| download: | idbf.exe |
| Full analysis: | https://app.any.run/tasks/798bf299-cf51-4108-bff7-8e7bf5de01b0 |
| Verdict: | Malicious activity |
| Analysis date: | October 06, 2019, 06:15:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D4A9E36E56A0A7B78A4C53BE6F427036 |
| SHA1: | B9152C02F2F34230904933954EA4A97C28C570C1 |
| SHA256: | 05728FD0DF896645CD8377ACE0CF2383EFCD6BAAFE72C66B7000F0A18A8B7C66 |
| SSDEEP: | 98304:D07phDseTWuvoASPqink4oV1ggxDbmh8U1x9:D0Lsg9oPPXhottAH9 |
MALICIOUS
Loads dropped or rewritten executable
- idbf.exe (PID: 3148)
- sysprep.exe (PID: 1200)
- svchost.exe (PID: 2580)
- spoolsv.exe (PID: 1192)
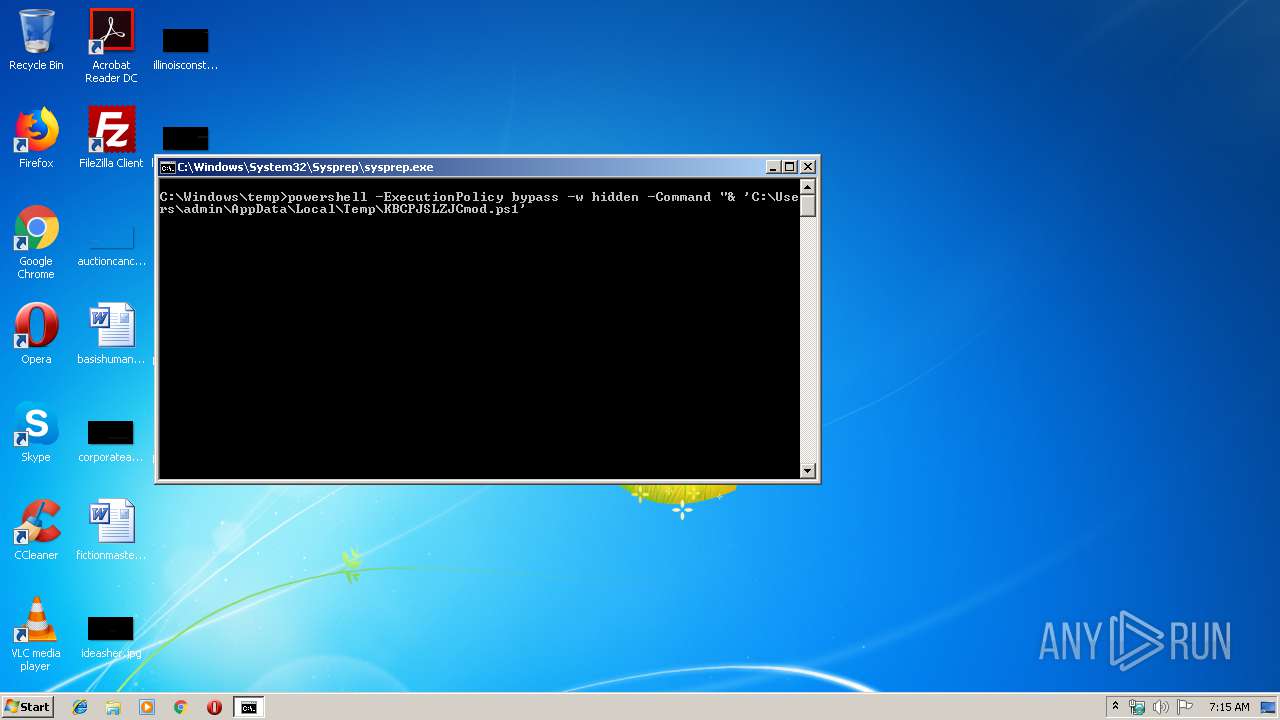
Executes PowerShell scripts
- cmd.exe (PID: 2448)
- cmd.exe (PID: 2944)
Starts NET.EXE to view/change users group
- powershell.exe (PID: 2316)
Changes settings of System certificates
- svchost.exe (PID: 2580)
Creates or modifies windows services
- reg.exe (PID: 2300)
Writes to a start menu file
- regsvr32.exe (PID: 3956)
Changes the autorun value in the registry
- regsvr32.exe (PID: 3956)
Changes internet zones settings
- rundll32.exe (PID: 3508)
- ie4uinit.exe (PID: 2996)
Loads the Task Scheduler COM API
- mctadmin.exe (PID: 1812)
- rundll32.exe (PID: 2704)
SUSPICIOUS
Executable content was dropped or overwritten
- idbf.exe (PID: 3148)
- powershell.exe (PID: 3056)
- wusa.exe (PID: 3032)
- spoolsv.exe (PID: 1192)
- powershell.exe (PID: 2316)
Creates files in the user directory
- powershell.exe (PID: 3056)
- powershell.exe (PID: 2316)
Starts CMD.EXE for commands execution
- idbf.exe (PID: 3148)
- sysprep.exe (PID: 1200)
- svchost.exe (PID: 2580)
- powershell.exe (PID: 2316)
Creates files in the Windows directory
- wusa.exe (PID: 3032)
- powershell.exe (PID: 3056)
- sysprep.exe (PID: 1200)
- svchost.exe (PID: 2580)
- spoolsv.exe (PID: 1192)
- powershell.exe (PID: 2316)
Removes files from Windows directory
- wusa.exe (PID: 3032)
- spoolsv.exe (PID: 1192)
Adds / modifies Windows certificates
- svchost.exe (PID: 2580)
Executed via COM
- TSTheme.exe (PID: 2456)
Uses ICACLS.EXE to modify access control list
- powershell.exe (PID: 2316)
Uses REG.EXE to modify Windows registry
- powershell.exe (PID: 2316)
Writes to a desktop.ini file (may be used to cloak folders)
- regsvr32.exe (PID: 3812)
- WinMail.exe (PID: 2836)
- ie4uinit.exe (PID: 3724)
- rundll32.exe (PID: 2704)
- mctadmin.exe (PID: 1812)
- regsvr32.exe (PID: 3956)
Application launched itself
- ie4uinit.exe (PID: 3724)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 2996)
Changes the started page of IE
- ie4uinit.exe (PID: 2996)
INFO
Manual execution by user
- regsvr32.exe (PID: 3812)
- unregmp2.exe (PID: 3152)
- rundll32.exe (PID: 3508)
- regsvr32.exe (PID: 3956)
- chrmstp.exe (PID: 2348)
- ie4uinit.exe (PID: 3724)
- ie4uinit.exe (PID: 2996)
- WinMail.exe (PID: 2836)
- sidebar.exe (PID: 3676)
- mctadmin.exe (PID: 1812)
- rundll32.exe (PID: 2704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:01+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 3782656 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31e9 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.8.2 |
| ProductVersionNumber: | 1.7.8.2 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | KBCPJSLZJC software |
| CompanyName: | KBCPJSLZJC company llc |
| FileDescription: | KBCPJSLZJC software package |
| FileVersion: | 1.7.8.2 |
| LegalCopyright: | KBCPJSLZJC company |
| LegalTrademarks: | KBCPJSLZJC |
| ProductName: | KBCPJSLZJC; software package |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:01 |
| Detected languages: |
|
| Comments: | KBCPJSLZJC software |
| CompanyName: | KBCPJSLZJC company llc |
| FileDescription: | KBCPJSLZJC software package |
| FileVersion: | 1.7.8.2 |
| LegalCopyright: | KBCPJSLZJC company |
| LegalTrademarks: | KBCPJSLZJC |
| ProductName: | KBCPJSLZJC; software package |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006068 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45071 |
.rdata | 0x00008000 | 0x00001250 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04164 |
.data | 0x0000A000 | 0x00399058 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.13238 |
.ndata | 0x003A4000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x003AD000 | 0x00033580 | 0x00033600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.09721 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2992 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.98192 | 45363 | UNKNOWN | English - United States | RT_ICON |
3 | 5.32439 | 38056 | UNKNOWN | English - United States | RT_ICON |
4 | 5.32436 | 21640 | UNKNOWN | English - United States | RT_ICON |
5 | 5.25901 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 5.48147 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 5.52924 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 5.69886 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 5.71526 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 3.03466 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
120
Monitored processes
45
Malicious processes
13
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Windows\system32\takeown.exe" /A /F rfxvmt.dll | C:\Windows\system32\takeown.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1192 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1200 | "C:\Windows\System32\Sysprep\sysprep.exe" | C:\Windows\System32\Sysprep\sysprep.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Preparation Tool Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1812 | "C:\Windows\System32\mctadmin.exe" | C:\Windows\System32\mctadmin.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MCTAdmin Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | "C:\Windows\system32\icacls.exe" rfxvmt.dll /grant "NT SERVICE\TrustedInstaller:F" | C:\Windows\system32\icacls.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Windows\system32\wusa.exe" "C:\Windows\system32\wusa.exe" C:\Users\admin\AppData\Local\Temp\uac.cab /extract:C:\Windows\System32\Sysprep\ | C:\Windows\system32\wusa.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2236 | "C:\Windows\System32\Sysprep\sysprep.exe" "C:\Windows\System32\Sysprep\sysprep.exe" | C:\Windows\System32\Sysprep\sysprep.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Preparation Tool Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2280 | "C:\Windows\System32\Sysprep\sysprep.exe" | C:\Windows\System32\Sysprep\sysprep.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Preparation Tool Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2284 | C:\Windows\System32\ie4uinit.exe -ClearIconCache | C:\Windows\System32\ie4uinit.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IE Per-User Initialization Utility Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Windows\system32\reg.exe" add HKLM\system\currentcontrolset\services\TermService\parameters /v ServiceDLL /t REG_EXPAND_SZ /d %SystemRoot%\help\tmp5211.dat /f | C:\Windows\system32\reg.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 216
Read events
3 271
Write events
942
Delete events
3
Modification events
| (PID) Process: | (3148) idbf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3148) idbf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3056) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3056) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3056) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2316) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4088) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server\WinStations\RDP-Tcp |
| Operation: | write | Name: | PortNumber |
Value: 7201 | |||
| (PID) Process: | (2300) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\TermService\Parameters |
| Operation: | write | Name: | ServiceDLL |
Value: %SystemRoot%\help\tmp5211.dat | |||
| (PID) Process: | (2580) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server |
| Operation: | write | Name: | fDenyTSConnections |
Value: 0 | |||
| (PID) Process: | (2580) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Terminal Server |
| Operation: | write | Name: | FSingleSessionPerUser |
Value: 1 | |||
Executable files
7
Suspicious files
25
Text files
291
Unknown types
139
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | idbf.exe | C:\Users\admin\AppData\Local\Temp\nsp5A82.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 3056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TVOYDS07OXNHTA1I2XA4.temp | — | |
MD5:— | SHA256:— | |||
| 3396 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3396_2 | — | |
MD5:— | SHA256:— | |||
| 3396 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3396_3 | — | |
MD5:— | SHA256:— | |||
| 3396 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3396_4 | — | |
MD5:— | SHA256:— | |||
| 3396 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3396_5 | — | |
MD5:— | SHA256:— | |||
| 3396 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_3396_6 | — | |
MD5:— | SHA256:— | |||
| 3032 | wusa.exe | C:\Windows\System32\Sysprep\$dpx$.tmp\629d0a03b8edb048940d3ffb129a6e24.tmp | — | |
MD5:— | SHA256:— | |||
| 3032 | wusa.exe | C:\Windows\Logs\DPX\setuperr.log | — | |
MD5:— | SHA256:— | |||
| 1200 | sysprep.exe | C:\Windows\System32\Sysprep\Panther\setuperr.log | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | svchost.exe | 185.163.47.214:443 | ggaooopdj44.pw | MivoCloud SRL | RO | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ggaooopdj44.pw |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2580 | svchost.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |
Process | Message |
|---|---|
sysprep.exe | Fubuki at your service.
|