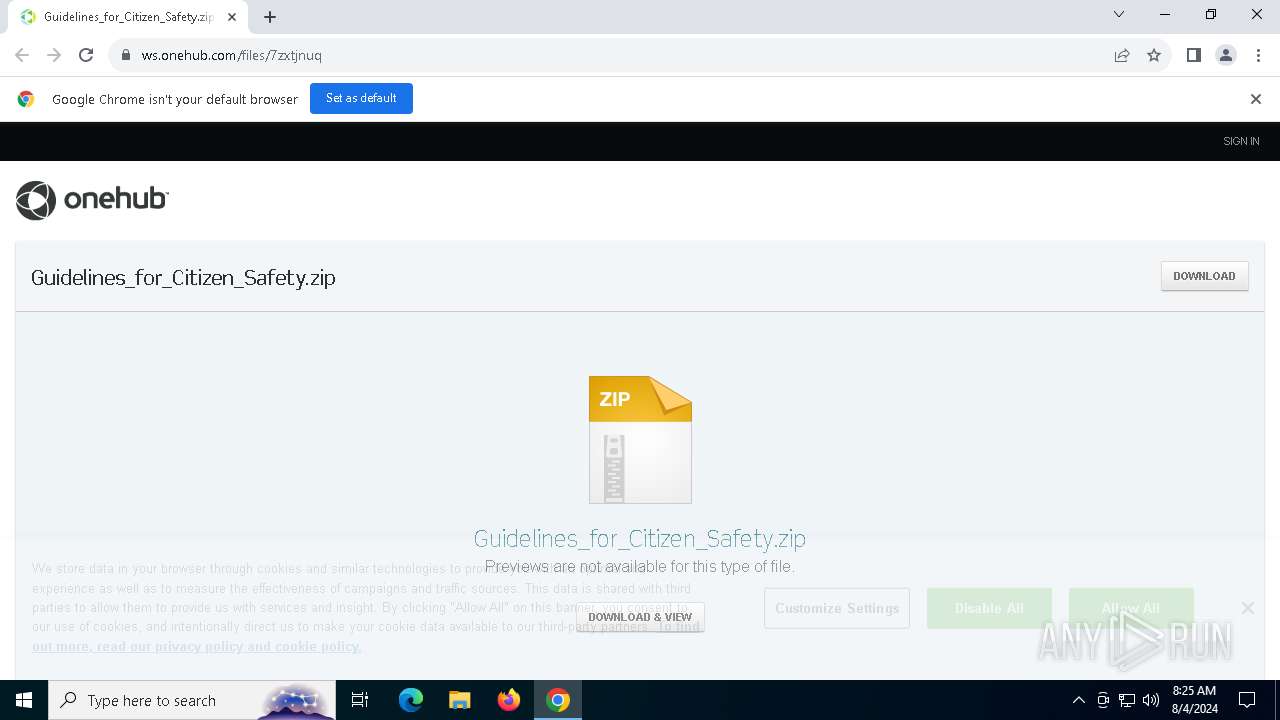
| URL: | https://ws.onehub.com/files/7zxtjnuq |
| Full analysis: | https://app.any.run/tasks/0b627ae5-25d7-472f-9c97-4a0558d52b84 |
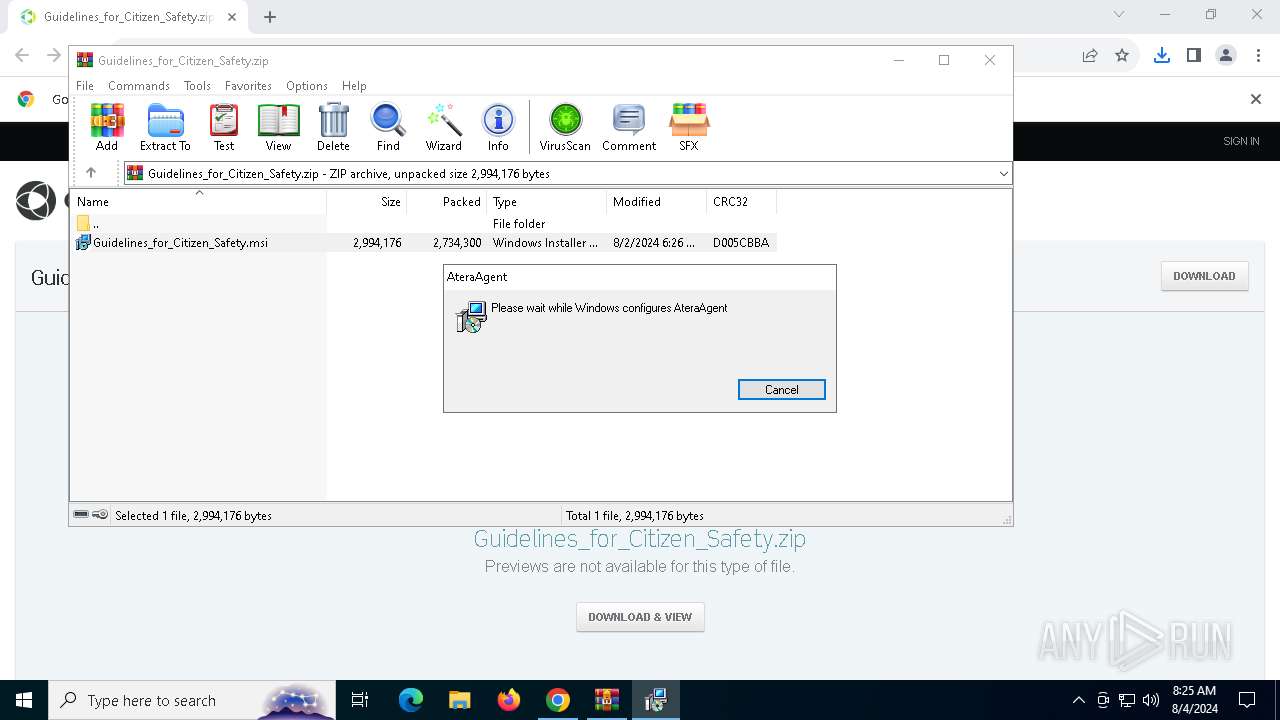
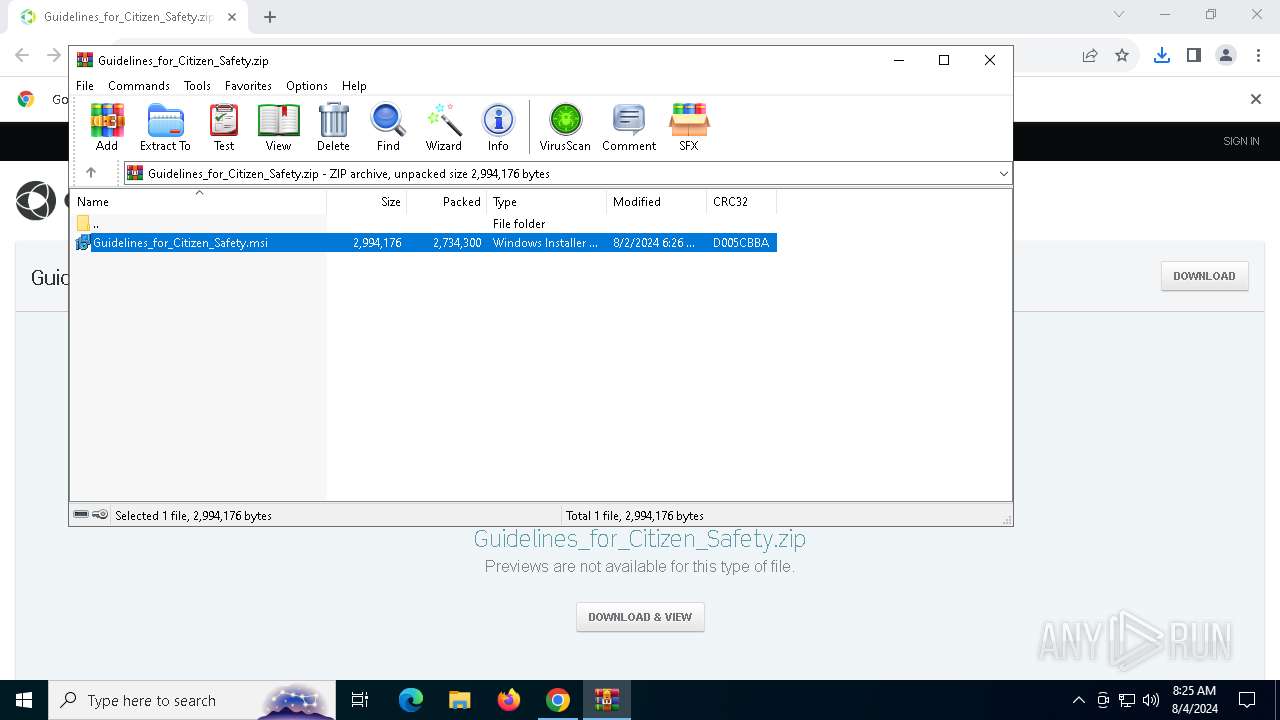
| Verdict: | Malicious activity |
| Analysis date: | August 04, 2024, 08:25:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
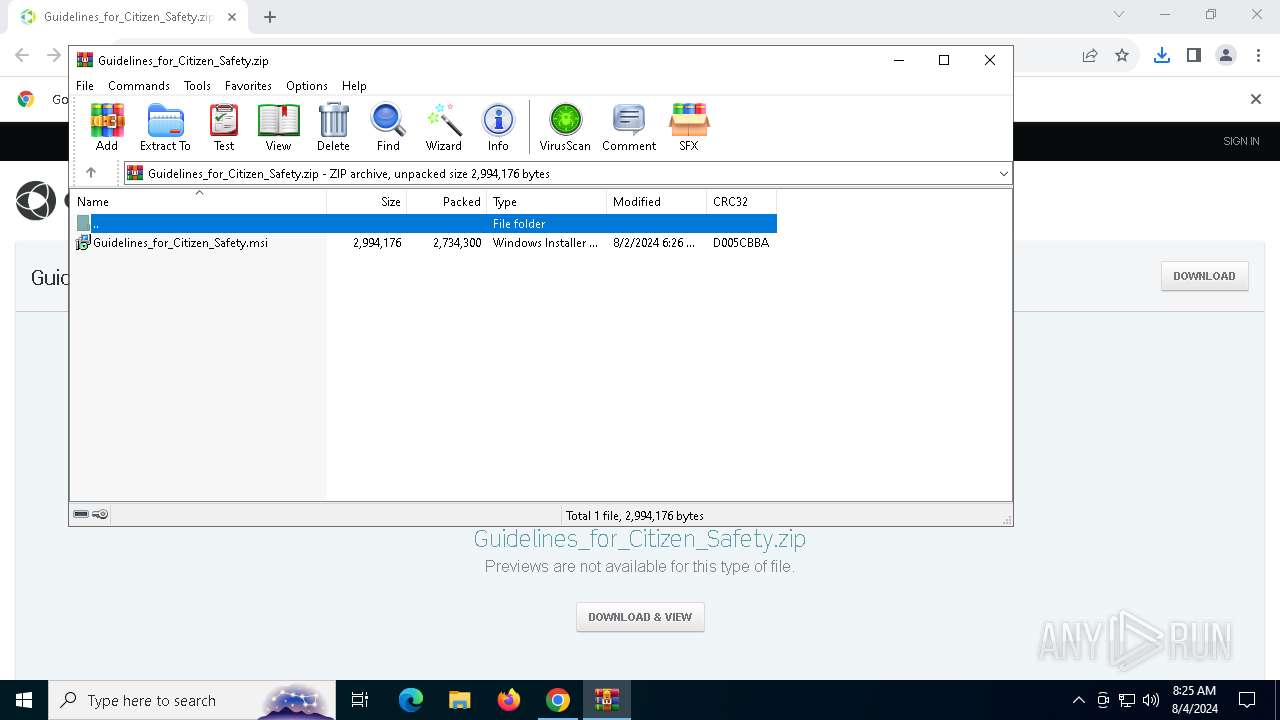
| MD5: | 25FAB596E4D150DBFCF0E0C598F396BB |
| SHA1: | C42505A9CC80F609257C5D570116E4CEB7C0562B |
| SHA256: | 0587C982FEC464D35A724701C4C756468E78E95596B844586ADAF7EA686D3D3C |
| SSDEEP: | 3:N8H5EyU0KSbPdn:2WyFd |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 8048)
- AteraAgent.exe (PID: 5984)
Starts NET.EXE for service management
- msiexec.exe (PID: 7660)
- net.exe (PID: 7968)
Changes powershell execution policy (Bypass)
- AgentPackageAgentInformation.exe (PID: 3812)
- AgentPackageAgentInformation.exe (PID: 6008)
Bypass execution policy to execute commands
- powershell.exe (PID: 8612)
- powershell.exe (PID: 8736)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 7752)
- WinRAR.exe (PID: 7928)
- msiexec.exe (PID: 8048)
- rundll32.exe (PID: 7840)
- rundll32.exe (PID: 7796)
- rundll32.exe (PID: 2128)
- rundll32.exe (PID: 7864)
- AteraAgent.exe (PID: 5984)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7928)
Executes as Windows Service
- VSSVC.exe (PID: 8100)
- AteraAgent.exe (PID: 5984)
- AteraAgent.exe (PID: 7860)
Checks Windows Trust Settings
- msiexec.exe (PID: 8048)
Executable content was dropped or overwritten
- rundll32.exe (PID: 7796)
- rundll32.exe (PID: 7840)
- rundll32.exe (PID: 2128)
- rundll32.exe (PID: 7864)
- AteraAgent.exe (PID: 5984)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 7660)
Starts SC.EXE for service management
- AteraAgent.exe (PID: 5984)
- AteraAgent.exe (PID: 7860)
Starts CMD.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 6008)
- AgentPackageAgentInformation.exe (PID: 3812)
The process executes VB scripts
- cmd.exe (PID: 1528)
- cmd.exe (PID: 7700)
Executes application which crashes
- cscript.exe (PID: 5092)
- cscript.exe (PID: 2476)
Starts POWERSHELL.EXE for commands execution
- AgentPackageAgentInformation.exe (PID: 3812)
- AgentPackageAgentInformation.exe (PID: 6008)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 6296)
- WinRAR.exe (PID: 7928)
Executable content was dropped or overwritten
- chrome.exe (PID: 7752)
- WinRAR.exe (PID: 7928)
- msiexec.exe (PID: 8048)
The process uses the downloaded file
- chrome.exe (PID: 7828)
- chrome.exe (PID: 6296)
- WinRAR.exe (PID: 7928)
Drops the executable file immediately after the start
- chrome.exe (PID: 7752)
- WinRAR.exe (PID: 7928)
- rundll32.exe (PID: 7796)
- rundll32.exe (PID: 7840)
- rundll32.exe (PID: 2128)
- rundll32.exe (PID: 7864)
Checks proxy server information
- msiexec.exe (PID: 7984)
Creates files or folders in the user directory
- msiexec.exe (PID: 7984)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7984)
Application launched itself
- chrome.exe (PID: 6296)
Reads the software policy settings
- msiexec.exe (PID: 7984)
- msiexec.exe (PID: 8048)
Checks supported languages
- msiexec.exe (PID: 8048)
Reads the machine GUID from the registry
- msiexec.exe (PID: 8048)
Reads the computer name
- msiexec.exe (PID: 8048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
60
Malicious processes
2
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1528 | "C:\Windows\System32\cmd.exe" /c cscript "C:\Program Files\Microsoft Office\Office16\ospp.vbs" /dstatus | C:\Windows\System32\cmd.exe | — | AgentPackageAgentInformation.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1664 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe" /i /IntegratorLogin="pitter.holand@emailband.com" /CompanyId="1" /IntegratorLoginUI="" /CompanyIdUI="" /FolderId="" /AccountId="001Q300000KtKx3IAF" /AgentId="26f36a07-4347-4468-82b3-b172d6734c40" | C:\Program Files (x86)\ATERA Networks\AteraAgent\AteraAgent.exe | — | msiexec.exe | |||||||||||
User: admin Company: ATERA Networks Ltd. Integrity Level: MEDIUM Description: AteraAgent Exit code: 0 Version: 1.8.7.2 | |||||||||||||||
| 2128 | rundll32.exe "C:\WINDOWS\Installer\MSIFD2A.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_982359 10 AlphaControlAgentInstallation!AlphaControlAgentInstallation.CustomActions.ShouldContinueInstallation | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4536 --field-trial-handle=1908,i,9780813108327962032,12567658151246236467,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2476 | cscript "C:\Program Files\Microsoft Office\Office16\ospp.vbs" /dstatus | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft ® Console Based Script Host Exit code: 3221225477 Version: 5.812.10240.16384 | |||||||||||||||
| 2508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | "TaskKill.exe" /f /im AteraAgent.exe | C:\Windows\SysWOW64\taskkill.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AgentPackageAgentInformation.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3324 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe" 26f36a07-4347-4468-82b3-b172d6734c40 "29afef52-586c-4eb9-827e-4d9dc4da36ca" agent-api.atera.com/Production 443 or8ixLi90Mf "minimalIdentification" 001Q300000KtKx3IAF | C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe | — | AteraAgent.exe | |||||||||||
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageAgentInformation Exit code: 0 Version: 37.2.0.0 | |||||||||||||||
| 3812 | "C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe" 26f36a07-4347-4468-82b3-b172d6734c40 "f4471848-d18e-4abe-9224-a20d8b2cafcd" agent-api.atera.com/Production 443 or8ixLi90Mf "generalinfo fromGui" 001Q300000KtKx3IAF | C:\Program Files (x86)\ATERA Networks\AteraAgent\Packages\AgentPackageAgentInformation\AgentPackageAgentInformation.exe | — | AteraAgent.exe | |||||||||||
User: SYSTEM Company: Atera Networks Integrity Level: SYSTEM Description: AgentPackageAgentInformation Version: 37.2.0.0 | |||||||||||||||
Total events
18 909
Read events
18 704
Write events
195
Delete events
10
Modification events
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6296) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
58
Suspicious files
86
Text files
38
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe5cf0.TMP | — | |
MD5:— | SHA256:— | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe5cf0.TMP | — | |
MD5:— | SHA256:— | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFe5ddb.TMP | text | |
MD5:390E3C6EDCE7036BB6F52670DC24ABAD | SHA256:D6F1B47CD05A8E1FAD989DEEC22ED67EA9A013C2DE0CCAFD68A539F69BD0DD70 | |||
| 6296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:A95974F48FC4A0E16E9D7729D7874157 | SHA256:926422473F59B7759EA8EB2064FD6DF9D00A88B548DEF1D5C3E08860357C03A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
66
DNS requests
46
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5292 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7984 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAooSZl45YmN9AojjrilUug%3D | unknown | — | — | whitelisted |
7984 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
2584 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7984 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAooSZl45YmN9AojjrilUug%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4780 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2092 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6564 | chrome.exe | 54.173.137.115:443 | ws.onehub.com | AMAZON-AES | US | unknown |
6296 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6564 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
6564 | chrome.exe | 104.18.14.62:443 | cookie-cdn.cookiepro.com | CLOUDFLARENET | — | unknown |
6564 | chrome.exe | 108.138.24.85:443 | dp0qkd77b9xjk.cloudfront.net | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ws.onehub.com |
| whitelisted |
accounts.google.com |
| whitelisted |
cookie-cdn.cookiepro.com |
| whitelisted |
dp0qkd77b9xjk.cloudfront.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
geolocation.onetrust.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
js-agent.newrelic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6564 | chrome.exe | Misc activity | ET INFO File Sharing Service Related Domain in DNS Lookup (ws .onehub .com) |
6564 | chrome.exe | Misc activity | ET INFO File Sharing Service Related Domain in DNS Lookup (ws .onehub .com) |
6564 | chrome.exe | Misc activity | ET INFO Observed File Sharing Service Related Domain (ws .onehub .com in TLS SNI) |
6564 | chrome.exe | Misc activity | ET INFO Observed File Sharing Service Related Domain (ws .onehub .com in TLS SNI) |
6564 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6564 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6564 | chrome.exe | Misc activity | ET INFO Observed File Sharing Service Related Domain (ws .onehub .com in TLS SNI) |
19 ETPRO signatures available at the full report