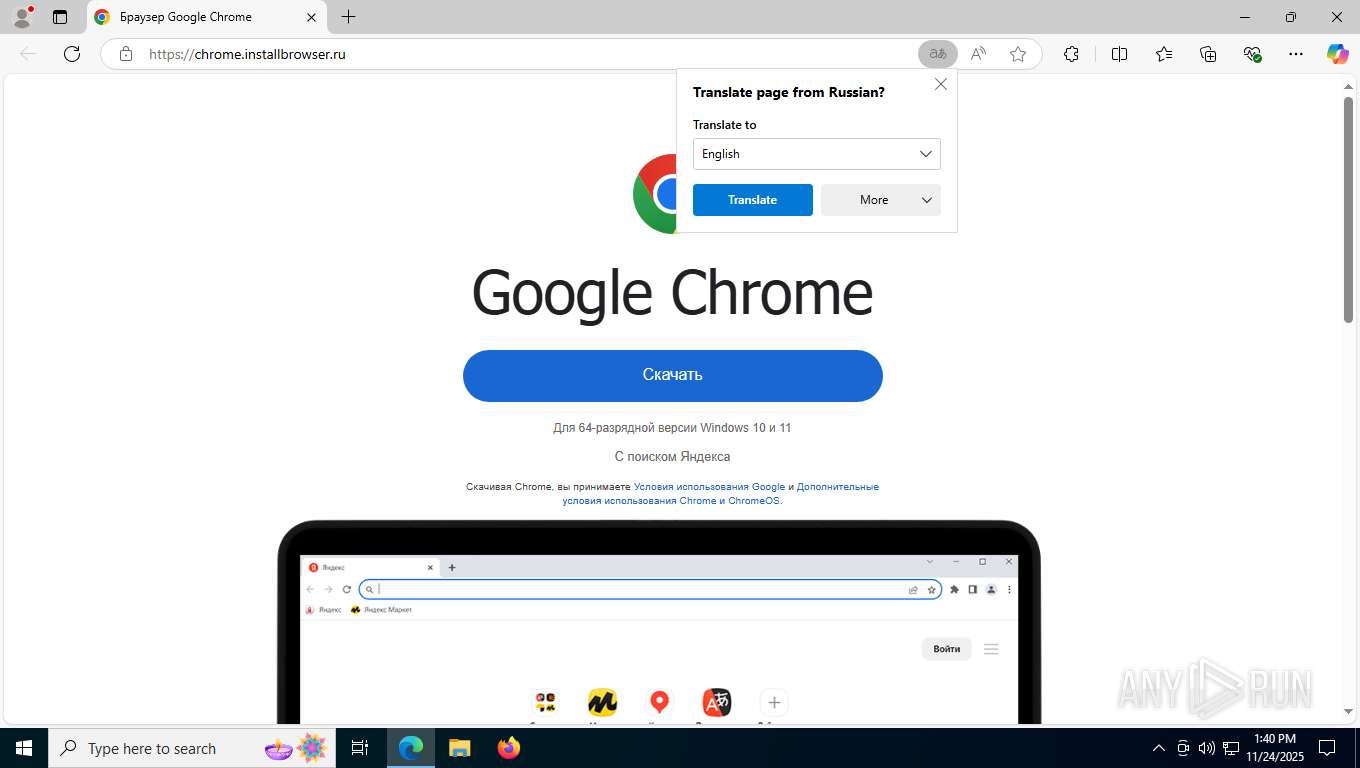
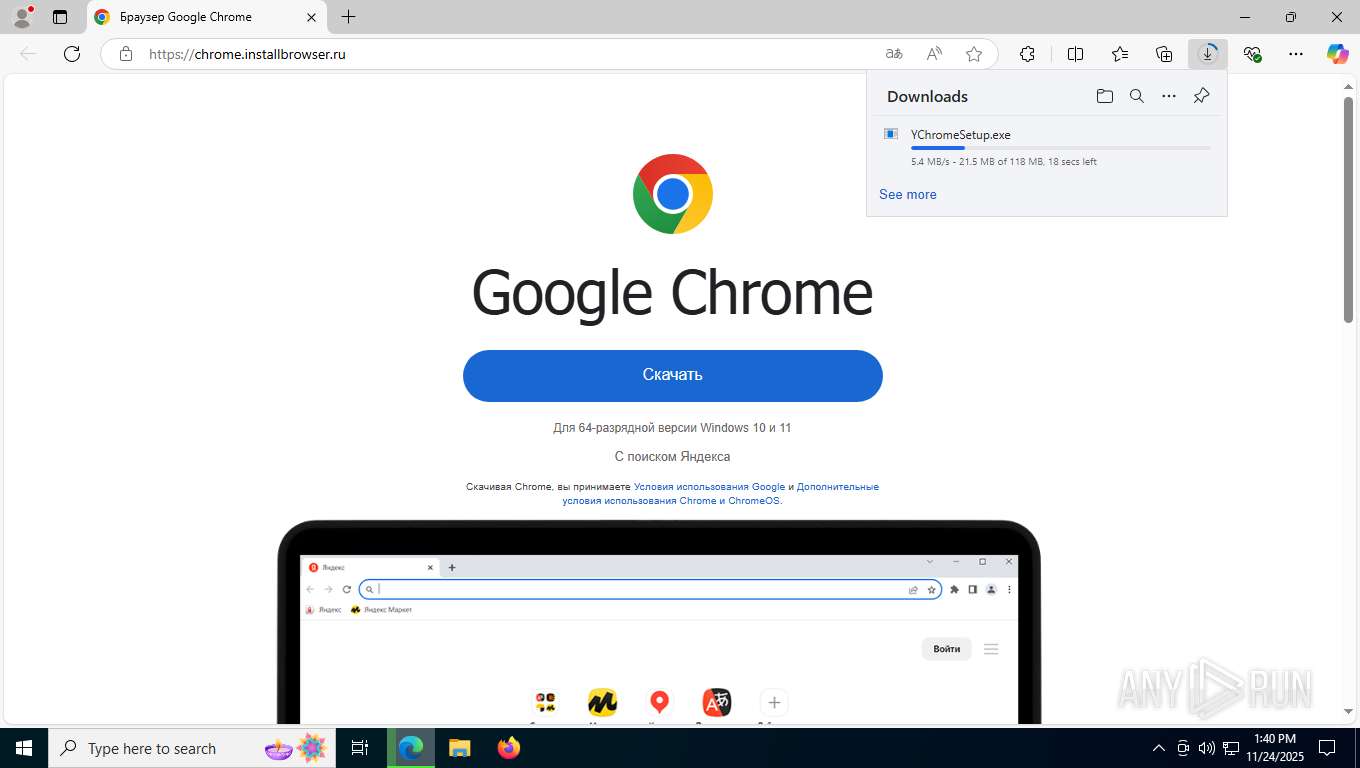
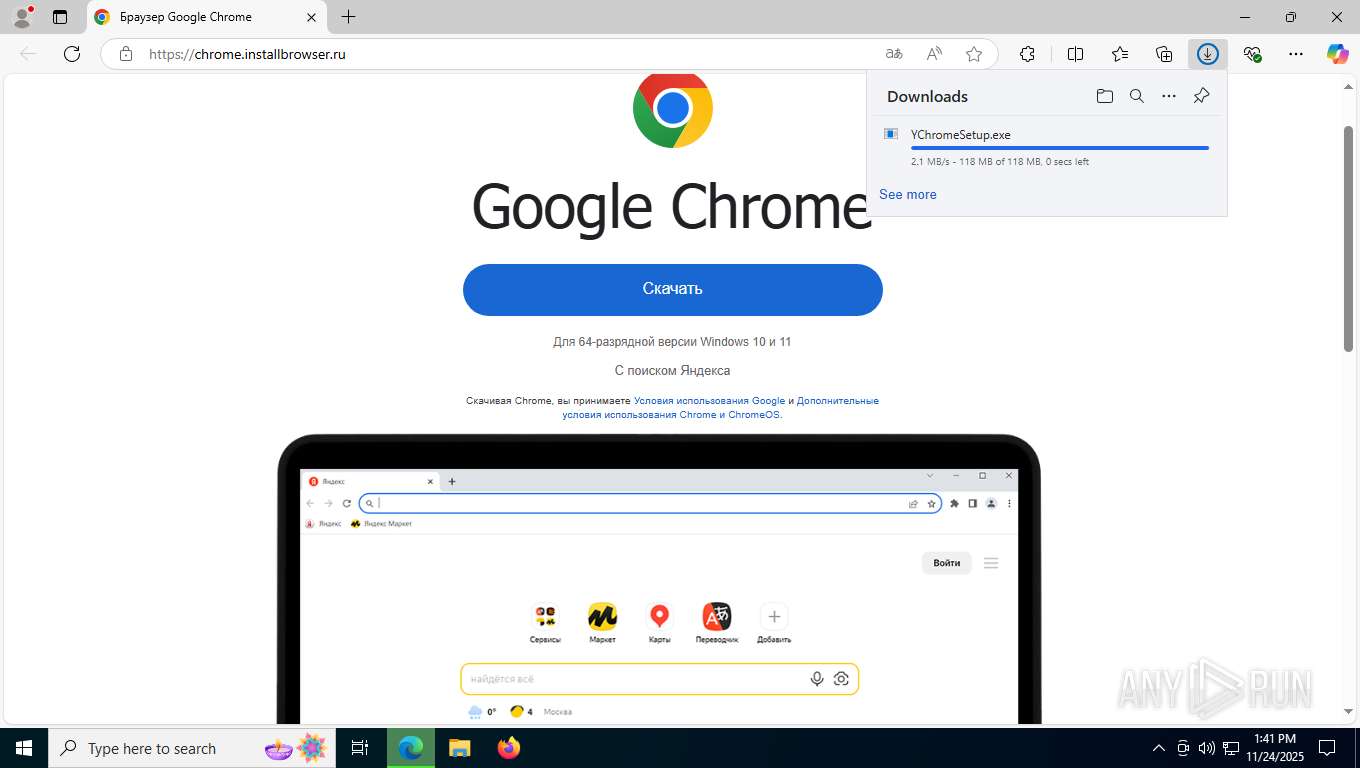
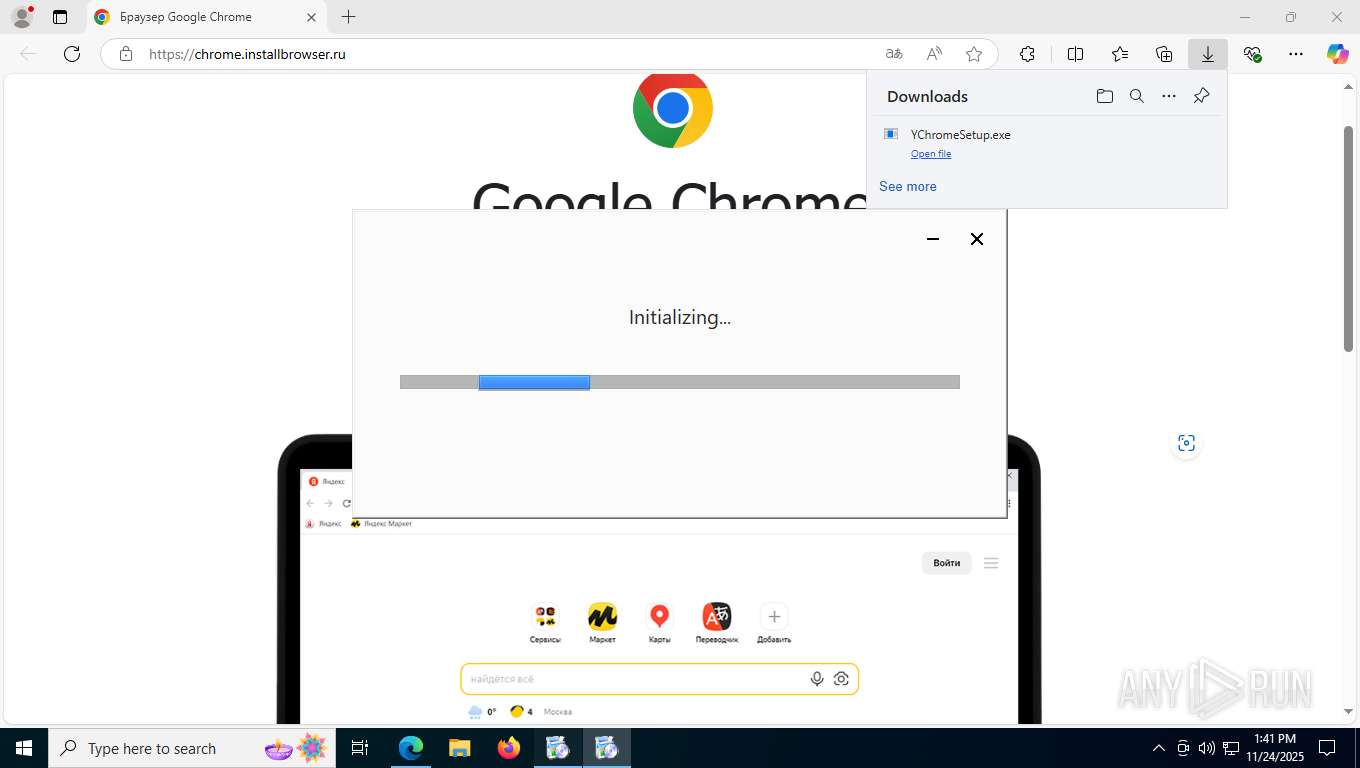
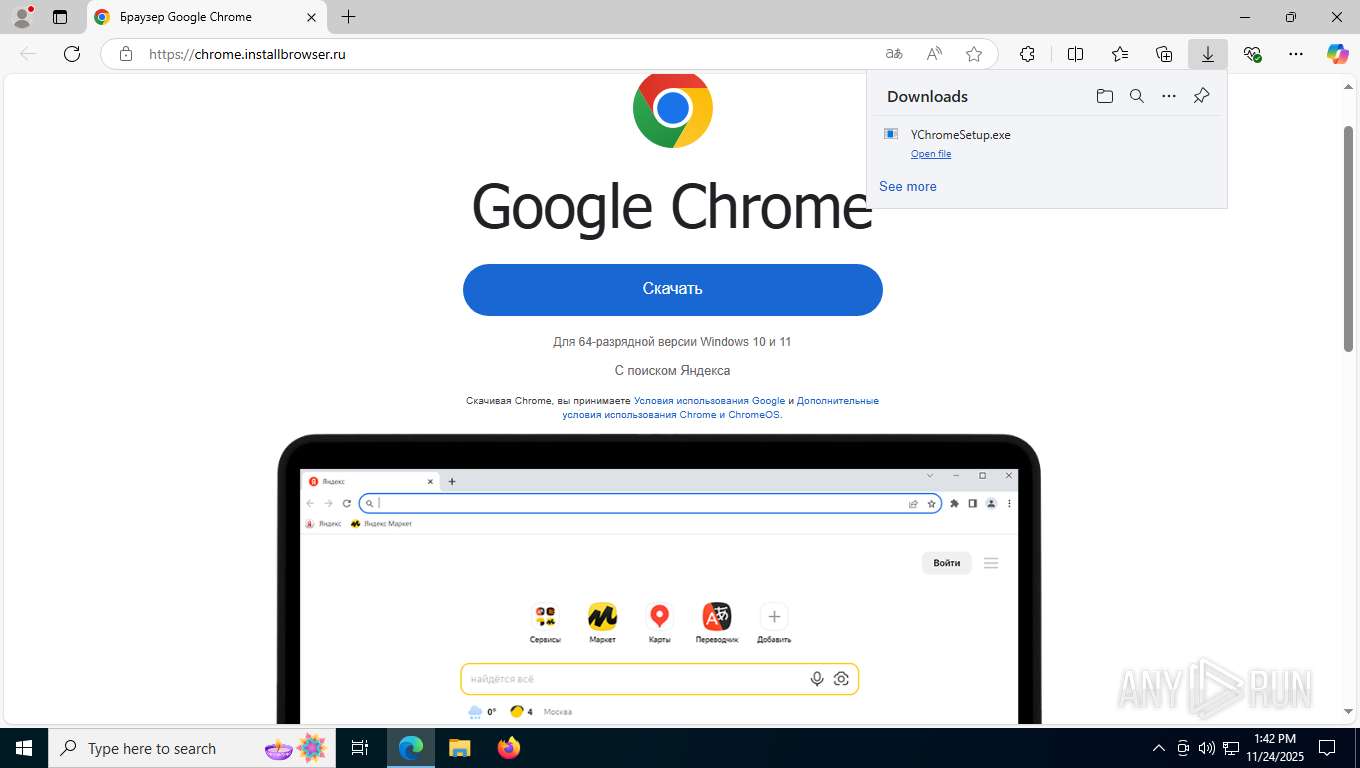
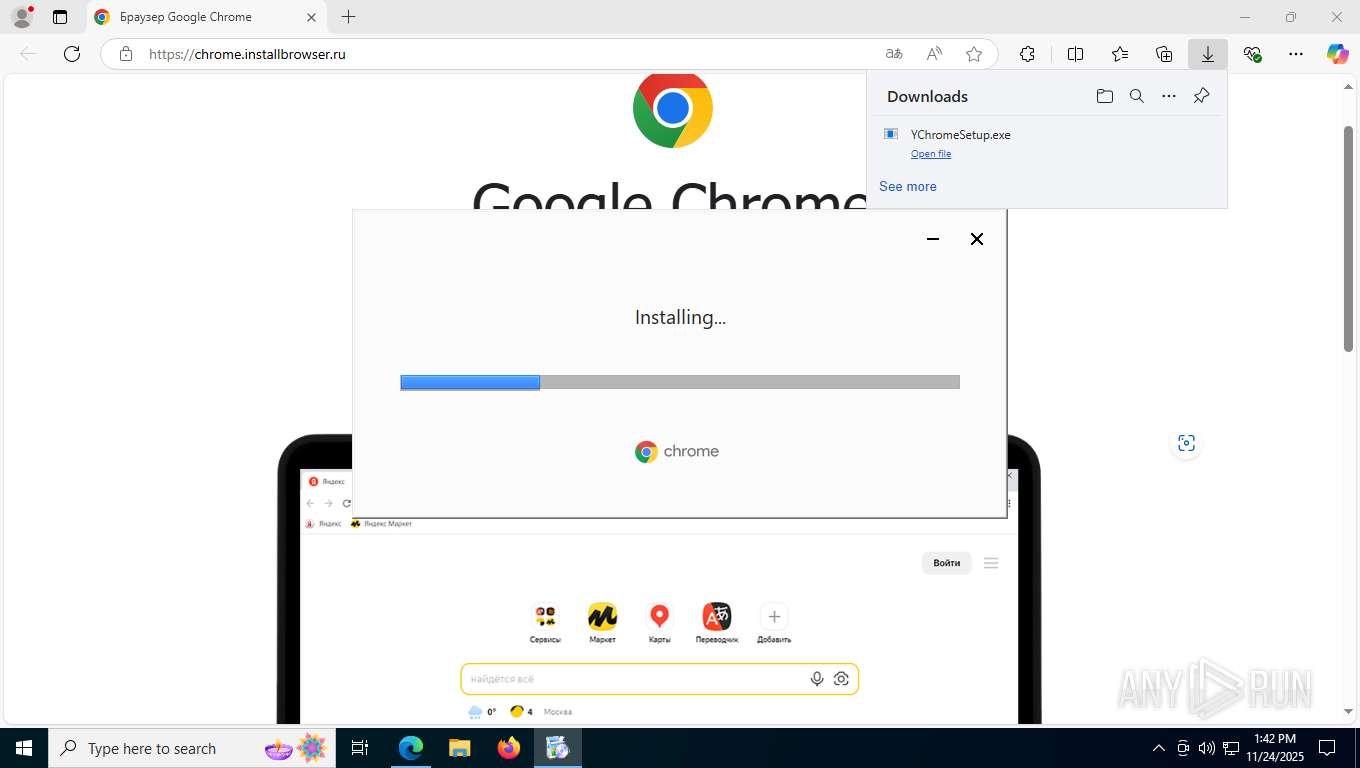
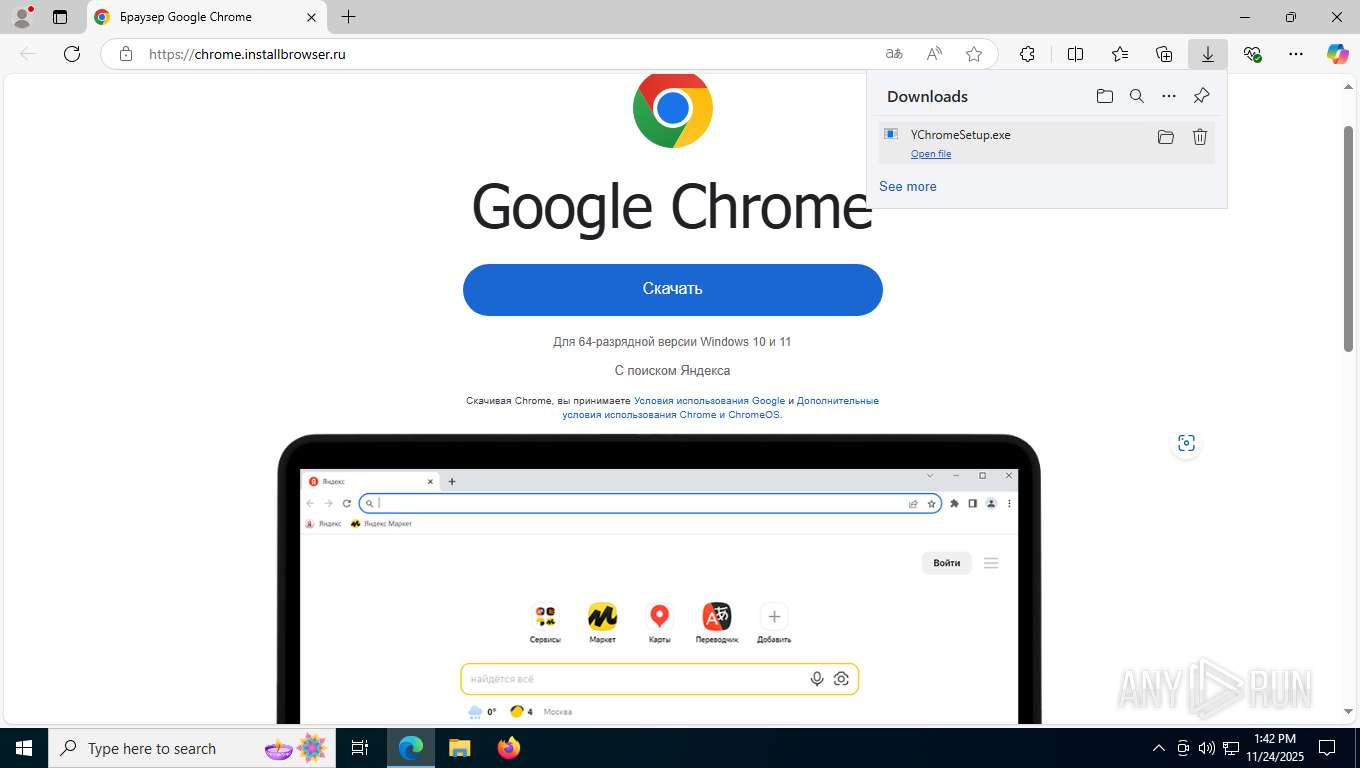
| URL: | chrome.installbrowser.ru |
| Full analysis: | https://app.any.run/tasks/cf39270b-c51a-441b-8a62-7c8d2f51d4f2 |
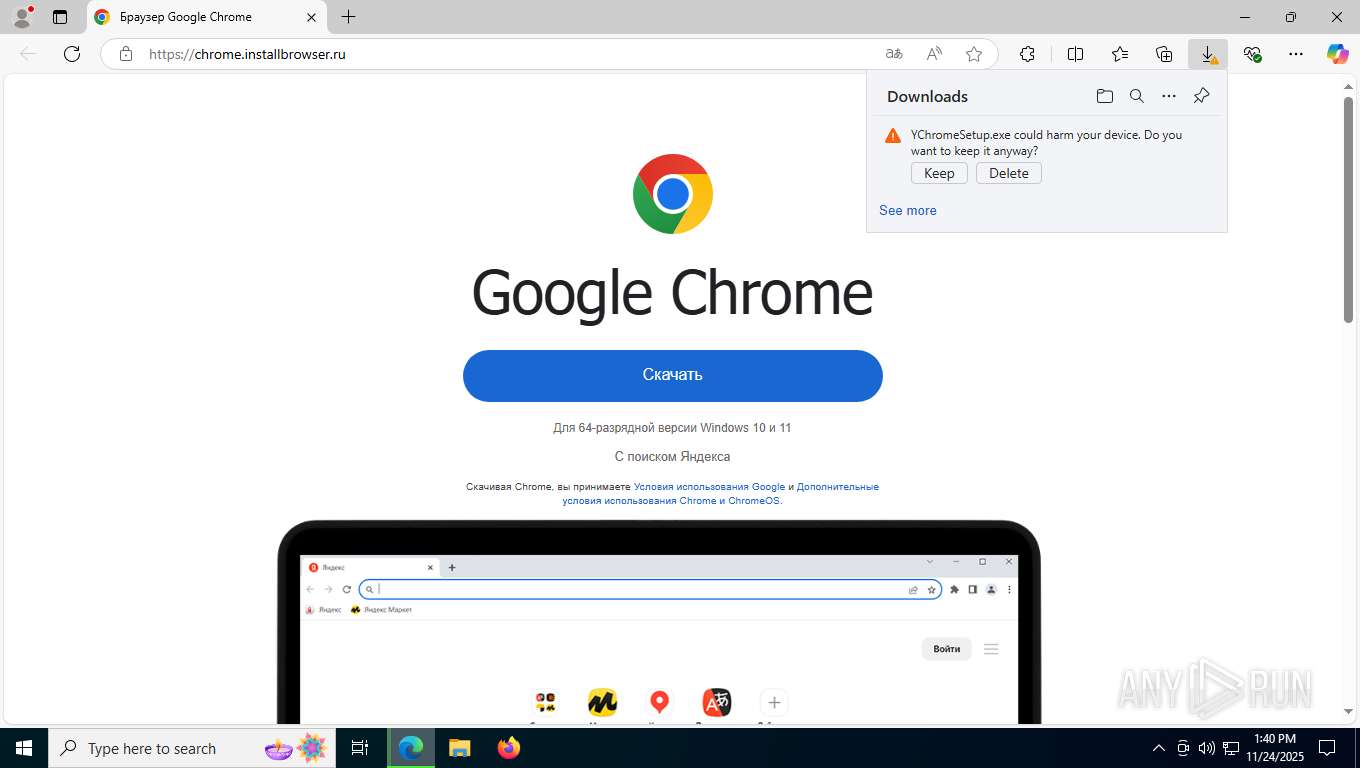
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2025, 13:40:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C300DA5D07B354FABD34F5E8E28B6CAD |
| SHA1: | 657B318B8D60C46DFE462B938C9B111897588124 |
| SHA256: | 05B6F614095C9F122CD8E9CA799FF5400B40E63D99BA35261267C5C692F92CF0 |
| SSDEEP: | 3:ZEnVjQ:ZEm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- updater.exe (PID: 2052)
- updater.exe (PID: 5580)
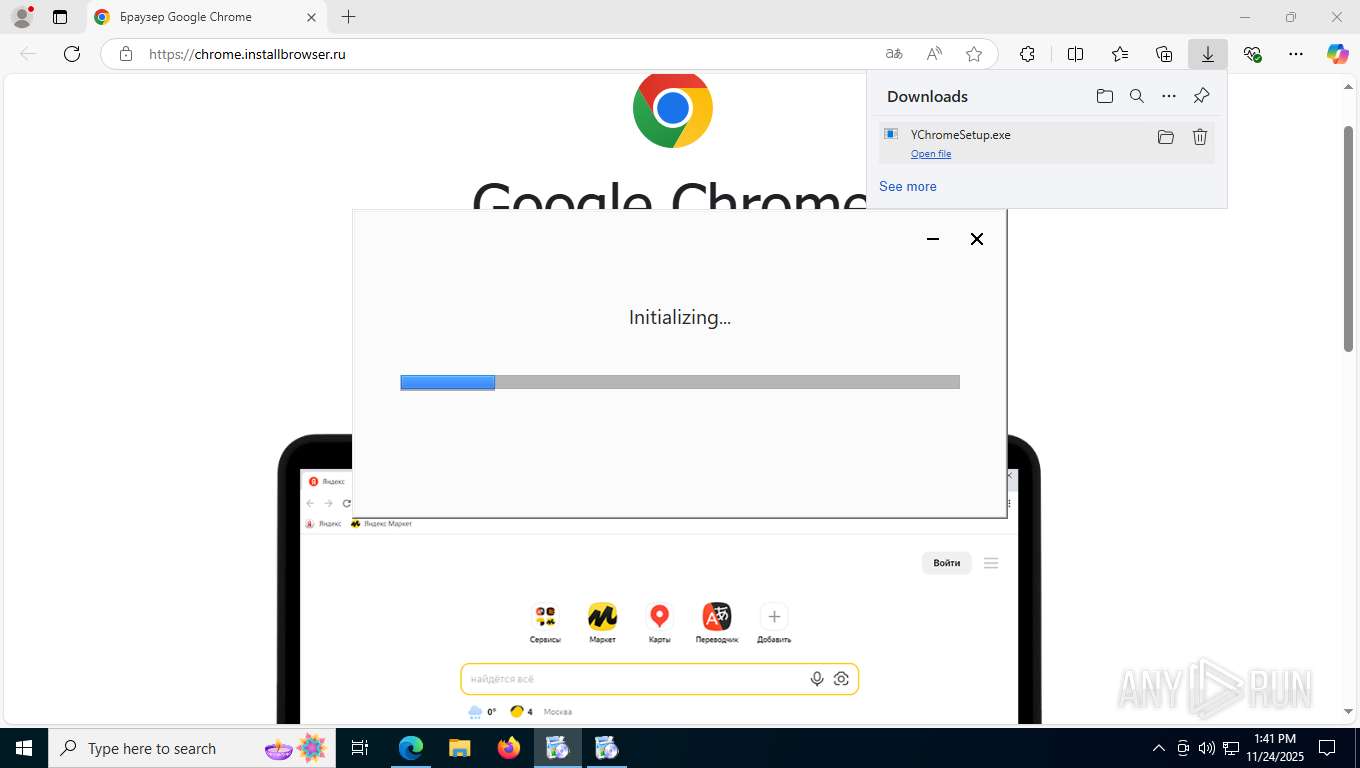
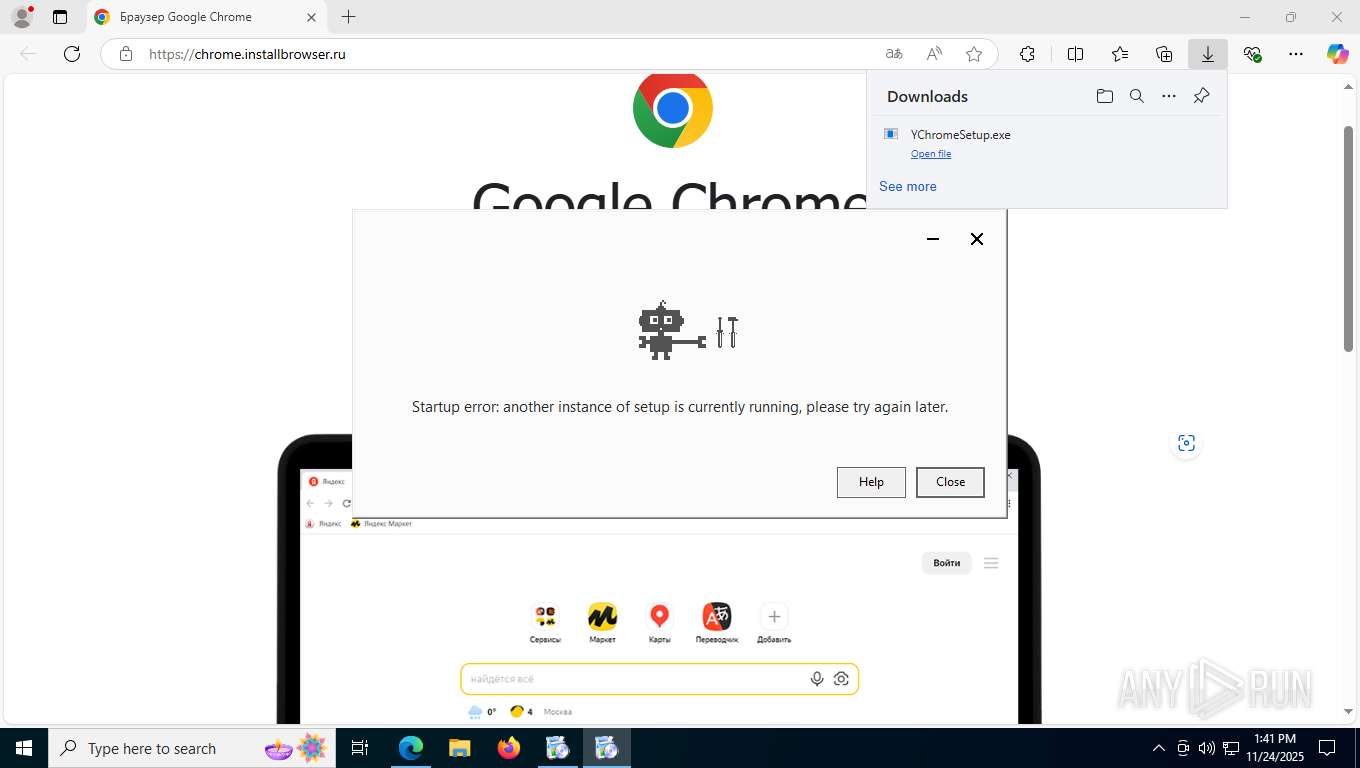
Application launched itself
- updater.exe (PID: 2764)
- updater.exe (PID: 2052)
- setup.exe (PID: 6636)
- updater.exe (PID: 5580)
- setup.exe (PID: 600)
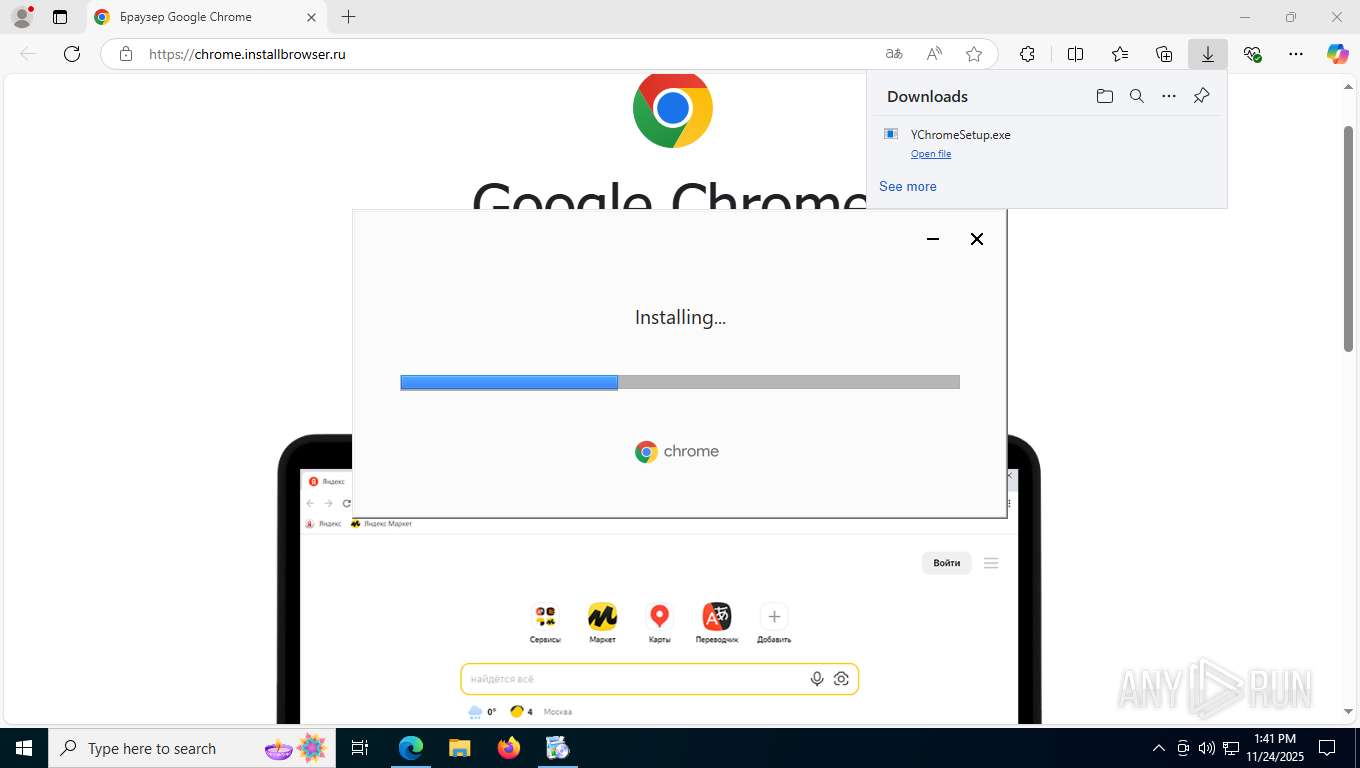
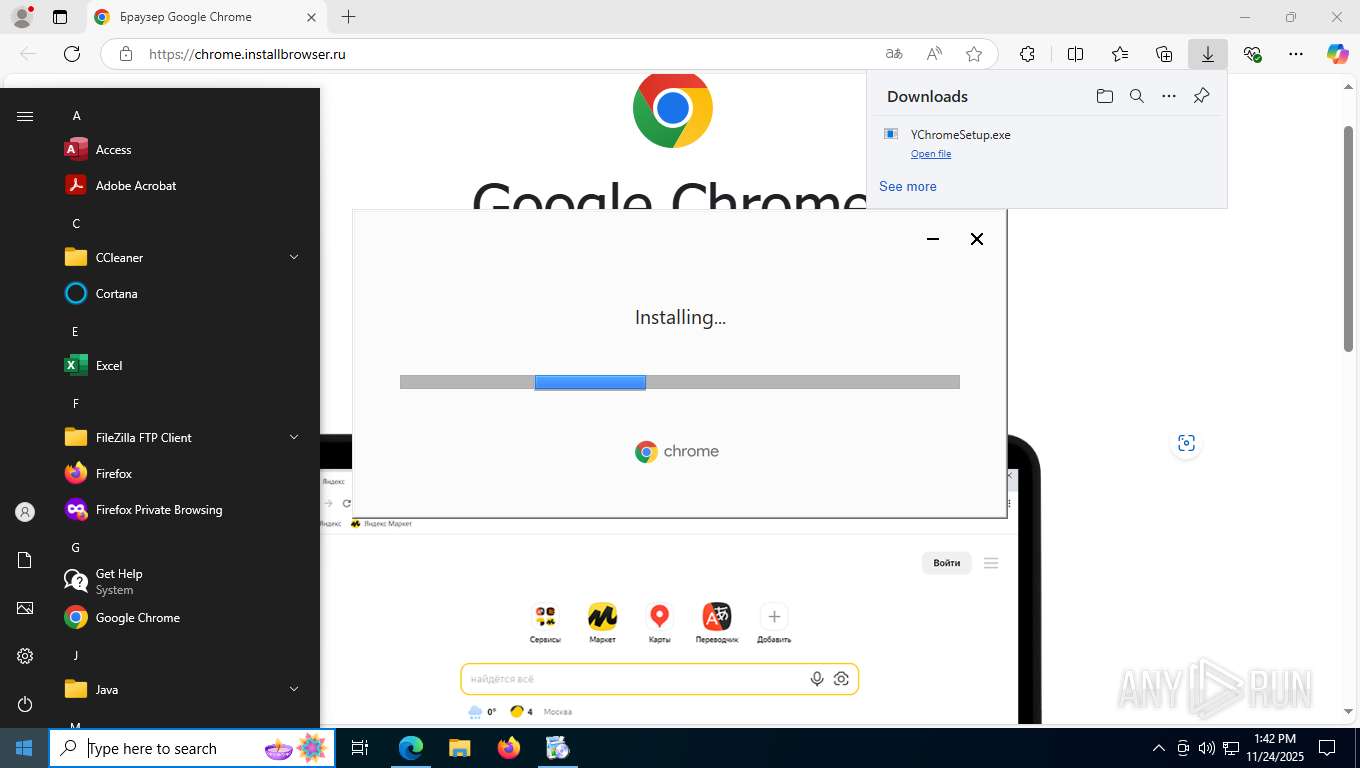
Executable content was dropped or overwritten
- updater.exe (PID: 2052)
- updater.exe (PID: 5420)
- 133.0.6943.60_chrome_installer.exe (PID: 3200)
- 133.0.6943.60_chrome_installer.exe (PID: 6048)
Non windows owned service launched
- updater.exe (PID: 5420)
- updater.exe (PID: 4464)
- updater.exe (PID: 5948)
Executes as Windows Service
- updater.exe (PID: 5420)
- updater.exe (PID: 4464)
- updater.exe (PID: 5948)
INFO
Application launched itself
- msedge.exe (PID: 7436)
Checks supported languages
- identity_helper.exe (PID: 6176)
- YChromeSetup.exe (PID: 6676)
- YChromeSetup.exe (PID: 2852)
- ChromeSetup.exe (PID: 7172)
- ChromeSetup.exe (PID: 2032)
- updater.exe (PID: 2052)
- updater.exe (PID: 7428)
- updater.exe (PID: 7676)
- updater.exe (PID: 2764)
- 133.0.6943.60_chrome_installer.exe (PID: 3200)
- setup.exe (PID: 6636)
- setup.exe (PID: 7096)
- ChromeSetup.exe (PID: 6456)
- YChromeSetup.exe (PID: 7256)
- updater.exe (PID: 5580)
- updater.exe (PID: 4240)
- 133.0.6943.60_chrome_installer.exe (PID: 6048)
- setup.exe (PID: 600)
- setup.exe (PID: 4064)
Reads Environment values
- identity_helper.exe (PID: 6176)
Reads the computer name
- identity_helper.exe (PID: 6176)
- ChromeSetup.exe (PID: 7172)
- ChromeSetup.exe (PID: 2032)
- updater.exe (PID: 2764)
- updater.exe (PID: 2052)
- setup.exe (PID: 6636)
- 133.0.6943.60_chrome_installer.exe (PID: 3200)
- ChromeSetup.exe (PID: 6456)
- updater.exe (PID: 5580)
- 133.0.6943.60_chrome_installer.exe (PID: 6048)
- setup.exe (PID: 600)
Executable content was dropped or overwritten
- msedge.exe (PID: 7436)
Creates files or folders in the user directory
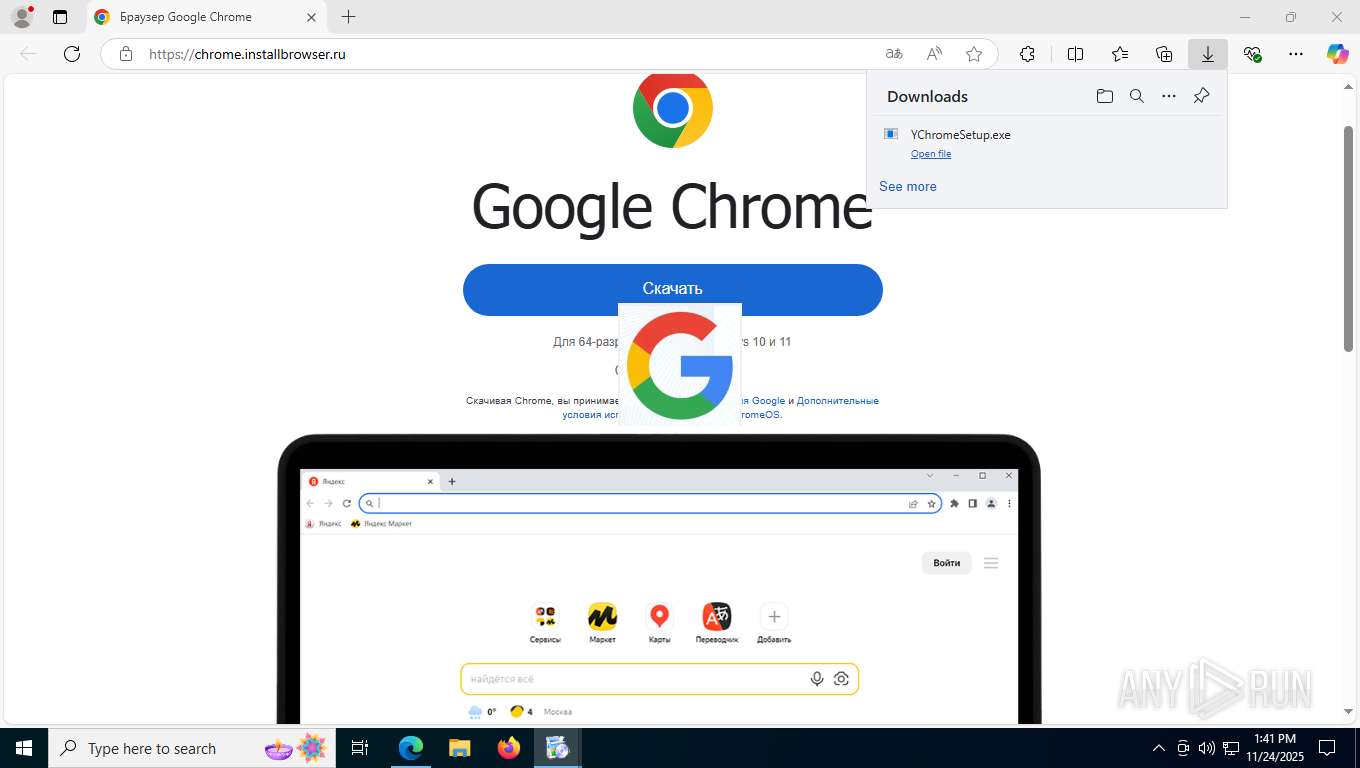
