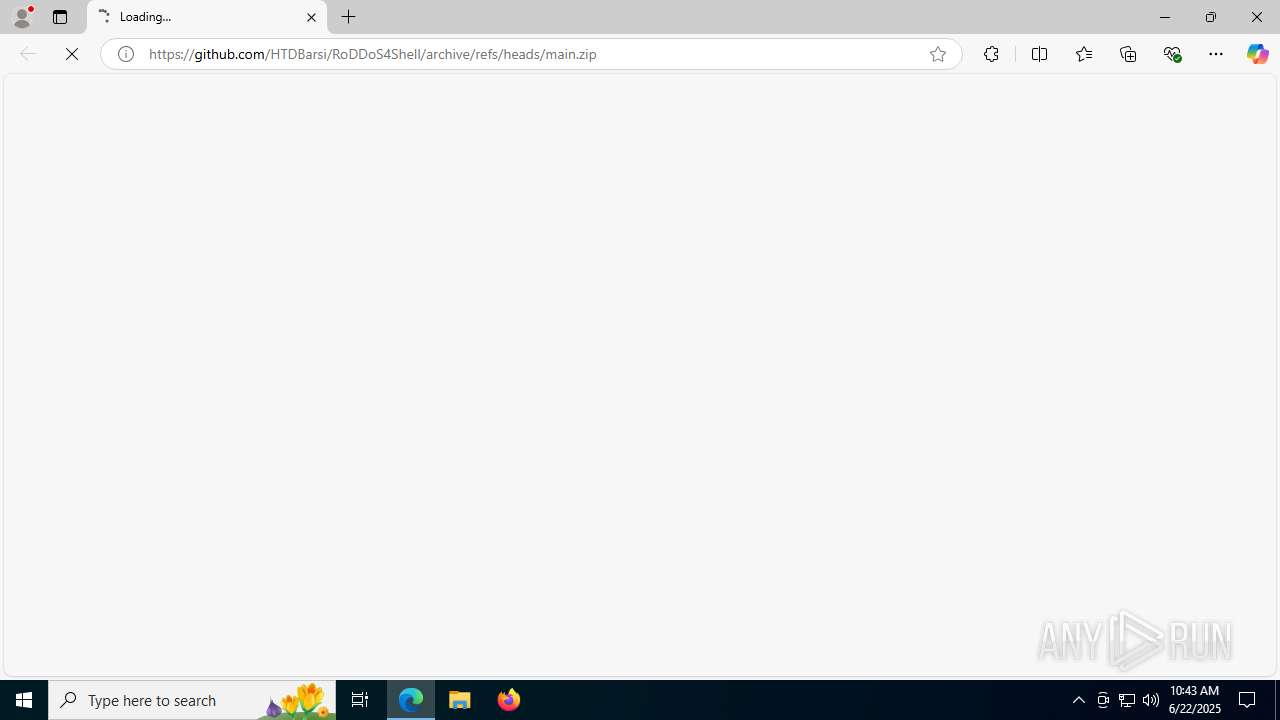
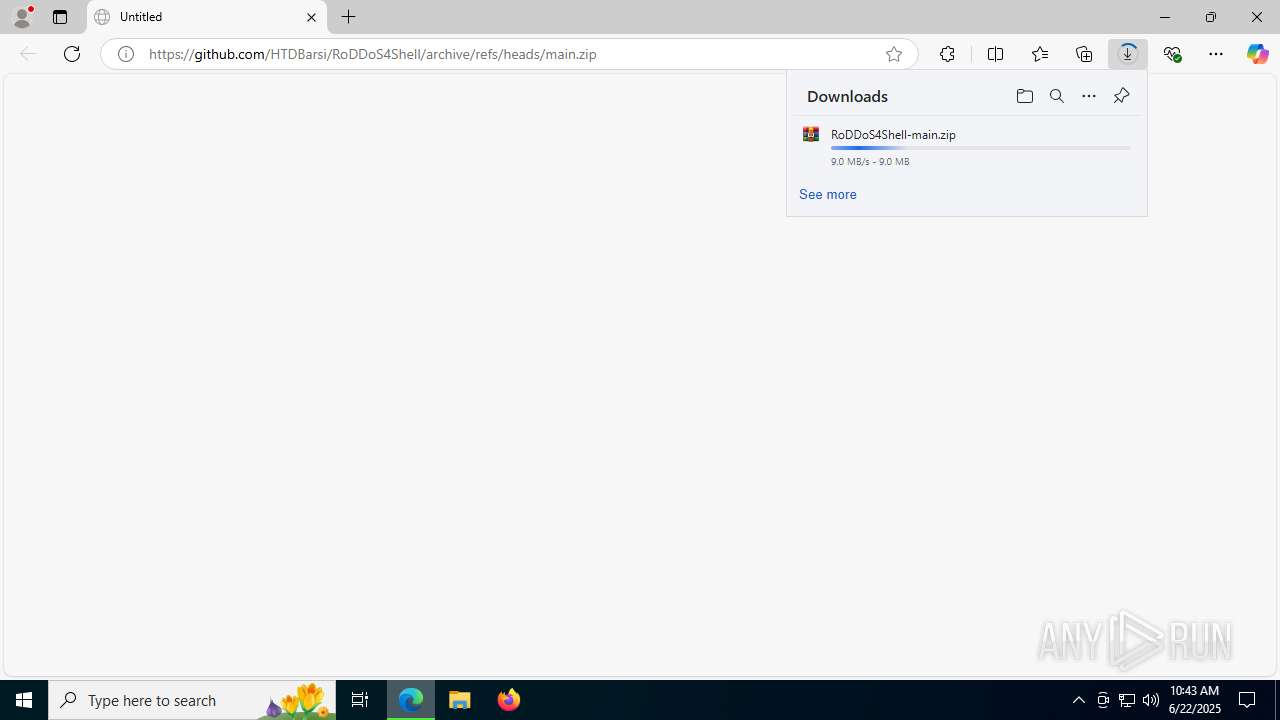
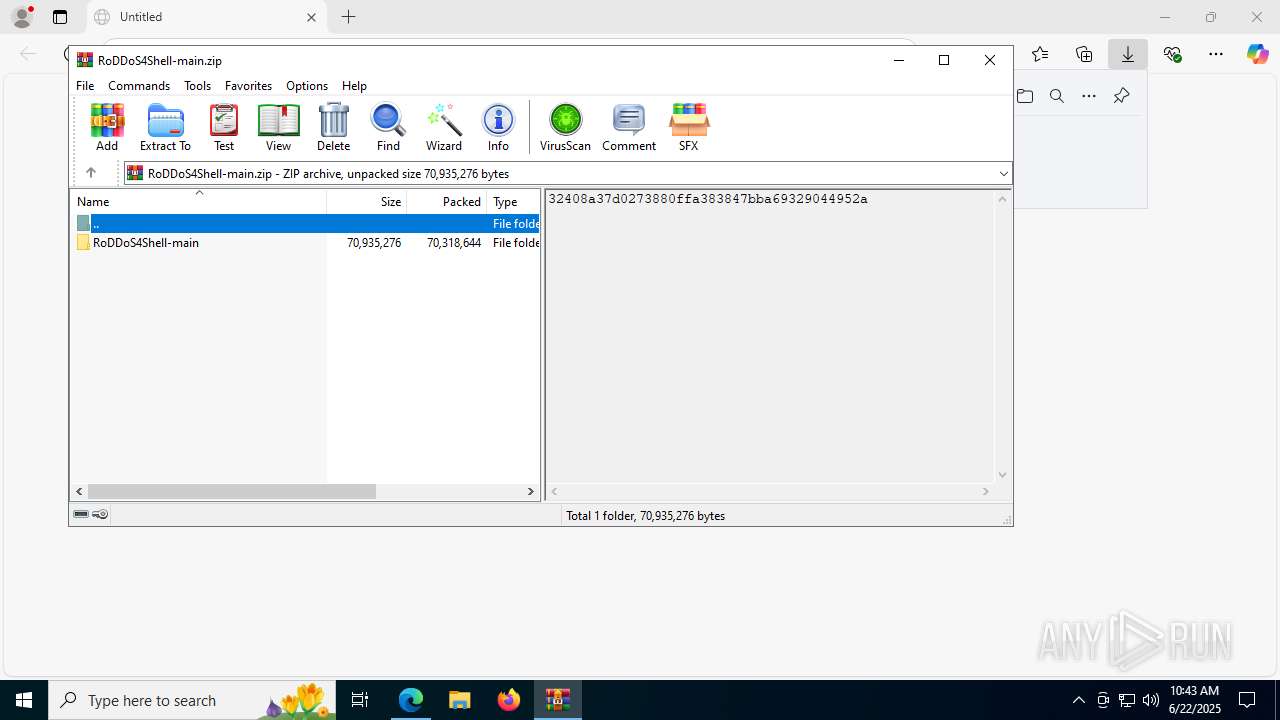
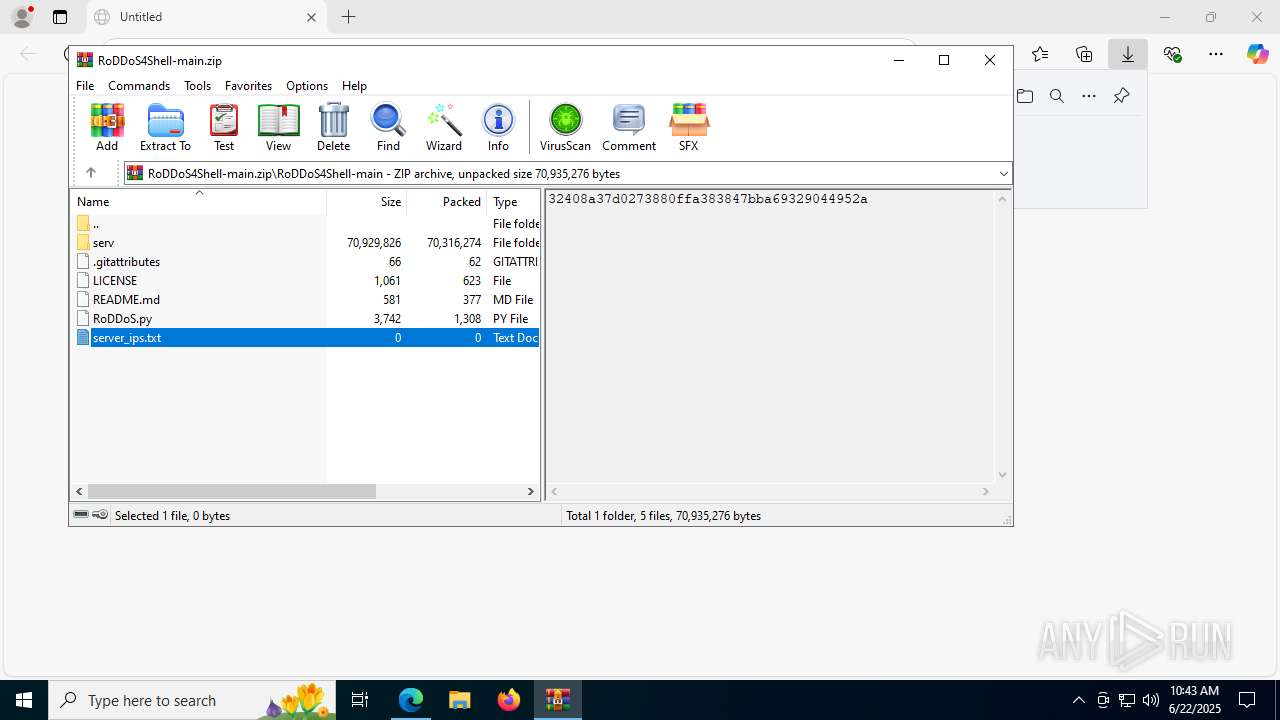
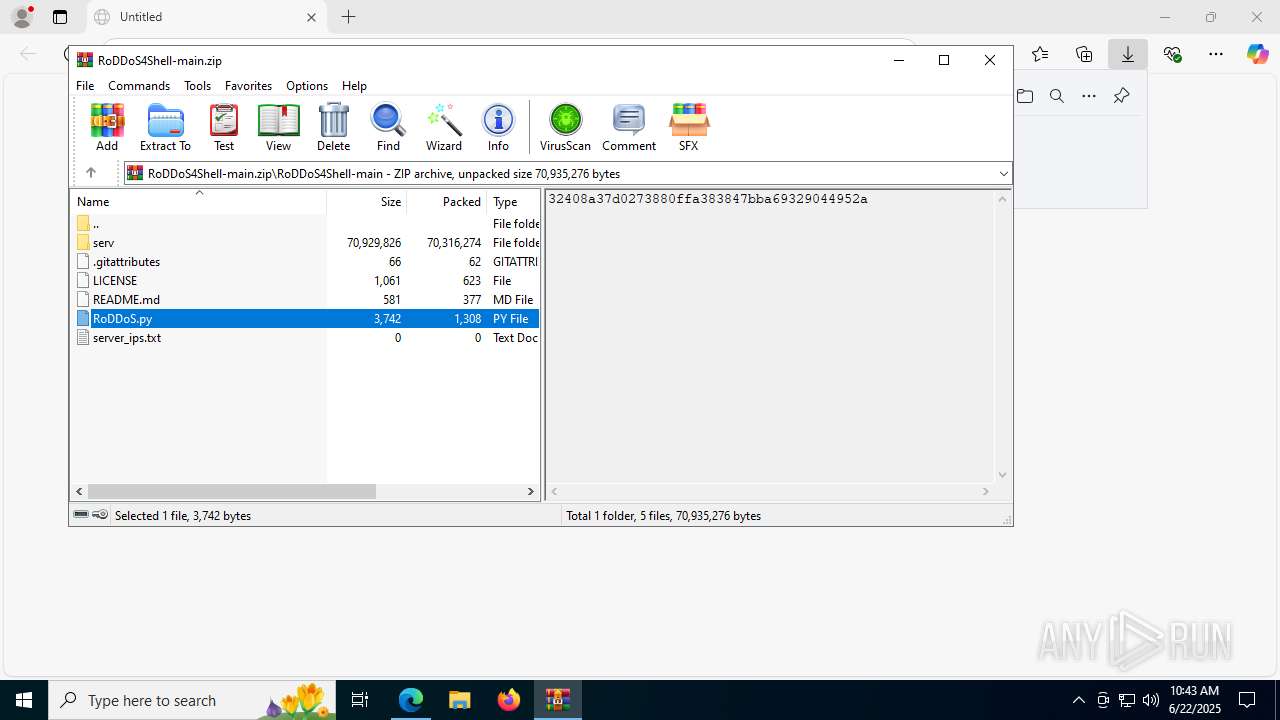
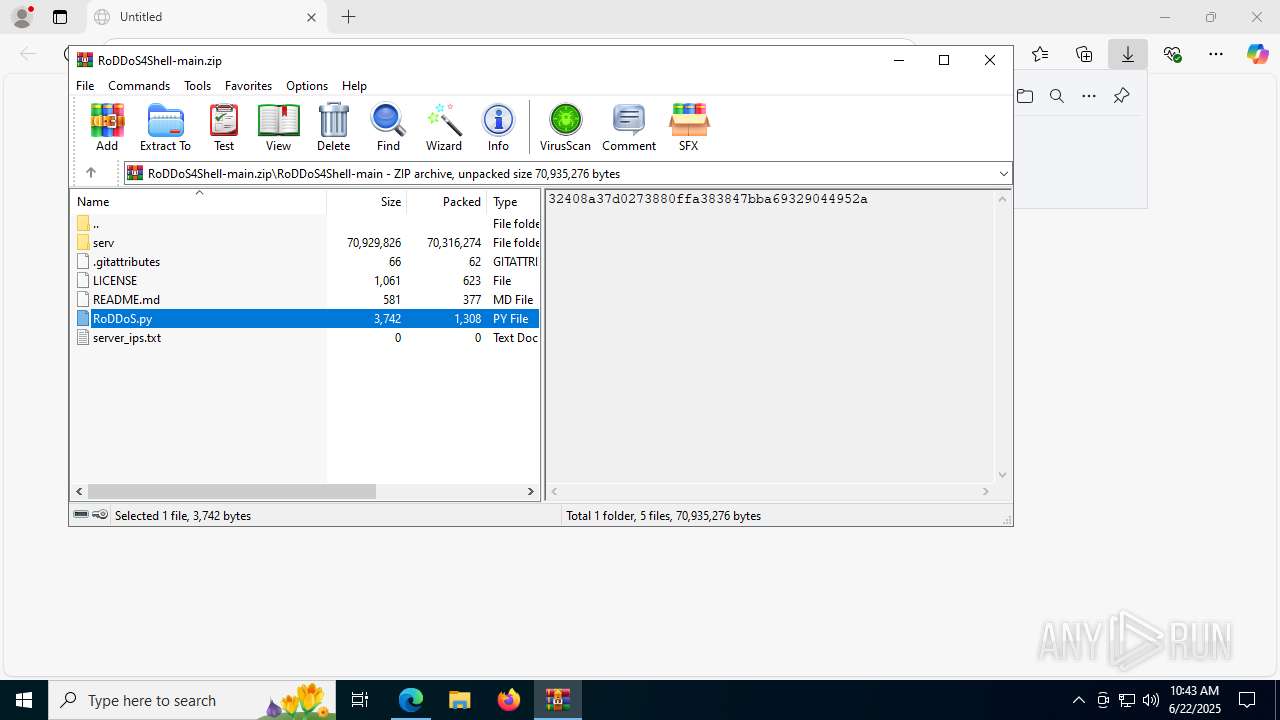
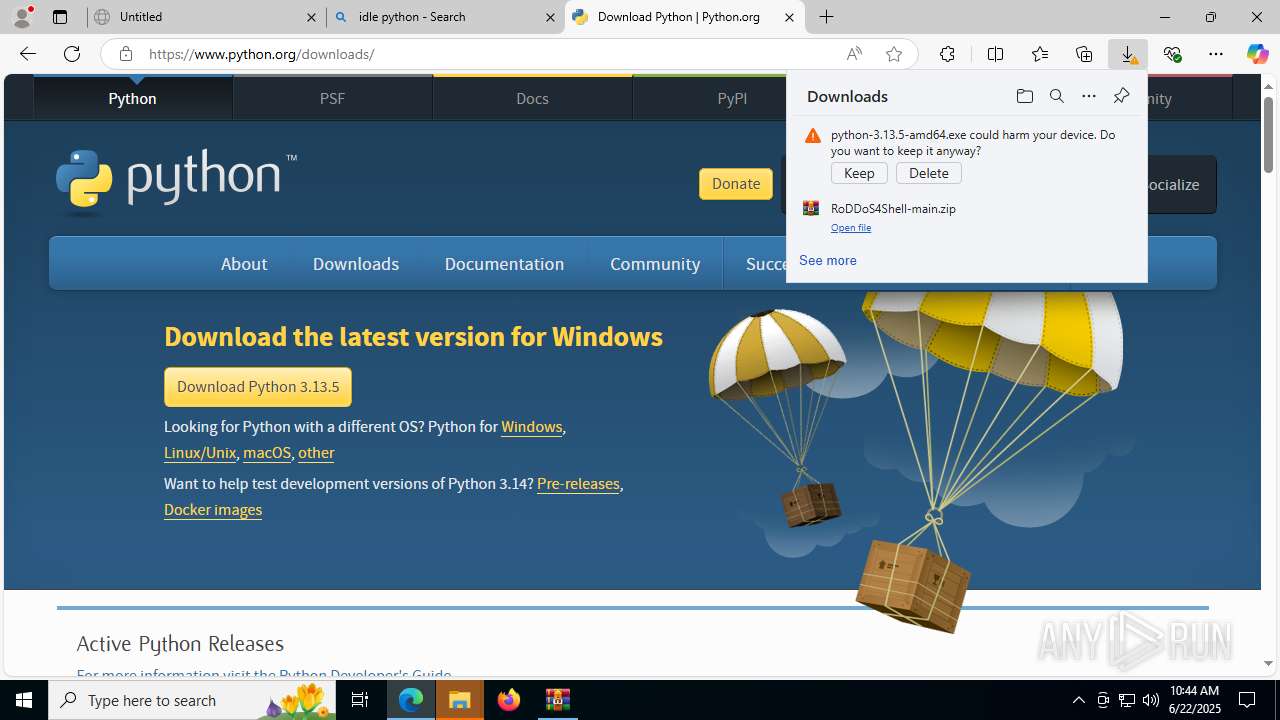
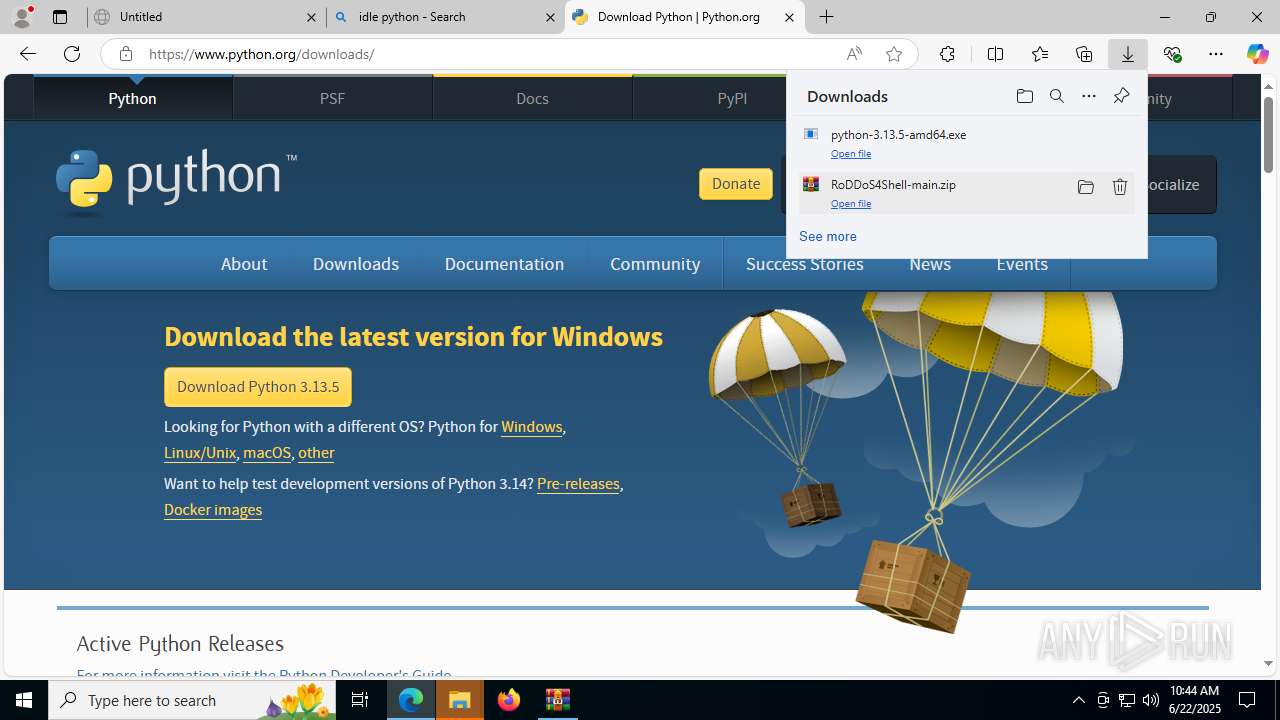
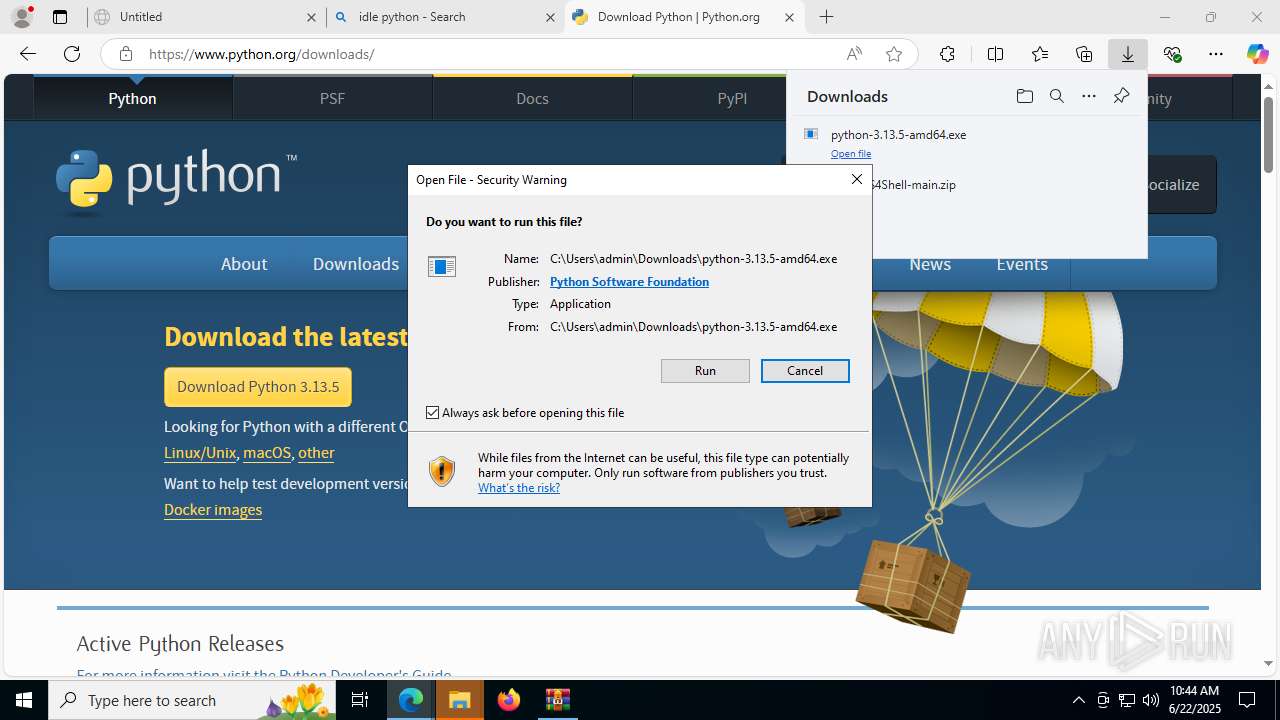
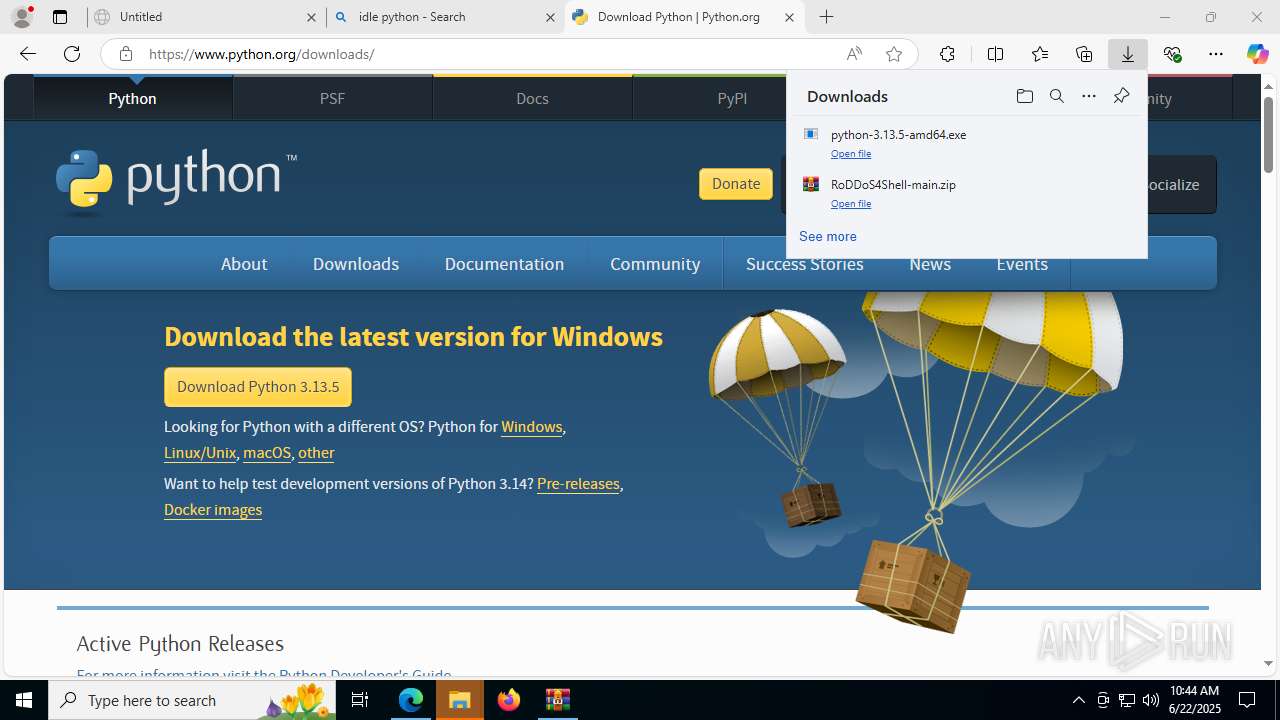
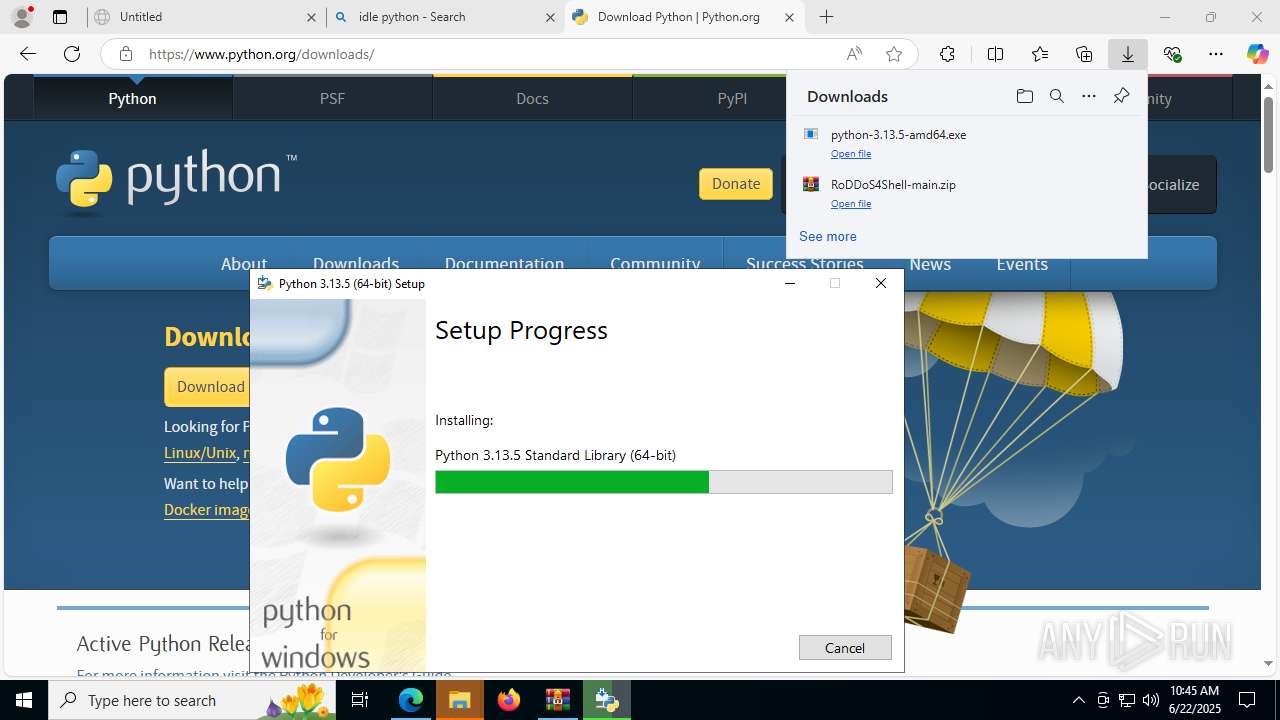
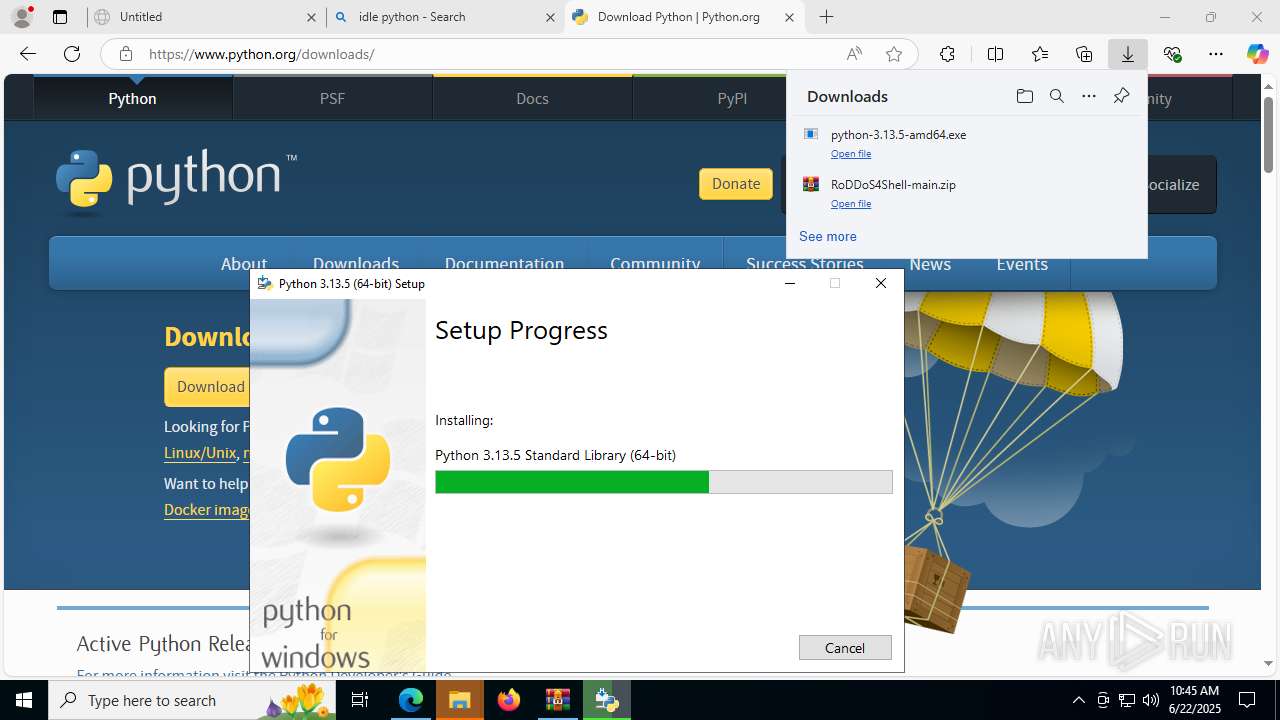
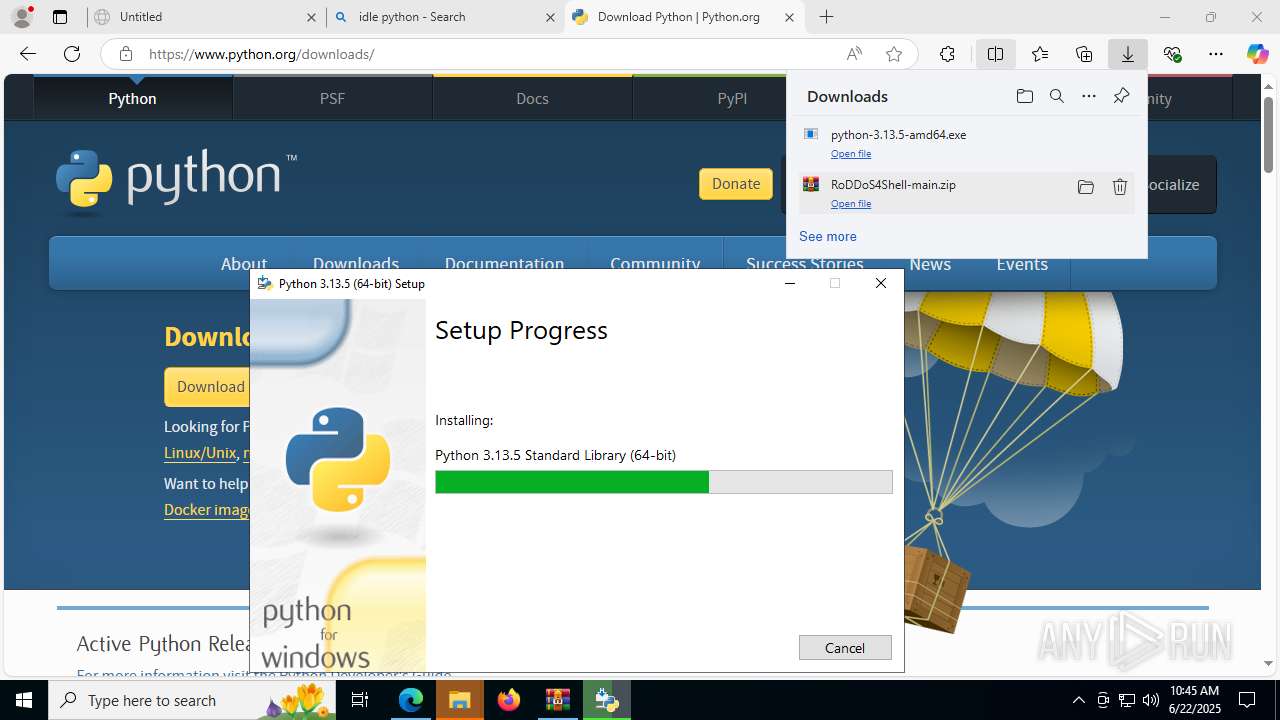
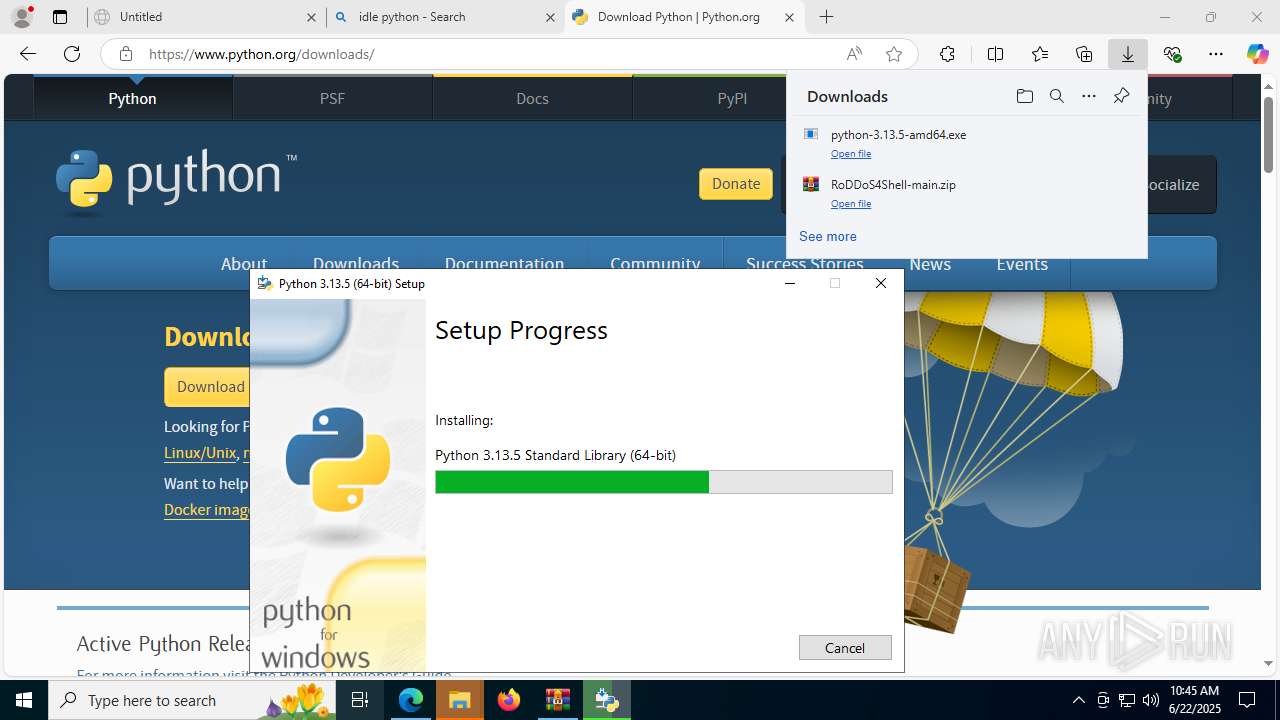
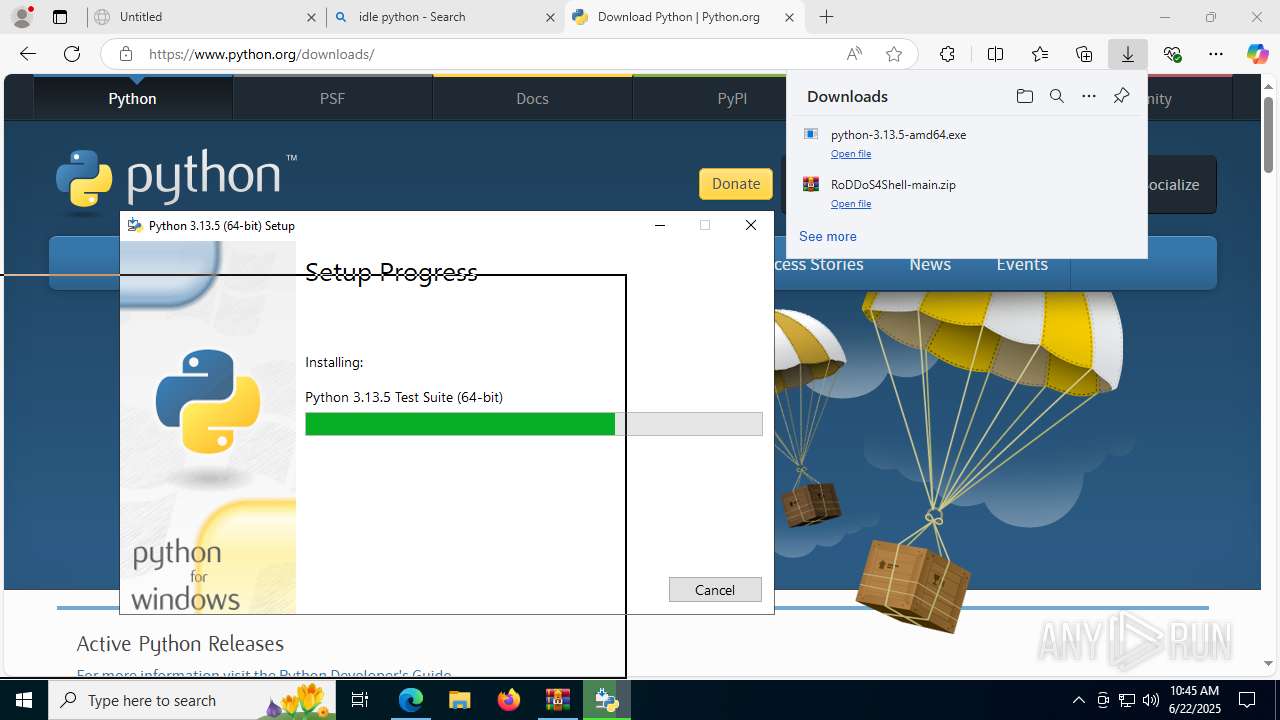
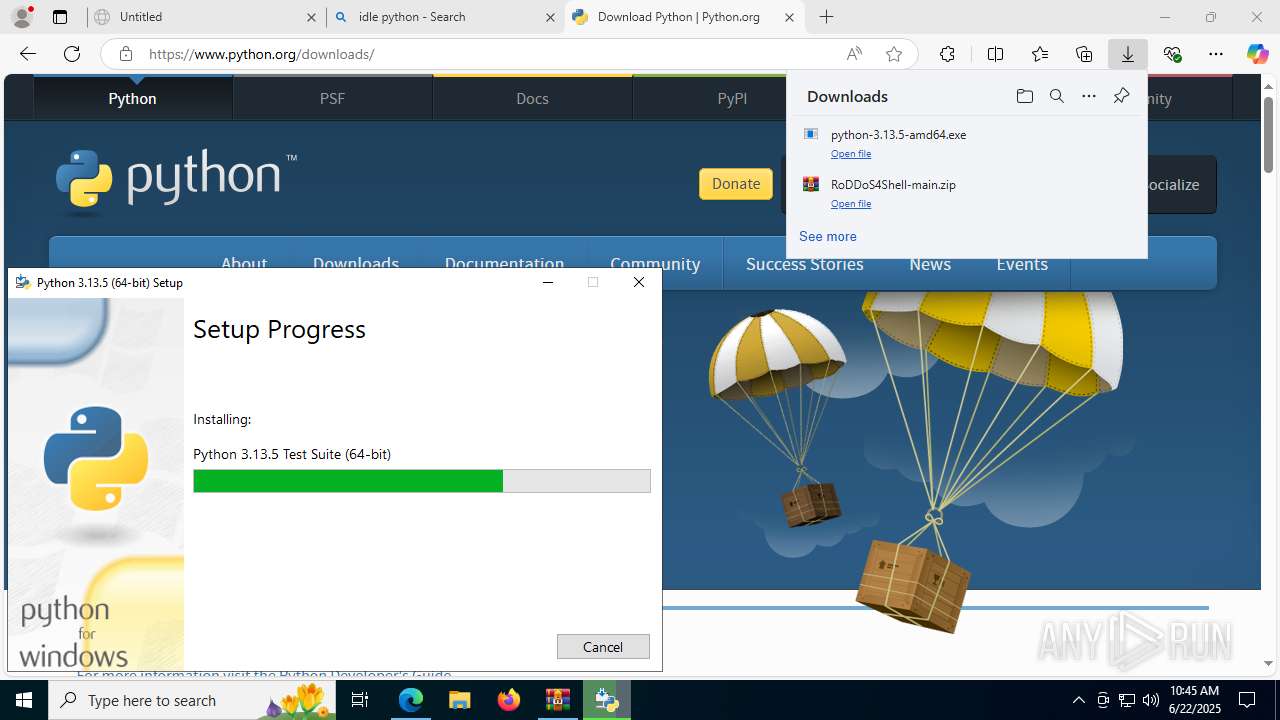
| URL: | https://github.com/HTDBarsi/RoDDoS4Shell/archive/refs/heads/main.zip |
| Full analysis: | https://app.any.run/tasks/5d8f21d3-173b-46dc-83ce-56dcb3b28812 |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2025, 10:43:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 94787388DD12675430C03F771F193751 |
| SHA1: | 5B1A4903A5CDA548784EBD45676DD44C410F01FE |
| SHA256: | 05848414754F9E40A4FC545DAC3912AEFA4AFB61756981E4E3DDFA0FBC91D001 |
| SSDEEP: | 3:N8tEdbMrhhK22p+GeT4RSLNLc:2u9M1hK724ULN4 |
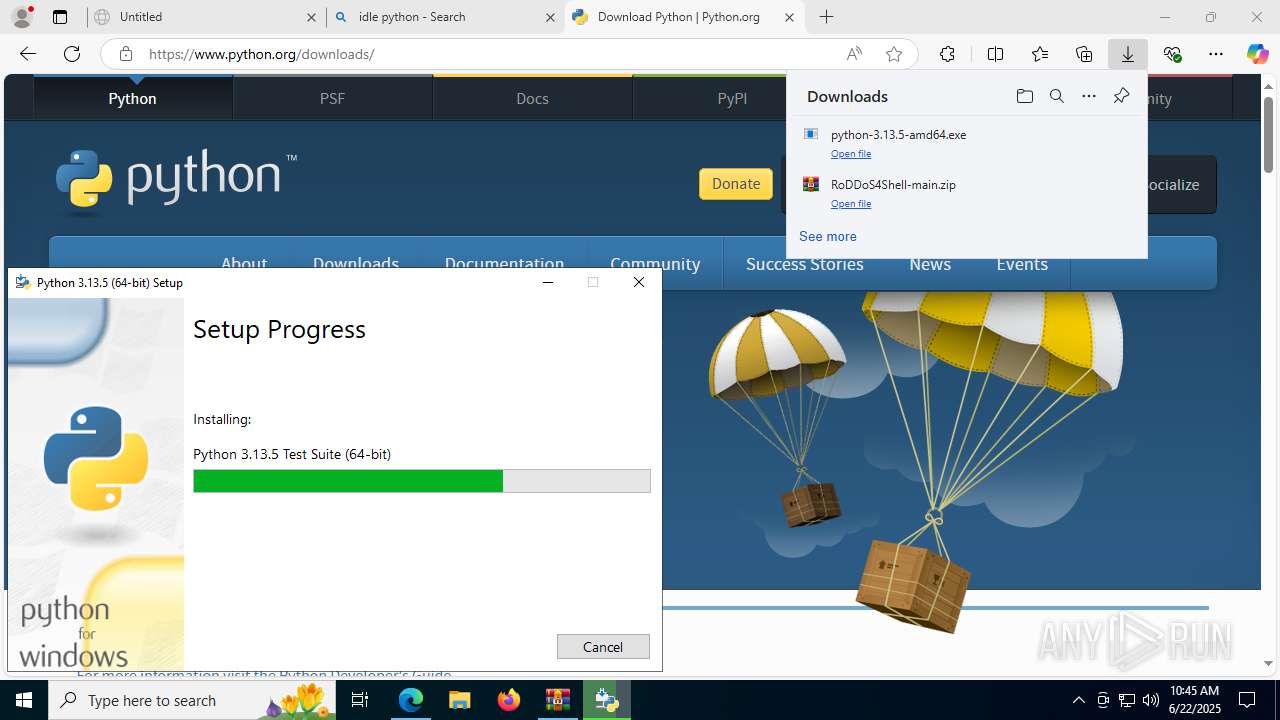
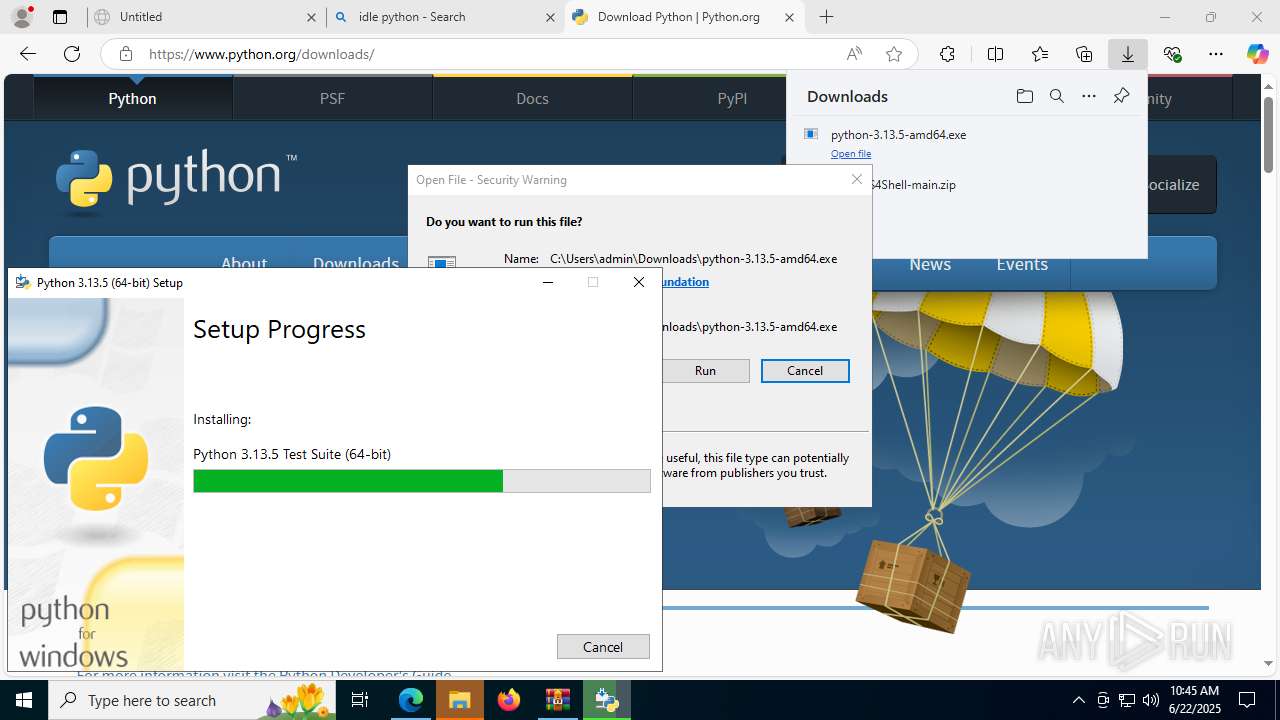
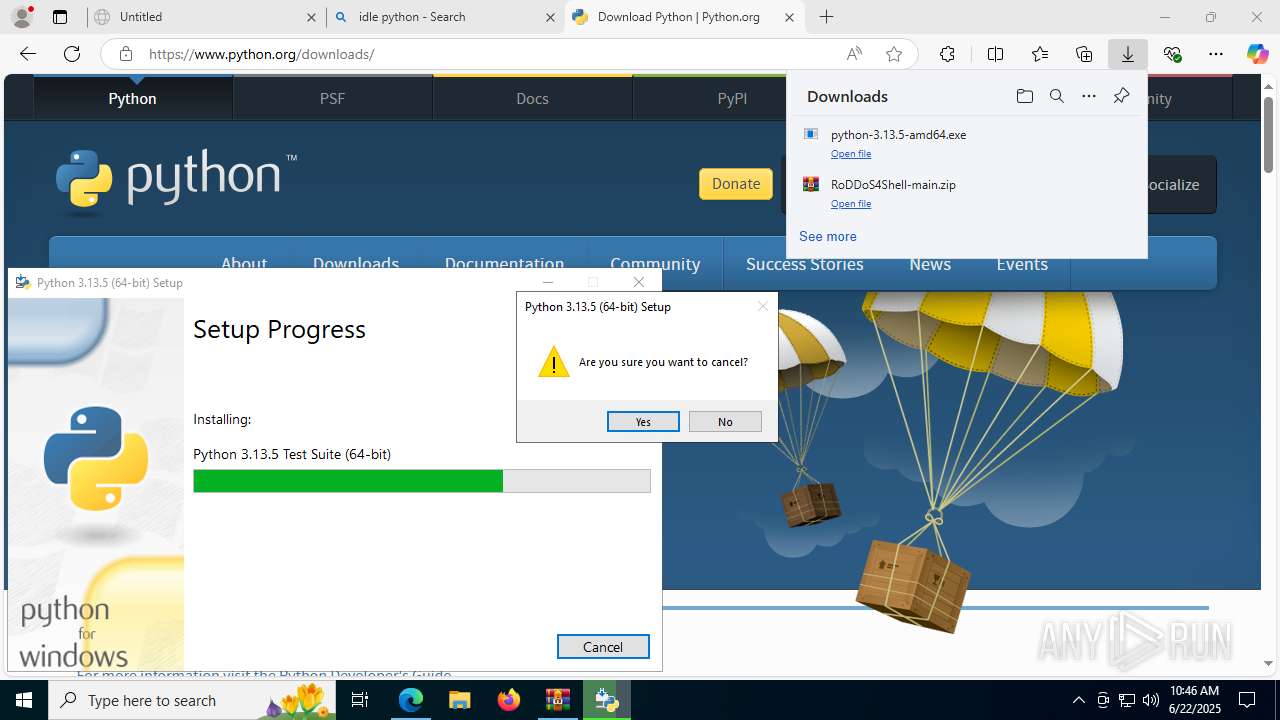
MALICIOUS
Changes the autorun value in the registry
- python-3.13.5-amd64.exe (PID: 5368)
SUSPICIOUS
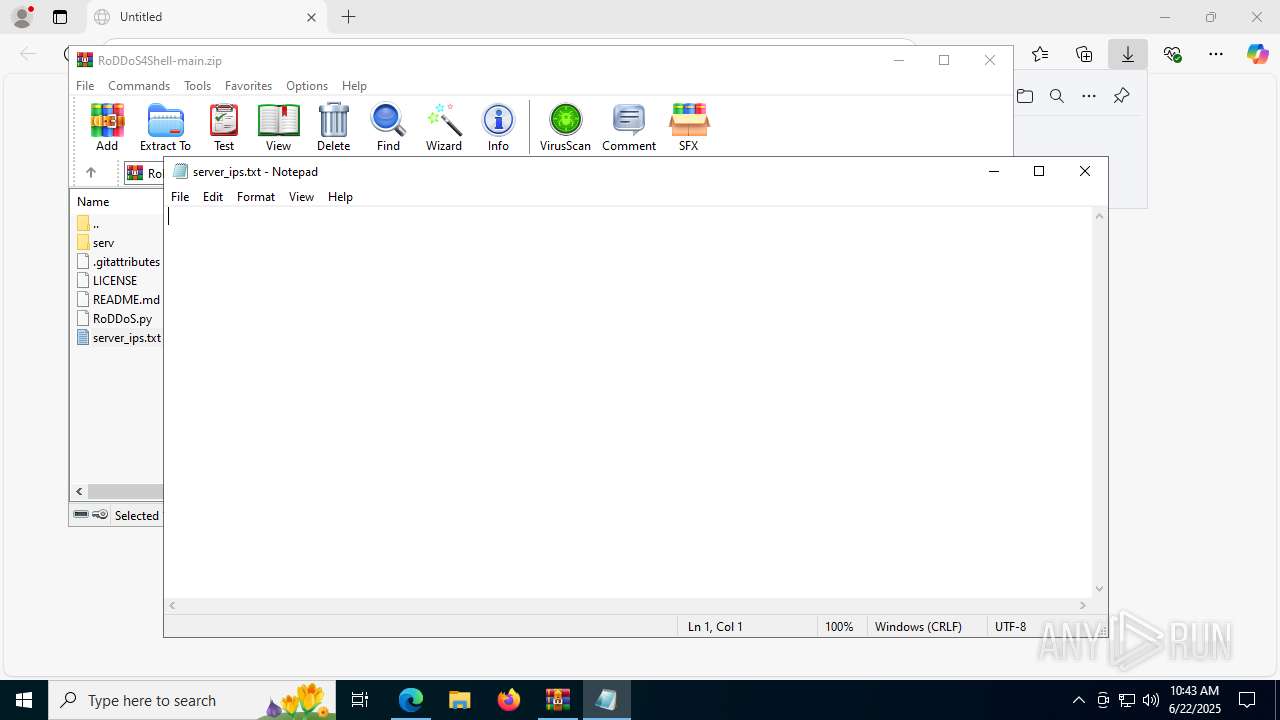
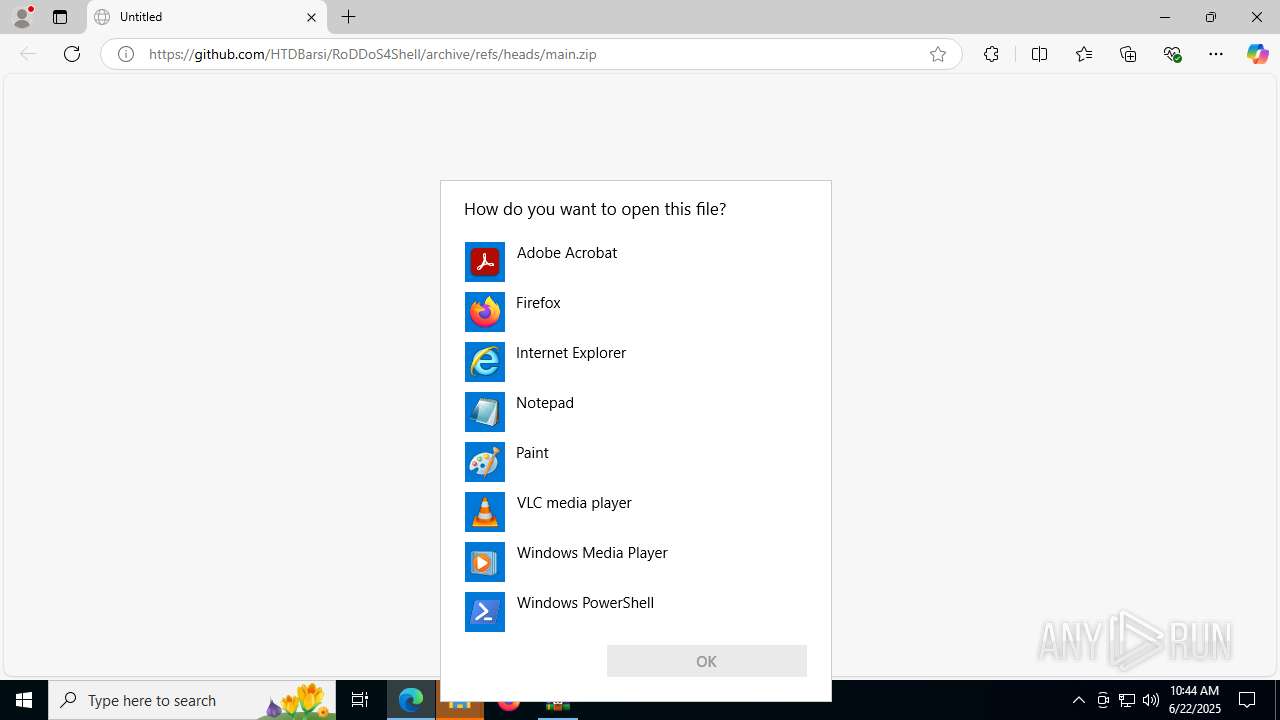
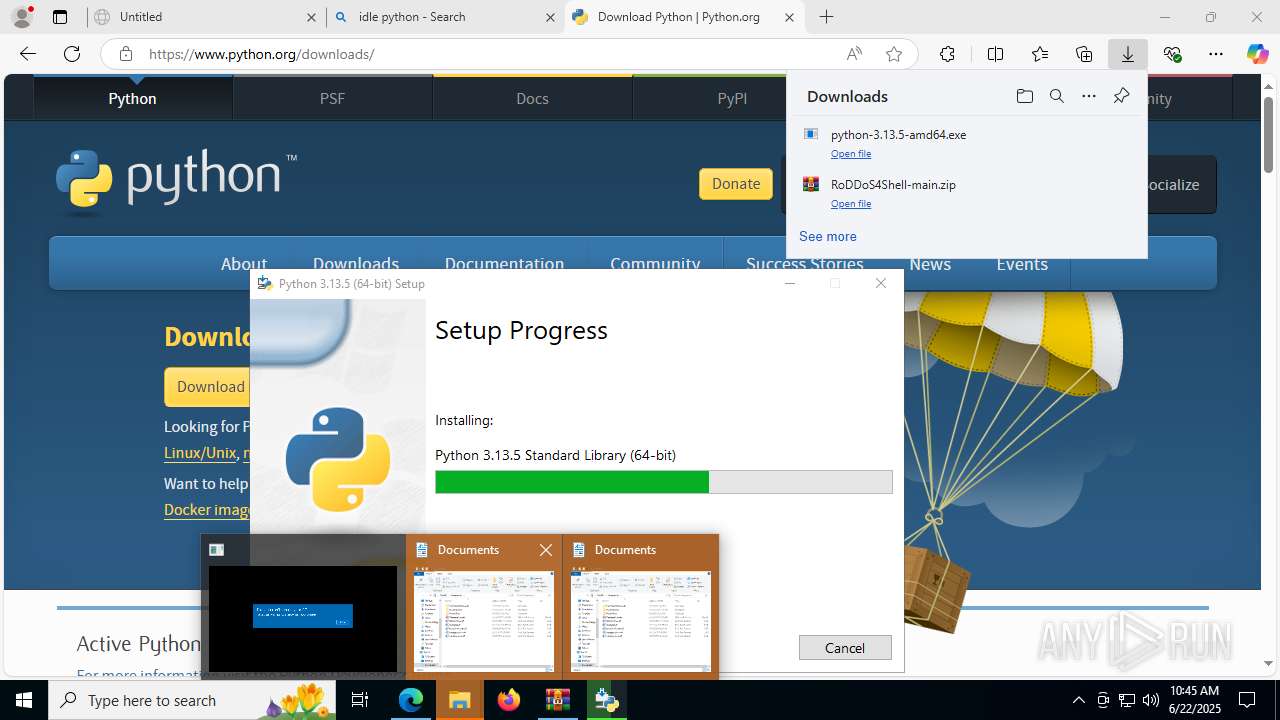
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 7824)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7824)
Executable content was dropped or overwritten
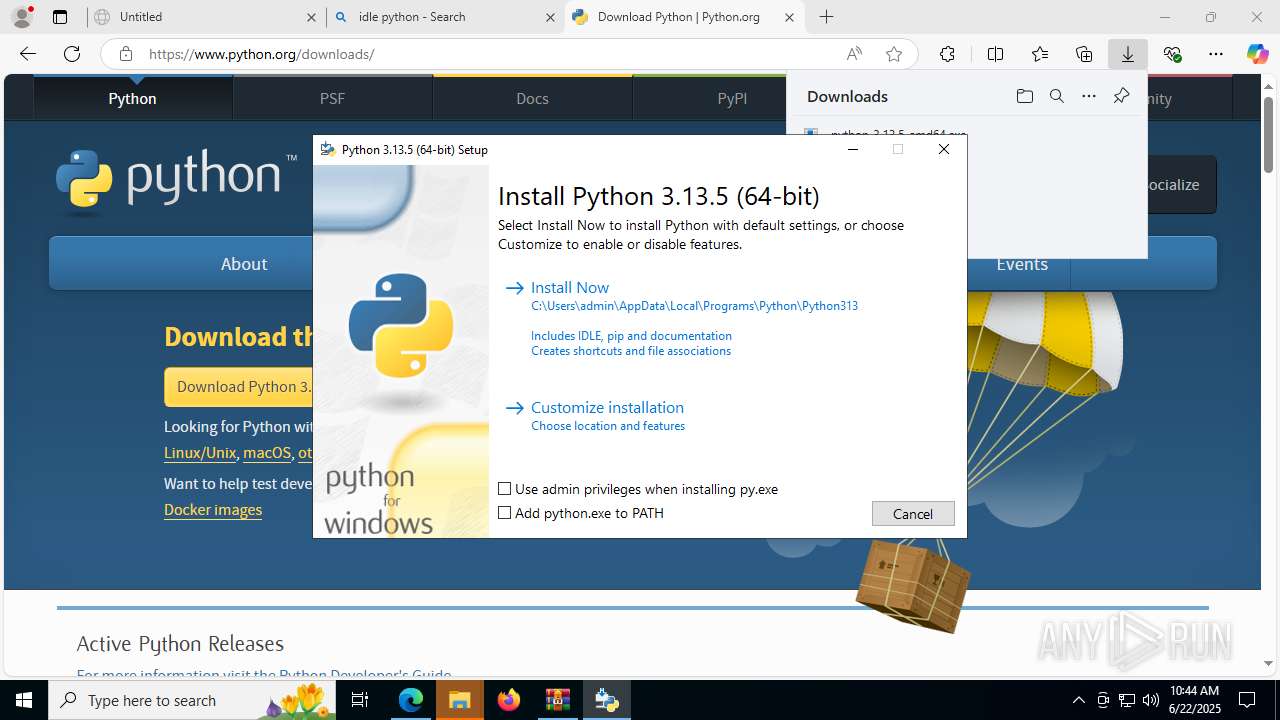
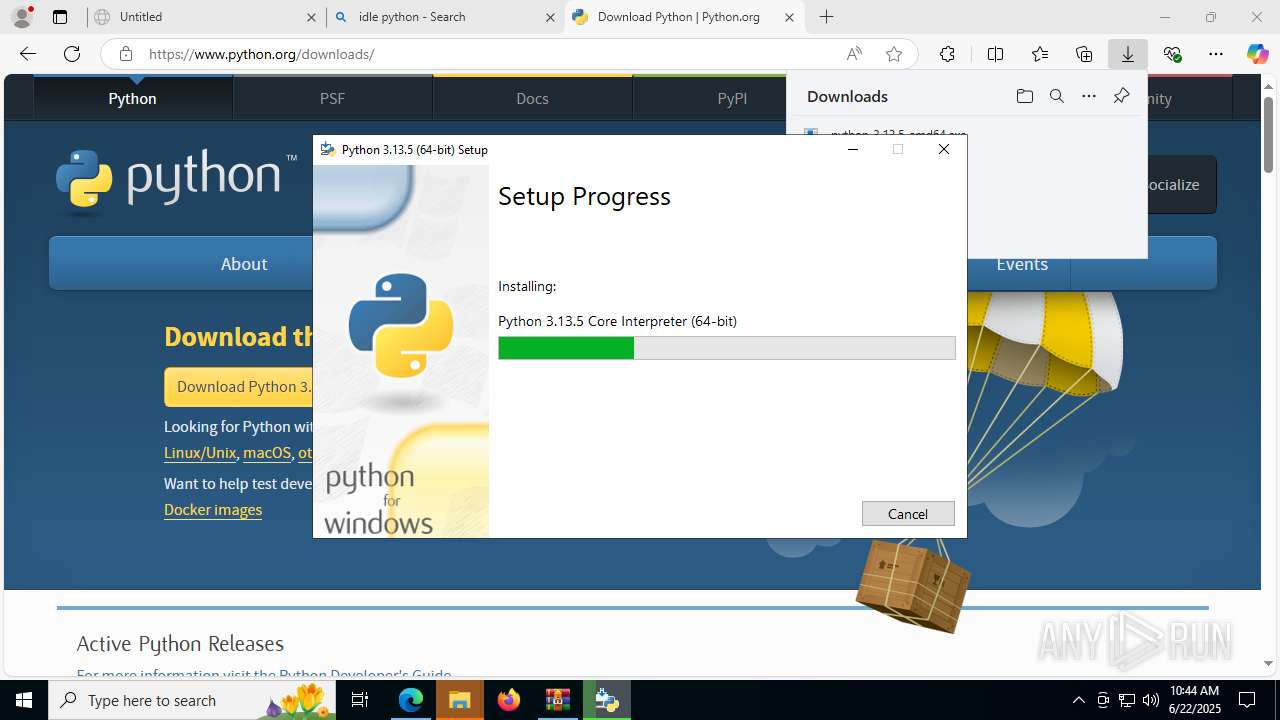
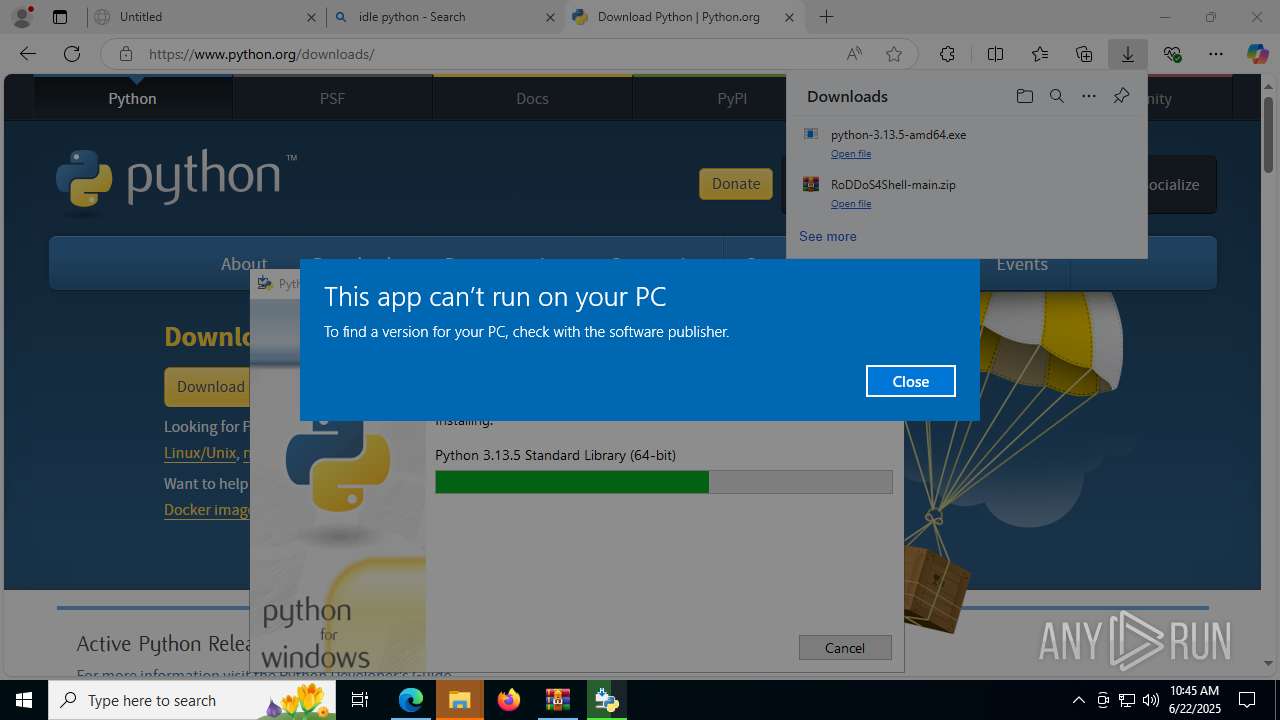
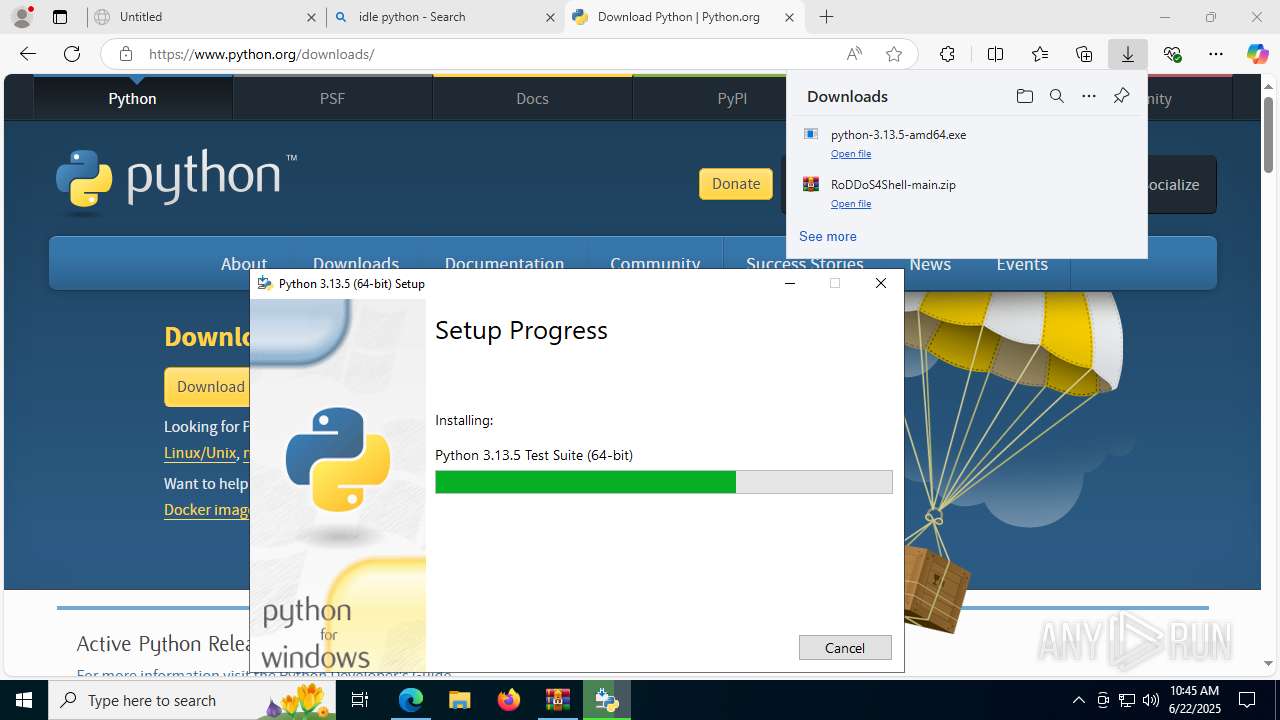
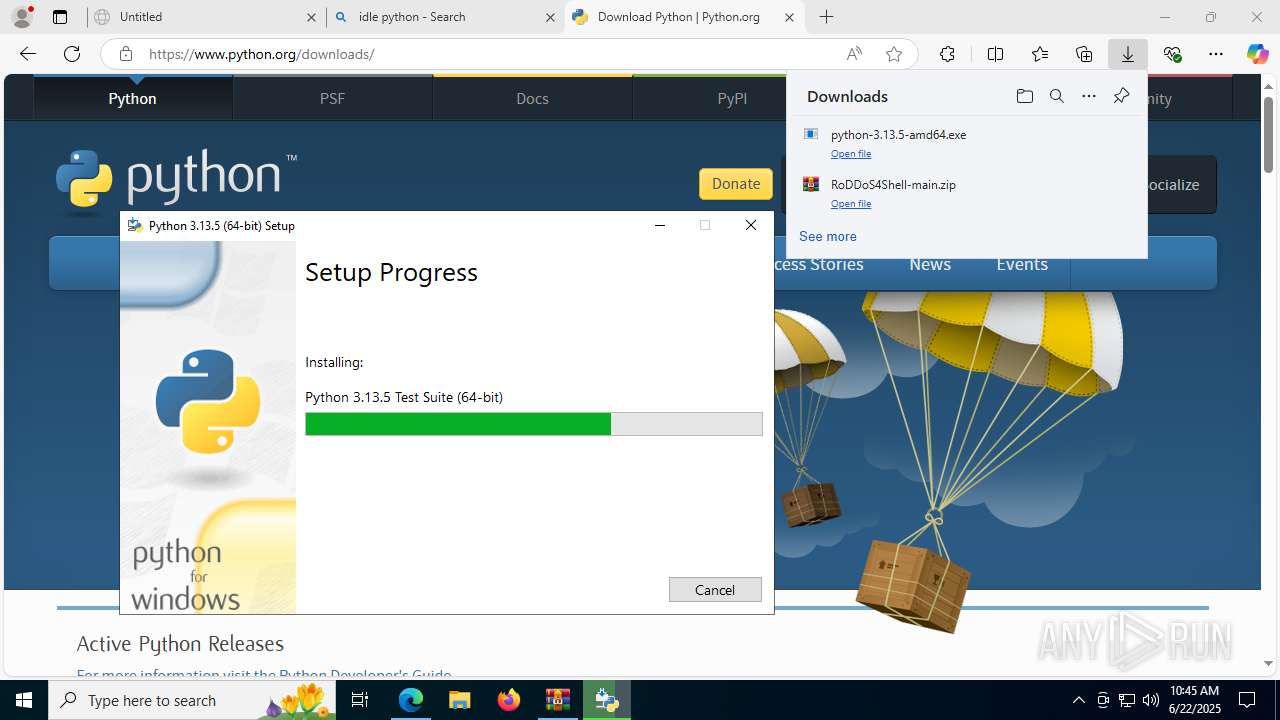
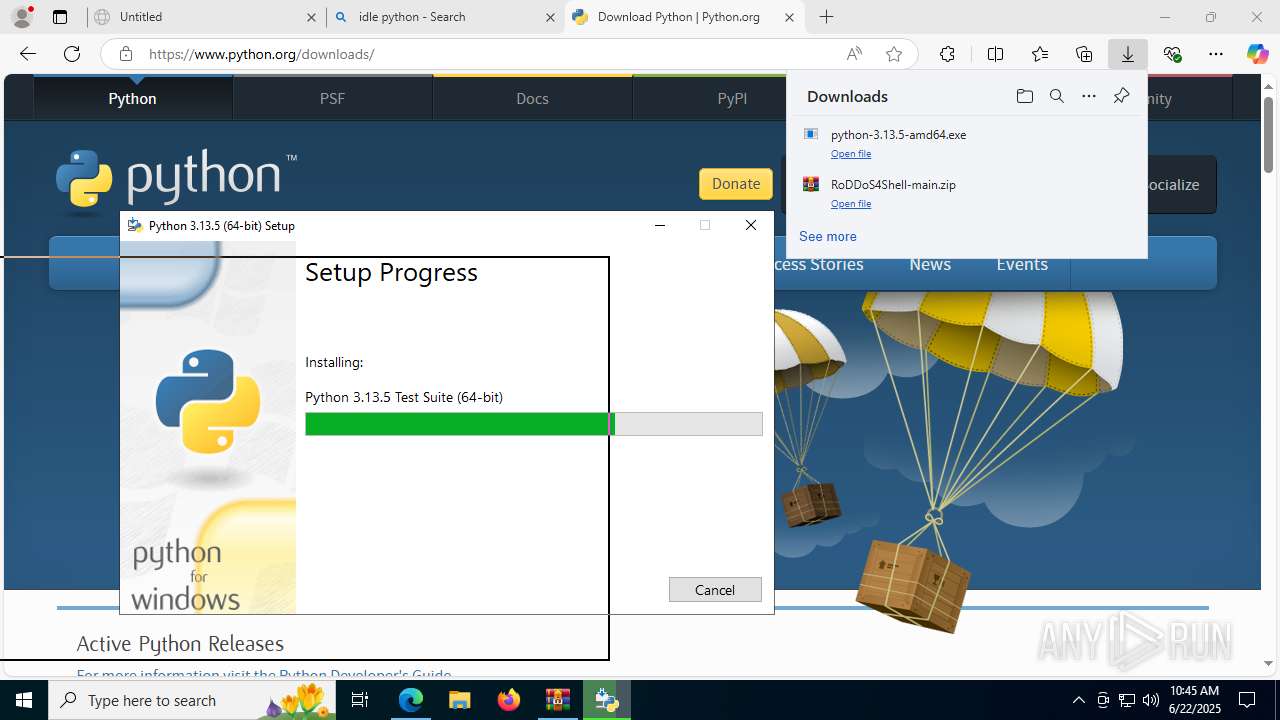
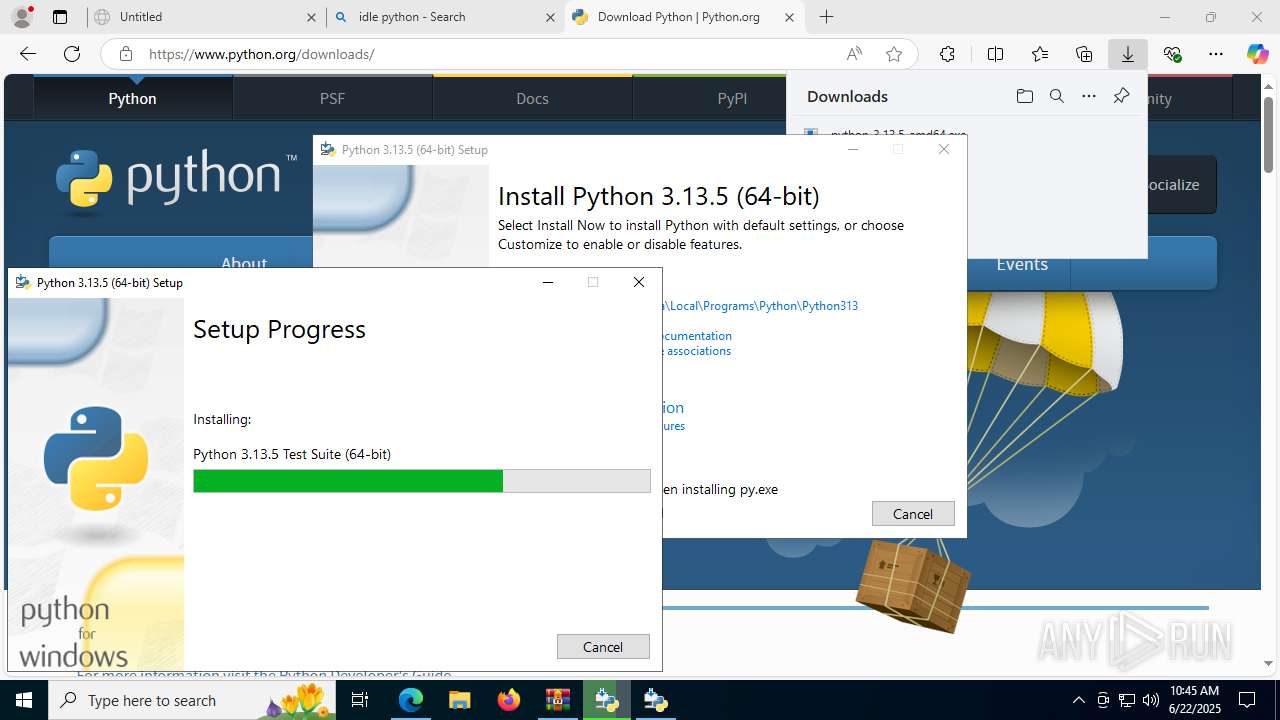
- python-3.13.5-amd64.exe (PID: 2800)
- python-3.13.5-amd64.exe (PID: 5368)
- python-3.13.5-amd64.exe (PID: 7540)
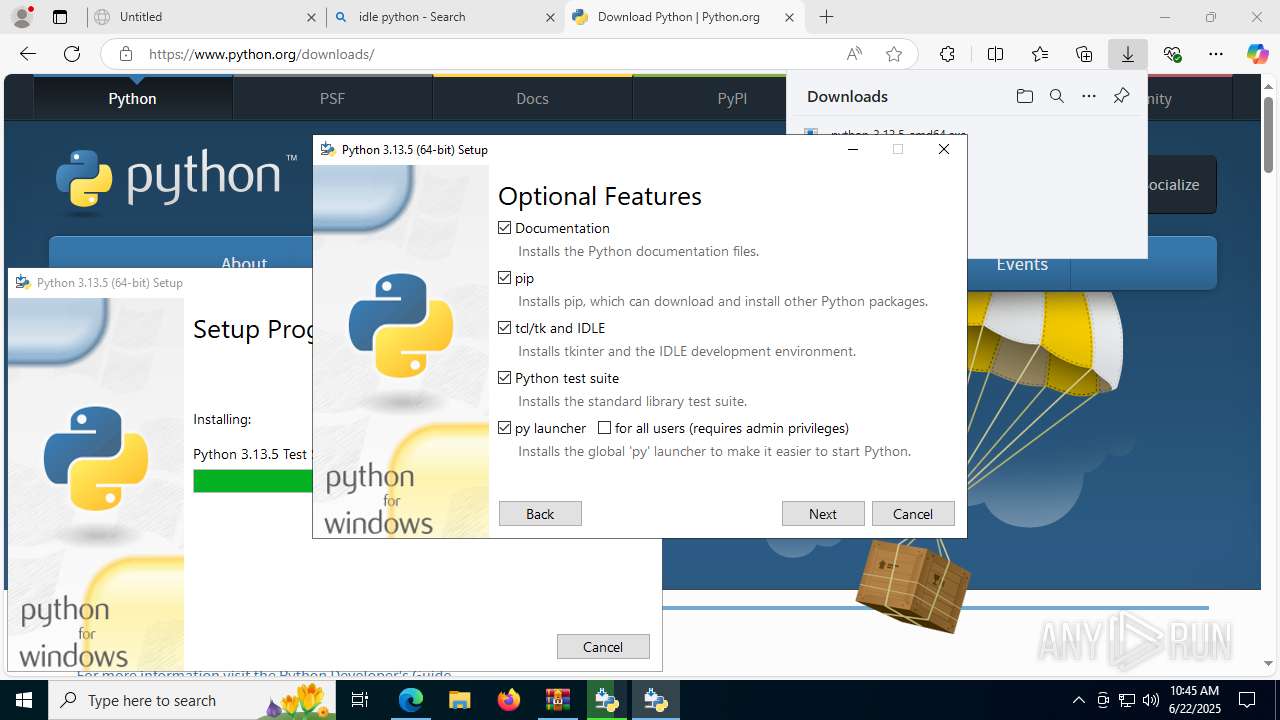
Searches for installed software
- python-3.13.5-amd64.exe (PID: 5368)
- python-3.13.5-amd64.exe (PID: 7084)
- python-3.13.5-amd64.exe (PID: 7540)
Creates a software uninstall entry
- python-3.13.5-amd64.exe (PID: 5368)
Process drops legitimate windows executable
- python-3.13.5-amd64.exe (PID: 5368)
- msiexec.exe (PID: 7980)
The process drops C-runtime libraries
- python-3.13.5-amd64.exe (PID: 5368)
- msiexec.exe (PID: 7980)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7980)
There is functionality for taking screenshot (YARA)
- python-3.13.5-amd64.exe (PID: 5368)
Application launched itself
- python-3.13.5-amd64.exe (PID: 7084)
- python-3.13.5-amd64.exe (PID: 3392)
Process drops python dynamic module
- msiexec.exe (PID: 7980)
INFO
Checks supported languages
- identity_helper.exe (PID: 7528)
- python-3.13.5-amd64.exe (PID: 2800)
- python-3.13.5-amd64.exe (PID: 5368)
- msiexec.exe (PID: 7980)
- python-3.13.5-amd64.exe (PID: 7084)
- python-3.13.5-amd64.exe (PID: 3392)
- python-3.13.5-amd64.exe (PID: 7540)
Application launched itself
- msedge.exe (PID: 3884)
Reads the computer name
- identity_helper.exe (PID: 7528)
- python-3.13.5-amd64.exe (PID: 5368)
- msiexec.exe (PID: 7980)
- python-3.13.5-amd64.exe (PID: 7540)
Reads Environment values
- identity_helper.exe (PID: 7528)
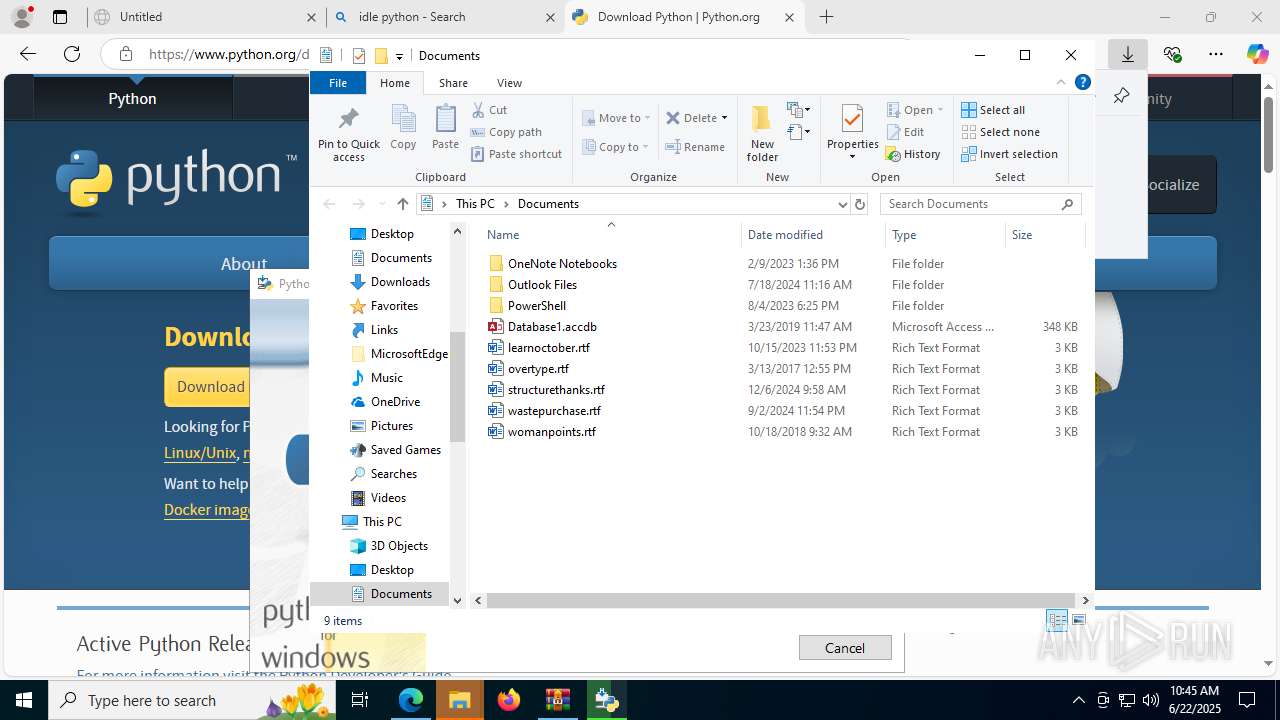
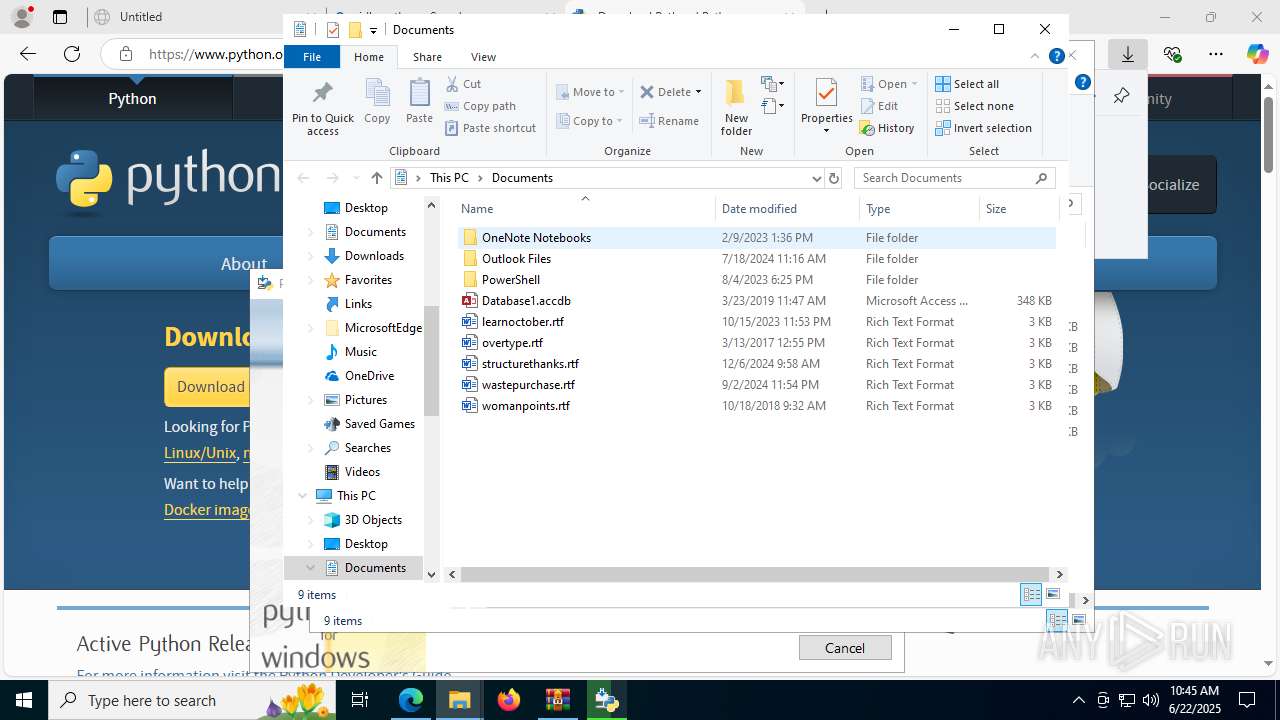
Reads Microsoft Office registry keys
- msedge.exe (PID: 3884)
- WinRAR.exe (PID: 7824)
- OpenWith.exe (PID: 5060)
- OpenWith.exe (PID: 4960)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1508)
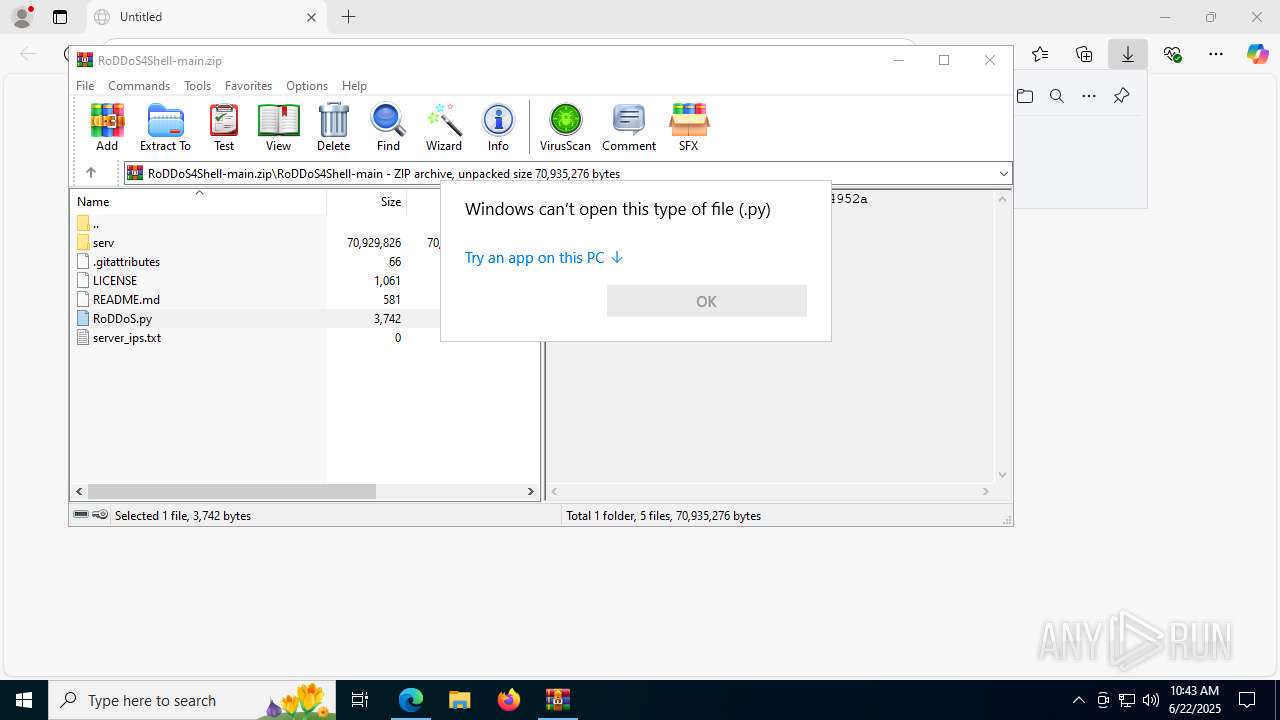
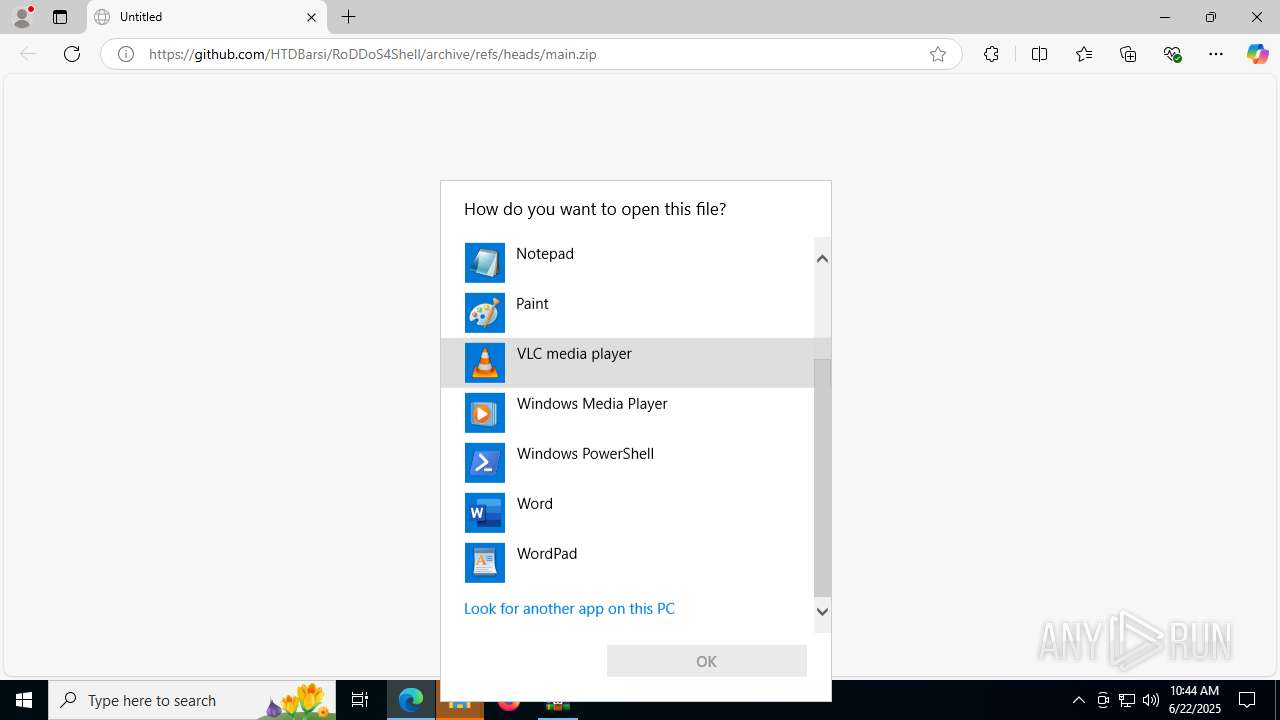
Manual execution by a user
- OpenWith.exe (PID: 4960)
- python-3.13.5-amd64.exe (PID: 7084)
Executable content was dropped or overwritten
- msedge.exe (PID: 3688)
- msedge.exe (PID: 3884)
- msiexec.exe (PID: 7980)
The sample compiled with english language support
- msedge.exe (PID: 3884)
- python-3.13.5-amd64.exe (PID: 2800)
- python-3.13.5-amd64.exe (PID: 5368)
- msiexec.exe (PID: 7980)
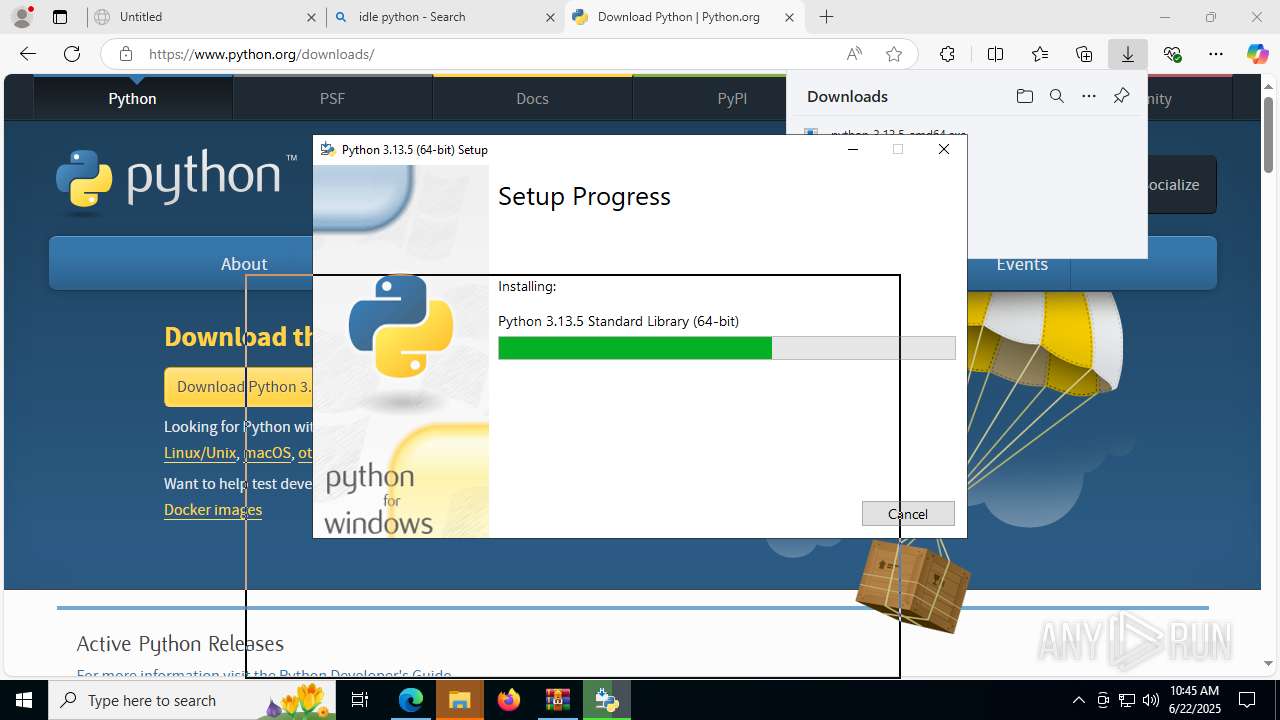
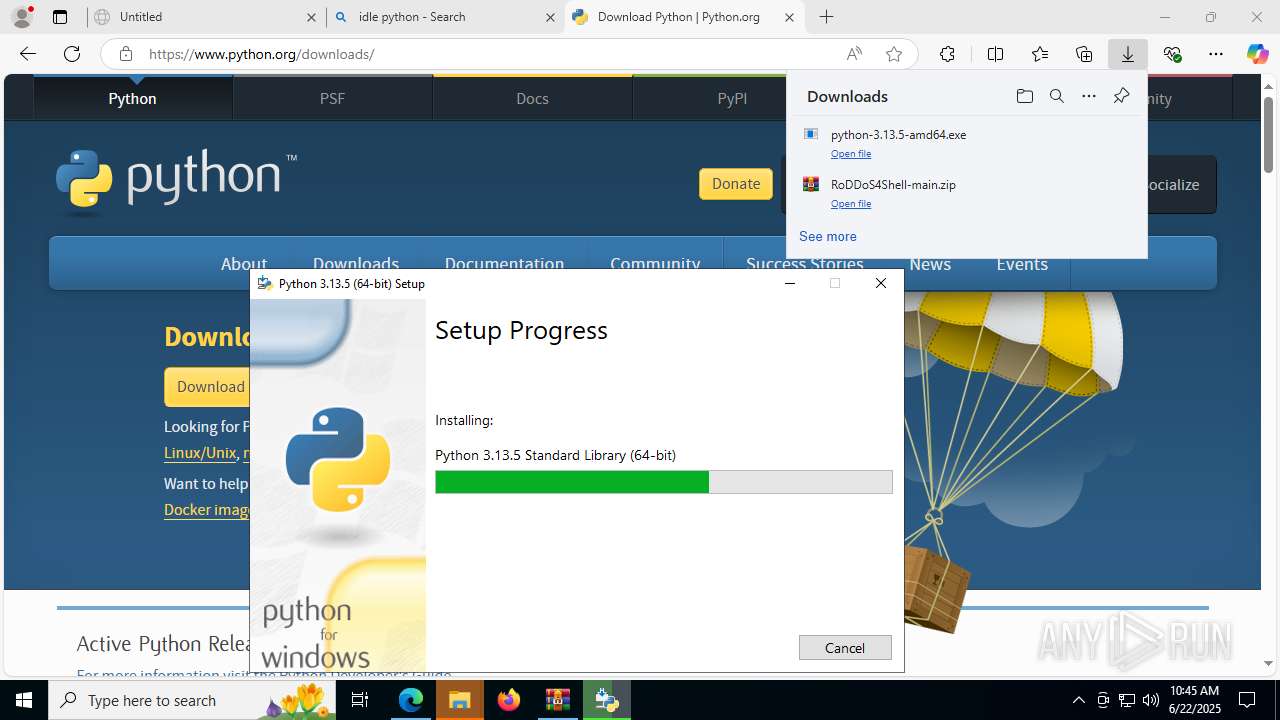
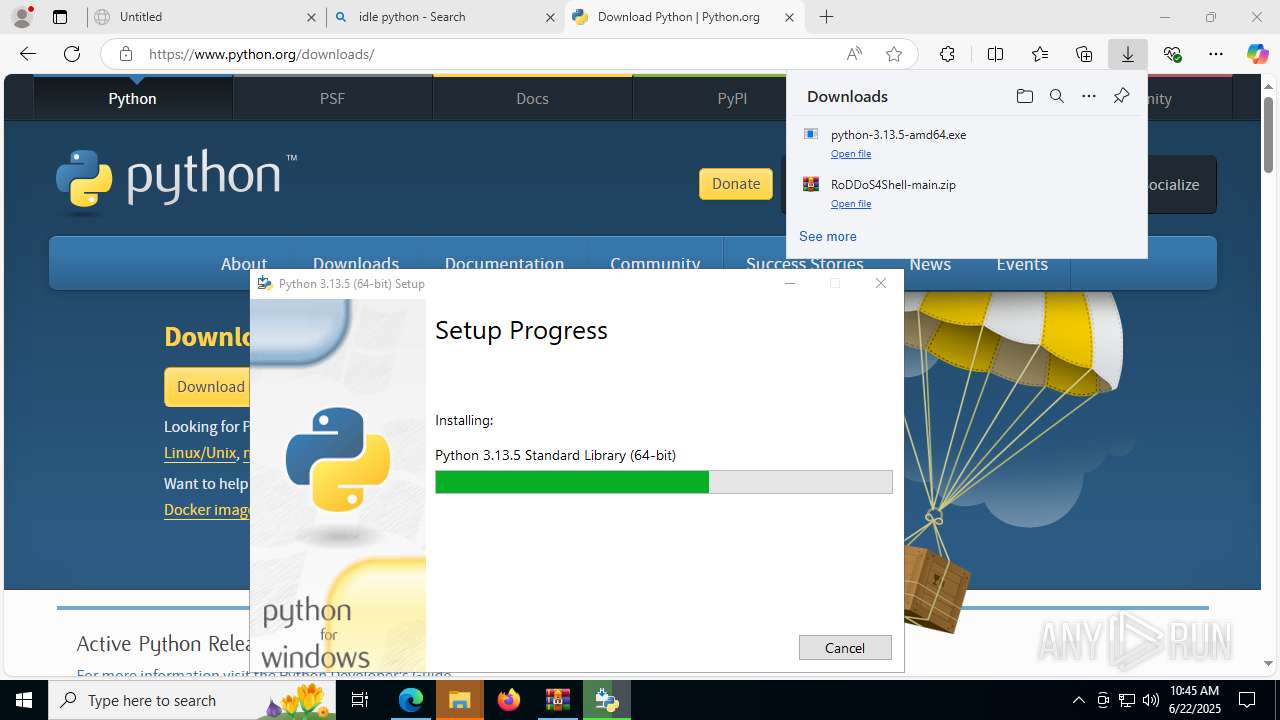
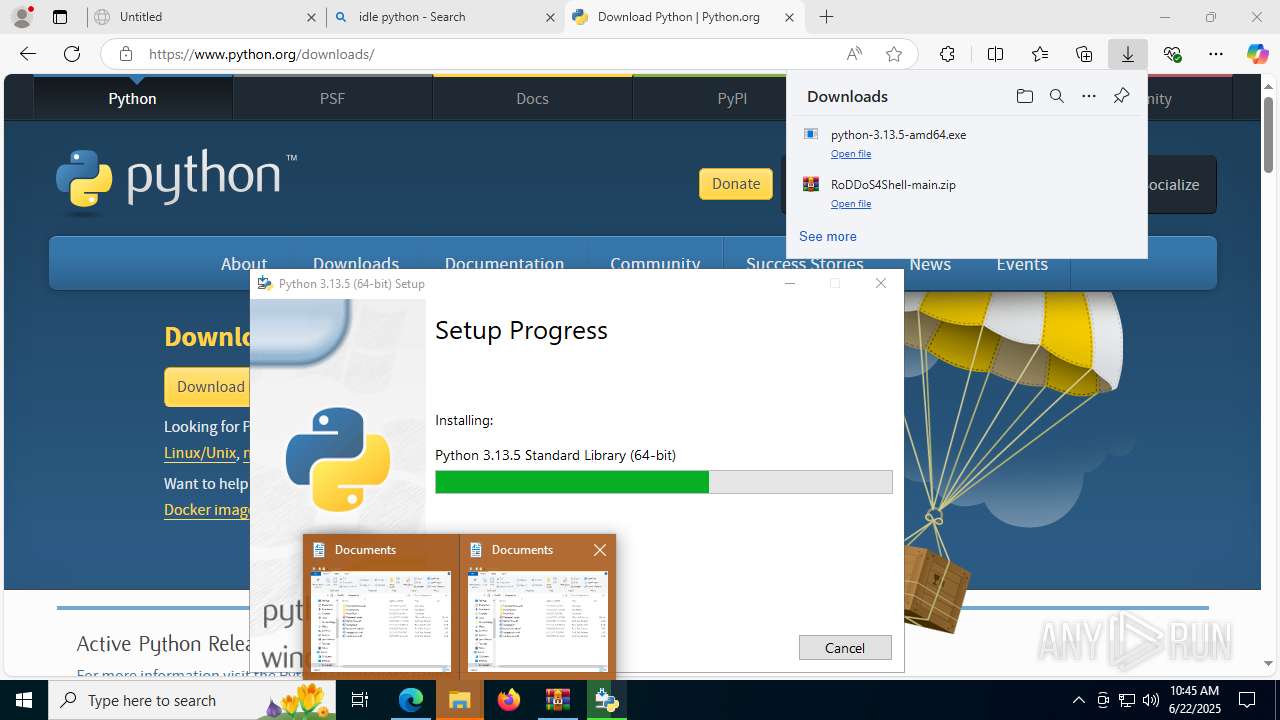
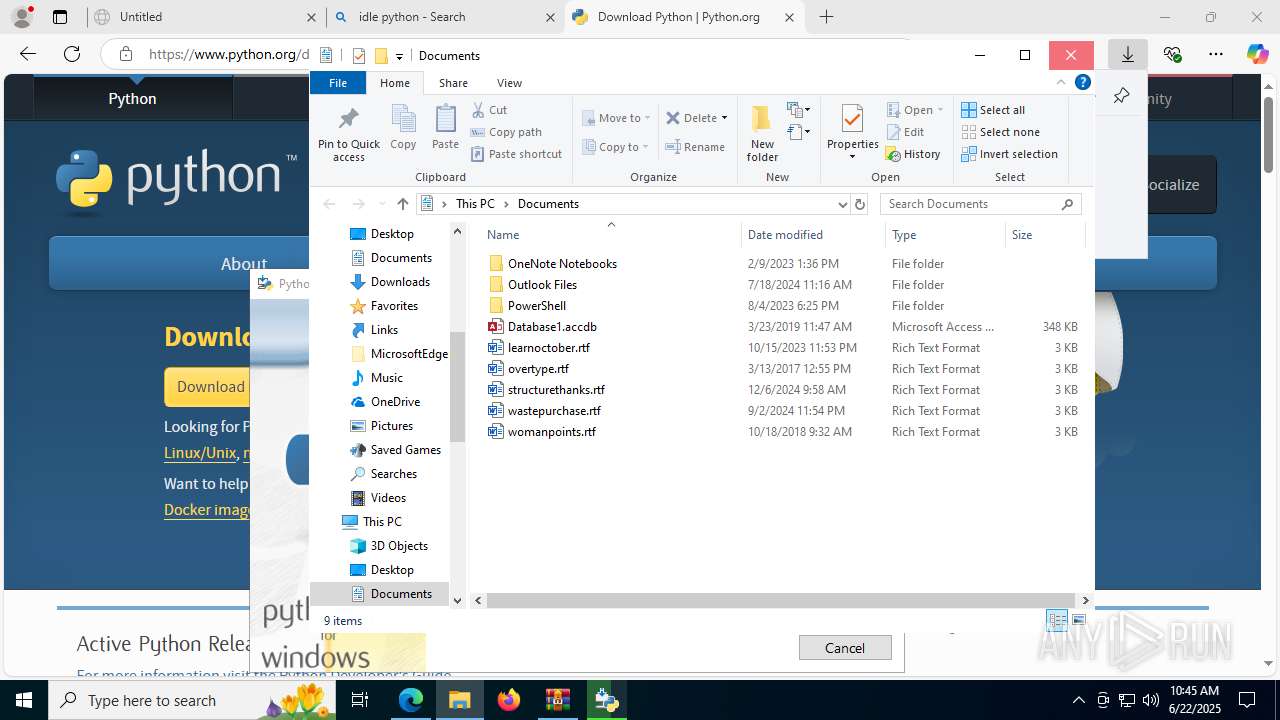
Launching a file from the Downloads directory
- msedge.exe (PID: 3884)
Create files in a temporary directory
- python-3.13.5-amd64.exe (PID: 2800)
- python-3.13.5-amd64.exe (PID: 5368)
- python-3.13.5-amd64.exe (PID: 7540)
Launching a file from a Registry key
- python-3.13.5-amd64.exe (PID: 5368)
Reads the machine GUID from the registry
- python-3.13.5-amd64.exe (PID: 5368)
- msiexec.exe (PID: 7980)
Reads the software policy settings
- msiexec.exe (PID: 7980)
- slui.exe (PID: 8024)
Creates a software uninstall entry
- msiexec.exe (PID: 7980)
Creates files or folders in the user directory
- python-3.13.5-amd64.exe (PID: 5368)
- msiexec.exe (PID: 7980)
Checks proxy server information
- slui.exe (PID: 8024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
195
Monitored processes
52
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1508 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa7824.33333\server_ips.