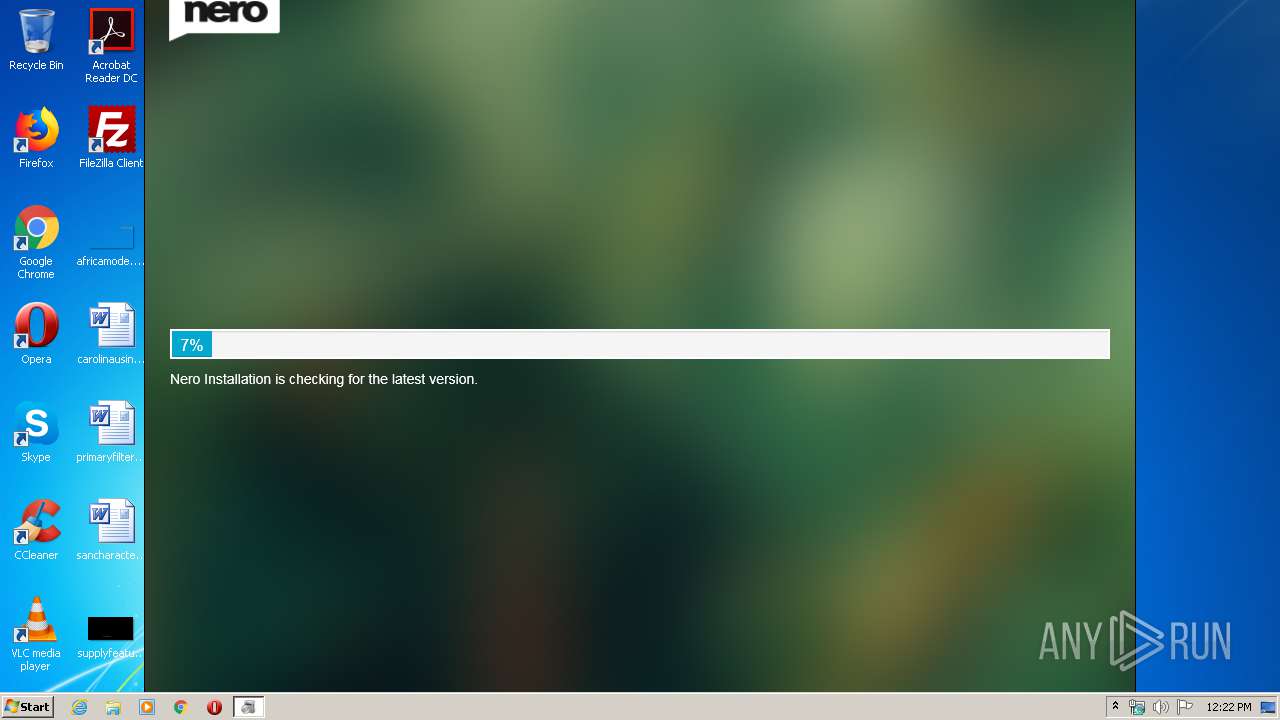
| File name: | Nero_Video-2.1.1.7_stub.exe |
| Full analysis: | https://app.any.run/tasks/3b04ccf8-dcdd-476b-abdd-178679b383a7 |
| Verdict: | Malicious activity |
| Analysis date: | May 01, 2020, 11:21:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 78DA7496580A081F1385430C5651EF1E |
| SHA1: | F77D4430BB352D1EC96D8C7670BEEF38A28DAF04 |
| SHA256: | 059CEAFAF124BE829449B5D2400FED0FA1E93F49CC41B7EBFEF81BEB4FC44C4C |
| SSDEEP: | 49152:+1Os2WaTs1jbPN6G6wgo1aBdyswBXSQhHyt0kUb4B7yhljI7qRPB:+1OnBqbFtXaBy/ytgb4BelmqRPB |
MALICIOUS
Application was dropped or rewritten from another process
- NeroInstaller.exe (PID: 3224)
Changes settings of System certificates
- NeroInstaller.exe (PID: 3224)
SUSPICIOUS
Executable content was dropped or overwritten
- Nero_Video-2.1.1.7_stub.exe (PID: 3596)
Reads Internet Cache Settings
- NeroInstaller.exe (PID: 3224)
Changes IE settings (feature browser emulation)
- NeroInstaller.exe (PID: 3224)
Creates files in the user directory
- NeroInstaller.exe (PID: 3224)
Reads internet explorer settings
- NeroInstaller.exe (PID: 3224)
Adds / modifies Windows certificates
- NeroInstaller.exe (PID: 3224)
INFO
Dropped object may contain Bitcoin addresses
- NeroInstaller.exe (PID: 3224)
Reads settings of System Certificates
- NeroInstaller.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 17:27:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 104960 |
| InitializedDataSize: | 572928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14b04 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.1.7 |
| ProductVersionNumber: | 2.1.1.7 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Nero AG |
| FileDescription: | NeroInstaller |
| FileVersion: | 2.1.1.7 |
| InternalName: | NeroInstaller.exe |
| LegalCopyright: | (c) 2015 Nero AG and its affiliates |
| OriginalFileName: | NeroInstaller.exe |
| ProductName: | NeroInstaller |
| ProductVersion: | 2.1.1.7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2010 16:27:35 |
| Detected languages: |
|
| CompanyName: | Nero AG |
| FileDescription: | NeroInstaller |
| FileVersion: | 2.1.1.7 |
| InternalName: | NeroInstaller.exe |
| LegalCopyright: | (c) 2015 Nero AG and its affiliates |
| OriginalFilename: | NeroInstaller.exe |
| ProductName: | NeroInstaller |
| ProductVersion: | 2.1.1.7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Nov-2010 16:27:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000199EA | 0x00019A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60849 |
.rdata | 0x0001B000 | 0x00004494 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.36802 |
.data | 0x00020000 | 0x00005A48 | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.37054 |
.sxdata | 0x00026000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00027000 | 0x00084348 | 0x00084400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.72423 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.35675 | 748 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 2.8195 | 10344 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.00885 | 2664 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.12043 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 1.43775 | 52 | Latin 1 / Western European | English - United States | RT_STRING |
6 | 3.33432 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.06544 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.01829 | 74792 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.21793 | 19496 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.54867 | 5672 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
42
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | "C:\Users\admin\AppData\Local\Temp\Nero_Video-2.1.1.7_stub.exe" | C:\Users\admin\AppData\Local\Temp\Nero_Video-2.1.1.7_stub.exe | — | explorer.exe | |||||||||||
User: admin Company: Nero AG Integrity Level: MEDIUM Description: NeroInstaller Exit code: 3221226540 Version: 2.1.1.7 Modules
| |||||||||||||||
| 3224 | .\NeroInstaller.exe -GMID=2020-NVTRIAL | C:\Users\admin\AppData\Local\Temp\7zSE596.tmp\NeroInstaller.exe | Nero_Video-2.1.1.7_stub.exe | ||||||||||||
User: admin Company: Nero AG Integrity Level: HIGH Description: Nero Installation Exit code: 0 Version: 2.1.1.7 Modules
| |||||||||||||||
| 3596 | "C:\Users\admin\AppData\Local\Temp\Nero_Video-2.1.1.7_stub.exe" | C:\Users\admin\AppData\Local\Temp\Nero_Video-2.1.1.7_stub.exe | explorer.exe | ||||||||||||
User: admin Company: Nero AG Integrity Level: HIGH Description: NeroInstaller Exit code: 0 Version: 2.1.1.7 Modules
| |||||||||||||||
Total events
1 405
Read events
192
Write events
1 213
Delete events
0
Modification events
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Nero\Setup |
| Operation: | write | Name: | StubInstallerSession |
Value: 0 | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | NeroInstaller.exe |
Value: 11001 | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3224) NeroInstaller.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
30
Text files
120
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\7zSE596.tmp\htmliam\Eula_Nero_en-US.htm | html | |
MD5:— | SHA256:— | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\7zSE596.tmp\htmliam\includes\nero_stub.css | text | |
MD5:— | SHA256:— | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\7zSE596.tmp\htmliam\index.html | html | |
MD5:— | SHA256:— | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\Cab14D3.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\Tar14D4.tmp | — | |
MD5:— | SHA256:— | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\UQEI0J59.txt | — | |
MD5:— | SHA256:— | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\7zSE596.tmp\htmliam\includes\sw-nero-iam.js | text | |
MD5:— | SHA256:— | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\7zSE596.tmp\htmliam\stub_background.jpg | image | |
MD5:— | SHA256:— | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\7zSE596.tmp\htmliam\includes\bootstrap\fonts\glyphicons-halflings-regular.svg | image | |
MD5:F721466883998665B87923B92DEA655B | SHA256:D985CDA034EAB4C9F2403976F8D171FBF6EFC4B593107D8B1401E5B6DAA46295 | |||
| 3224 | NeroInstaller.exe | C:\Users\admin\AppData\Local\Temp\7zSE596.tmp\htmliam\includes\bootstrap\fonts\glyphicons-halflings-regular.ttf | ttf | |
MD5:E18BBF611F2A2E43AFC071AA2F4E1512 | SHA256:E395044093757D82AFCB138957D06A1EA9361BDCF0B442D06A18A8051AF57456 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
45
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3224 | NeroInstaller.exe | HEAD | 301 | 172.217.21.238:80 | http://www.youtube.com/ | US | — | — | whitelisted |
3224 | NeroInstaller.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8DYx | US | der | 1.49 Kb | whitelisted |
3224 | NeroInstaller.exe | HEAD | 301 | 172.217.21.238:80 | http://www.youtube.com/ | US | — | — | whitelisted |
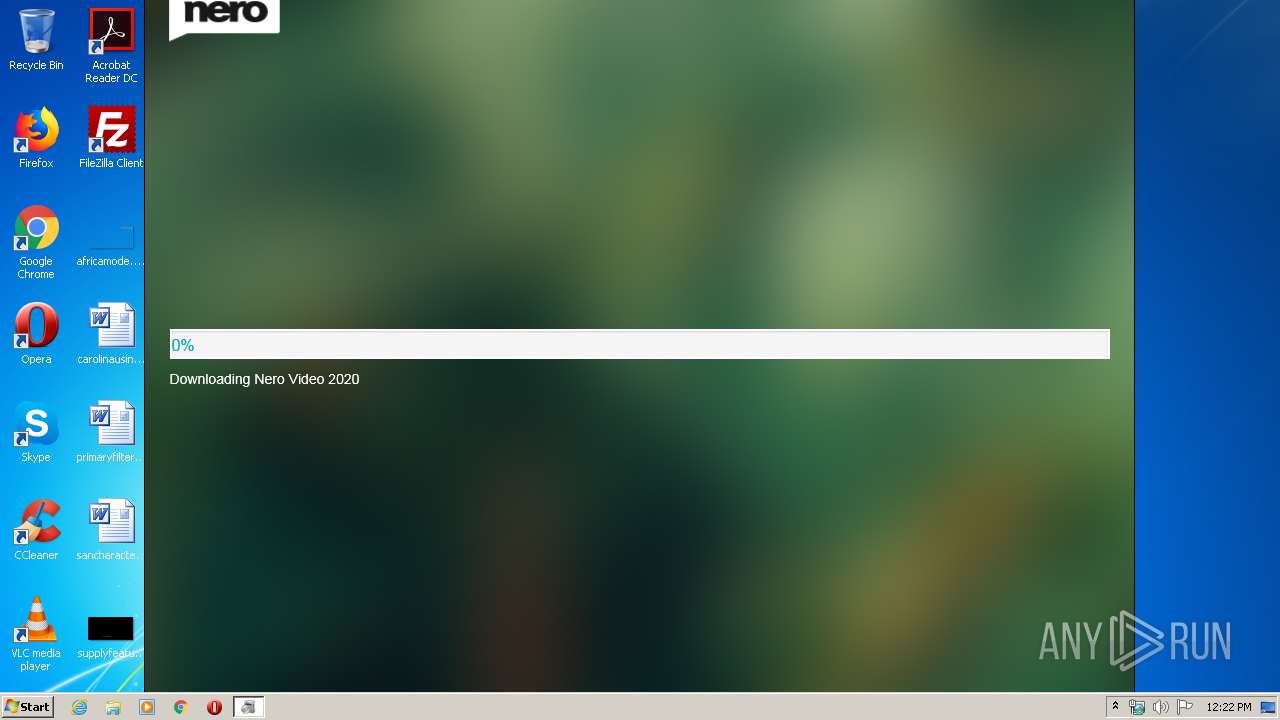
3224 | NeroInstaller.exe | GET | 200 | 209.239.121.96:80 | http://ftp20.us.nero.com/stubinfo/stubinstaller_paid/MinVersion.txt | US | text | 7 b | suspicious |
3224 | NeroInstaller.exe | HEAD | 301 | 172.217.21.238:80 | http://www.youtube.com/ | US | — | — | whitelisted |
3224 | NeroInstaller.exe | GET | 200 | 209.239.121.96:80 | http://ftp20.us.nero.com/stubinfo/2020-NVTRIAL/NeroInstaller2.xml | US | xml | 559 b | suspicious |
3224 | NeroInstaller.exe | GET | 200 | 209.239.121.96:80 | http://ftp20.us.nero.com/stubinfo/2020-NVTRIAL-22.0.00700/NeroInstaller2.xml | US | xml | 1.00 Kb | suspicious |
3224 | NeroInstaller.exe | GET | 200 | 209.239.121.96:80 | http://ftp20.us.nero.com/stubinfo/2019-EULA/NeroInstaller2.hash | US | text | 256 b | suspicious |
3224 | NeroInstaller.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsalphasha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSE1Wv4CYvTB7dm2OHrrWWWqmtnYQQU9c3VPAhQ%2BWpPOreX2laD5mnSaPcCDEuxMmKXwp5fNwVRlA%3D%3D | US | der | 1.49 Kb | whitelisted |
3224 | NeroInstaller.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDRK%2F8FyaXbFAgAAAABiBxA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 209.239.121.96:80 | ftp20.us.nero.com | server4you Inc. | US | suspicious |
3224 | NeroInstaller.exe | 172.217.21.238:80 | www.youtube.com | Google Inc. | US | whitelisted |
3224 | NeroInstaller.exe | 172.217.21.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
3224 | NeroInstaller.exe | 216.58.206.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3224 | NeroInstaller.exe | 216.58.205.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
3224 | NeroInstaller.exe | 172.217.22.35:443 | www.google.no | Google Inc. | US | whitelisted |
3224 | NeroInstaller.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
3224 | NeroInstaller.exe | 209.239.121.96:80 | ftp20.us.nero.com | server4you Inc. | US | suspicious |
3224 | NeroInstaller.exe | 151.101.130.217:443 | cdn.ravenjs.com | Fastly | US | suspicious |
3224 | NeroInstaller.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
i2am.nero.com |
| unknown |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
www.nero.com |
| suspicious |
ftp20.us.nero.com |
| suspicious |
www.youtube.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3224 | NeroInstaller.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |