| download: | pwbreg.exe |
| Full analysis: | https://app.any.run/tasks/a0fdd42b-548f-4caf-ad05-c01eac6d6d12 |
| Verdict: | Malicious activity |
| Analysis date: | May 08, 2019, 10:54:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 281CB68EB153BD695A0DAC6A914578CB |
| SHA1: | 9F7B4B2A65F8E7AFE107FBDE3DACA732ECAF6E02 |
| SHA256: | 058AA4788D86EA43515B7A0D28604F64164289BE6FE0B70ED9895F5EF2BBC353 |
| SSDEEP: | 98304:FsAqEnjMTtOU9GOY7ccHB8r++ClpdlMuRAflH/YD2C:uA5j2vOckLEuIx/Yp |
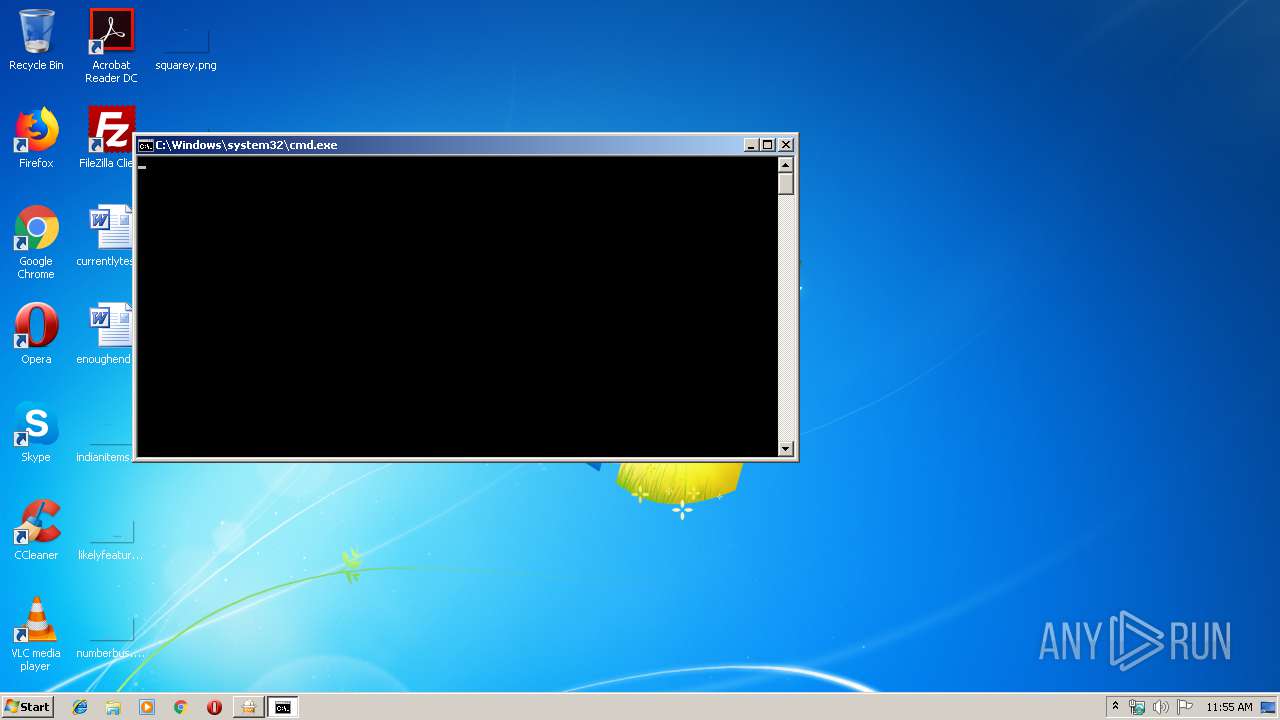
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 3132)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3944)
- WerFault.exe (PID: 2732)
SUSPICIOUS
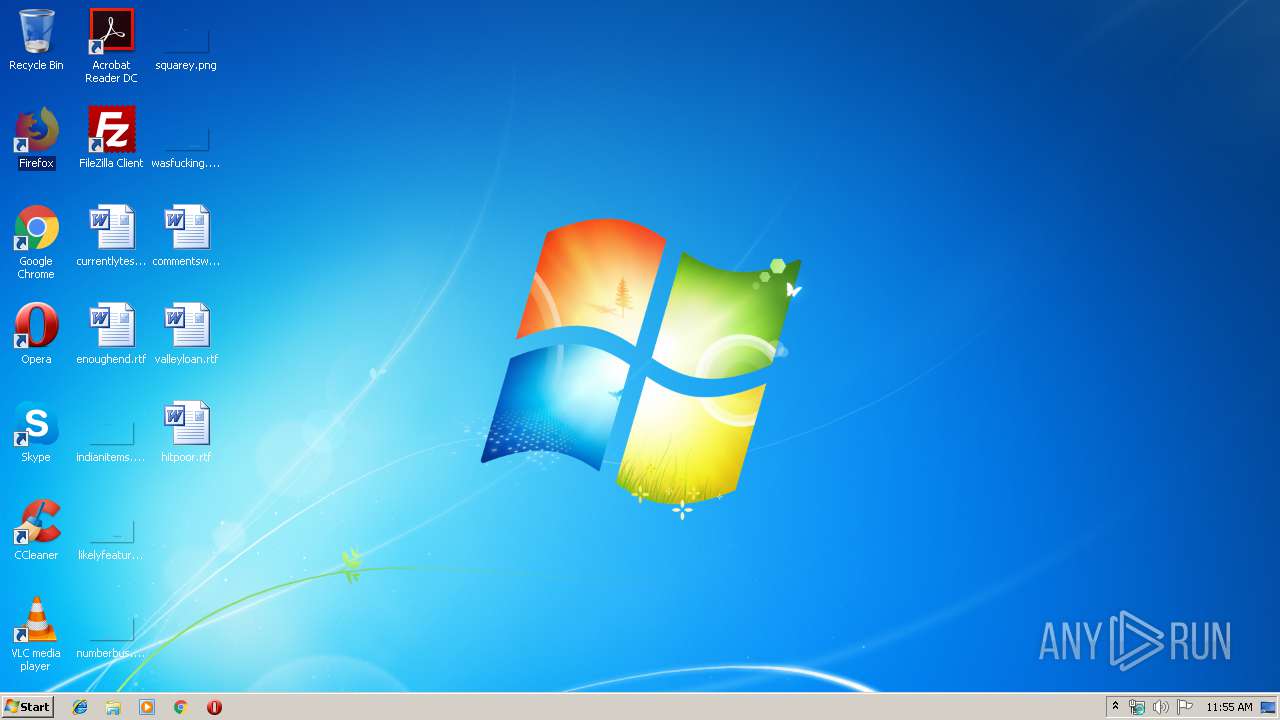
Creates files in the Windows directory
- pwbreg.exe (PID: 3816)
Starts CMD.EXE for commands execution
- pwbreg.exe (PID: 3816)
Application launched itself
- pwbreg.exe (PID: 916)
Executable content was dropped or overwritten
- pwbreg.exe (PID: 3816)
Creates COM task schedule object
- regsvr32.exe (PID: 3944)
Creates files in the program directory
- WerFault.exe (PID: 2732)
INFO
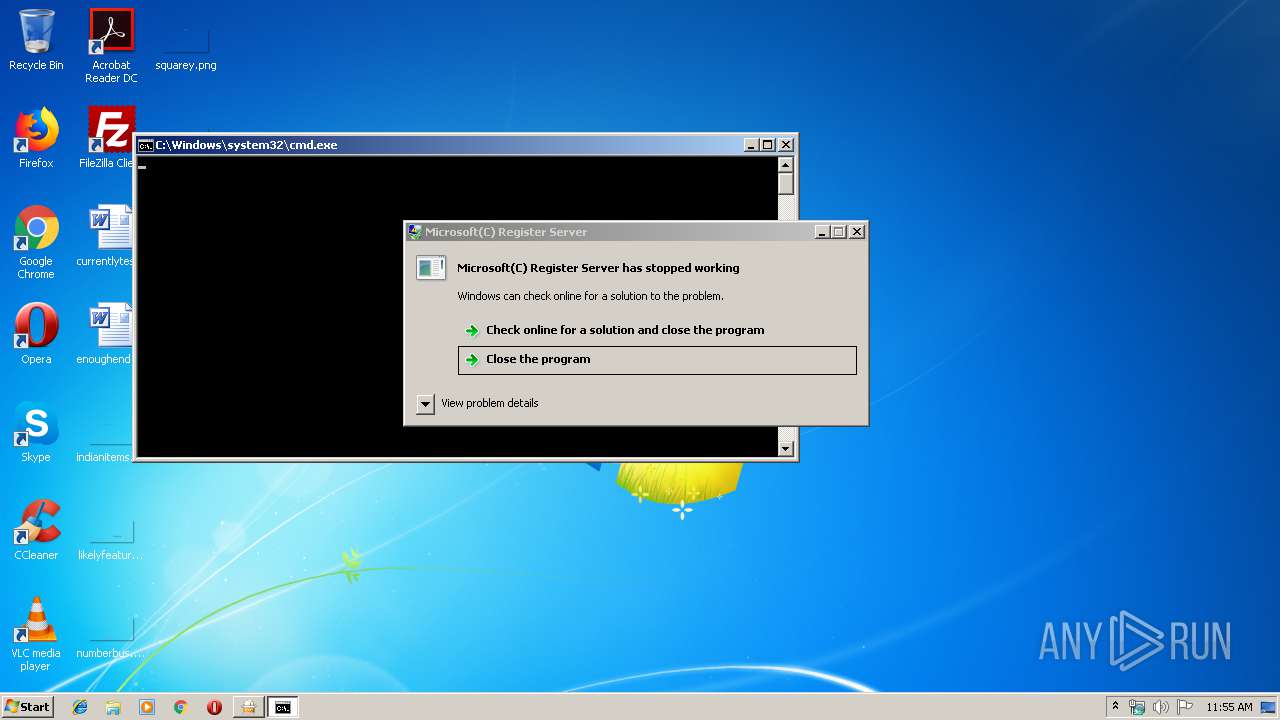
Application was crashed
- regsvr32.exe (PID: 3944)
Dropped object may contain Bitcoin addresses
- WerFault.exe (PID: 2732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:03:28 16:46:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 180224 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | 348160 |
| EntryPoint: | 0x81a10 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.3.28.0 |
| ProductVersionNumber: | 10.3.28.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Unicode |
| CompanyName: | ESTsoft Corp. |
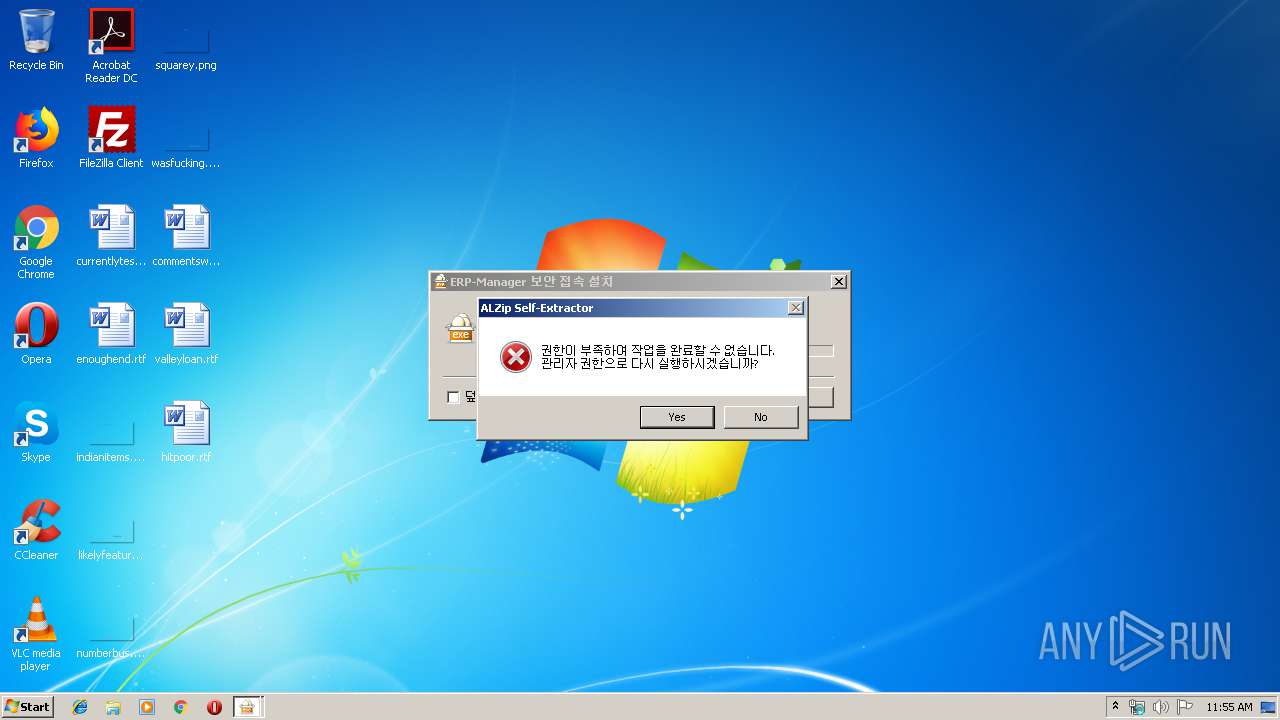
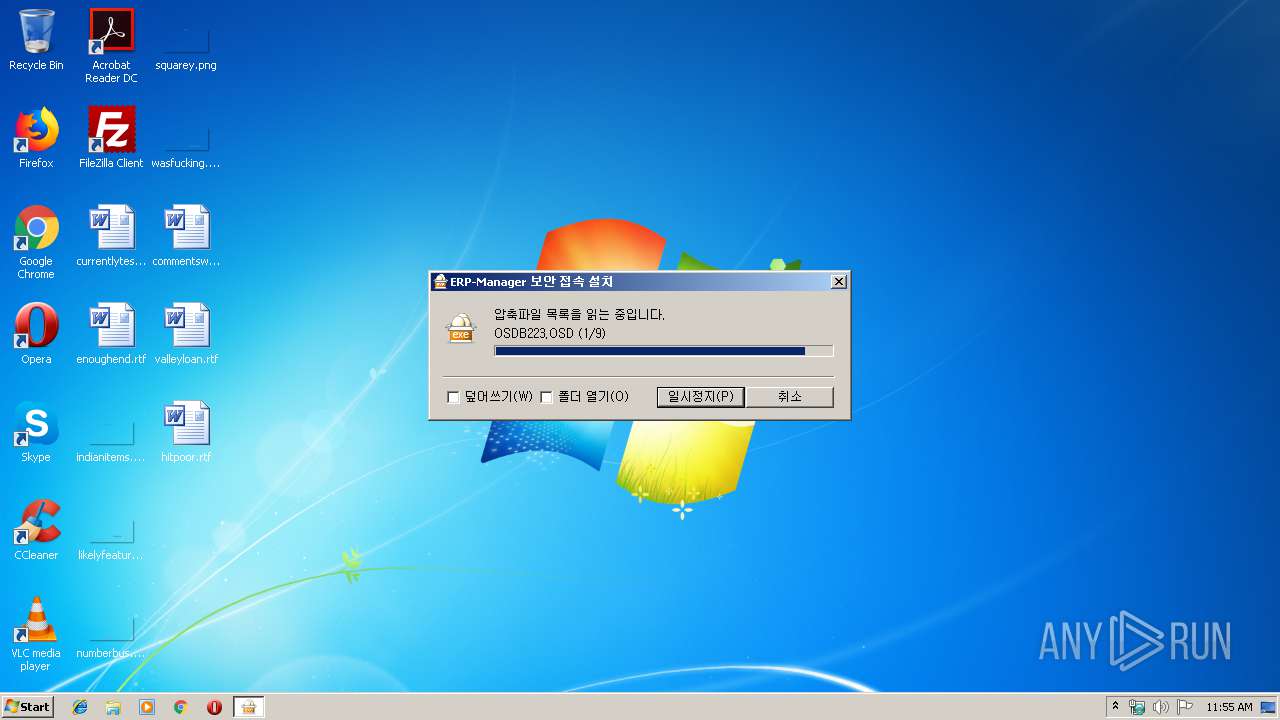
| FileDescription: | ALZip SFX |
| FileVersion: | 10, 3, 28, 0 |
| InternalName: | ALZip SFX |
| LegalCopyright: | Copyright (C) 2010 by ESTsoft Corp. |
| ProductName: | ALZip |
| ProductVersion: | 10, 3, 28, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Mar-2010 14:46:16 |
| Detected languages: |
|
| CompanyName: | ESTsoft Corp. |
| FileDescription: | ALZip SFX |
| FileVersion: | 10, 3, 28, 0 |
| InternalName: | ALZip SFX |
| LegalCopyright: | Copyright (C) 2010 by ESTsoft Corp. |
| ProductName: | ALZip |
| ProductVersion: | 10, 3, 28, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 28-Mar-2010 14:46:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00055000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00056000 | 0x0002C000 | 0x0002BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92874 |
.rsrc | 0x00082000 | 0x0000E000 | 0x0000DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.03163 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02301 | 622 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.95916 | 2216 | Latin 1 / Western European | Korean - Korea | RT_ICON |
3 | 3.26596 | 1384 | Latin 1 / Western European | Korean - Korea | RT_ICON |
4 | 7.97042 | 31136 | Latin 1 / Western European | Korean - Korea | RT_ICON |
5 | 4.71021 | 9640 | Latin 1 / Western European | Korean - Korea | RT_ICON |
6 | 4.85769 | 4264 | Latin 1 / Western European | Korean - Korea | RT_ICON |
7 | 7.30274 | 386 | Latin 1 / Western European | Korean - Korea | RT_STRING |
8 | 7.18322 | 336 | Latin 1 / Western European | Korean - Korea | RT_STRING |
9 | 7.12074 | 346 | Latin 1 / Western European | Korean - Korea | RT_STRING |
10 | 7.50279 | 610 | Latin 1 / Western European | Korean - Korea | RT_STRING |
Imports
COMDLG32.dll |
KERNEL32.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
41
Monitored processes
5
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Users\admin\AppData\Local\Temp\pwbreg.exe" | C:\Users\admin\AppData\Local\Temp\pwbreg.exe | — | explorer.exe | |||||||||||
User: admin Company: ESTsoft Corp. Integrity Level: MEDIUM Description: ALZip SFX Exit code: 1 Version: 10, 3, 28, 0 Modules
| |||||||||||||||
| 2732 | C:\Windows\system32\WerFault.exe -u -p 3944 -s 324 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3132 | cmd /c ""C:\Windows\System32\pwbreg.bat" pwbreg.bat" | C:\Windows\system32\cmd.exe | — | pwbreg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221226356 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3816 | "C:\Users\admin\AppData\Local\Temp\pwbreg.exe" | C:\Users\admin\AppData\Local\Temp\pwbreg.exe | pwbreg.exe | ||||||||||||
User: admin Company: ESTsoft Corp. Integrity Level: HIGH Description: ALZip SFX Exit code: 1 Version: 10, 3, 28, 0 Modules
| |||||||||||||||
| 3944 | regsvr32 /s psdwc110.dll | C:\Windows\system32\regsvr32.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3221226356 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
524
Read events
451
Write events
73
Delete events
0
Modification events
| (PID) Process: | (916) pwbreg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (916) pwbreg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3816) pwbreg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3816) pwbreg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3944) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\FontSubstitutes |
| Operation: | write | Name: | PB Sans Serif |
Value: Tahoma | |||
| (PID) Process: | (3944) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{BBBB1500-BBBB-1000-8000-080009AC61A9}\1.0 |
| Operation: | write | Name: | |
Value: Powersoft DataWindow Web Control | |||
| (PID) Process: | (3944) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{BBBB1500-BBBB-1000-8000-080009AC61A9}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 2 | |||
| (PID) Process: | (3944) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{BBBB1500-BBBB-1000-8000-080009AC61A9}\1.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\Windows\system32\psdwc110.dll | |||
| (PID) Process: | (3944) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{BBBB1500-BBBB-1000-8000-080009AC61A9}\1.0\HELPDIR |
| Operation: | write | Name: | |
Value: C:\Windows\system32 | |||
| (PID) Process: | (3944) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{BBBB1501-BBBB-1000-8000-080009AC61A9} |
| Operation: | write | Name: | |
Value: _DPSDWC | |||
Executable files
6
Suspicious files
1
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3816 | pwbreg.exe | C:\Windows\System32\OSDB223.OSD | xml | |
MD5:— | SHA256:— | |||
| 2732 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_regsvr32.exe_cf5c8d4b7b6dd82a7a4de3593c77fb076aa80de_0aa2a94b\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2732 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\regsvr32.exe.3944.dmp | dmp | |
MD5:— | SHA256:— | |||
| 3816 | pwbreg.exe | C:\Windows\System32\PowerBuilder DW Control & JDBC.osd | xml | |
MD5:— | SHA256:— | |||
| 3816 | pwbreg.exe | C:\Windows\System32\pwbreg.bat | text | |
MD5:— | SHA256:— | |||
| 3816 | pwbreg.exe | C:\Windows\System32\PSDWC110.DLL | executable | |
MD5:— | SHA256:— | |||
| 3816 | pwbreg.exe | C:\Windows\System32\mfc71u.dll | executable | |
MD5:7B93C623333F121DC9E689CCB1B7A733 | SHA256:0C58F682E1B3AF064963DD616E80609006E9317F2FCB0F3A51ED32FEF13B1081 | |||
| 3816 | pwbreg.exe | C:\Windows\System32\atl71.dll | executable | |
MD5:8F2097E8B174F38178570C611464935F | SHA256:3F25E7B097B65EAF82A6D5B58646DFF38CA19347664F40C2B8A409B9D6939457 | |||
| 3816 | pwbreg.exe | C:\Windows\System32\msvcr71.dll | executable | |
MD5:86F1895AE8C5E8B17D99ECE768A70732 | SHA256:8094AF5EE310714CAEBCCAEEE7769FFB08048503BA478B879EDFEF5F1A24FEFE | |||
| 3816 | pwbreg.exe | C:\Windows\System32\gdiplus.dll | executable | |
MD5:84637D0DDEF17005967A8E0856E99A75 | SHA256:9E99A5763796015D46914D279EB823F318D94E0EBD1BB5515A8133C703A8979D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report