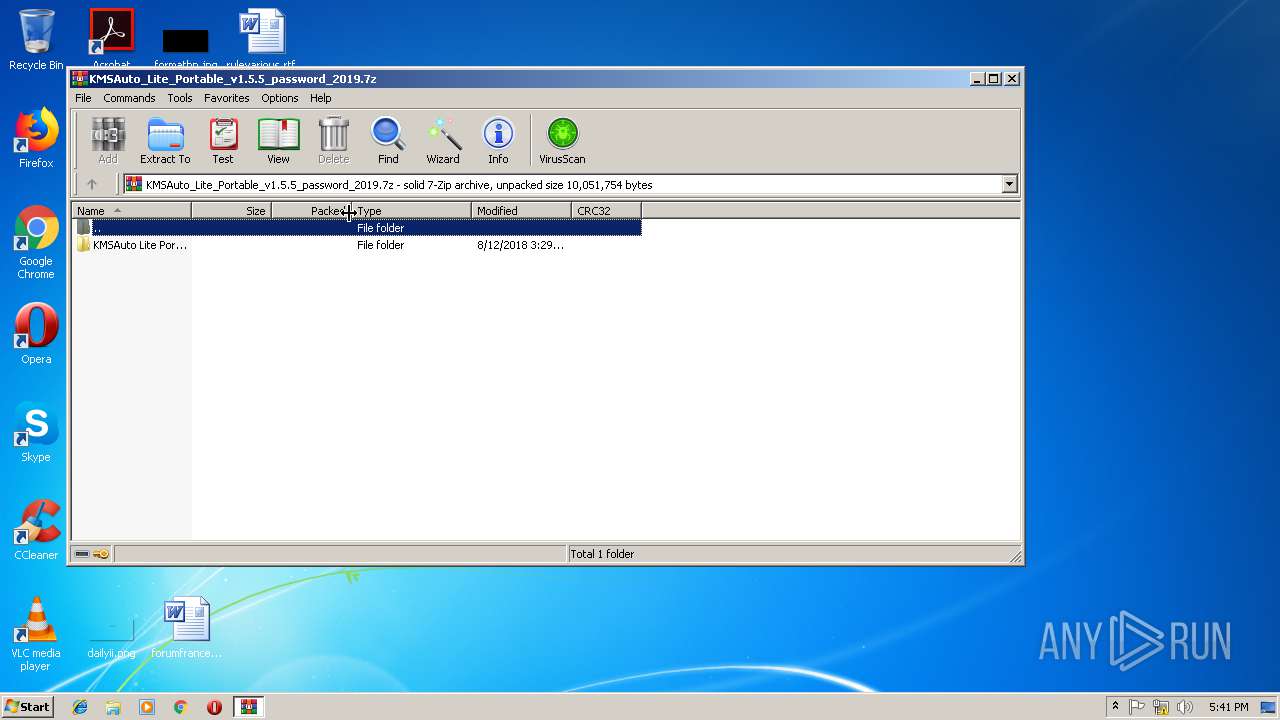
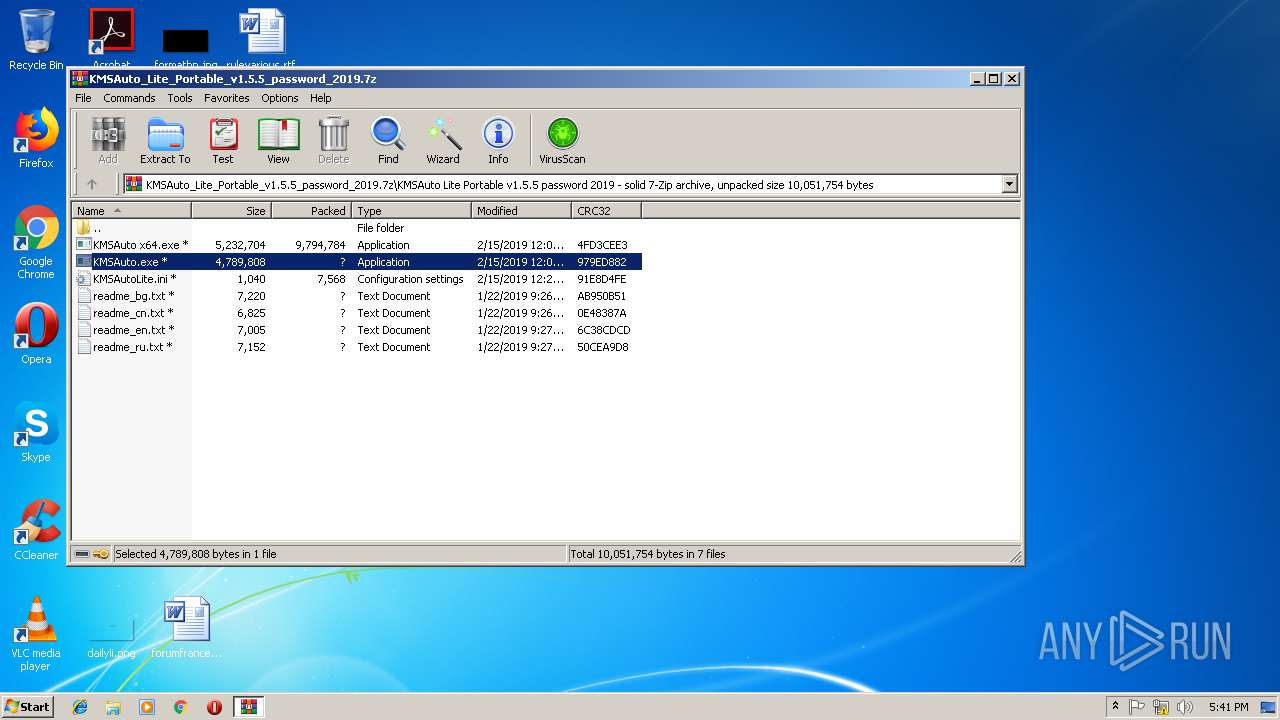
| File name: | KMSAuto_Lite_Portable_v1.5.5_password_2019.7z |
| Full analysis: | https://app.any.run/tasks/37da6013-bd66-4132-bb0f-dba35f64903c |
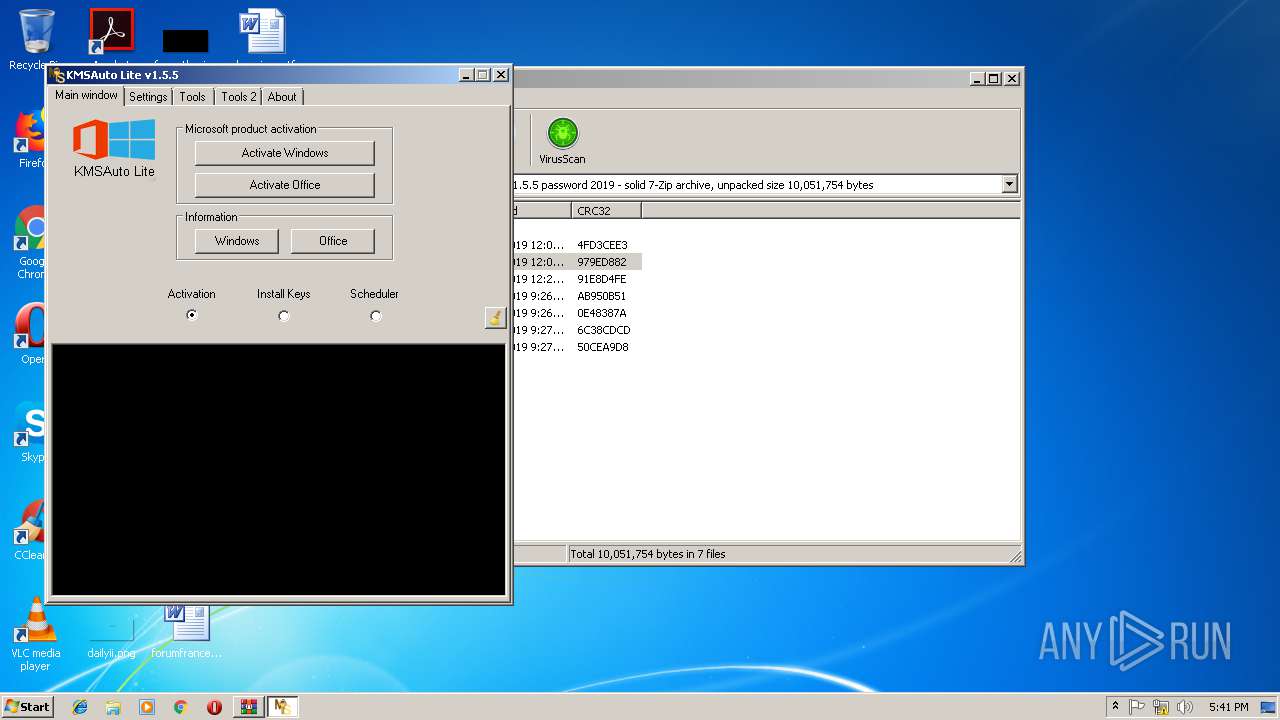
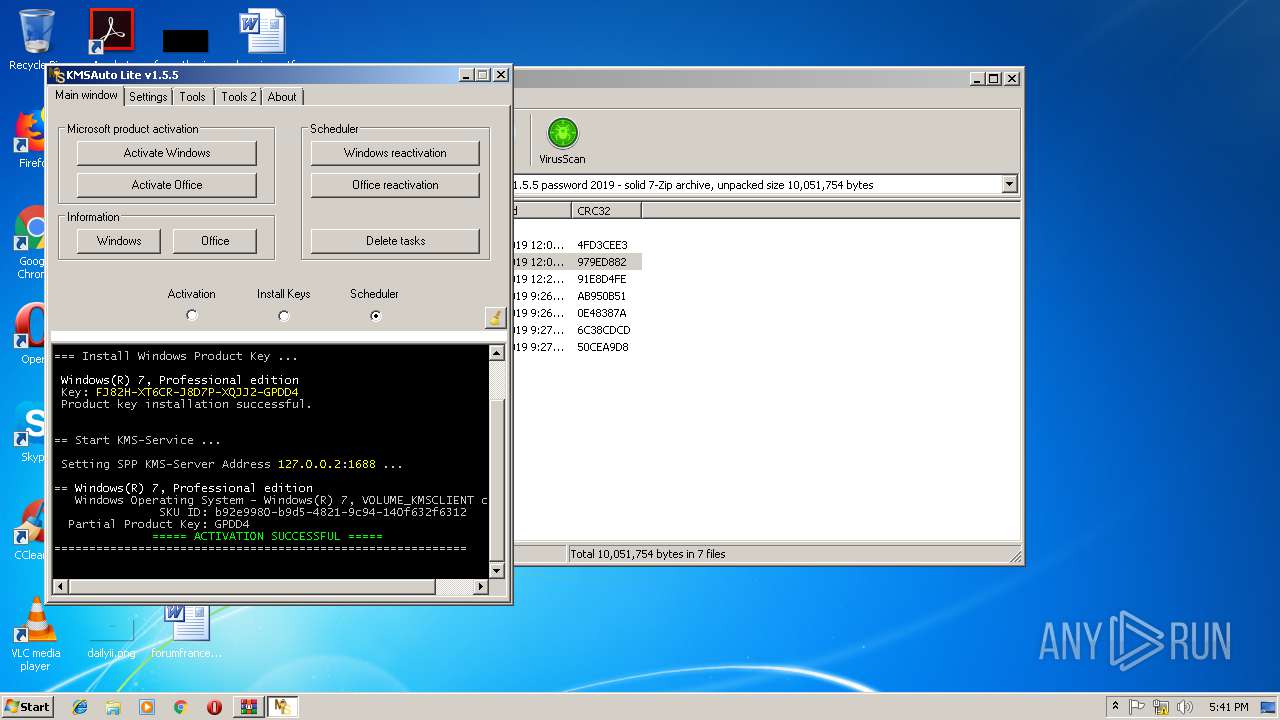
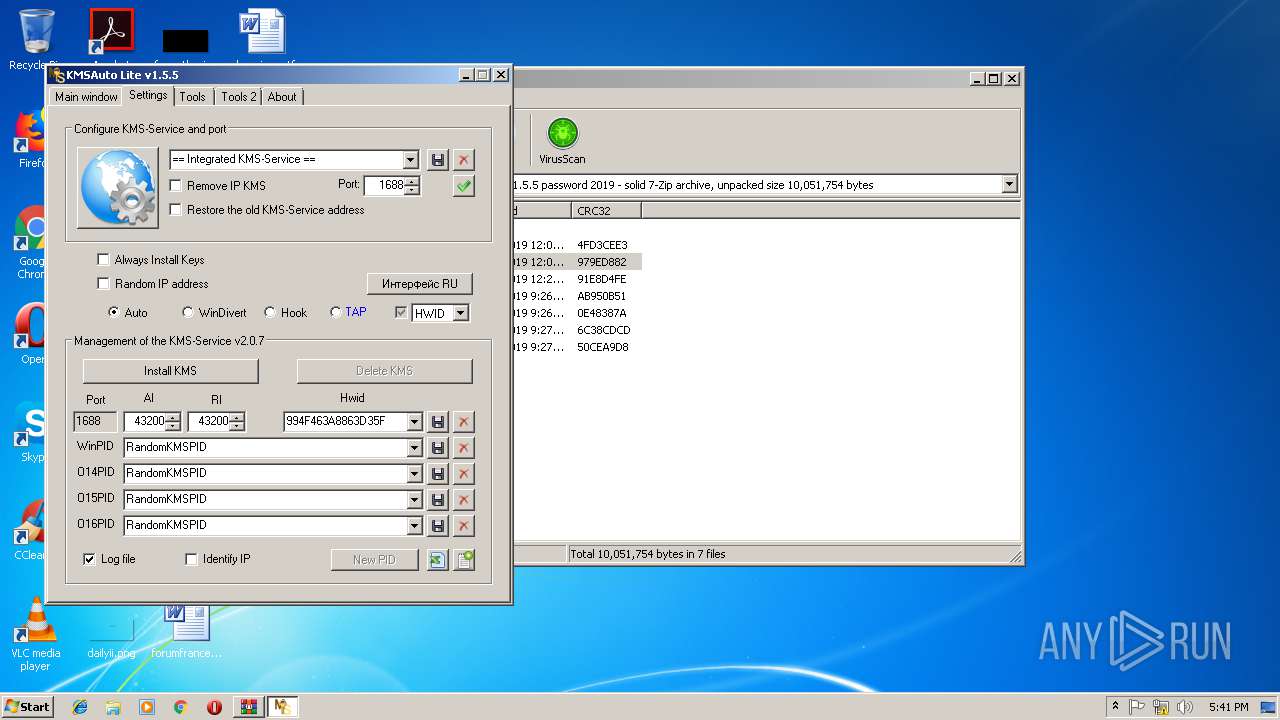
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2019, 17:40:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 5432104AF433387A9445501286454C2E |
| SHA1: | 9E4680B272A8F9984A090250DA9EB515E1DD739D |
| SHA256: | 0553CED31C385D8DBC36CD2FFA7C8D660A69853C3FB769A5E3C62F24F16C3DD7 |
| SSDEEP: | 196608:8a+ha7bcBJY+S2caHZ2Y8Z3lSja0427wnJUrhY/ag9ldDdYKTGsFKwVbtEfo7Fo:p+I74BJYs7HZ2ZZ3Y+2MJUre/xDN6s5k |
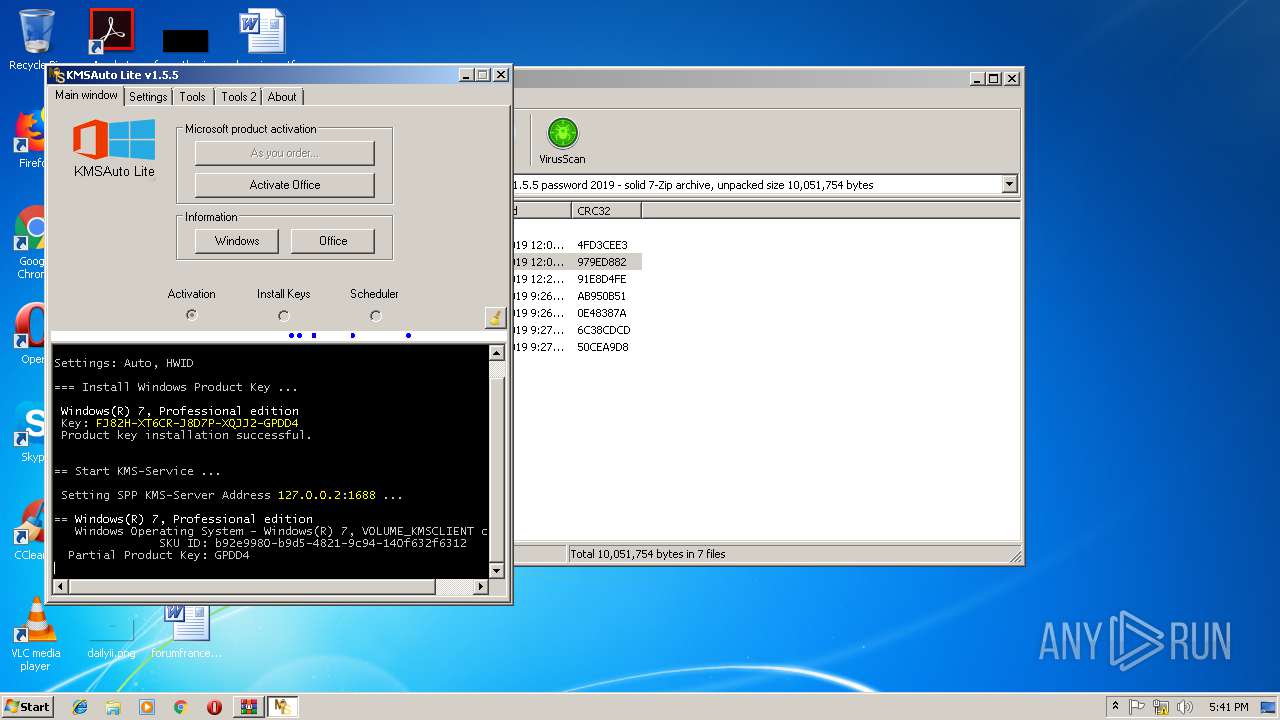
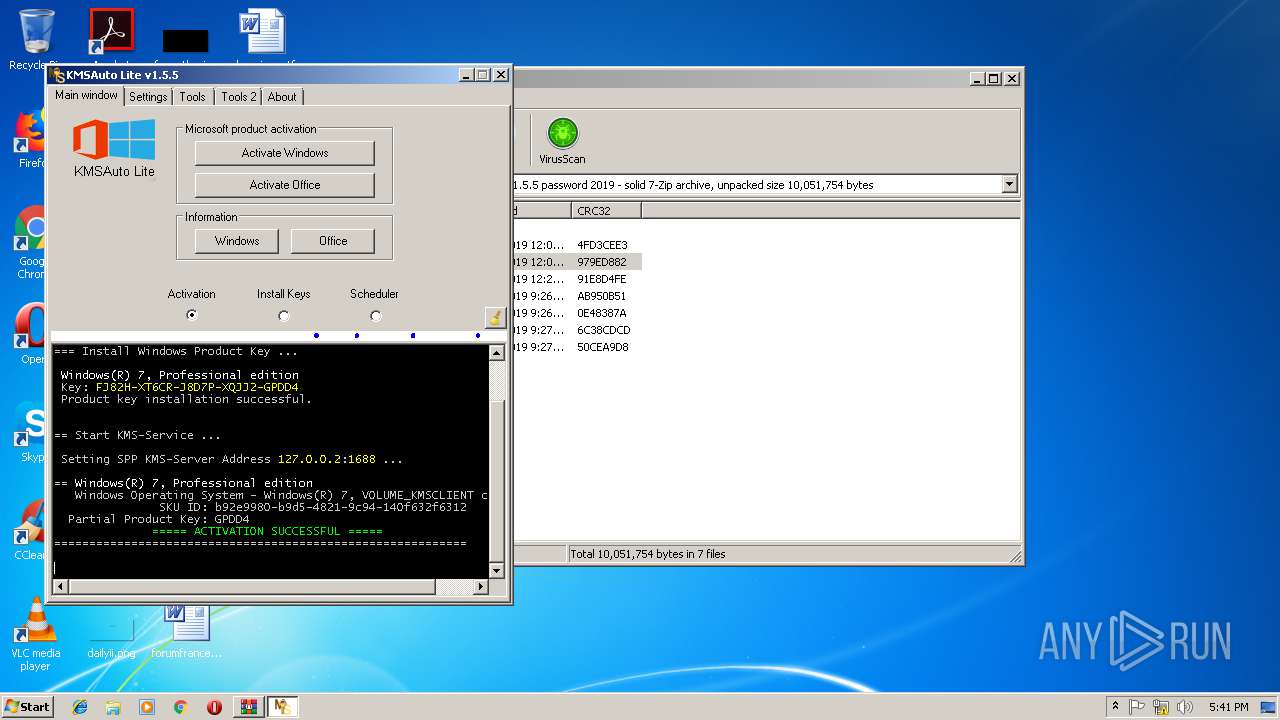
MALICIOUS
Application was dropped or rewritten from another process
- KMSAuto.exe (PID: 3932)
- KMSSS.exe (PID: 3836)
- KMSAuto.exe (PID: 3084)
- signtool.exe (PID: 2664)
Changes settings of System certificates
- signtool.exe (PID: 2664)
SUSPICIOUS
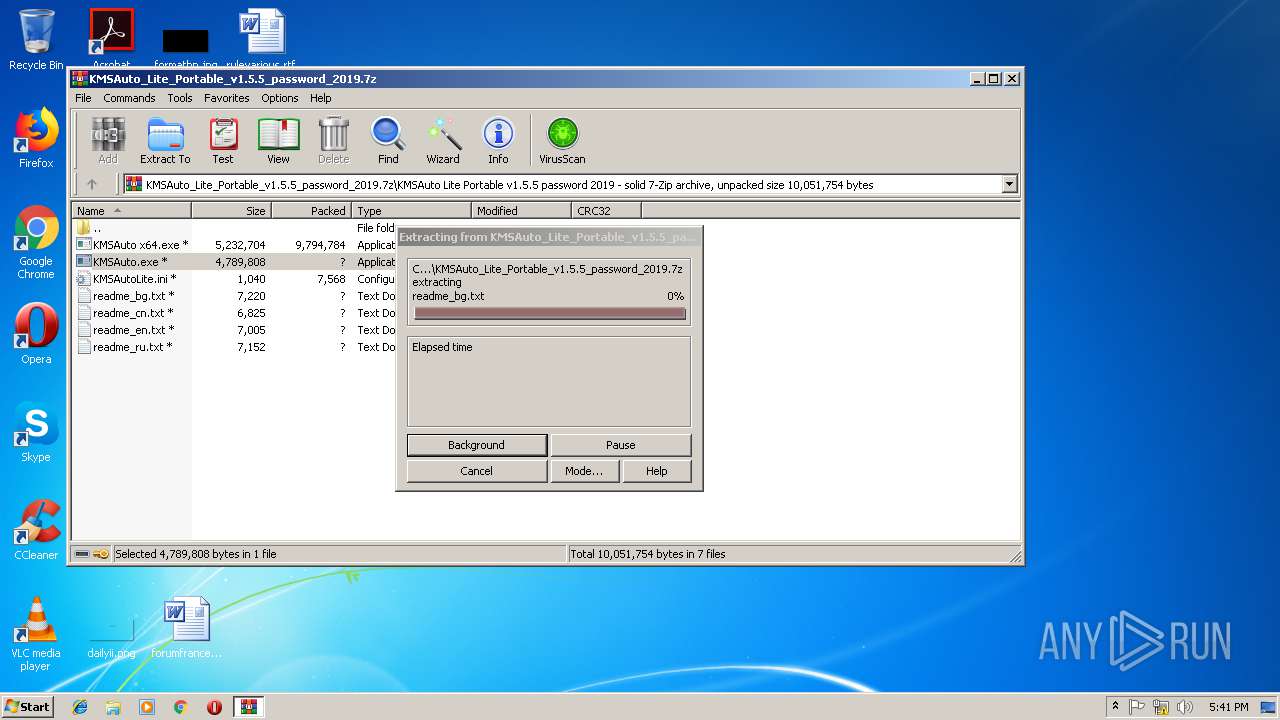
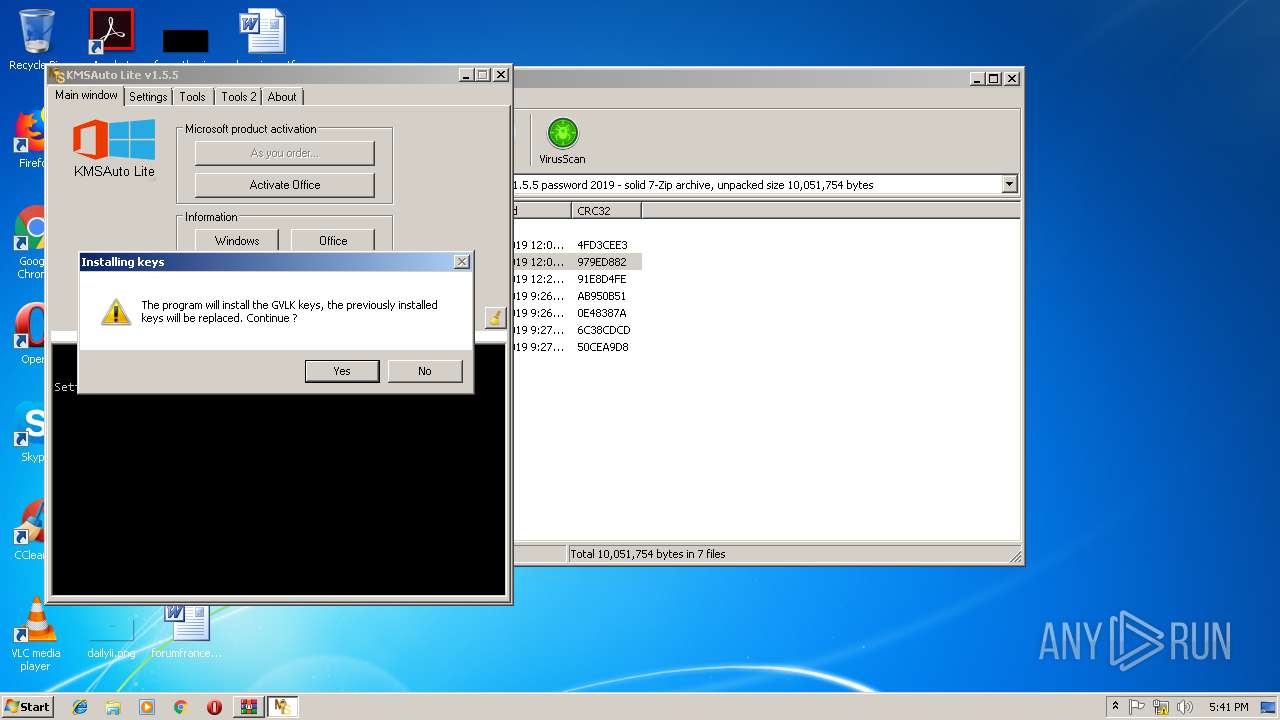
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3232)
- KMSAuto.exe (PID: 3084)
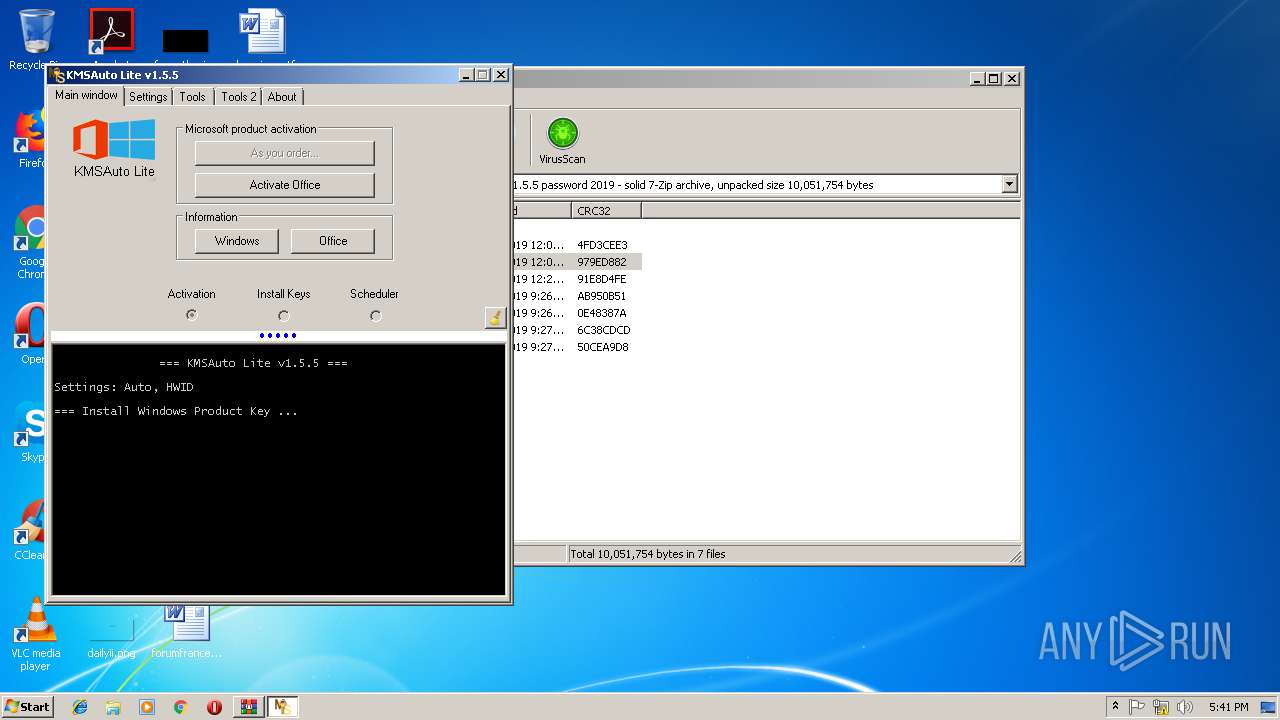
Starts CMD.EXE for commands execution
- KMSAuto.exe (PID: 3084)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2684)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 2248)
- cmd.exe (PID: 3728)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 2288)
Starts SC.EXE for service management
- cmd.exe (PID: 4092)
- cmd.exe (PID: 3200)
- cmd.exe (PID: 3932)
- cmd.exe (PID: 3168)
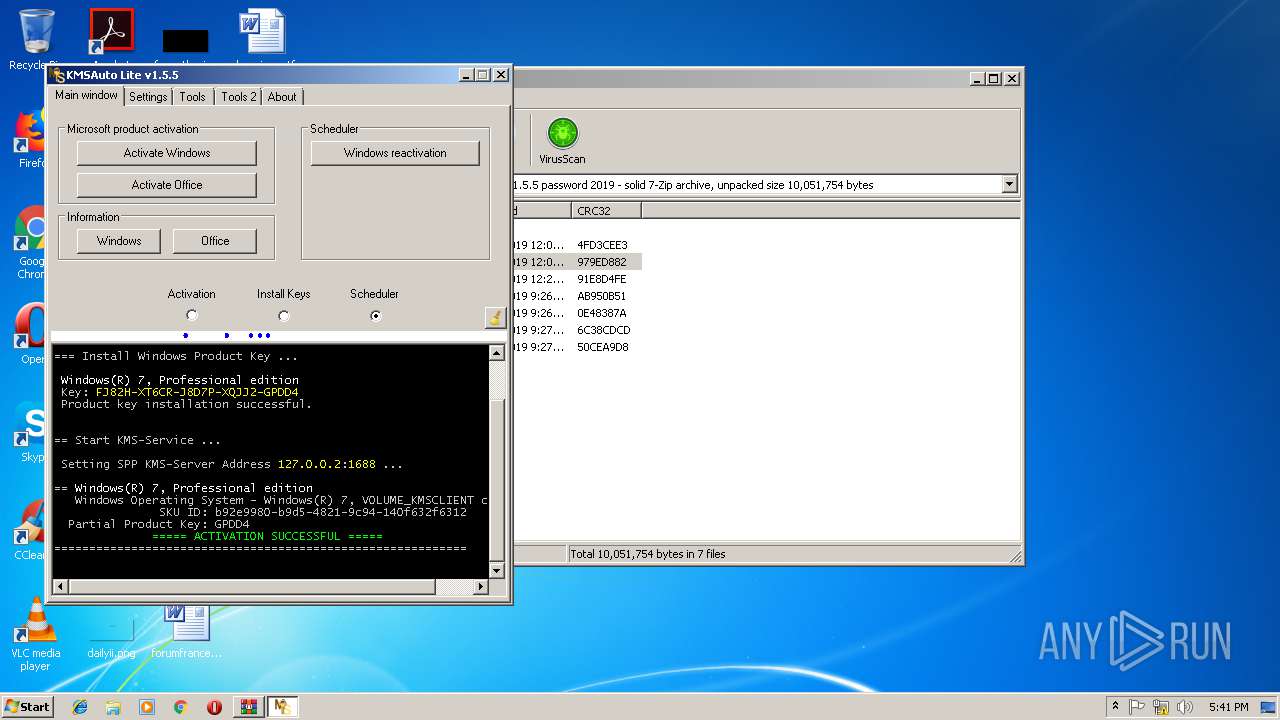
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2828)
- cmd.exe (PID: 2396)
- cmd.exe (PID: 2736)
- cmd.exe (PID: 3032)
Adds / modifies Windows certificates
- signtool.exe (PID: 2664)
Creates or modifies windows services
- KMSAuto.exe (PID: 3084)
Executes scripts
- cmd.exe (PID: 2924)
- cmd.exe (PID: 3400)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
101
Monitored processes
43
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "wmic.exe" path SoftwareLicensingService get Version /value /FORMAT:List | C:\Windows\System32\Wbem\wmic.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1632 | Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS2 protocol=TCP | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
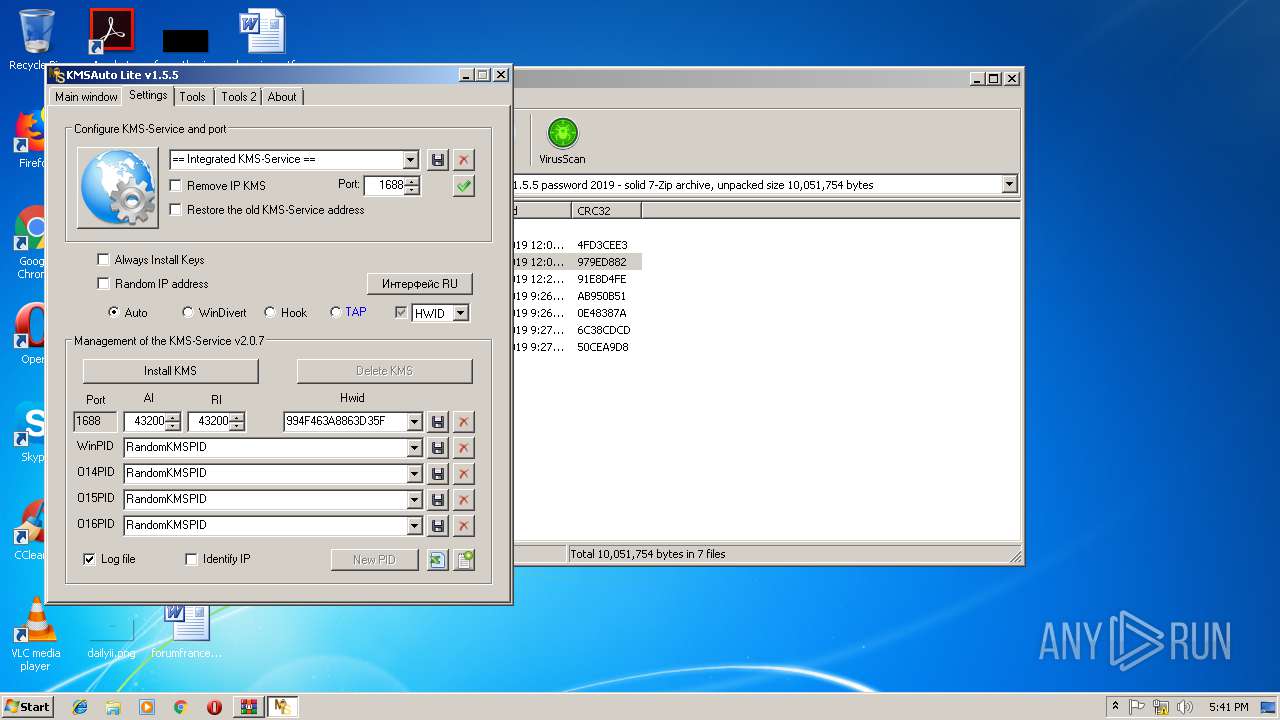
| 2168 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServicePort /d 1688 /t REG_SZ /reg:32 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS dir=in action=allow protocol=TCP localport=1688 | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2288 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS2 protocol=TCP | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2372 | sc.exe delete KMSEmulator | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServicePort /d 1688 /t REG_SZ /reg:64 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Windows\System32\cmd.exe" /c reg.exe add "HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v KeyManagementServicePort /d 1688 /t REG_SZ /reg:32 | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2544 | sc.exe stop KMSEmulator | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2560 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 040
Read events
736
Write events
304
Delete events
0
Modification events
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMSAuto_Lite_Portable_v1.5.5_password_2019.7z | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3232) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
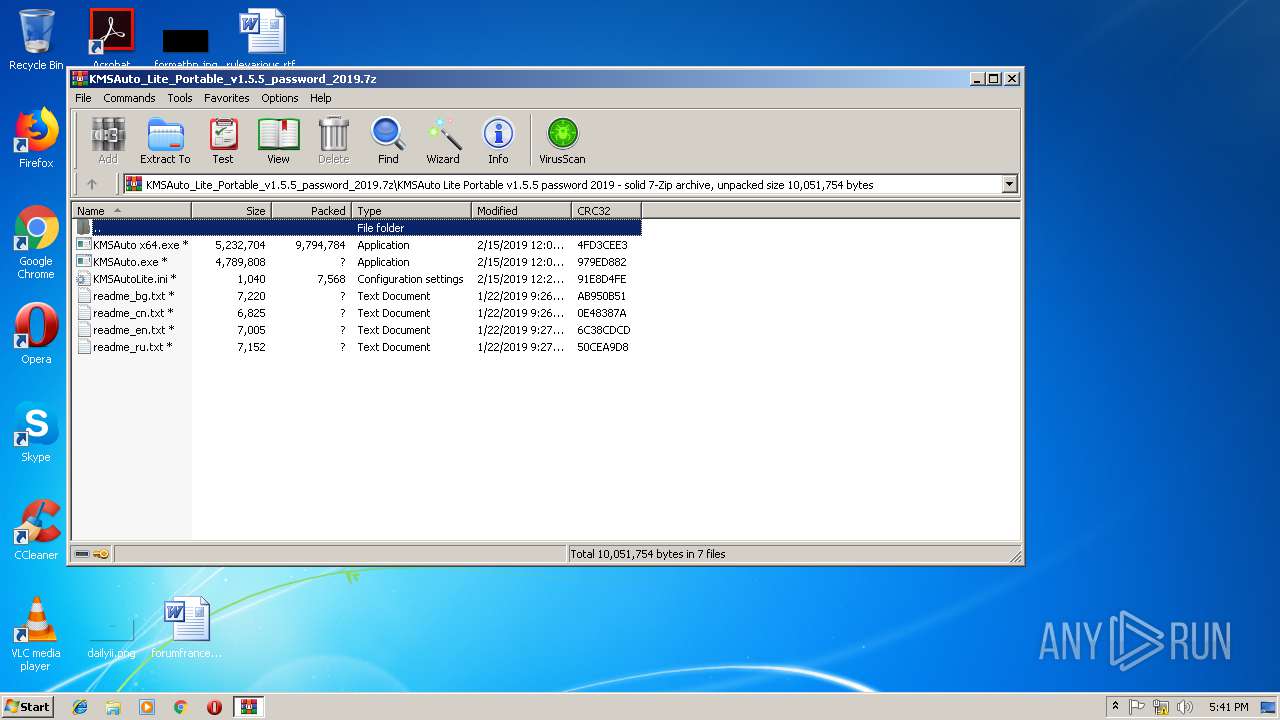
Executable files
4
Suspicious files
5
Text files
83
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | signtool.exe | C:\Users\admin\AppData\Local\Temp\Cab3893.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | signtool.exe | C:\Users\admin\AppData\Local\Temp\Tar3894.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | signtool.exe | C:\Users\admin\AppData\Local\Temp\Cab38C4.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | signtool.exe | C:\Users\admin\AppData\Local\Temp\Tar38C5.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | signtool.exe | C:\Users\admin\AppData\Local\Temp\Cab38D6.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | signtool.exe | C:\Users\admin\AppData\Local\Temp\Tar38D7.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | signtool.exe | C:\Users\admin\AppData\Local\Temp\Tar3A11.tmp | — | |
MD5:— | SHA256:— | |||
| 3232 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3232.47355\KMSAuto Lite Portable v1.5.5 password 2019\KMSAutoLite.ini | text | |
MD5:872BC16CDCC95B7F15FBFF3D41418039 | SHA256:A65C3E25C68469310E156A721697DC7BB9869738011AE882878992361C0B279E | |||
| 3232 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3232.47355\KMSAuto Lite Portable v1.5.5 password 2019\KMSAuto.exe | executable | |
MD5:92F16F34CABD29B2C587DD3A06E35AFB | SHA256:FE9E92957E22F009FD22FBA305CAA0172D5DCDD11010B848DC75913E640473CA | |||
| 3232 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb3232.47355\KMSAuto Lite Portable v1.5.5 password 2019\KMSAuto x64.exe | executable | |
MD5:5BF1DBAF1DB9D91200A27FC2670EC0C0 | SHA256:D00977521DBA67111876729E4B8ED09455B85C653BEF2FD0C23E9E8A09F0A9B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2664 | signtool.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2664 | signtool.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |