| File name: | x.msi |
| Full analysis: | https://app.any.run/tasks/c1132b5e-2667-4c91-b3a5-89aad61cc1d4 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 18:07:08 |
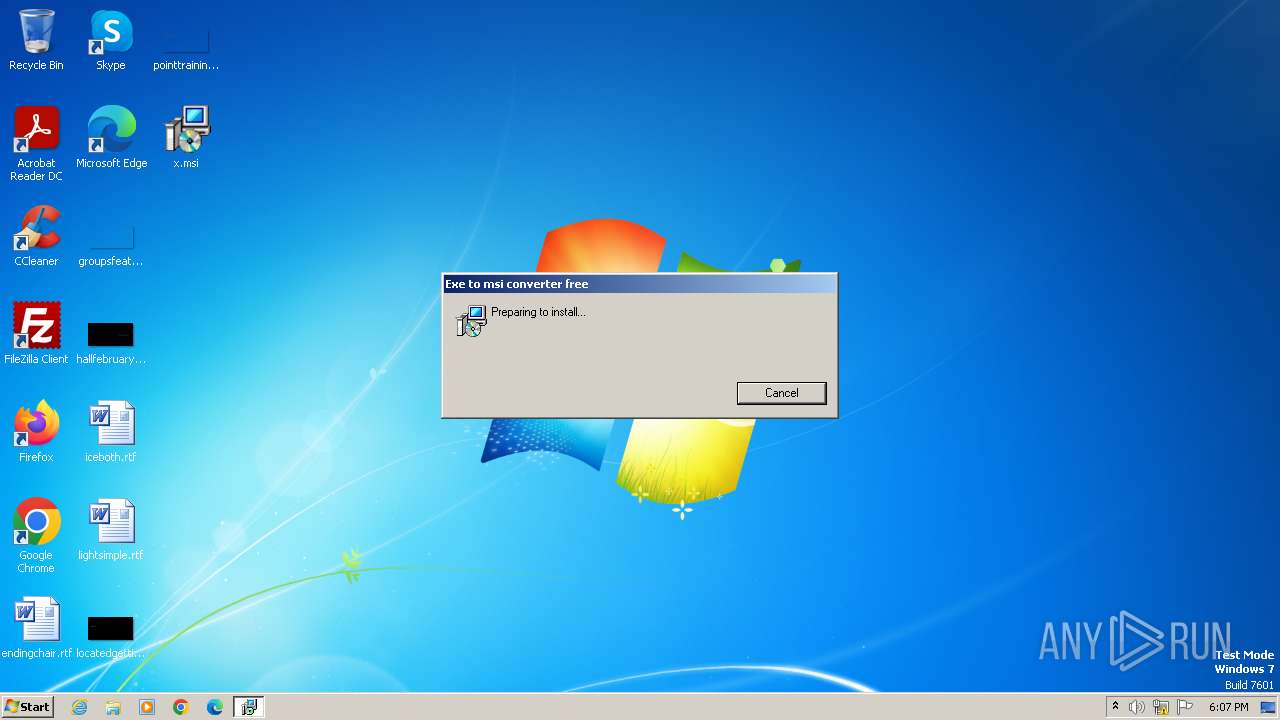
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 1252, Last Printed: Fri Sep 21 10:56:09 2012, Create Time/Date: Fri Sep 21 10:56:09 2012, Name of Creating Application: Windows Installer, Comments: :), Template: ;0, Last Saved By: devuser, Revision Number: {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E}, Last Saved Time/Date: Tue May 21 12:56:44 2013, Number of Pages: 100, Number of Words: 0, Security: 0, Author: Devilson |
| MD5: | ABB63F630360FB300D5AB50E7B5BFDE8 |
| SHA1: | 7CDE4B202A86600A44A684A422196AA4C6E402C4 |
| SHA256: | 05C0C4A694A0AC84338AC1E3BA41C73FA670F4C29A6699C8A80E2157BCE47CF8 |
| SSDEEP: | 3072:tEVq5DlfEHcMYMcelfwD2lmJ7TMftdT72yddlKCL52632wx9MtEPPX16N11+bkbY:tEVWDuHweCy6GtdTisdjNfkQoaaRm |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 3816)
Run PowerShell with an invisible window
- powershell.exe (PID: 3452)
Bypass execution policy to execute commands
- powershell.exe (PID: 3452)
Changes powershell execution policy (Bypass)
- MSI85C0.tmp (PID: 2996)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 2624)
The process executes Powershell scripts
- MSI85C0.tmp (PID: 2996)
Starts POWERSHELL.EXE for commands execution
- MSI85C0.tmp (PID: 2996)
Powershell version downgrade attack
- powershell.exe (PID: 3452)
INFO
Reads the computer name
- msiexec.exe (PID: 3816)
Checks supported languages
- msiexec.exe (PID: 3816)
- MSI85C0.tmp (PID: 2996)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3816)
Create files in a temporary directory
- msiexec.exe (PID: 3816)
Starts application with an unusual extension
- msiexec.exe (PID: 3816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LastPrinted: | 2012:09:21 09:56:09 |
| CreateDate: | 2012:09:21 09:56:09 |
| Software: | Windows Installer |
| Subject: | - |
| Keywords: | - |
| Comments: | :) |
| Template: | ;0 |
| LastModifiedBy: | devuser |
| RevisionNumber: | {C35CF0AA-9B3F-4903-9F05-EBF606D58D3E} |
| ModifyDate: | 2013:05:21 11:56:44 |
| Pages: | 100 |
| Words: | - |
| Security: | None |
| Author: | Devilson |
Total processes
46
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\x.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | "C:\Windows\Installer\MSI85C0.tmp" /s | C:\Windows\Installer\MSI85C0.tmp | — | msiexec.exe | |||||||||||
User: admin Company: TODO: <Company name> Integrity Level: MEDIUM Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3452 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -WindowStyle Hidden -ExecutionPolicy Bypass -file "C:\Users\admin\AppData\Local\Temp\ps85DD.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | MSI85C0.tmp | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 247
