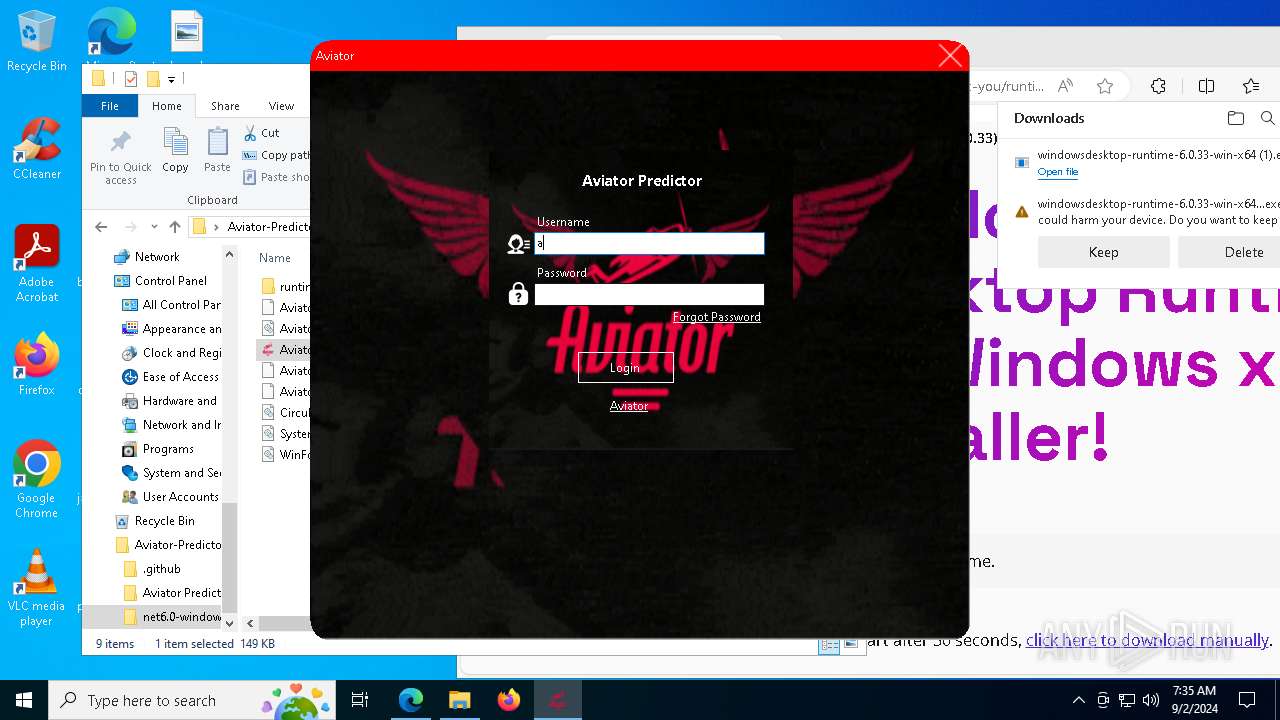
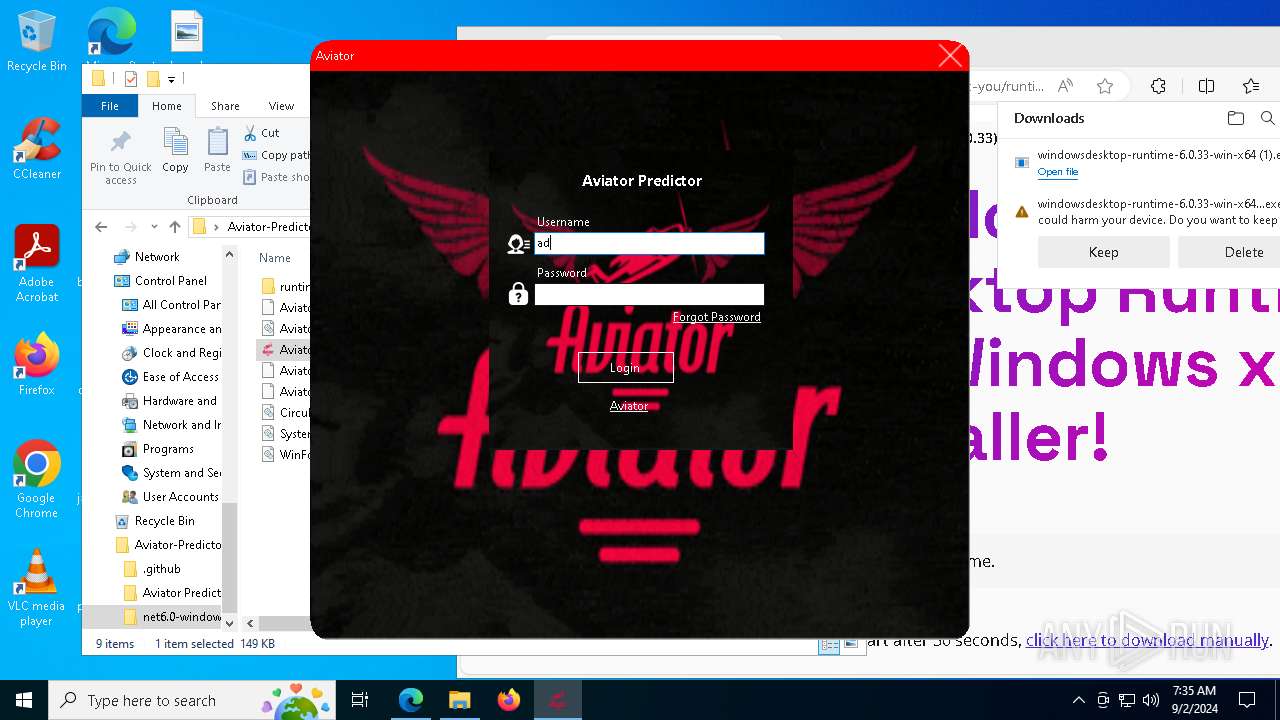
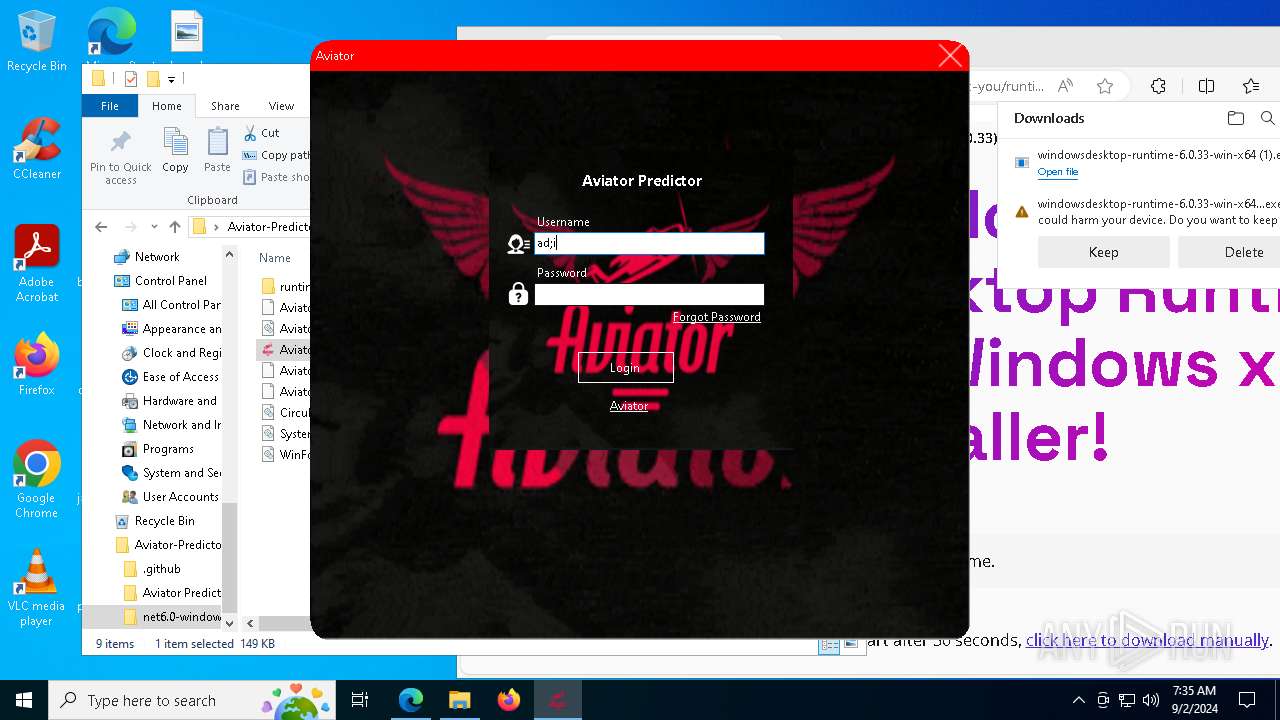
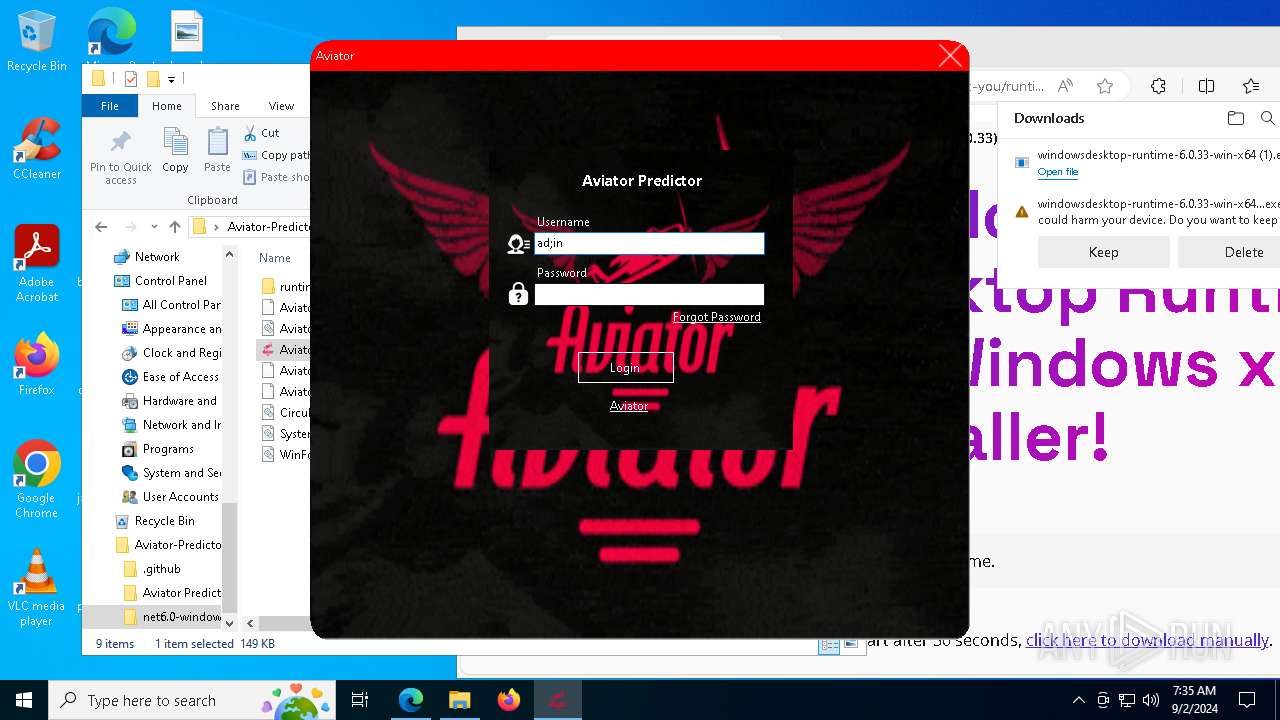
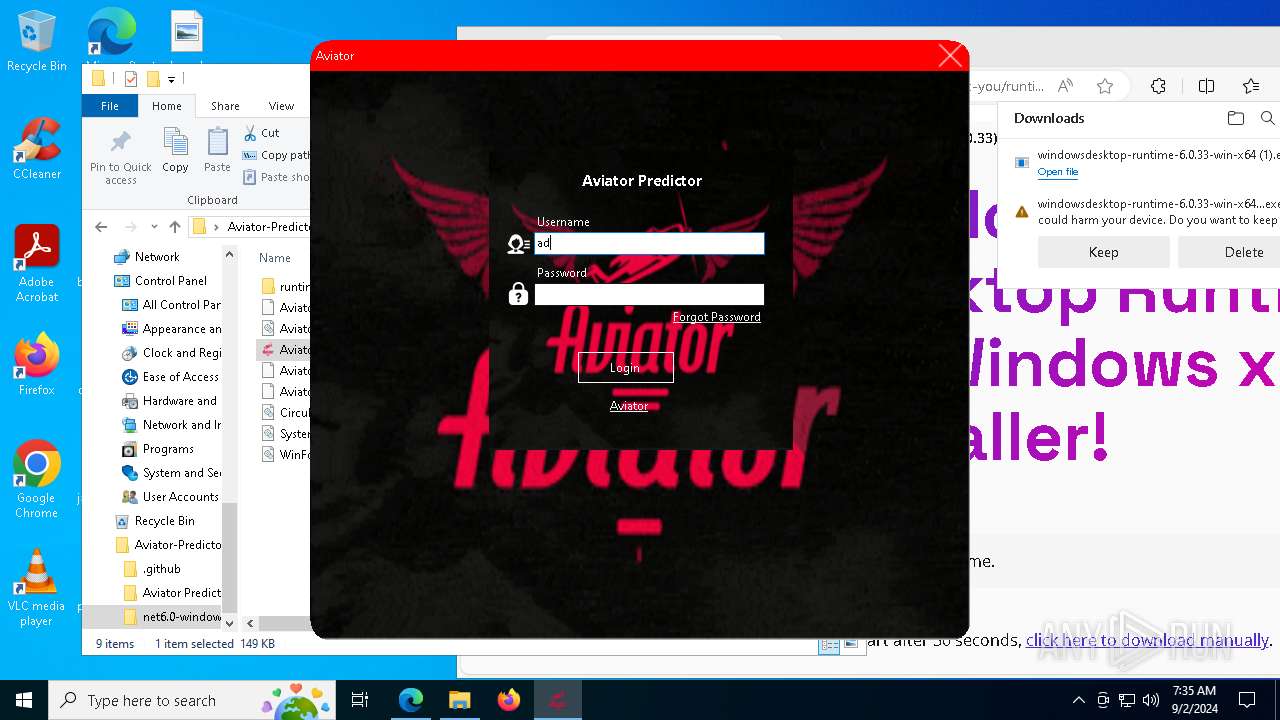
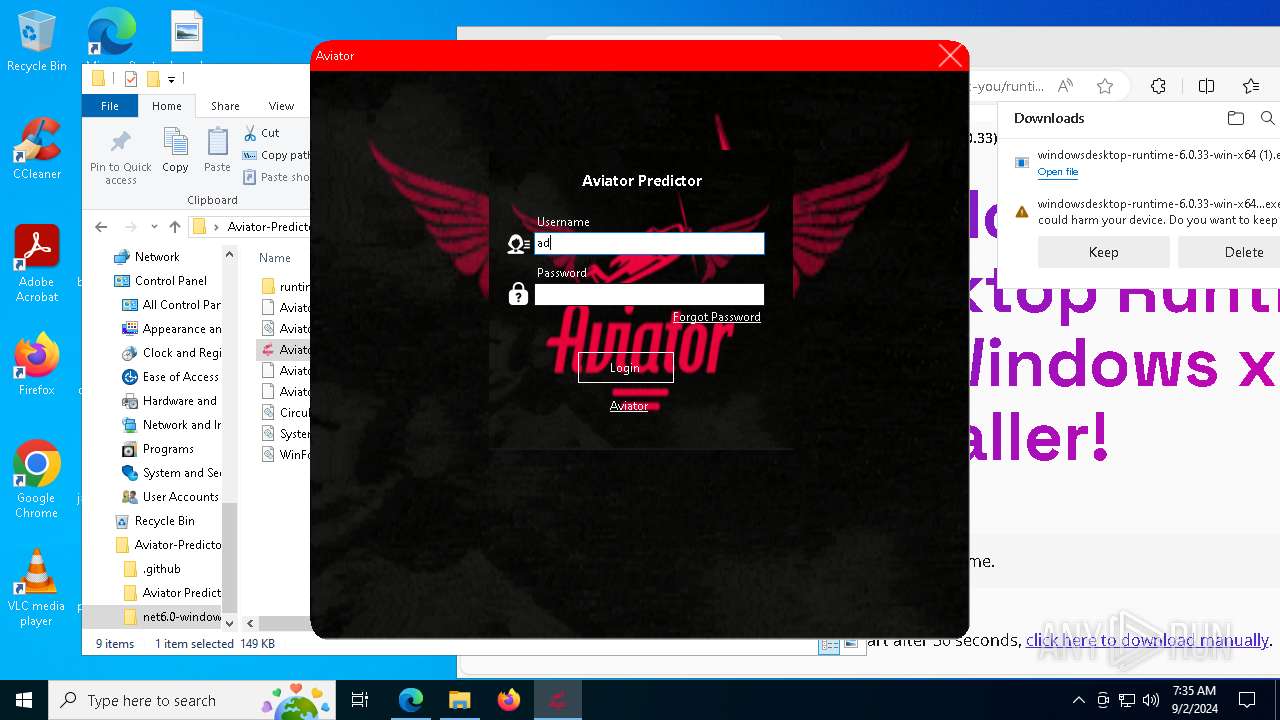
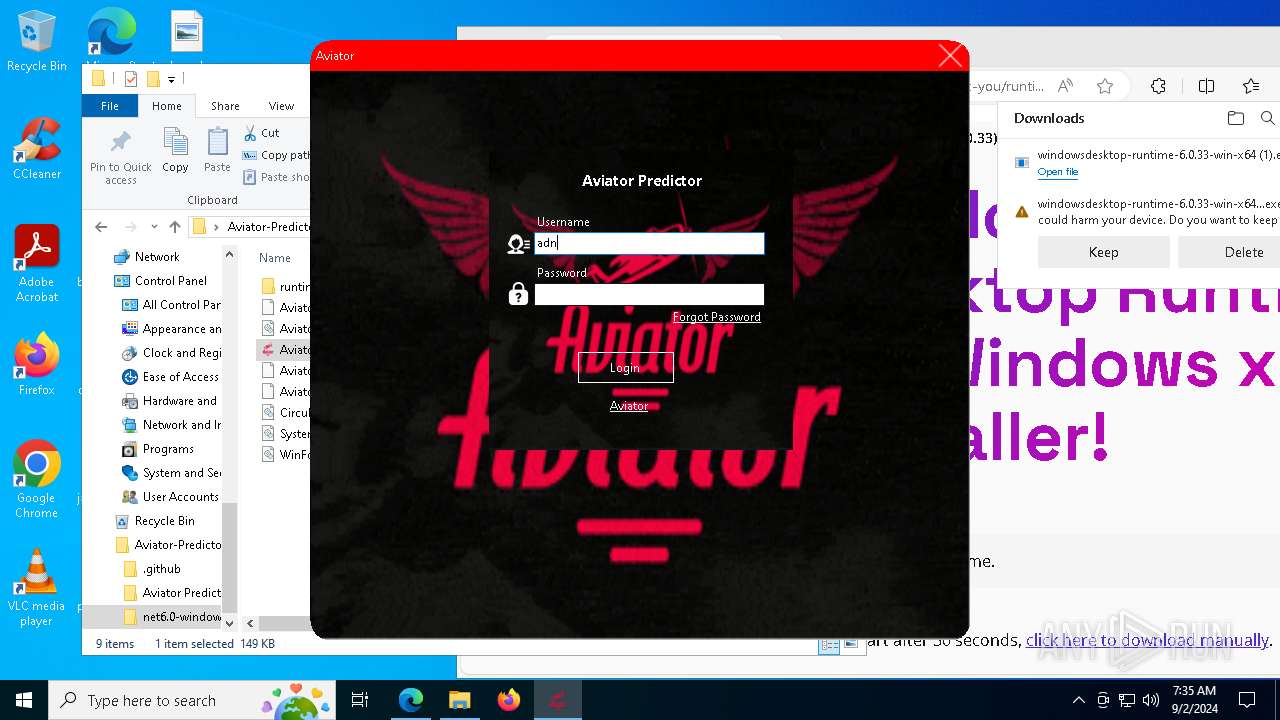
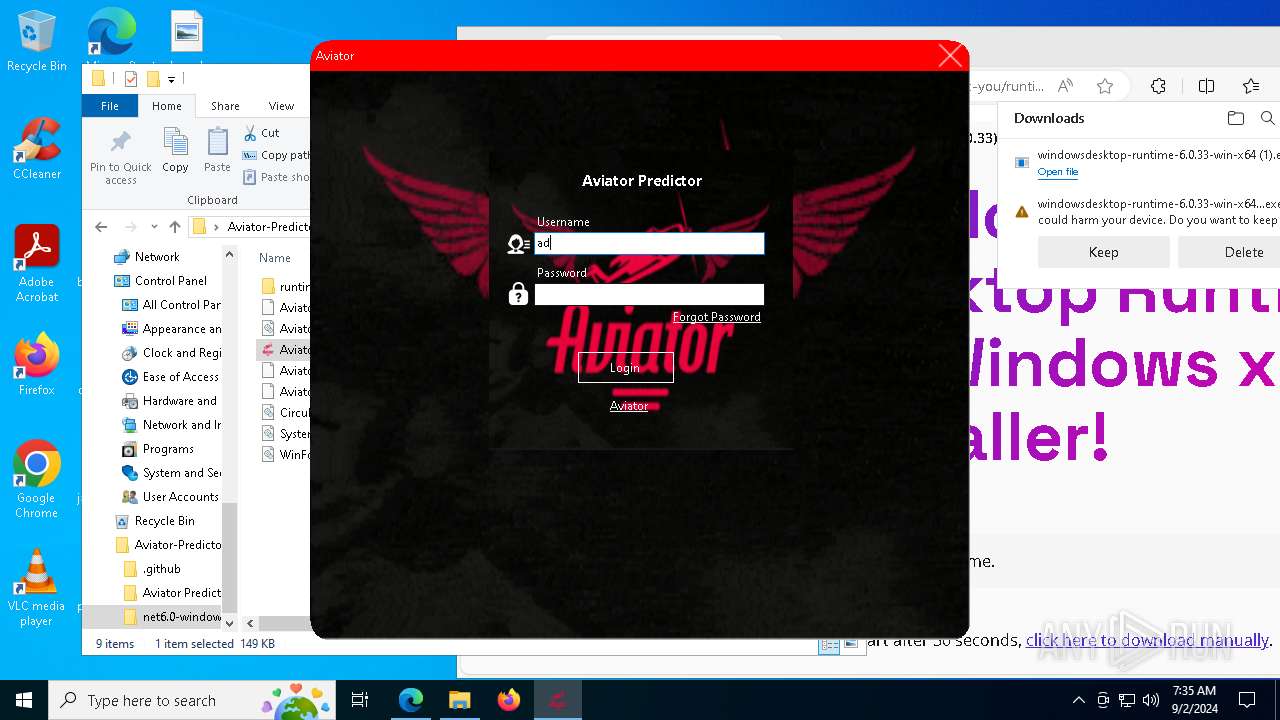
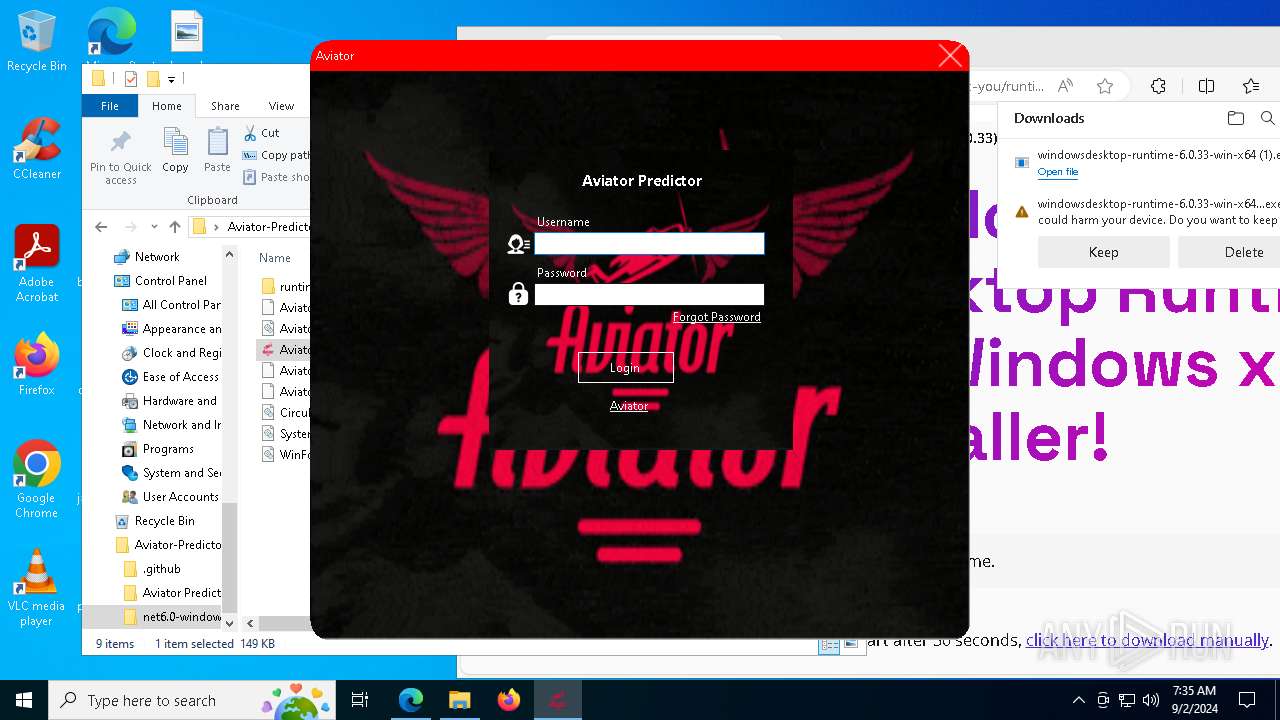
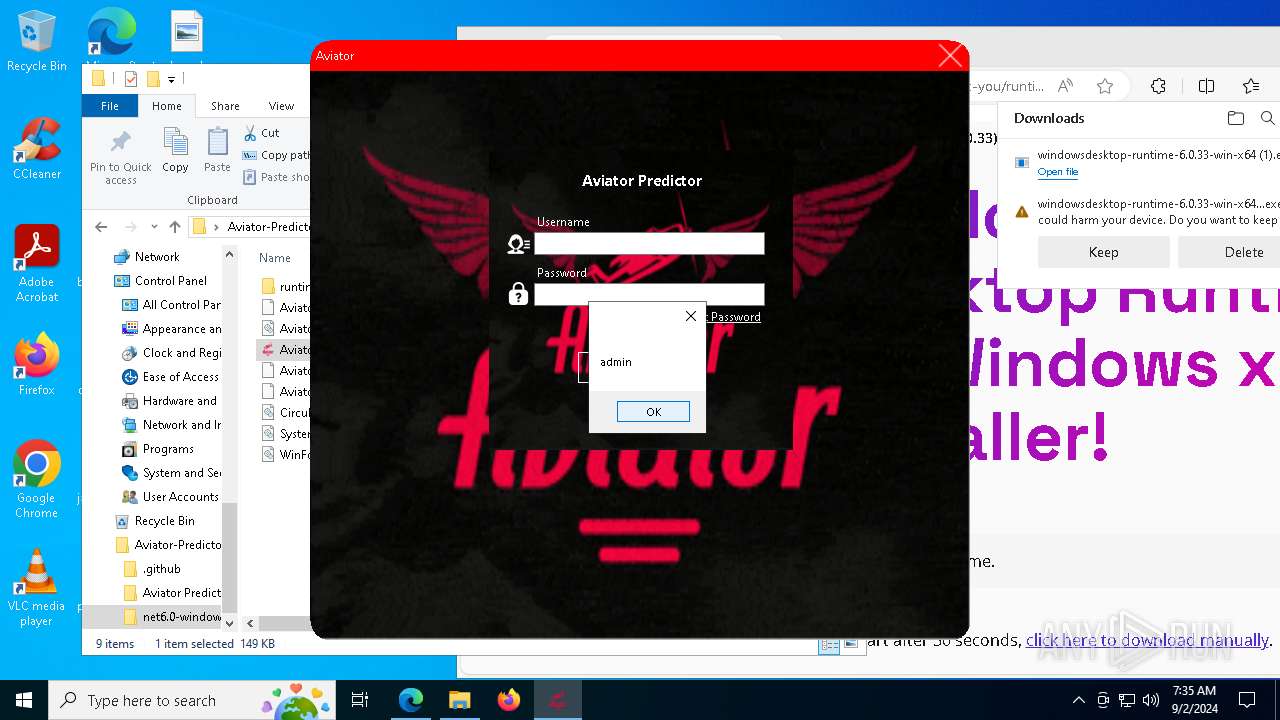
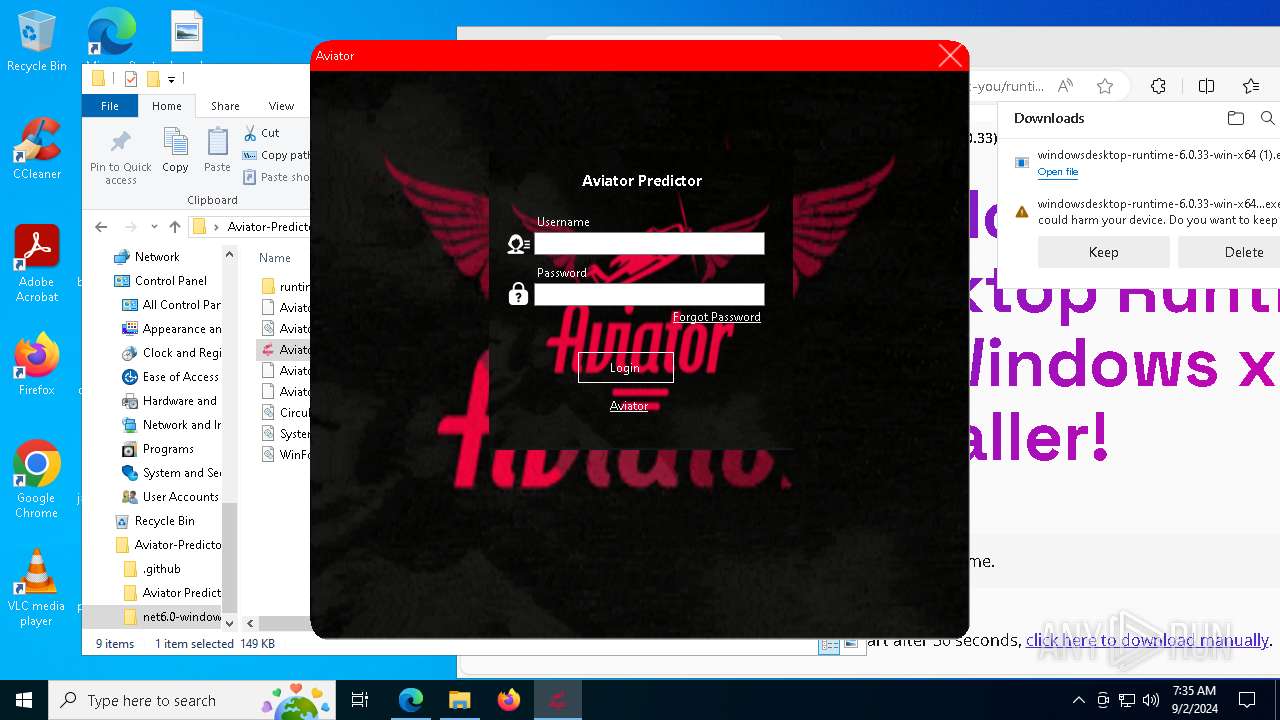
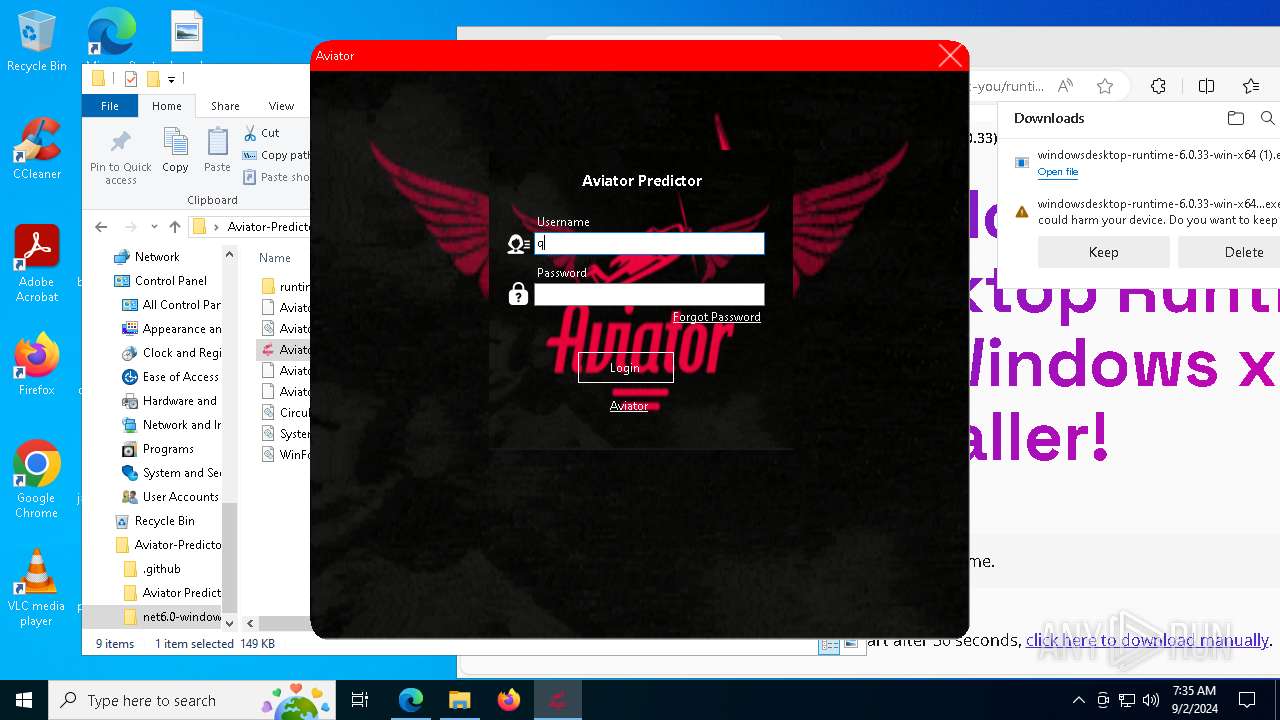
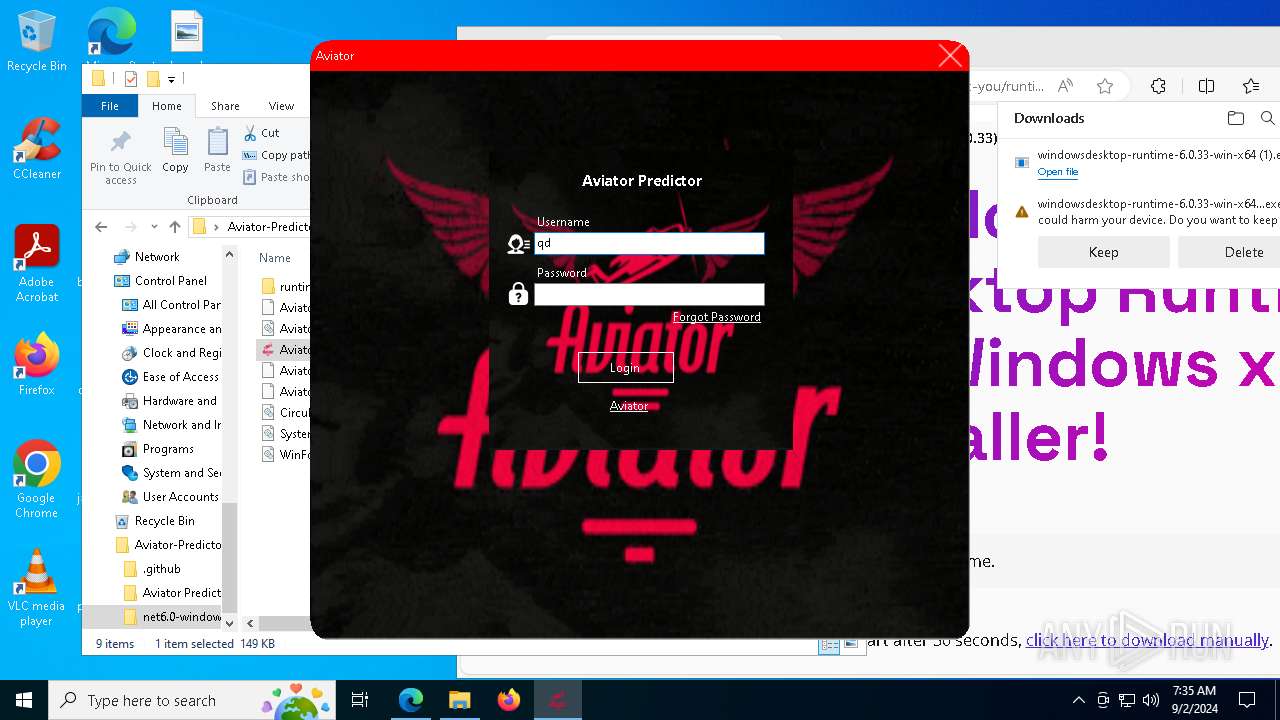
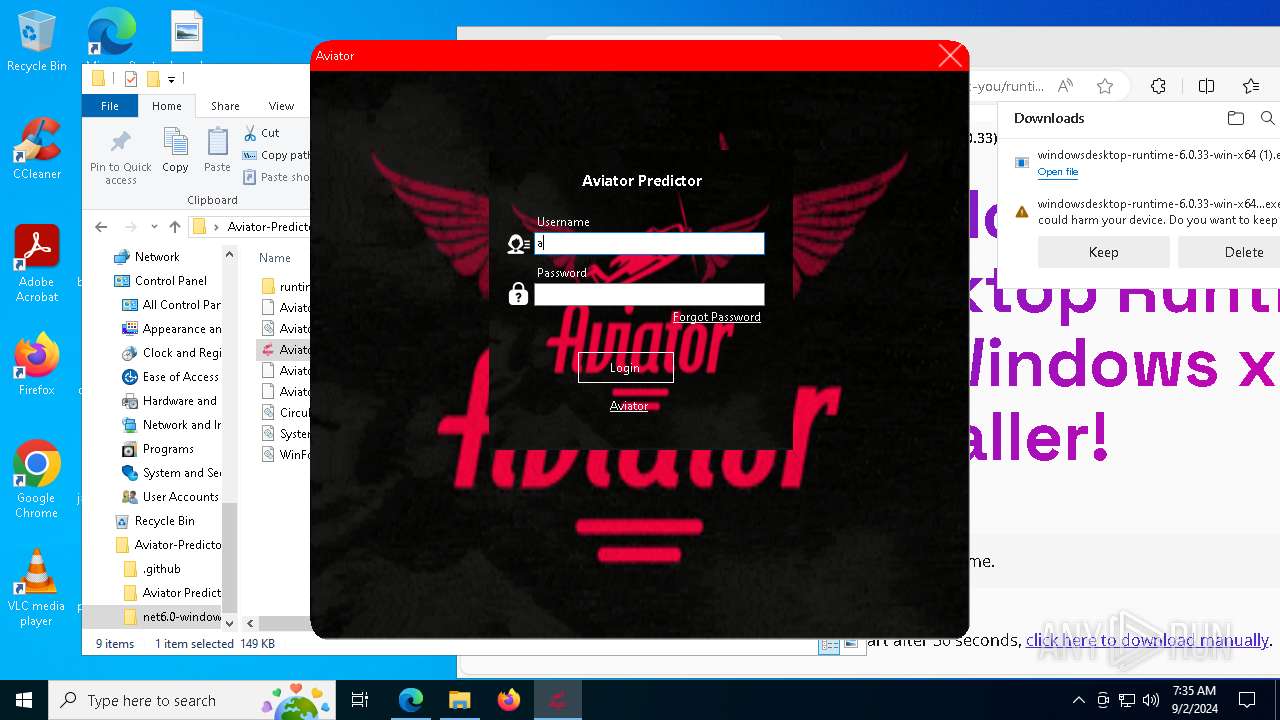
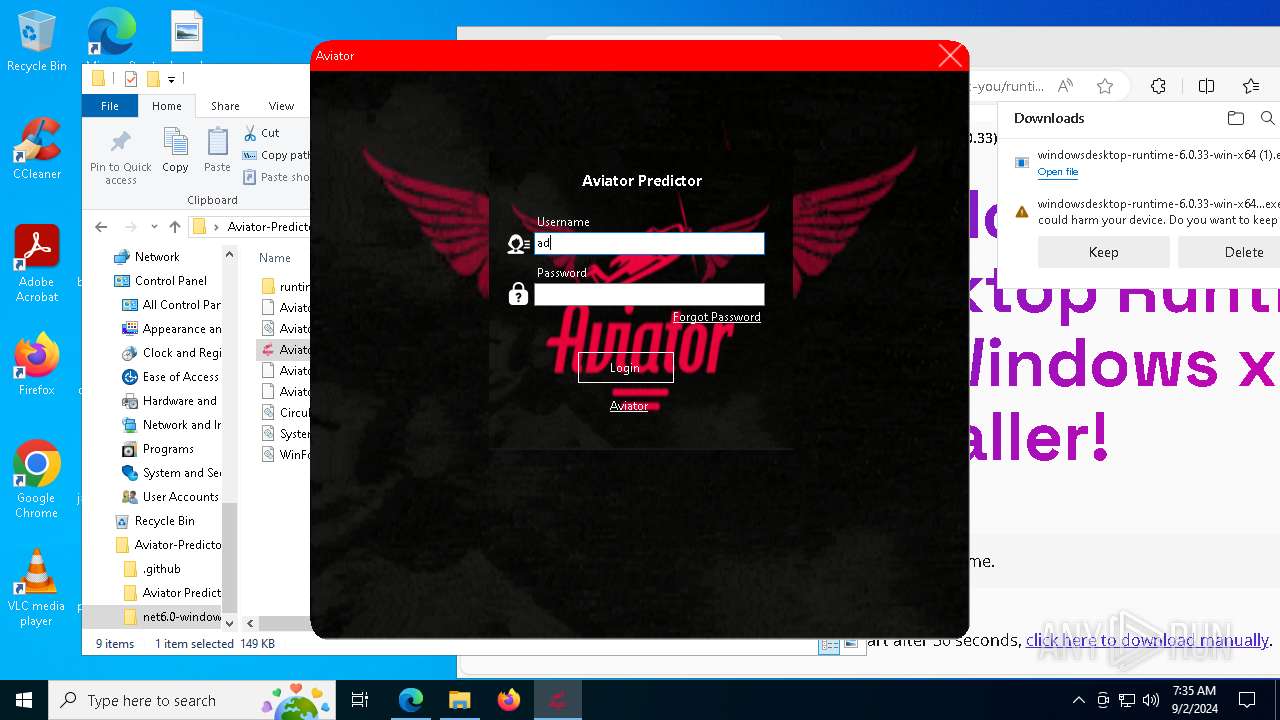
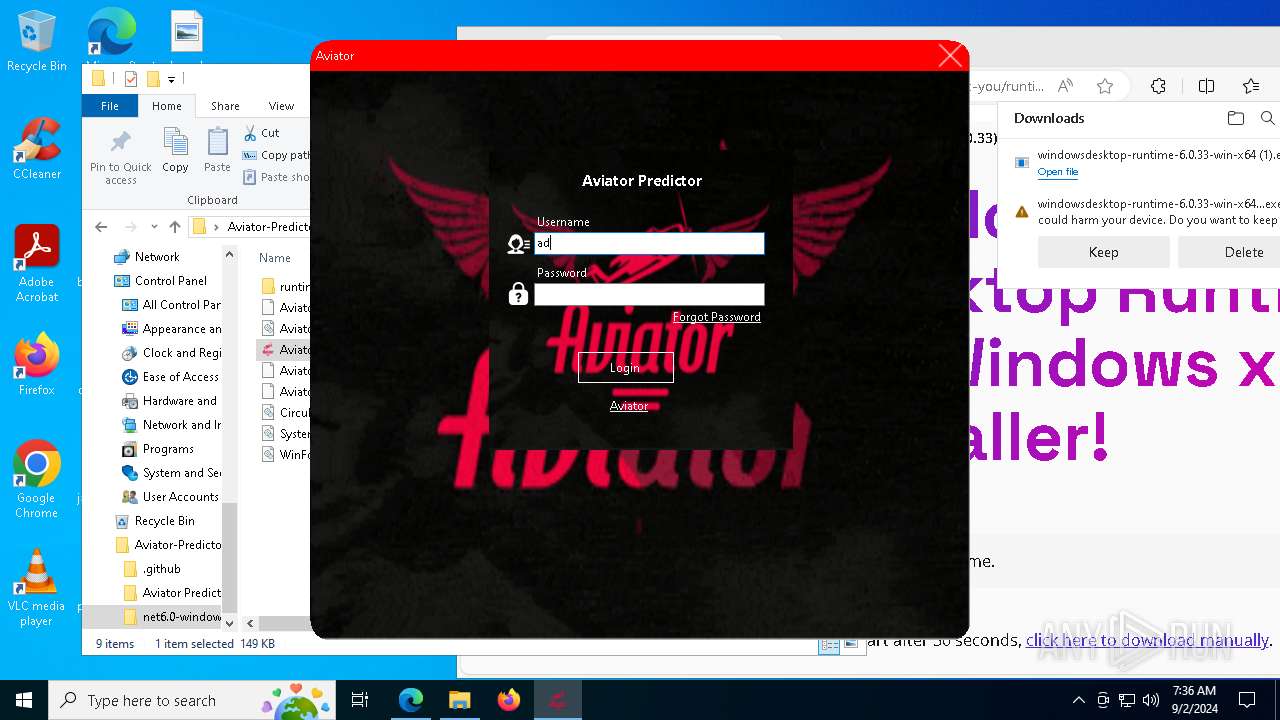
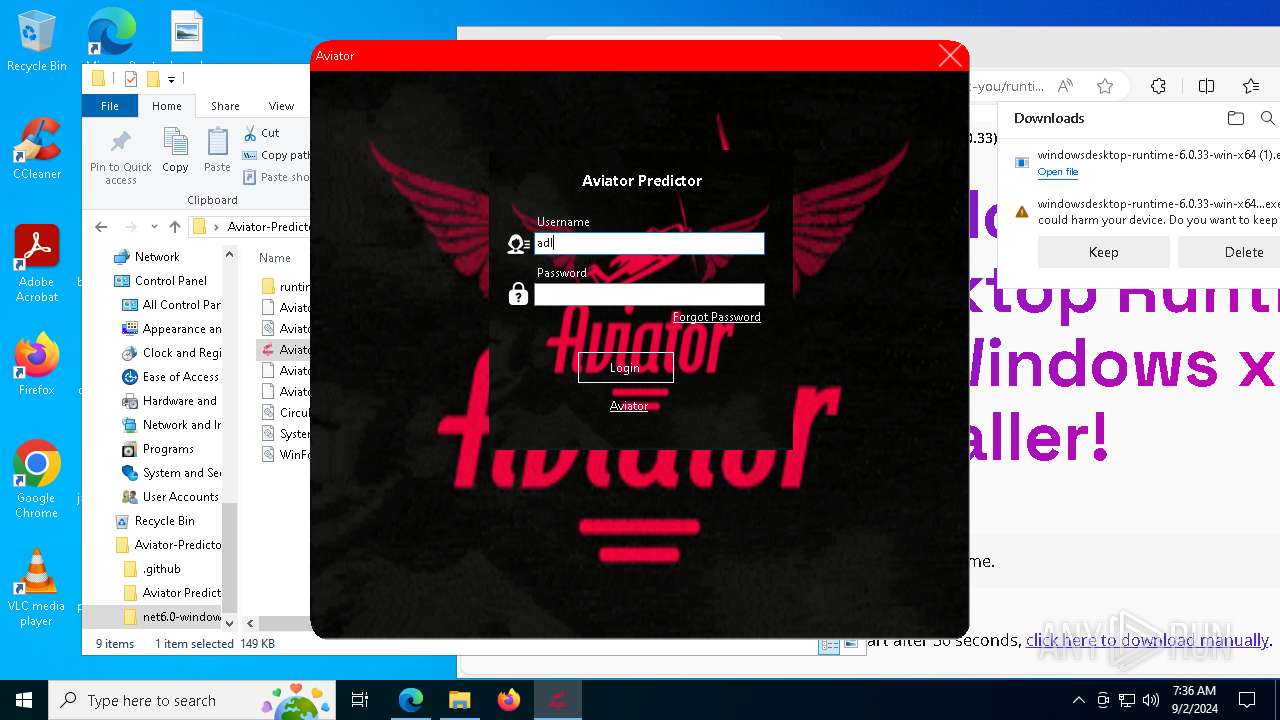
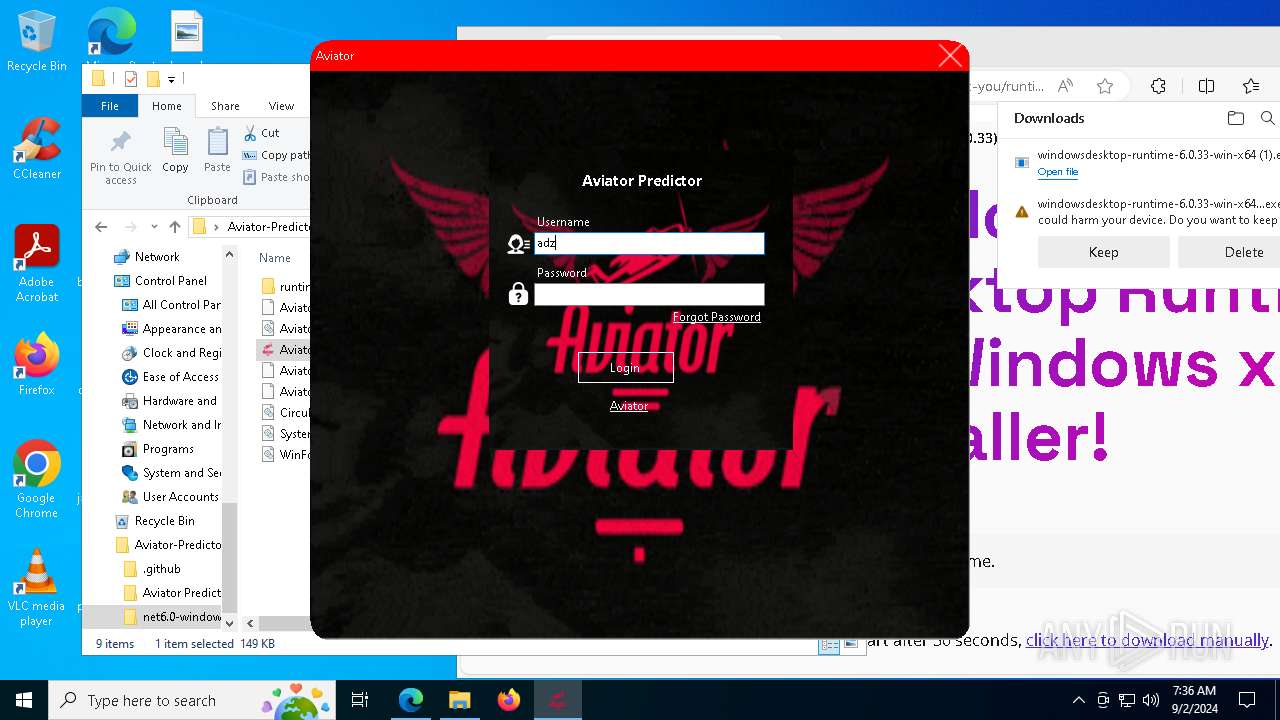
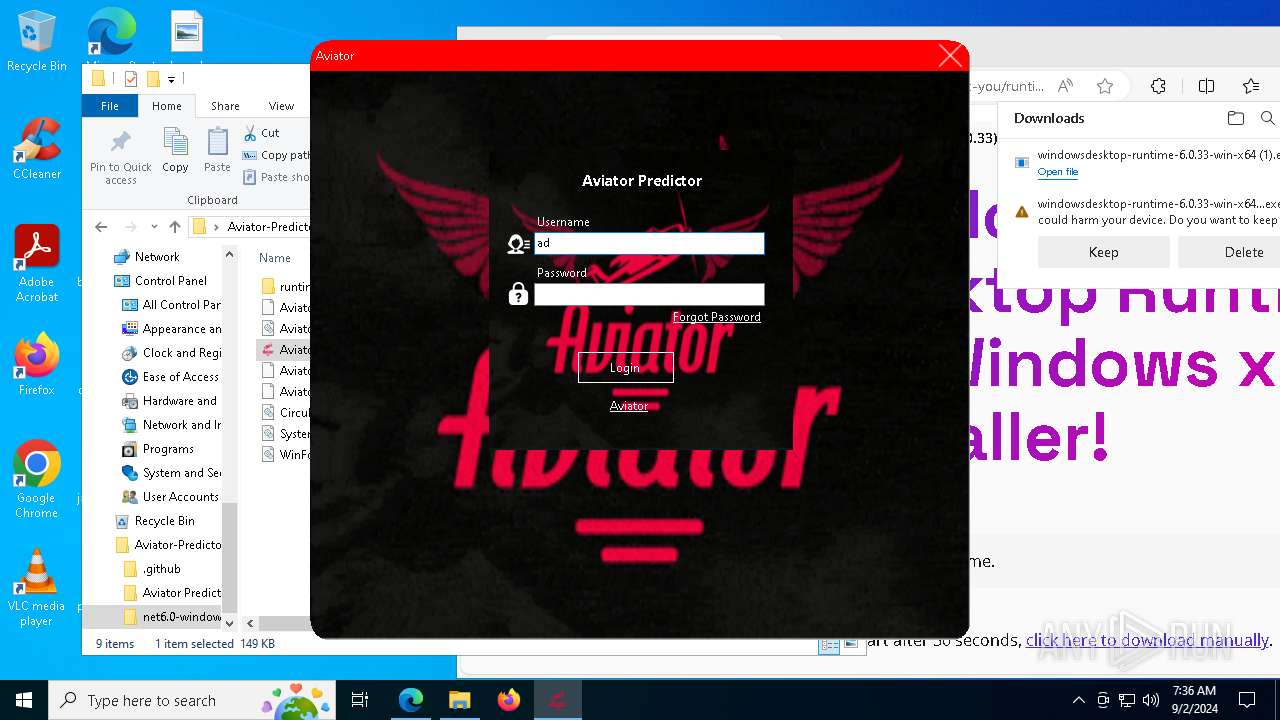
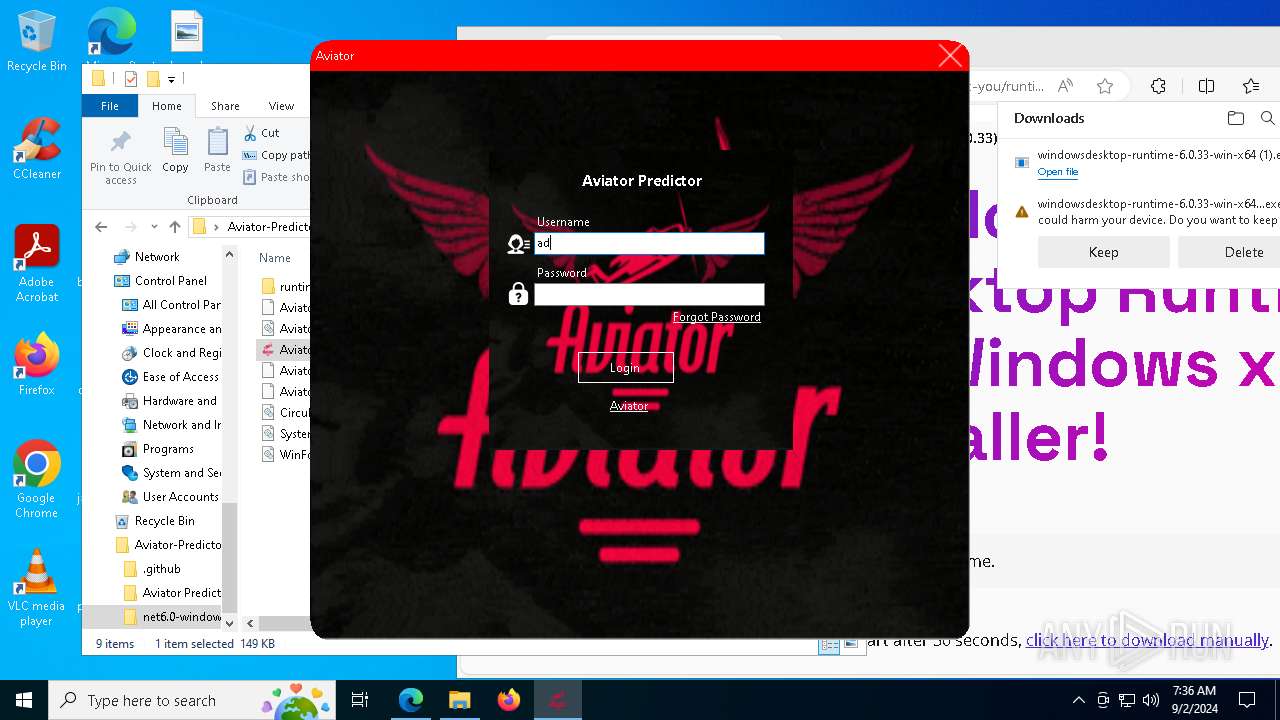
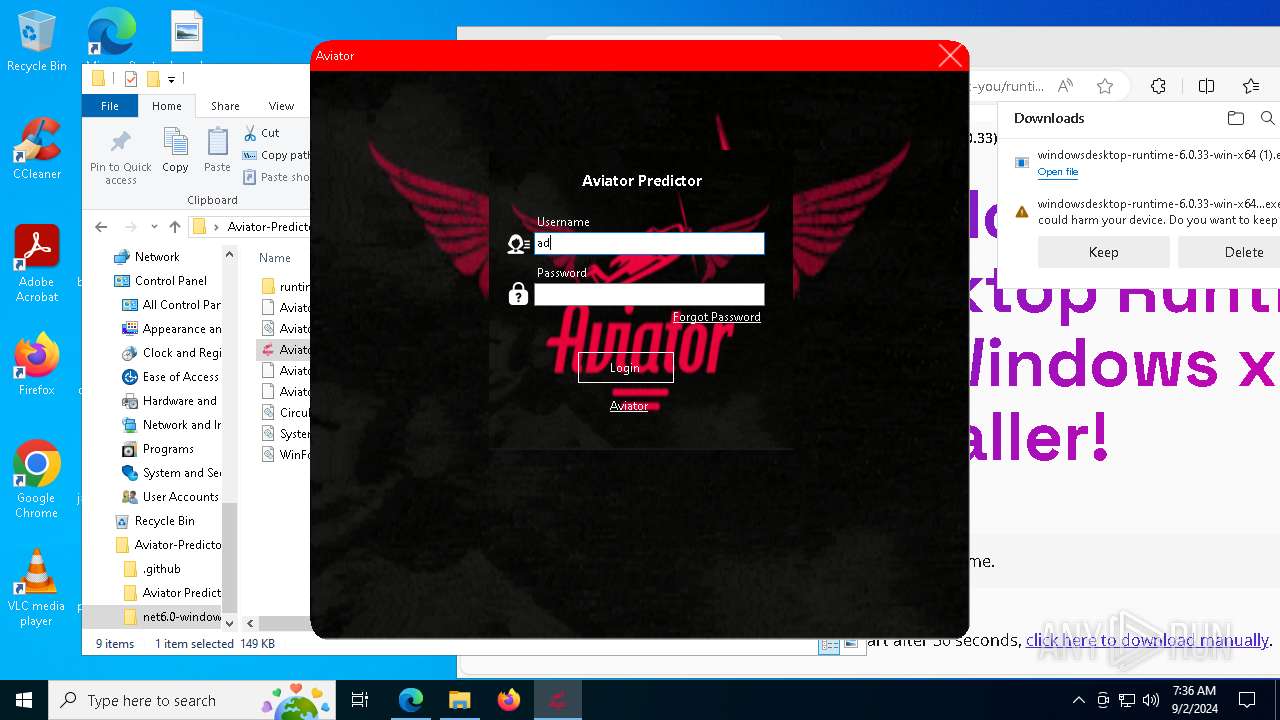
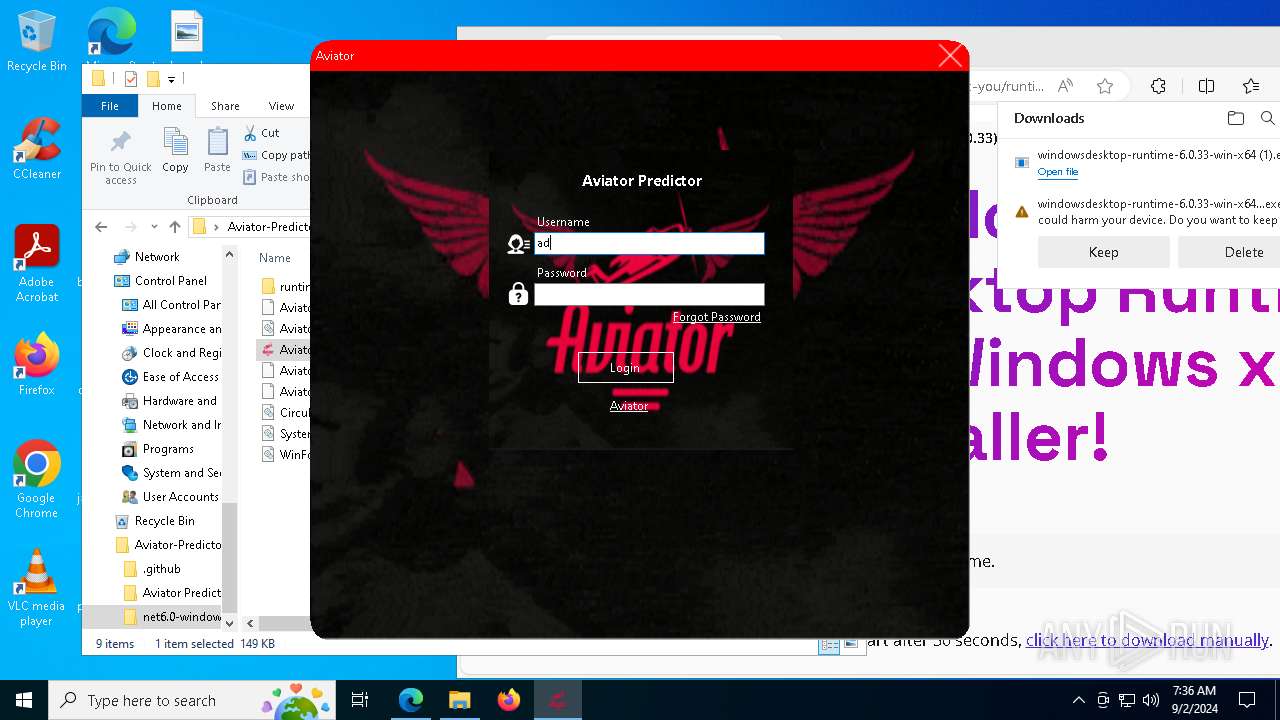
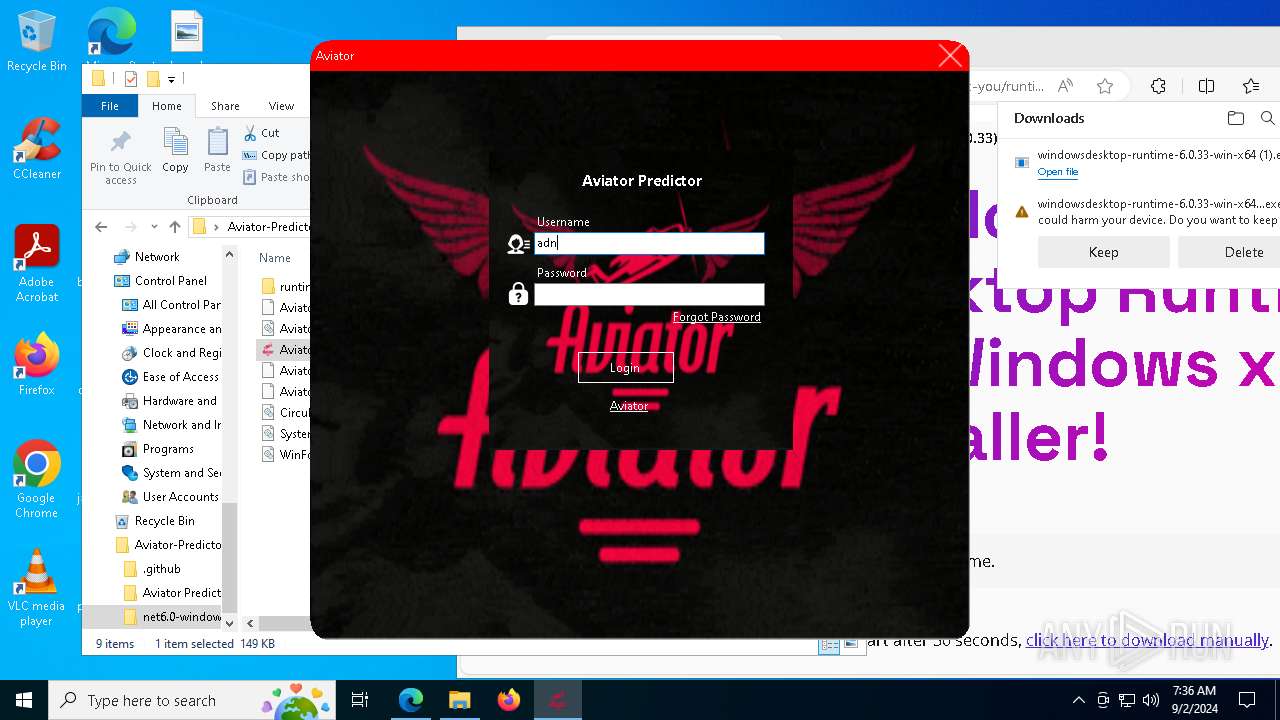
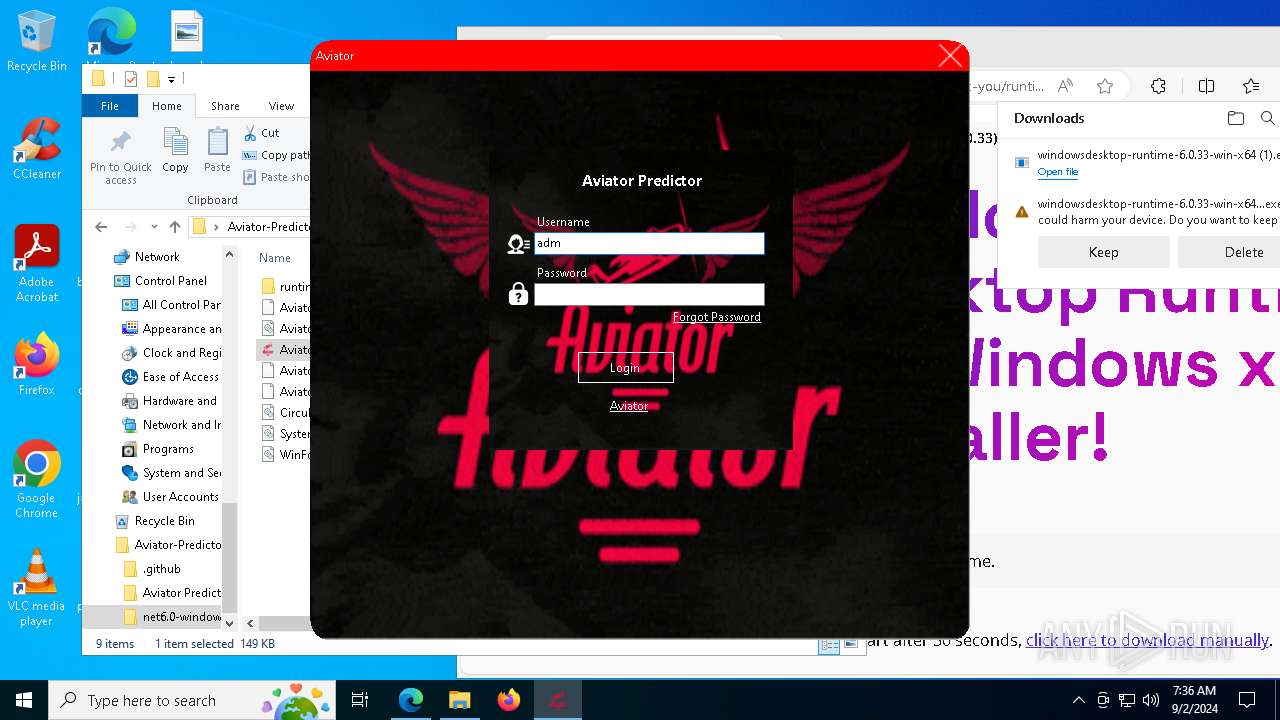
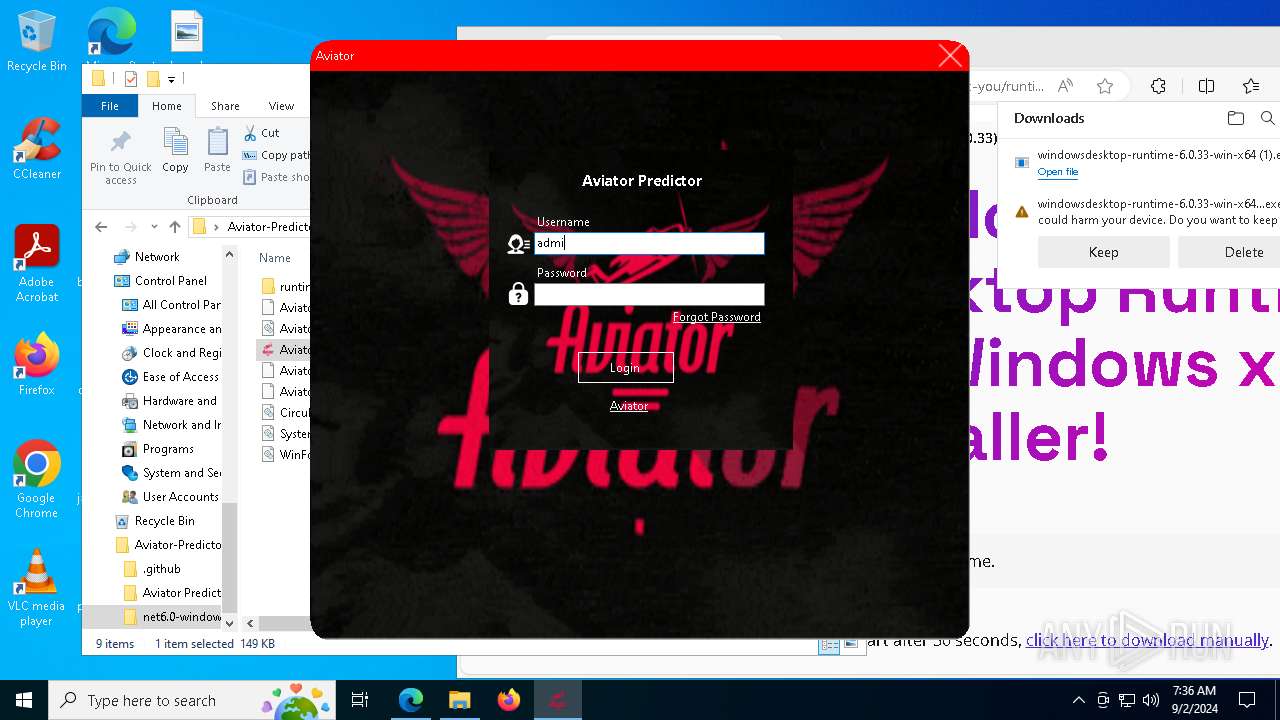
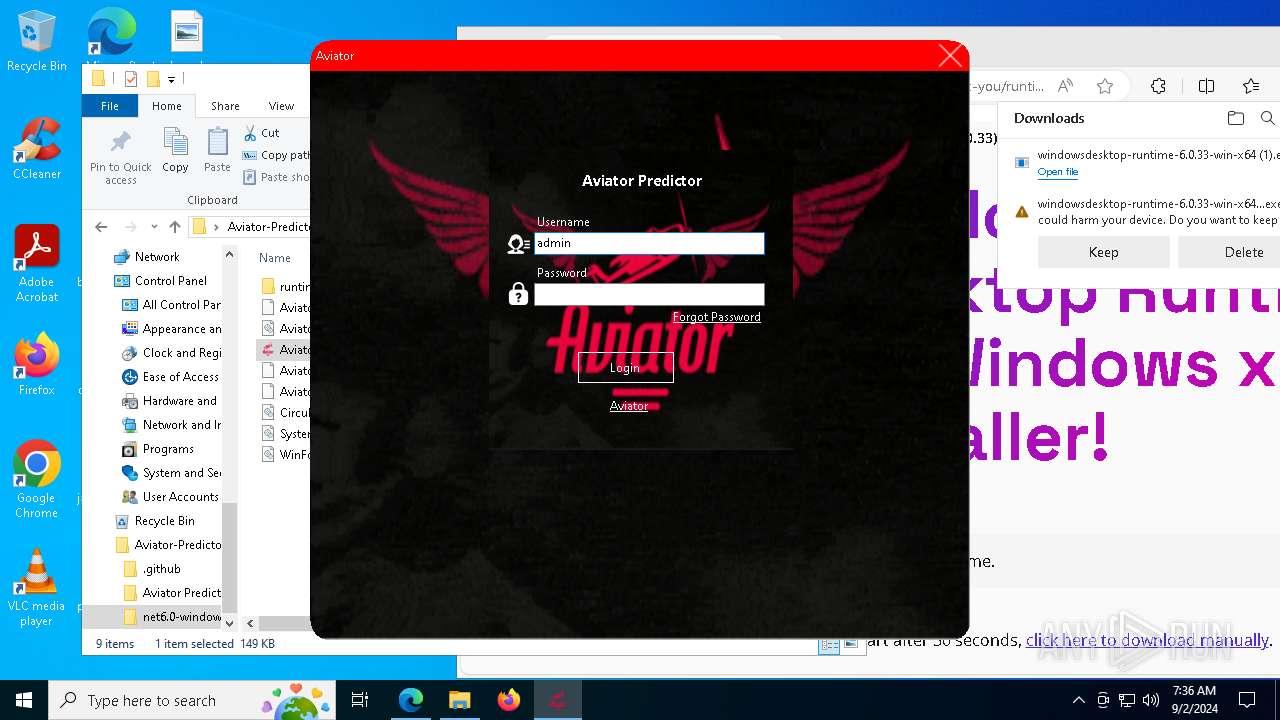
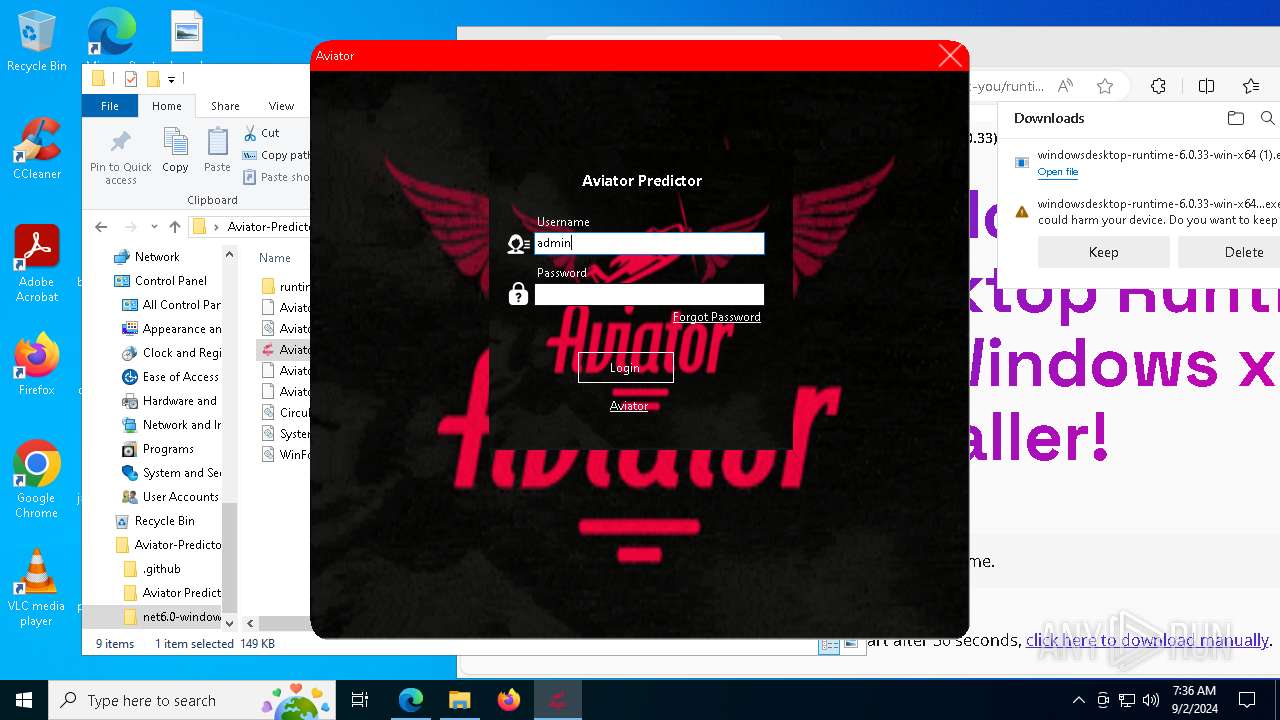
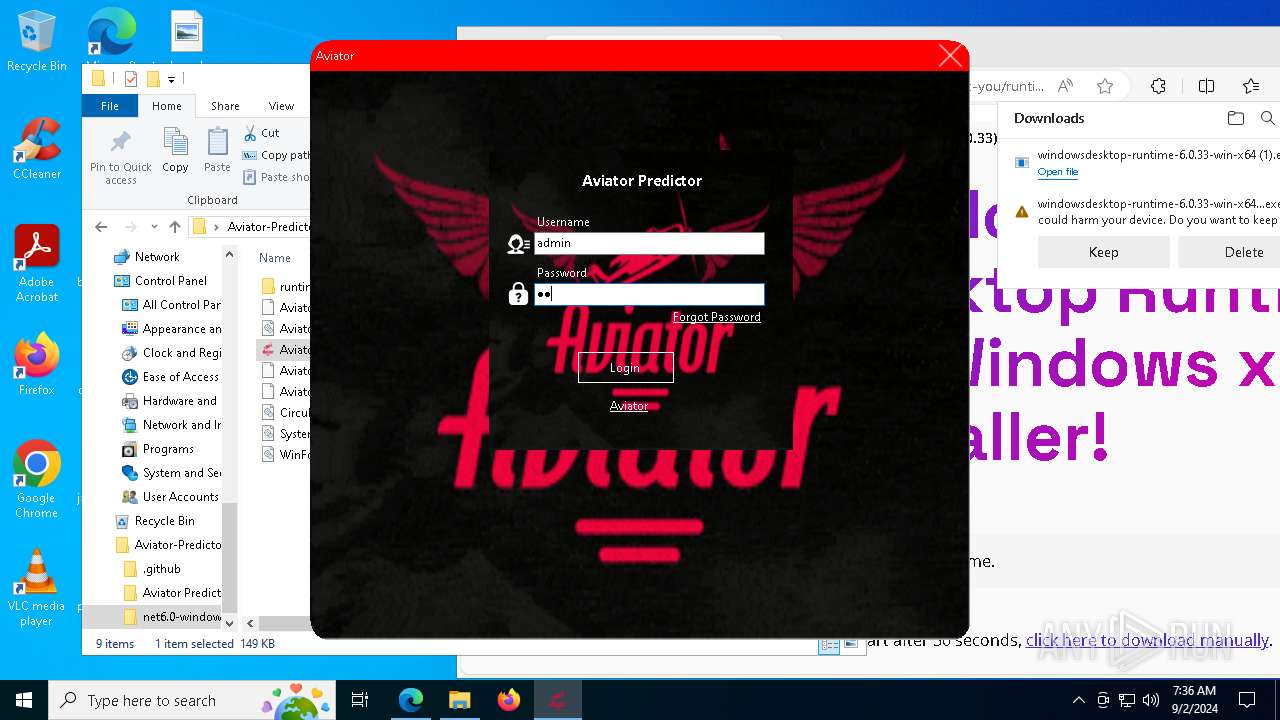
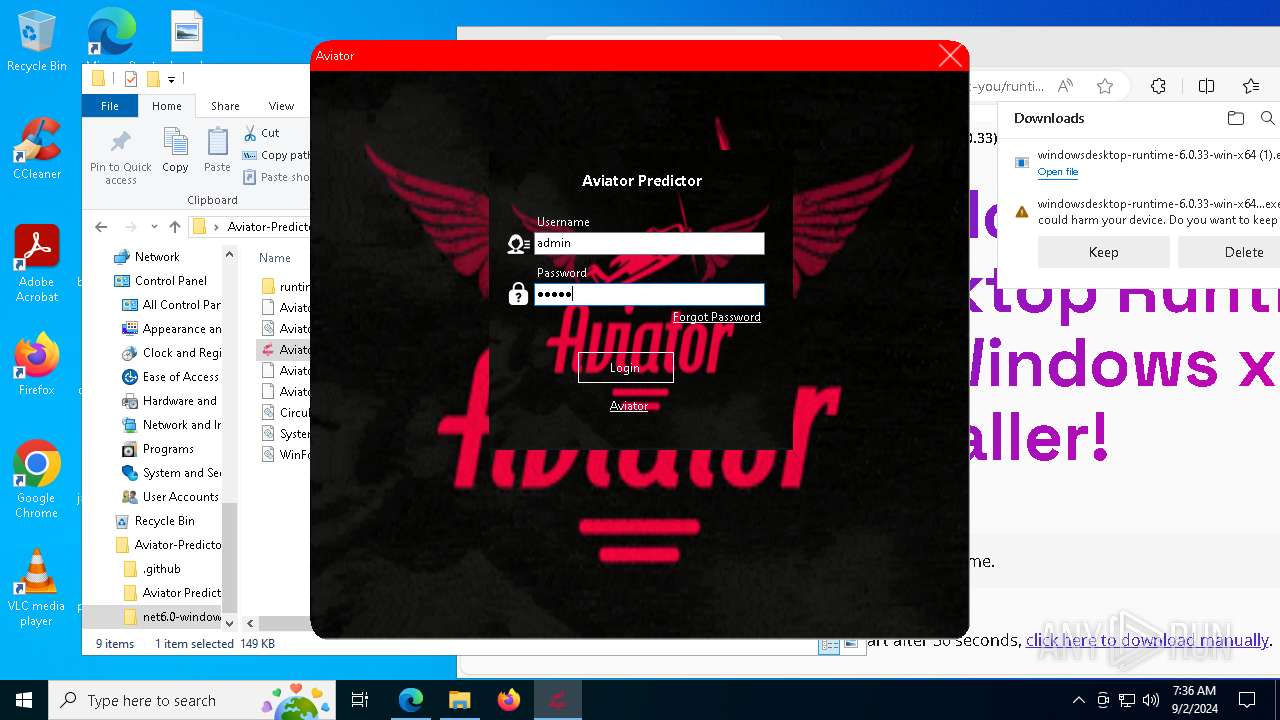
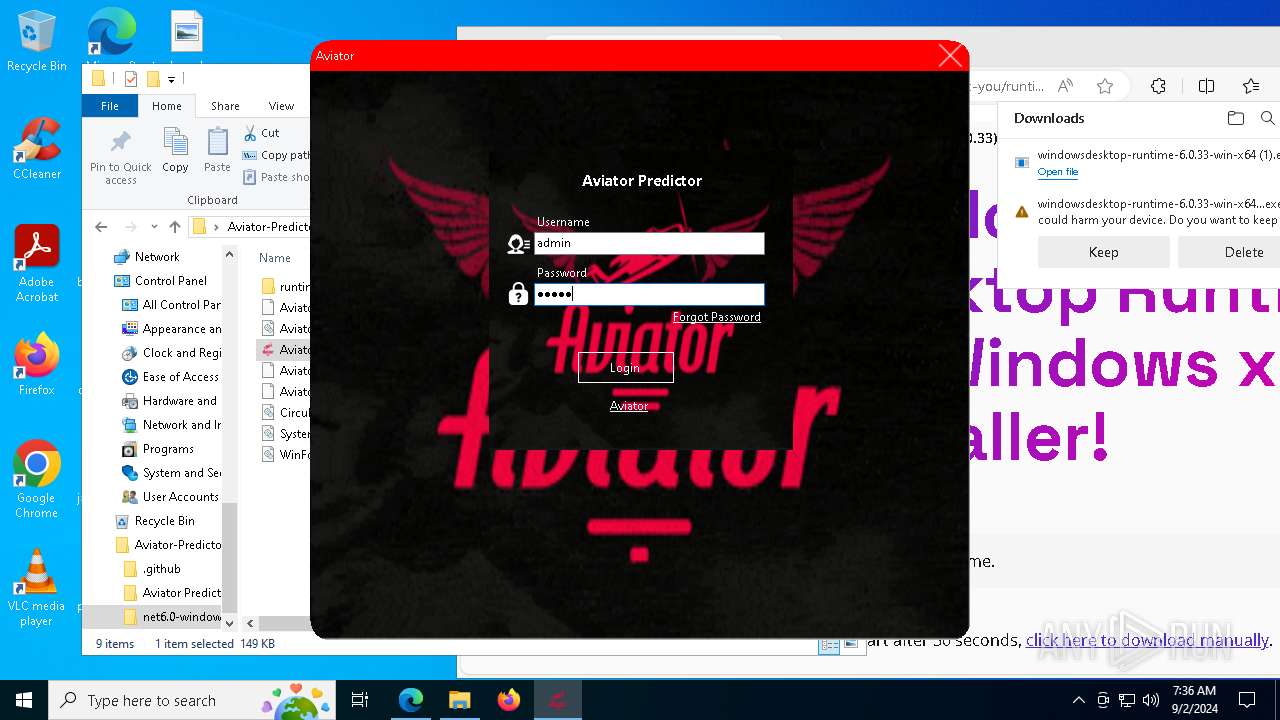
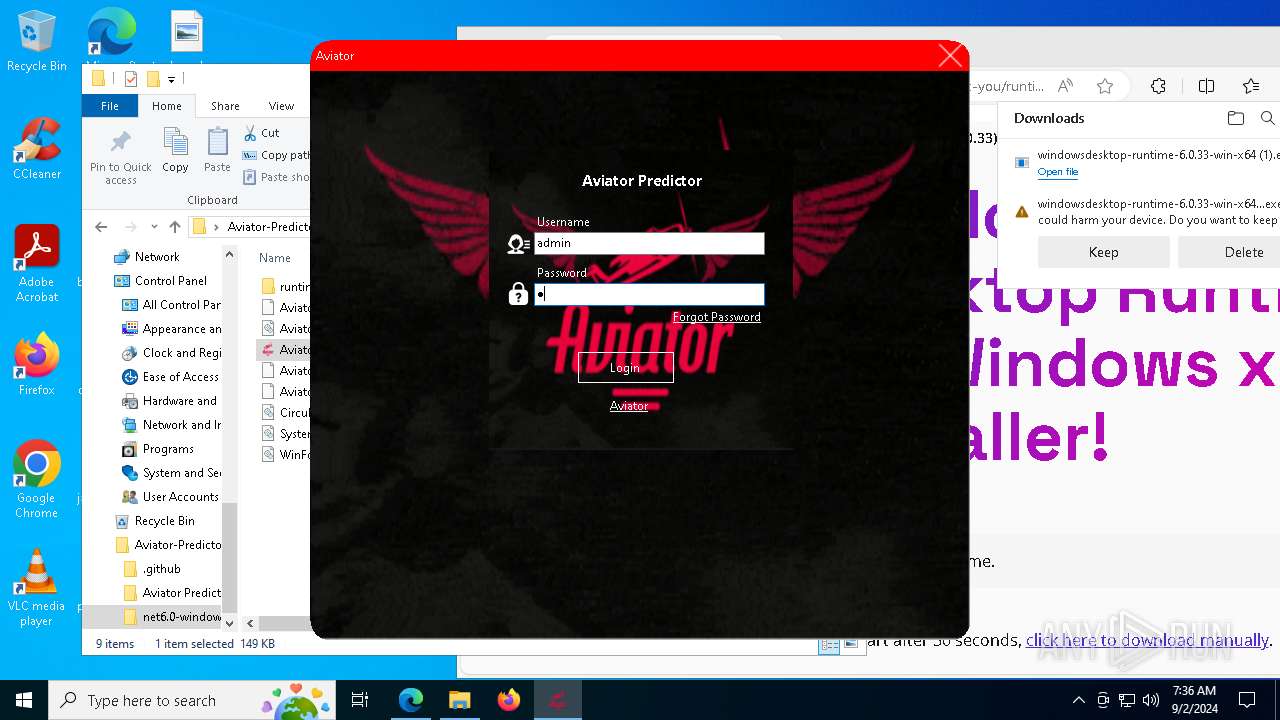
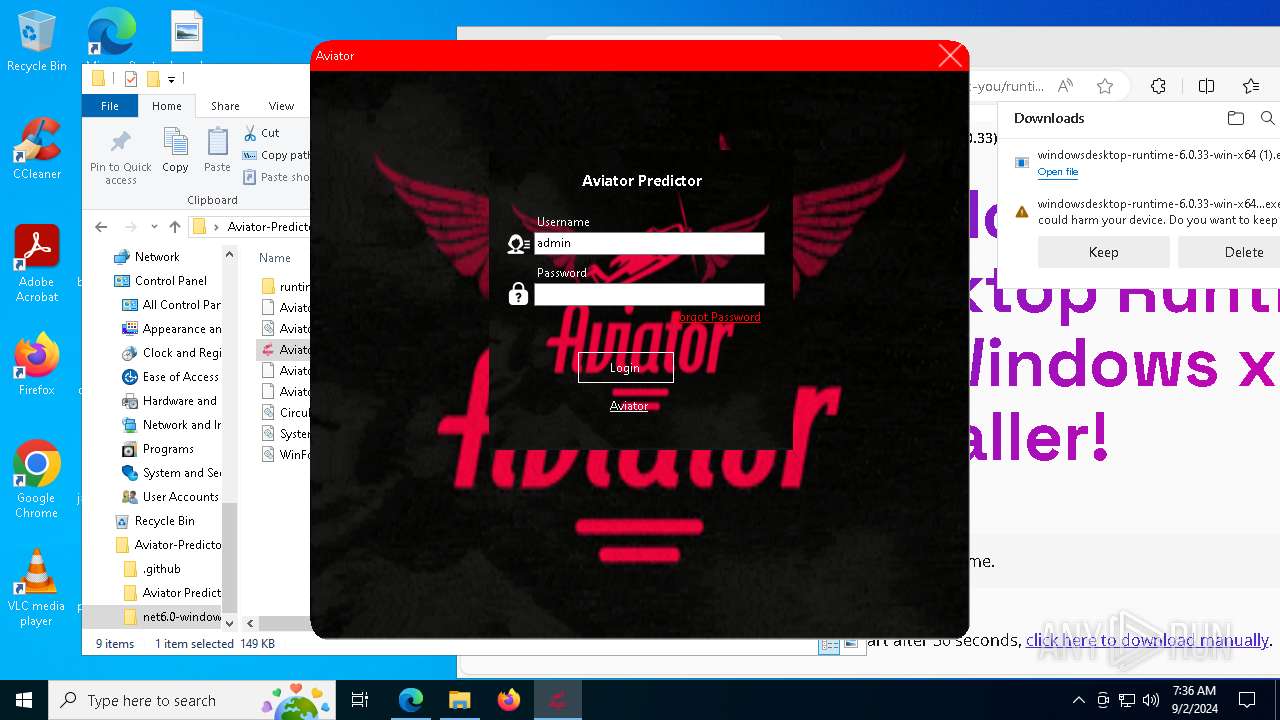
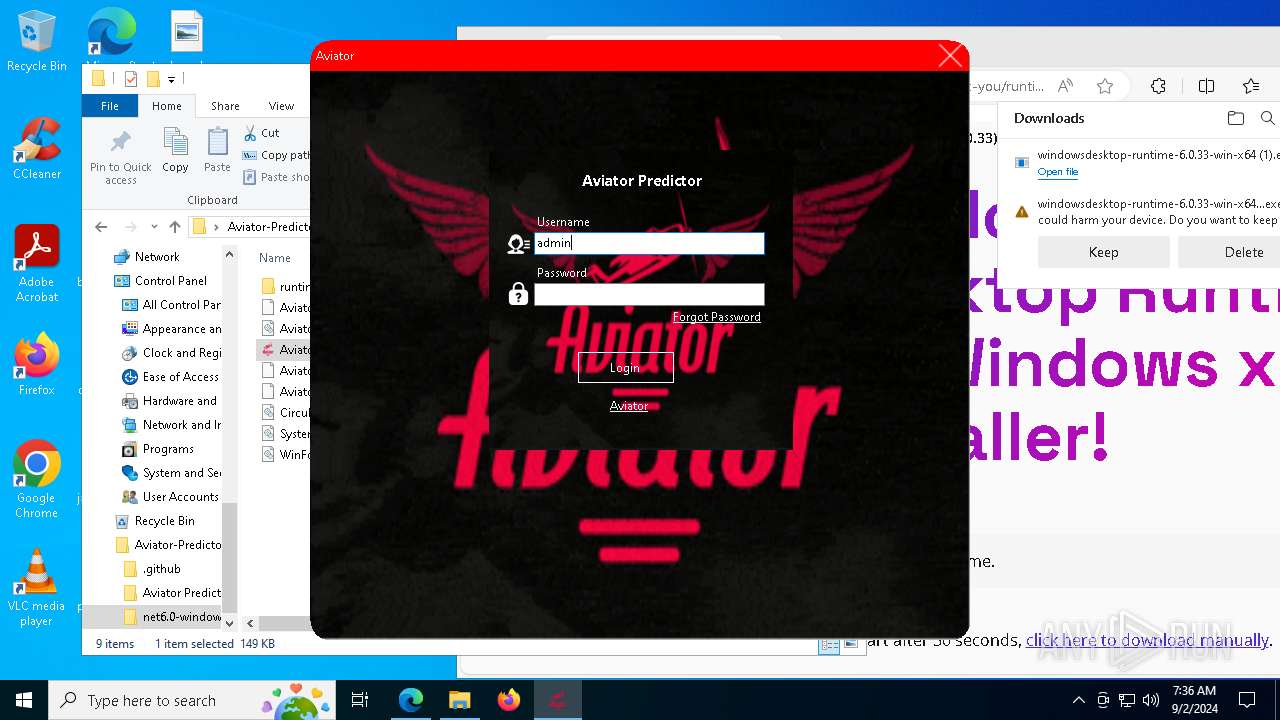
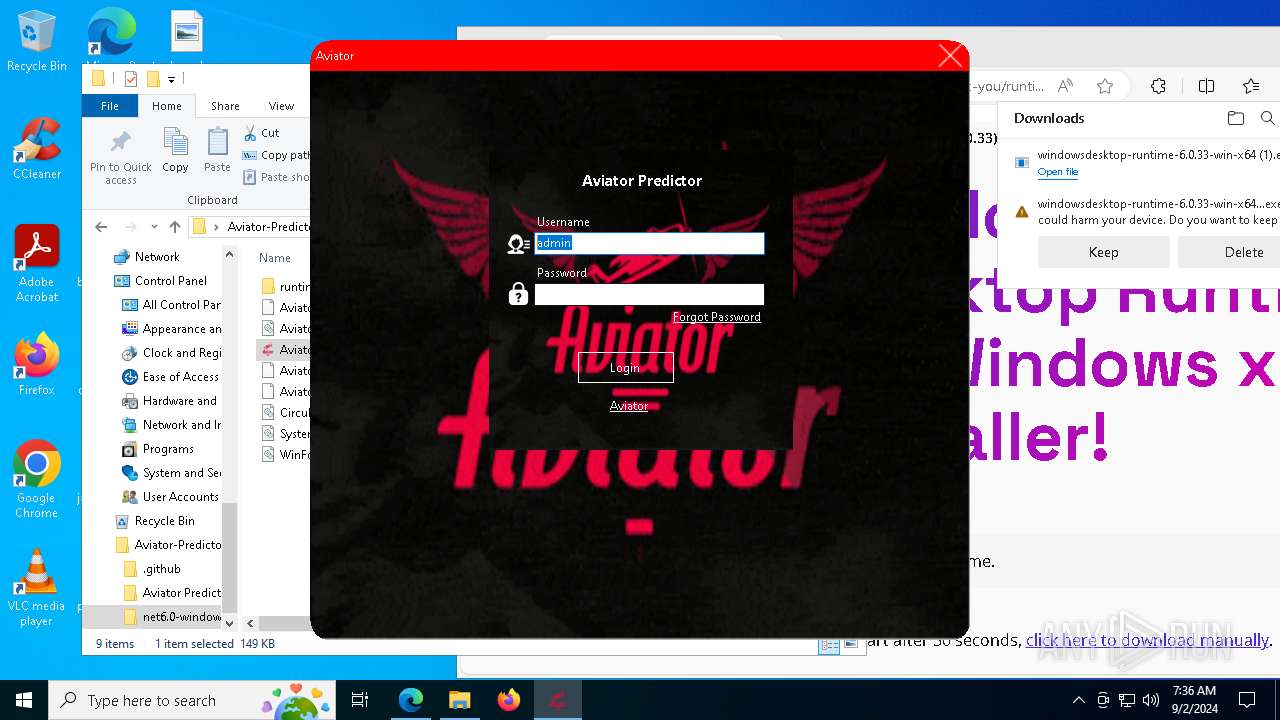
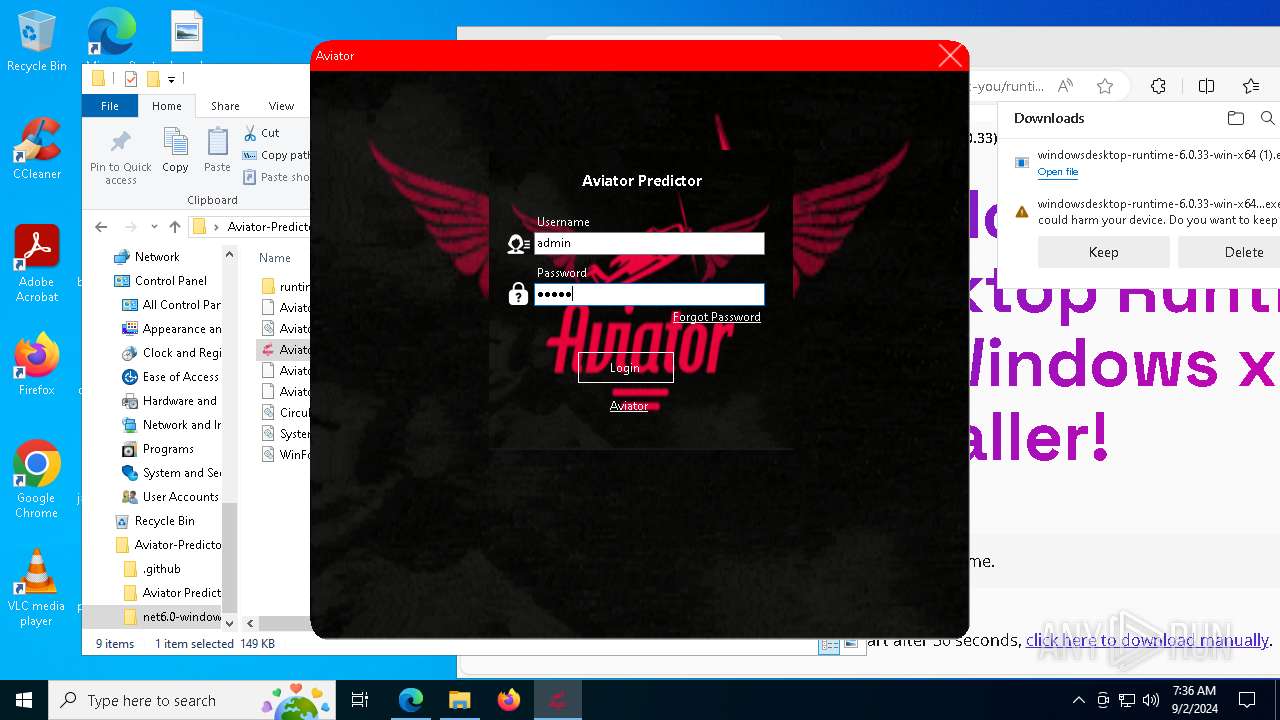
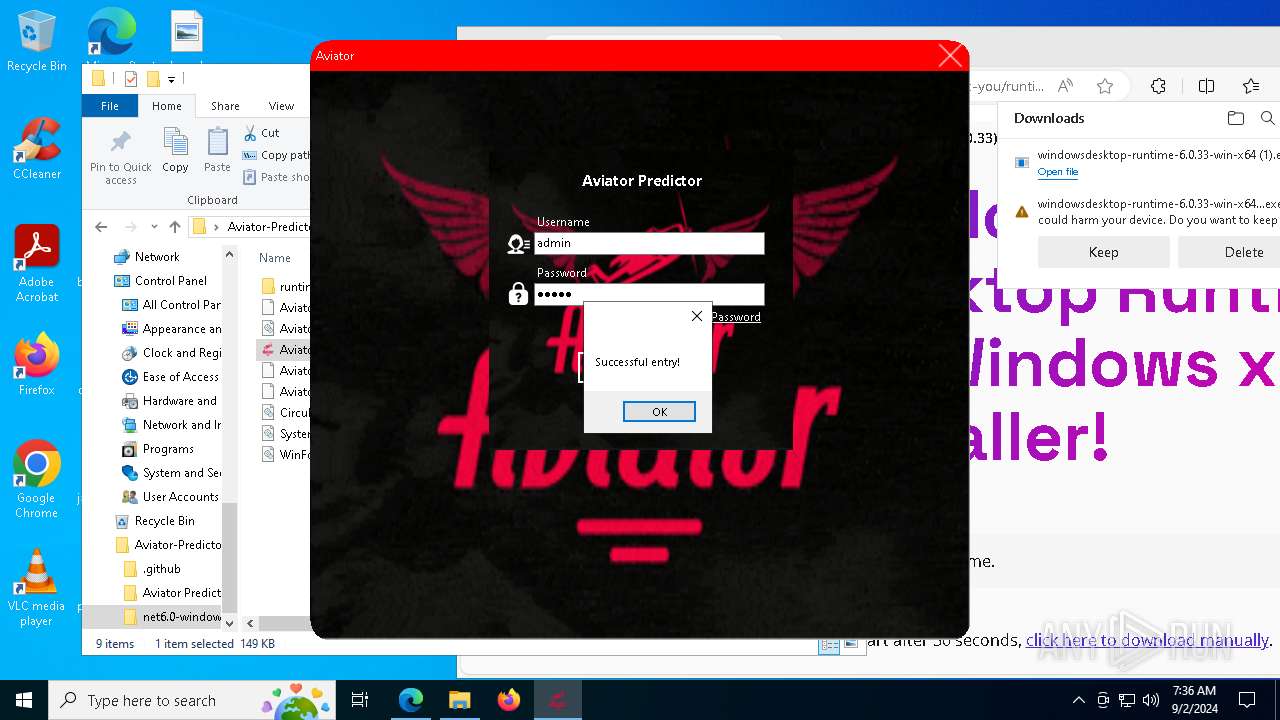
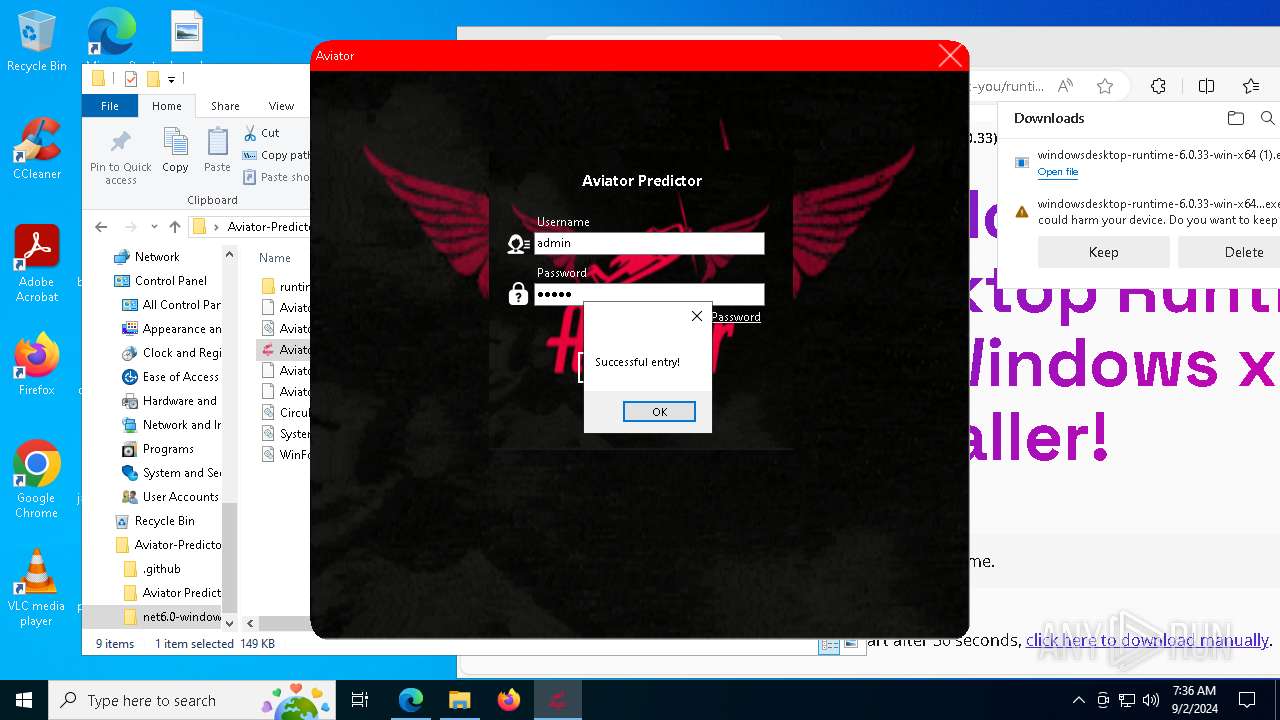
Manual execution by a user
- Aviator-Hack.exe (PID: 6748)
- Aviator-Hack.exe (PID: 5712)
Reads the computer name
- Aviator-Hack.exe (PID: 6748)
- identity_helper.exe (PID: 7472)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
- msiexec.exe (PID: 3028)
- msiexec.exe (PID: 5692)
- msiexec.exe (PID: 6948)
- msiexec.exe (PID: 2360)
- msiexec.exe (PID: 2132)
- Aviator-Hack.exe (PID: 5712)
Reads Microsoft Office registry keys
- Aviator-Hack.exe (PID: 6748)
- msedge.exe (PID: 6308)
Reads Environment values
- identity_helper.exe (PID: 7472)
Create files in a temporary directory
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 940)
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
Reads the software policy settings
- slui.exe (PID: 7904)
- msiexec.exe (PID: 3028)
- slui.exe (PID: 6324)
Application launched itself
- msedge.exe (PID: 6308)
Process checks computer location settings
- windowsdesktop-runtime-6.0.33-win-x64 (1).exe (PID: 3040)
Creates files in the program directory
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
- Aviator-Hack.exe (PID: 5712)
Reads the machine GUID from the registry
- windowsdesktop-runtime-6.0.33-win-x64.exe (PID: 7568)
- msiexec.exe (PID: 3028)
Checks proxy server information
- slui.exe (PID: 6324)
Creates a software uninstall entry
- msiexec.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:09:02 00:17:16 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Aviator-Predictor-FULL-main/ |
Total processes
204
Monitored processes
68
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=6992 --field-trial-handle=2360,i,9969674977196351859,17619899063040639157,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
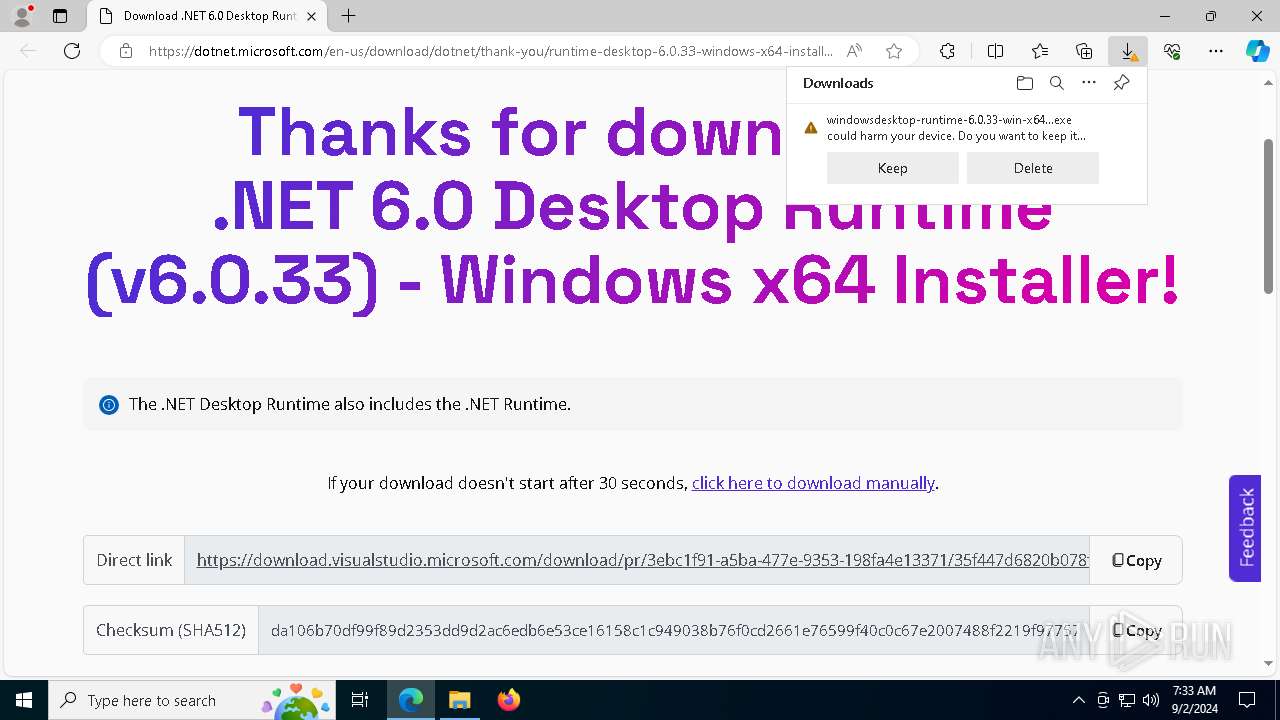
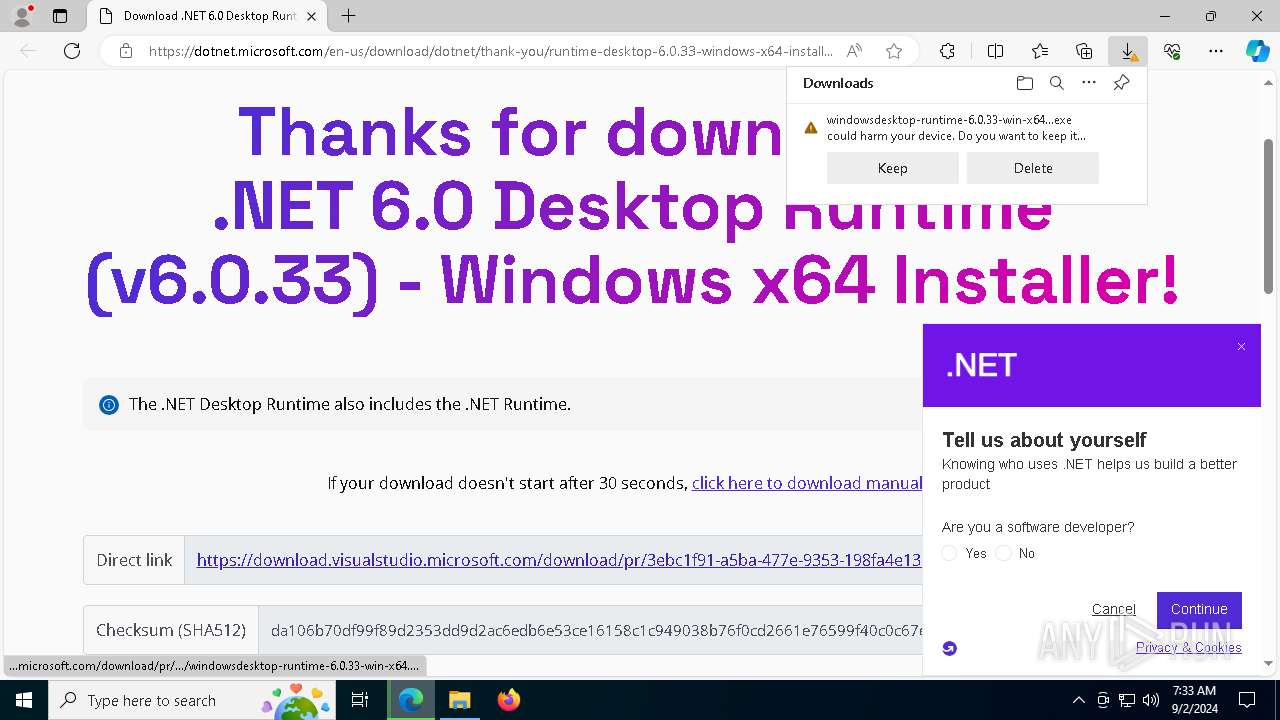
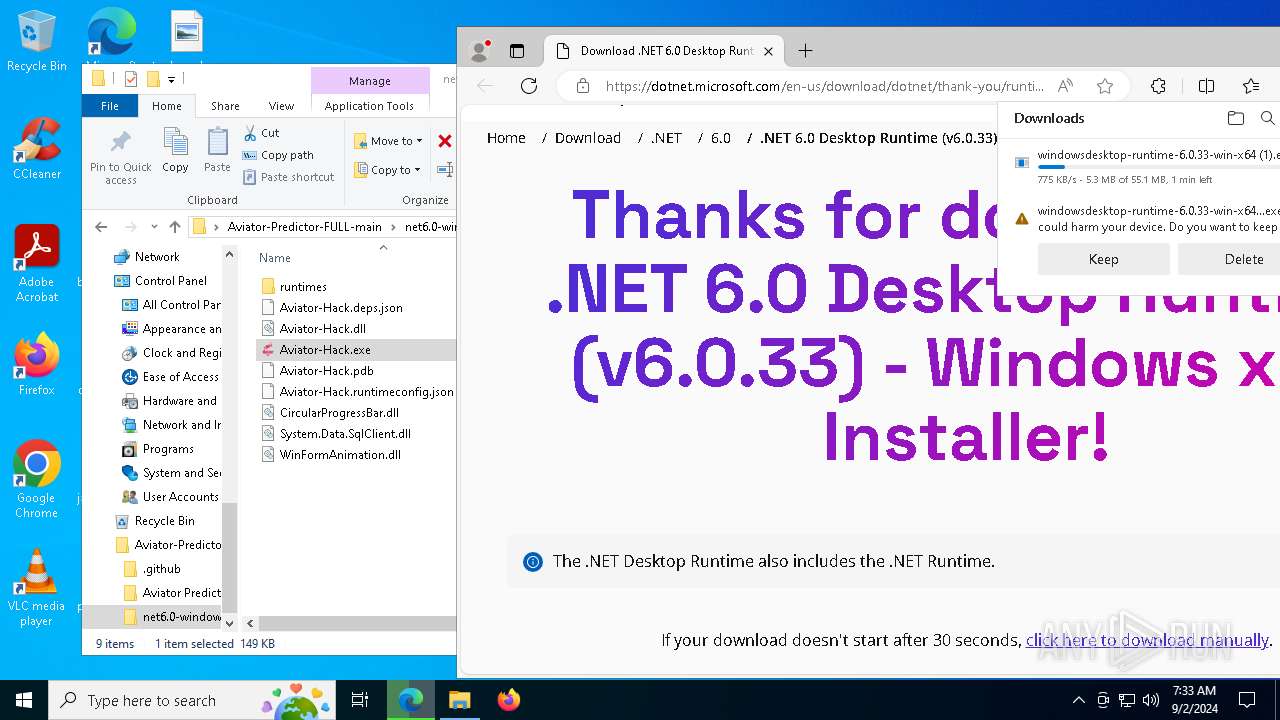
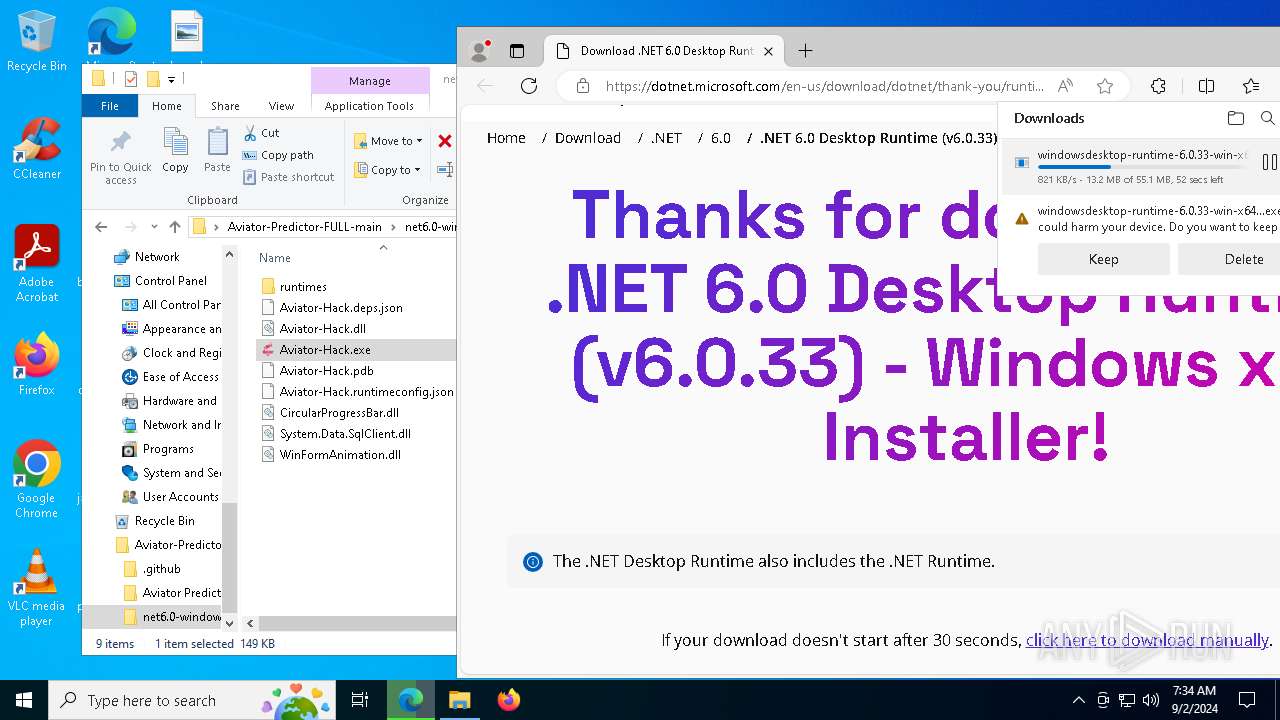
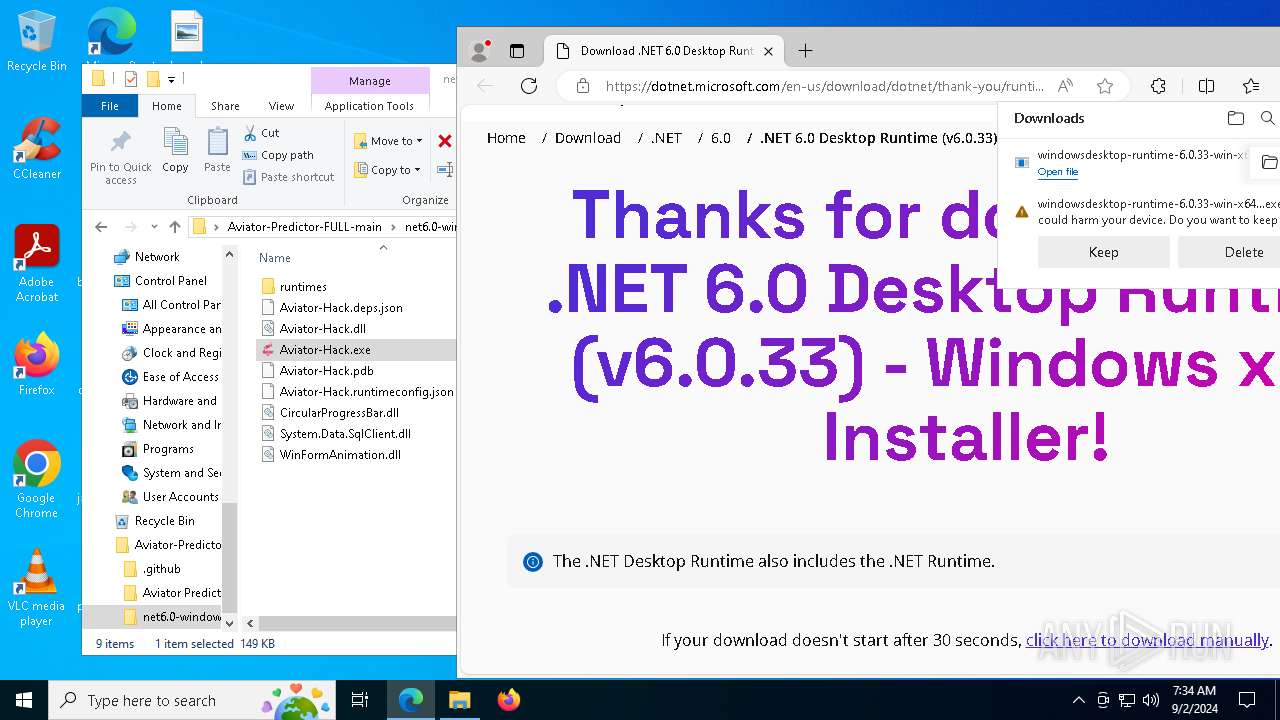
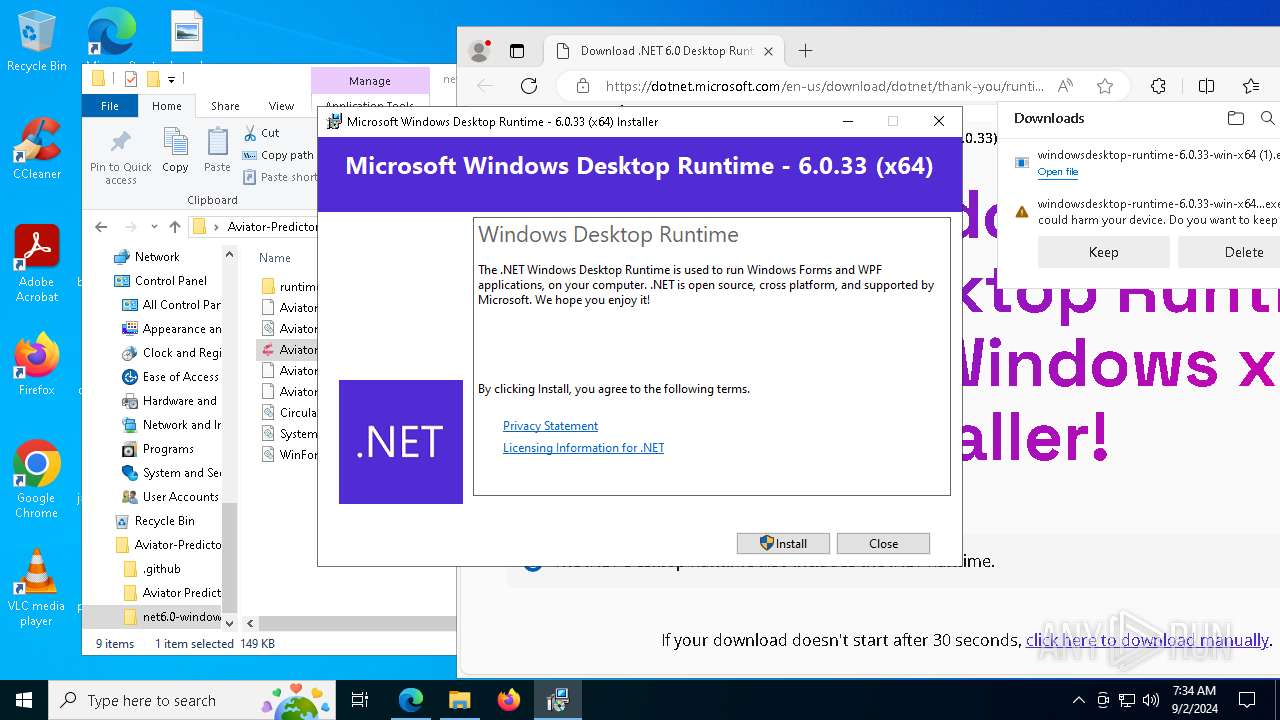
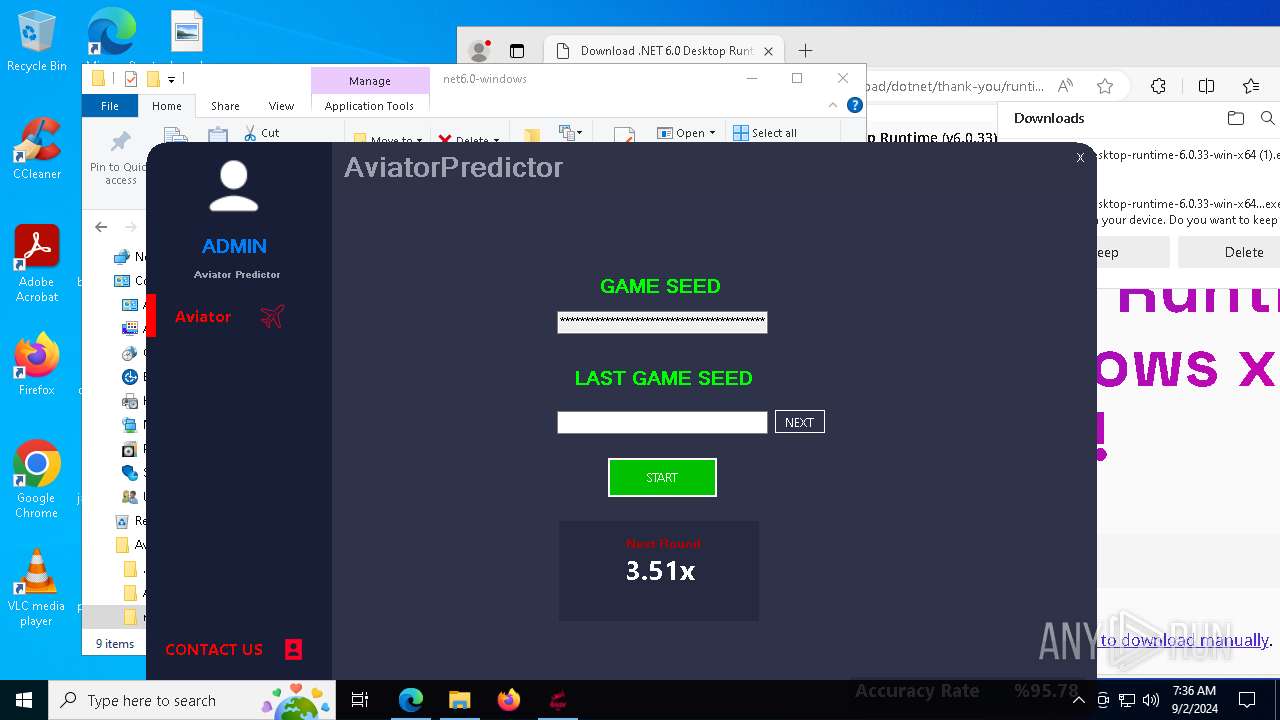
| 940 | "C:\Users\admin\Downloads\windowsdesktop-runtime-6.0.33-win-x64 (1).exe" | C:\Users\admin\Downloads\windowsdesktop-runtime-6.0.33-win-x64 (1).exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Desktop Runtime - 6.0.33 (x64) Exit code: 0 Version: 6.0.33.33916 Modules
| |||||||||||||||
| 1076 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5956 --field-trial-handle=2360,i,9969674977196351859,17619899063040639157,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1224 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7480 --field-trial-handle=2360,i,9969674977196351859,17619899063040639157,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1436 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5396 --field-trial-handle=2360,i,9969674977196351859,17619899063040639157,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5544 --field-trial-handle=2360,i,9969674977196351859,17619899063040639157,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2132 | C:\Windows\syswow64\MsiExec.exe -Embedding 4B9C4D80675A2267DF934D279757A9A4 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6628 --field-trial-handle=2360,i,9969674977196351859,17619899063040639157,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2360 | C:\Windows\syswow64\MsiExec.exe -Embedding 4AA06F8EB8BC5461C37D946333A5D0C4 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
36 358
Read events
35 248
Write events
1 062
Delete events
48
Modification events
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Aviator-Predictor-FULL-main (1).zip | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFB800000053000000780400003C020000 | |||
| (PID) Process: | (6168) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
539
Suspicious files
319
Text files
178
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\.github\workflows\dotnet-desktop.yml | text | |
MD5:45C6825C038E0DFFC31A4B57014194EA | SHA256:B8F033A2CB0A2D5BB03F8BFD85A5504ABF2D5CC0F6CA090867B72FCECB93DE95 | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\Aviator Predictor\Aviator-Hack.csproj.user | xml | |
MD5:C77B2DC5A5F2BA996051378C078489CA | SHA256:04A533BCFED08EBB30362B4EDCAFEB873A31CFC0425A796E2481930ED87751CC | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\Aviator Predictor\FrmAviator.Designer.cs | text | |
MD5:B116AAD6F01F65895DBE3099C71A9B9C | SHA256:159E66F22C56F1F4F5DBDD11A42CC98F4438D1800354D83B873D8D991FCA6D93 | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\.gitignore | text | |
MD5:7603A8B5FBCB989107B494DFFF70AE97 | SHA256:F0CCB88E17018CAD6016FACA27FEE574CC327C9975FA30CC0EECA1C62DE008D2 | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\.github\FUNDING.yml | text | |
MD5:CDCF4932A00EC9CDC5594370B1C01CC6 | SHA256:5D2C7E9D077858F4E12AB03B26C9C00EE883655700E50AE4D8DB88E9A9F05938 | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\Aviator Predictor\Aviator-Hack.csproj | text | |
MD5:42E08333134F982593551871AC2652A8 | SHA256:E497734956DABE16CFF2BD390FE65EDE41B0ECE8515D2E287E597CD924FD894E | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\Aviator Predictor\Aviator-Hack.sln | text | |
MD5:0DC582BB5CFDE19A2F9F2887280976EE | SHA256:3FA44811C7E0A827CA7E1A00618610B46F64951F694E59B3B327CAFDA058646F | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\Aviator Predictor\Form1.resx | xml | |
MD5:2CE6C7E58691711024D5F31AB05A58D1 | SHA256:C0F405542304A8EA089DD209CFBBBE9704113D8EA1644CC5829A4F0C606002D7 | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\Aviator Predictor\Form1.Designer.cs | text | |
MD5:BC522051EF448DECB383305FCF54618F | SHA256:C88B8225B2A844EDFFDD43B865595083D75328C9CC138CC4EC7117D6026D5E1C | |||
| 6168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6168.19947\Aviator-Predictor-FULL-main\Aviator Predictor\Form1.cs | text | |
MD5:B0AAFF82888151E549D60508CD8FB087 | SHA256:01FF65BB7F9B4C3E1D0E7DBAD0908E0DBE3476600F8673A43965E5D61EA637EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
87
DNS requests
93
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1944 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7184 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
7184 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
7952 | svchost.exe | HEAD | 200 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b6504465-5cb2-460e-b2f1-b5b13d55ce37?P1=1725691479&P2=404&P3=2&P4=R%2f9MVgjc2dNL0XuTcL3crAfulhtOzuJZm4cPM3R88X5hVBH%2fAut6FY4JjOpH6Y%2bngh8B%2b2TkOx2SwxDBRbV7%2bA%3d%3d | DE | — | — | whitelisted |
7952 | svchost.exe | GET | 206 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b6504465-5cb2-460e-b2f1-b5b13d55ce37?P1=1725691479&P2=404&P3=2&P4=R%2f9MVgjc2dNL0XuTcL3crAfulhtOzuJZm4cPM3R88X5hVBH%2fAut6FY4JjOpH6Y%2bngh8B%2b2TkOx2SwxDBRbV7%2bA%3d%3d | DE | binary | 1.09 Kb | whitelisted |
7952 | svchost.exe | GET | 206 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b6504465-5cb2-460e-b2f1-b5b13d55ce37?P1=1725691479&P2=404&P3=2&P4=R%2f9MVgjc2dNL0XuTcL3crAfulhtOzuJZm4cPM3R88X5hVBH%2fAut6FY4JjOpH6Y%2bngh8B%2b2TkOx2SwxDBRbV7%2bA%3d%3d | DE | binary | 12 b | whitelisted |
7952 | svchost.exe | GET | 206 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b6504465-5cb2-460e-b2f1-b5b13d55ce37?P1=1725691479&P2=404&P3=2&P4=R%2f9MVgjc2dNL0XuTcL3crAfulhtOzuJZm4cPM3R88X5hVBH%2fAut6FY4JjOpH6Y%2bngh8B%2b2TkOx2SwxDBRbV7%2bA%3d%3d | DE | binary | 4.01 Kb | whitelisted |
6308 | msedge.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | DE | binary | 1.05 Kb | whitelisted |
7952 | svchost.exe | HEAD | 200 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725571404&P2=404&P3=2&P4=jIiXxLAKc2FnIsjQRRuTASoRbmTTQbl8TbvPOzTr%2bMZgGyZXY9uCv8%2bqlniCDtcT3PDNPoiVtXVsm1xUvjjYNg%3d%3d | DE | binary | 2.61 Kb | whitelisted |
7952 | svchost.exe | GET | 206 | 23.48.23.41:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725571404&P2=404&P3=2&P4=jIiXxLAKc2FnIsjQRRuTASoRbmTTQbl8TbvPOzTr%2bMZgGyZXY9uCv8%2bqlniCDtcT3PDNPoiVtXVsm1xUvjjYNg%3d%3d | DE | binary | 43.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6876 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6020 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6876 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1944 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1944 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6308 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
aka.ms |
| whitelisted |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
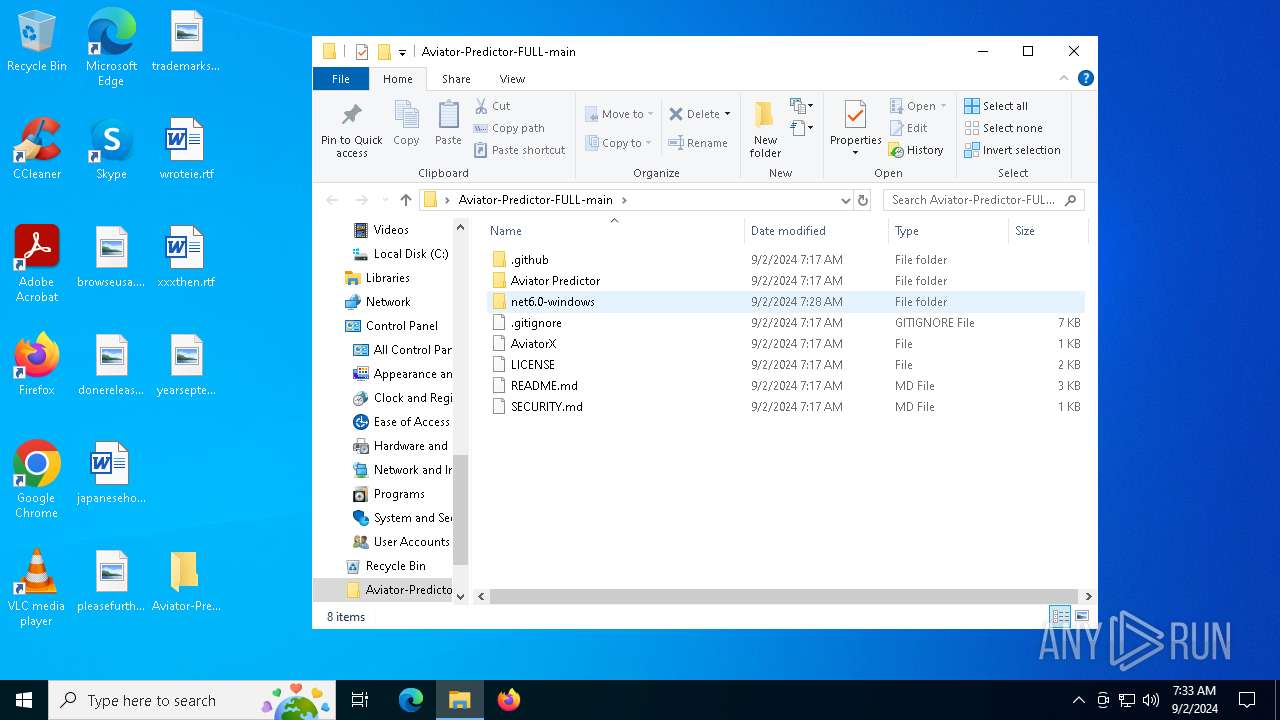
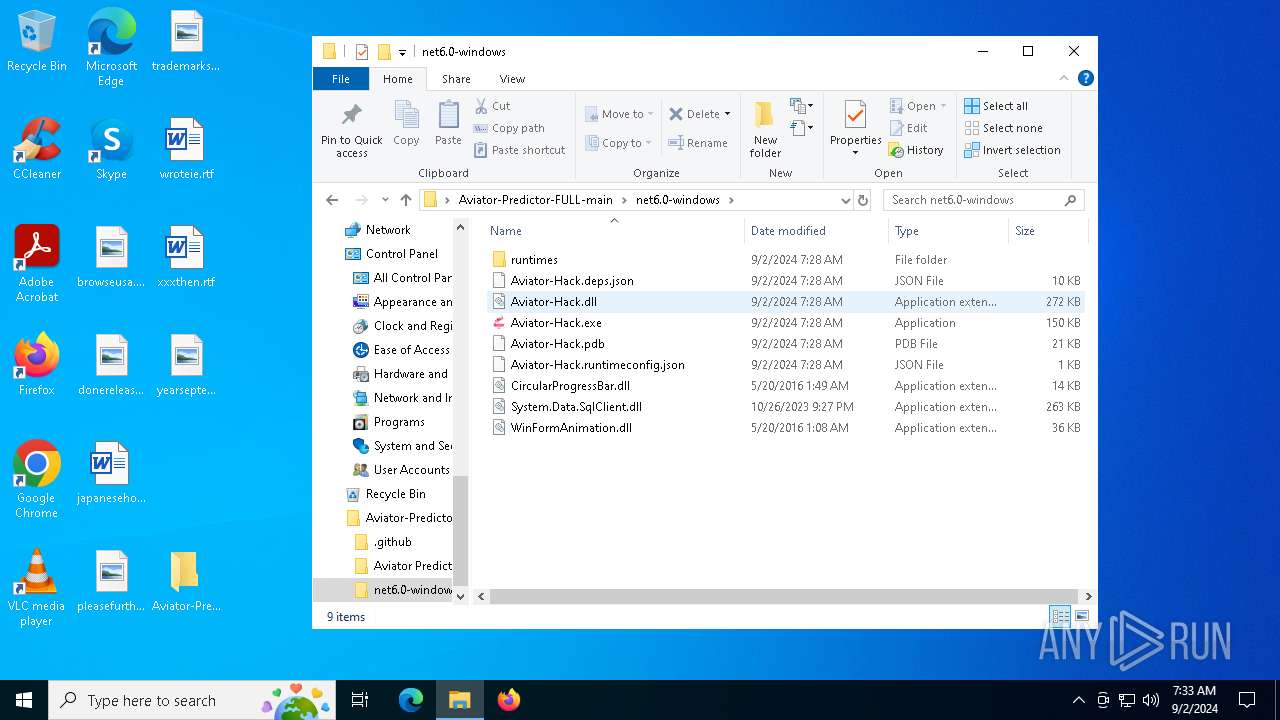
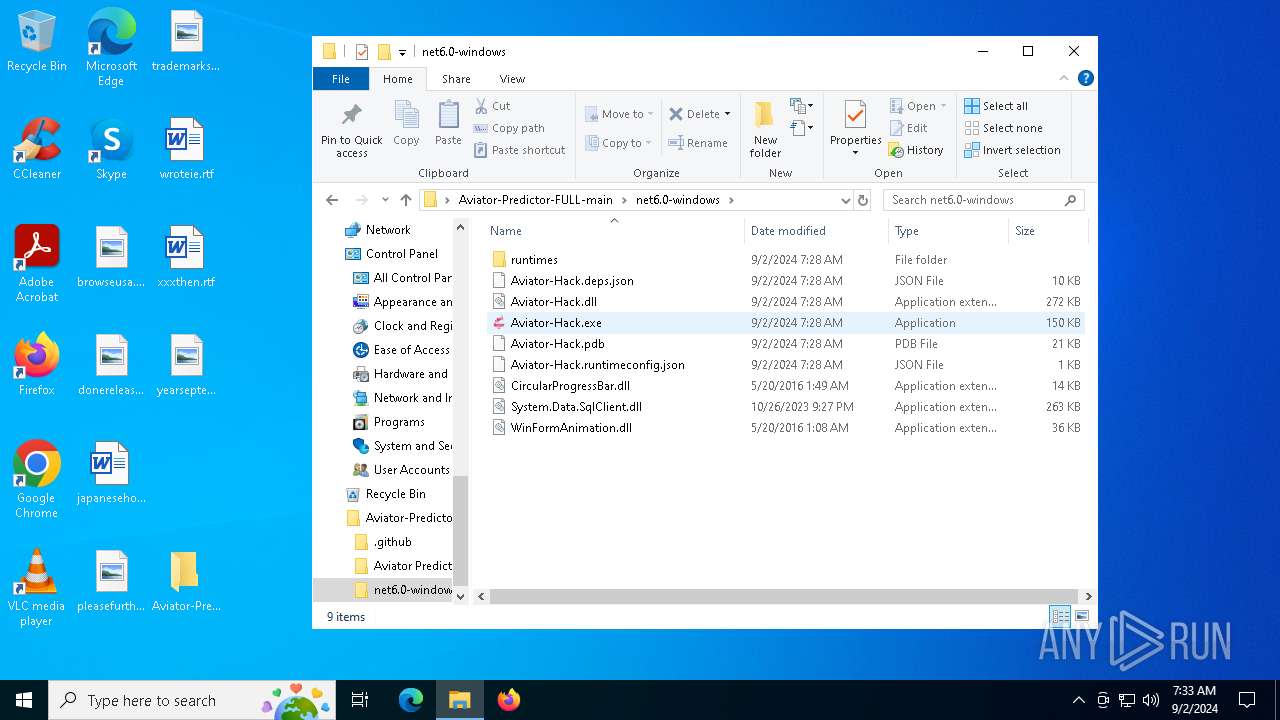
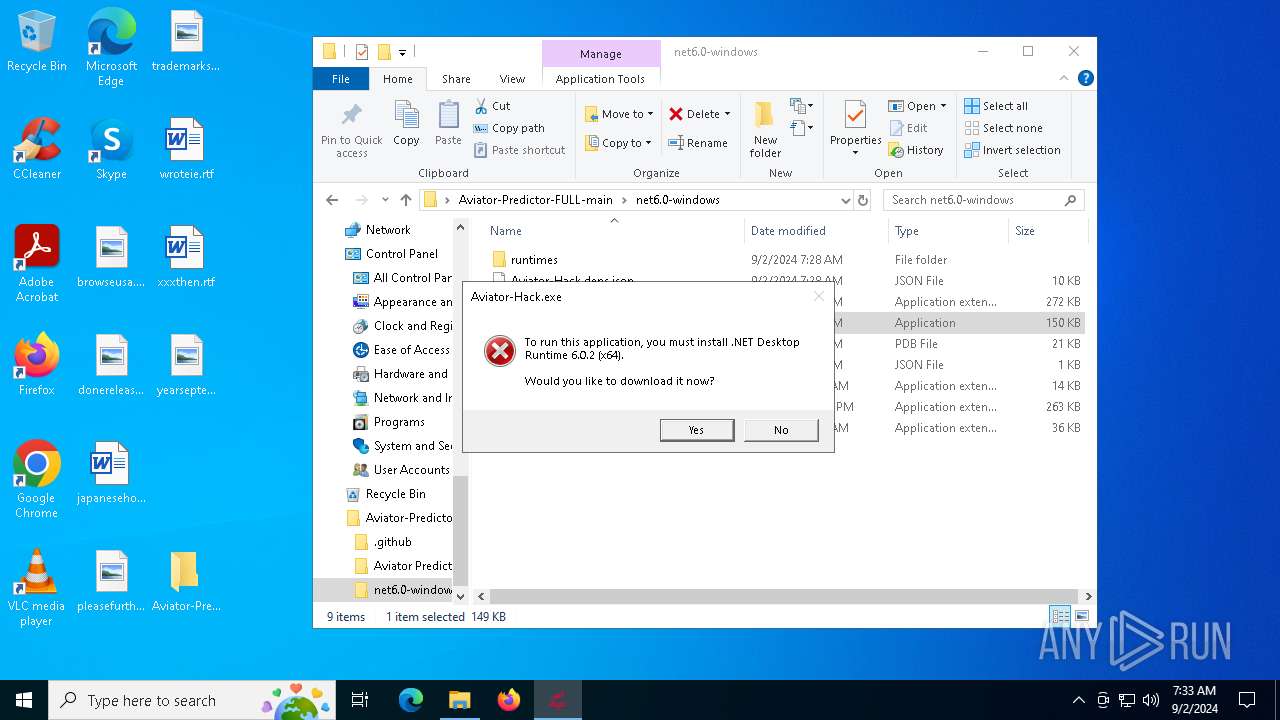
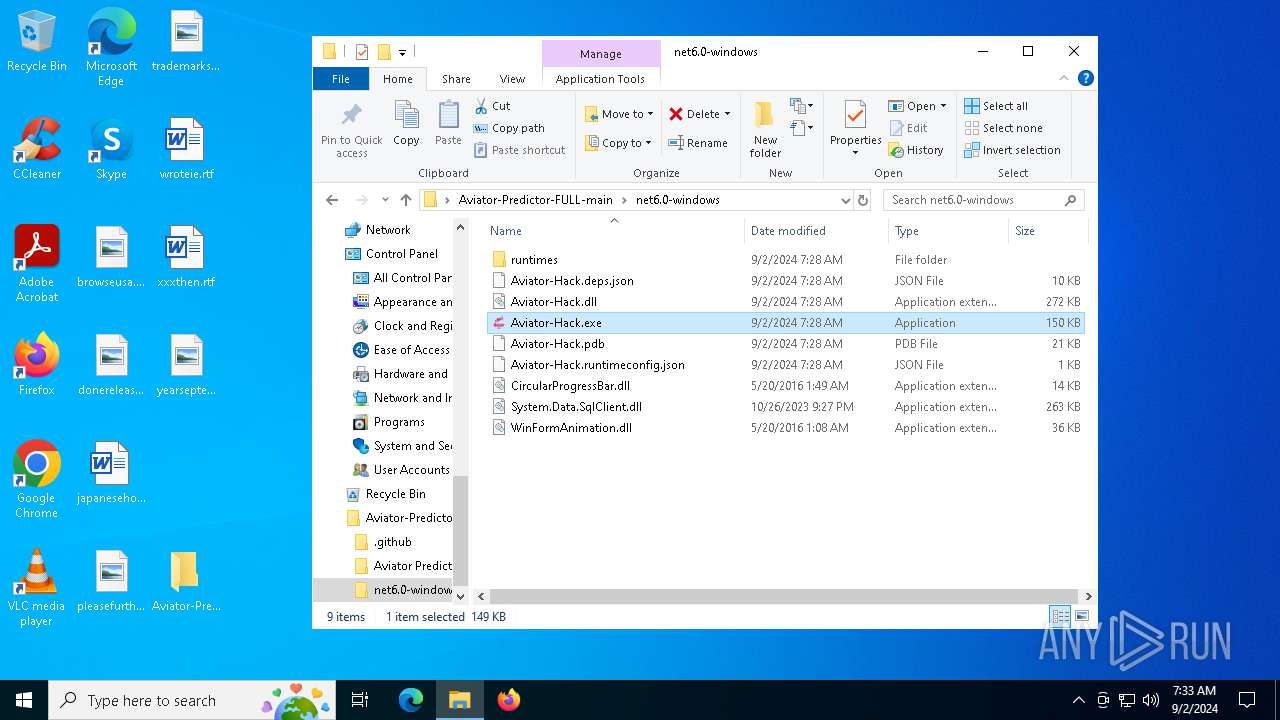
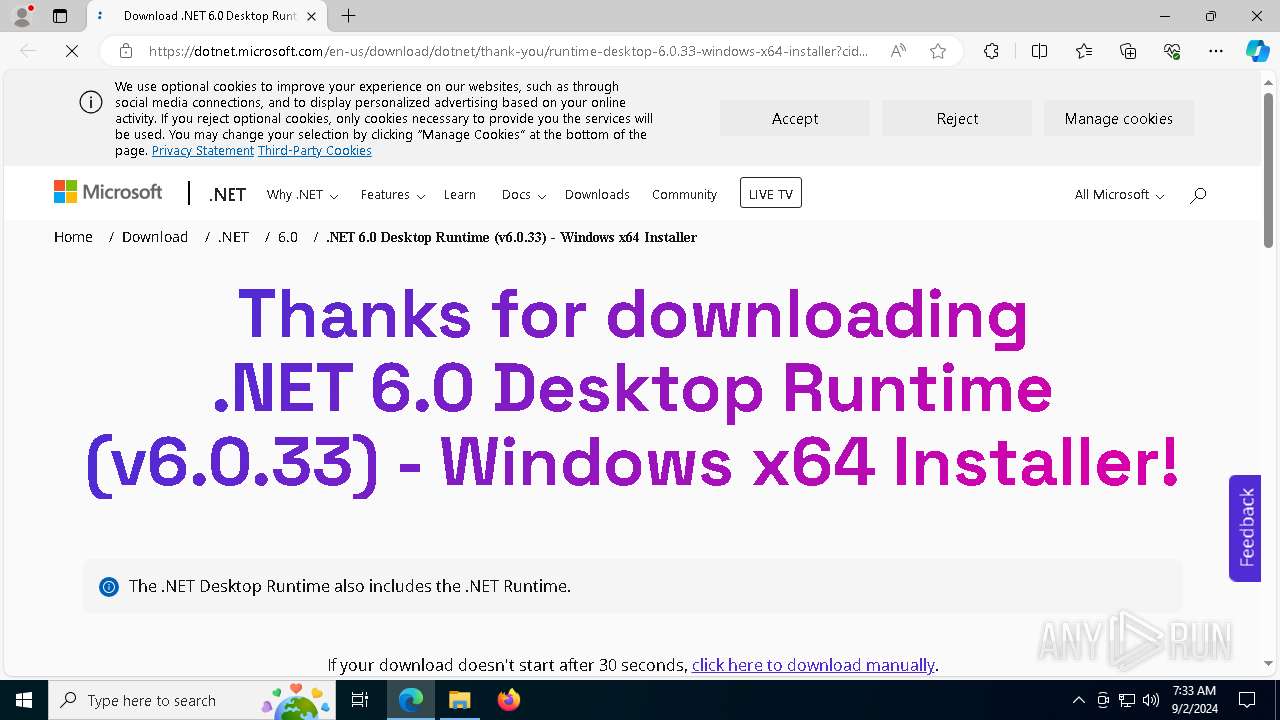
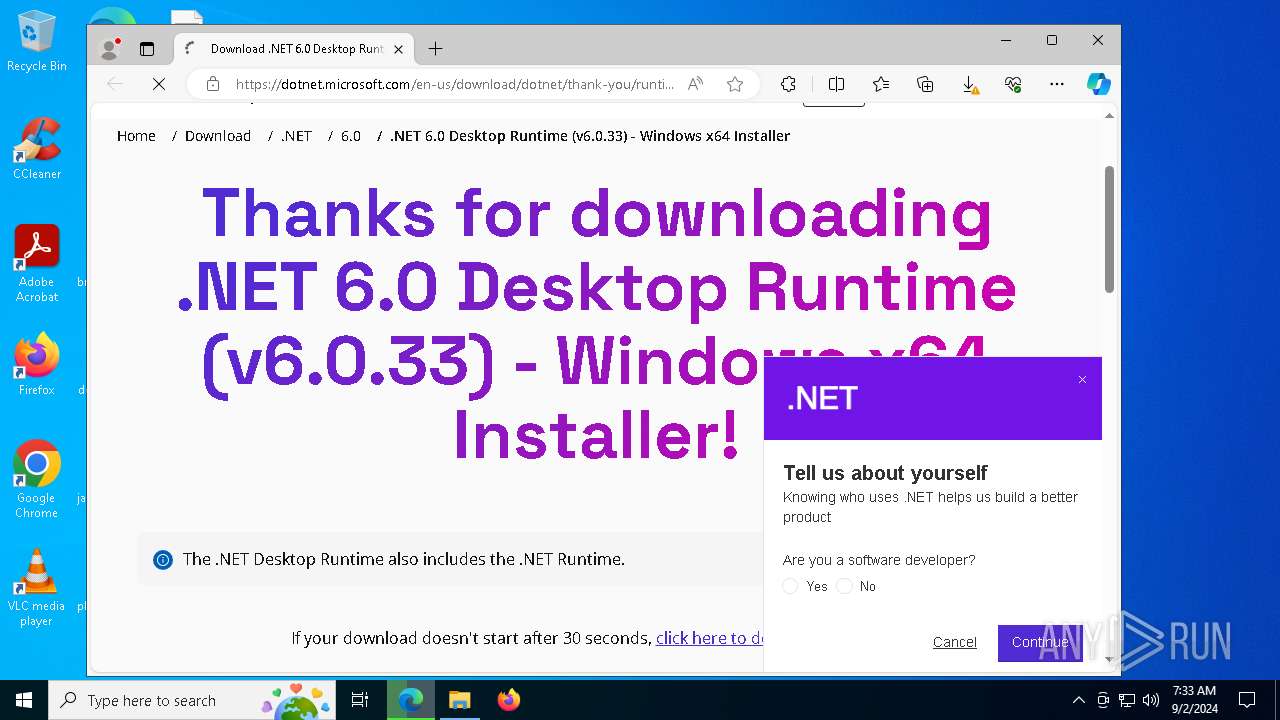
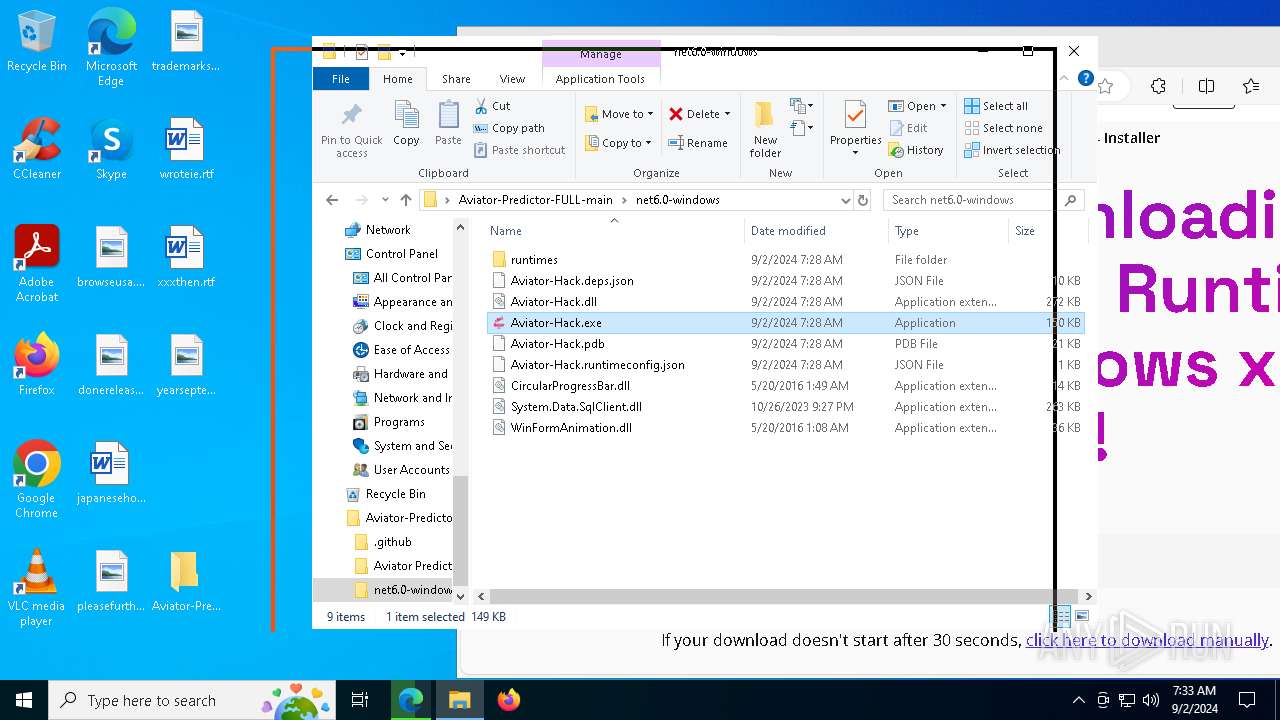
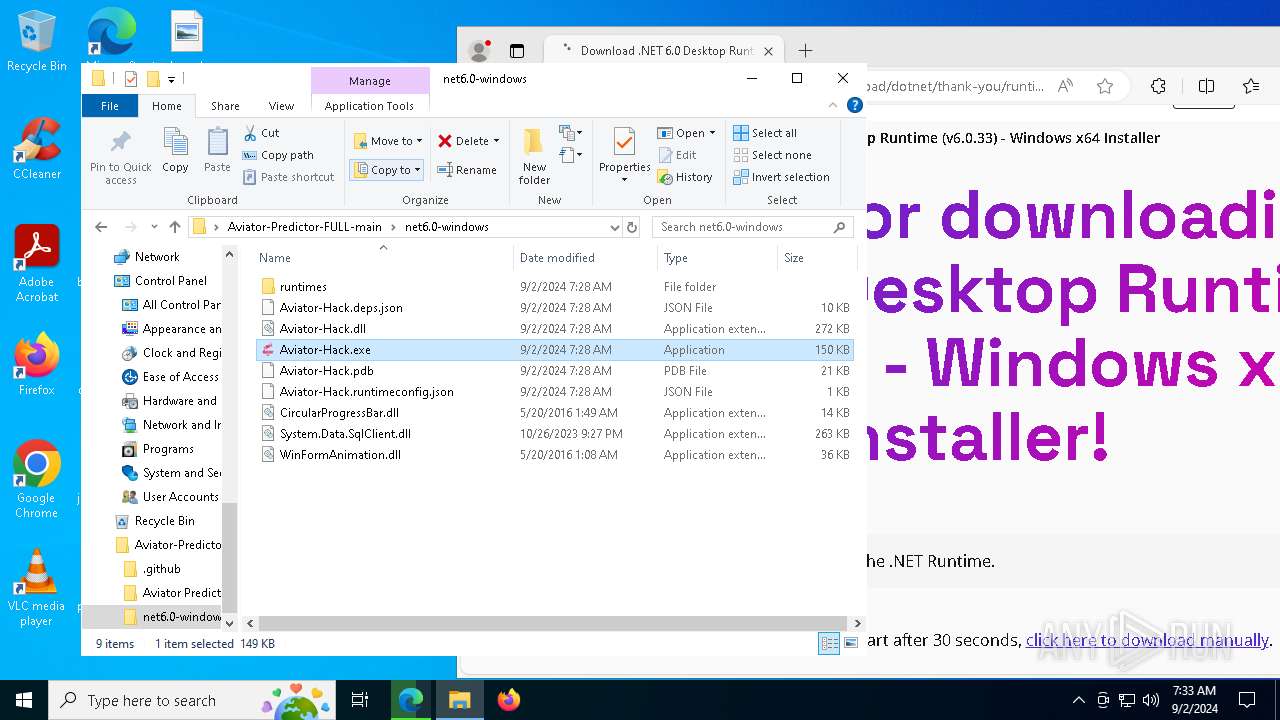
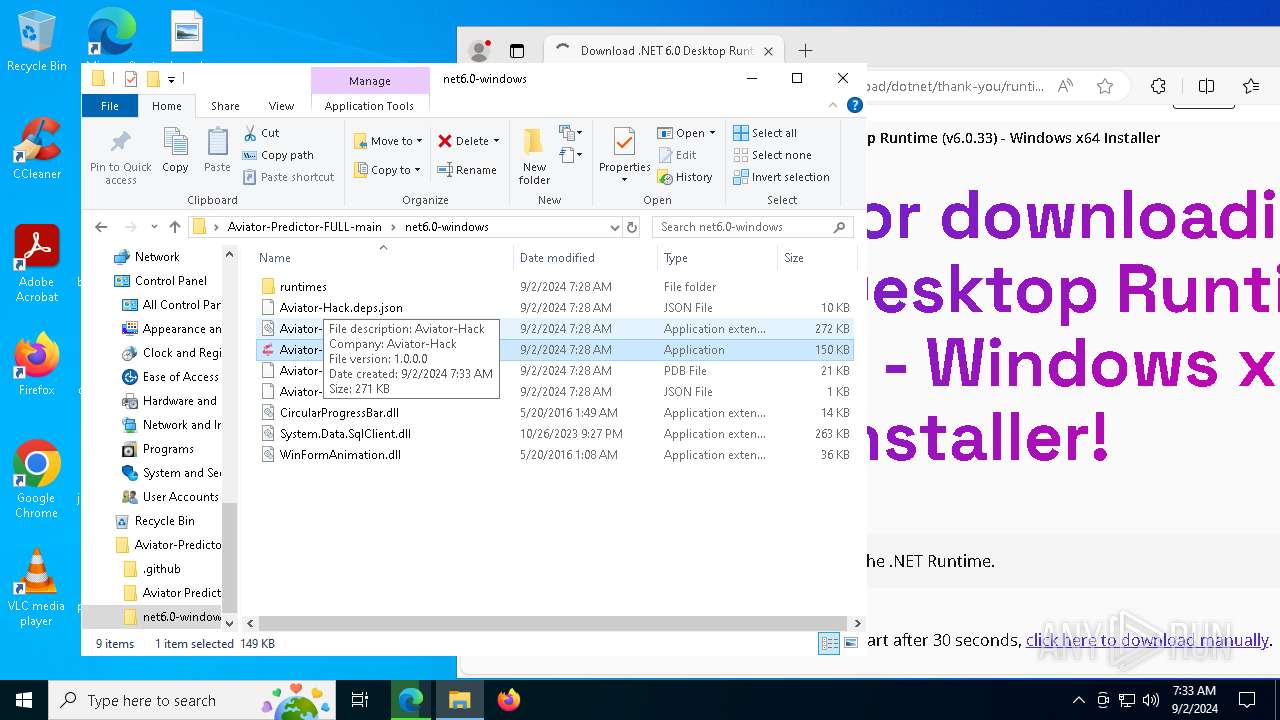
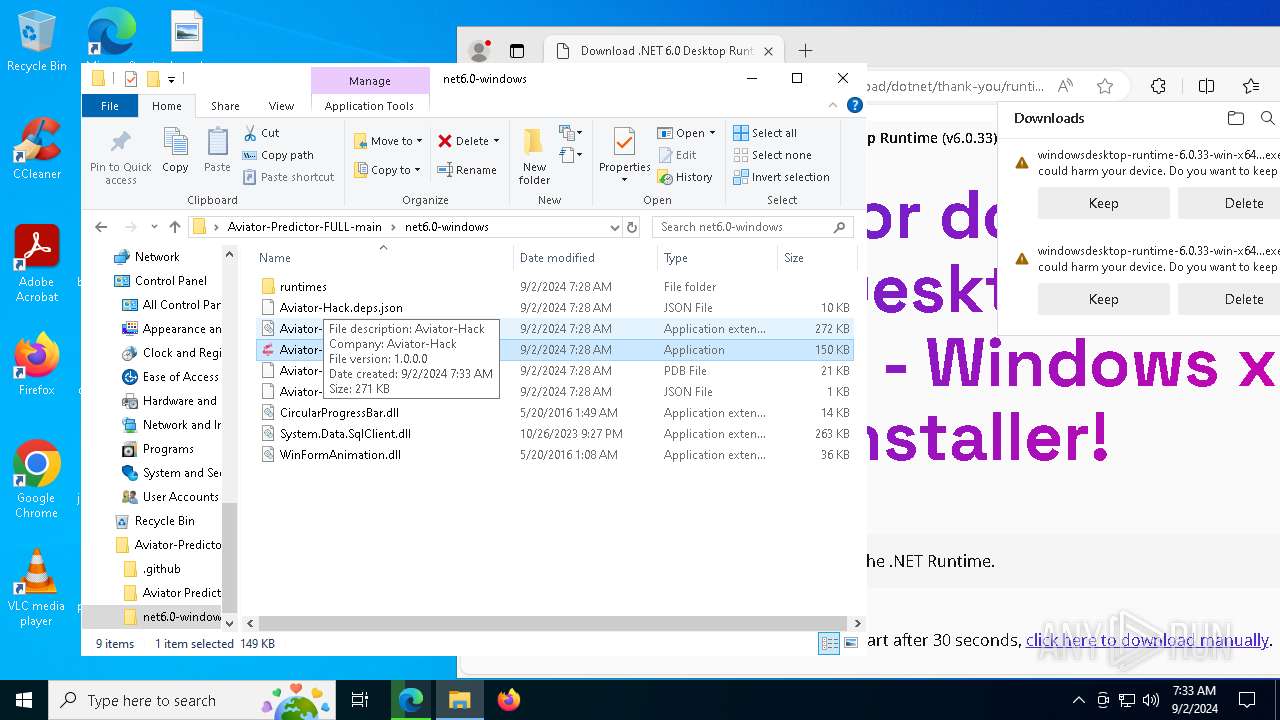
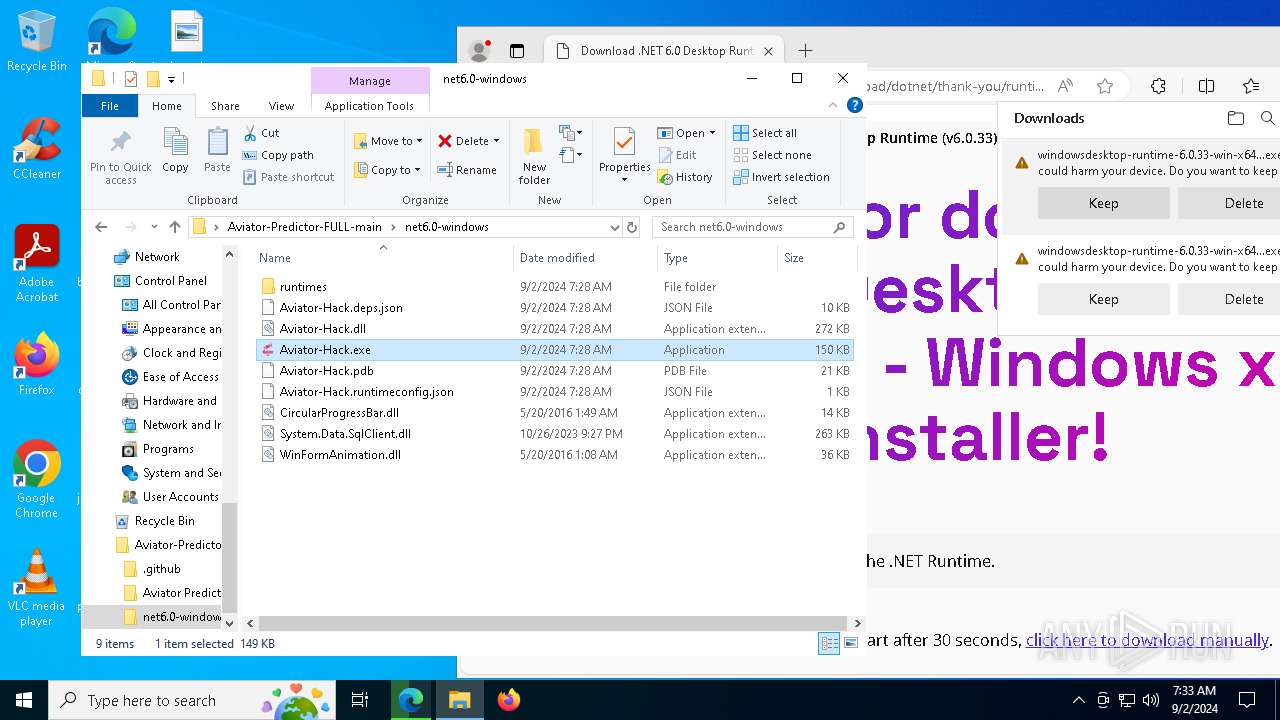
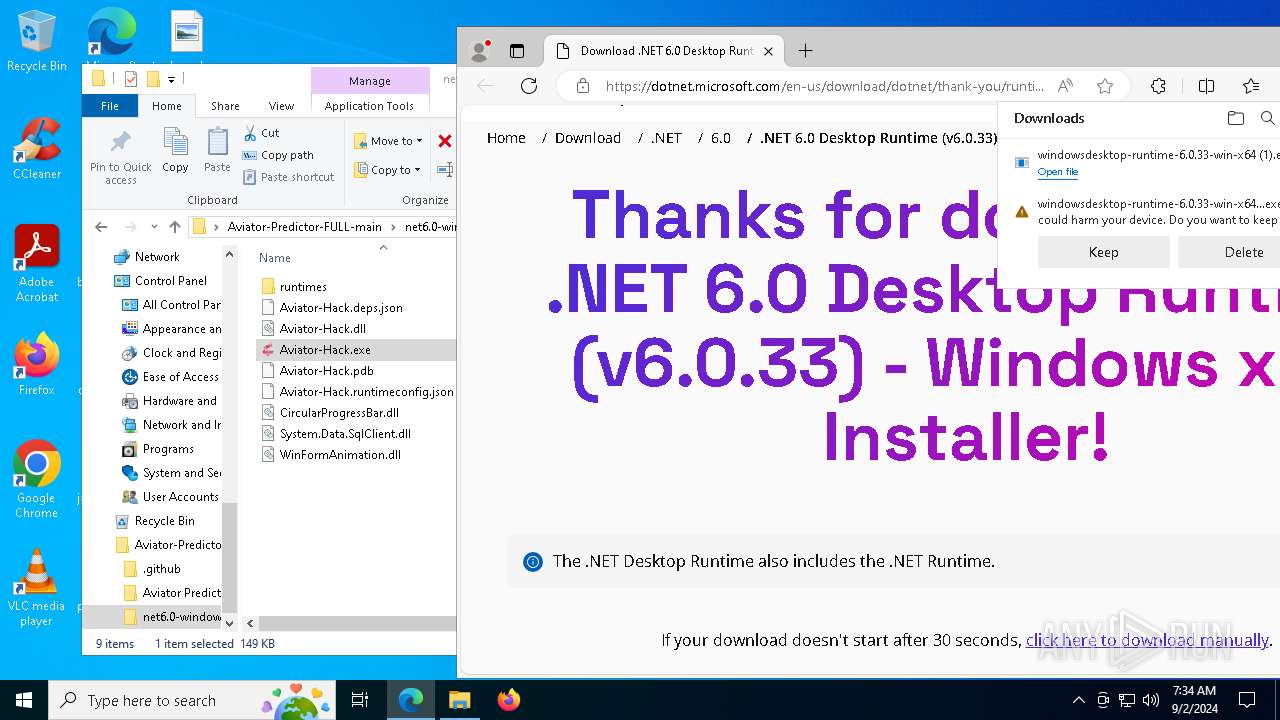
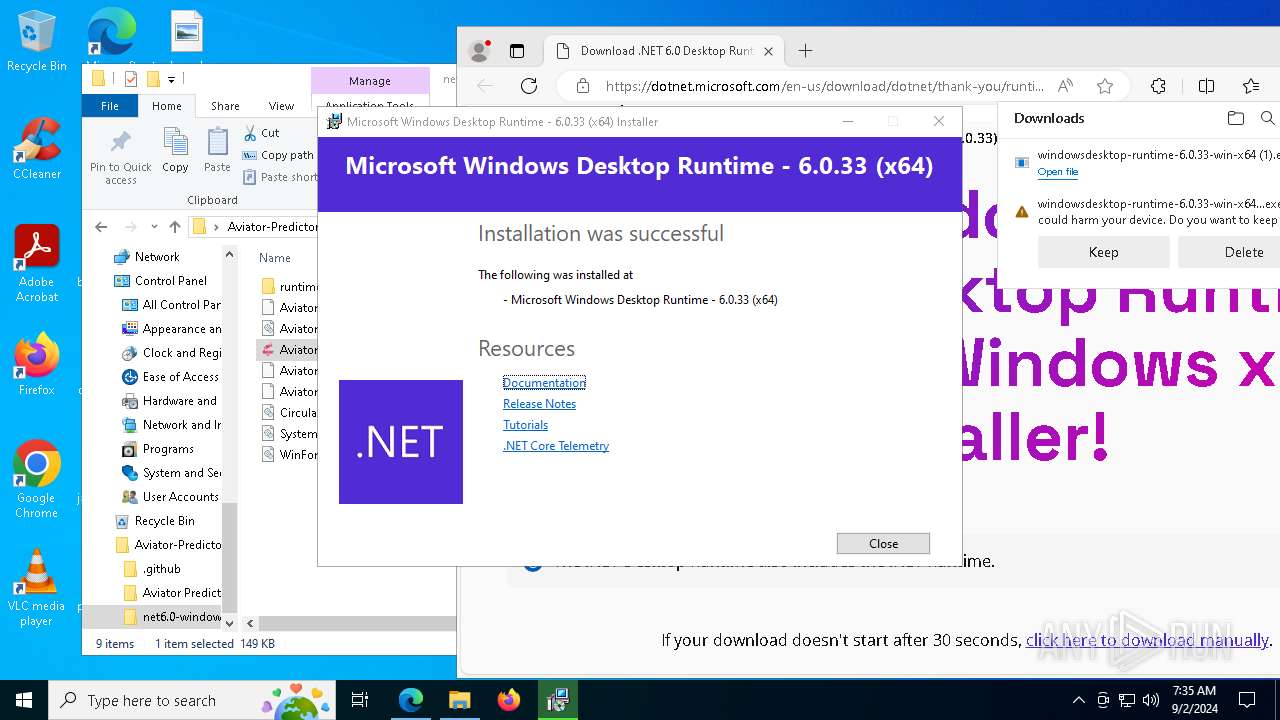
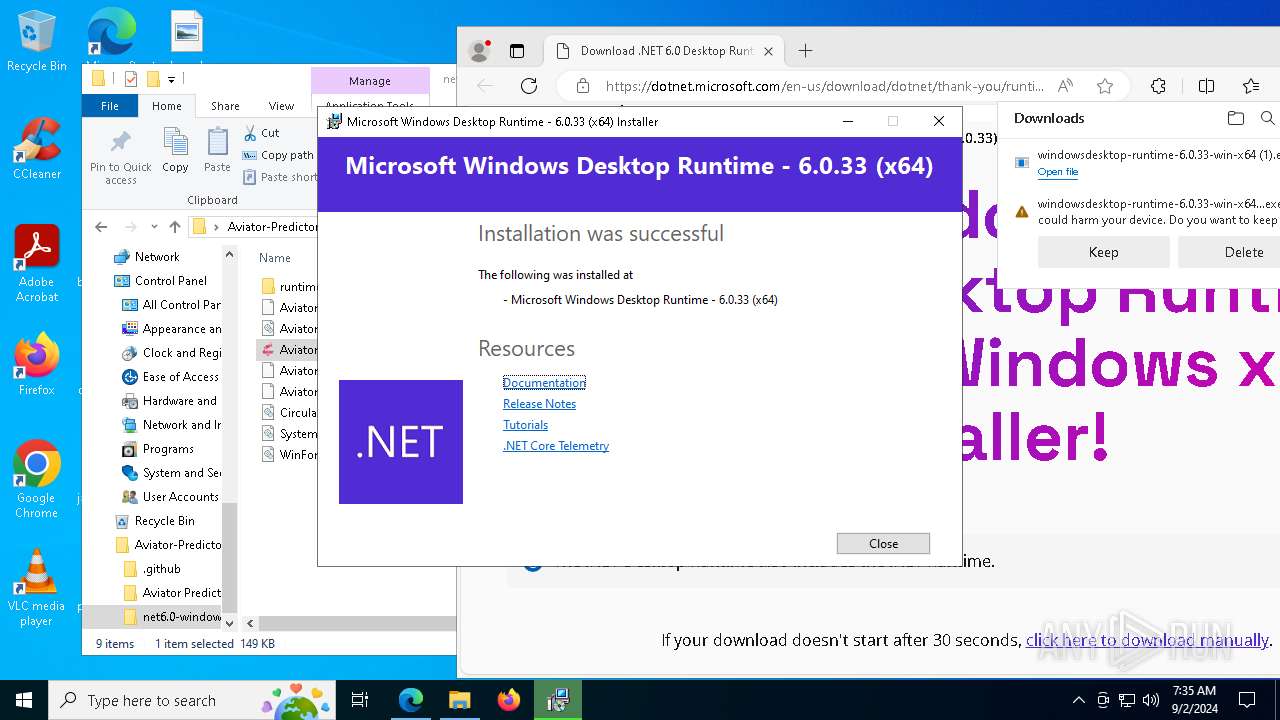
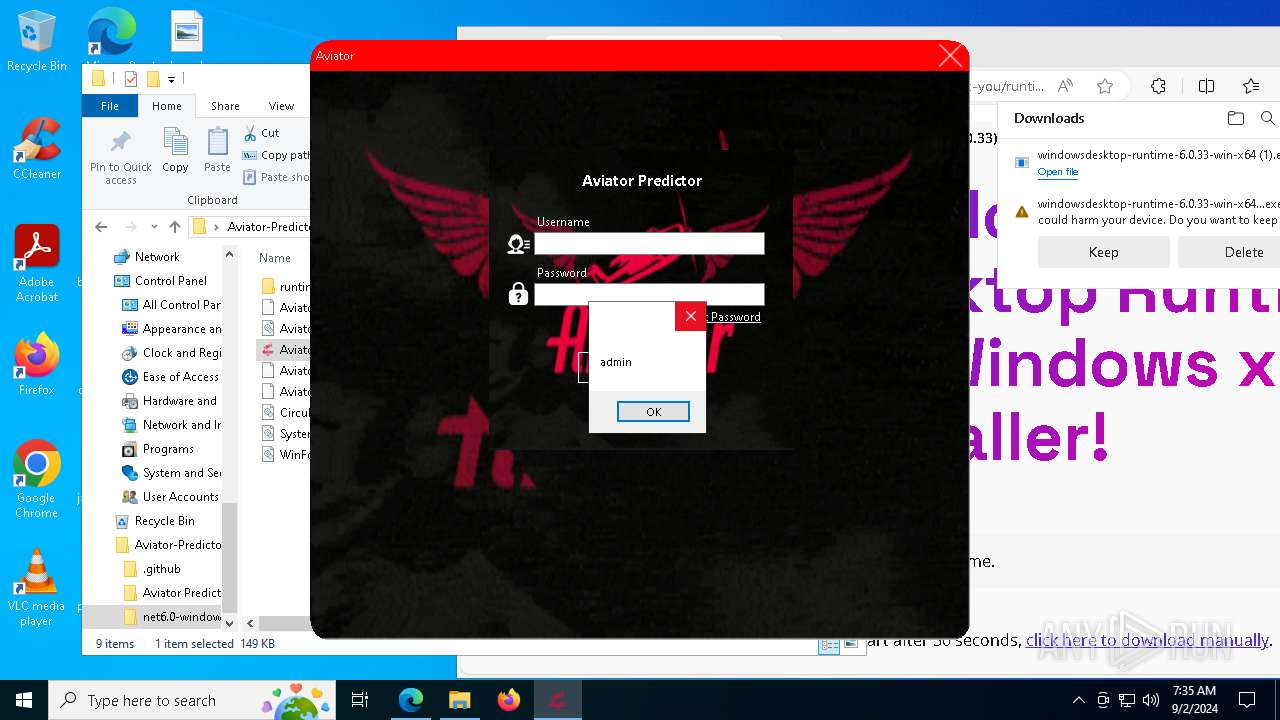
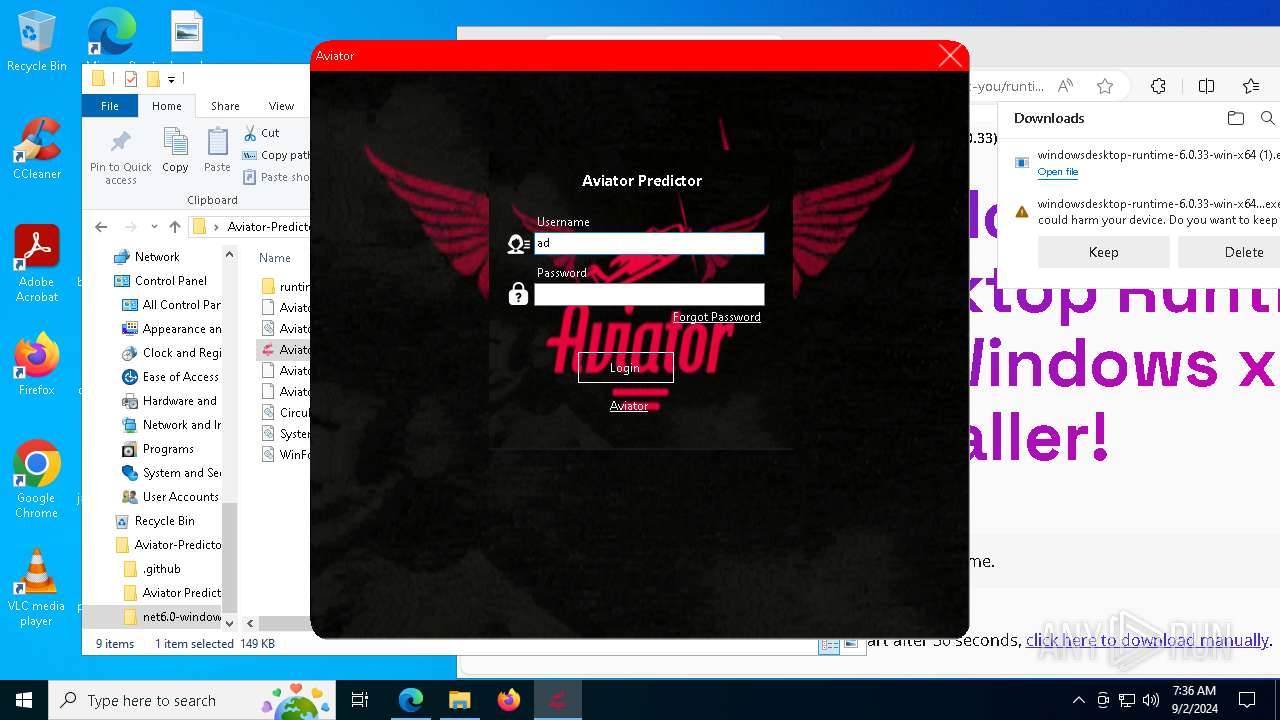
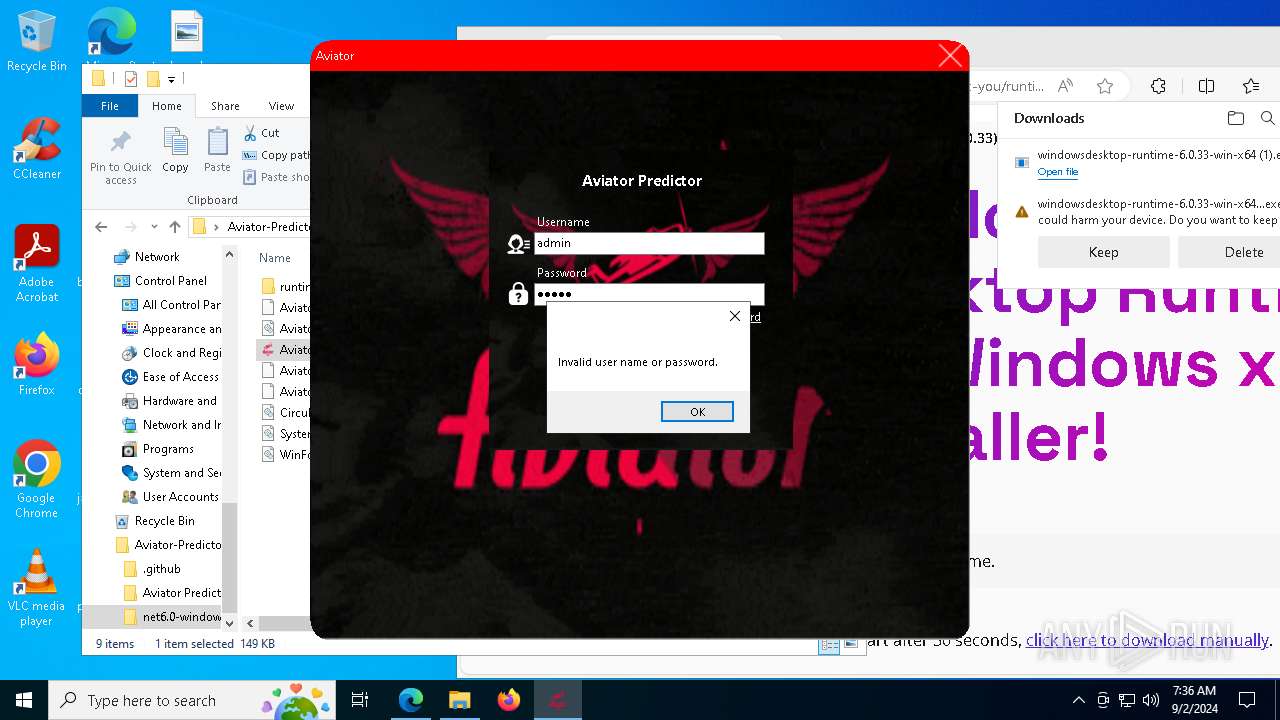
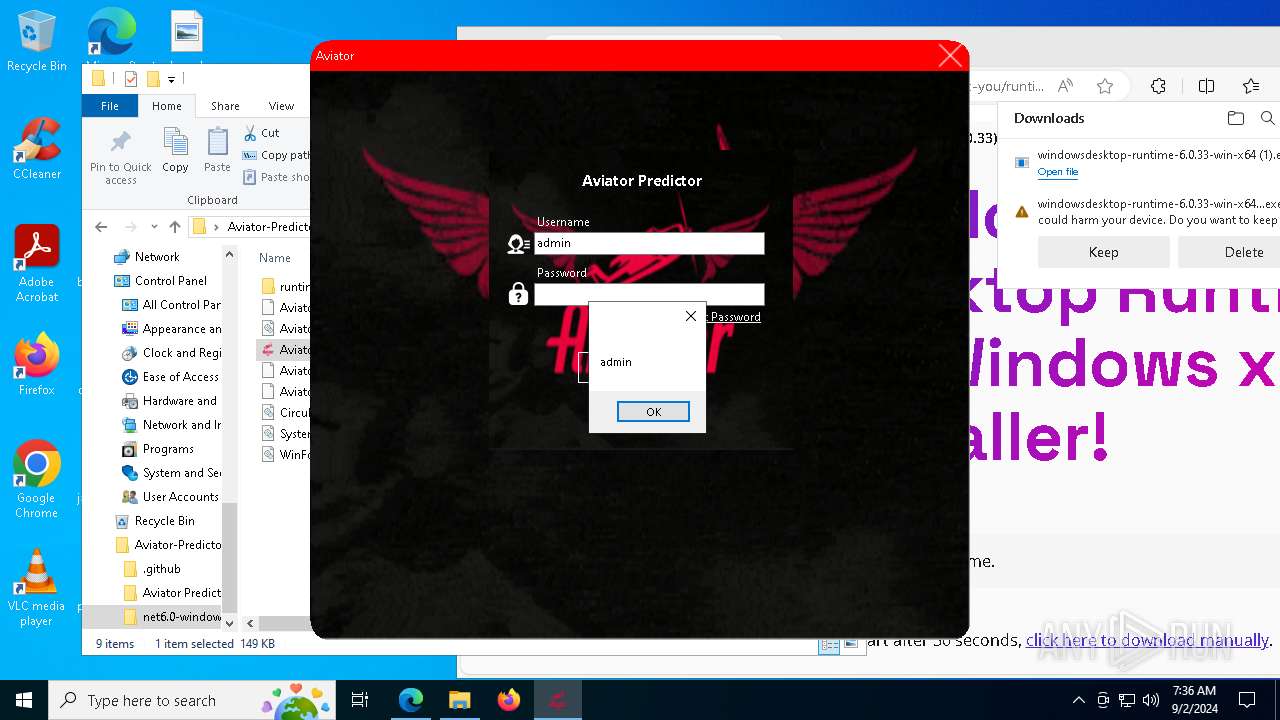
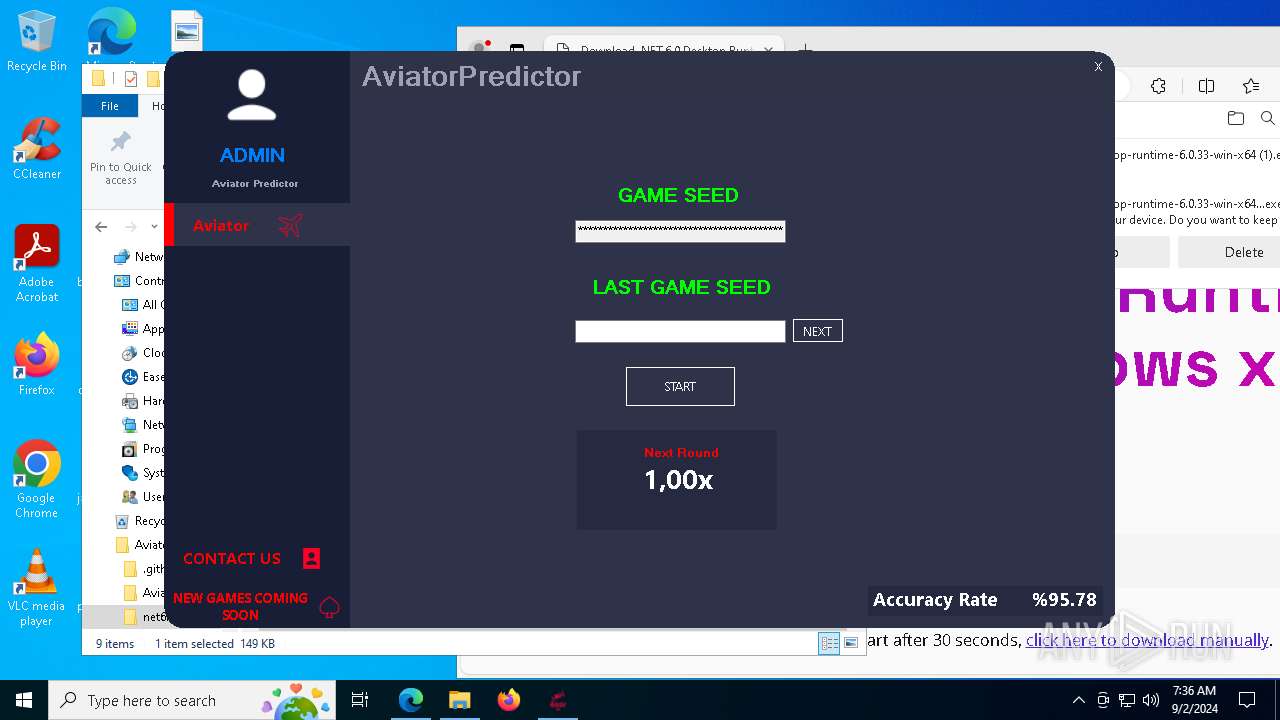
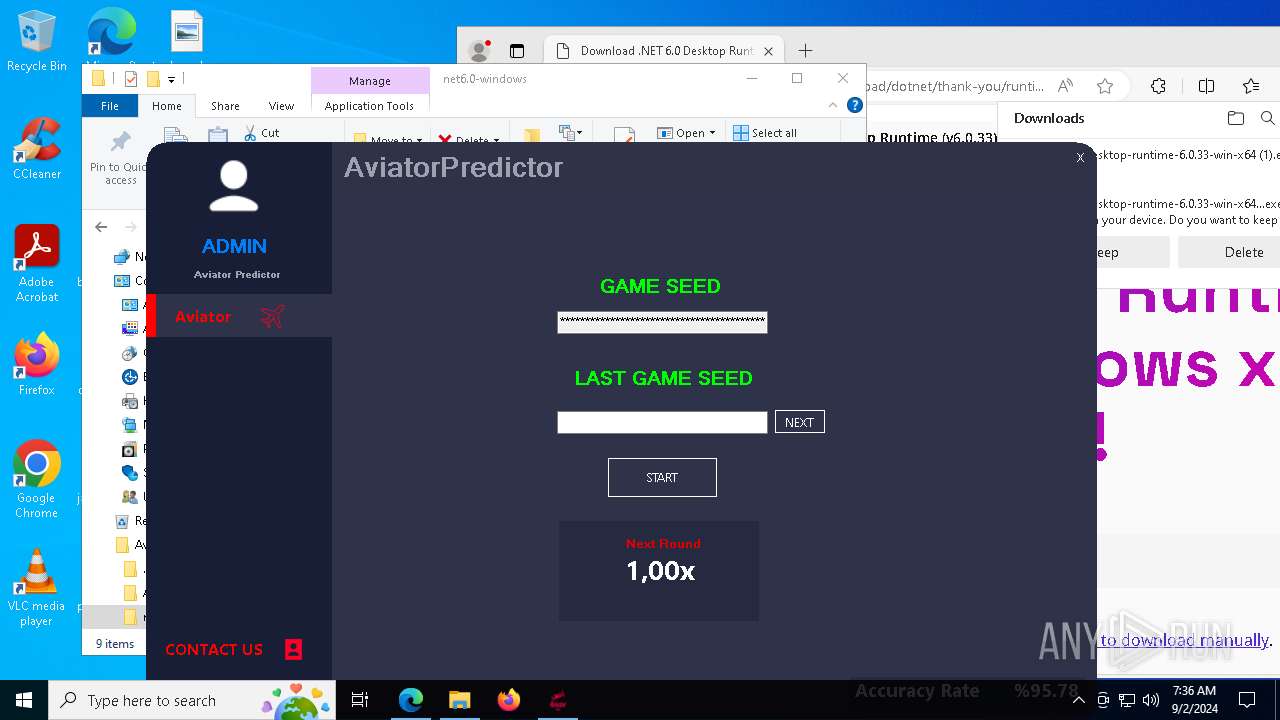
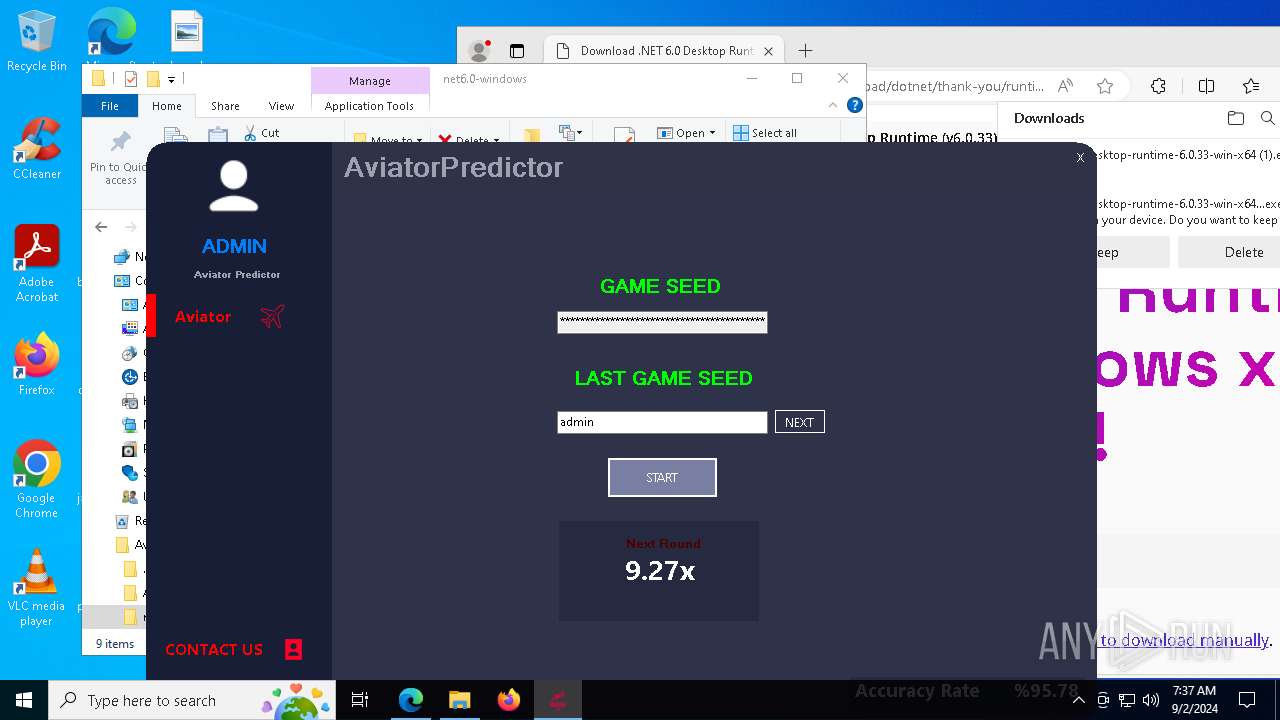
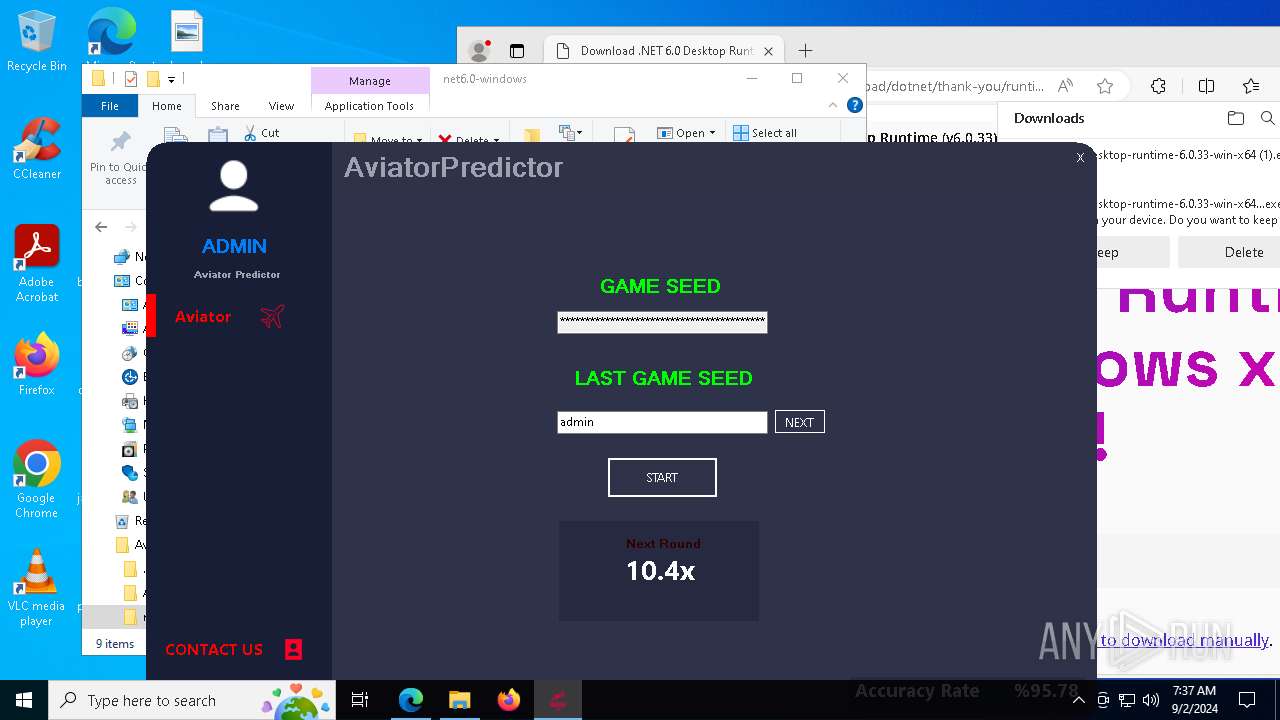
Aviator-Hack.exe | A fatal error occurred. The required library hostfxr.dll could not be found.
If this is a self-contained application, that library should exist in [C:\Users\admin\Desktop\Aviator-Predictor-FULL-main\net6.0-windows\].
If this is a framework-dependent application, install the runtime in the global location [C:\Program Files\dotnet] or use the DOTNET_ROOT environment variable to specify the runtime location or register the runtime location in [HKLM\SOFTWARE\dotnet\Setup\InstalledVersions\x64\InstallLocation]. |
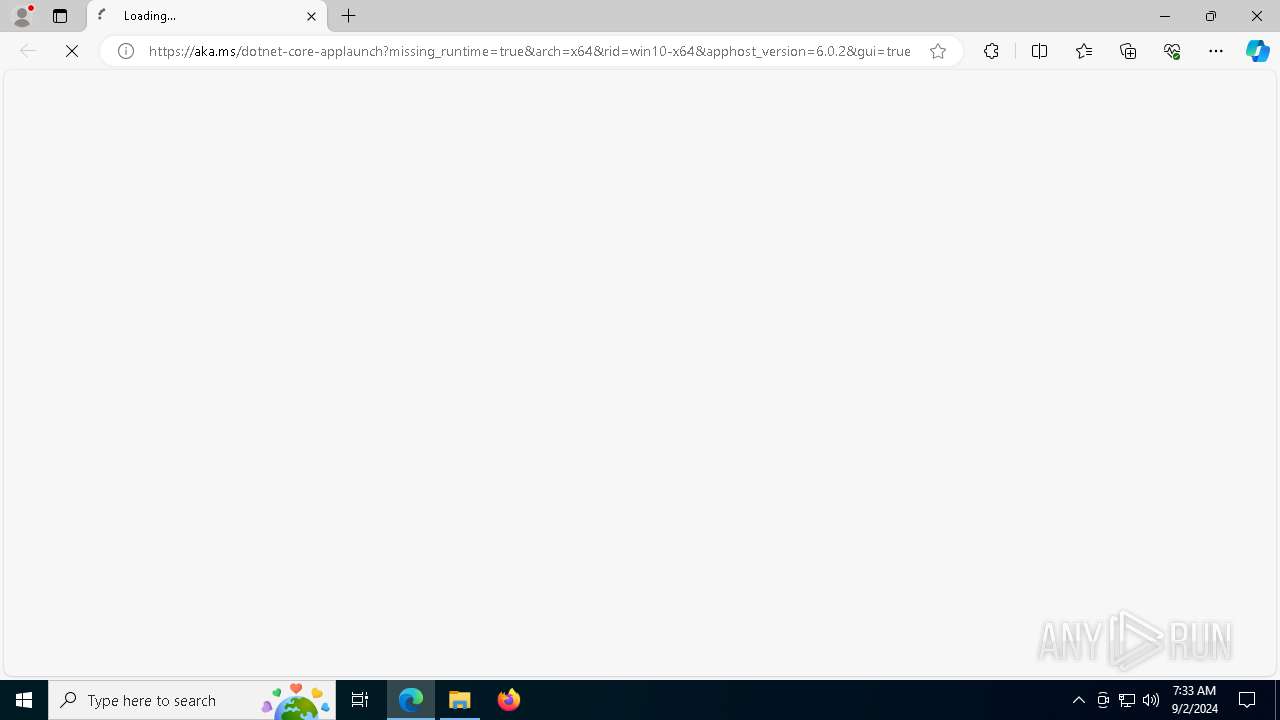
Aviator-Hack.exe | The .NET runtime can be found at: |
Aviator-Hack.exe | - https://aka.ms/dotnet-core-applaunch?missing_runtime=true&arch=x64&rid=win10-x64&apphost_version=6.0.2 |
Aviator-Hack.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 5712. Message ID: [0x2509].
|