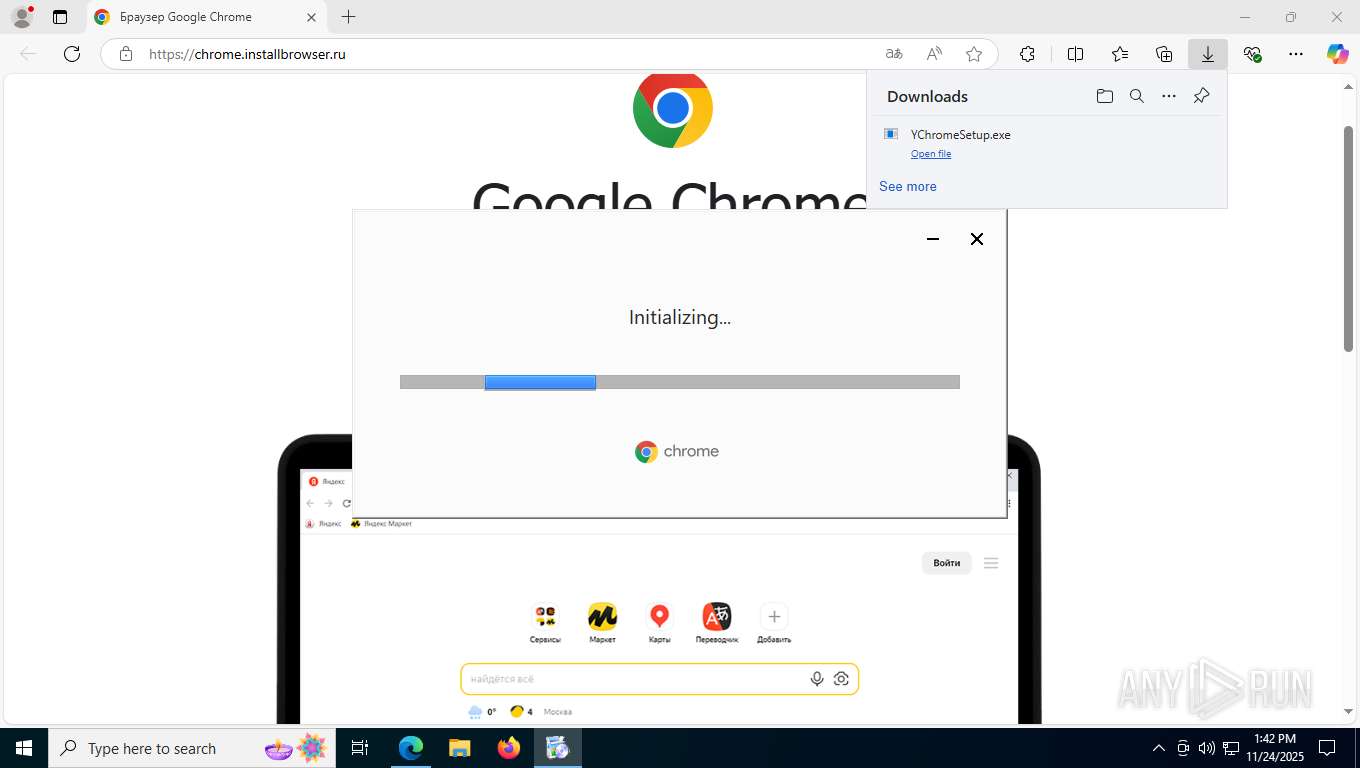
- YChromeSetup.exe (PID: 6676)
- updater.exe (PID: 2052)
Creates files in the program directory
- YChromeSetup.exe (PID: 6676)
- updater.exe (PID: 2052)
- updater.exe (PID: 5420)
- setup.exe (PID: 6636)
- updater.exe (PID: 4464)
- setup.exe (PID: 600)
- updater.exe (PID: 5948)
Create files in a temporary directory
- YChromeSetup.exe (PID: 6676)
- YChromeSetup.exe (PID: 2852)
- updater.exe (PID: 2052)
- YChromeSetup.exe (PID: 7256)
- updater.exe (PID: 5580)
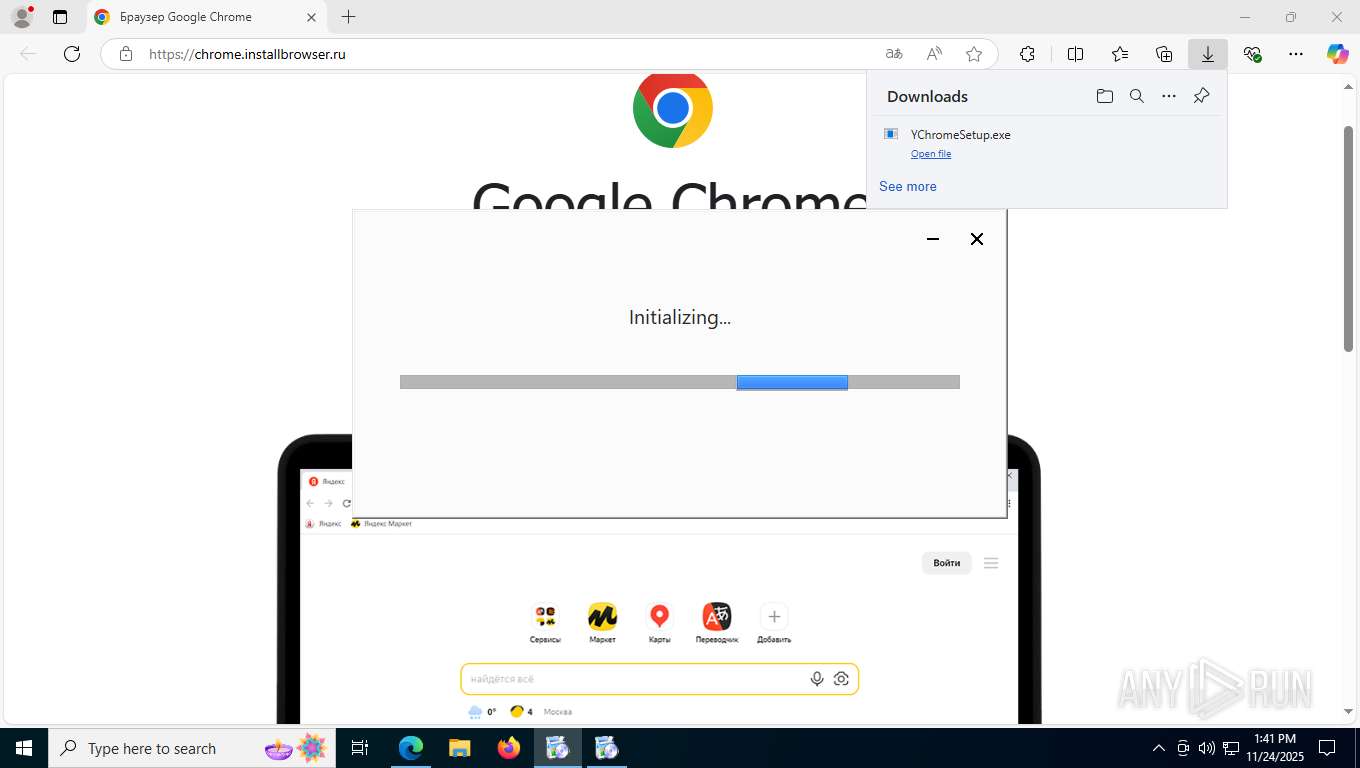
Process checks whether UAC notifications are on
- updater.exe (PID: 2052)
- updater.exe (PID: 2764)
- updater.exe (PID: 5580)
The sample compiled with english language support
- updater.exe (PID: 2052)
- updater.exe (PID: 5420)
- 133.0.6943.60_chrome_installer.exe (PID: 3200)
- 133.0.6943.60_chrome_installer.exe (PID: 6048)
Checks proxy server information
- updater.exe (PID: 2052)
- slui.exe (PID: 4900)
- updater.exe (PID: 5580)
Reads the machine GUID from the registry
- updater.exe (PID: 2052)
- updater.exe (PID: 5580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
213
Monitored processes
57
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5436,i,3036916590293040384,8921814886413198872,262144 --variations-seed-version --mojo-platform-channel-handle=5412 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 600 | "C:\WINDOWS\SystemTemp\Google6456_894759764\bin\Offline\{f7cace56-cdb1-4c42-92f1-c41b25a8624f}\{8a69d345-d564-463c-aff1-a69d9e530f96}\CR_80E65.tmp\setup.exe" --install-archive="C:\WINDOWS\SystemTemp\Google6456_894759764\bin\Offline\{f7cace56-cdb1-4c42-92f1-c41b25a8624f}\{8a69d345-d564-463c-aff1-a69d9e530f96}\CR_80E65.tmp\CHROME.PACKED.7Z" --do-not-launch-chrome --installerdata="C:\Windows\SystemTemp\scoped_dir5948_1245977799\bc6ef9f7-f3aa-4802-9970-1a3f44d3edd2.tmp" | C:\Windows\SystemTemp\Google6456_894759764\bin\Offline\{f7cace56-cdb1-4c42-92f1-c41b25a8624f}\{8A69D345-D564-463c-AFF1-A69D9E530F96}\CR_80E65.tmp\setup.exe | — | 133.0.6943.60_chrome_installer.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Chrome Installer Exit code: 4 Version: 133.0.6943.60 Modules
| |||||||||||||||
| 916 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3944,i,3036916590293040384,8921814886413198872,262144 --variations-seed-version --mojo-platform-channel-handle=3612 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3916,i,3036916590293040384,8921814886413198872,262144 --variations-seed-version --mojo-platform-channel-handle=5620 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2032 | C:\Users\admin\AppData\Local\Temp\ChromeSetup.exe | C:\Users\admin\AppData\Local\Temp\ChromeSetup.exe | — | YChromeSetup.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Installer Exit code: 4 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 2052 | "C:\WINDOWS\SystemTemp\Google2032_429502041\bin\updater.exe" --install=appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={56823542-6D38-F4C6-B3DF-92DF7DF2AB53}&lang=en&browser=4&usagestats=0&appname=Google%20Chrome&needsadmin=prefers&ap=x64-statsdef_1&installdataindex=empty --enable-logging --vmodule=*/components/winhttp/*=1,*/components/update_client/*=2,*/chrome/enterprise_companion/*=2,*/chrome/updater/*=2 --offlinedir={f7cace56-cdb1-4c42-92f1-c41b25a8624f} | C:\Windows\SystemTemp\Google2032_429502041\bin\updater.exe | ChromeSetup.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Updater Exit code: 4 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 2564 | "C:\Users\admin\Downloads\YChromeSetup.exe" | C:\Users\admin\Downloads\YChromeSetup.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5680,i,3036916590293040384,8921814886413198872,262144 --variations-seed-version --mojo-platform-channel-handle=5836 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2764 | "C:\WINDOWS\SystemTemp\Google7172_2040990628\bin\updater.exe" --install=appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={56823542-6D38-F4C6-B3DF-92DF7DF2AB53}&lang=en&browser=4&usagestats=0&appname=Google%20Chrome&needsadmin=prefers&ap=x64-statsdef_1&installdataindex=empty --enable-logging --vmodule=*/components/winhttp/*=1,*/components/update_client/*=2,*/chrome/enterprise_companion/*=2,*/chrome/updater/*=2 --offlinedir={f7cace56-cdb1-4c42-92f1-c41b25a8624f} | C:\Windows\SystemTemp\Google7172_2040990628\bin\updater.exe | — | ChromeSetup.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Updater Exit code: 75075 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\Downloads\YChromeSetup.exe" | C:\Users\admin\Downloads\YChromeSetup.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
7 001
Read events
6 888
Write events
102
Delete events
11
Modification events
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\Clients\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | pv |
Value: 134.0.6985.0 | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\Clients\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | name |
Value: GoogleUpdater | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientState\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | pv |
Value: 134.0.6985.0 | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientState\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | name |
Value: GoogleUpdater | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1DEF635A-C3EF-530A-8F03-E90E7C834B9F} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{1DEF635A-C3EF-530A-8F03-E90E7C834B9F} |
| Operation: | write | Name: | AppID |
Value: {1DEF635A-C3EF-530A-8F03-E90E7C834B9F} | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{1DEF635A-C3EF-530A-8F03-E90E7C834B9F} |
| Operation: | write | Name: | LocalService |
Value: GoogleUpdaterInternalService134.0.6985.0 | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{1DEF635A-C3EF-530A-8F03-E90E7C834B9F} |
| Operation: | write | Name: | ServiceParameters |
Value: --com-service | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{9640E544-7267-58DA-B168-300752A6C920}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (2052) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{9640E544-7267-58DA-B168-300752A6C920}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
Executable files
21
Suspicious files
293
Text files
68
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1626d6.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1626e6.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1626f5.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1626f5.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1626f5.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
89
DNS requests
79
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7800 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:w34wUoi9MwHkmyy50fp0yZ0-h10eT3jn-2QvgA-c2cs&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
5972 | svchost.exe | GET | 200 | 104.94.127.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2348 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4400 | SIHClient.exe | GET | 200 | 104.76.201.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
4400 | SIHClient.exe | GET | 200 | 104.76.201.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
4400 | SIHClient.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | DE | binary | 824 b | whitelisted |
4400 | SIHClient.exe | GET | 200 | 104.76.201.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
4400 | SIHClient.exe | GET | 200 | 104.76.201.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
4400 | SIHClient.exe | GET | 200 | 104.76.201.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
4400 | SIHClient.exe | GET | 200 | 104.76.201.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | DE | binary | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2348 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4264 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 104.126.37.160:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7800 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7800 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7800 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7800 | msedge.exe | 104.18.23.222:443 | copilot.microsoft.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
chrome.installbrowser.ru |
| unknown |
copilot.microsoft.com |
| whitelisted |
tools.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP request field missing colon |
— | — | Generic Protocol Command Decode | SURICATA HTTP request header invalid |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |