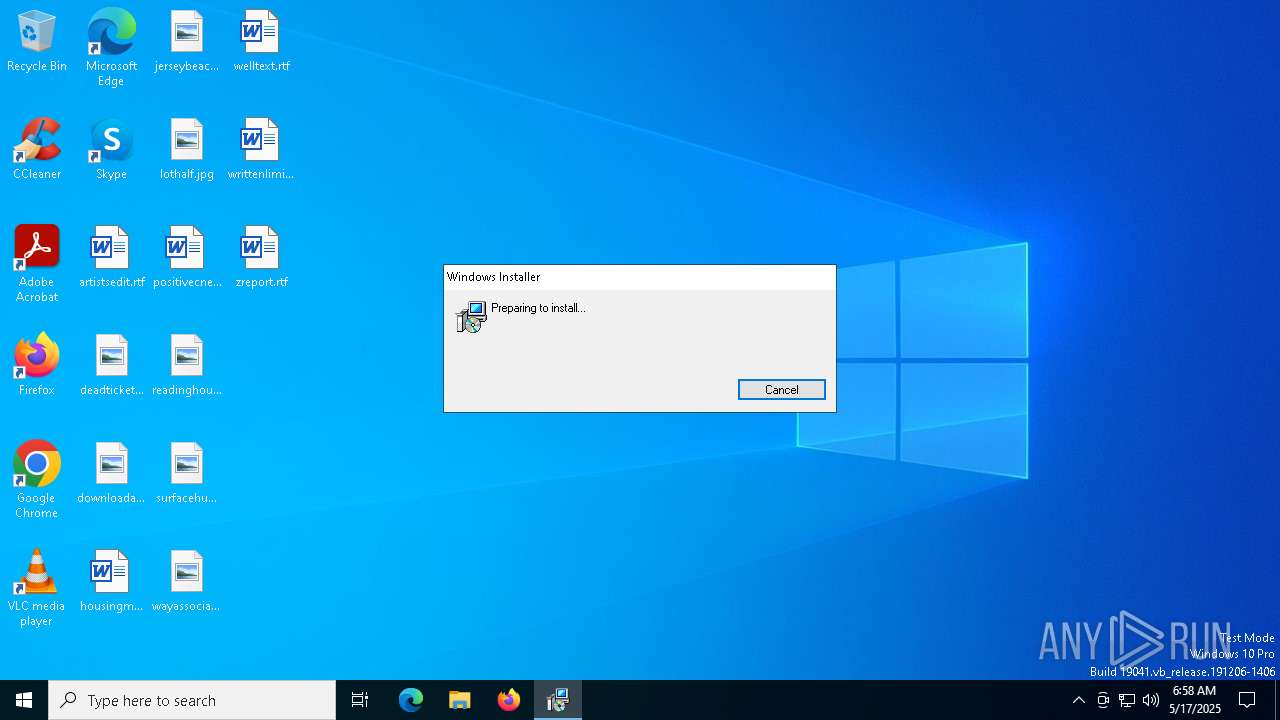
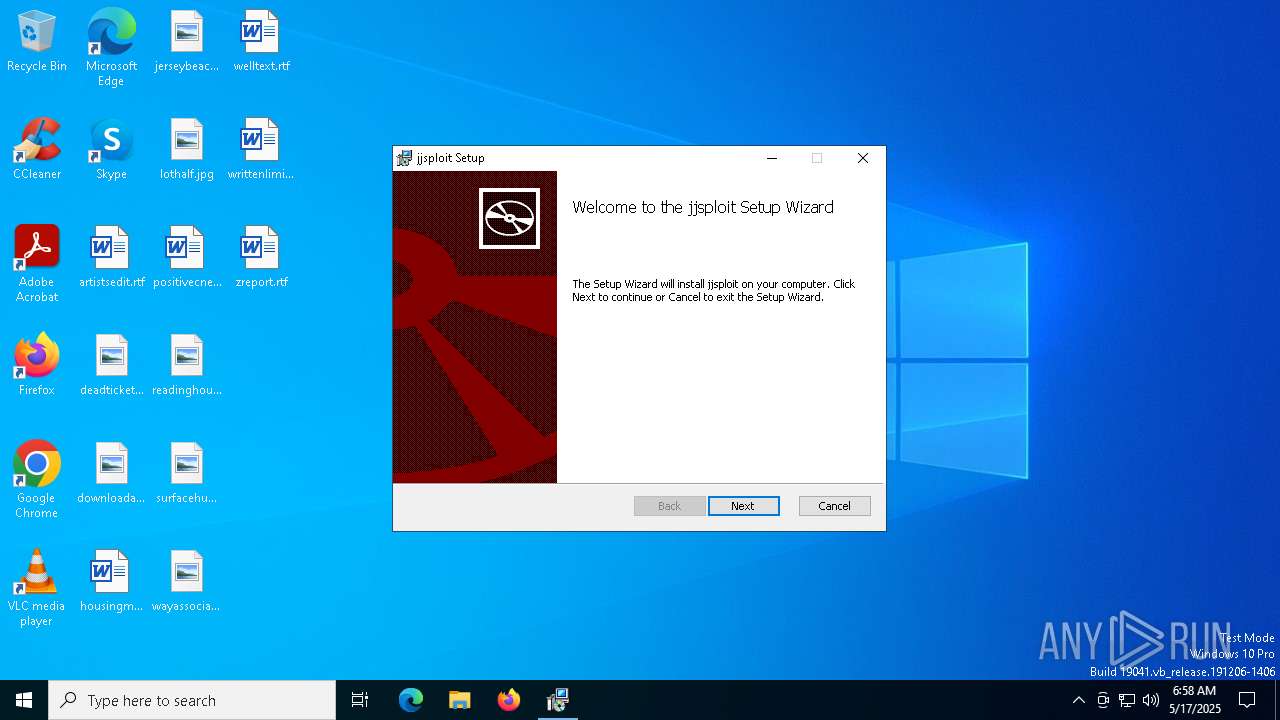
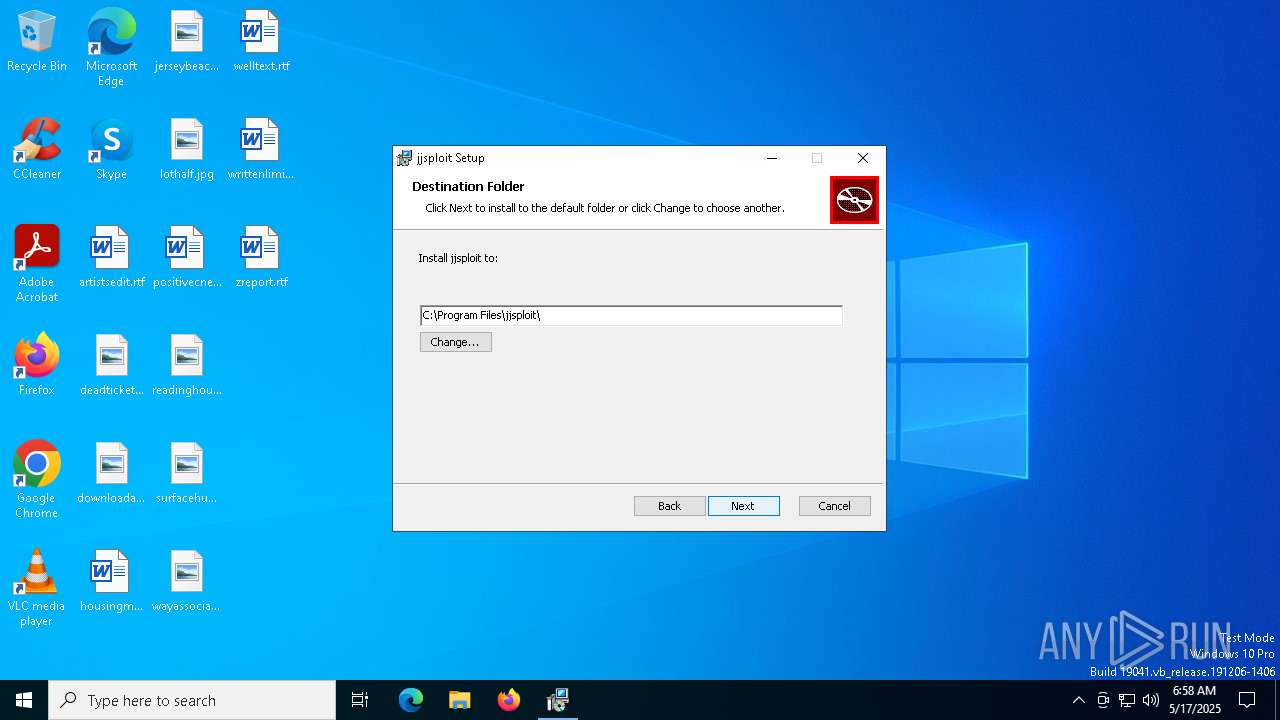
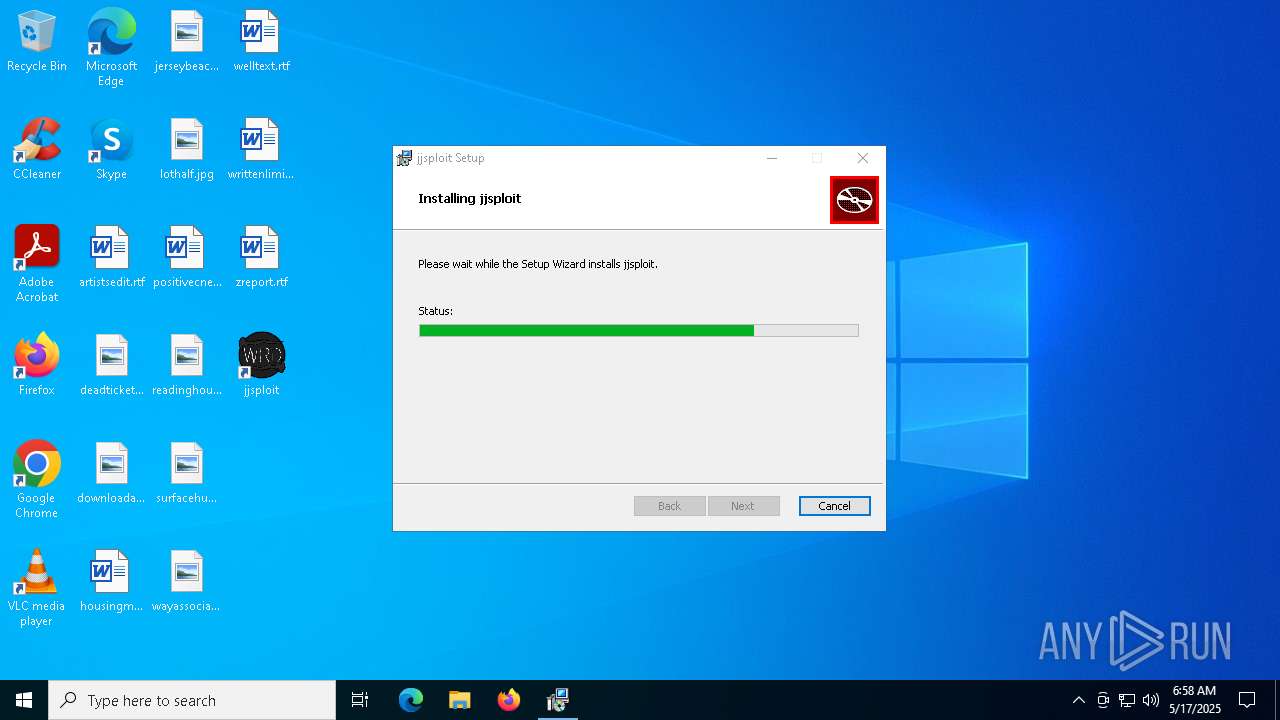
| File name: | jjsploit_8.14.4_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/82c21a8d-3a33-4f41-a801-7abbe4fae8e6 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 06:58:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: jjsploit, Author: wearedevs, Keywords: Installer, Comments: This installer database contains the logic and data required to install jjsploit., Template: x64;0, Revision Number: {78647BD7-A6F9-441C-8198-F83F1E9F555E}, Create Time/Date: Sun May 11 16:25:20 2025, Last Saved Time/Date: Sun May 11 16:25:20 2025, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | 07BFE4CEF3BE354020BBF50205ECAD9B |
| SHA1: | 286AAB63F0174A1D5B01E794AEF1E2A13786C6F0 |
| SHA256: | 05A0CC8F1FBB4A7479734159822511A534BC65766B9A01B0D01450391A7D7711 |
| SSDEEP: | 98304:HVigAXvy/XuMQNHEpW4pabtGpp9SeNbQfK4rpRkxQp6qUykuxiBZ4/6MDVYDJhND:8QC27E4MKZ1h/n |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 5892)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7912)
Downloads file from URI via Powershell
- powershell.exe (PID: 5892)
Starts process via Powershell
- powershell.exe (PID: 5892)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 7440)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 7440)
Manipulates environment variables
- powershell.exe (PID: 5892)
Executable content was dropped or overwritten
- powershell.exe (PID: 5892)
- MicrosoftEdgeUpdate.exe (PID: 7648)
- MicrosoftEdgeWebview2Setup.exe (PID: 7732)
Process drops legitimate windows executable
- powershell.exe (PID: 5892)
- MicrosoftEdgeWebview2Setup.exe (PID: 7732)
- MicrosoftEdgeUpdate.exe (PID: 7648)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 7732)
- MicrosoftEdgeUpdate.exe (PID: 7648)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 7648)
INFO
An automatically generated document
- msiexec.exe (PID: 7356)
Checks supported languages
- msiexec.exe (PID: 7440)
- msiexec.exe (PID: 7840)
Reads the computer name
- msiexec.exe (PID: 7440)
- msiexec.exe (PID: 7840)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7356)
- msiexec.exe (PID: 7440)
Manages system restore points
- SrTasks.exe (PID: 5988)
The sample compiled with english language support
- powershell.exe (PID: 5892)
- MicrosoftEdgeWebview2Setup.exe (PID: 7732)
- MicrosoftEdgeUpdate.exe (PID: 7648)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 7732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | jjsploit |
| Author: | wearedevs |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install jjsploit. |
| Template: | x64;0 |
| RevisionNumber: | {78647BD7-A6F9-441C-8198-F83F1E9F555E} |
| CreateDate: | 2025:05:11 16:25:20 |
| ModifyDate: | 2025:05:11 16:25:20 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
151
Monitored processes
19
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.59\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.59\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.59 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.59\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.59\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.59 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" -Embedding | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.59 Modules
| |||||||||||||||
| 3240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4464 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{0A8C1BB7-0C7A-41D8-AF54-9CFC0ADF9FA0}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.59 Modules
| |||||||||||||||
| 5260 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4xOTUuNTkiIHNoZWxsX3ZlcnNpb249IjEuMy4xOTUuNTkiIGlzbWFjaGluZT0iMCIgc2Vzc2lvbmlkPSJ7MEE4QzFCQjctMEM3QS00MUQ4LUFGNTQtOUNGQzBBREY5RkEwfSIgdXNlcmlkPSJ7RUJBQjVGNjItQjY0OS00MTkzLTgzNzctNEM3QUU0RDlFMjJBfSIgaW5zdGFsbHNvdXJjZT0ib3RoZXJpbnN0YWxsY21kIiByZXF1ZXN0aWQ9InsxMzk2NjZBMy0wRDUyLTRFNTctQTg3Ny02Nzc0NjNCQkE1NTV9IiBkZWR1cD0iY3IiIGRvbWFpbmpvaW5lZD0iMCI-PGh3IGxvZ2ljYWxfY3B1cz0iNCIgcGh5c21lbW9yeT0iNCIgZGlza190eXBlPSIyIiBzc2U9IjEiIHNzZTI9IjEiIHNzZTM9IjEiIHNzc2UzPSIxIiBzc2U0MT0iMSIgc3NlNDI9IjEiIGF2eD0iMSIvPjxvcyBwbGF0Zm9ybT0id2luIiB2ZXJzaW9uPSIxMC4wLjE5MDQ1LjQwNDYiIHNwPSIiIGFyY2g9Ing2NCIgcHJvZHVjdF90eXBlPSI0OCIgaXNfd2lwPSIwIiBpc19pbl9sb2NrZG93bl9tb2RlPSIwIi8-PG9lbSBwcm9kdWN0X21hbnVmYWN0dXJlcj0iREVMTCIgcHJvZHVjdF9uYW1lPSJERUxMIi8-PGV4cCBldGFnPSIiLz48YXBwIGFwcGlkPSJ7RjNDNEZFMDAtRUZENS00MDNCLTk1NjktMzk4QTIwRjFCQTRBfSIgdmVyc2lvbj0iIiBuZXh0dmVyc2lvbj0iMS4zLjE5NS41OSIgbGFuZz0iIiBicmFuZD0iIiBjbGllbnQ9IiI-PGV2ZW50IGV2ZW50dHlwZT0iMiIgZXZlbnRyZXN1bHQ9IjEiIGVycm9yY29kZT0iMCIgZXh0cmFjb2RlMT0iMCIgc3lzdGVtX3VwdGltZV90aWNrcz0iMTAwMjIzNjkzOTMiIGluc3RhbGxfdGltZV9tcz0iNTk0Ii8-PC9hcHA-PC9yZXF1ZXN0Pg | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.59 Modules
| |||||||||||||||
| 5392 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | powershell.exe -NoProfile -windowstyle hidden try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12 } catch {}; Invoke-WebRequest -Uri "https://go.microsoft.com/fwlink/p/?LinkId=2124703" -OutFile "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" ; Start-Process -FilePath "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" -ArgumentList ('/silent', '/install') -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5988 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6652 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.59\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.59\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.59 Modules
| |||||||||||||||
Total events
11 699
Read events
10 717
Write events
939
Delete events
43
Modification events
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000034309B16F9C6DB01101D0000D81E0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000034309B16F9C6DB01101D0000D81E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000005757E016F9C6DB01101D0000D81E0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000005757E016F9C6DB01101D0000D81E0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000DBBAE216F9C6DB01101D0000D81E0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000D281E716F9C6DB01101D0000D81E0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7440) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000BADA6517F9C6DB01101D0000D81E0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7912) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000D71F7417F9C6DB01E81E0000041F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7912) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000D71F7417F9C6DB01E81E0000081F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
204
Suspicious files
19
Text files
20
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7440 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7440 | msiexec.exe | C:\Windows\Installer\112632.msi | — | |
MD5:— | SHA256:— | |||
| 7356 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIDB4E.tmp | executable | |
MD5:CFBB8568BD3711A97E6124C56FCFA8D9 | SHA256:7F47D98AB25CFEA9B3A2E898C3376CC9BA1CD893B4948B0C27CAA530FD0E34CC | |||
| 7440 | msiexec.exe | C:\Program Files\jjsploit\resources\luascripts\general\fly.lua | binary | |
MD5:54A3C002B2B1E311B6488B5796094457 | SHA256:4F4098A0CCAD434E7CF4684DF559858BDDD5D17768F4C8BF89B0BED072575A47 | |||
| 7440 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{6a948cd4-201f-43a5-bcfb-b7a71b90ca79}_OnDiskSnapshotProp | binary | |
MD5:5382EB4E9B1E154DDC8D55696F83F2D4 | SHA256:78A17042CBBF23F270E57C98F13AF58FF16F0B91D03B8AE06709063BF2F2CB7C | |||
| 7440 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:CE251B83D182A8637444E2B040FF6020 | SHA256:31409F2190498358FE61AD2373AE9611B5211741BE8DA074309ED7FA39032EC6 | |||
| 7440 | msiexec.exe | C:\Program Files\jjsploit\resources\luascripts\general\god.lua | text | |
MD5:121A9CE65D07175515C986D40502F1A5 | SHA256:DBFBB0B80576AA03C66CA23D4510C5B5EB33FCA8AB2031BE75556073230DE323 | |||
| 7440 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:5382EB4E9B1E154DDC8D55696F83F2D4 | SHA256:78A17042CBBF23F270E57C98F13AF58FF16F0B91D03B8AE06709063BF2F2CB7C | |||
| 7440 | msiexec.exe | C:\Windows\Installer\MSI29CC.tmp | binary | |
MD5:11622FC6E7AC249863C75775DB9686ED | SHA256:310D5079B3AF350B2D797EE700B4D312498BFF55666F6B44B9B453829030D0EF | |||
| 7440 | msiexec.exe | C:\Windows\Temp\~DF5CD1A8E971C243F3.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
34
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8188 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1132 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6eb5dca7-2768-4016-8dbe-9762e2b79397?P1=1748069934&P2=404&P3=2&P4=WZMfzKXR6wgq%2bJMg1NRpt9Df%2b4piBrWiR6pFk2UP6BdyfklBVDXVyreA%2fP7QnvPiAhgji1BiStIPe4MpXuXT4g%3d%3d | unknown | — | — | whitelisted |
1132 | svchost.exe | GET | — | 199.232.214.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6eb5dca7-2768-4016-8dbe-9762e2b79397?P1=1748069934&P2=404&P3=2&P4=WZMfzKXR6wgq%2bJMg1NRpt9Df%2b4piBrWiR6pFk2UP6BdyfklBVDXVyreA%2fP7QnvPiAhgji1BiStIPe4MpXuXT4g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
msedge.sf.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1132 | svchost.exe | Misc activity | ET INFO Packed Executable Download |