Read events
3 222
Write events
15
Delete events
10
Modification events
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000F2B487BA16B0D901C80700002C0A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000F2B487BA16B0D901C80700002C0A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 72 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000008C62D6BA16B0D901C80700002C0A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 400000000000000064514ABC16B0D901C80700002C0A0000D3070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 400000000000000064514ABC16B0D901C80700002C0A0000D4070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 400000000000000034645DBC16B0D901C80700002C0A0000D4070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Leave) |
Value: 4000000000000000781D5ABD16B0D901C80700002C0A0000D0070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Leave) |
Value: 4000000000000000781D5ABD16B0D901C80700002C0A0000D5070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore |
| Operation: | write | Name: | FirstRun |
Value: 0 | |||
Executable files
2
Suspicious files
12
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3816 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3816 | msiexec.exe | C:\Windows\Installer\MSI8551.tmp | binary | |
MD5:CB7DC81FAD456C1F5D669DF0913D9015 | SHA256:5FCC7D56F72CAB3244EC46921E344427817A295B8483748ACE06AADD75ABD529 | |||
| 3816 | msiexec.exe | C:\Windows\Installer\2081d8.ipi | binary | |
MD5:7C1FF49401D9B127F8E76069BFC14A63 | SHA256:0BFE93BC073241EC3DCBF3BC1D28628A6B846CDF9DE4D43A83A98DF83C624355 | |||
| 3816 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF9C6EF4FD05BA699A.TMP | binary | |
MD5:1B7E1EDD05B027325237C3230A3C8327 | SHA256:95953F8C084F9DE26691C8534BF193173853E4281B7B542E8719C098C3E145E8 | |||
| 3816 | msiexec.exe | C:\Windows\Installer\MSI85C0.tmp | executable | |
MD5:1AA31126E607BEA7C6A3050A8E8DE705 | SHA256:00B5D1191C53408CEBB034F4B17EC7AFCA6A8A4A72227D784FFAEEDC298EADF0 | |||
| 2996 | MSI85C0.tmp | C:\Users\admin\AppData\Local\Temp\ps85DD.tmp | text | |
MD5:19C2C33F140609A73D41D24A7833B425 | SHA256:5F26182E003865B371793CDD14C1AACDBEC3C5A22BB79169D61F2114D5CEFD07 | |||
| 3816 | msiexec.exe | C:\Windows\Installer\2081d6.msi | executable | |
MD5:ABB63F630360FB300D5AB50E7B5BFDE8 | SHA256:05C0C4A694A0AC84338AC1E3BA41C73FA670F4C29A6699C8A80E2157BCE47CF8 | |||
| 2996 | MSI85C0.tmp | C:\Users\admin\AppData\Local\Temp\ps85DD.tmp.ps1 | text | |
MD5:19C2C33F140609A73D41D24A7833B425 | SHA256:5F26182E003865B371793CDD14C1AACDBEC3C5A22BB79169D61F2114D5CEFD07 | |||
| 3816 | msiexec.exe | C:\Config.Msi\2081d9.rbs | binary | |
MD5:72417A50465369FB8E89AAF5D87A9DDF | SHA256:C21186336B03266F3FDBAC1731C1F37043304A7D74D59B82F6973DB09C8AD69D | |||
| 3816 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF5347FD3A223691CC.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |