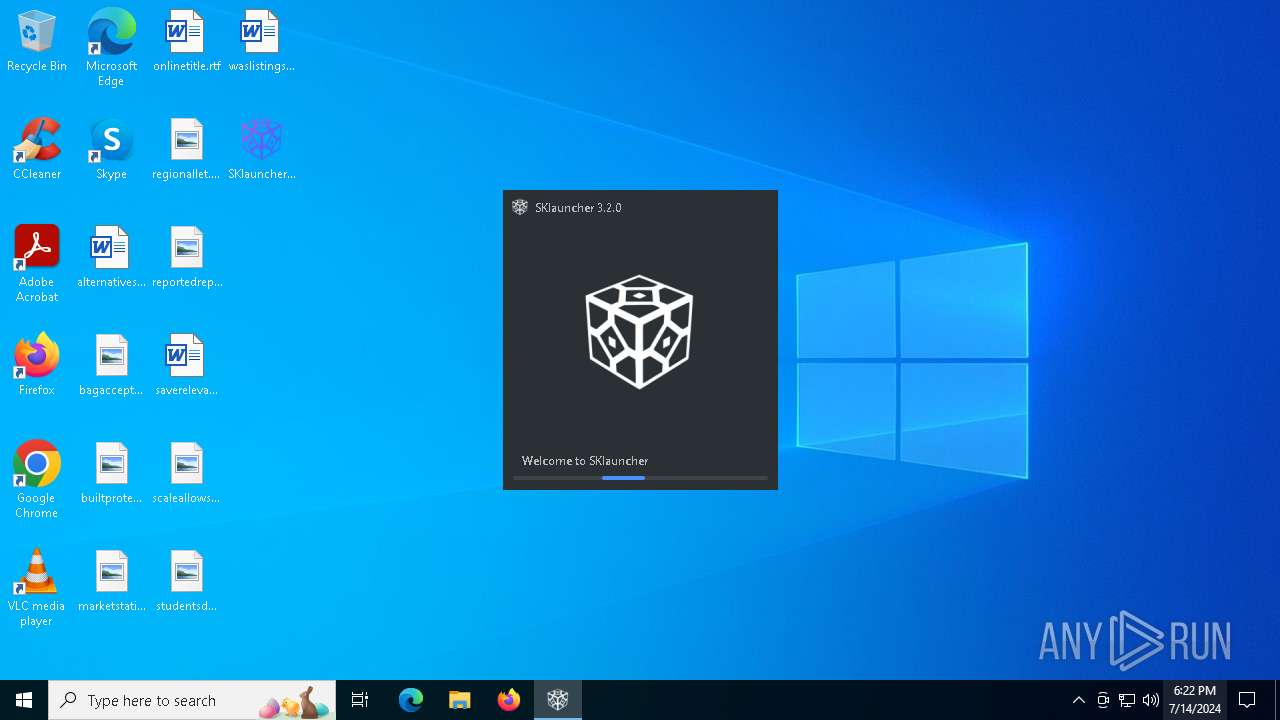
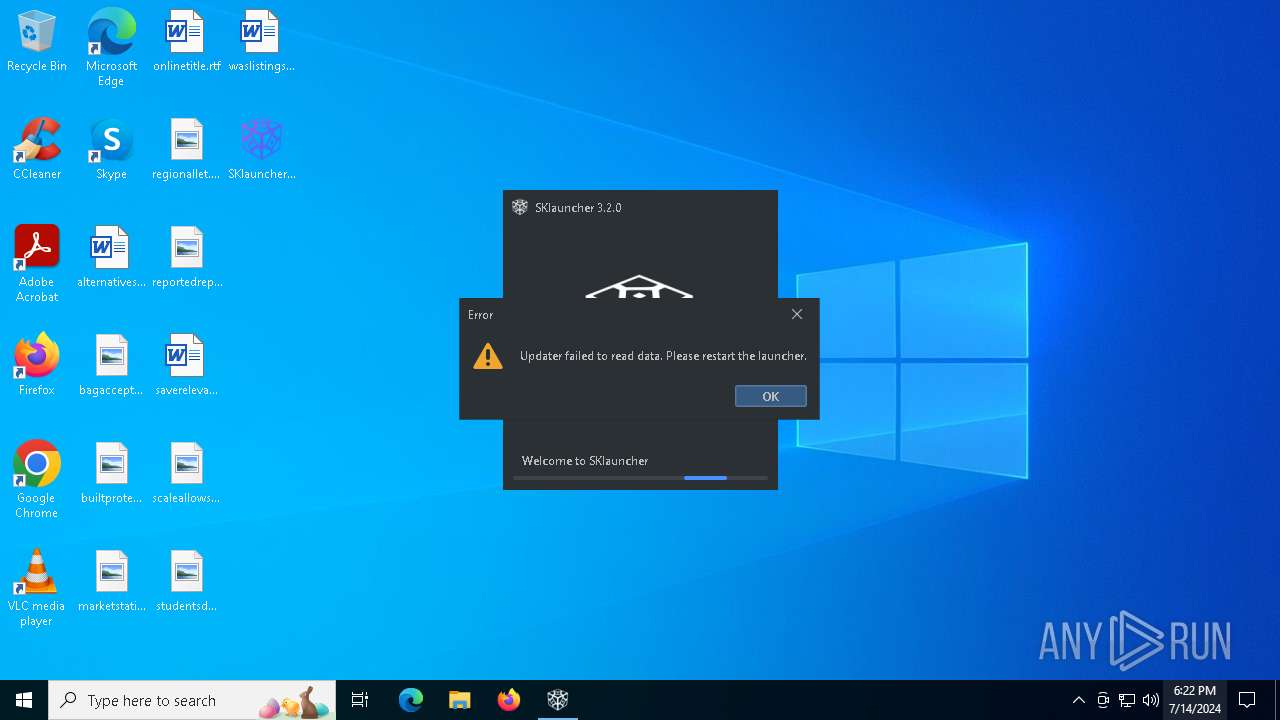
| File name: | SKlauncher-3.2.exe |
| Full analysis: | https://app.any.run/tasks/d7230fd9-375c-4a42-9f43-db5a9a2330e8 |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2024, 18:21:48 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | B63468DD118DFBCA5EF7967BA344E0E3 |
| SHA1: | 2BA4F0DF5F3BD284BF2A89ABA320E4440D8B8355 |
| SHA256: | 05AE2F0DD61EF10019B94C200E8DF192B767BB4CC24A7E7B329AB43CC9C74CAF |
| SSDEEP: | 49152:YFEn3+XxVys8eSHmL3FF+TviOsmxup8bZ1ayPjkCmoHeGkqbIYT4Z6mitOw68pt5:Ye3heSHCF+TviOsmxueZ8mmqIOztOT8V |
MALICIOUS
Drops the executable file immediately after the start
- SKlauncher-3.2.exe (PID: 4564)
SUSPICIOUS
Checks for Java to be installed
- SKlauncher-3.2.exe (PID: 4564)
Executable content was dropped or overwritten
- SKlauncher-3.2.exe (PID: 4564)
INFO
Checks supported languages
- SKlauncher-3.2.exe (PID: 4564)
- java.exe (PID: 1228)
- i4jdel0.exe (PID: 4004)
Creates files in the program directory
- java.exe (PID: 1228)
Creates files or folders in the user directory
- SKlauncher-3.2.exe (PID: 4564)
Reads the computer name
- SKlauncher-3.2.exe (PID: 4564)
Create files in a temporary directory
- java.exe (PID: 1228)
- SKlauncher-3.2.exe (PID: 4564)
Reads the machine GUID from the registry
- SKlauncher-3.2.exe (PID: 4564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2022:11:18 17:55:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 9 |
| CodeSize: | 244736 |
| InitializedDataSize: | 171520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21394 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.0.0 |
| ProductVersionNumber: | 3.2.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Mojang |
| FileDescription: | The Minecraft Launcher |
| FileVersion: | 3.2.0.0 |
| LegalCopyright: | - |
| ProductName: | SKlauncher |
| ProductVersion: | 3.2.0 |
| OriginalFileName: | SKlauncher-3.2-x64.exe |
| InternalName: | SKlauncher |
Total processes
125
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | "c:\PROGRA~1\java\JRE18~1.0_2\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_271\bin\java.exe | — | SKlauncher-3.2.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3188 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4004 | C:\Users\admin\AppData\Local\Temp\i4jdel0.exe i4j2003957759427947516.tmp | C:\Users\admin\AppData\Local\Temp\i4jdel0.exe | — | SKlauncher-3.2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4564 | "C:\Users\admin\Desktop\SKlauncher-3.2.exe" | C:\Users\admin\Desktop\SKlauncher-3.2.exe | explorer.exe | ||||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: The Minecraft Launcher Exit code: 1 Version: 3.2.0.0 Modules
| |||||||||||||||
Total events
1 141
Read events
1 138
Write events
3
Delete events
0
Modification events
| (PID) Process: | (4564) SKlauncher-3.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ej-technologies\exe4j\jvms2\c:/program files/java/jre1.8.0_271/bin/java.exe |
| Operation: | write | Name: | LastWriteTime |
Value: FE850DA0993CD901 | |||
| (PID) Process: | (4564) SKlauncher-3.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ej-technologies\exe4j\jvms2\c:/program files/java/jre1.8.0_271/bin/java.exe |
| Operation: | write | Name: | Version |
Value: 1.8.0_271 | |||
| (PID) Process: | (4564) SKlauncher-3.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ej-technologies\exe4j\jvms2\c:/program files/java/jre1.8.0_271/bin/java.exe |
| Operation: | write | Name: | Machine |
Value: 34404 | |||
Executable files
3
Suspicious files
4
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Local\Temp\e4jFAE2.tmp_dir1720981316\i4jdel.exe | executable | |
MD5:802D1182A4685E1B86C0A9DCB3F2BE36 | SHA256:E48EF14933F4EB6071497A5311CA0AC6E115F7A0D57A60E519296F8FD42AD4FE | |||
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Local\Temp\e4jFAE2.tmp_dir1720981316\exe4jlib.jar | compressed | |
MD5:BD8451491A92B1AA5FE6D44BC9F3E1C6 | SHA256:8A416DAB7B3028F3E79B41521B65432AB2D25DEC9F85E220ADE0157BADC0DD41 | |||
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\83aa4cc77f591dfc2374580bbd95f6ba_bb926e54-e3ca-40fd-ae90-2764341e7792 | binary | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.vmoptions | text | |
MD5:616097195B6350DD5271AA6F30CC167A | SHA256:C0AD6503240446061D7DA9181B625F149574430135E0D6AB32FB61F176C831FE | |||
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Local\Temp\flatlaf.temp\flatlaf-windows-x86_64-19018588968700.dll | executable | |
MD5:DCD68A87B7E6EDBCFDE48150403B22EB | SHA256:AE3352B6AD6CFFAAE55F4387F9F5E79365EA17F8D5FB45EF11D21C3300A49A4C | |||
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Local\Temp\i4j2003957759427947516.tmp | binary | |
MD5:3776E28DBA1023ECA65CCE0E25E33131 | SHA256:C0EC0777064C06FFC89016DB8F67CC00FC9BDD8BF42ECC61828737D48A7C9850 | |||
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Local\Temp\e4jFAE2.tmp_dir1720981316\SKlauncher-3.2.jar | compressed | |
MD5:4D653E61BA01A521C56B9A70A9C9814E | SHA256:F7D3E01DCFC001CC80A988C518D4358955842D140054214D1367972C5C543350 | |||
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Local\Temp\imageio8137544499984996355.tmp | image | |
MD5:8EE50698797304540FC85117D67FE39A | SHA256:90F1E2BCC7B6C2E9B5ACBF3211ECB0B58F9E36B4F3DB56ACFC07F2A3577B644A | |||
| 1228 | java.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:9C9B43B3B7F1715EA0C5A938DA22B0A8 | SHA256:67D8182B10AA24D06C9BC9F0C247CC43190DE6348150069C6316AE1302D46041 | |||
| 4564 | SKlauncher-3.2.exe | C:\Users\admin\AppData\Local\Temp\imageio2434617287584301991.tmp | image | |
MD5:4BC22D05B225A34A3DDB4F17D2469B77 | SHA256:FACE76C9C4FAD9476A1D80483D41772C805808A1383012B1C22065E30D32EDE6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
33
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
528 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
528 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
2868 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4448 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | POST | 200 | 104.208.16.95:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
528 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 104.126.37.35:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4448 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2868 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
528 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
528 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4564 | SKlauncher-3.2.exe | 188.114.96.3:443 | files.skmedix.pl | CLOUDFLARENET | NL | unknown |
2868 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
files.skmedix.pl |
| unknown |
bitbucket.org |
| shared |
self.events.data.microsoft.com |
| whitelisted |