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1604 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2380,i,16447018790378724786,6424974890952781436,262144 --variations-seed-version --mojo-platform-channel-handle=2728 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7136,i,16447018790378724786,6424974890952781436,262144 --variations-seed-version --mojo-platform-channel-handle=2172 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2124 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --always-read-main-dll --field-trial-handle=7476,i,16447018790378724786,6424974890952781436,262144 --variations-seed-version --mojo-platform-channel-handle=7012 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2596 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3632,i,16447018790378724786,6424974890952781436,262144 --variations-seed-version --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
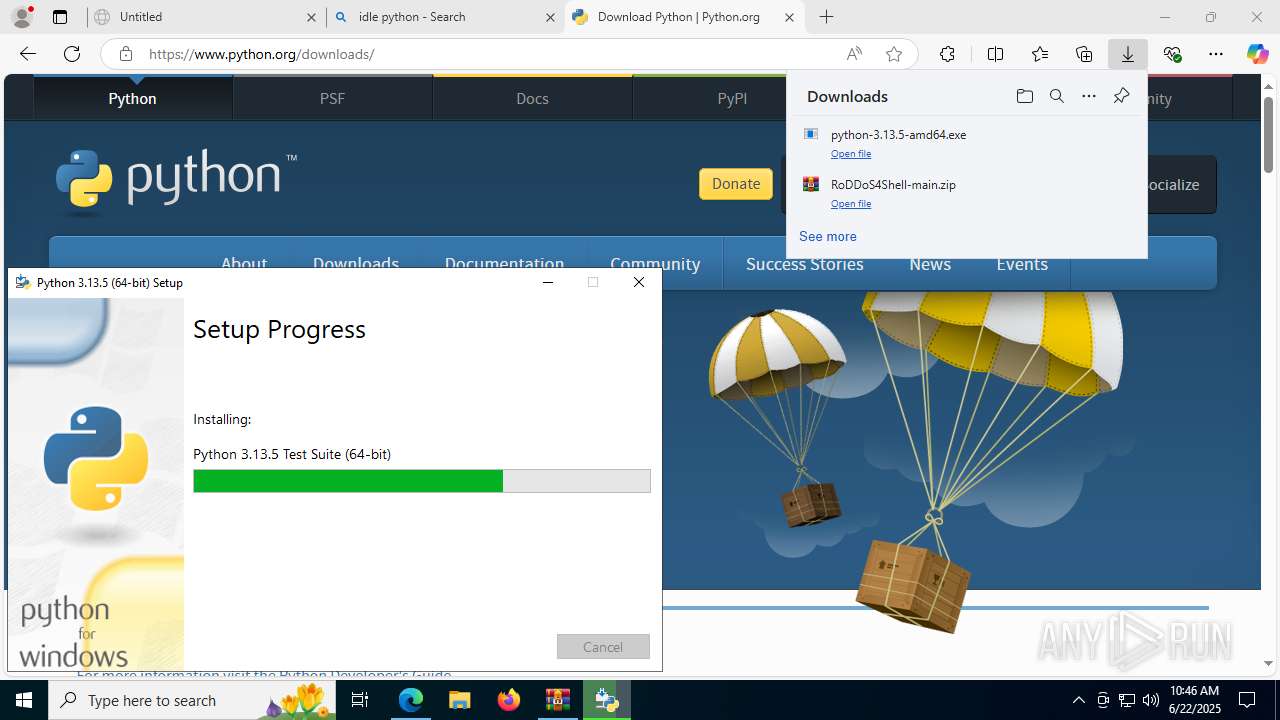
| 2800 | "C:\Users\admin\Downloads\python-3.13.5-amd64.exe" | C:\Users\admin\Downloads\python-3.13.5-amd64.exe | msedge.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.13.5 (64-bit) Version: 3.13.5150.0 Modules
| |||||||||||||||
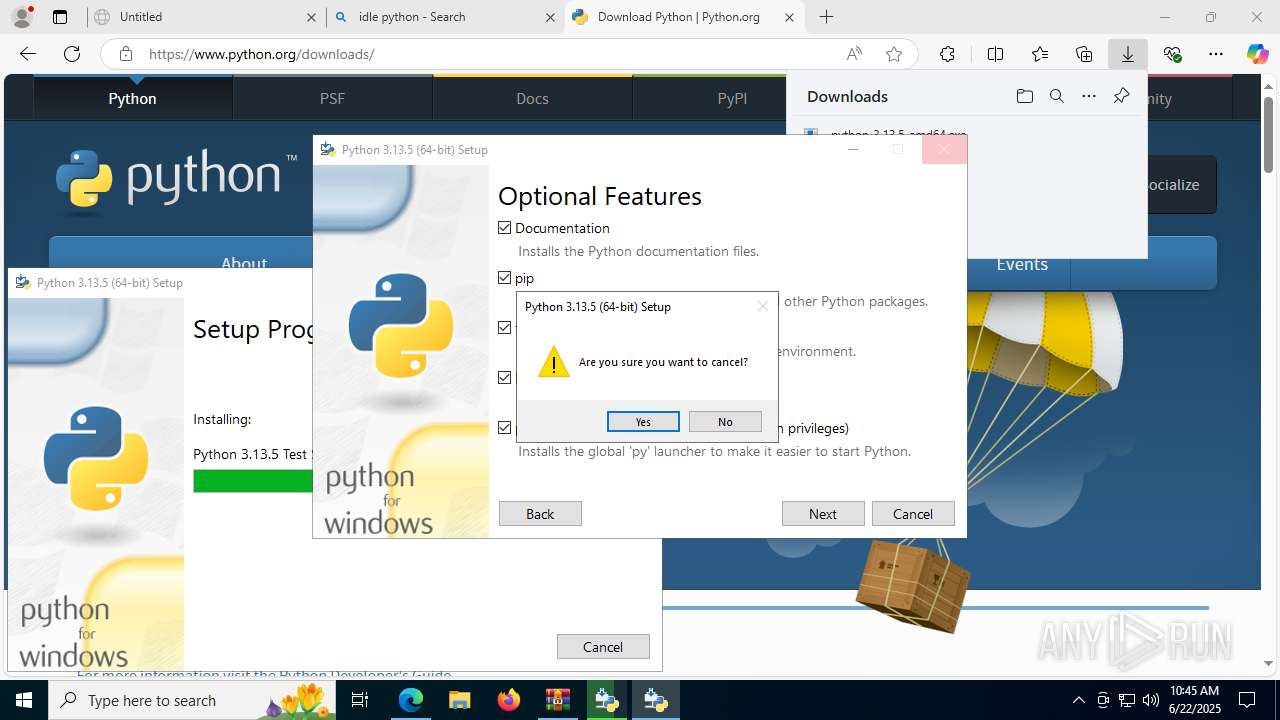
| 3392 | "C:\Users\admin\AppData\Local\Package Cache\{2a612b01-6a34-408a-b31b-2fa0f048823f}\python-3.13.5-amd64.exe" /burn.log.append "C:\Users\admin\AppData\Local\Temp\Python 3.13.5 (64-bit)_20250622104447.log" | C:\Users\admin\AppData\Local\Package Cache\{2a612b01-6a34-408a-b31b-2fa0f048823f}\python-3.13.5-amd64.exe | — | python-3.13.5-amd64.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.13.5 (64-bit) Exit code: 1602 Version: 3.13.5150.0 Modules
| |||||||||||||||
| 3624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --always-read-main-dll --field-trial-handle=7532,i,16447018790378724786,6424974890952781436,262144 --variations-seed-version --mojo-platform-channel-handle=7464 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3688 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2228,i,16447018790378724786,6424974890952781436,262144 --variations-seed-version --mojo-platform-channel-handle=2700 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3884 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/HTDBarsi/RoDDoS4Shell/archive/refs/heads/main.zip" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
59 859
Read events
52 084
Write events
3 129
Delete events
4 646
Modification events
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BB9C760CBD962F00 | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4AD4C9DD-7266-402F-8CC2-B9892DF5F278} | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6E30ECCB-5A3F-454A-8253-C4EECA965229} | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 722FB00CBD962F00 | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (3884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {52C0863E-64D1-42EA-8748-57DA71AFC6D5} | |||
Executable files
114
Suspicious files
721
Text files
1 842
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176830.TMP | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17683f.TMP | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17683f.TMP | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17683f.TMP | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17684f.TMP | — | |
MD5:— | SHA256:— | |||
| 3884 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17684f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
104
DNS requests
132
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3688 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:9i0k6ZLVWLko2Adg1mbf6SNEV4uN3q0osY2h1Utm0Wg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
3936 | svchost.exe | GET | 200 | 104.75.232.13:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.149.13:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.41.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7372 | SIHClient.exe | GET | 200 | 2.20.41.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7372 | SIHClient.exe | GET | 200 | 2.20.41.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6772 | svchost.exe | HEAD | 200 | 95.101.137.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750918744&P2=404&P3=2&P4=lwC7NhQSumwhxkZ9LTYFTtUNO2BewvyN1UrQC%2b4vtUtccwY0DpV1RBNO2H3ffGTWBFpwDKZHmjwV57Y%2bBWmWvA%3d%3d | unknown | — | — | whitelisted |
6772 | svchost.exe | GET | 206 | 95.101.137.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750918744&P2=404&P3=2&P4=lwC7NhQSumwhxkZ9LTYFTtUNO2BewvyN1UrQC%2b4vtUtccwY0DpV1RBNO2H3ffGTWBFpwDKZHmjwV57Y%2bBWmWvA%3d%3d | unknown | — | — | whitelisted |
6772 | svchost.exe | GET | 206 | 95.101.137.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750918744&P2=404&P3=2&P4=lwC7NhQSumwhxkZ9LTYFTtUNO2BewvyN1UrQC%2b4vtUtccwY0DpV1RBNO2H3ffGTWBFpwDKZHmjwV57Y%2bBWmWvA%3d%3d | unknown | — | — | whitelisted |
6772 | svchost.exe | HEAD | 200 | 95.101.137.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750918750&P2=404&P3=2&P4=JbJLMVoxBmR5YwmRn4Eztlln6kFt%2bC8AcxtsWUe52l4MXfekWBYbJsefT1KdamBU%2bQkHGu7FKB5QlImiITRCnw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4808 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3688 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3688 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3688 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3688 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
3688 | msedge.exe | 2.18.40.135:443 | copilot.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
codeload.github.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |