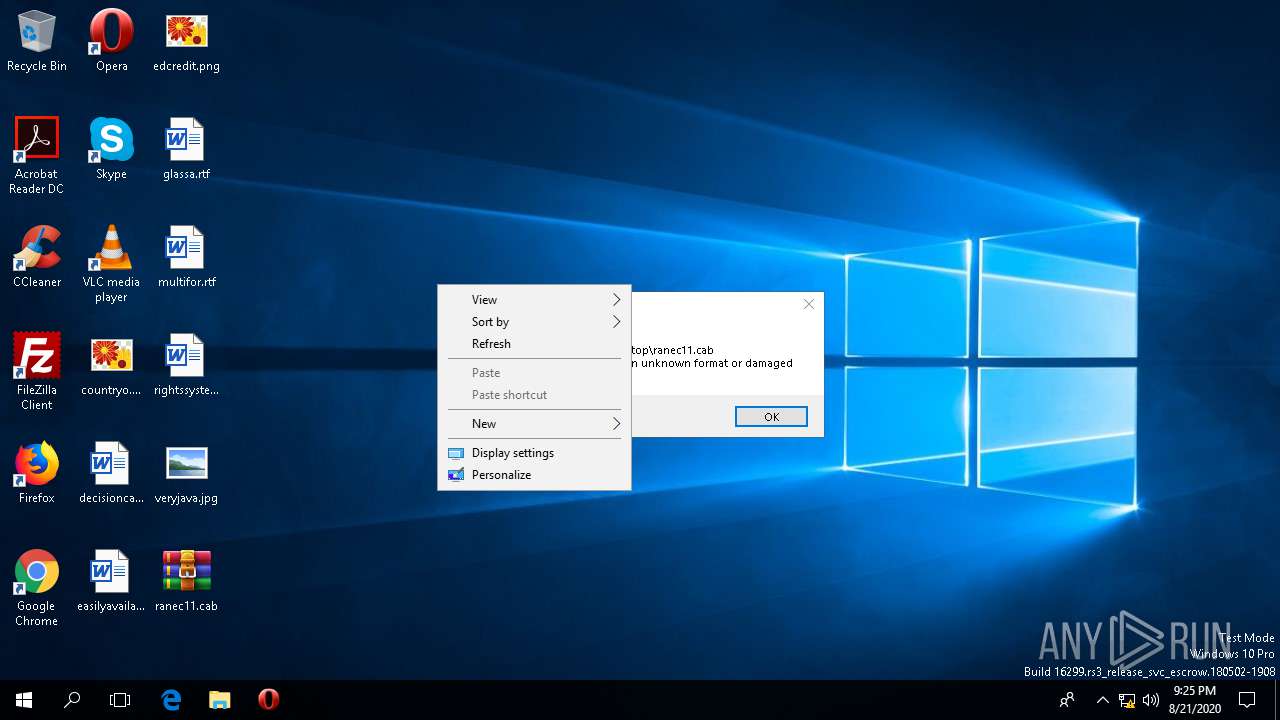
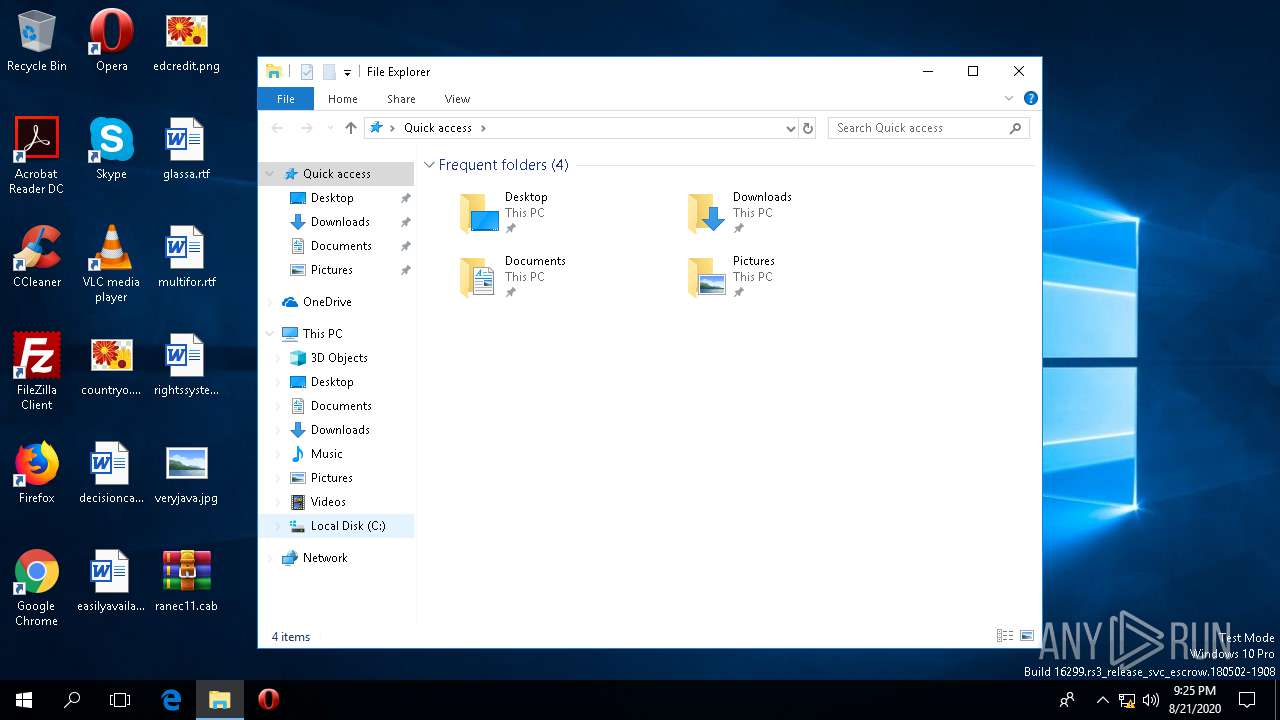
| File name: | ranec11.cab |
| Full analysis: | https://app.any.run/tasks/3c4a9f63-7c35-496a-a14c-5704fd9cda88 |
| Verdict: | Suspicious activity |
| Threats: | IcedID is a banking trojan-type malware which allows attackers to utilize it to steal banking credentials of the victims. IcedID aka BokBot mainly targets businesses and steals payment information, it also acts as a loader and can deliver another viruses or download additional modules. |
| Analysis date: | August 21, 2020, 21:25:16 |
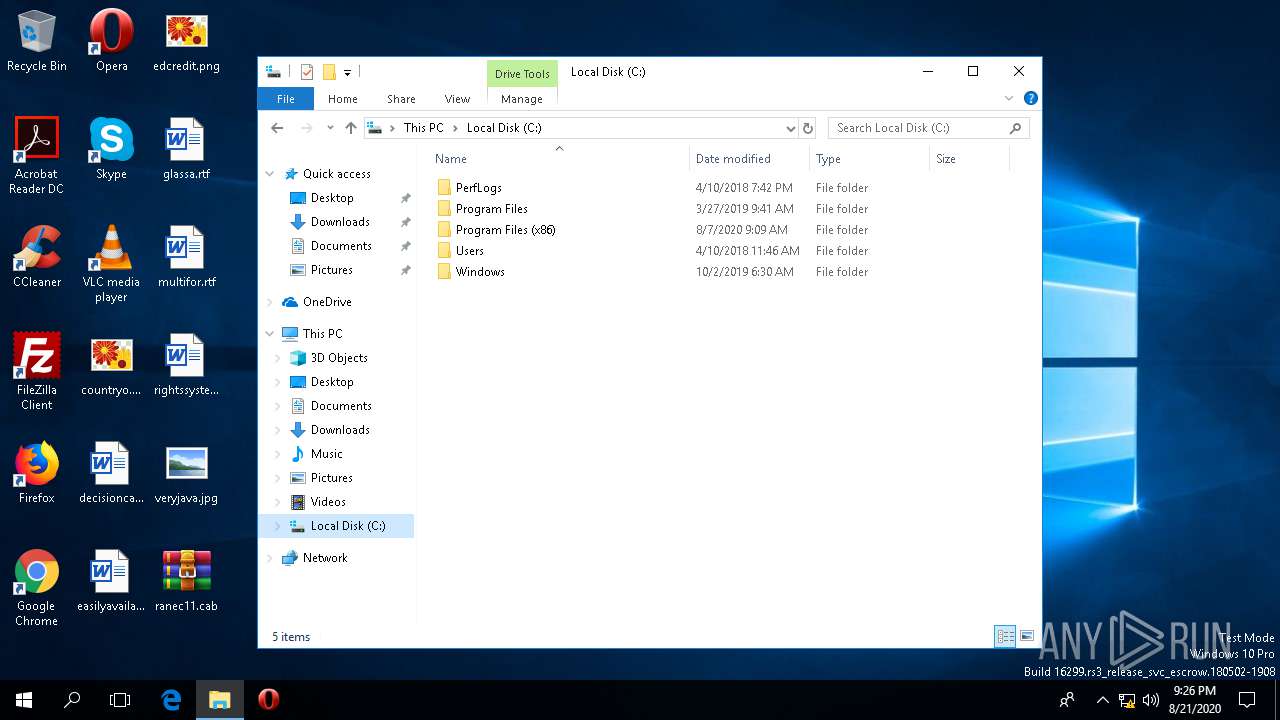
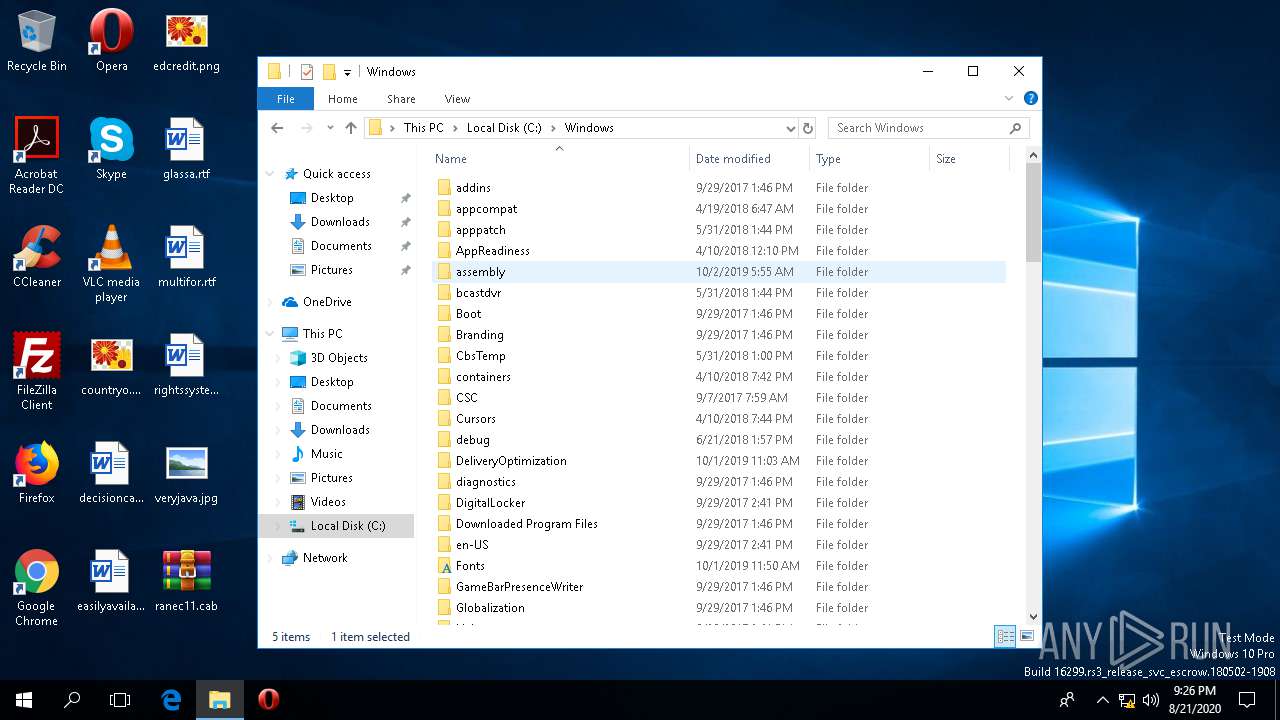
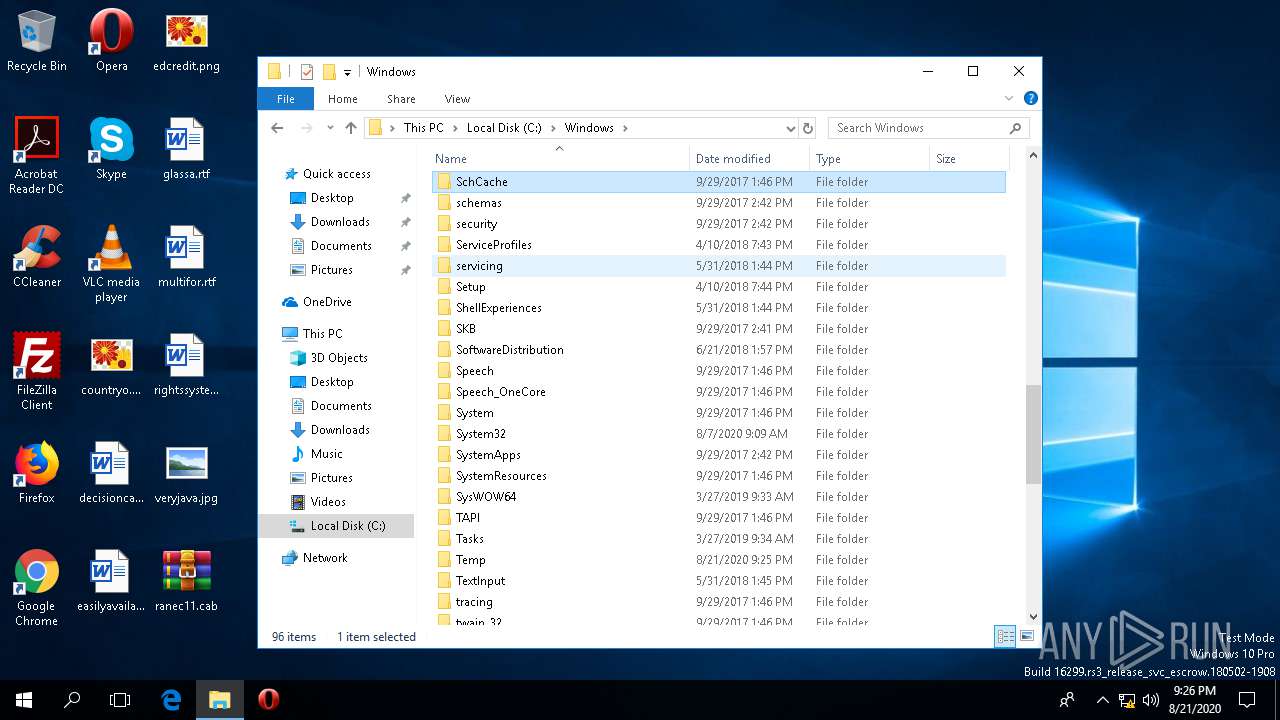
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | A52A1E151BF4B993EFCFF87B3780D731 |
| SHA1: | F0ACF0B669505BED5BD7FCB7F32C88C08E7DE76B |
| SHA256: | 054FF4620AAA40928CA67A2C364BEDF71D79672874D75BA50FF8231069AD74D9 |
| SSDEEP: | 6144:ULdSq++cF0NsjJ8AbcHf97Qv680yDI6S6zIu+vGAOv9IjF:Ux+qNs1dbctQveyDou+vGxAF |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 5004)
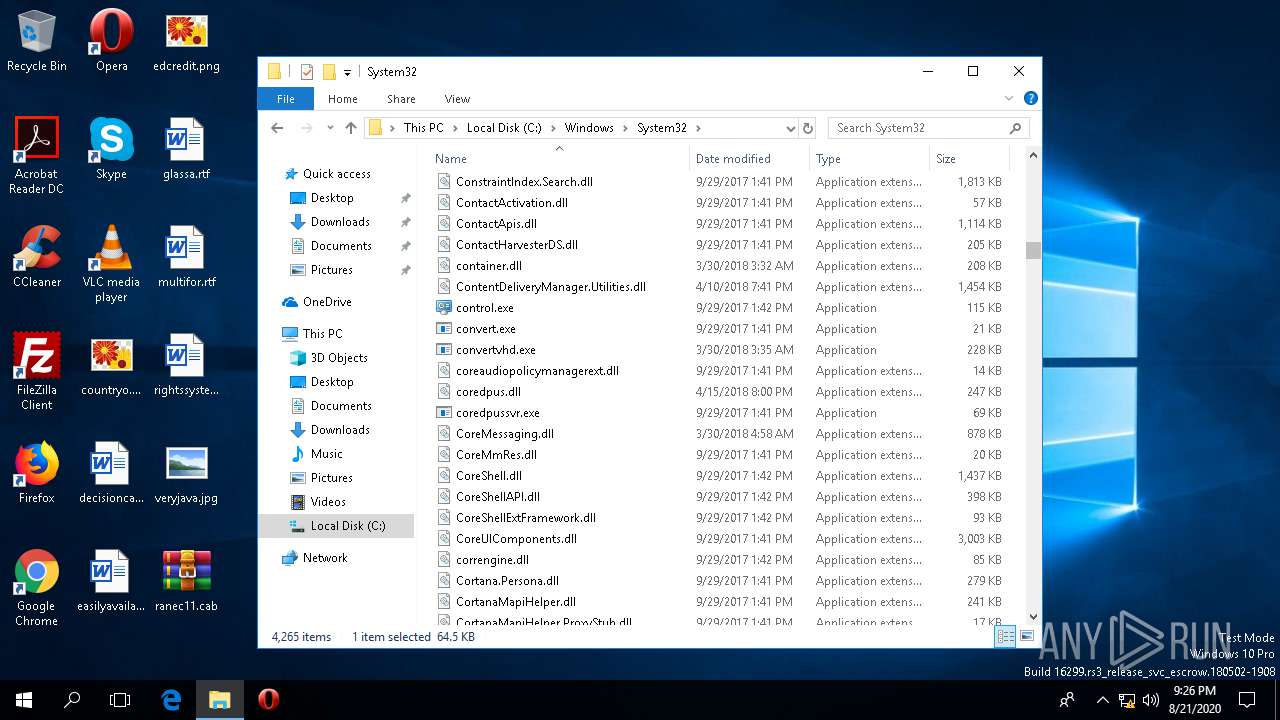
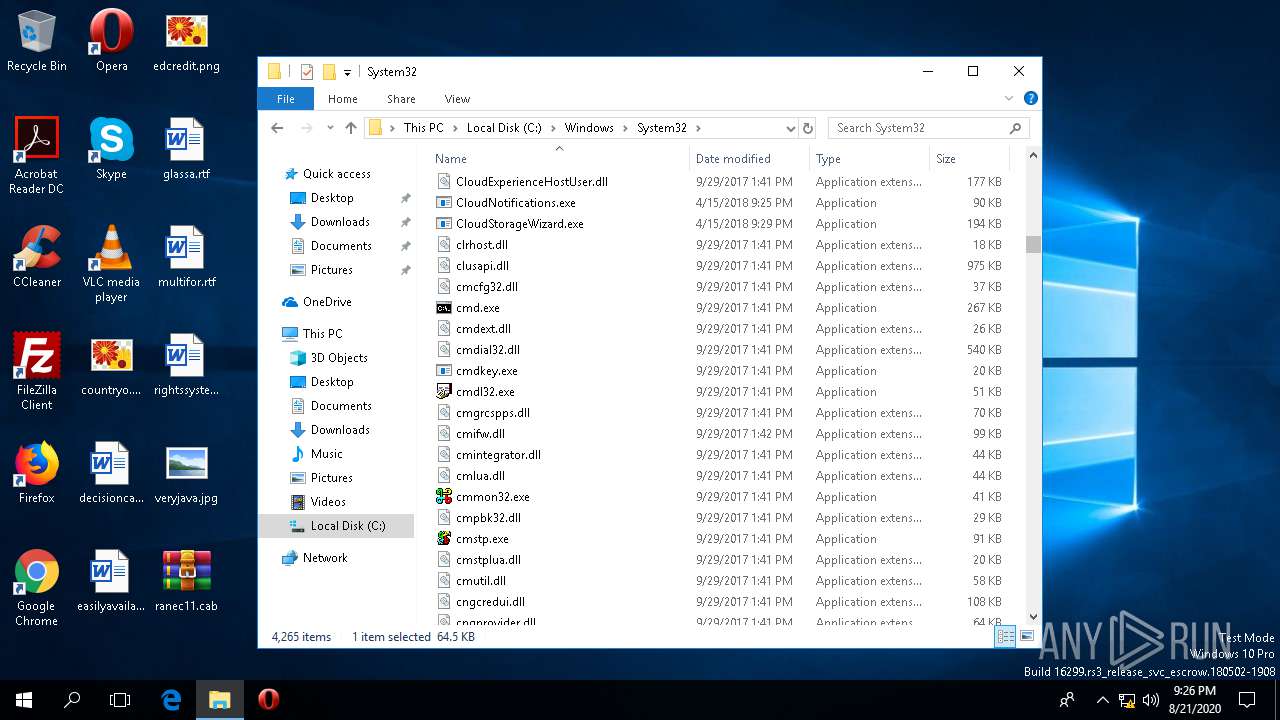
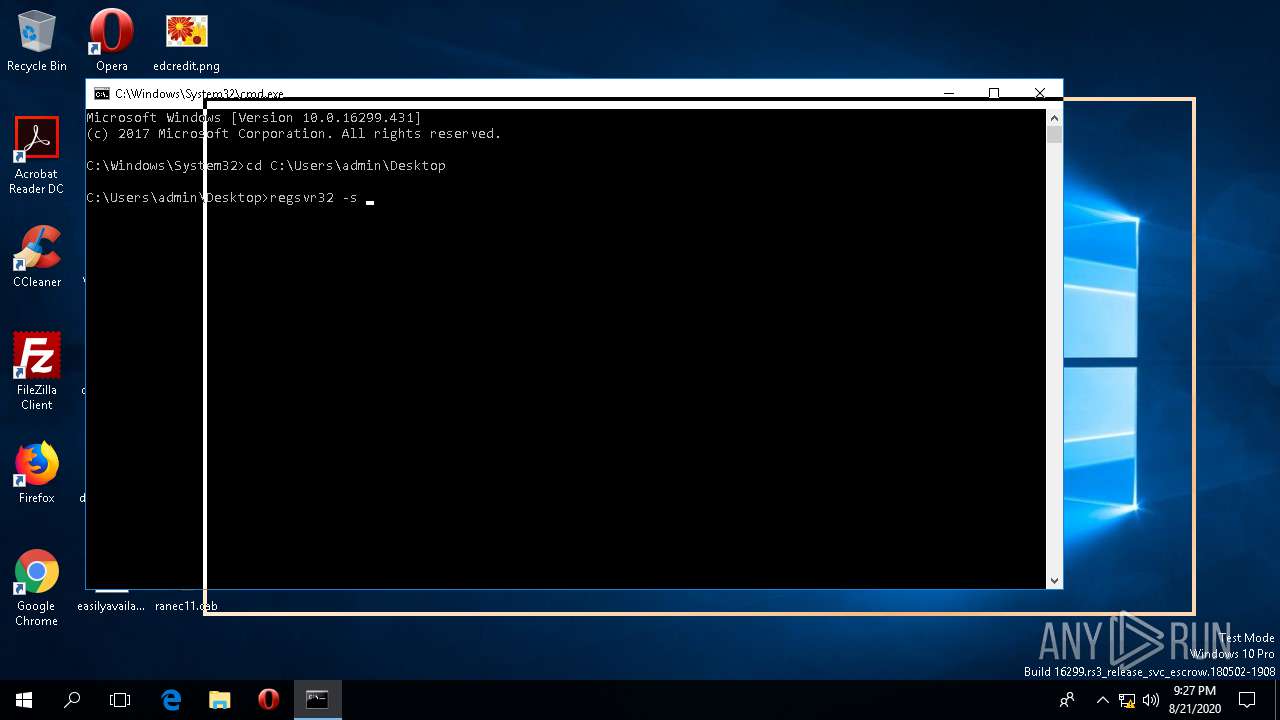
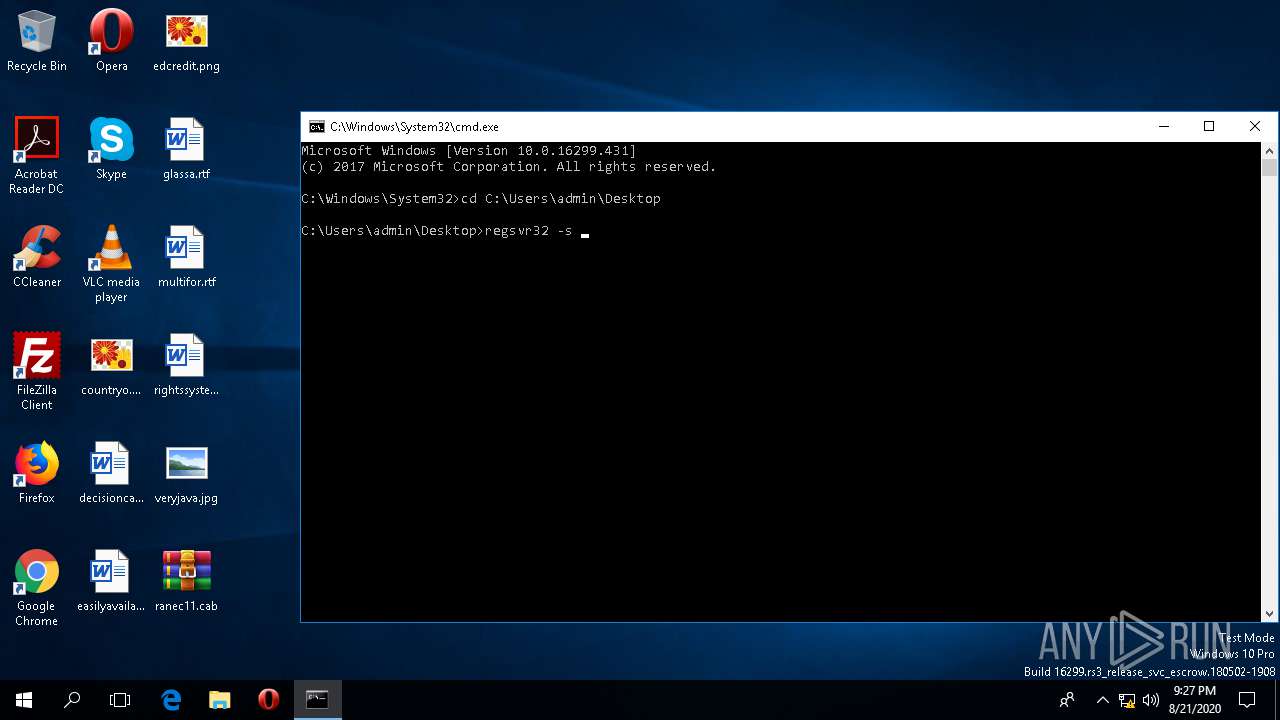
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 468)
SUSPICIOUS
Executed via COM
- rundll32.exe (PID: 4572)
Reads the machine GUID from the registry
- WinRAR.exe (PID: 1748)
- regsvr32.exe (PID: 5004)
INFO
Reads settings of System Certificates
- regsvr32.exe (PID: 5004)
Reads the software policy settings
- regsvr32.exe (PID: 5004)
Manual execution by user
- cmd.exe (PID: 468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:15 18:36:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.26 |
| CodeSize: | 206336 |
| InitializedDataSize: | 97280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10687 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.8.4.924 |
| ProductVersionNumber: | 8.8.4.924 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Bought Pointfig |
| ProductName: | Whileagain |
| FileDescription: | Whileagain |
| ProductVersion: | 8.8.4.924 |
| LegalCopyright: | Copyright © Bought Pointfig 1998-2012 |
| OriginalFileName: | note.dll |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Aug-2020 16:36:54 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Bought Pointfig |
| ProductName: | Whileagain |
| FileDescription: | Whileagain |
| ProductVersion: | 8.8.4.924 |
| LegalCopyright: | Copyright © Bought Pointfig 1998-2012 |
| OriginalFilename: | note.dll |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Aug-2020 16:36:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00032573 | 0x00032600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.78617 |
.rdata | 0x00034000 | 0x00013102 | 0x00013200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.47415 |
.data | 0x00048000 | 0x00009F88 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.40997 |
.rsrc | 0x00052000 | 0x00000474 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63231 |
.reloc | 0x00053000 | 0x00002BDC | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6226 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.43292 | 632 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
KERNEL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
DllRegisterServer | 1 | 0x0000856A |
Total processes
94
Monitored processes
6
Malicious processes
0
Suspicious processes
0
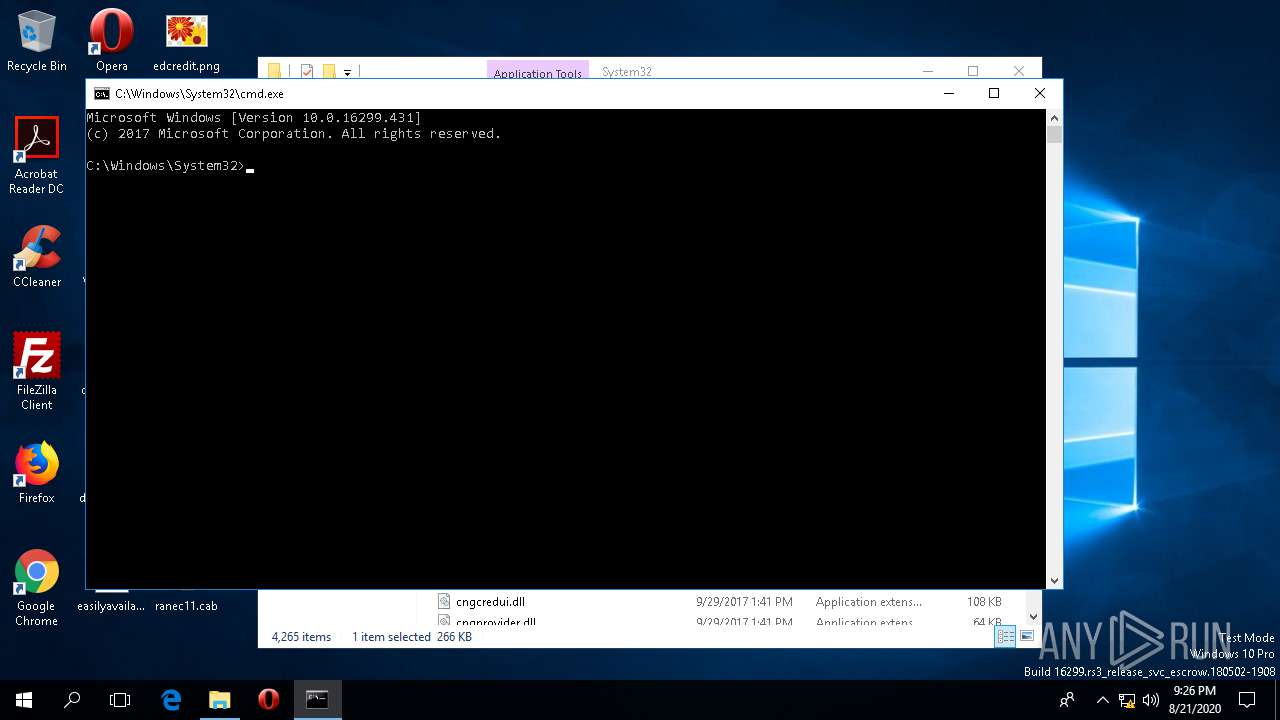
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ranec11.cab" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.60.0 Modules
| |||||||||||||||
| 4496 | regsvr32 -s ranec11.cab | C:\WINDOWS\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4572 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\WINDOWS\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5004 | -s ranec11.cab | C:\WINDOWS\SysWOW64\regsvr32.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
734
Read events
712
Write events
22
Delete events
0
Modification events
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\19a\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\19a\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\system32\windows.storage.dll,-9216 |
Value: This PC | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\19a\52C64B7E |
| Operation: | write | Name: | @windows.storage.dll,-21825 |
Value: 3D Objects | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\19a\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\system32\windows.storage.dll,-50691 |
Value: Libraries | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\19a\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5004 | regsvr32.exe | GET | 302 | 23.8.7.184:443 | https://support.oracle.com/ | NL | — | — | whitelisted |
5004 | regsvr32.exe | GET | 302 | 23.8.7.184:443 | https://support.oracle.com/portal | NL | html | 265 b | whitelisted |
5004 | regsvr32.exe | GET | 200 | 23.8.7.184:443 | https://support.oracle.com/portal/ | NL | html | 15.9 Kb | whitelisted |
5004 | regsvr32.exe | GET | 503 | 23.8.11.23:443 | https://www.oracle.com/splash/support/generic/error-page1-416750.html | NL | html | 11.1 Kb | whitelisted |
5004 | regsvr32.exe | GET | 200 | 104.111.214.198:443 | https://support.microsoft.com/ | NL | html | 103 Kb | malicious |
5004 | regsvr32.exe | GET | 200 | 104.111.214.198:443 | https://support.microsoft.com/socbundles/jsll | NL | text | 53.7 Kb | malicious |
5004 | regsvr32.exe | GET | 200 | 104.244.42.3:443 | https://help.twitter.com/en | US | html | 95.8 Kb | whitelisted |
5004 | regsvr32.exe | GET | 200 | 104.244.42.3:443 | https://help.twitter.com/etc/clientlibs/dtm/help-twitter/ac0b17d7a4556cd264c3df3fac5054e8fd5023f8/satelliteLib-60fd3ea258ba845f84504d35cda3c27b0dcdc5d3.js | US | text | 78.8 Kb | whitelisted |
5004 | regsvr32.exe | GET | 200 | 104.121.154.81:443 | https://support.apple.com/ | NL | html | 65.7 Kb | whitelisted |
5004 | regsvr32.exe | GET | 302 | 23.8.7.184:443 | https://support.oracle.com/js/universal/jQuery.js | NL | html | 280 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5004 | regsvr32.exe | 23.8.7.184:443 | support.oracle.com | Akamai International B.V. | NL | unknown |
5004 | regsvr32.exe | 23.8.11.23:443 | www.oracle.com | Akamai International B.V. | NL | whitelisted |
5004 | regsvr32.exe | 104.111.214.198:443 | support.microsoft.com | Akamai International B.V. | NL | whitelisted |
5004 | regsvr32.exe | 104.244.42.3:443 | help.twitter.com | Twitter Inc. | US | suspicious |
5004 | regsvr32.exe | 104.121.154.81:443 | support.apple.com | Akamai Technologies, Inc. | NL | unknown |
5004 | regsvr32.exe | 45.147.231.132:443 | ldrbravo.casa | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
support.oracle.com |
| whitelisted |
www.oracle.com |
| whitelisted |
support.microsoft.com |
| malicious |
help.twitter.com |
| whitelisted |
support.apple.com |
| whitelisted |
ldrbravo.casa |
| suspicious |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |