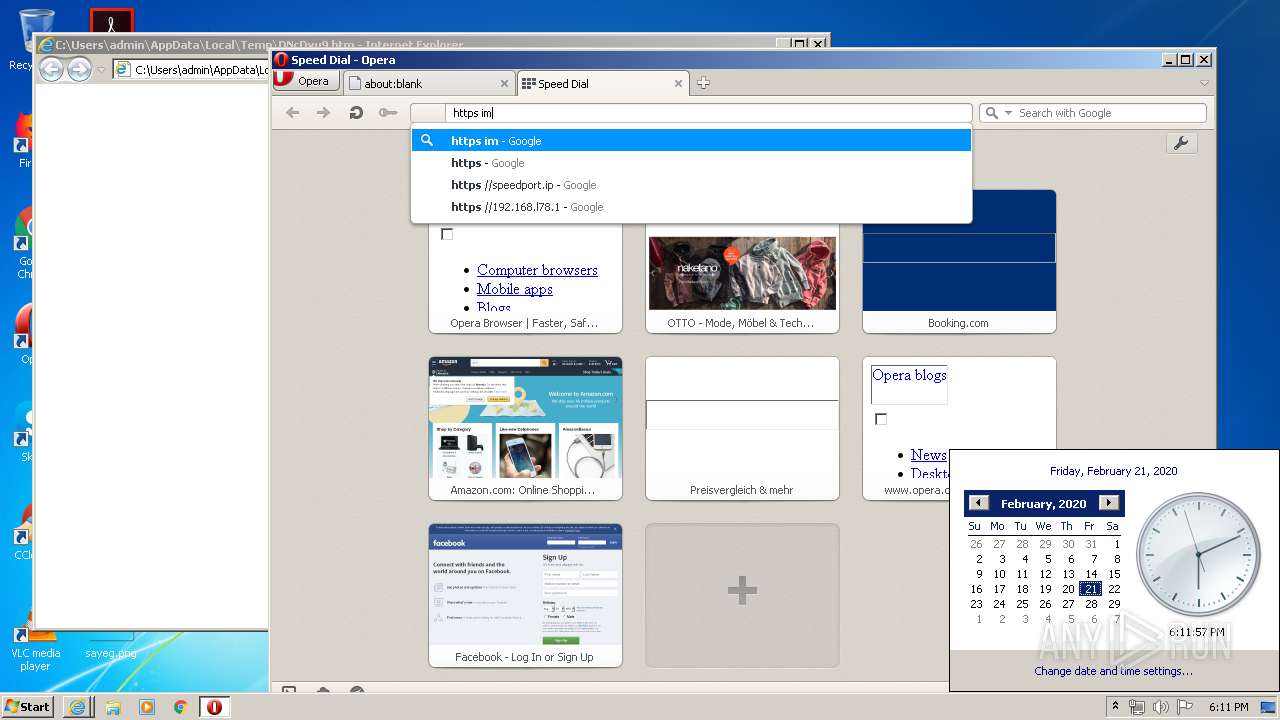
| download: | DNcDvu9 |
| Full analysis: | https://app.any.run/tasks/4eee2b8f-7bac-4861-9d4c-534cbc8a44b4 |
| Verdict: | Malicious activity |
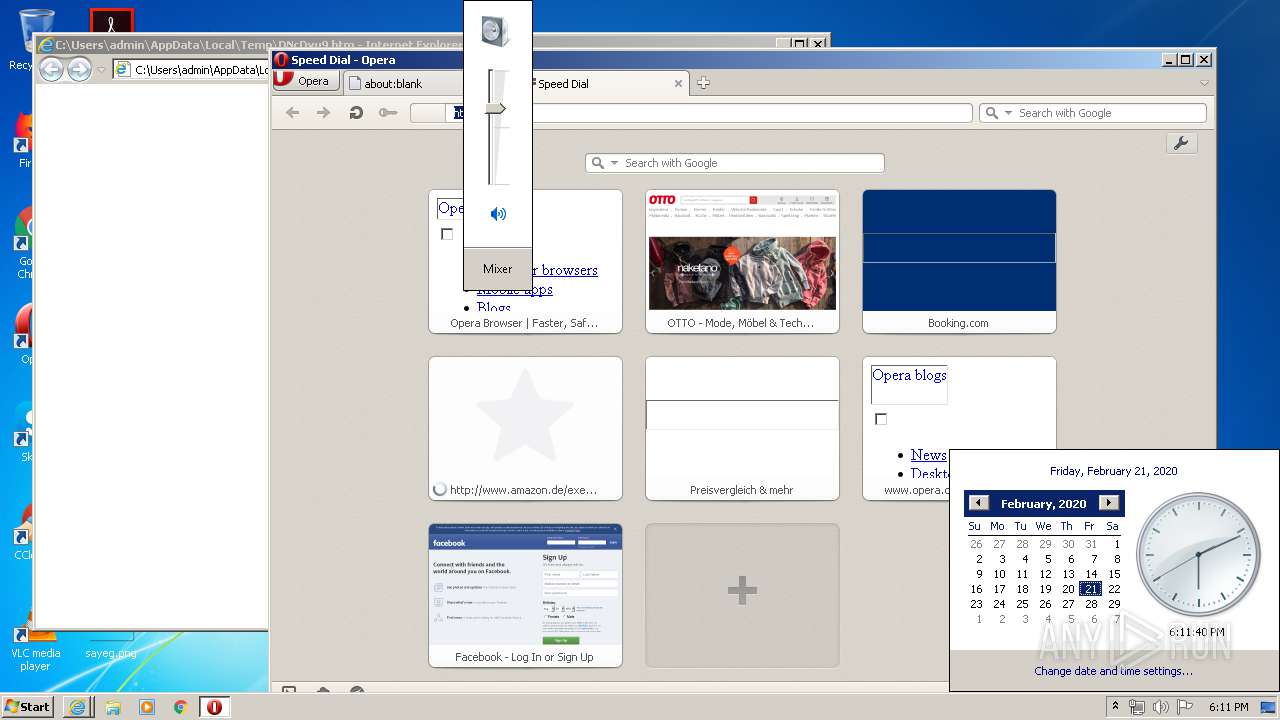
| Analysis date: | February 21, 2020, 18:10:28 |
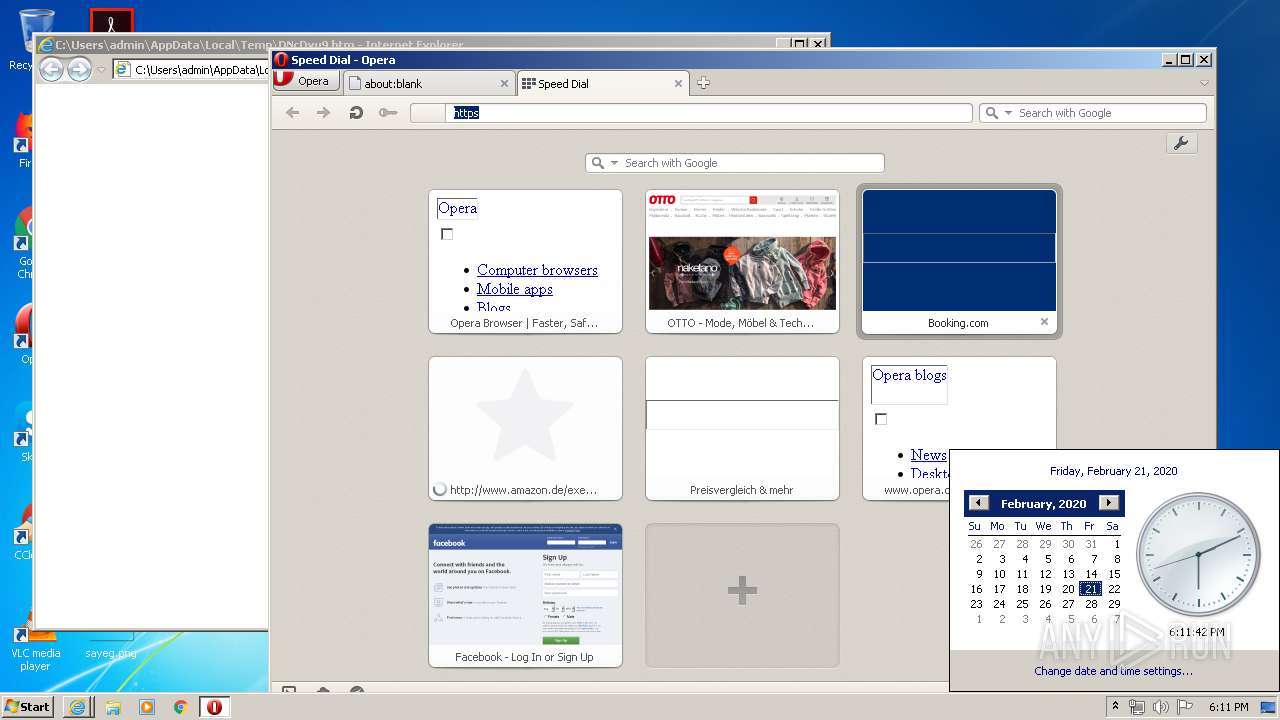
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 0F2D71AEE97B024AA25FCA55DFFBFFF0 |
| SHA1: | D5A47D1220C20DE2F71F8BF67F2C4C3BF93F462B |
| SHA256: | 05C260CA3FC50DD0A8C1B4170A6E5ACB14B9E0A088CC001541182858226CB8E5 |
| SSDEEP: | 768:YgSpcnx2YStzKrKCKUFnX23lgiEltTilUzkE/AsrxZcjtyF9o:YgSqnx2YStzuZtdX28TVzkEEjto9o |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 3388)
Application launched itself
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 3560)
Reads internet explorer settings
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2344)
Changes internet zones settings
- iexplore.exe (PID: 3448)
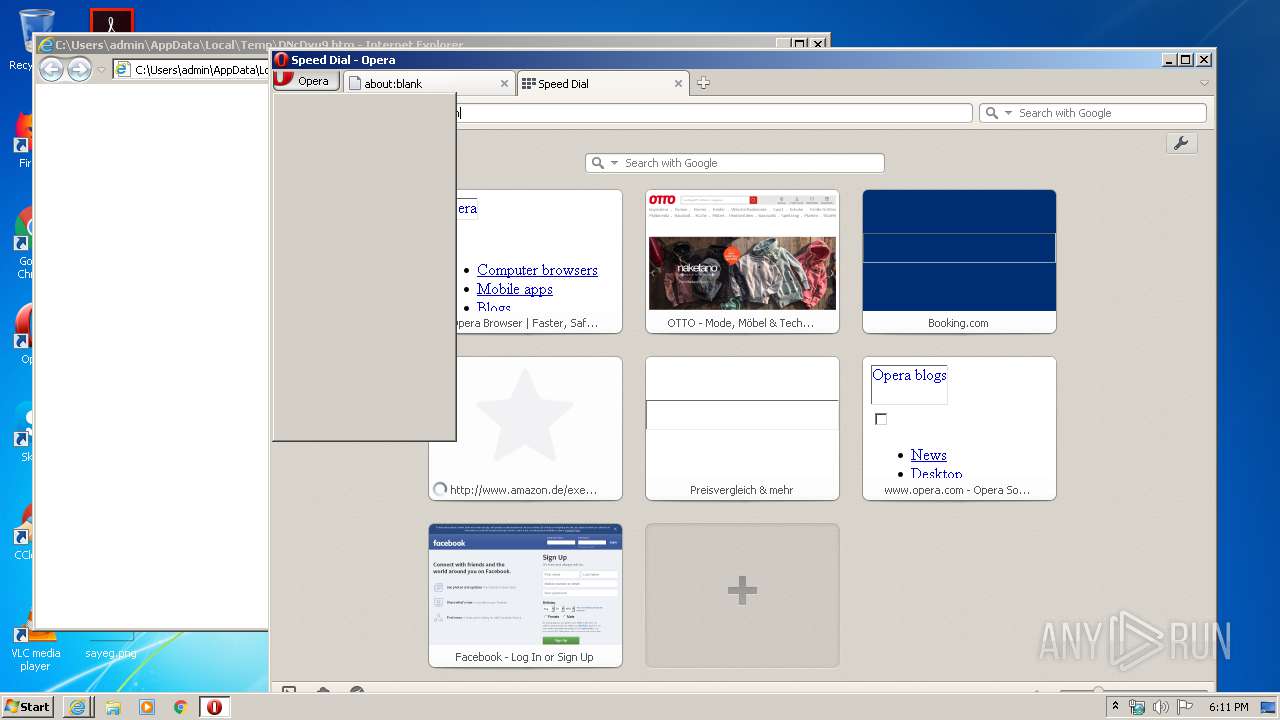
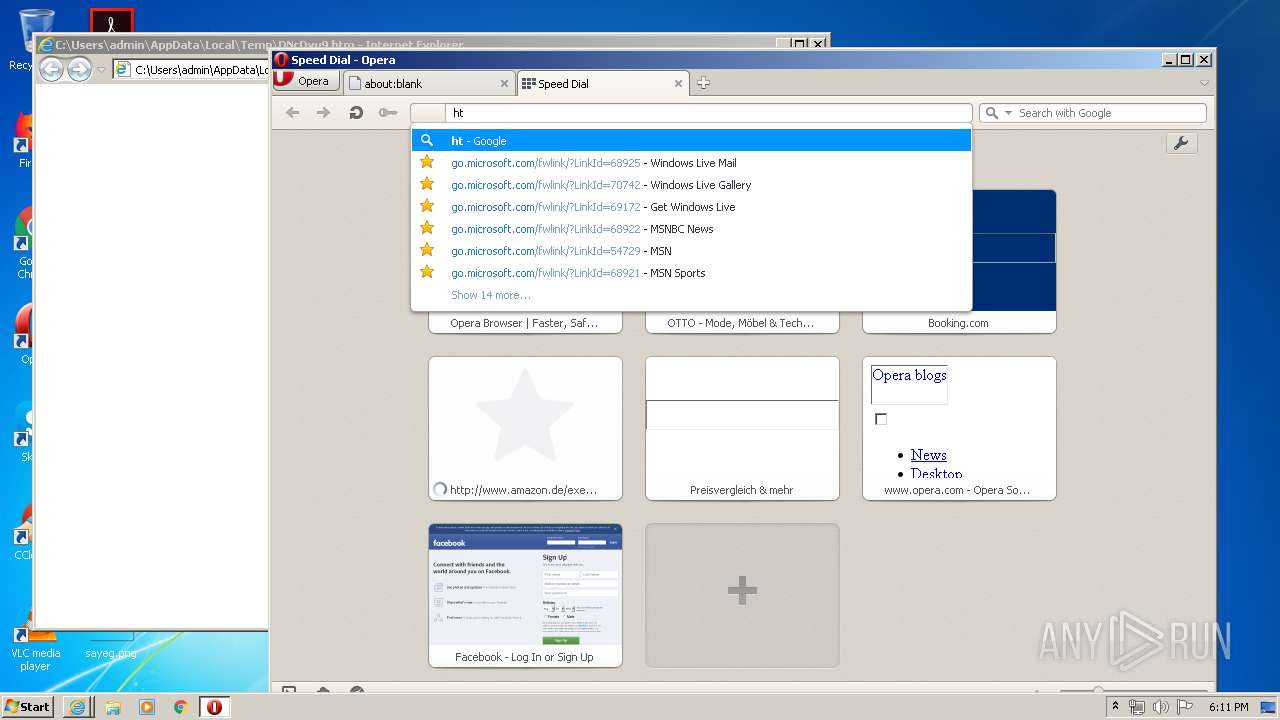
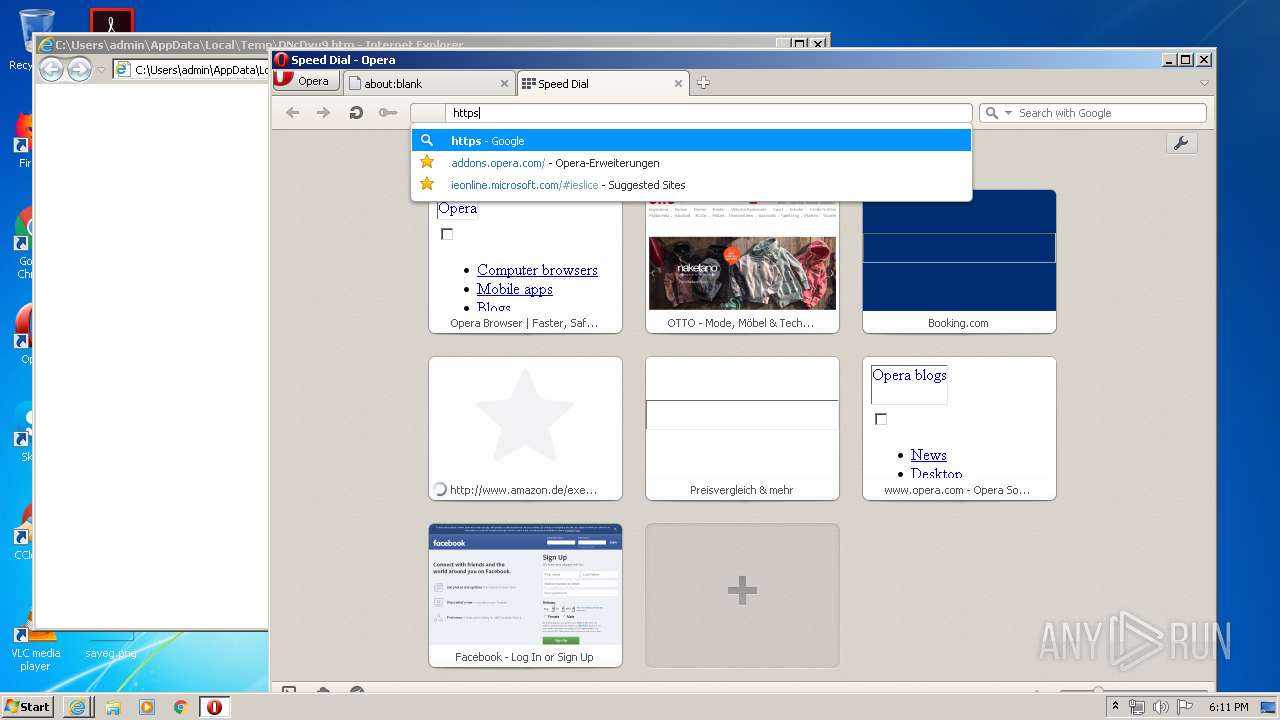
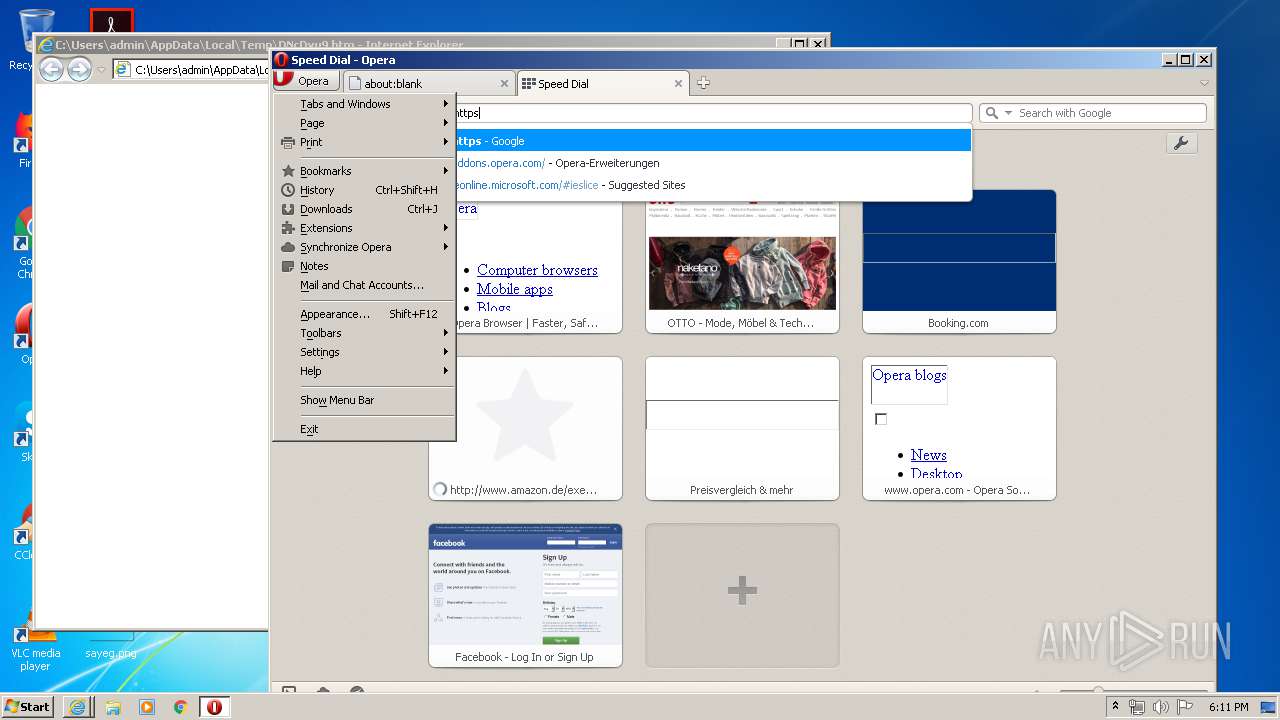
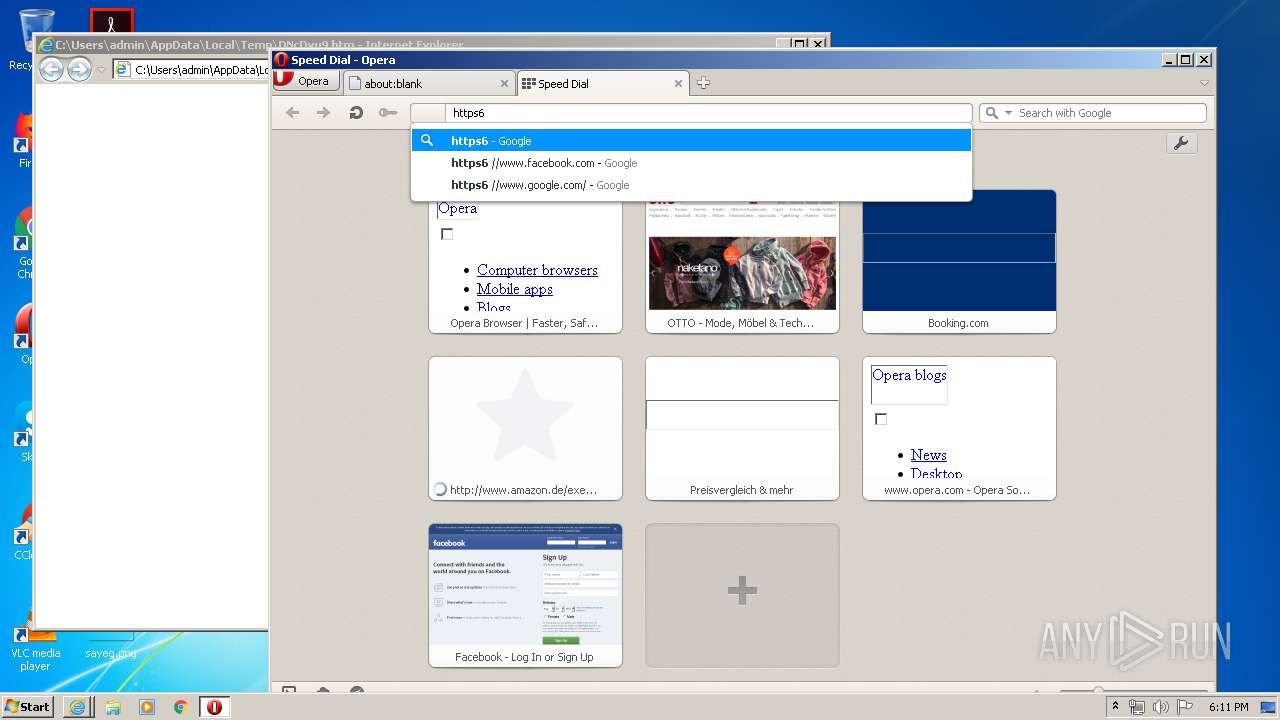
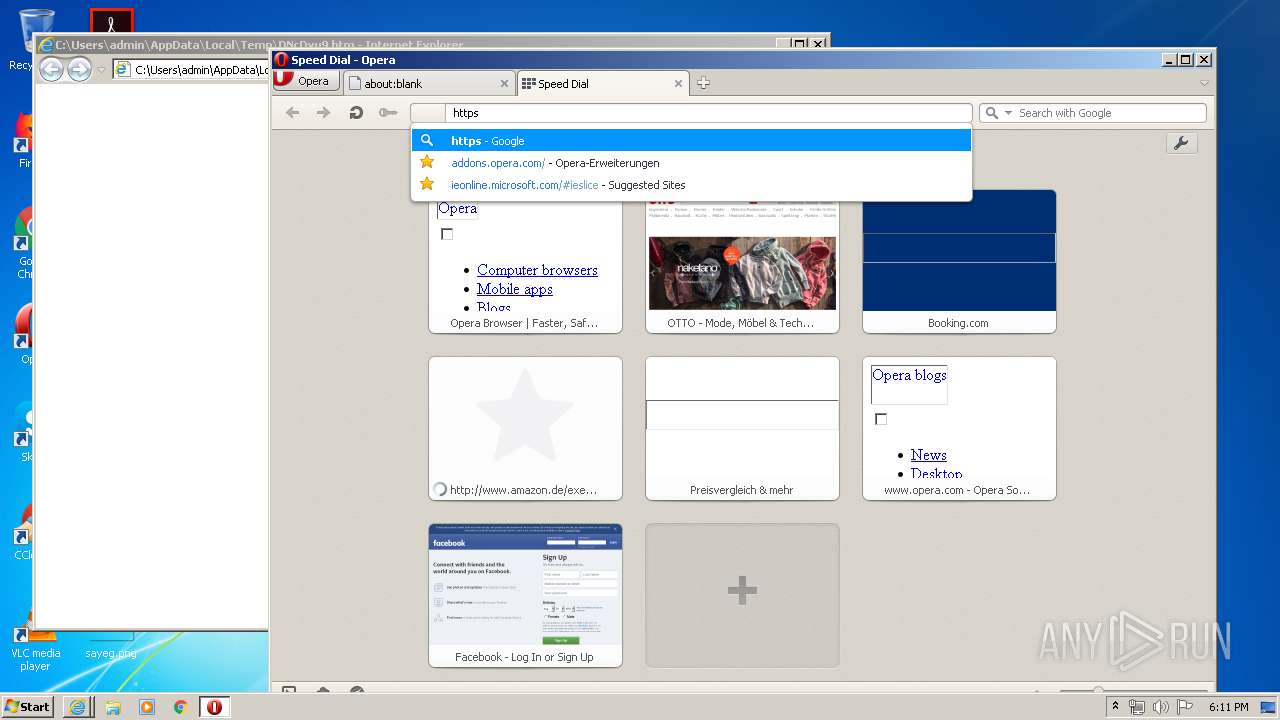
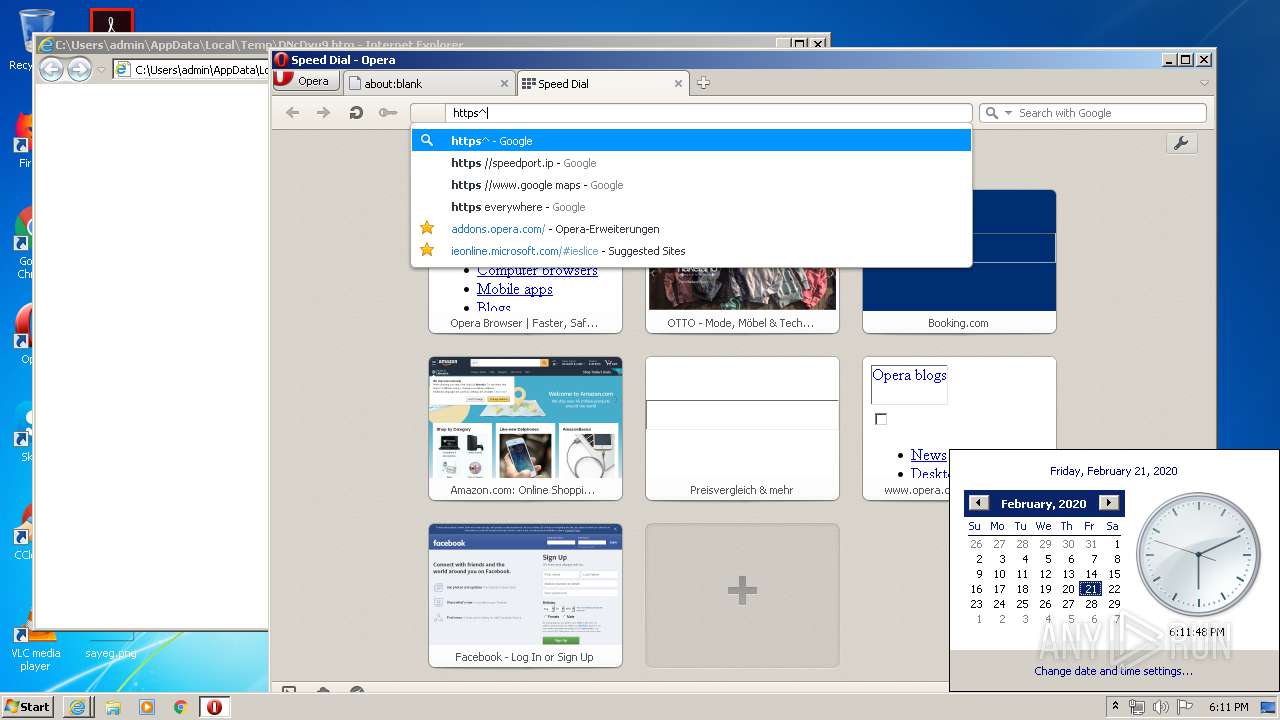
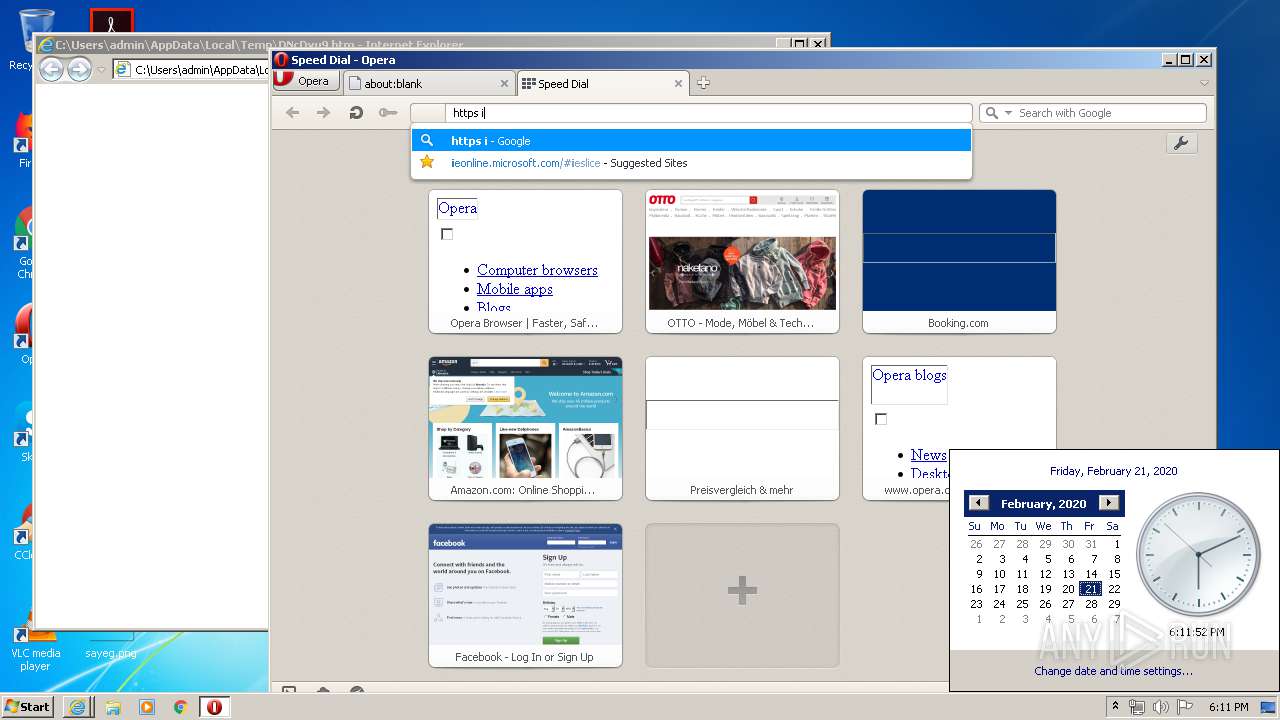
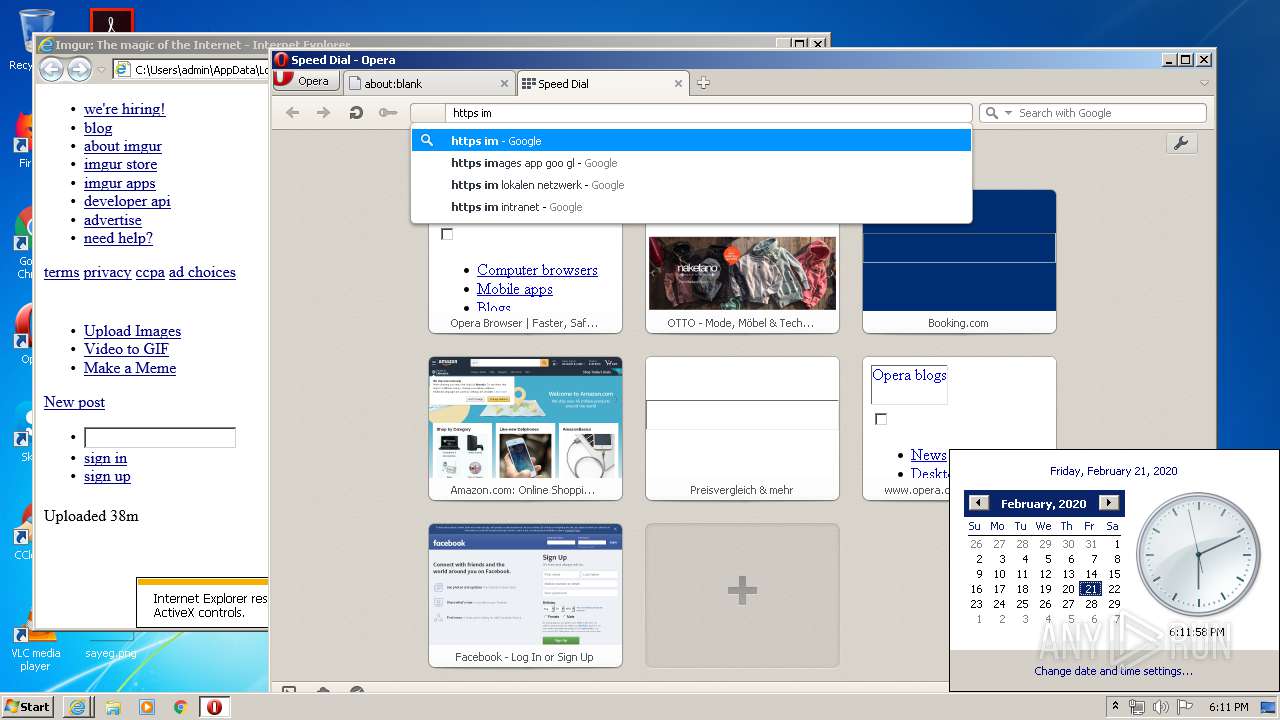
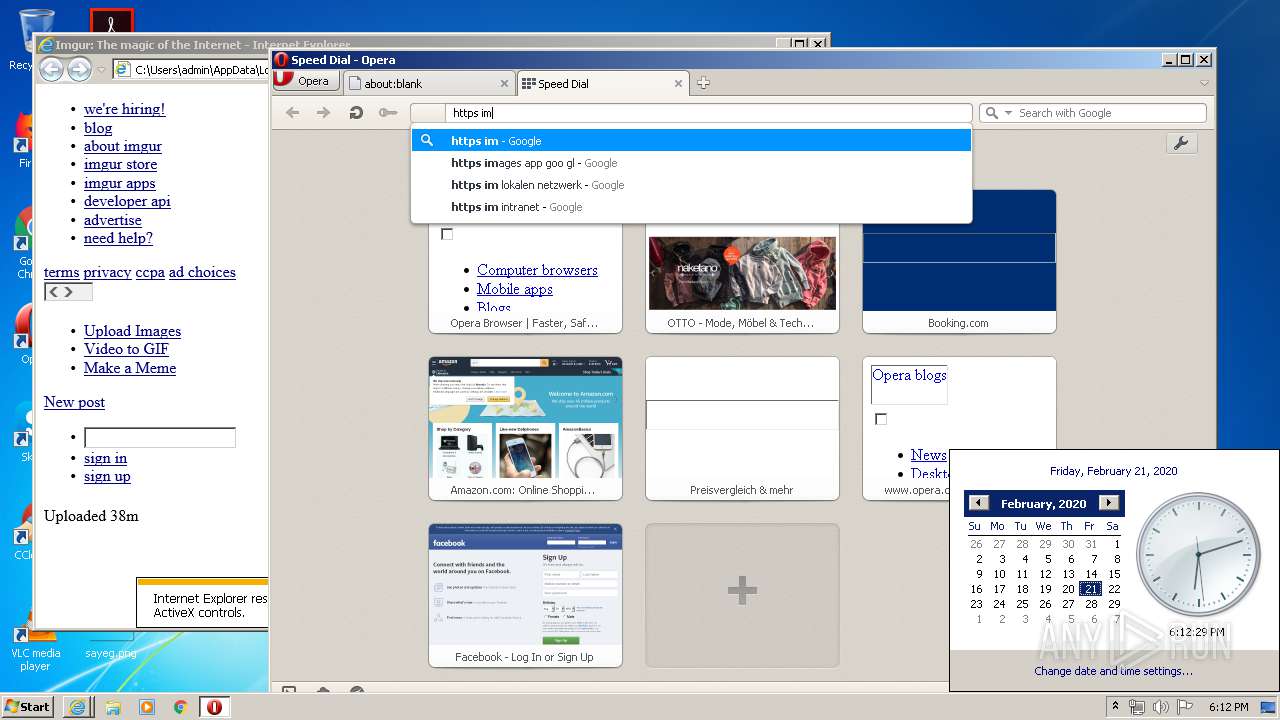
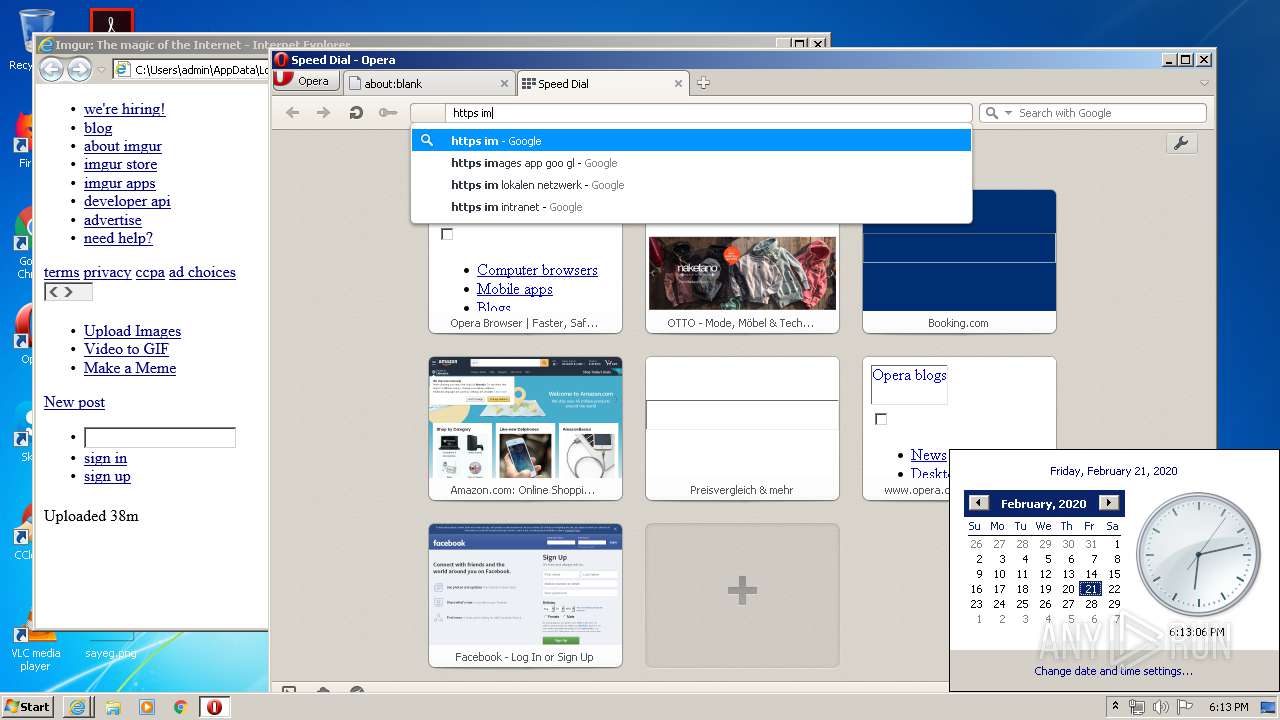
Manual execution by user
- opera.exe (PID: 3308)
- SndVol.exe (PID: 2448)
Creates files in the user directory
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2344)
- opera.exe (PID: 3308)
- iexplore.exe (PID: 3448)
Reads settings of System Certificates
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2344)
Changes settings of System certificates
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2344)
- iexplore.exe (PID: 3448)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2344)
- iexplore.exe (PID: 3448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| Title: | Imgur: The magic of the Internet |
|---|---|
| ContentType: | text/html;charset=utf-8 |
| viewport: | width=1138 |
| Robots: | noindex, follow |
| Keywords: | images, photos, gif, gifs, memes, pictures, new pictures, reaction gifs, share photos, share images, latest images, funny, cute, visual storytelling, imgur |
| Description: | Post with 5 views. |
| Copyright: | Copyright 2020 Imgur, Inc. |
| HTTPEquivXUACompatible: | IE=Edge; |
| msapplicationTileColor: | #2cd63c |
| msapplicationTileImage: | //s.imgur.com/images/favicon-144.png |
| pDomain_verify: | 834554521765408b9effdc758b69c5ee |
| twitterSite: | @imgur |
| twitterDomain: | imgur.com |
| twitterAppIdGoogleplay: | com.imgur.mobile |
| twitterTitle: | Imgur |
| monetization: | $ilp.gatehub.net/472322412 |
| twitterImage: | https://i.imgur.com/L1PUmHbh.jpg |
| twitterCard: | summary_large_image |
Total processes
42
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
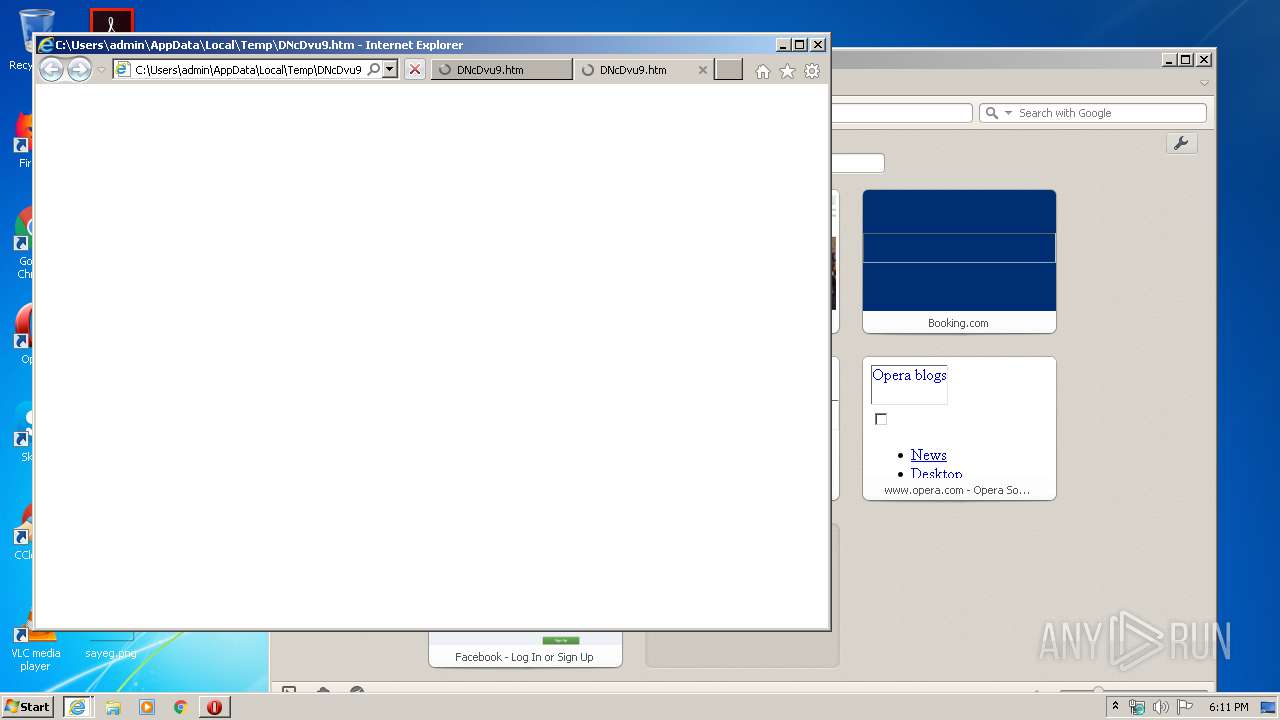
| 2344 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:144390 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2448 | SndVol.exe -f 7078386 12059 | C:\Windows\system32\SndVol.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Volume Mixer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3388 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:398593 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3448 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\DNcDvu9.htm | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3560 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
17 144
Read events
1 225
Write events
10 608
Delete events
5 311
Modification events
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1326108158 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796002 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
96
Text files
232
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprAB3C.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprAB7C.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprBBA9.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YNQMLJNCF6P10XAW6Q8U.temp | — | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\00\1F\oprDE84.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\pstorage\oprDE85.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
87
TCP/UDP connections
318
DNS requests
90
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | opera.exe | GET | 302 | 185.26.182.110:80 | http://redir.opera.com/speeddials/amazon/ | unknown | html | 319 b | whitelisted |
3308 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
3308 | opera.exe | GET | 200 | 143.204.208.198:80 | http://crl.rootg2.amazontrust.com/rootg2.crl | US | der | 608 b | whitelisted |
3308 | opera.exe | GET | 200 | 93.184.220.29:80 | http://s.symcb.com/pca3-g5.crl | US | der | 712 b | whitelisted |
3308 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertGlobalRootG2.crl | US | der | 588 b | whitelisted |
3308 | opera.exe | GET | 302 | 185.26.182.110:80 | http://redir.opera.com/speeddials/amazon/ | unknown | html | 319 b | whitelisted |
3308 | opera.exe | GET | 200 | 13.35.254.143:80 | http://s.ss2.us/r.crl | US | der | 434 b | whitelisted |
3308 | opera.exe | GET | 200 | 13.35.254.210:80 | http://crl.rootca1.amazontrust.com/rootca1.crl | US | der | 439 b | whitelisted |
3560 | iexplore.exe | GET | 200 | 172.217.16.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3308 | opera.exe | GET | 200 | 13.35.254.90:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAv2T7WiWm2%2F1URMh2LjqJU%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 151.101.112.193:445 | s.imgur.com | Fastly | US | malicious |
— | — | 151.101.112.193:137 | s.imgur.com | Fastly | US | malicious |
3448 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3308 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2344 | iexplore.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3308 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3308 | opera.exe | 185.26.182.93:80 | certs.opera.com | Opera Software AS | — | whitelisted |
3560 | iexplore.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3308 | opera.exe | 99.86.5.212:443 | www.amazon.com | AT&T Services, Inc. | US | unknown |
4 | System | 13.35.254.224:445 | d1fh3f0kkan5vq.cloudfront.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fonts.googleapis.com |
| whitelisted |
s.imgur.com |
| malicious |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
redir.opera.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
www.amazon.com |
| whitelisted |
s.symcb.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3308 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3308 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3308 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3308 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
16 ETPRO signatures available at the full report