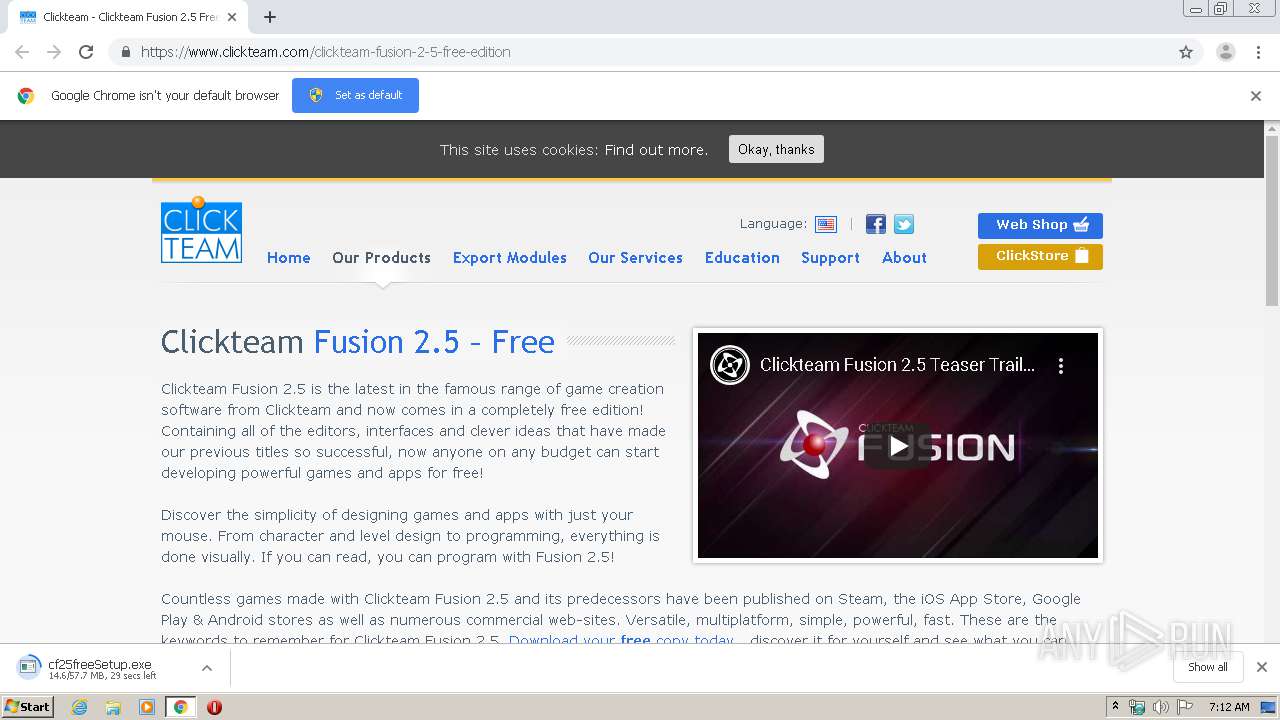
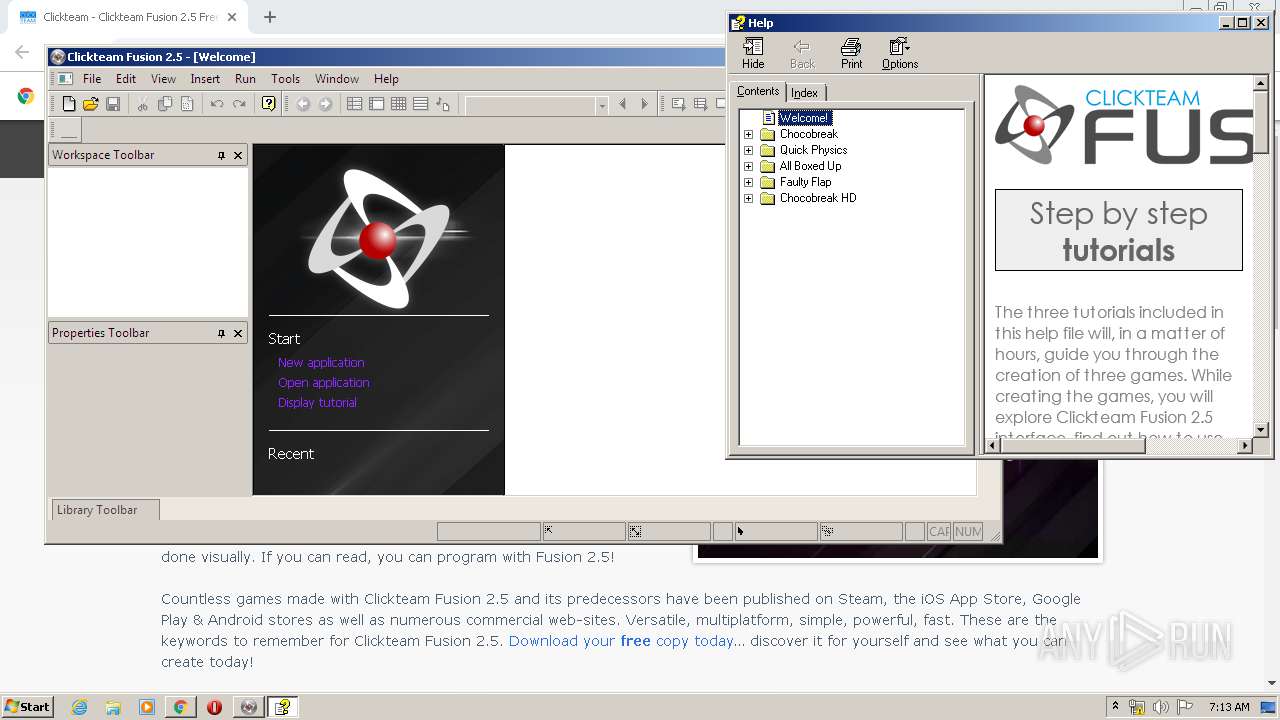
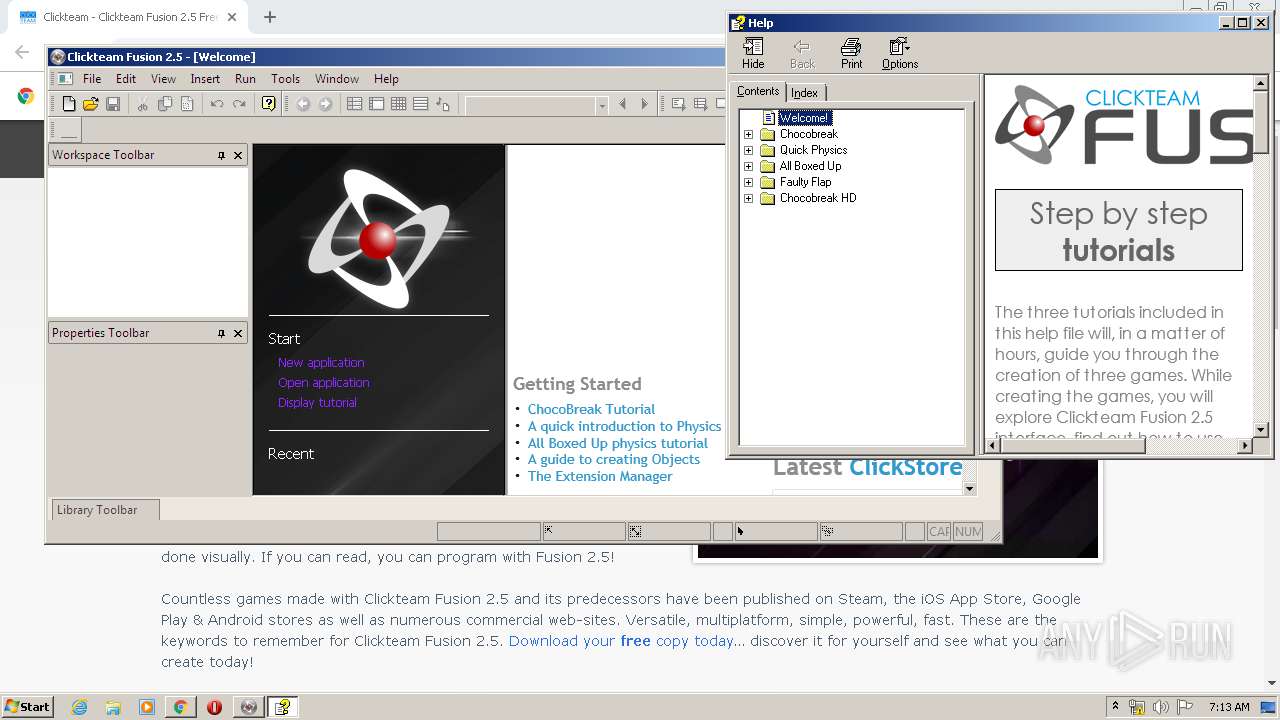
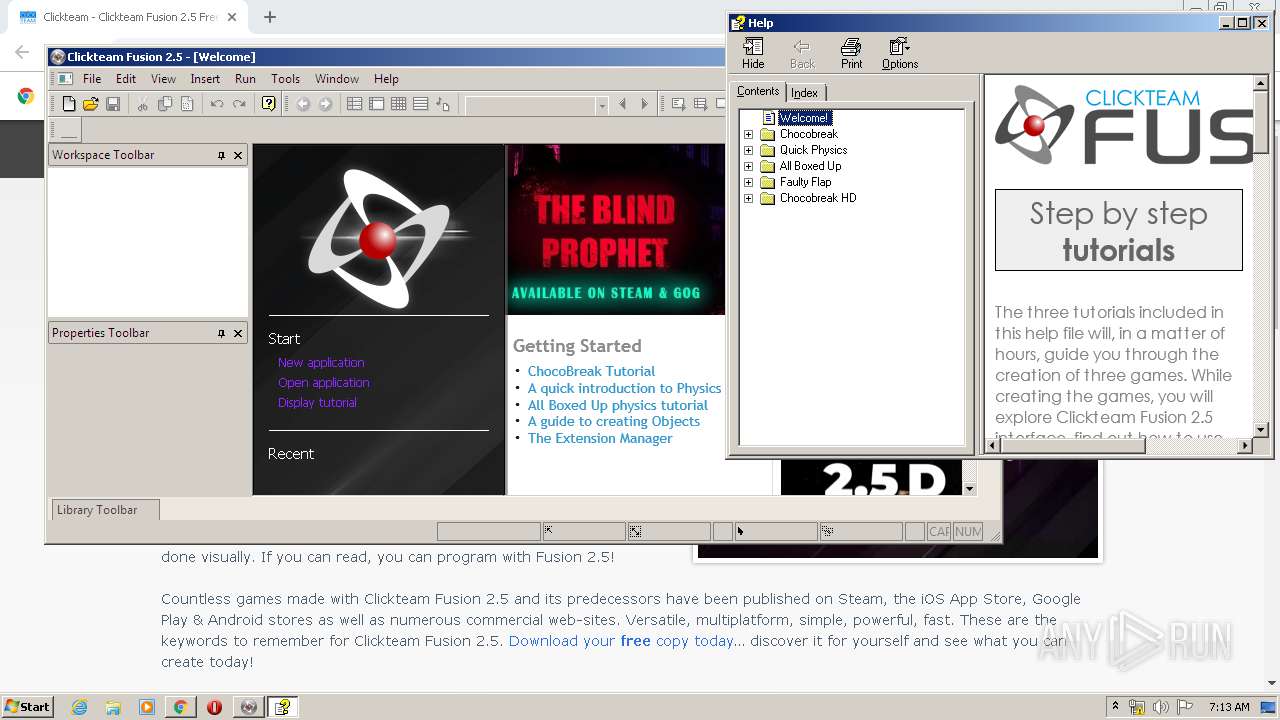
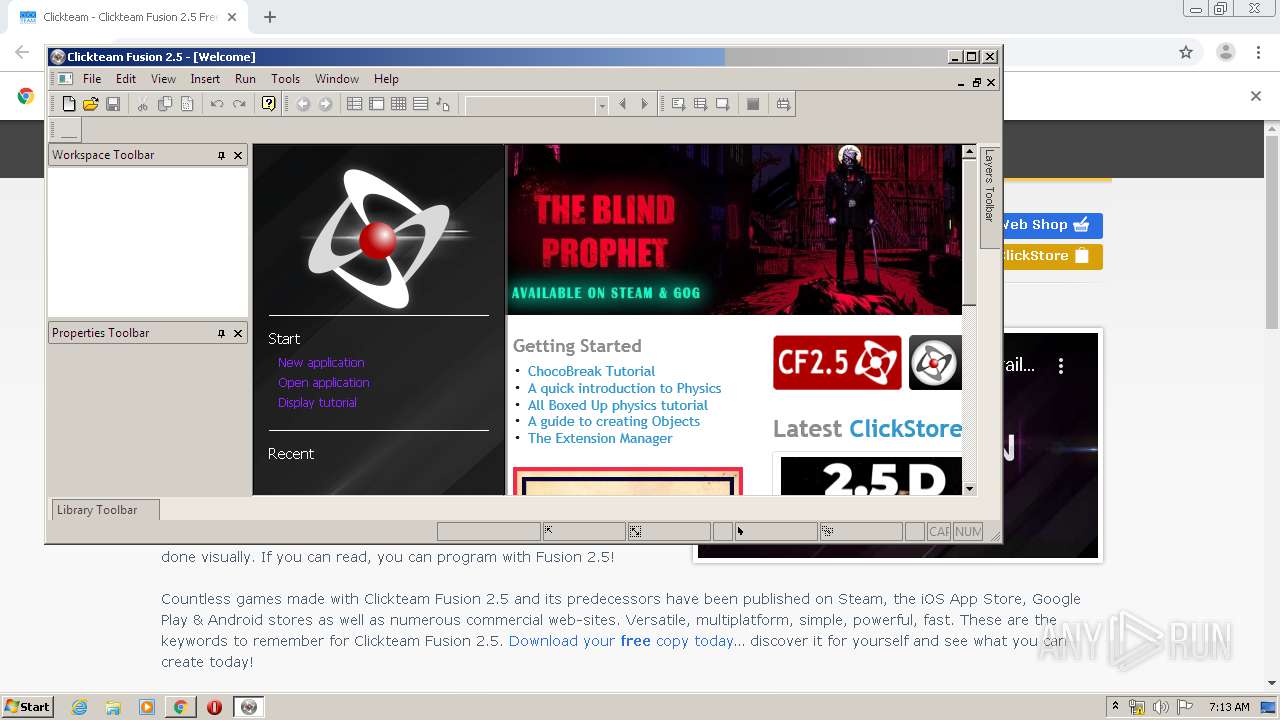
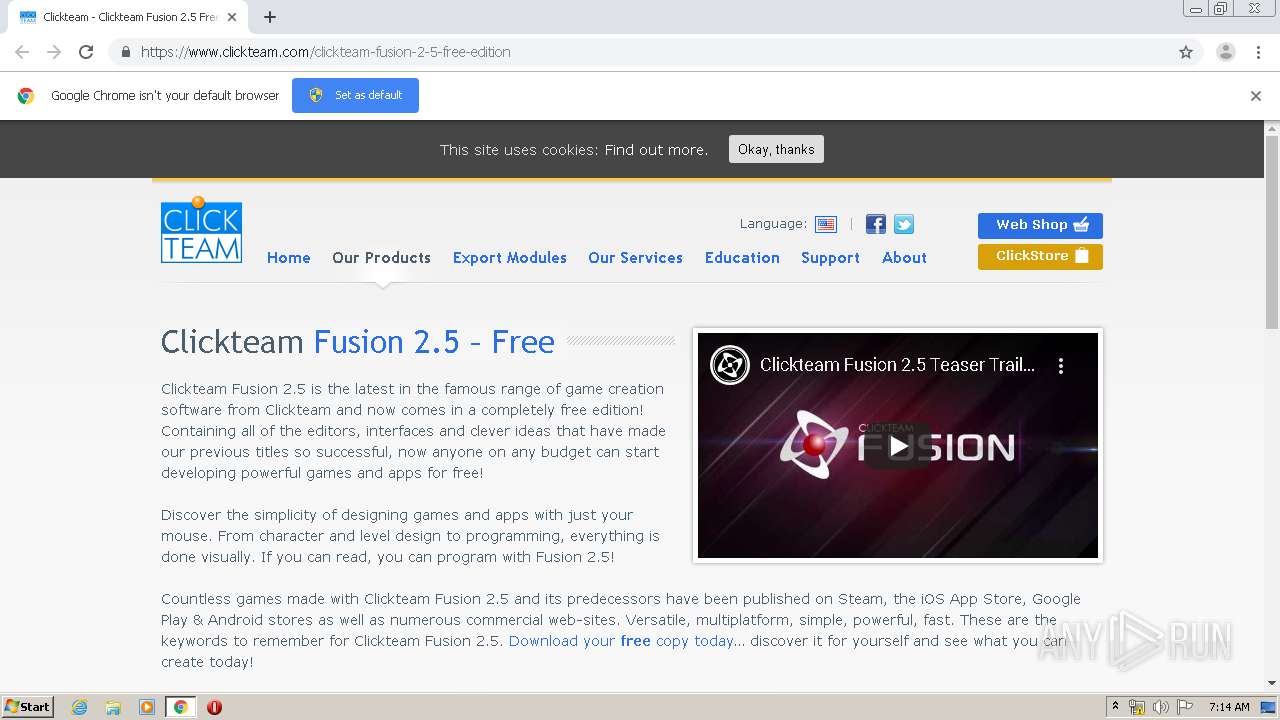
| URL: | https://www.clickteam.com/clickteam-fusion-2-5-free-edition |
| Full analysis: | https://app.any.run/tasks/4e986cbb-fa0c-4bfa-abaa-6cff2a873369 |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2020, 06:11:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 600D70EBE1AF4BE775AF8183CA47FA7C |
| SHA1: | 4204B249E92A9975B3C56B49BB1021AB4DE5900B |
| SHA256: | 0564EE554BCB8F5F75A7F84DB6790C12A4C92D2EE6E86FA0F6AC229555F837F8 |
| SSDEEP: | 3:N8DSL7hUeMpJQ29BMR/:2OL73Mk296R/ |
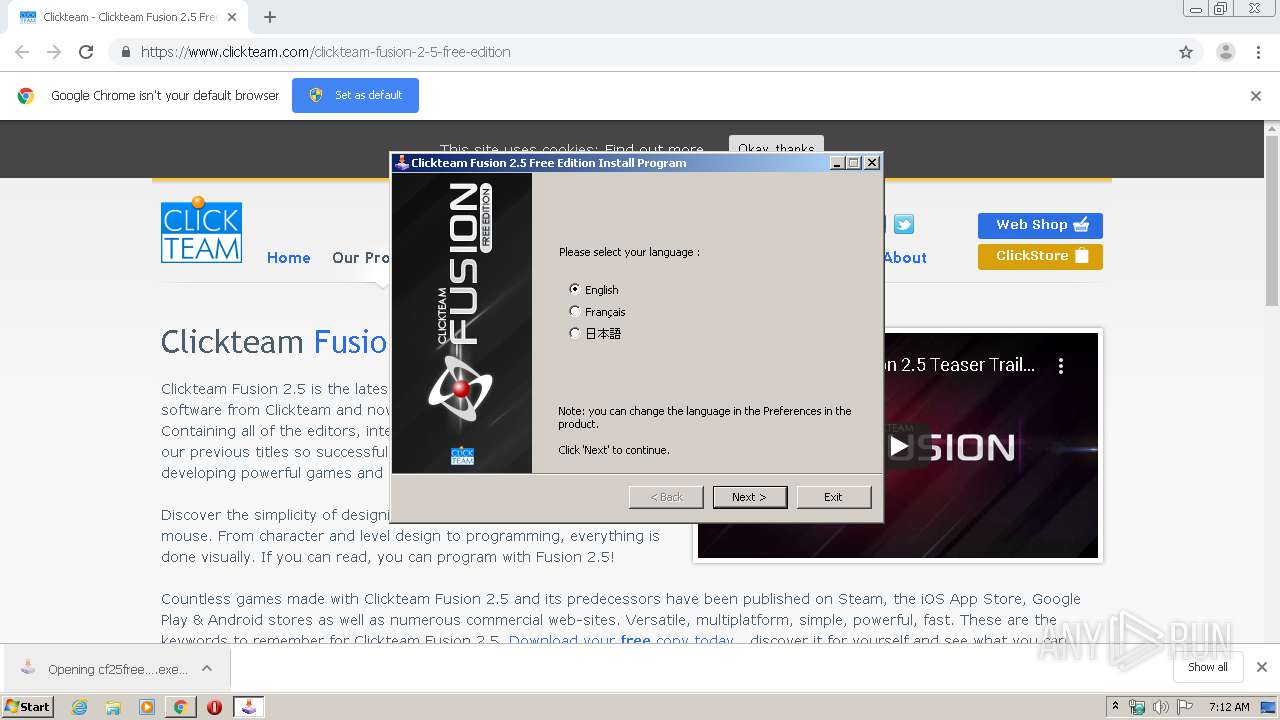
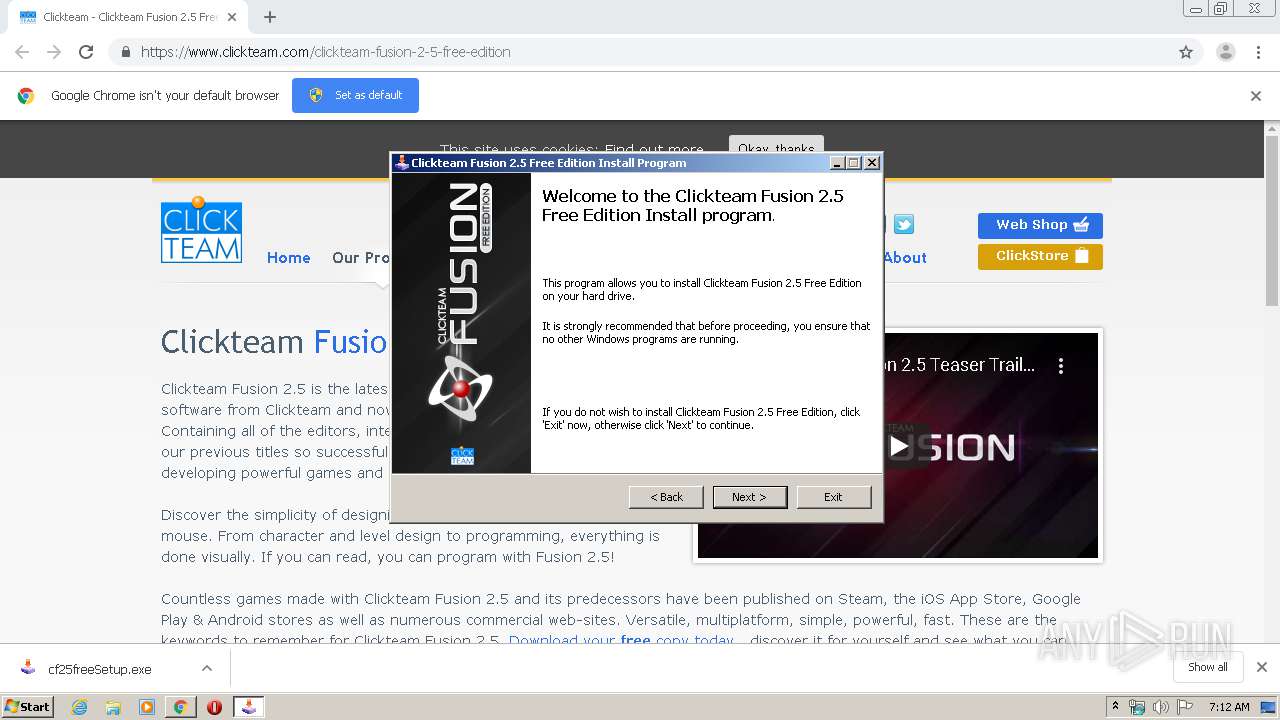
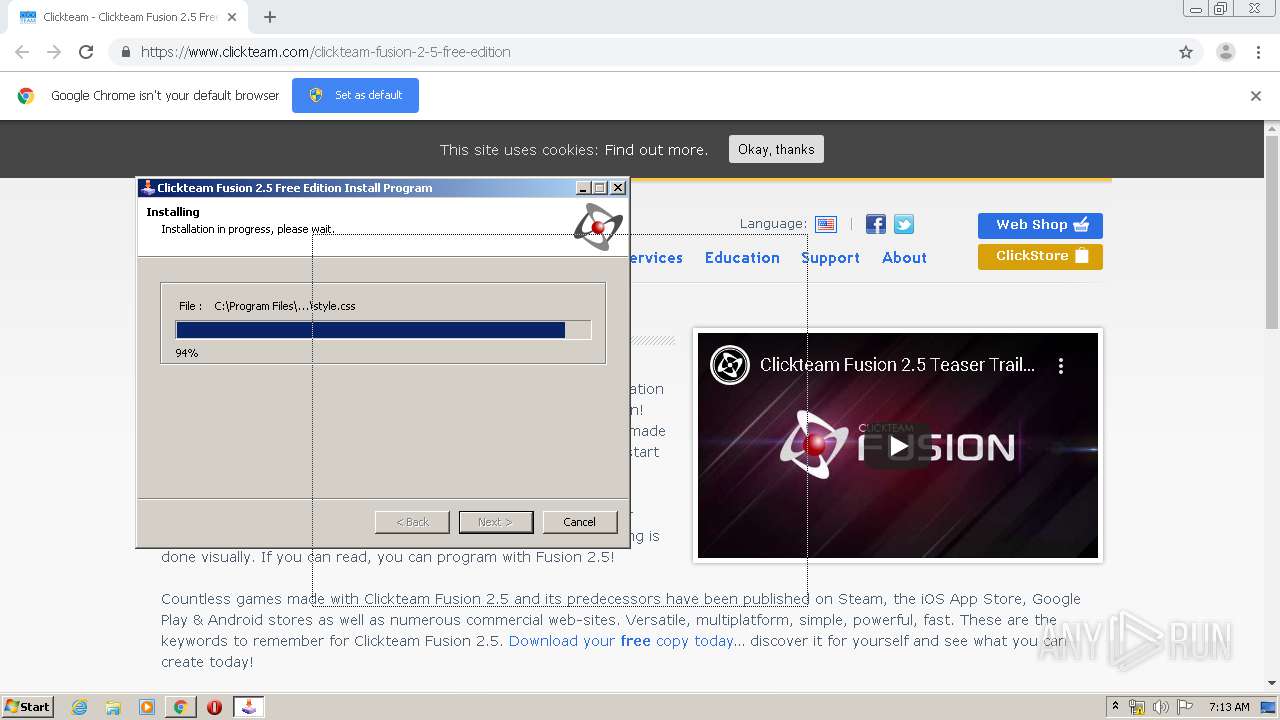
MALICIOUS
Application was dropped or rewritten from another process
- cf25freeSetup.exe (PID: 2124)
- cf25freeSetup.exe (PID: 2728)
- mmf2u.exe (PID: 3928)
- edrt.exe (PID: 1444)
Loads dropped or rewritten executable
- mmf2u.exe (PID: 3928)
- edrt.exe (PID: 1444)
SUSPICIOUS
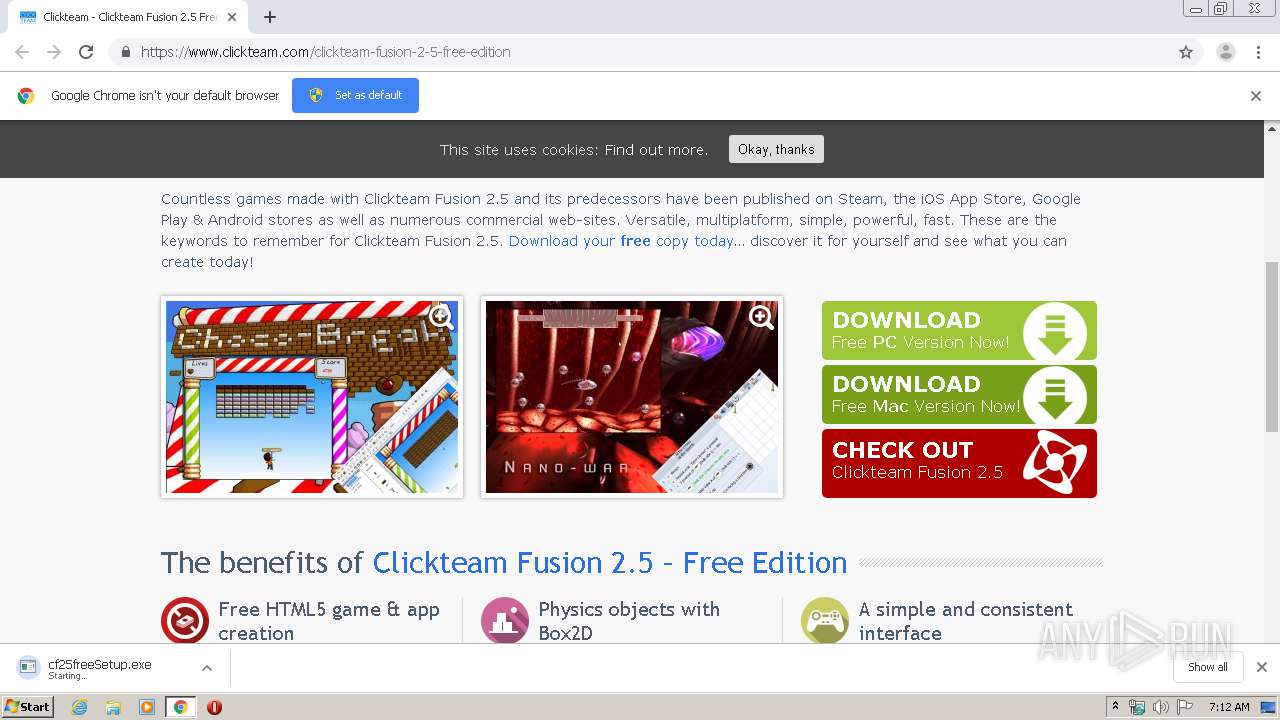
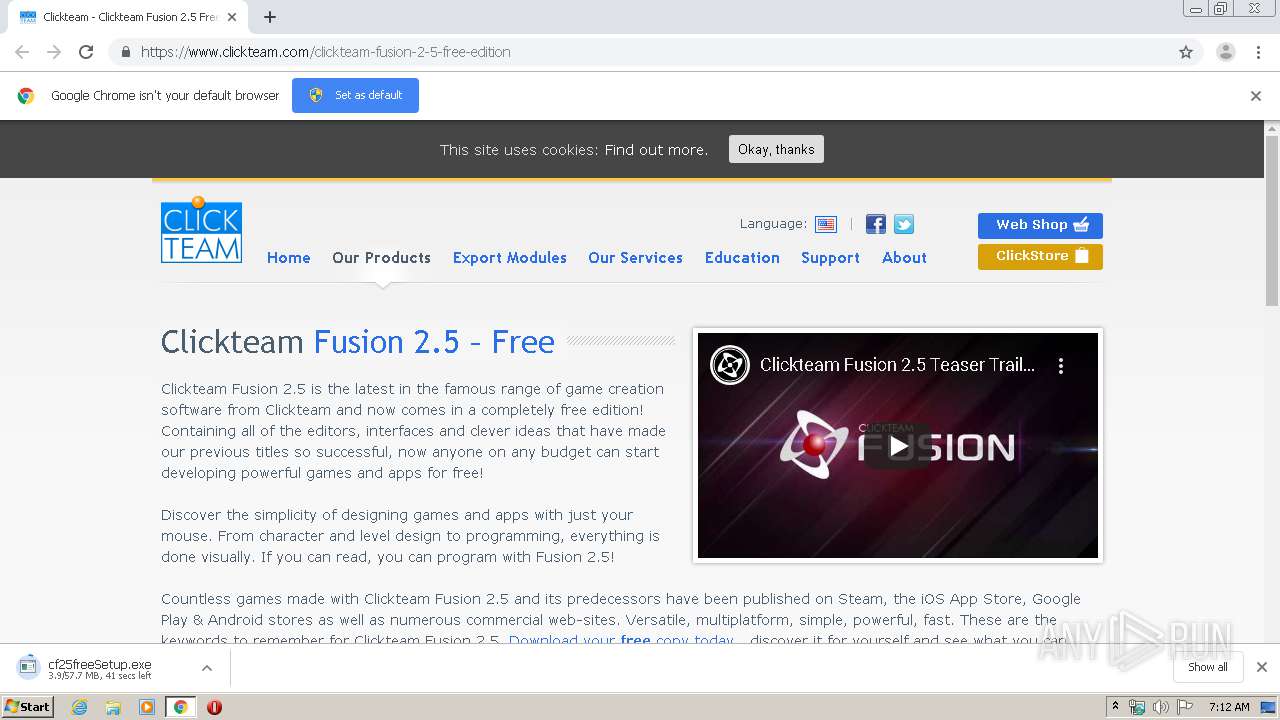
Executable content was dropped or overwritten
- chrome.exe (PID: 3820)
- cf25freeSetup.exe (PID: 2124)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3820)
Modifies the open verb of a shell class
- cf25freeSetup.exe (PID: 2124)
Reads Internet Cache Settings
- mmf2u.exe (PID: 3928)
Creates files in the user directory
- mmf2u.exe (PID: 3928)
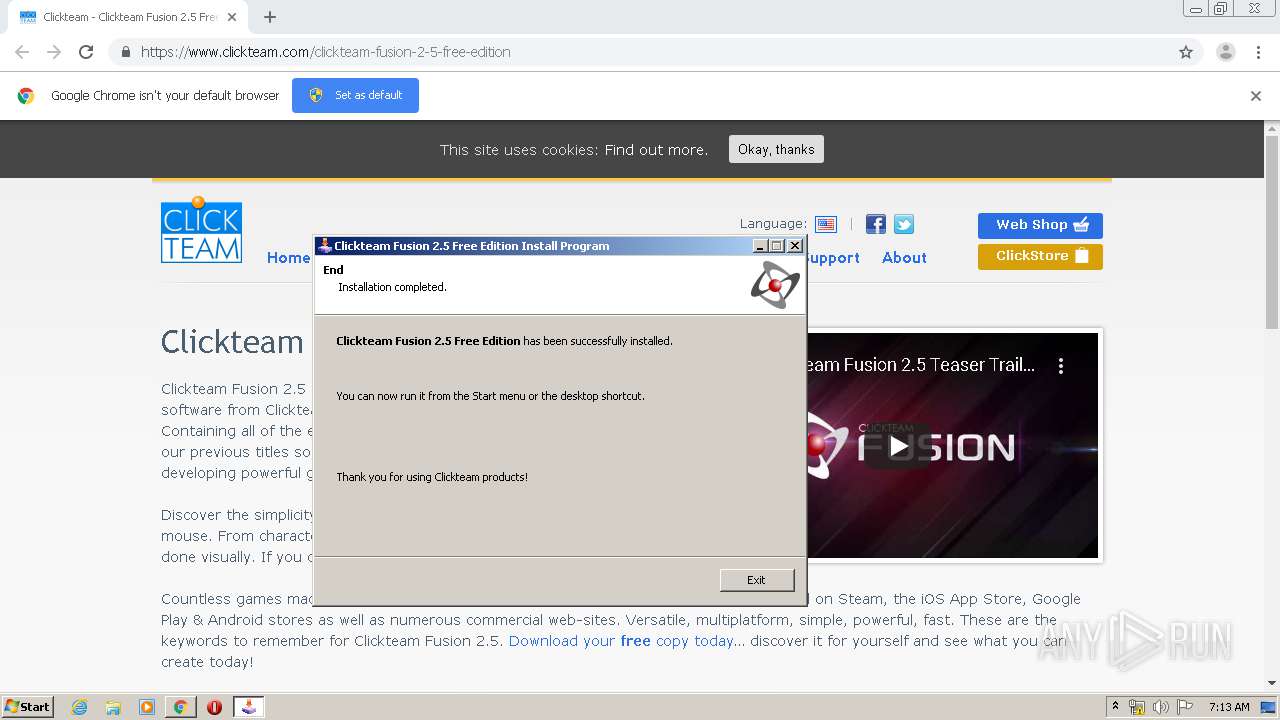
Creates a software uninstall entry
- cf25freeSetup.exe (PID: 2124)
Reads internet explorer settings
- mmf2u.exe (PID: 3928)
- hh.exe (PID: 4004)
Creates files in the program directory
- cf25freeSetup.exe (PID: 2124)
INFO
Reads the hosts file
- chrome.exe (PID: 3236)
- chrome.exe (PID: 3820)
Dropped object may contain Bitcoin addresses
- cf25freeSetup.exe (PID: 2124)
Reads settings of System Certificates
- chrome.exe (PID: 3820)
- mmf2u.exe (PID: 3928)
- chrome.exe (PID: 3236)
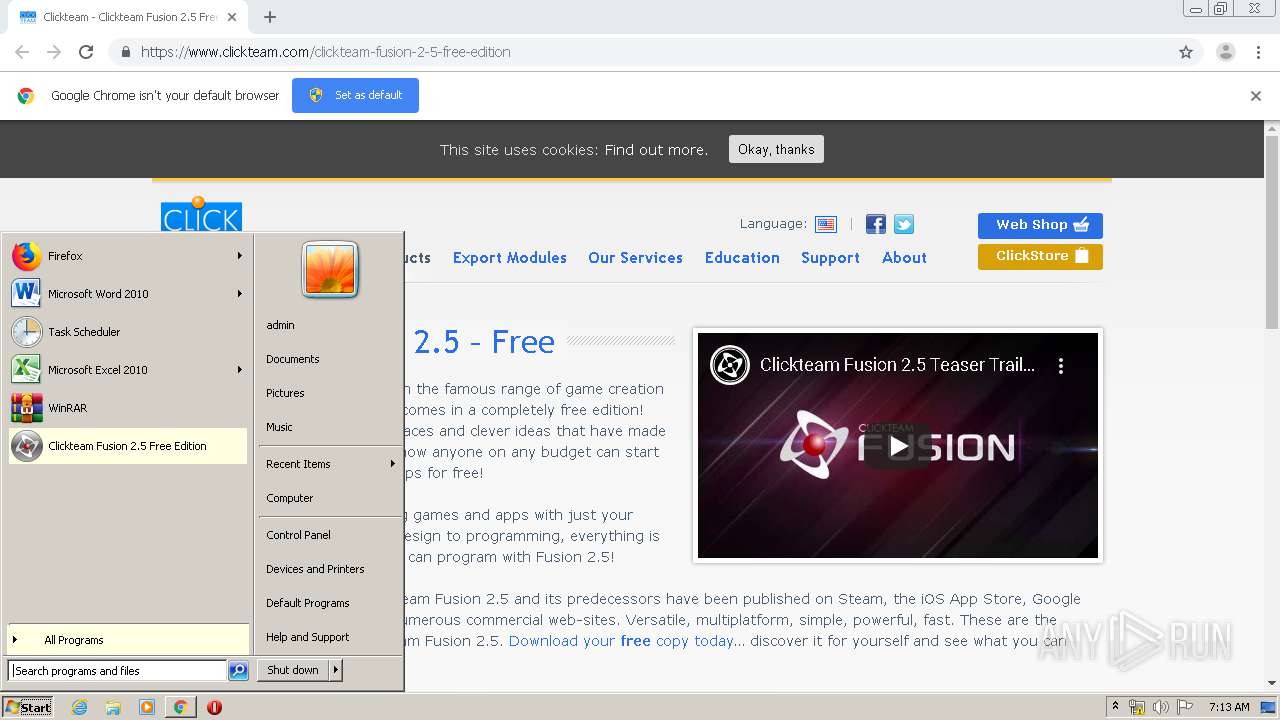
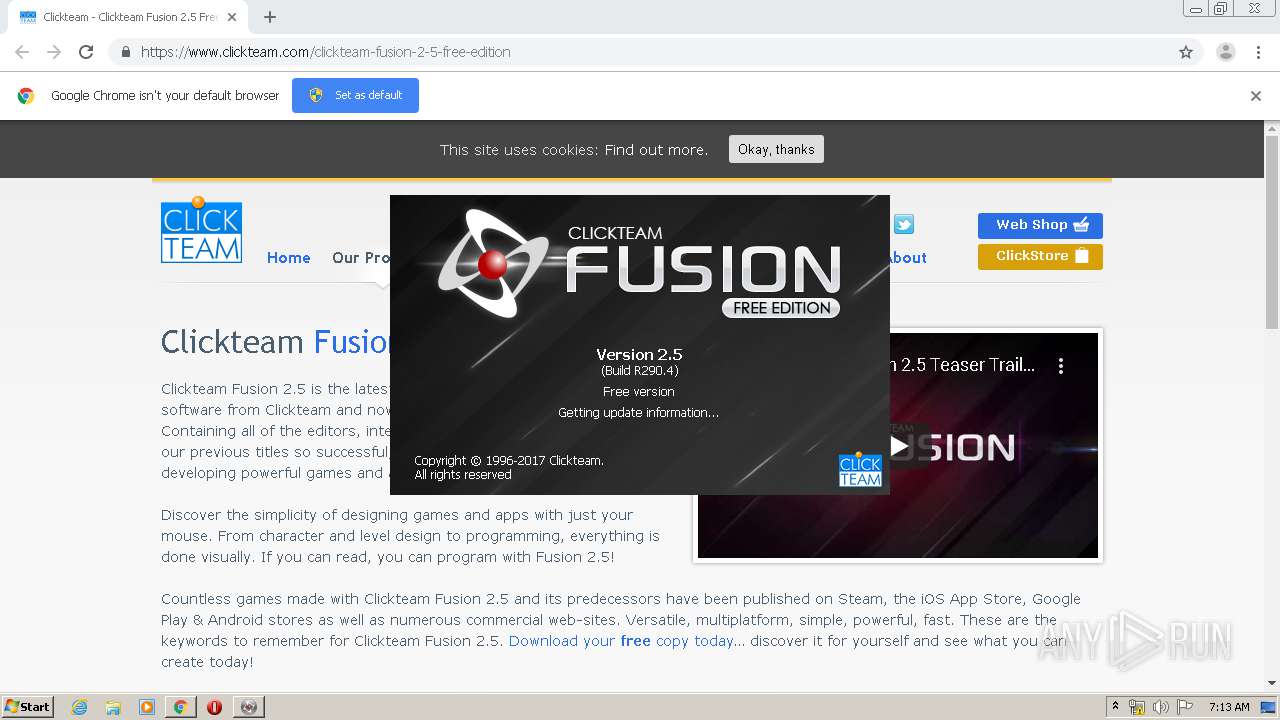
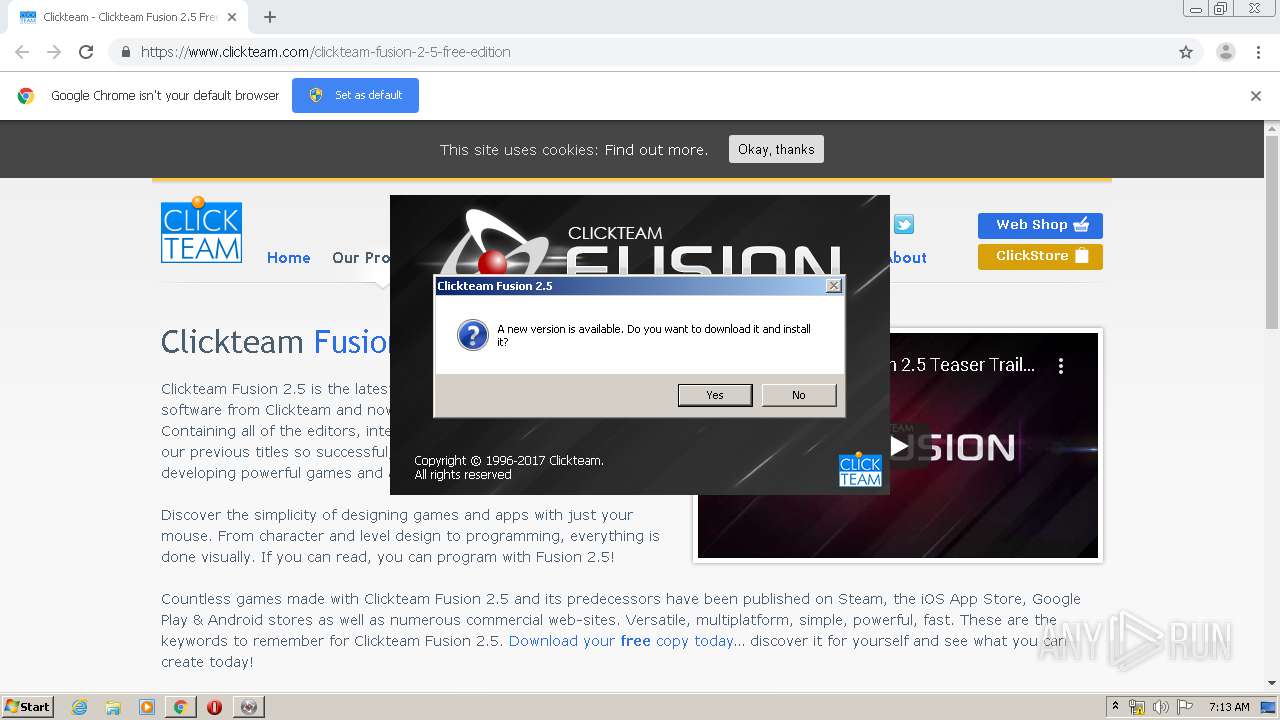
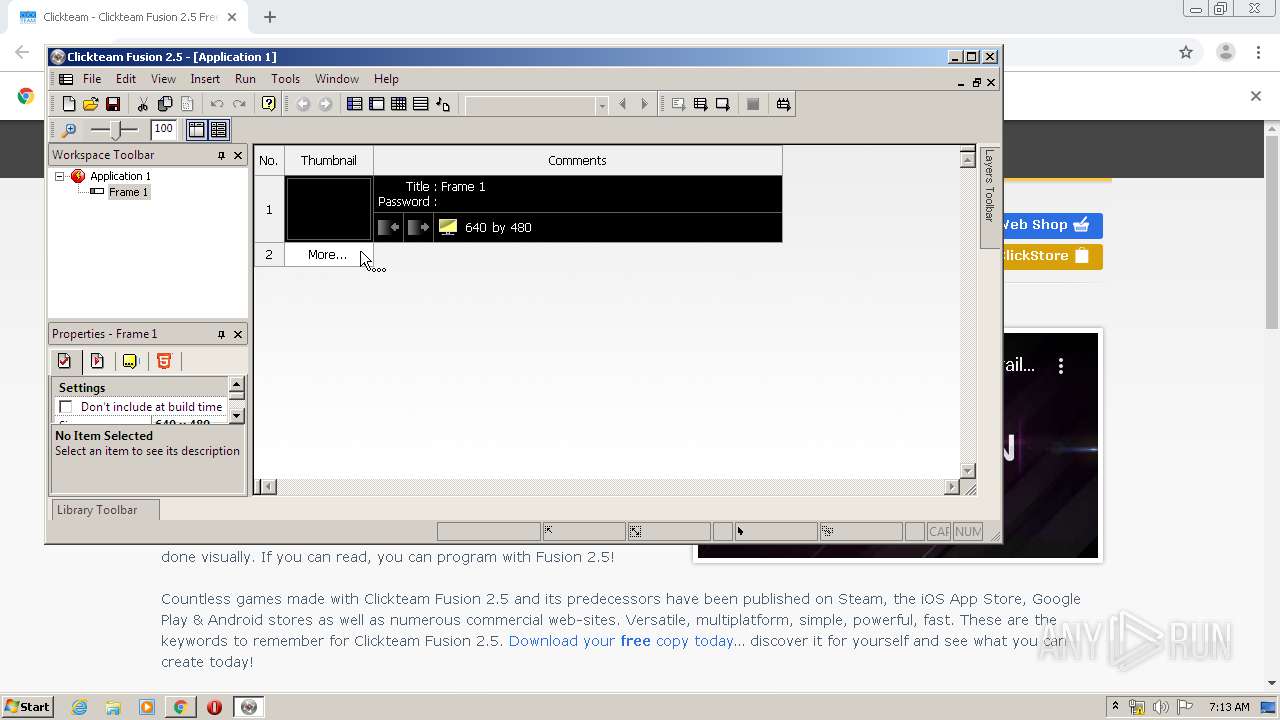
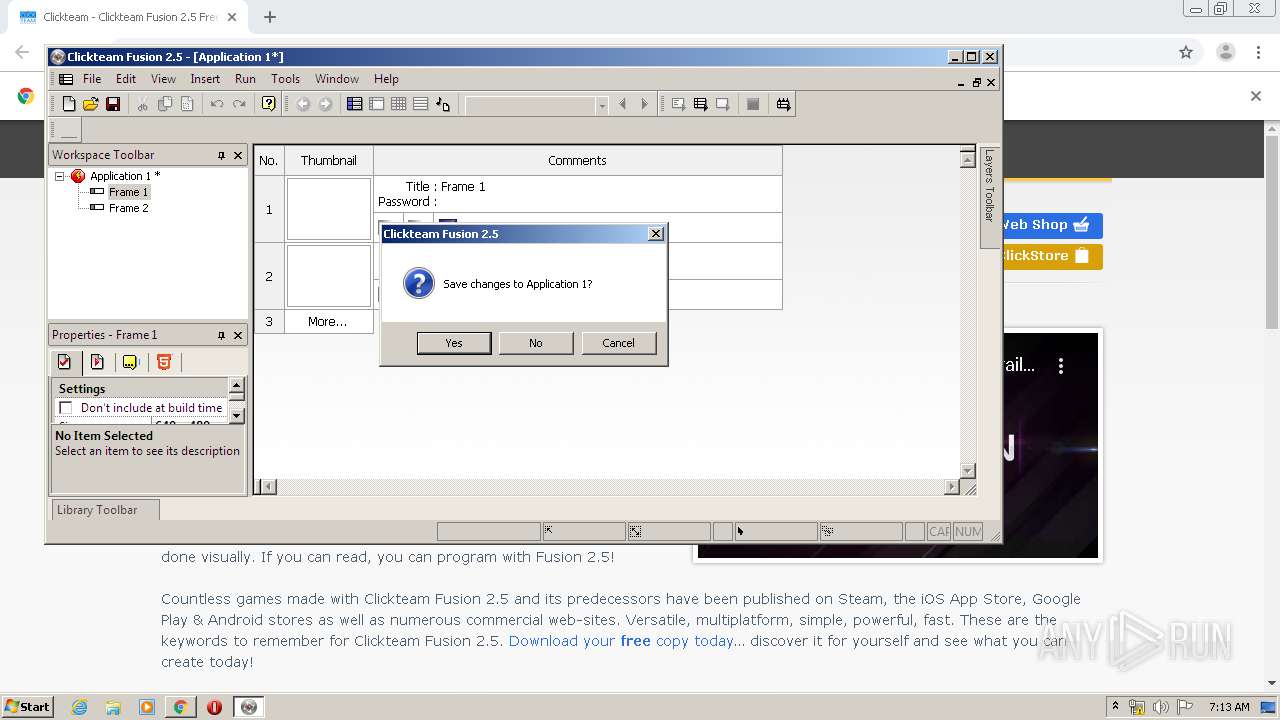
Manual execution by user
- mmf2u.exe (PID: 3928)
Reads Internet Cache Settings
- chrome.exe (PID: 3820)
Application launched itself
- chrome.exe (PID: 3820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
34
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,10726458680723332394,69278293526918667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9120741641082015675 --mojo-platform-channel-handle=4492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,10726458680723332394,69278293526918667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15585287094899464533 --mojo-platform-channel-handle=5032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1064,10726458680723332394,69278293526918667,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2813303003422959907 --mojo-platform-channel-handle=4388 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=272 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Clickteam Fusion 2.5 Free Edition\Data\Runtime\Unicode\edrt.exe" /F"C:\Users\admin\AppData\Local\Temp\mft498A.tmp\app0.ccn" /P"RunCom11039984" | C:\Program Files\Clickteam Fusion 2.5 Free Edition\Data\Runtime\Unicode\edrt.exe | — | mmf2u.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,10726458680723332394,69278293526918667,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3799210437166604402 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,10726458680723332394,69278293526918667,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5443815626931456871 --mojo-platform-channel-handle=3052 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,10726458680723332394,69278293526918667,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15583304158762001466 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3616 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,10726458680723332394,69278293526918667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8998859011158173065 --mojo-platform-channel-handle=4956 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1064,10726458680723332394,69278293526918667,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2674308098746583967 --mojo-platform-channel-handle=4632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 891
Read events
1 488
Write events
395
Delete events
8
Modification events
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3820-13232009527162250 |
Value: 259 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3820) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
52
Suspicious files
114
Text files
903
Unknown types
298
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E9FE037-EEC.pma | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\adbff713-7253-4710-bcbc-166ddc0cda70.tmp | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:AC43135B8C9FED46A92448C4E711F45C | SHA256:D840BA7CEBACF86DDBAD75BFB61A53449AA7AE3DE6B8ADC97FE45624626A6F09 | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e0f2.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa6e131.TMP | text | |
MD5:AC43135B8C9FED46A92448C4E711F45C | SHA256:D840BA7CEBACF86DDBAD75BFB61A53449AA7AE3DE6B8ADC97FE45624626A6F09 | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e2b7.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
52
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3928 | mmf2u.exe | GET | 307 | 198.74.56.211:80 | http://startpane.clickteam.com/welcomefree.html?days=0;count=1;lang=9;steam=0;id=0 | US | html | 284 b | shared |
3928 | mmf2u.exe | GET | 200 | 45.79.185.105:80 | http://oogaboogawooga.clickteam.com/welcomeFuncs.js | US | text | 778 b | unknown |
3928 | mmf2u.exe | GET | 200 | 198.74.56.211:80 | http://www.clickteam.com/webftp/files/mmf2/update/upd.php?cnf=K5C13H2C16W15121R2KW6JTFYMRW6JTFYMRW6111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111111 | US | text | 135 b | malicious |
3928 | mmf2u.exe | GET | 200 | 45.79.185.105:80 | http://oogaboogawooga.clickteam.com/welcomefree.html?days=0%3bcount=1%3blang=9%3bsteam=0%3bid=0 | US | html | 298 b | unknown |
3928 | mmf2u.exe | GET | 301 | 45.79.185.105:80 | http://oogaboogawooga.clickteam.com/startpane-en | US | text | 778 b | unknown |
3928 | mmf2u.exe | GET | 200 | 45.79.185.105:80 | http://oogaboogawooga.clickteam.com/ | US | html | 5.83 Kb | unknown |
3928 | mmf2u.exe | GET | 200 | 45.79.185.105:80 | http://oogaboogawooga.clickteam.com/wp-content/plugins/arscode-ninja-popups/tooltipster/tooltipster.bundle.min.css?ver=6c384dc662603955acc21c91176981fa | US | text | 1.07 Kb | unknown |
3928 | mmf2u.exe | GET | 200 | 198.74.56.211:80 | http://indiegames.clickteam.com/wp-content/uploads/JamesBonk_Splash-209x118.jpg | US | image | 10.2 Kb | shared |
3928 | mmf2u.exe | GET | 200 | 45.79.185.105:80 | http://oogaboogawooga.clickteam.com/wp-content/plugins/arscode-ninja-popups/tooltipster/plugins/tooltipster/sideTip/themes/tooltipster-sideTip-light.min.css?ver=6c384dc662603955acc21c91176981fa | US | text | 318 b | unknown |
3928 | mmf2u.exe | GET | 200 | 45.79.185.105:80 | http://oogaboogawooga.clickteam.com/wp-includes/js/wp-emoji-release.min.js?ver=6c384dc662603955acc21c91176981fa | US | text | 11.7 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3236 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3236 | chrome.exe | 172.217.16.174:443 | apis.google.com | Google Inc. | US | whitelisted |
3236 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3236 | chrome.exe | 172.217.16.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3236 | chrome.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3236 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3236 | chrome.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
3236 | chrome.exe | 172.217.16.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3236 | chrome.exe | 45.33.3.7:443 | clickteam.postaffiliatepro.com | Linode, LLC | US | unknown |
3236 | chrome.exe | 74.125.133.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.clickteam.com |
| malicious |
accounts.google.com |
| shared |
cdn.datatables.net |
| whitelisted |
apis.google.com |
| whitelisted |
code.jquery.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
s.w.org |
| whitelisted |
www.google-analytics.com |
| whitelisted |