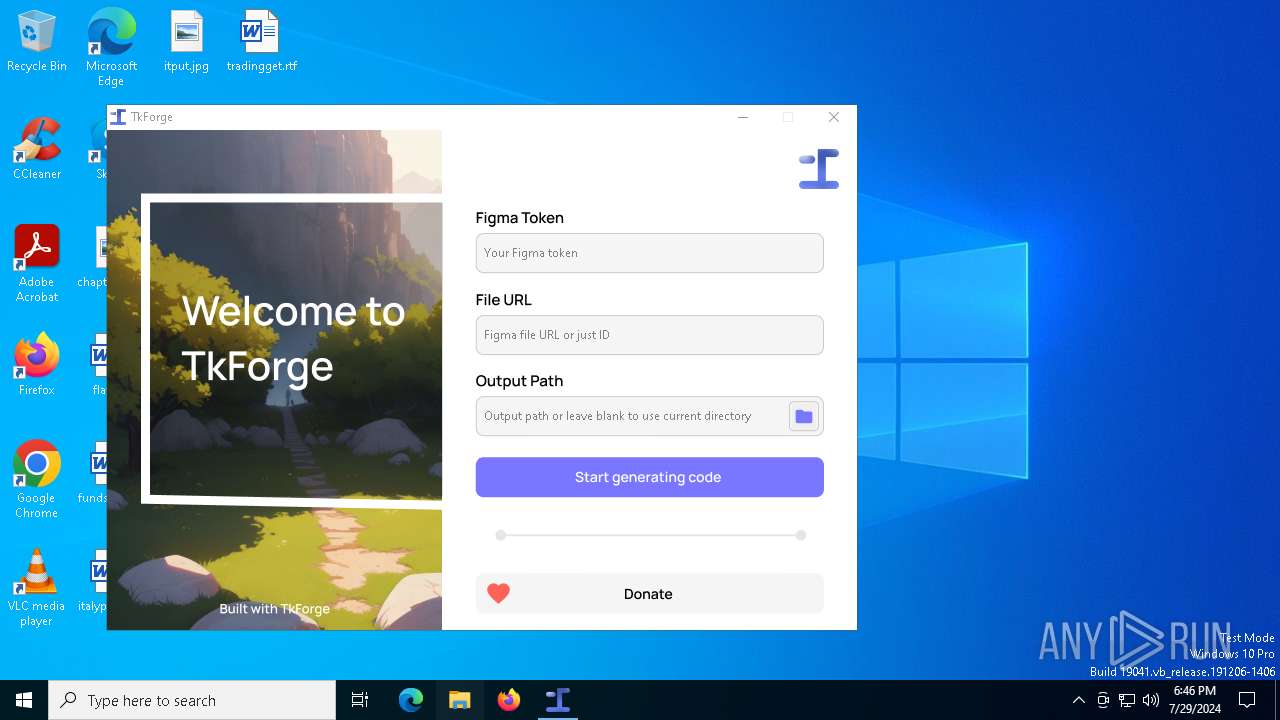
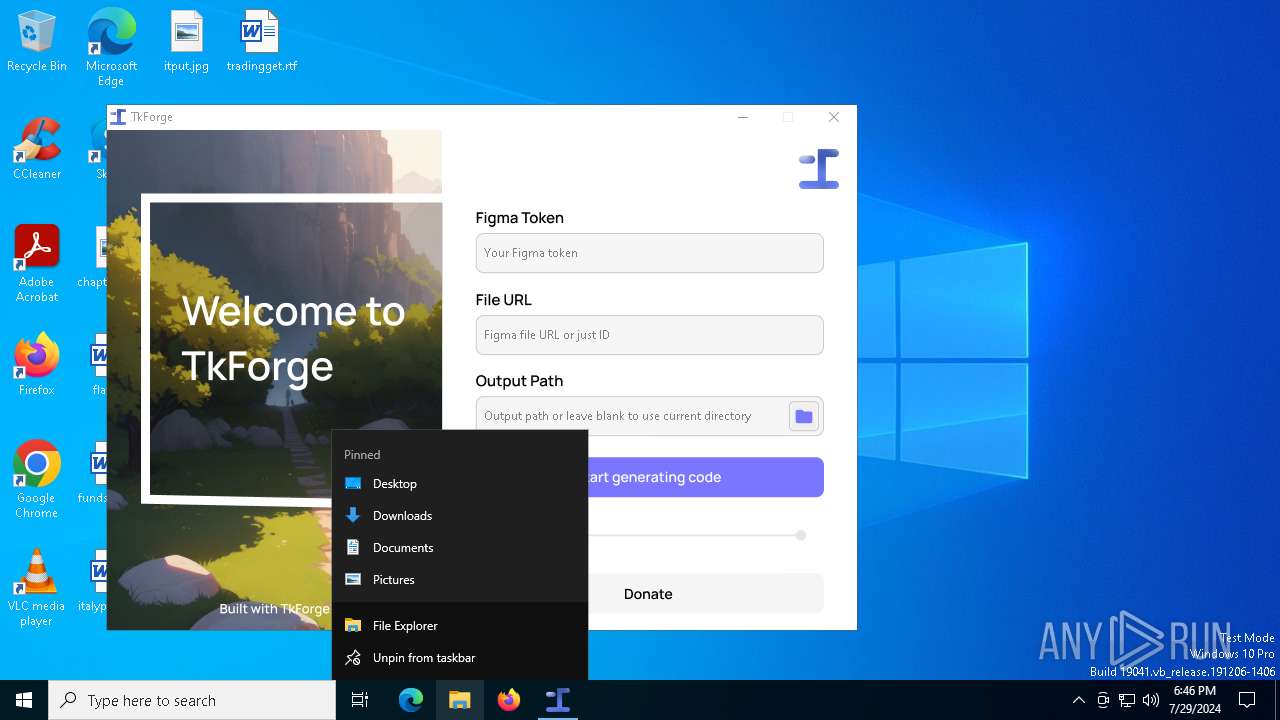
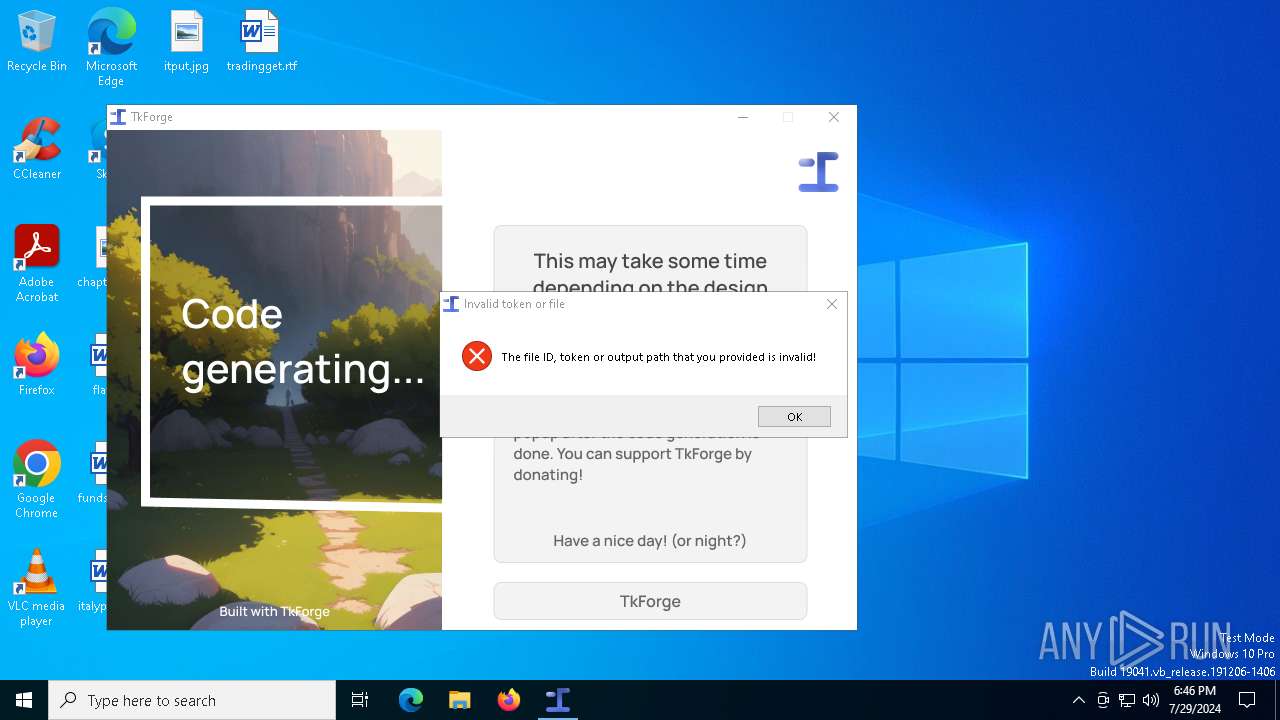
| File name: | TkForge.exe |
| Full analysis: | https://app.any.run/tasks/594ab59d-5f00-4f68-ae51-d9cd6f53e51c |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2024, 18:45:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 0BB3CFA296ECE78C0FD5EECDCB1DF2CB |
| SHA1: | 67D992FF2AF497C984DF926EA60E92FC8124154B |
| SHA256: | 0563553E8670846B2DE6FAB299C6B248C3C61F39C19A15AAC669586D2BA12EE3 |
| SSDEEP: | 98304:KrkPFDCpok2xumzy7266xKeXt5xUtQenoQHYCUcZ9wMK6Yrjcd3/dPtXJ6ylJ1j7:yNzM/rEEZIZQUICkzZ5j3 |
MALICIOUS
Drops the executable file immediately after the start
- TkForge.exe (PID: 6616)
SUSPICIOUS
Process drops legitimate windows executable
- TkForge.exe (PID: 6616)
Process drops python dynamic module
- TkForge.exe (PID: 6616)
Executable content was dropped or overwritten
- TkForge.exe (PID: 6616)
The process drops C-runtime libraries
- TkForge.exe (PID: 6616)
Application launched itself
- TkForge.exe (PID: 6616)
Loads Python modules
- TkForge.exe (PID: 6372)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 1620)
INFO
Checks supported languages
- TkForge.exe (PID: 6616)
- TkForge.exe (PID: 6372)
- ShellExperienceHost.exe (PID: 1620)
Create files in a temporary directory
- TkForge.exe (PID: 6616)
Reads the computer name
- TkForge.exe (PID: 6616)
- TkForge.exe (PID: 6372)
- ShellExperienceHost.exe (PID: 1620)
Checks proxy server information
- TkForge.exe (PID: 6372)
- slui.exe (PID: 6576)
Reads the software policy settings
- slui.exe (PID: 6576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:06:17 11:51:35+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.37 |
| CodeSize: | 171008 |
| InitializedDataSize: | 177152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc1a0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
147
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1620 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | "C:\Users\admin\AppData\Local\Temp\TkForge.exe" | C:\Users\admin\AppData\Local\Temp\TkForge.exe | TkForge.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6576 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6616 | "C:\Users\admin\AppData\Local\Temp\TkForge.exe" | C:\Users\admin\AppData\Local\Temp\TkForge.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
2 601
Read events
2 601
Write events
0
Delete events
0
Modification events
Executable files
57
Suspicious files
3
Text files
933
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-interlocked-l1-1-0.dll | executable | |
MD5:7C7B61FFA29209B13D2506418746780B | SHA256:C23FE8D5C3CA89189D11EC8DF983CC144D168CB54D9EAB5D9532767BCB2F1FA3 | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\_queue.pyd | executable | |
MD5:7F52EF40B083F34FD5E723E97B13382F | SHA256:3F8E7E6AA13B417ACC78B63434FB1144E6319A010A9FC376C54D6E69B638FE4C | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:73433EBFC9A47ED16EA544DDD308EAF8 | SHA256:C43075B1D2386A8A262DE628C93A65350E52EAE82582B27F879708364B978E29 | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-namedpipe-l1-1-0.dll | executable | |
MD5:B3F887142F40CB176B59E58458F8C46D | SHA256:8E015CDF2561450ED9A0773BE1159463163C19EAB2B6976155117D16C36519DA | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:0F7D418C05128246AFA335A1FB400CB9 | SHA256:5C9BC70586AD538B0DF1FCF5D6F1F3527450AE16935AA34BD7EB494B4F1B2DB9 | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:2DB5666D3600A4ABCE86BE0099C6B881 | SHA256:46079C0A1B660FC187AAFD760707F369D0B60D424D878C57685545A3FCE95819 | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:D1DF480505F2D23C0B5C53DF2E0E2A1A | SHA256:0B3DFB8554EAD94D5DA7859A12DB353942406F9D1DFE3FAC3D48663C233EA99D | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:07EBE4D5CEF3301CCF07430F4C3E32D8 | SHA256:8F8B79150E850ACC92FD6AAB614F6E3759BEA875134A62087D5DD65581E3001F | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-processenvironment-l1-1-0.dll | executable | |
MD5:89F35CB1212A1FD8FBE960795C92D6E8 | SHA256:058EB7CE88C22D2FF7D3E61E6593CA4E3D6DF449F984BF251D9432665E1517D1 | |||
| 6616 | TkForge.exe | C:\Users\admin\AppData\Local\Temp\_MEI66162\api-ms-win-core-profile-l1-1-0.dll | executable | |
MD5:8D12FFD920314B71F2C32614CC124FEC | SHA256:E63550608DD58040304EA85367E9E0722038BA8E7DC7BF9D91C4D84F0EC65887 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
48
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
968 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6572 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 95.100.146.19:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
4028 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1560 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6564 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |