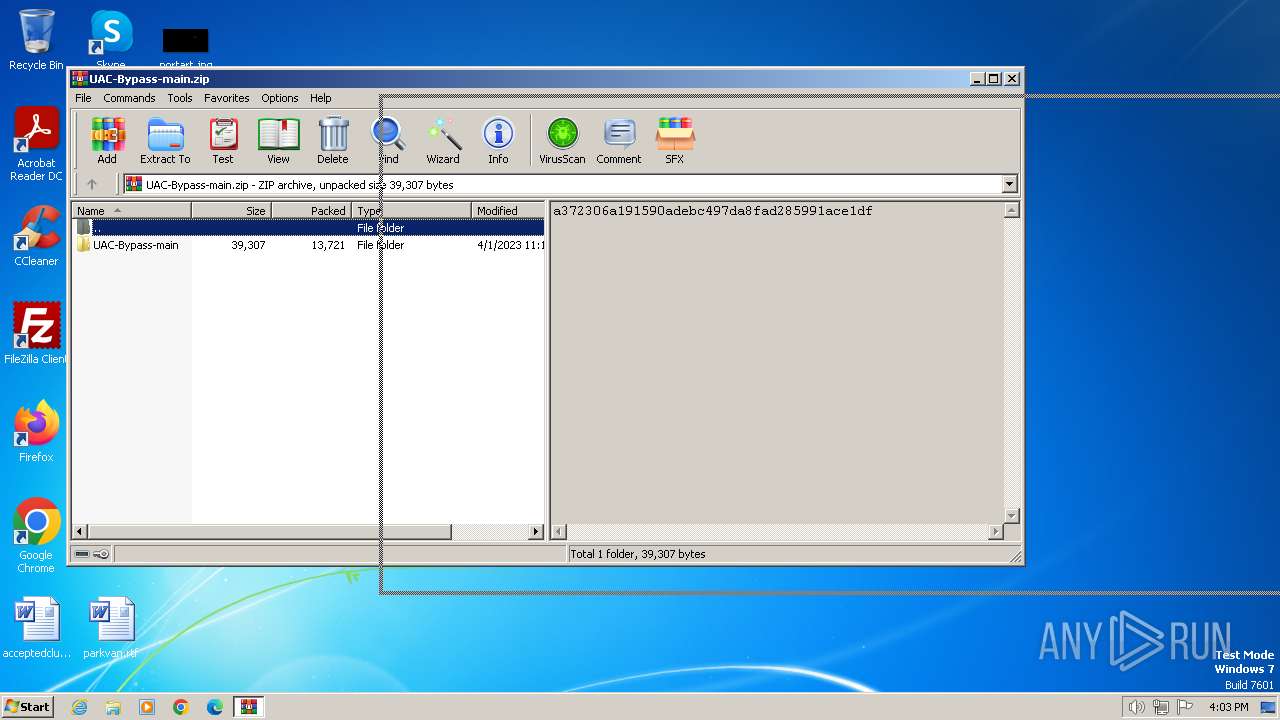
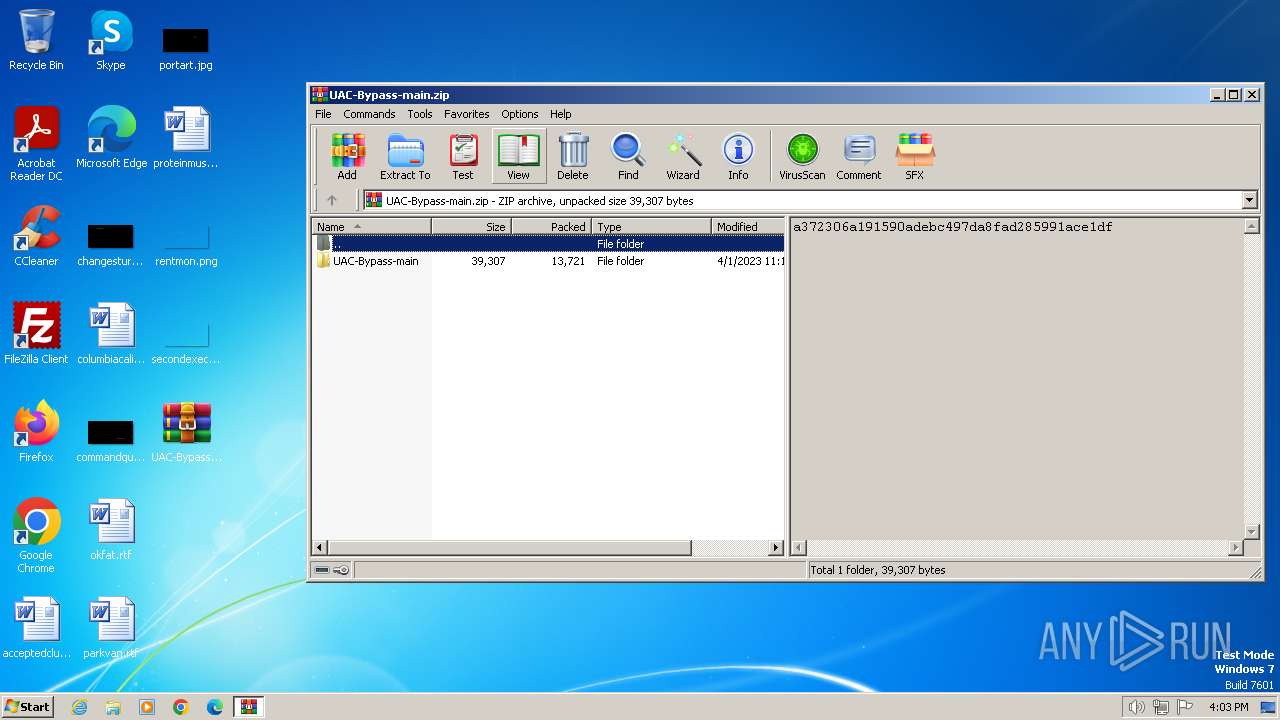
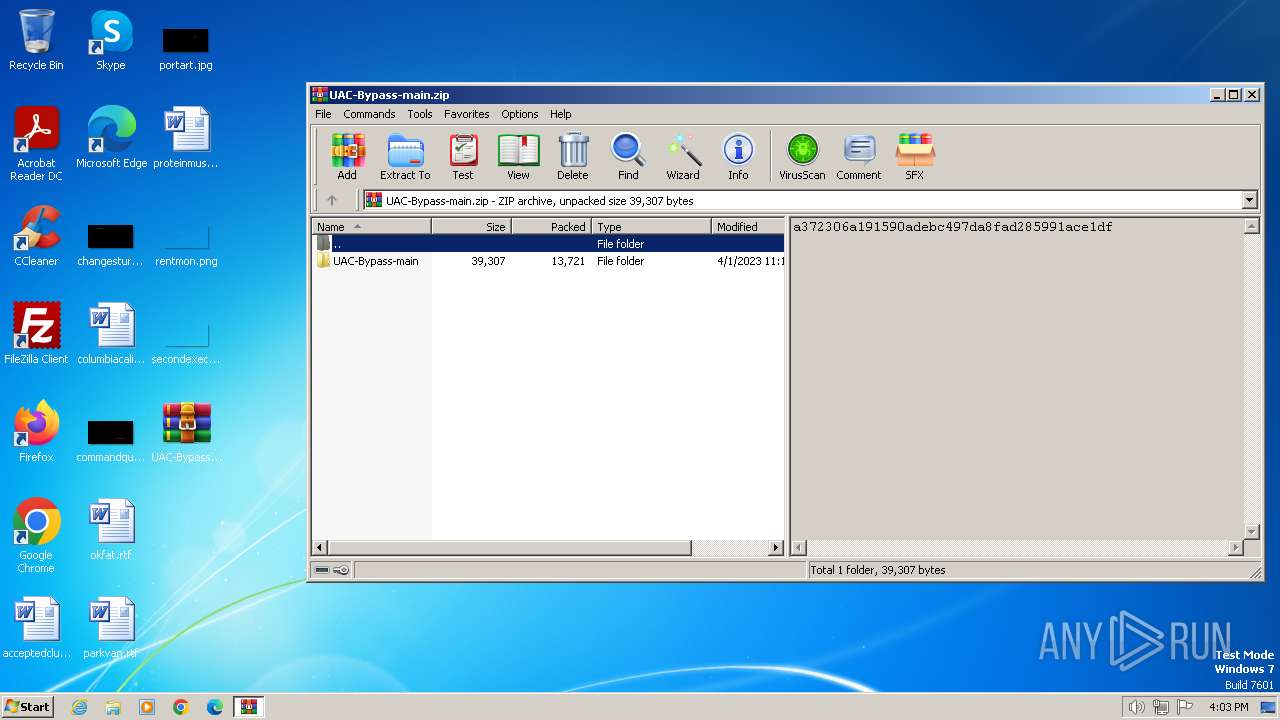
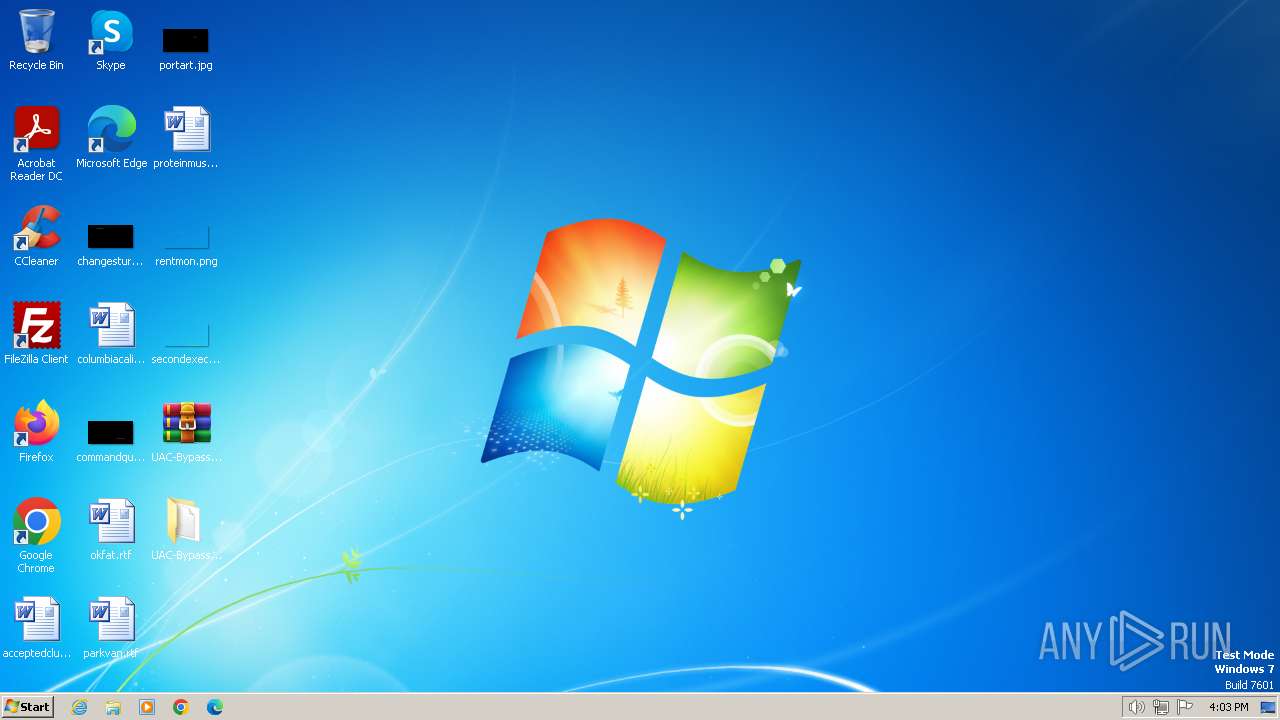
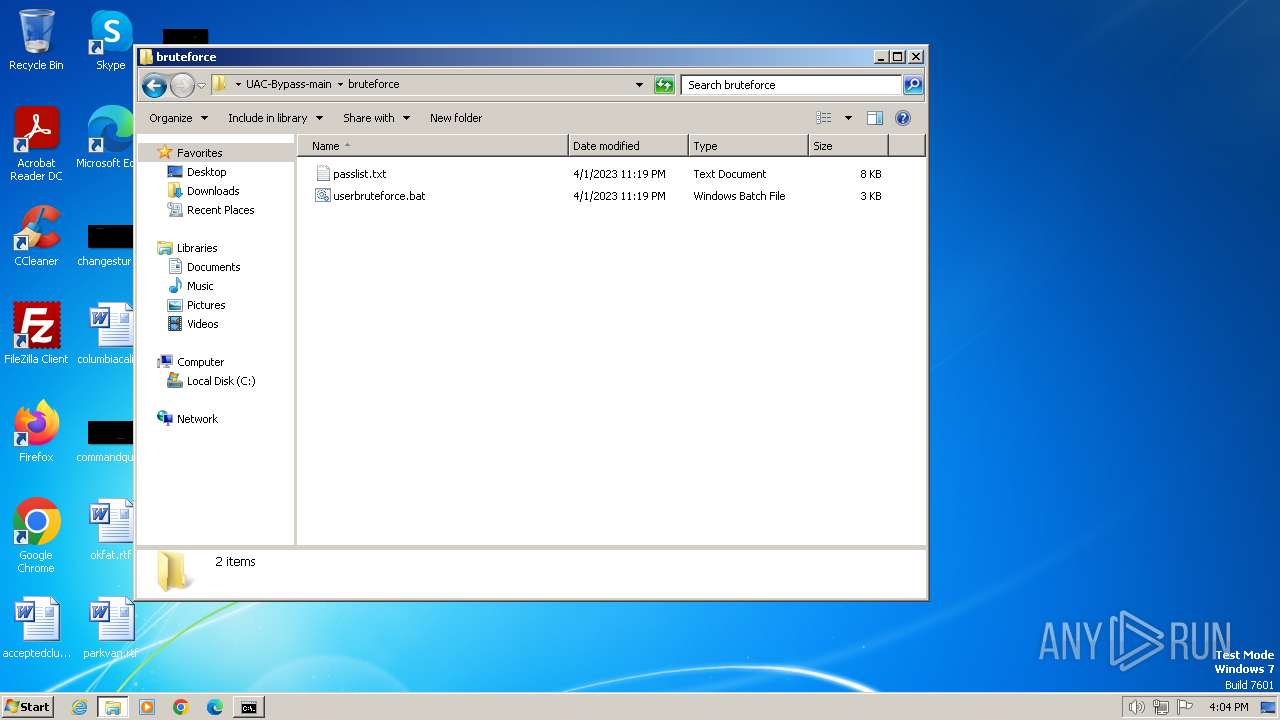
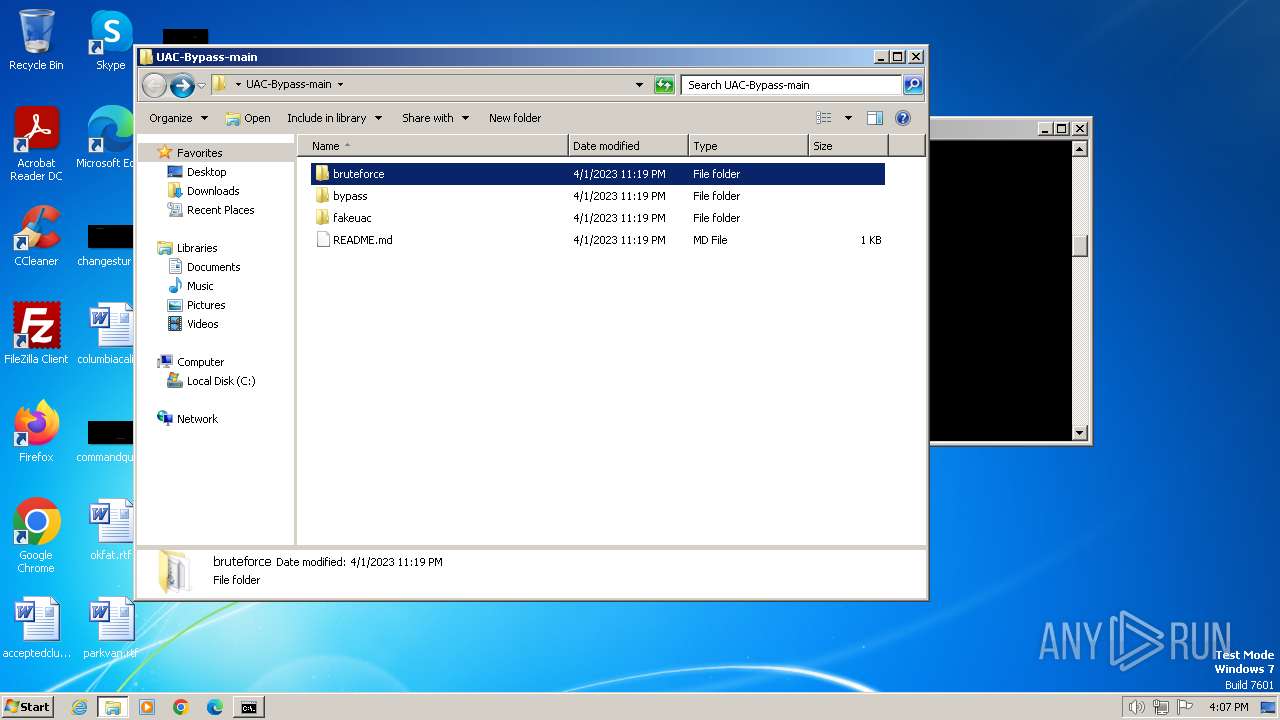
| File name: | UAC-Bypass-main.zip |
| Full analysis: | https://app.any.run/tasks/4ade8460-1c4a-4414-9729-41c5e98ec14f |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2023, 16:03:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | E0541B292557662C3A27FA0390666C06 |
| SHA1: | 000E2CFCA6D4C5EE329E57B746F8CDCD4508EF6F |
| SHA256: | 054136605F6F0DB2AE501057E94C74611F7CD0AD6C61C3D181C05EF723DC5855 |
| SSDEEP: | 384:+CNHEutqqElREJmotw7YJ0fHuOqSndmWkuUU9ReIL1XSE:/BEWcK8ot9J0QWJU8ZX |
MALICIOUS
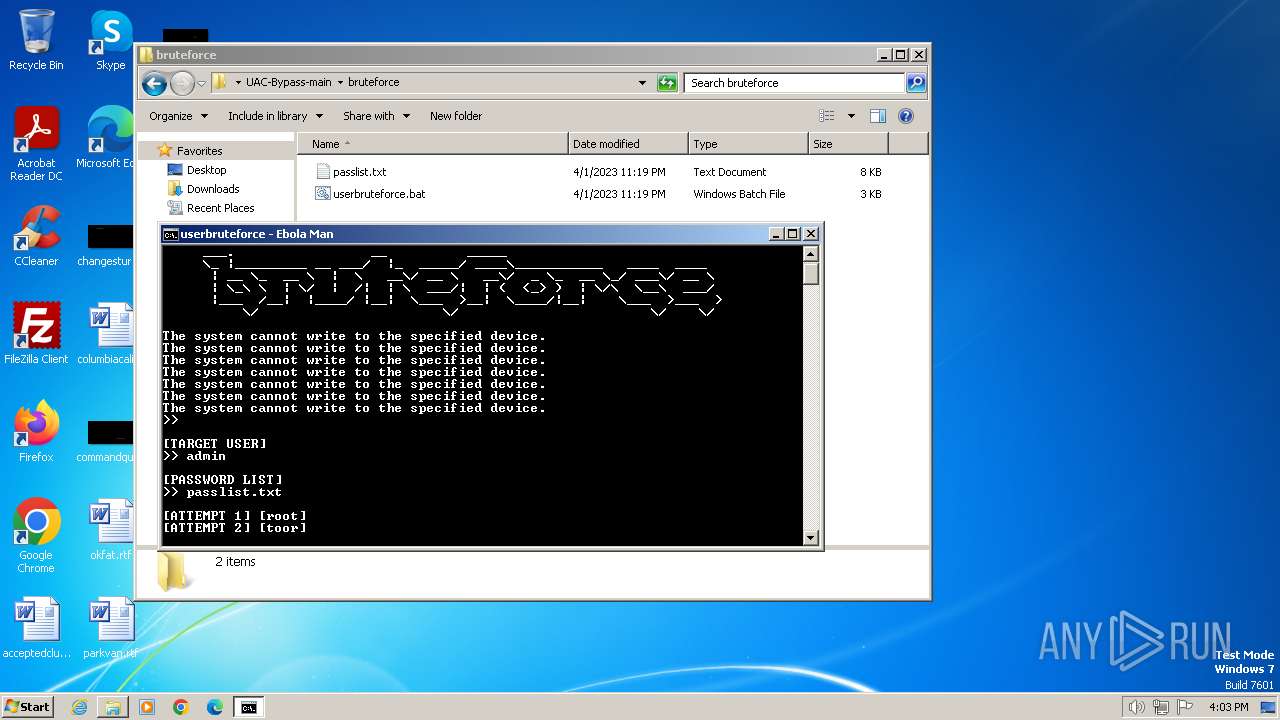
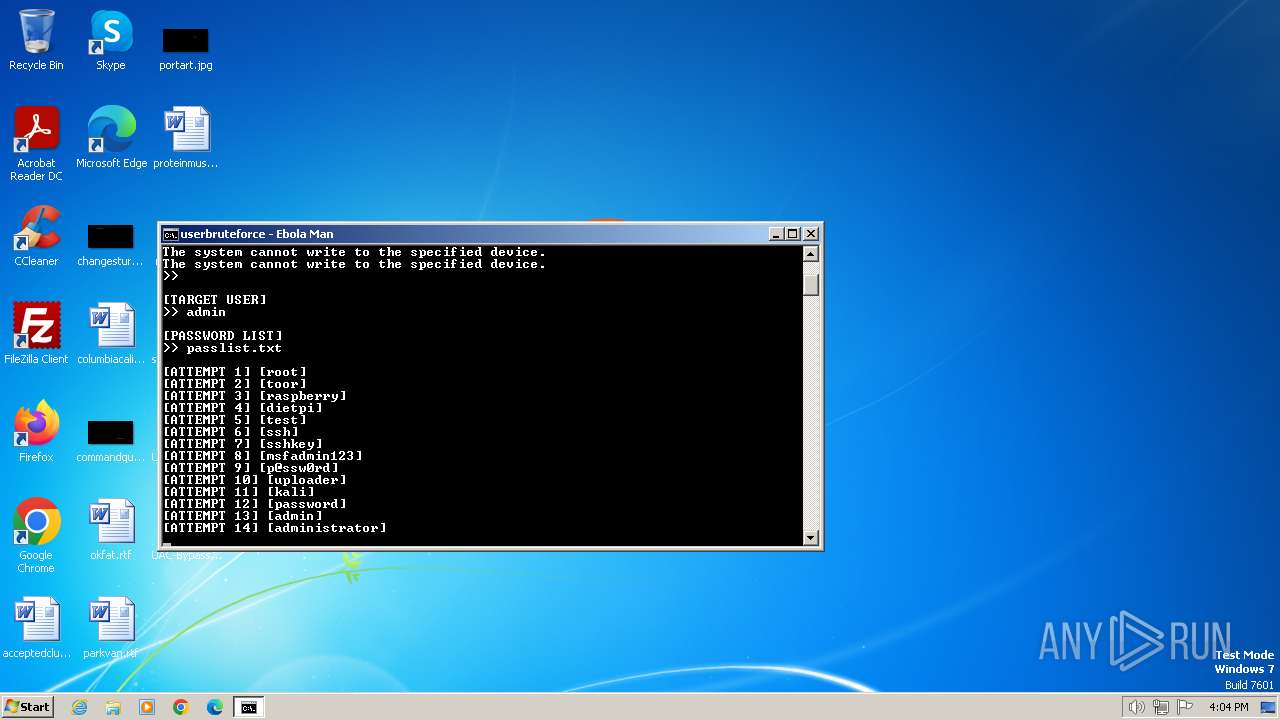
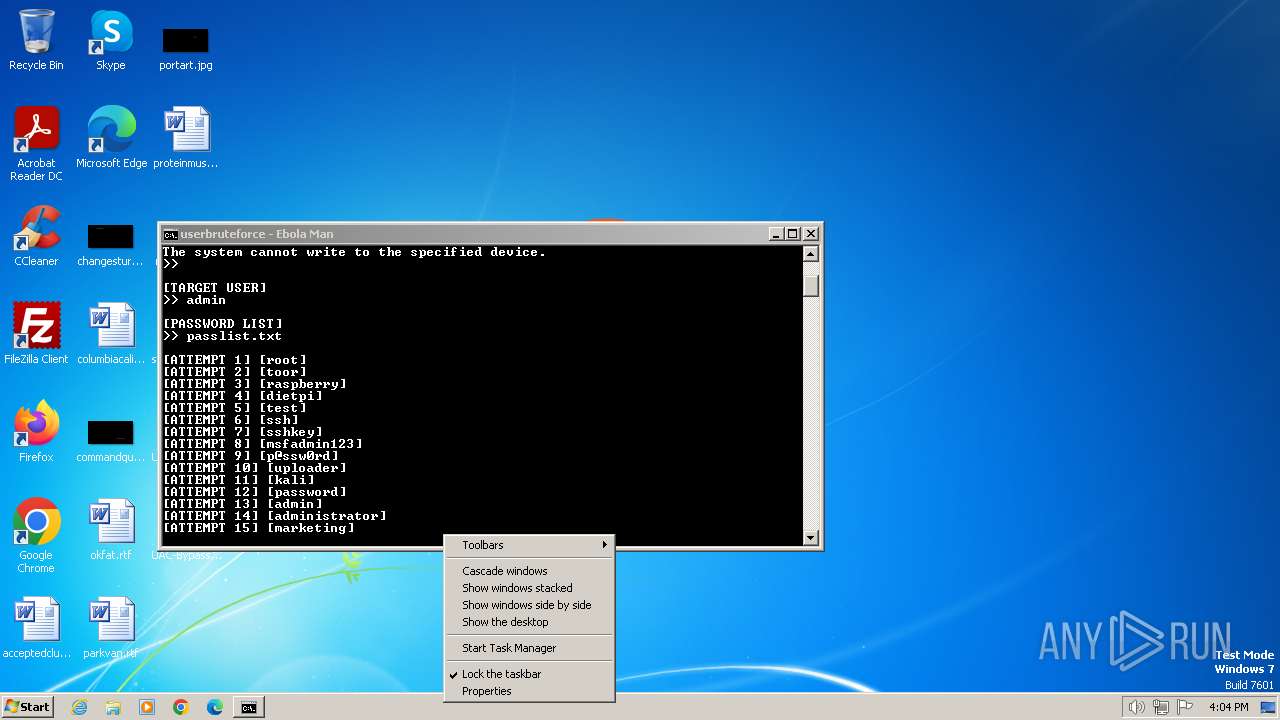
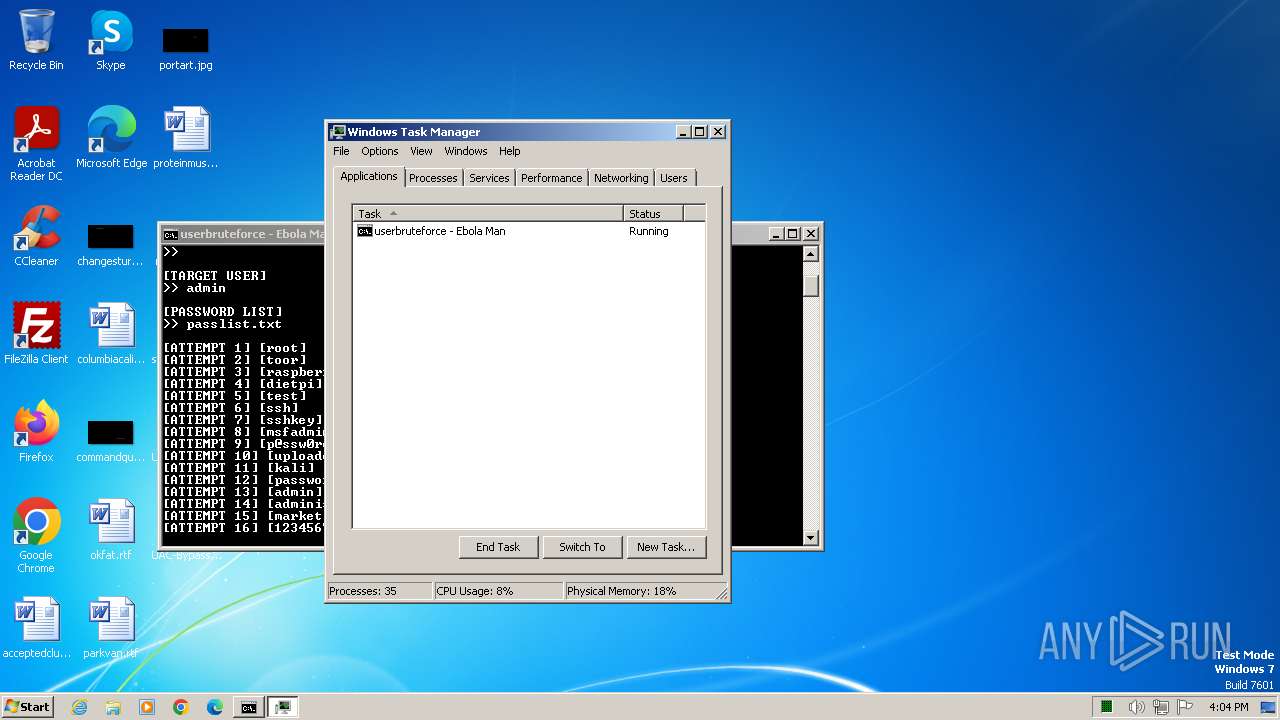
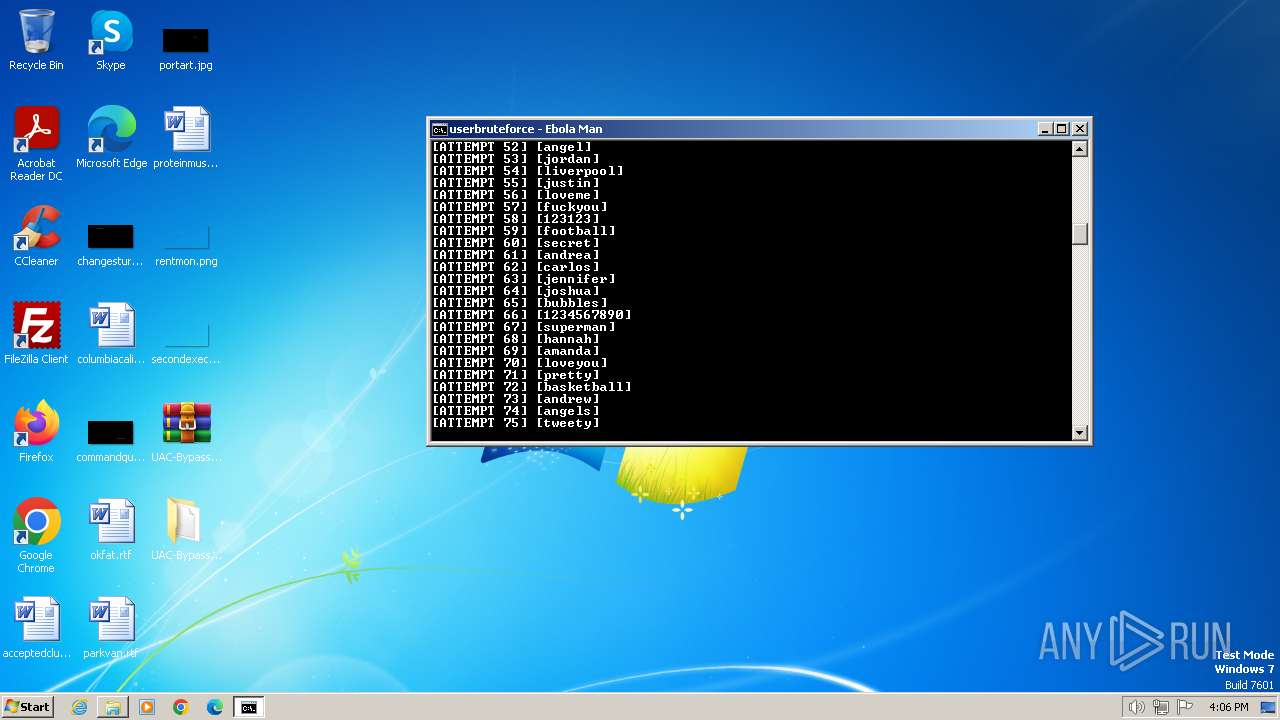
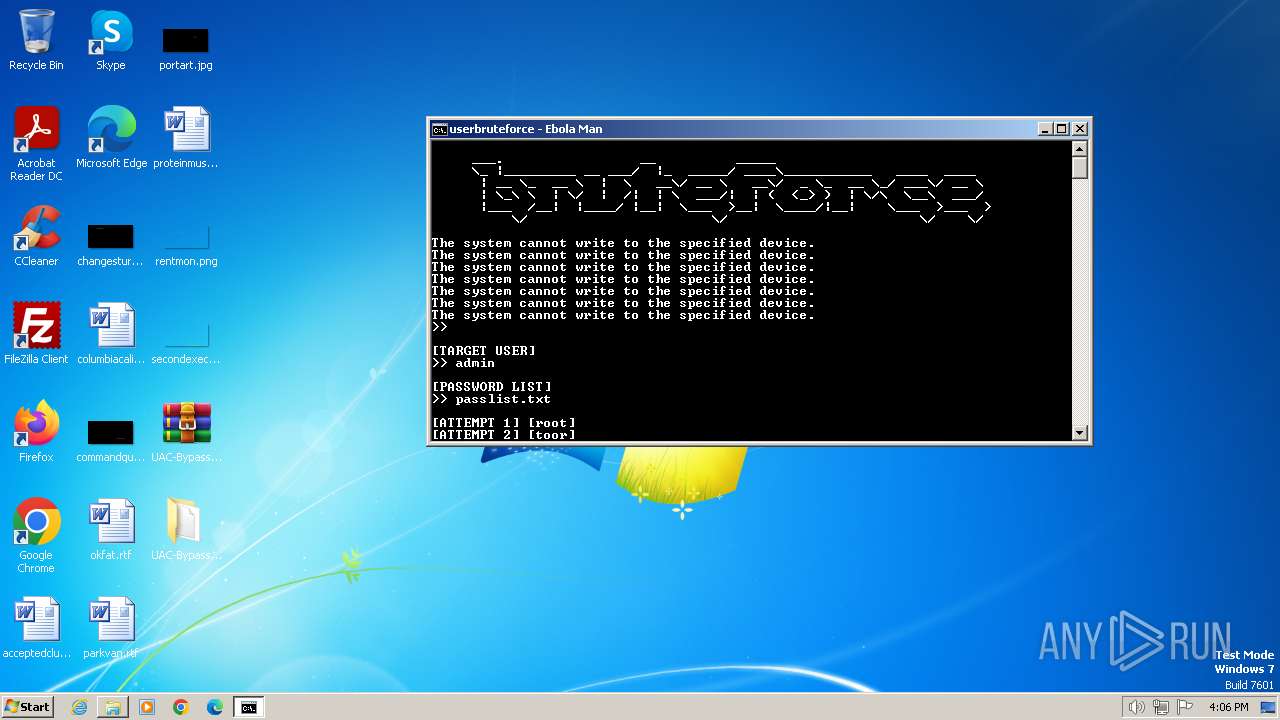
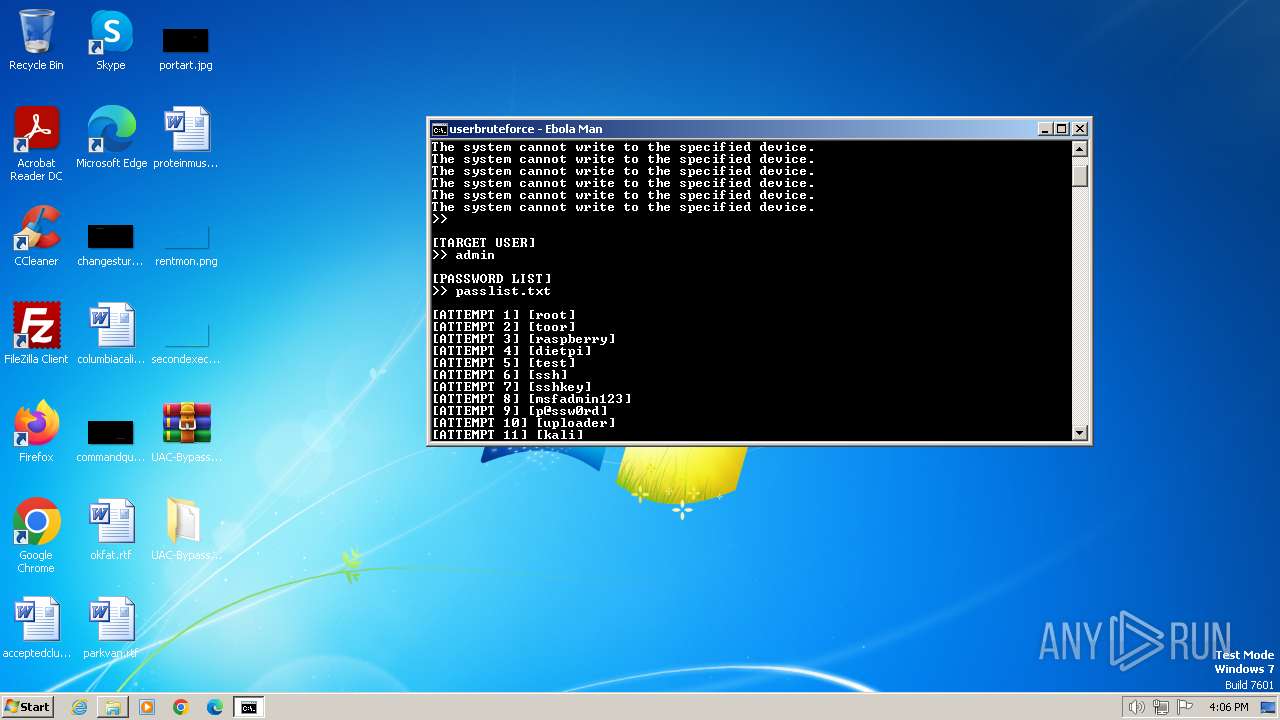
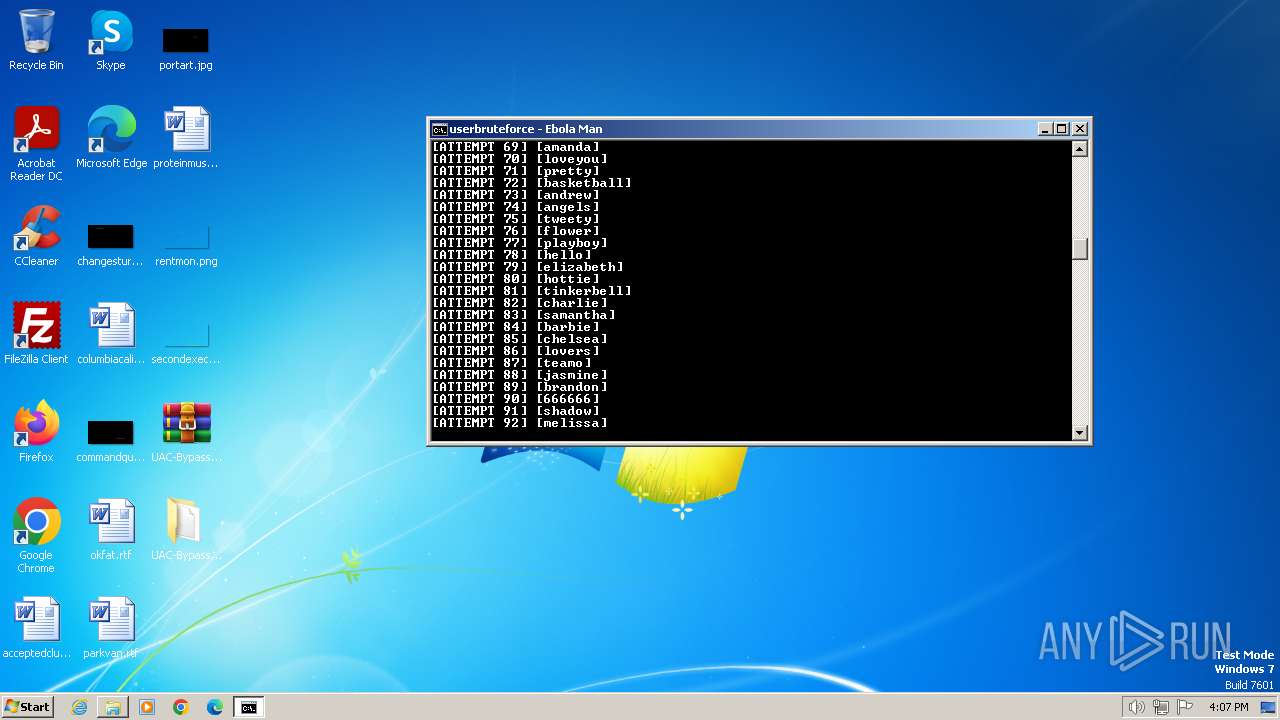
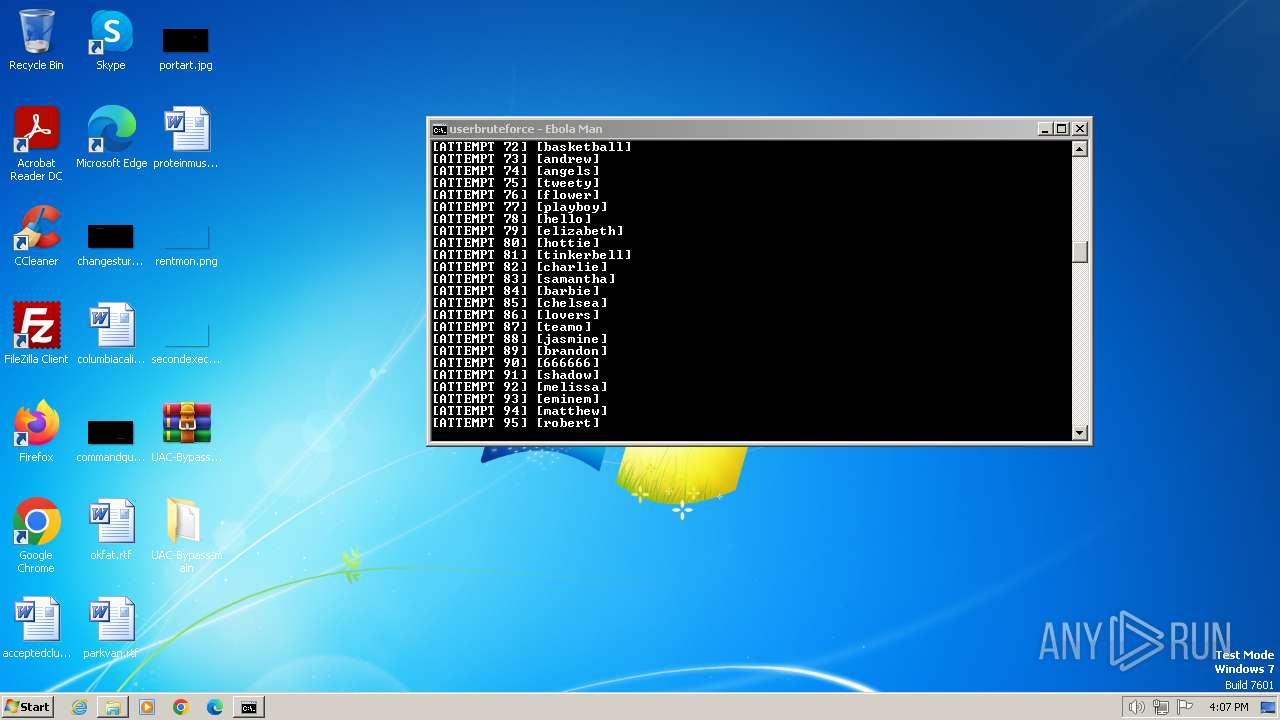
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 1636)
- cmd.exe (PID: 1820)
SUSPICIOUS
Reads the Internet Settings
- net.exe (PID: 1600)
- net.exe (PID: 1196)
- net.exe (PID: 3016)
- net.exe (PID: 2908)
- net.exe (PID: 1904)
- net.exe (PID: 2692)
- net.exe (PID: 2732)
- net.exe (PID: 3060)
- net.exe (PID: 968)
- net.exe (PID: 2664)
- net.exe (PID: 2384)
- net.exe (PID: 2772)
- net.exe (PID: 3124)
- net.exe (PID: 4028)
- net.exe (PID: 1344)
- net.exe (PID: 3832)
- net.exe (PID: 1936)
- net.exe (PID: 1848)
- net.exe (PID: 568)
- net.exe (PID: 2296)
- net.exe (PID: 1880)
- net.exe (PID: 3260)
- net.exe (PID: 3492)
- net.exe (PID: 2132)
- net.exe (PID: 2428)
- net.exe (PID: 2372)
- net.exe (PID: 4084)
- net.exe (PID: 1572)
- net.exe (PID: 2860)
- net.exe (PID: 3704)
- net.exe (PID: 2596)
- net.exe (PID: 3032)
- net.exe (PID: 1932)
- net.exe (PID: 2664)
- net.exe (PID: 2904)
- net.exe (PID: 3920)
- net.exe (PID: 3500)
- net.exe (PID: 3544)
- net.exe (PID: 3288)
- net.exe (PID: 4028)
- net.exe (PID: 3784)
- net.exe (PID: 3660)
- net.exe (PID: 2056)
- net.exe (PID: 3860)
- net.exe (PID: 2020)
- net.exe (PID: 2452)
- net.exe (PID: 3096)
- net.exe (PID: 3336)
- net.exe (PID: 996)
- net.exe (PID: 2508)
- net.exe (PID: 1832)
- net.exe (PID: 952)
- net.exe (PID: 552)
- net.exe (PID: 3040)
- net.exe (PID: 3352)
- net.exe (PID: 2652)
- net.exe (PID: 3904)
- net.exe (PID: 2556)
- net.exe (PID: 3920)
- net.exe (PID: 2976)
- net.exe (PID: 3968)
- net.exe (PID: 3532)
- net.exe (PID: 3748)
- net.exe (PID: 3876)
- net.exe (PID: 1432)
- net.exe (PID: 3784)
- net.exe (PID: 1020)
- net.exe (PID: 2084)
- net.exe (PID: 1380)
- net.exe (PID: 1232)
- net.exe (PID: 3484)
- net.exe (PID: 1652)
- net.exe (PID: 2760)
- net.exe (PID: 3472)
- net.exe (PID: 2668)
- net.exe (PID: 3336)
- net.exe (PID: 3284)
- net.exe (PID: 2648)
- net.exe (PID: 2584)
- net.exe (PID: 2460)
- net.exe (PID: 2812)
- net.exe (PID: 3972)
- net.exe (PID: 3512)
- net.exe (PID: 2364)
- net.exe (PID: 2836)
- net.exe (PID: 3000)
- net.exe (PID: 1388)
- net.exe (PID: 1308)
- net.exe (PID: 1924)
- net.exe (PID: 2480)
- net.exe (PID: 1236)
- net.exe (PID: 1808)
- net.exe (PID: 4036)
- net.exe (PID: 2204)
- net.exe (PID: 1088)
- net.exe (PID: 2072)
- net.exe (PID: 2388)
- net.exe (PID: 2660)
- net.exe (PID: 2804)
- net.exe (PID: 2904)
- net.exe (PID: 1632)
- net.exe (PID: 2360)
- net.exe (PID: 3044)
- net.exe (PID: 3488)
- net.exe (PID: 2944)
- net.exe (PID: 3496)
- net.exe (PID: 1124)
- net.exe (PID: 2148)
- net.exe (PID: 3936)
- net.exe (PID: 2532)
- net.exe (PID: 3348)
- net.exe (PID: 3104)
- net.exe (PID: 2616)
- net.exe (PID: 3672)
- net.exe (PID: 3864)
- net.exe (PID: 752)
- net.exe (PID: 2892)
- net.exe (PID: 1424)
- net.exe (PID: 3716)
- net.exe (PID: 3012)
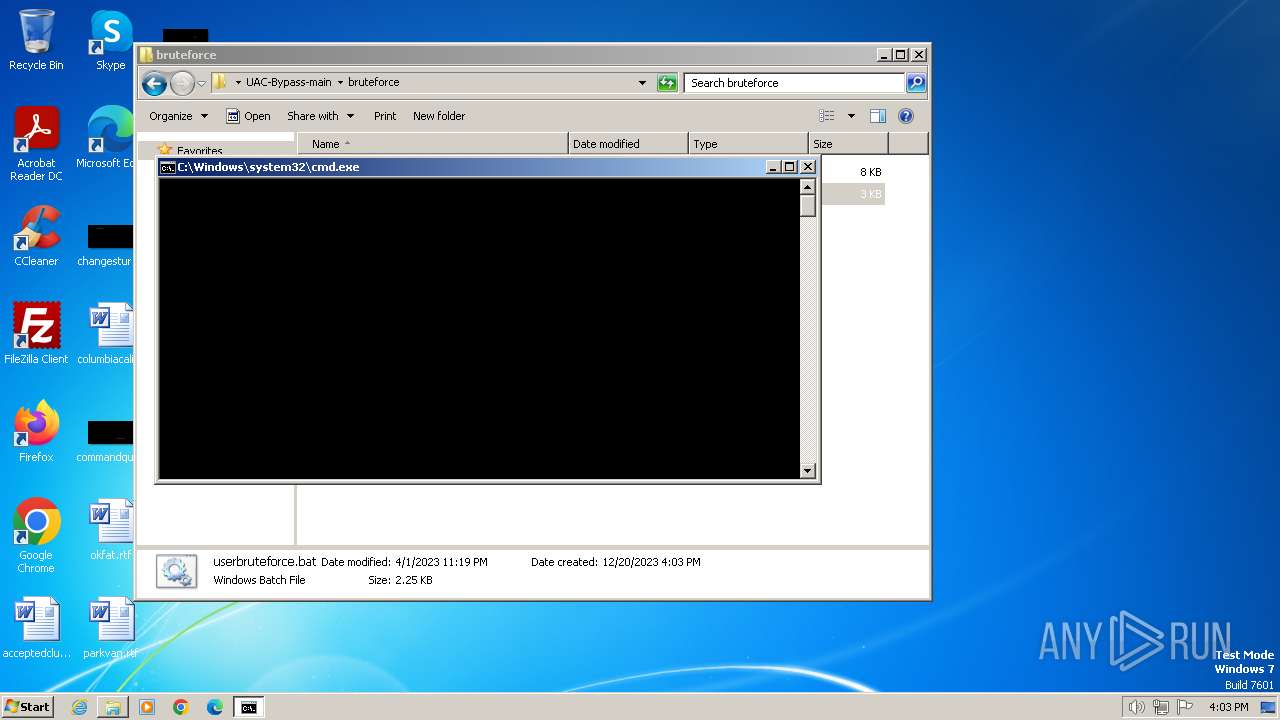
Starts application with an unusual extension
- cmd.exe (PID: 1820)
Starts NET.EXE to map network drives
- cmd.exe (PID: 1820)
INFO
Drops the executable file immediately after the start
- WinRAR.exe (PID: 124)
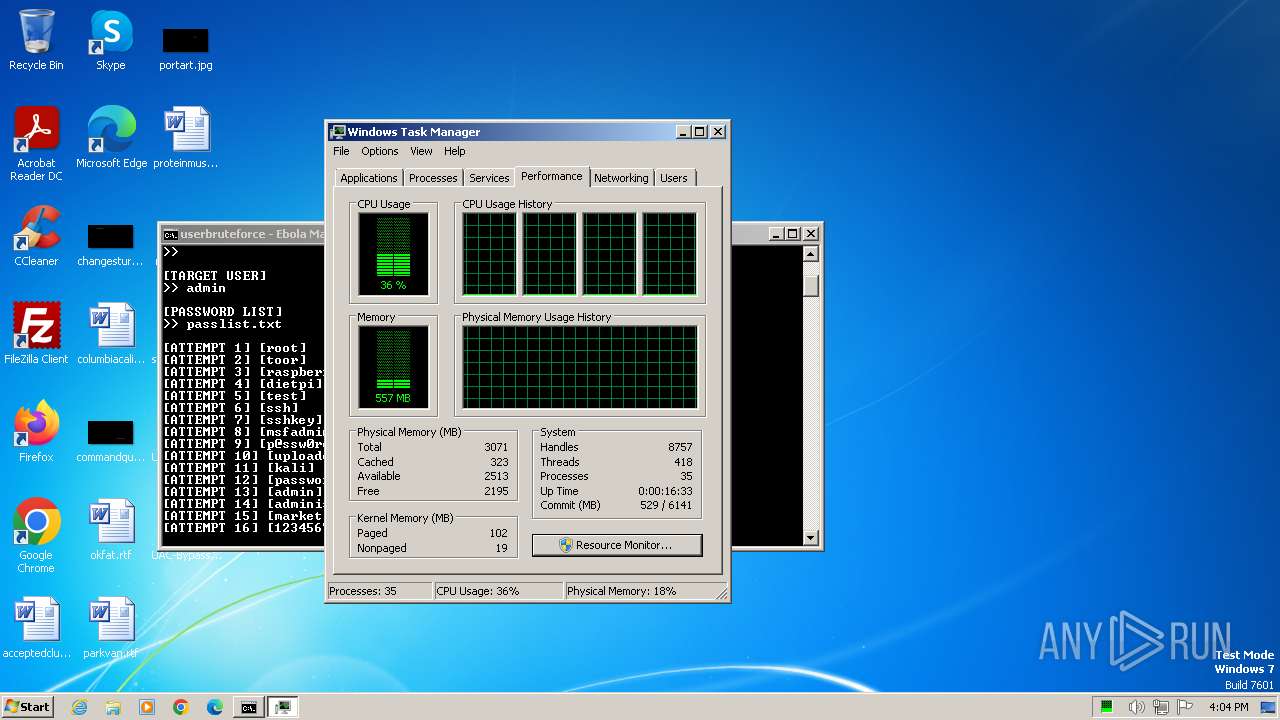
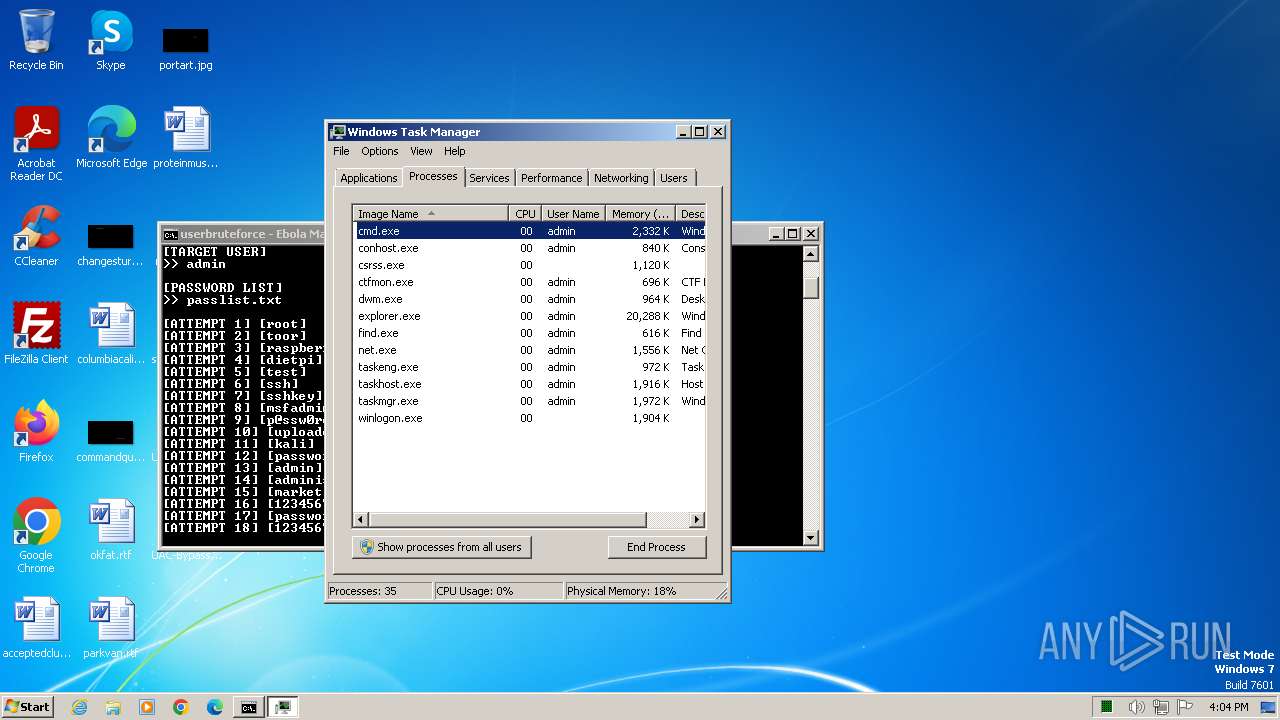
Manual execution by a user
- cmd.exe (PID: 1820)
- notepad.exe (PID: 548)
- taskmgr.exe (PID: 3664)
Checks supported languages
- chcp.com (PID: 844)
Reads the time zone
- net1.exe (PID: 2308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:04:01 15:19:06 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | UAC-Bypass-main/ |
Total processes
528
Monitored processes
487
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
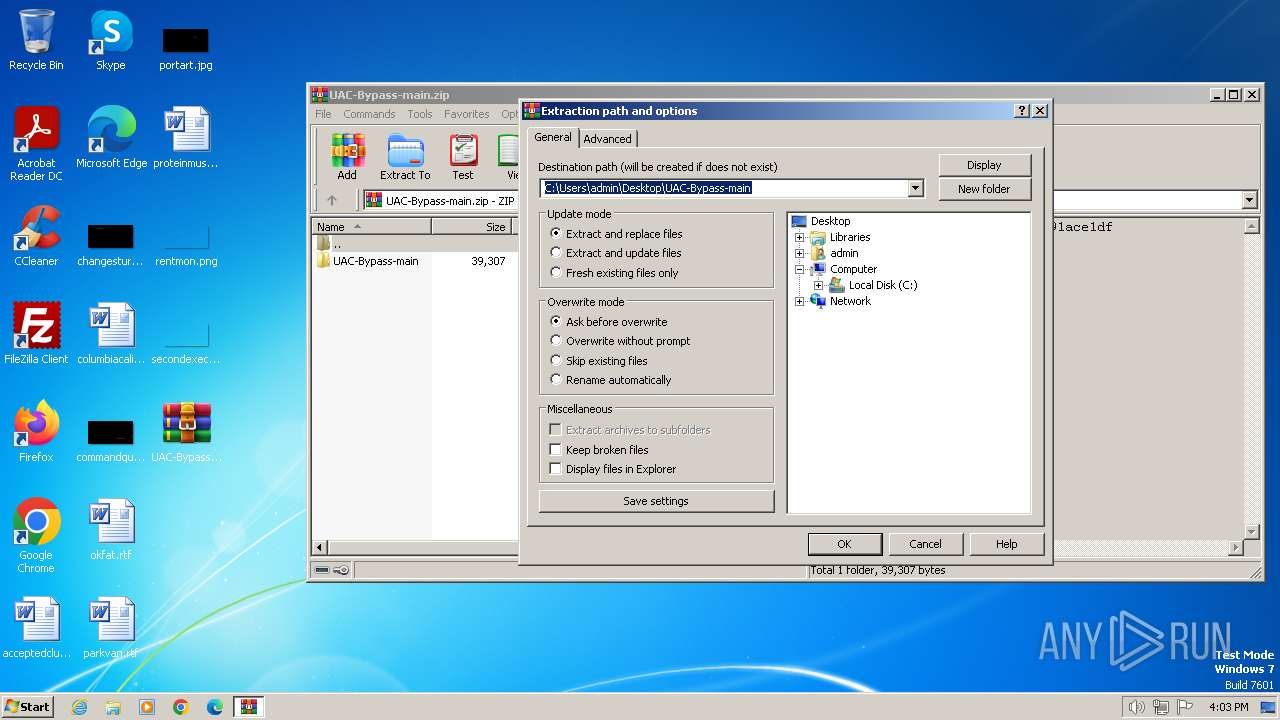
| 124 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\UAC-Bypass-main.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 188 | net use | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | find "\\127.0.0.1" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | find "System error 1331" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | find "System error 1331" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 268 | net use | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | find "System error 1331" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | find "\\127.0.0.1" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | net use | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | find "System error 1331" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
34 534
Read events
34 511
Write events
23
Delete events
0
Modification events
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
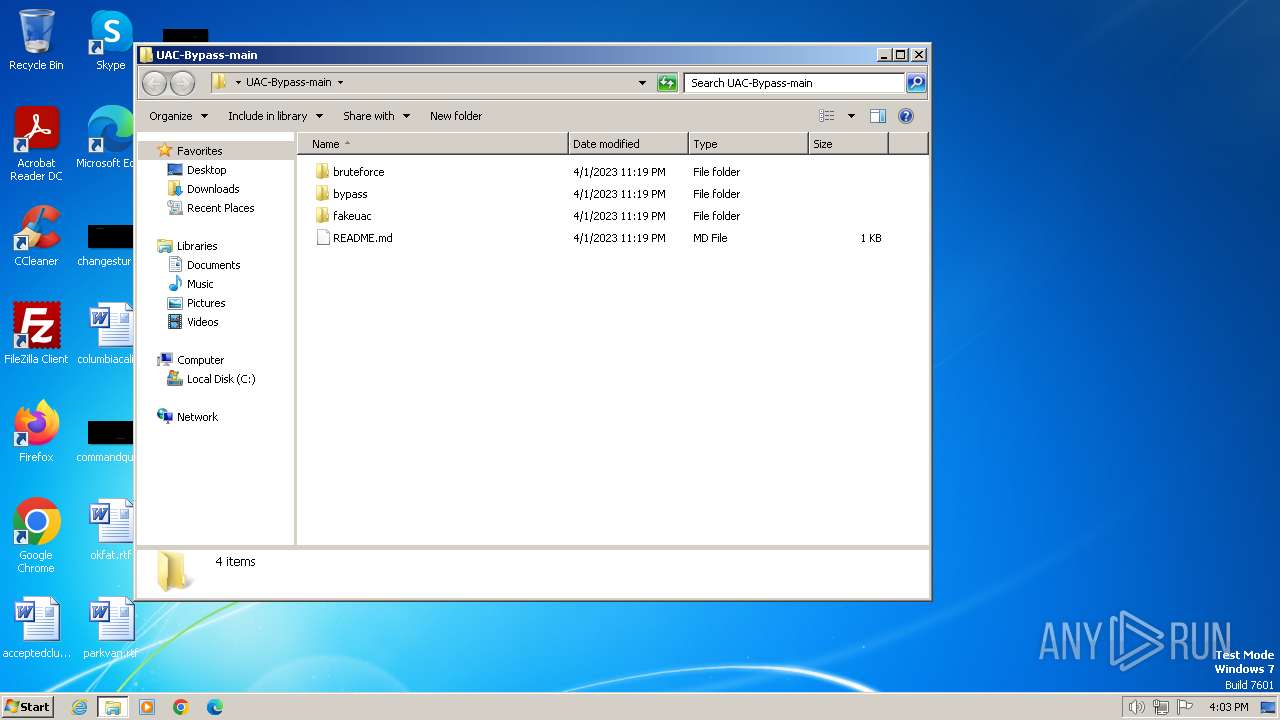
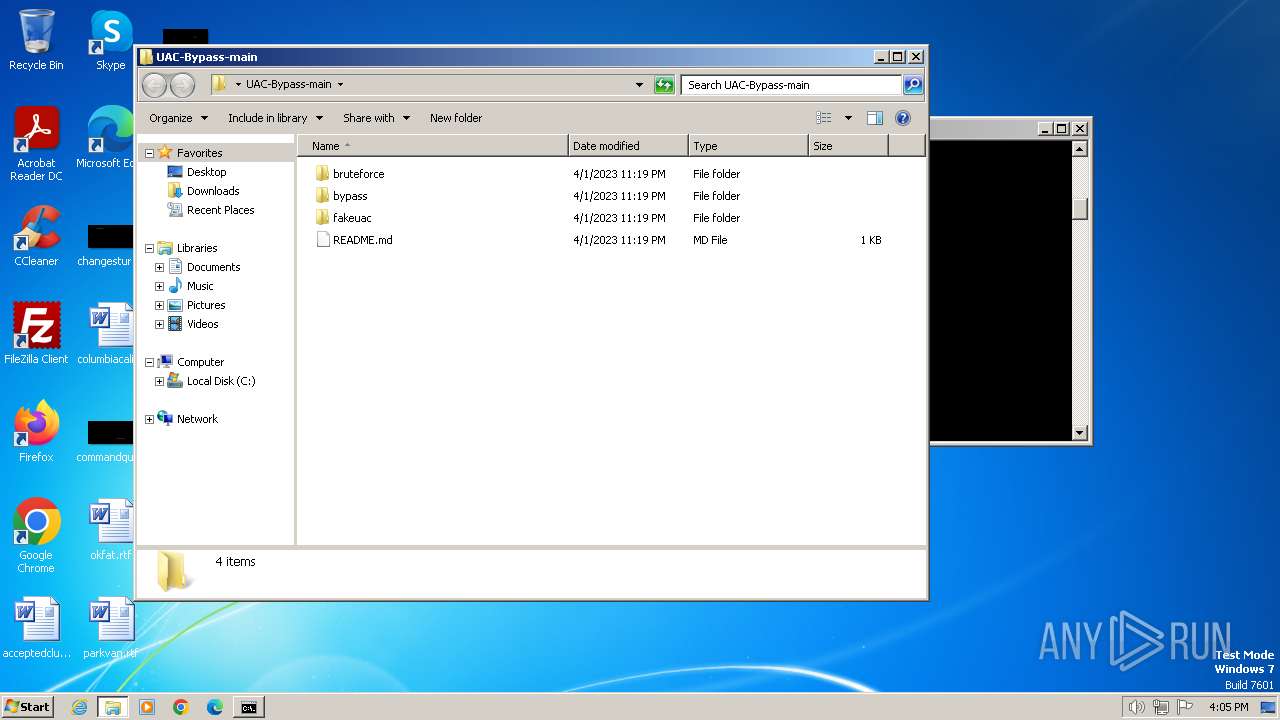
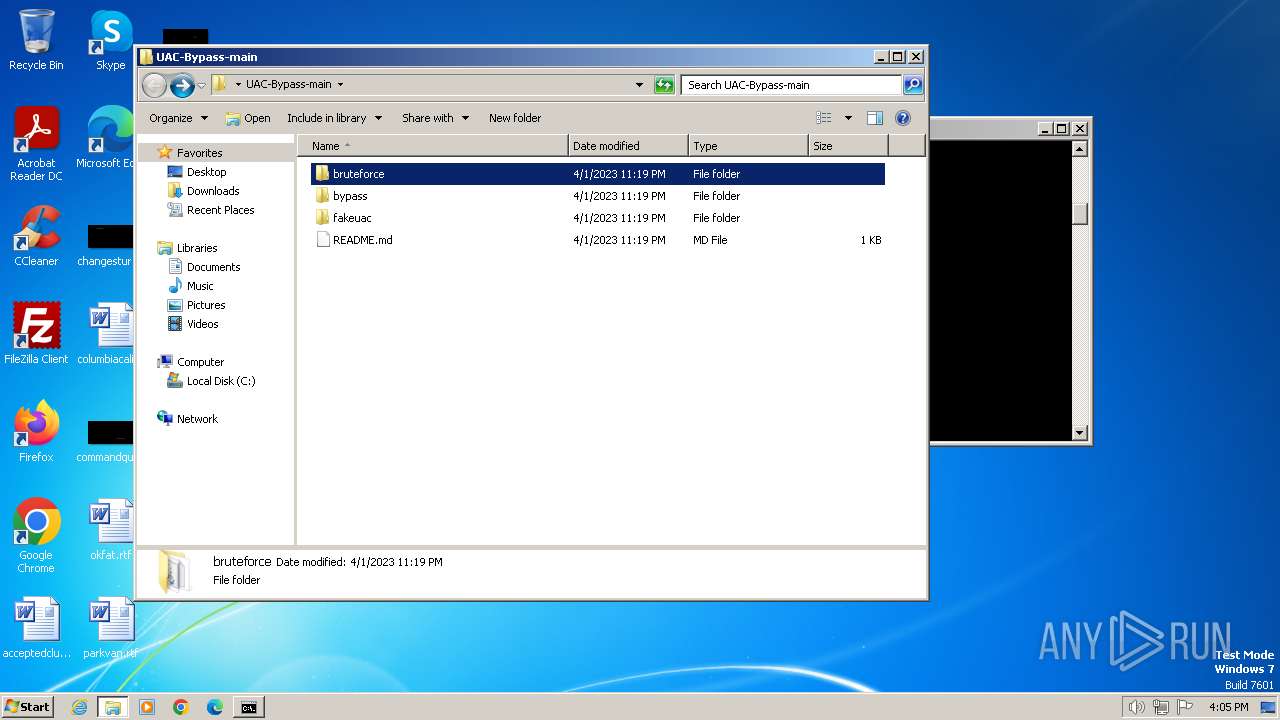
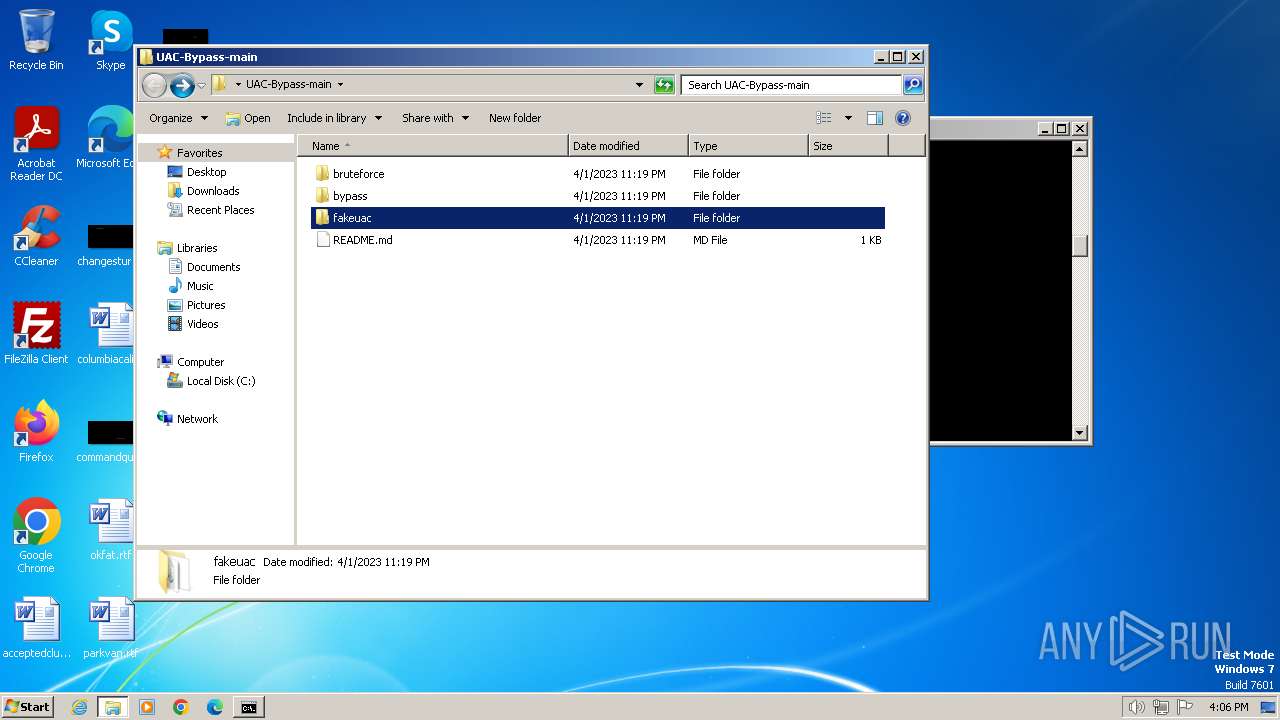
| 124 | WinRAR.exe | C:\Users\admin\Desktop\UAC-Bypass-main\README.md | text | |
MD5:A96C77B0B14B751735DB66BA25A8AC41 | SHA256:78D93AE3EE55B0BCF74EB571CD24D17DB986455377DE70D118C24B95B5AF2D1C | |||
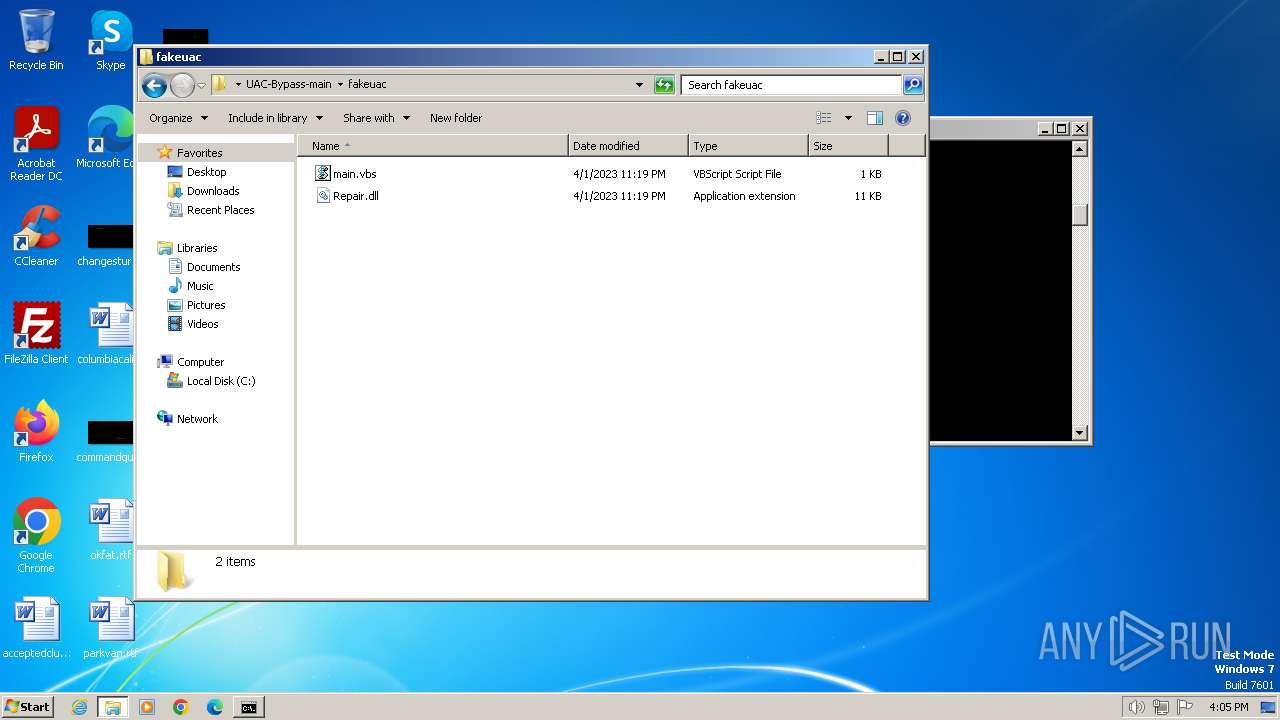
| 124 | WinRAR.exe | C:\Users\admin\Desktop\UAC-Bypass-main\fakeuac\Repair.dll | executable | |
MD5:7DBC6474F0C364E73DE100828CA4A3E5 | SHA256:E10E73AB91EADE93DC78437F54D4D5D338CA949401A2E50E6F5954BAA59CE2DA | |||
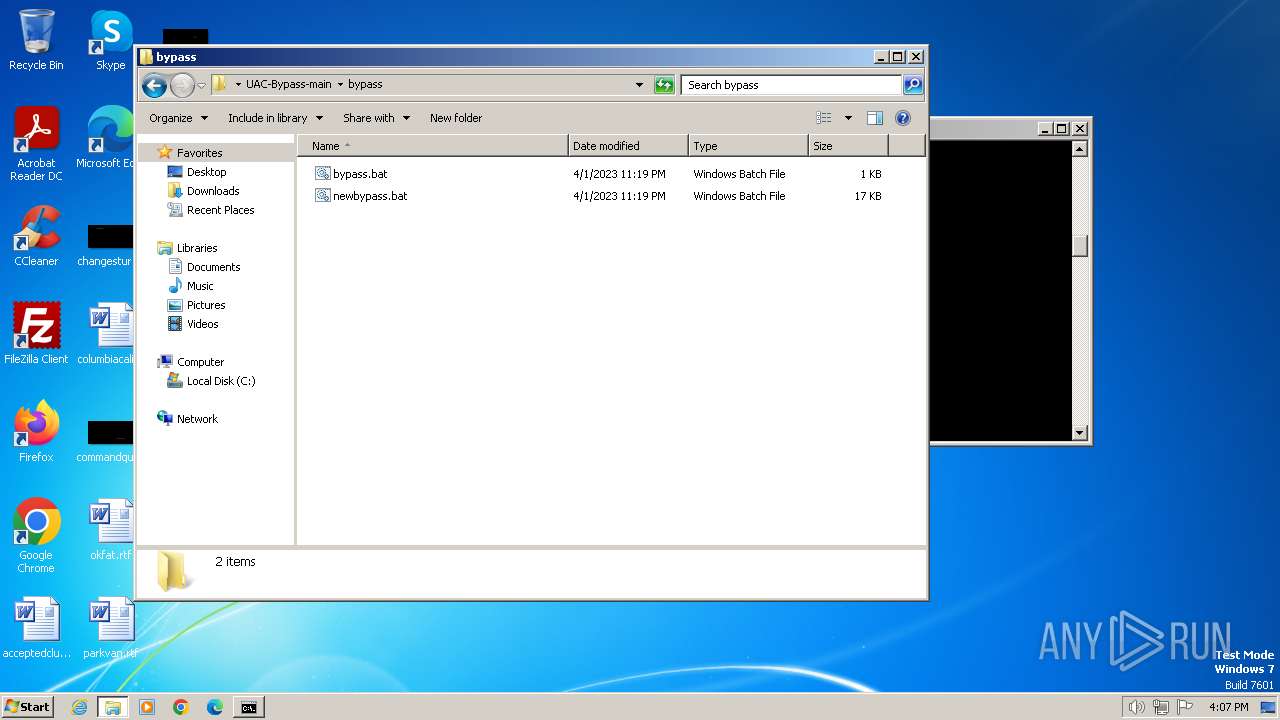
| 124 | WinRAR.exe | C:\Users\admin\Desktop\UAC-Bypass-main\bypass\bypass.bat | text | |
MD5:78437AFE24F3EA7E6E4857C933B064C9 | SHA256:91794F3EAAA83D113FF55E7812A0C8F840887251B83413D4F0D9AC394D133B90 | |||
| 124 | WinRAR.exe | C:\Users\admin\Desktop\UAC-Bypass-main\bypass\newbypass.bat | text | |
MD5:8D03525FFF275F7AC3EBA742EF24E3AE | SHA256:A4D01181ED6E9C6CB7A02081DB67982C32F01C7EC0A96F264F2C306D390DAB49 | |||
| 124 | WinRAR.exe | C:\Users\admin\Desktop\UAC-Bypass-main\fakeuac\main.vbs | text | |
MD5:897C4666D9D669DB6EDA37E21085085E | SHA256:CA4AABB3968B7AB7823A7734E110C6C871CFA497B37F134516E71CBE670D1950 | |||
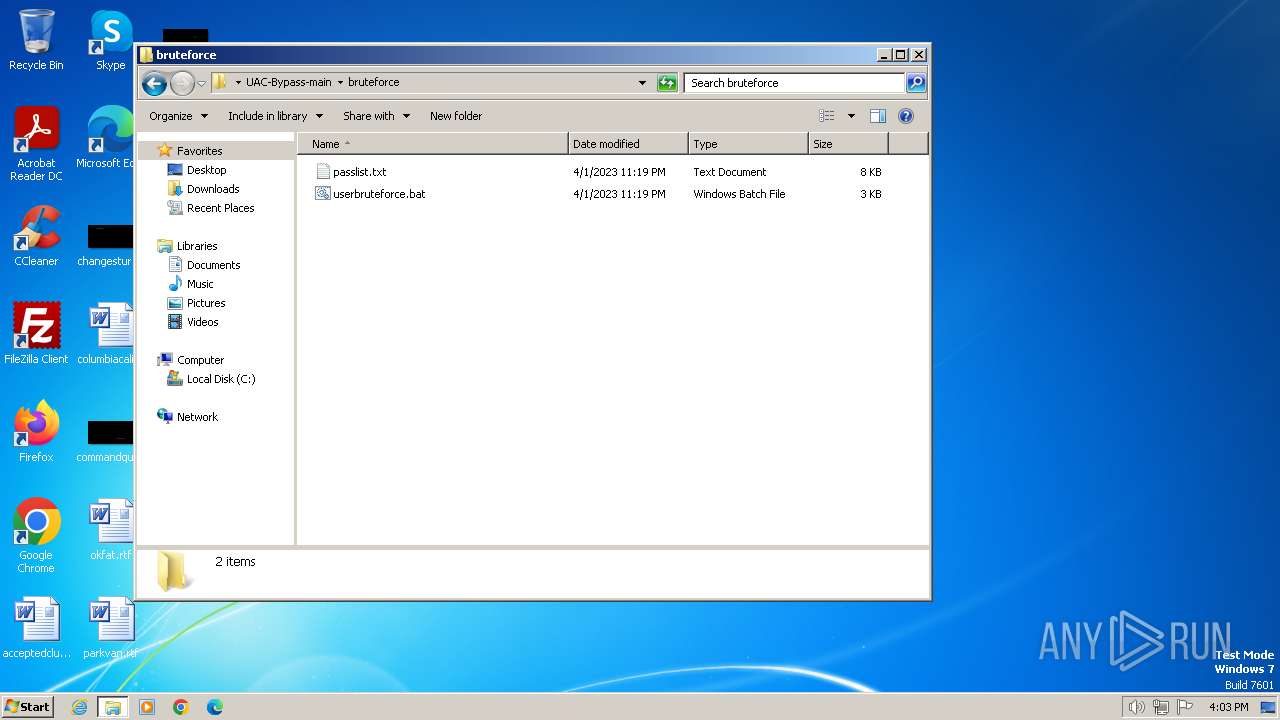
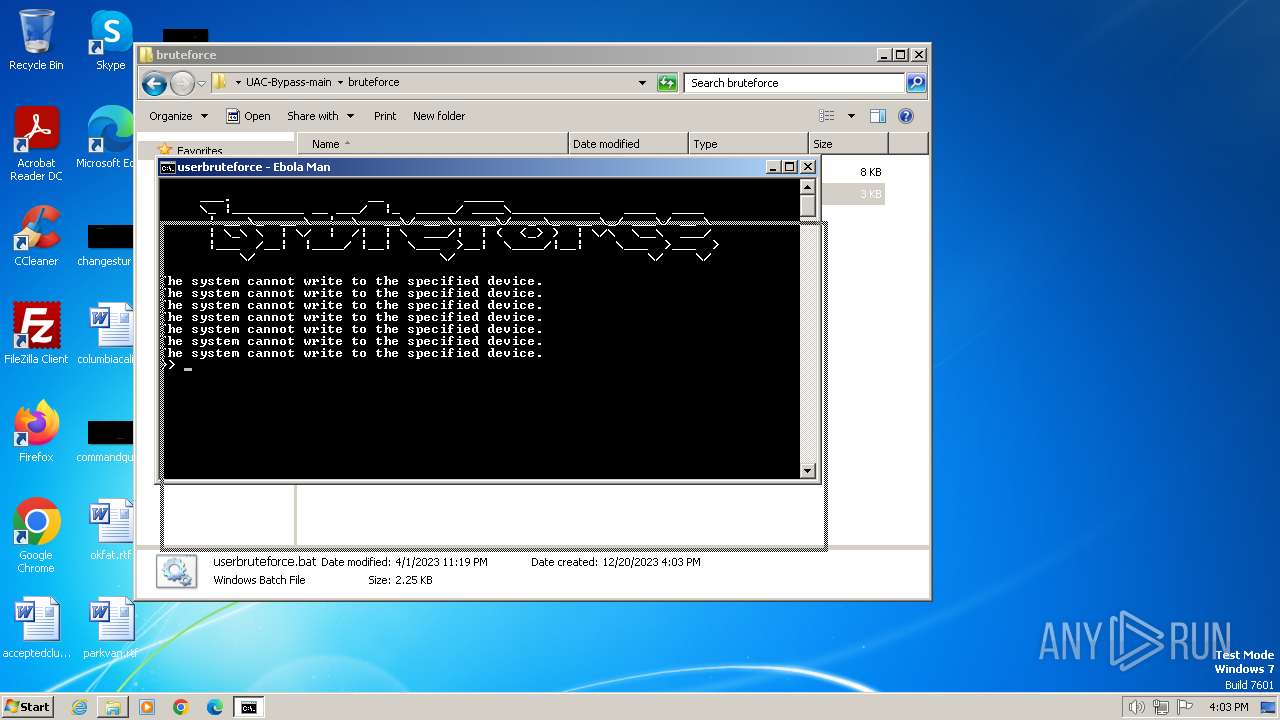
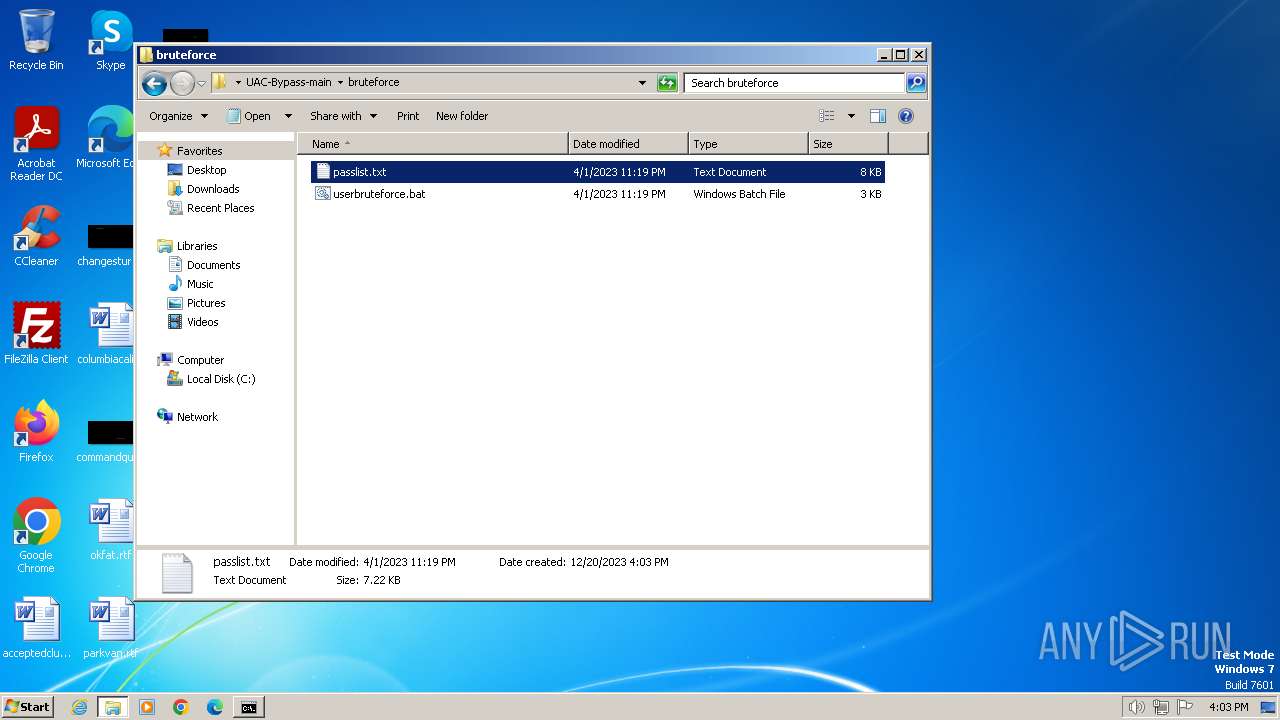
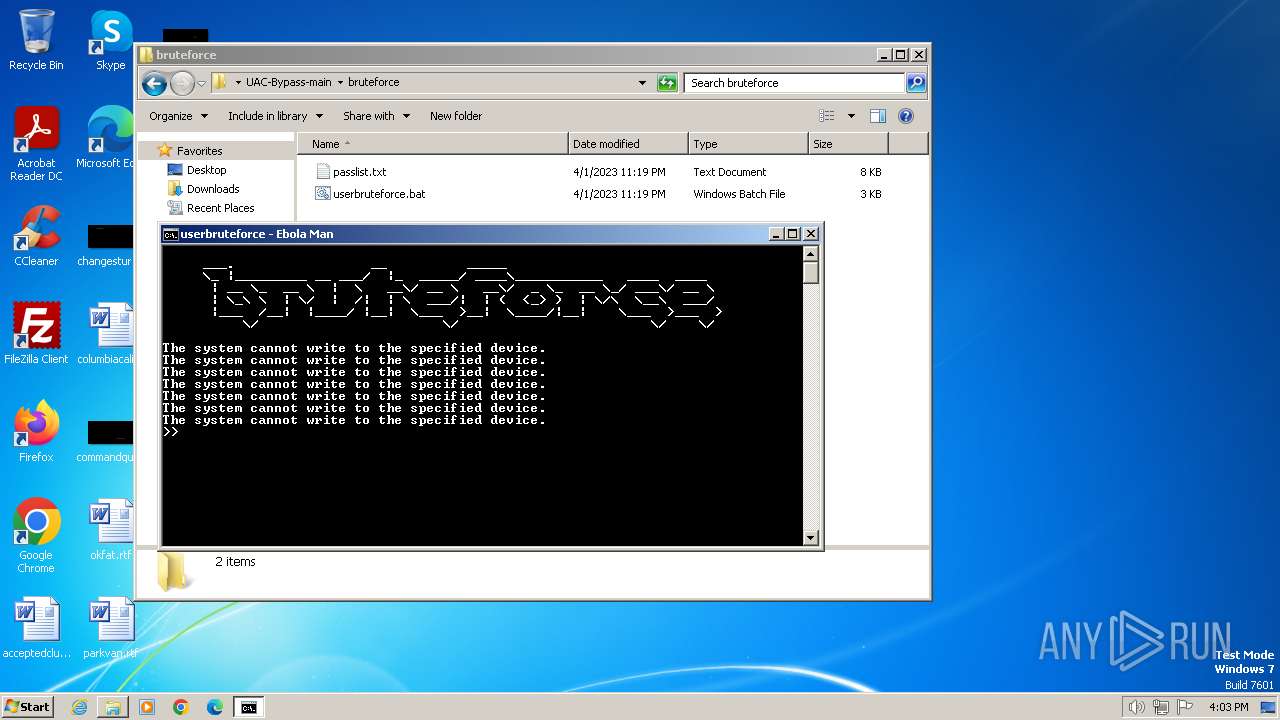
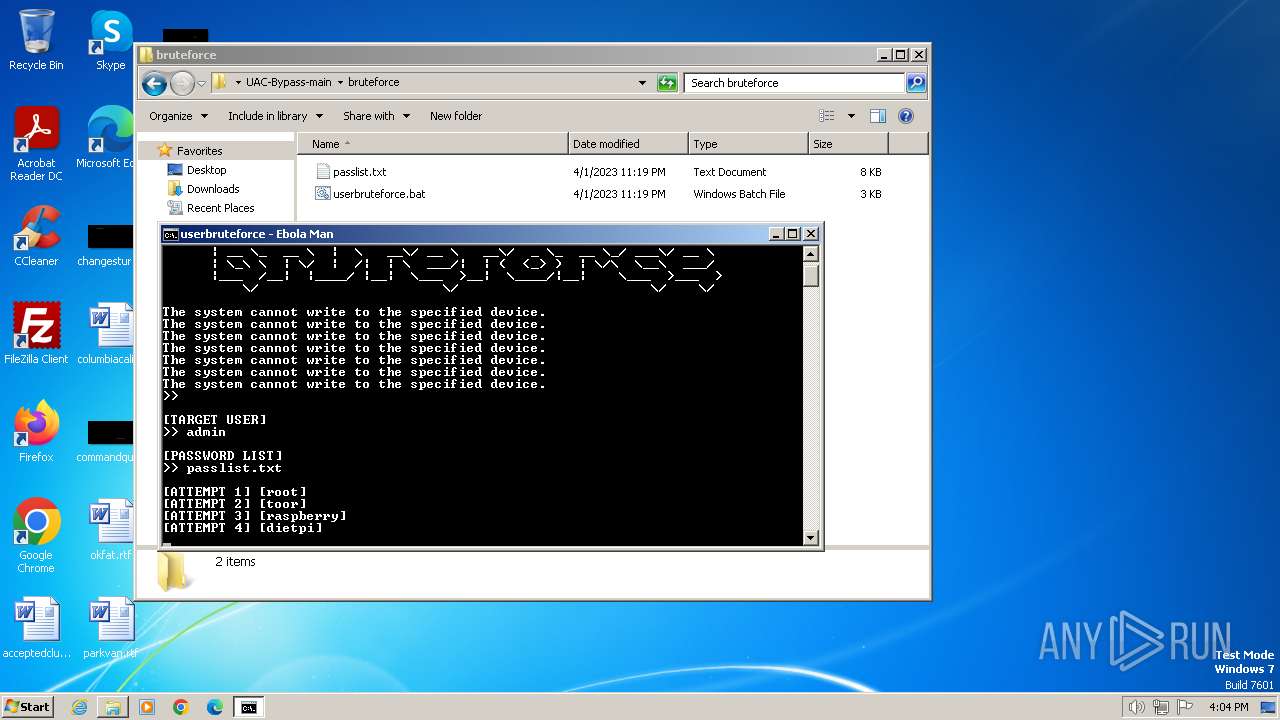
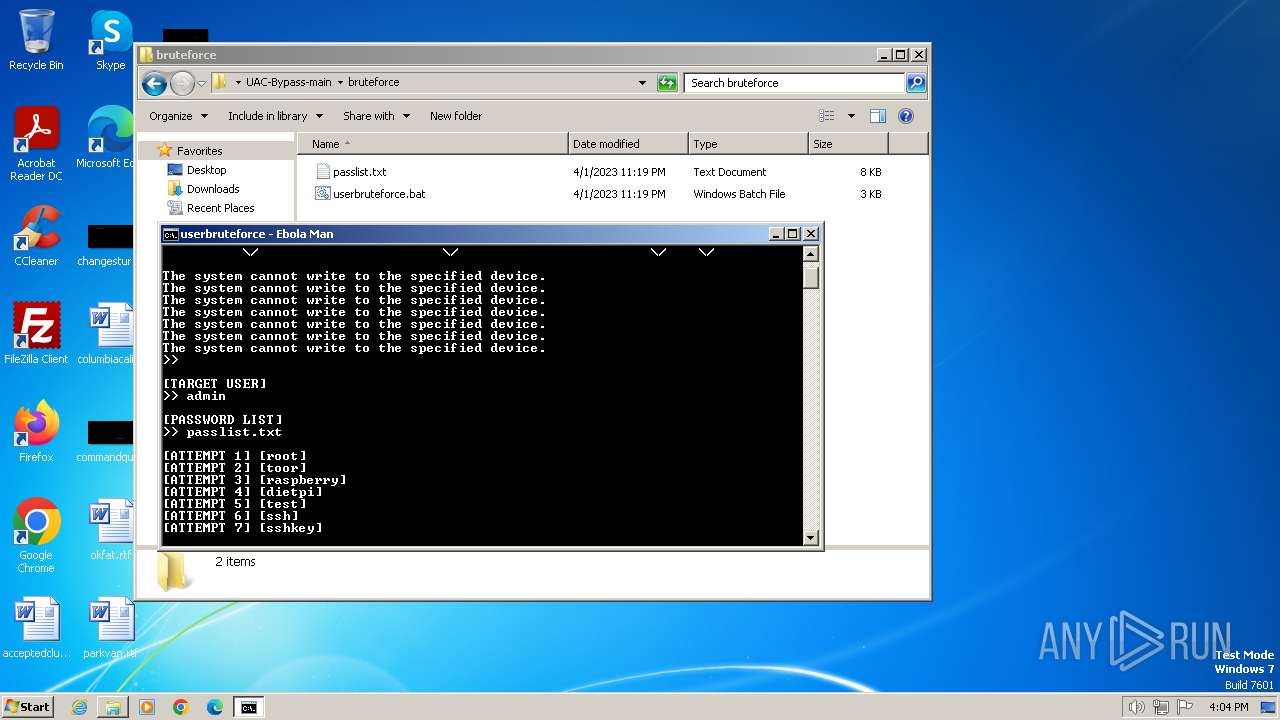
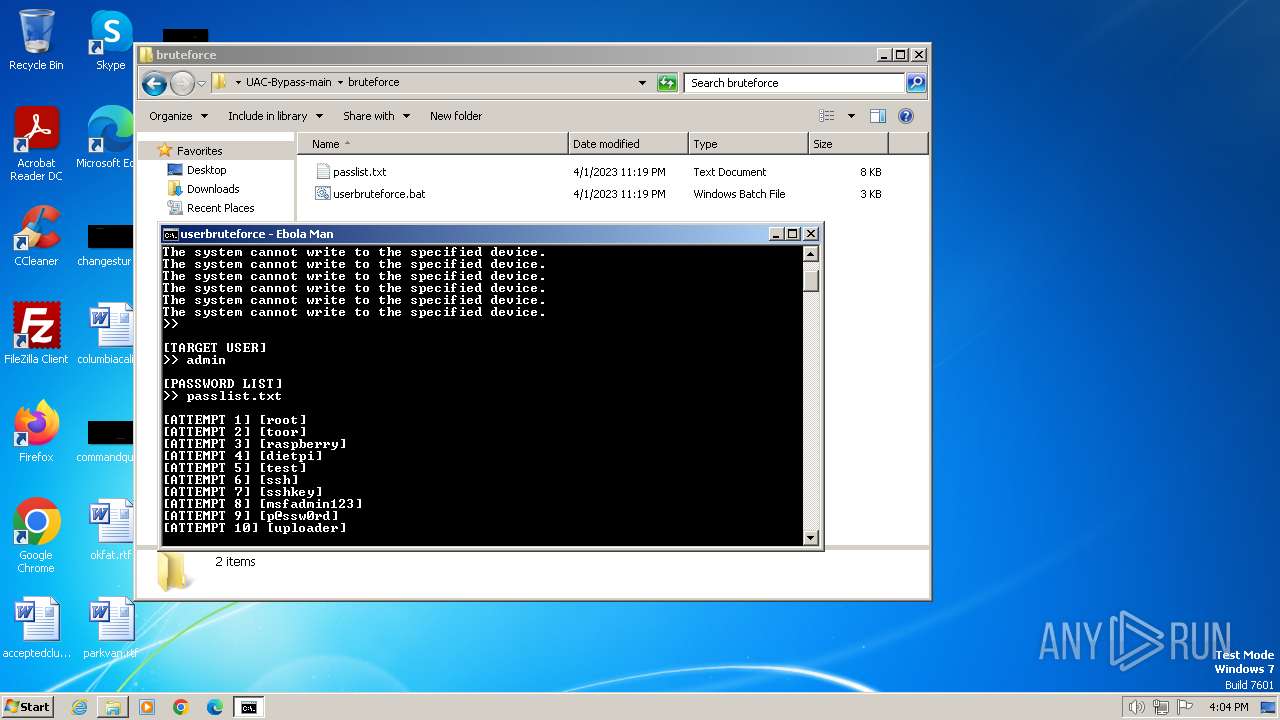
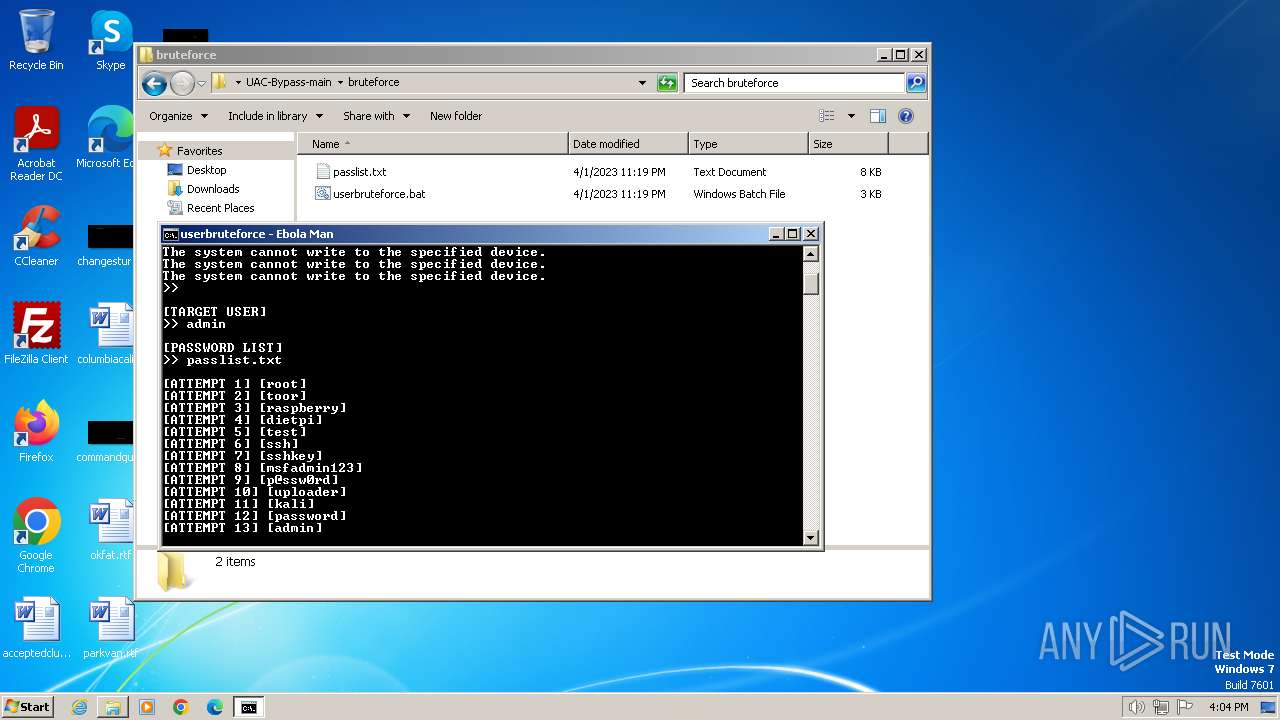
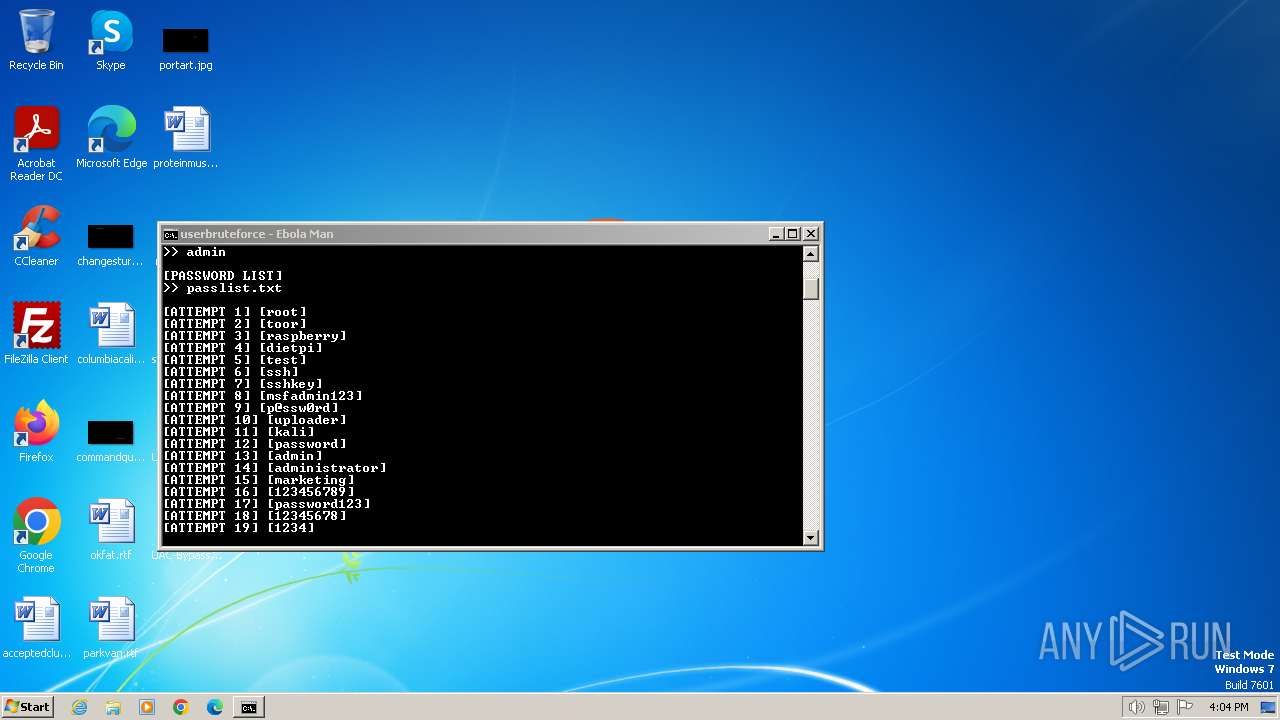
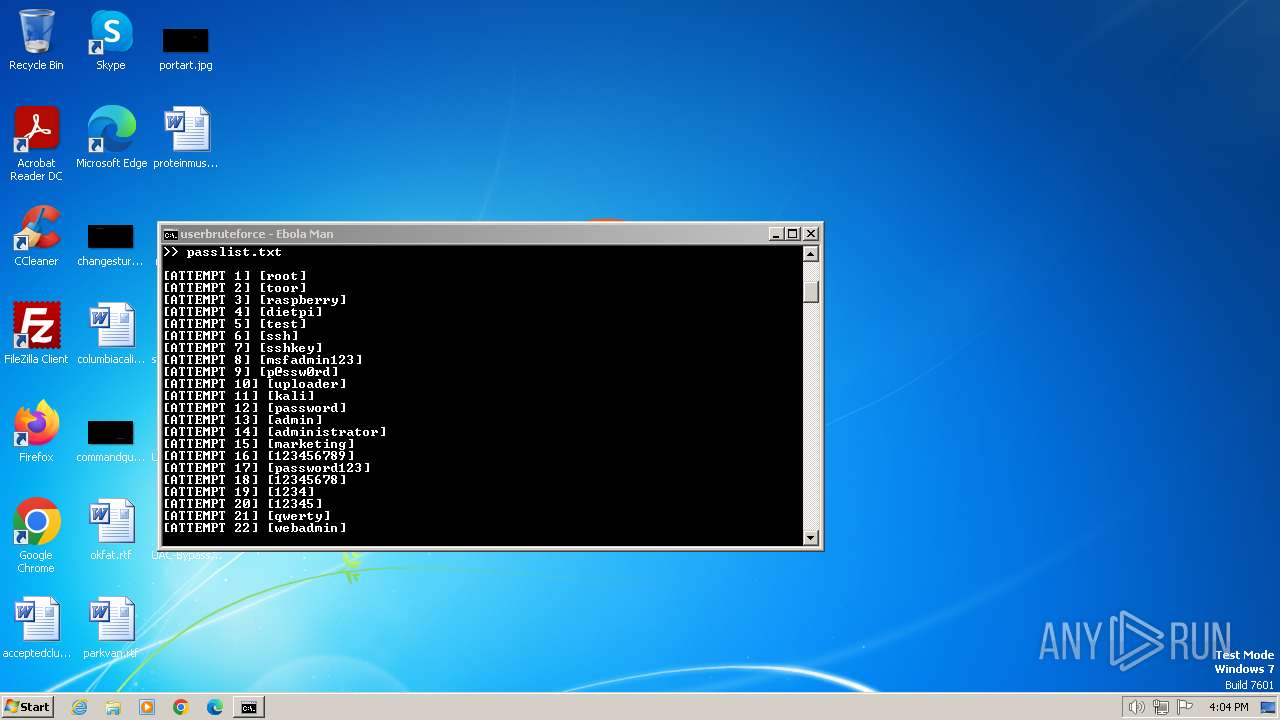
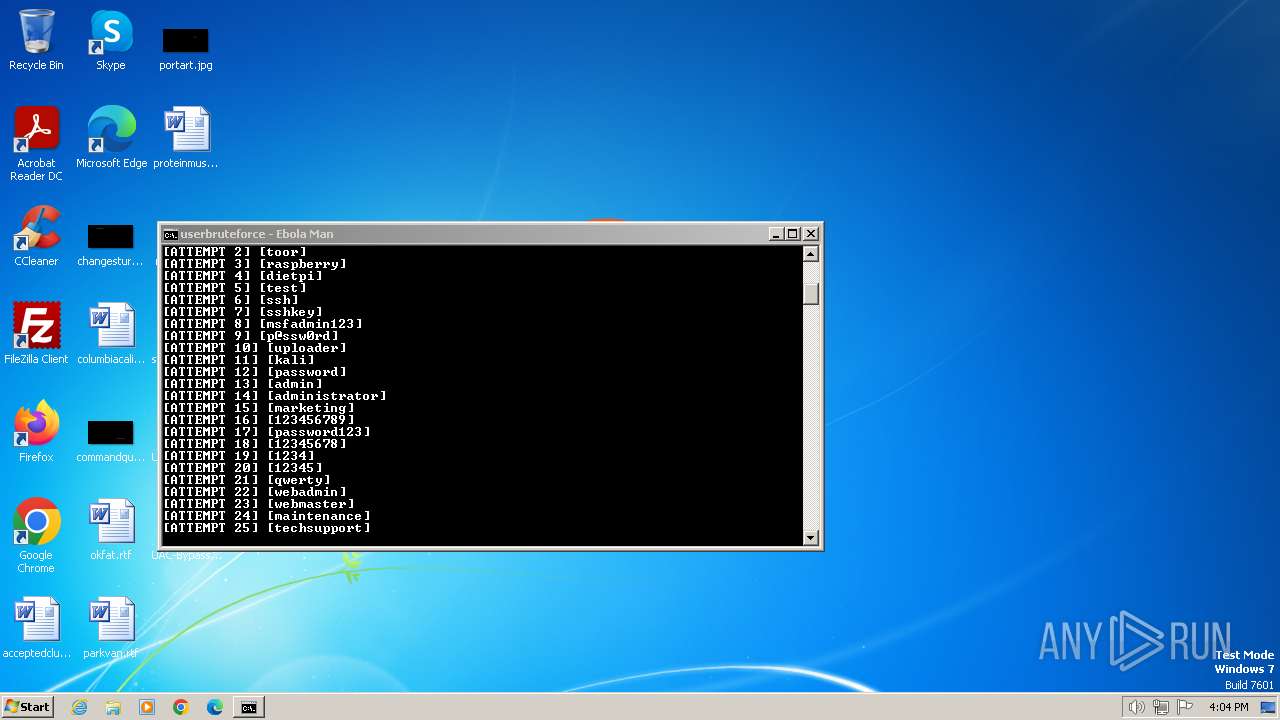
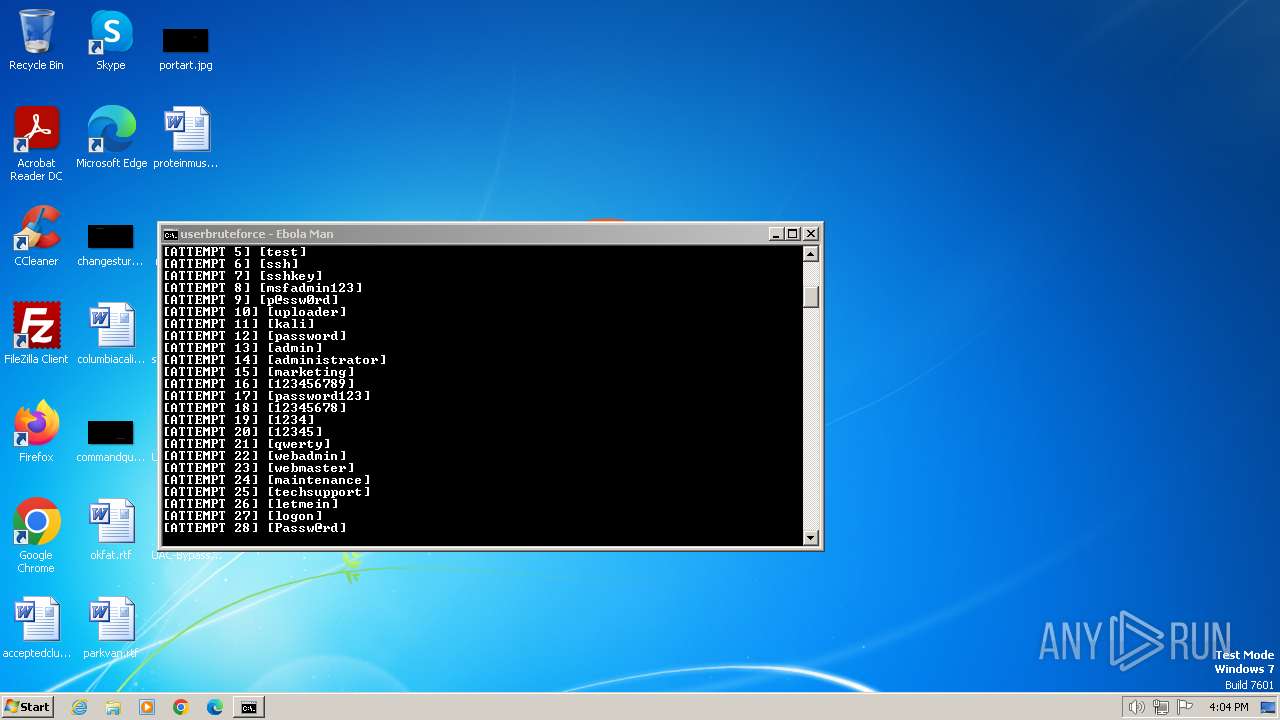
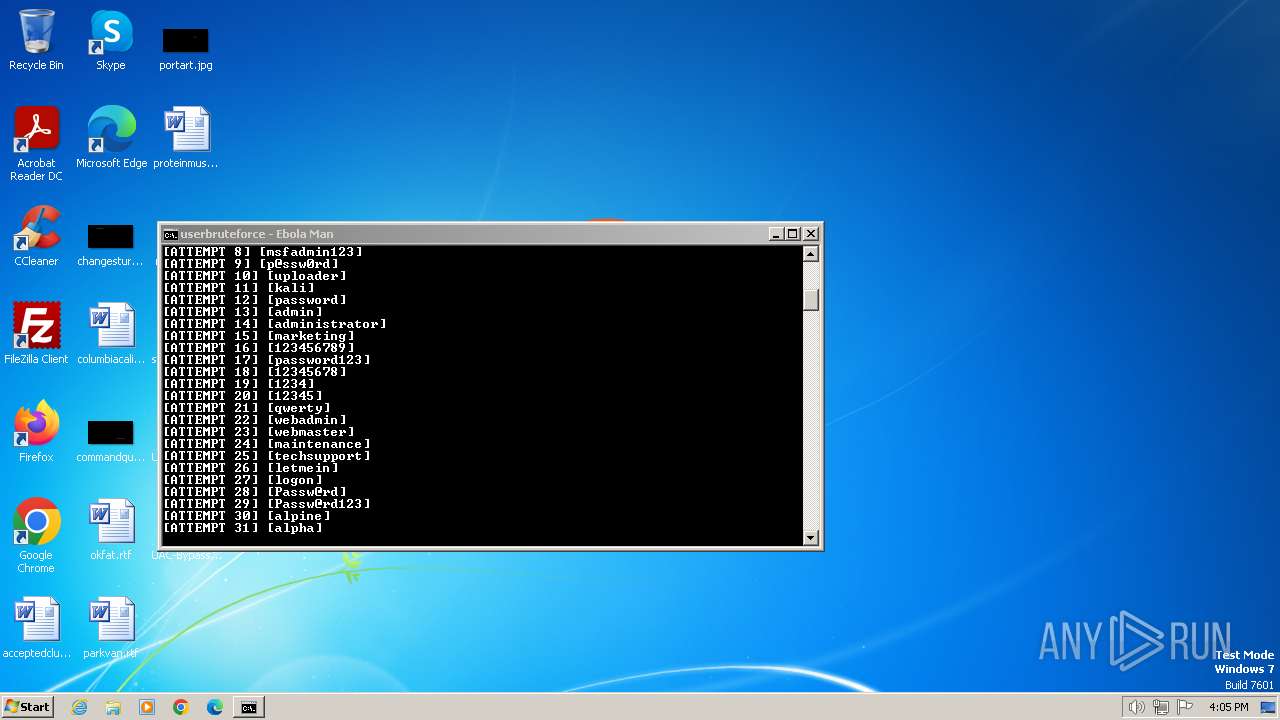
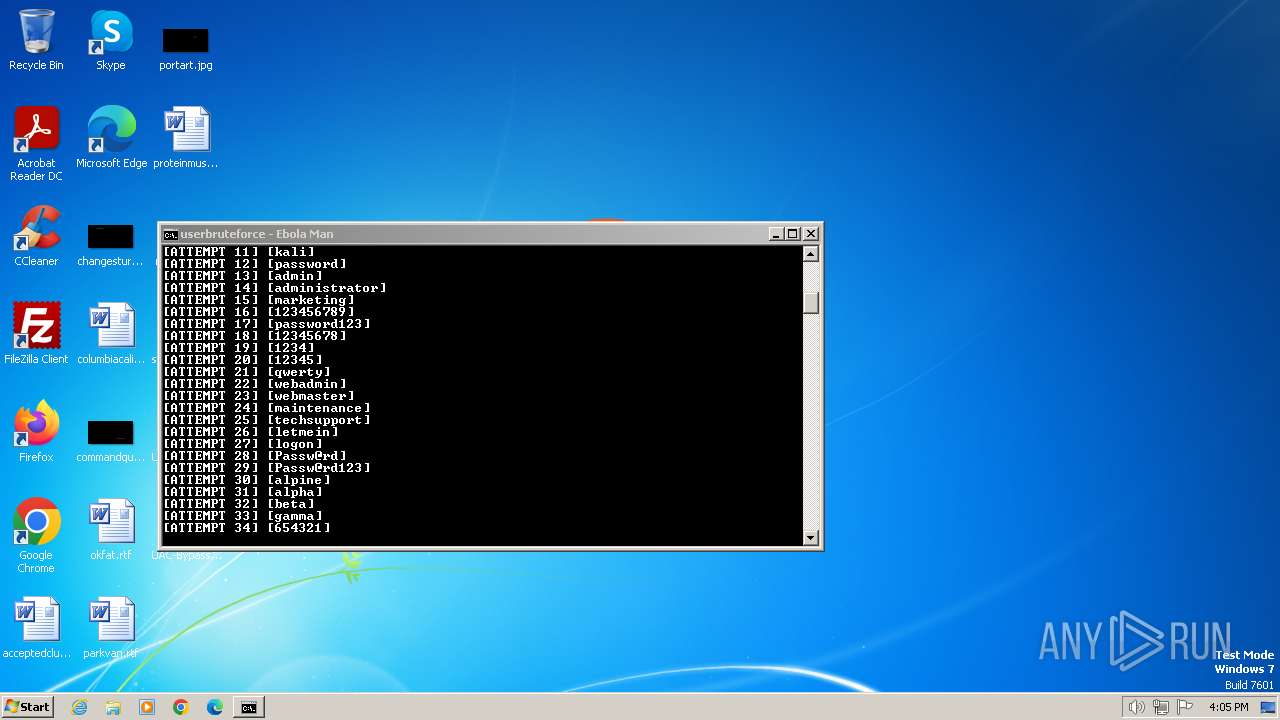
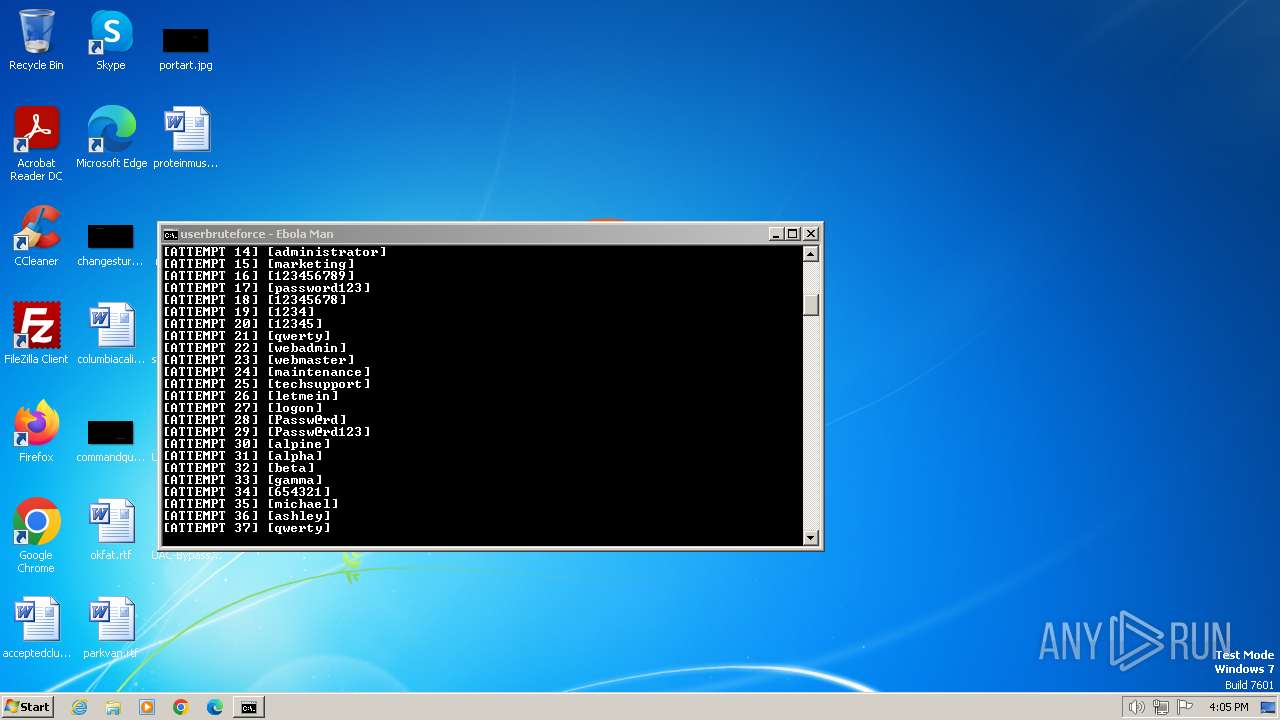
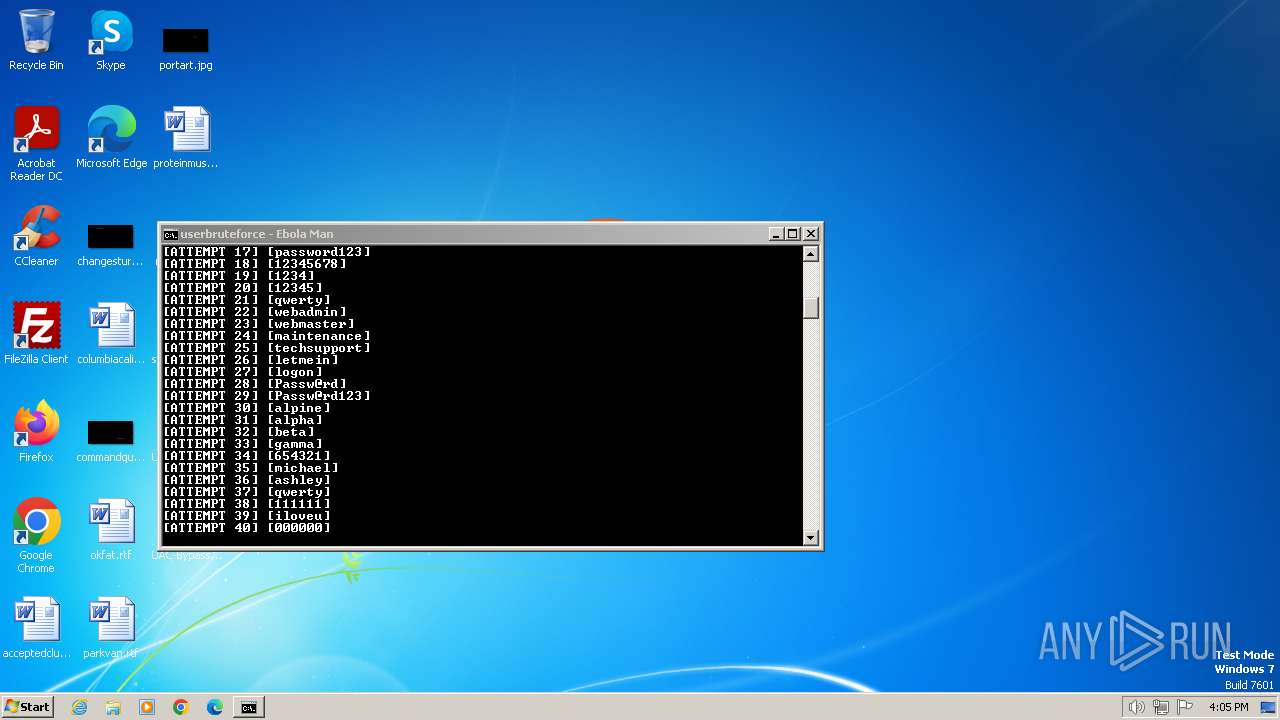
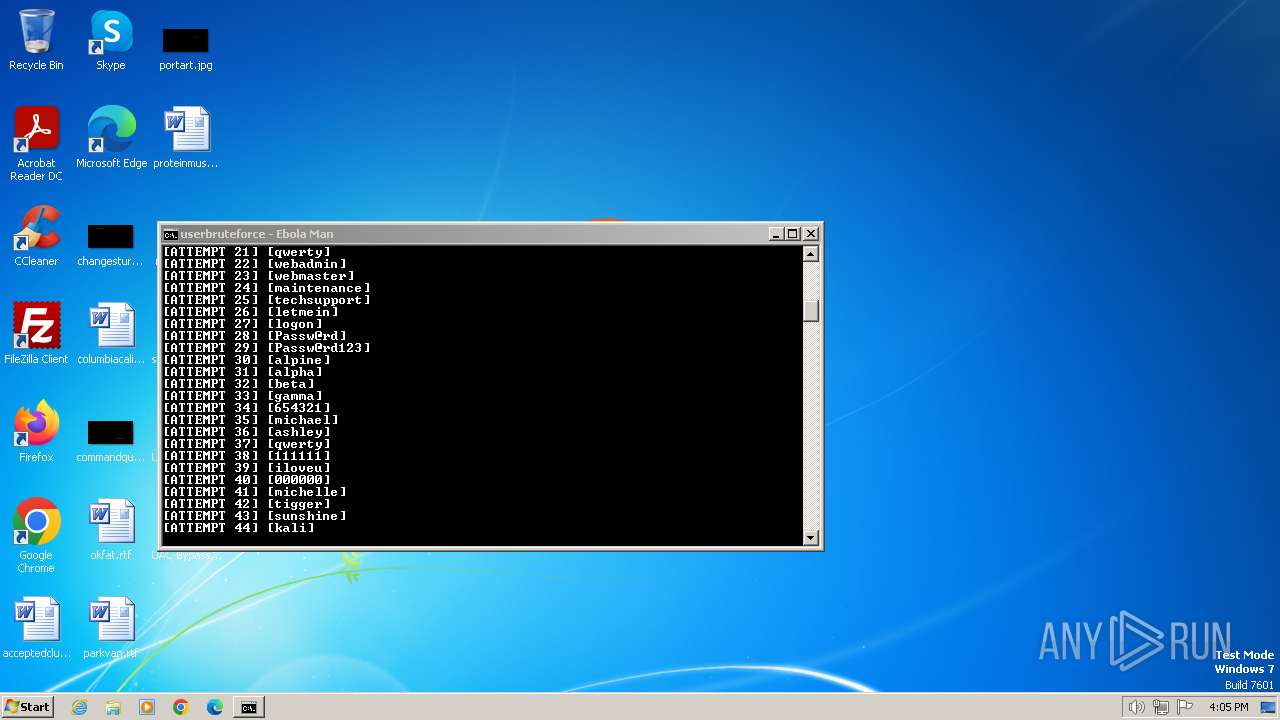
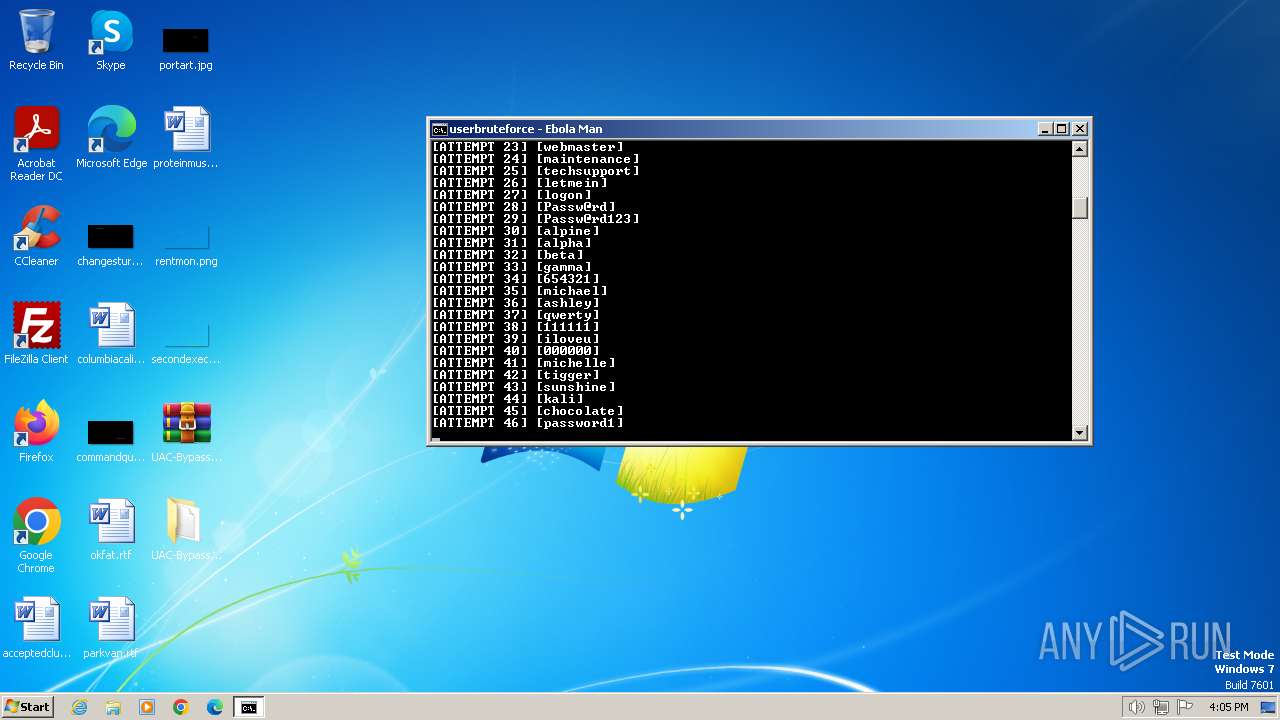
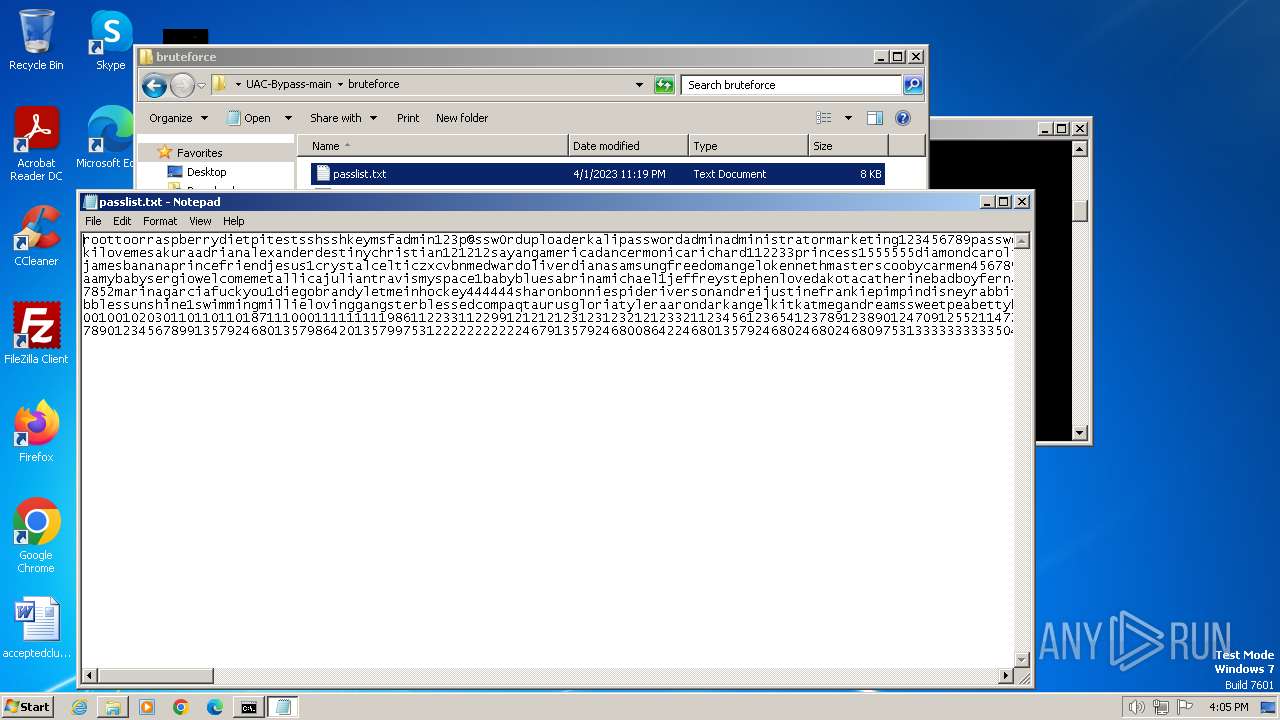
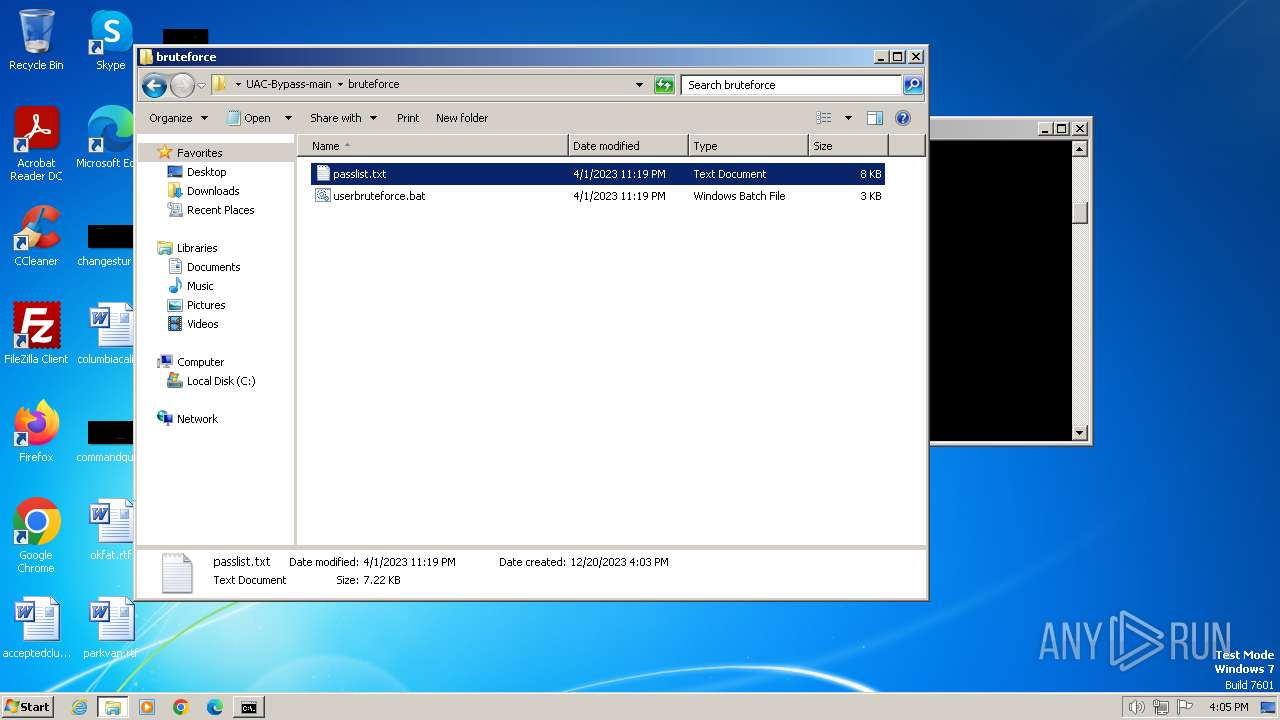
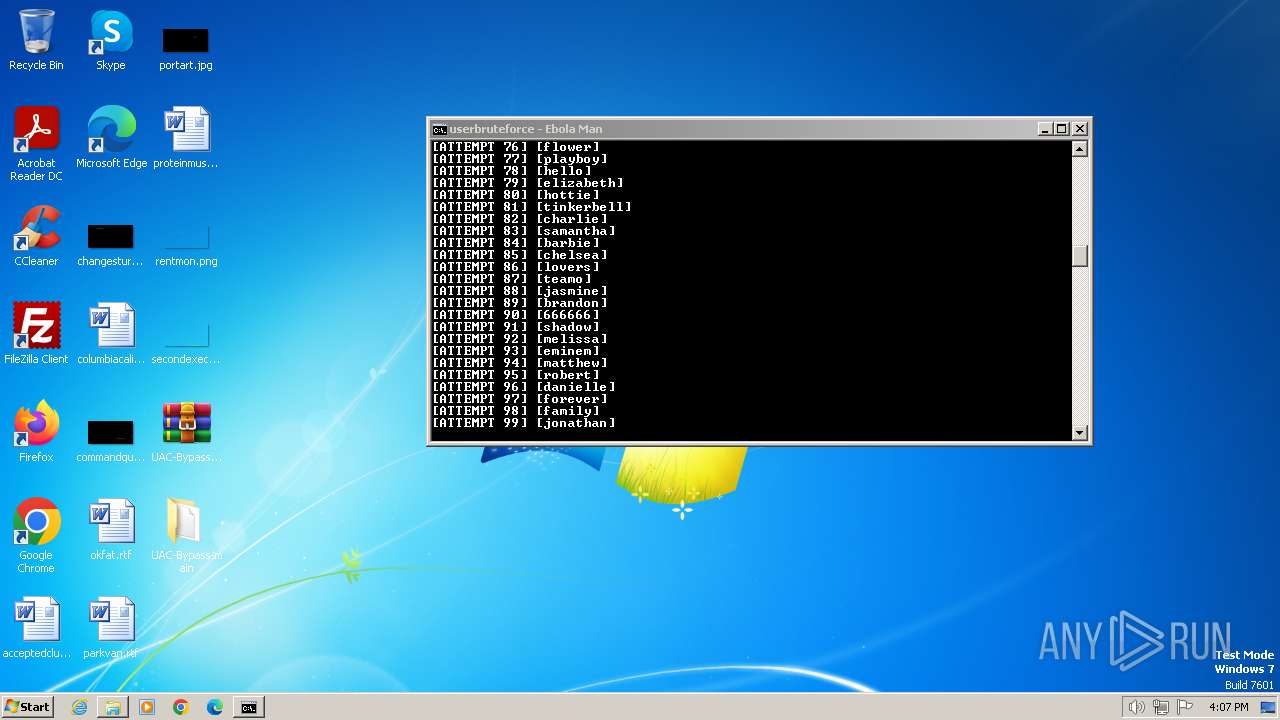
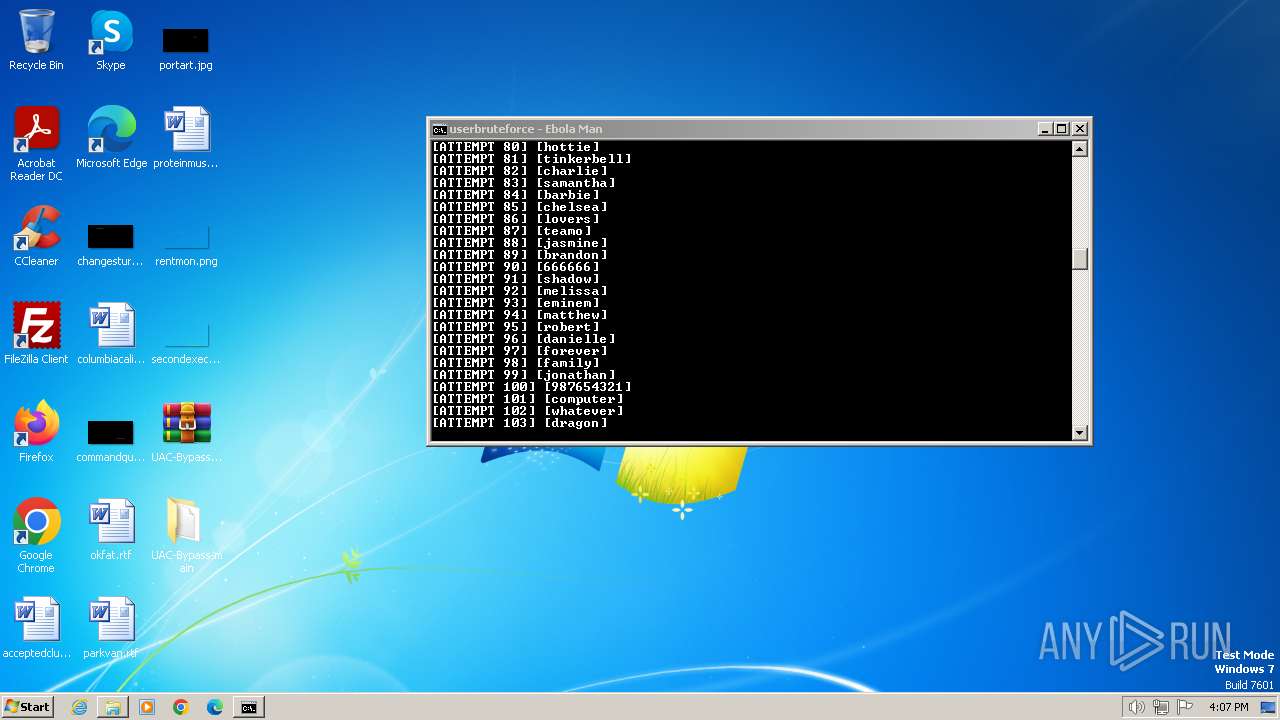
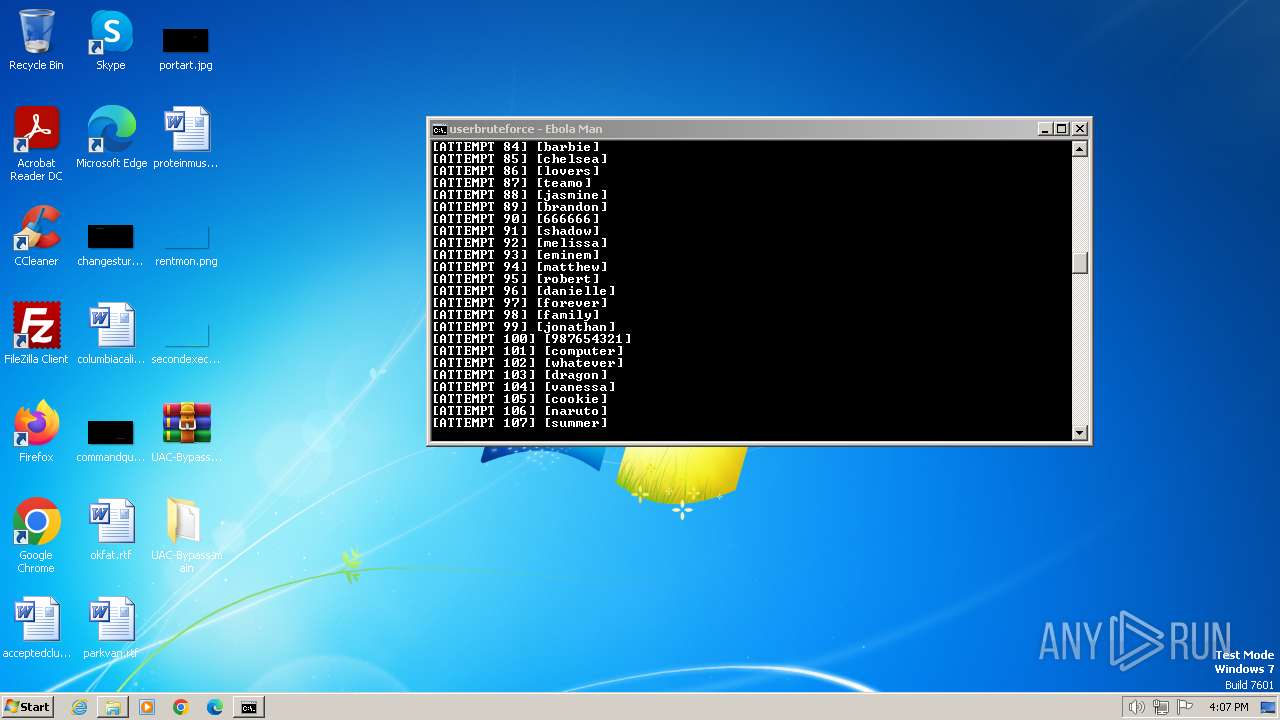
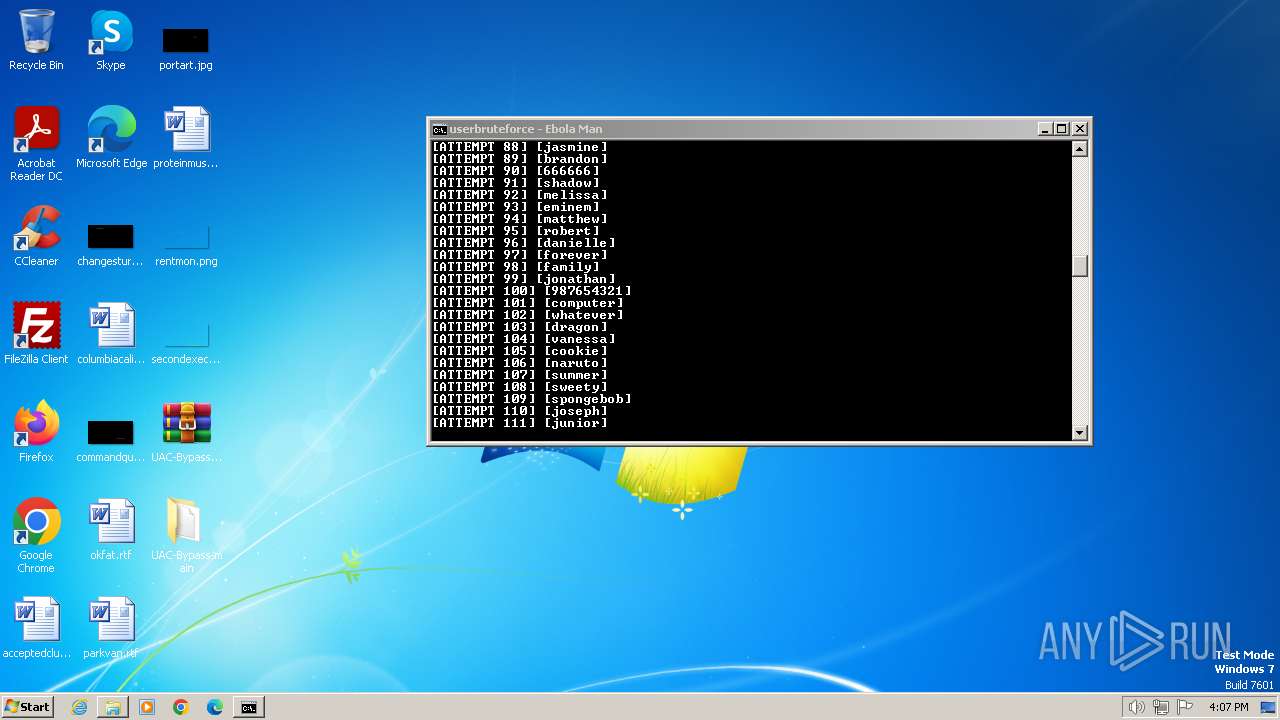
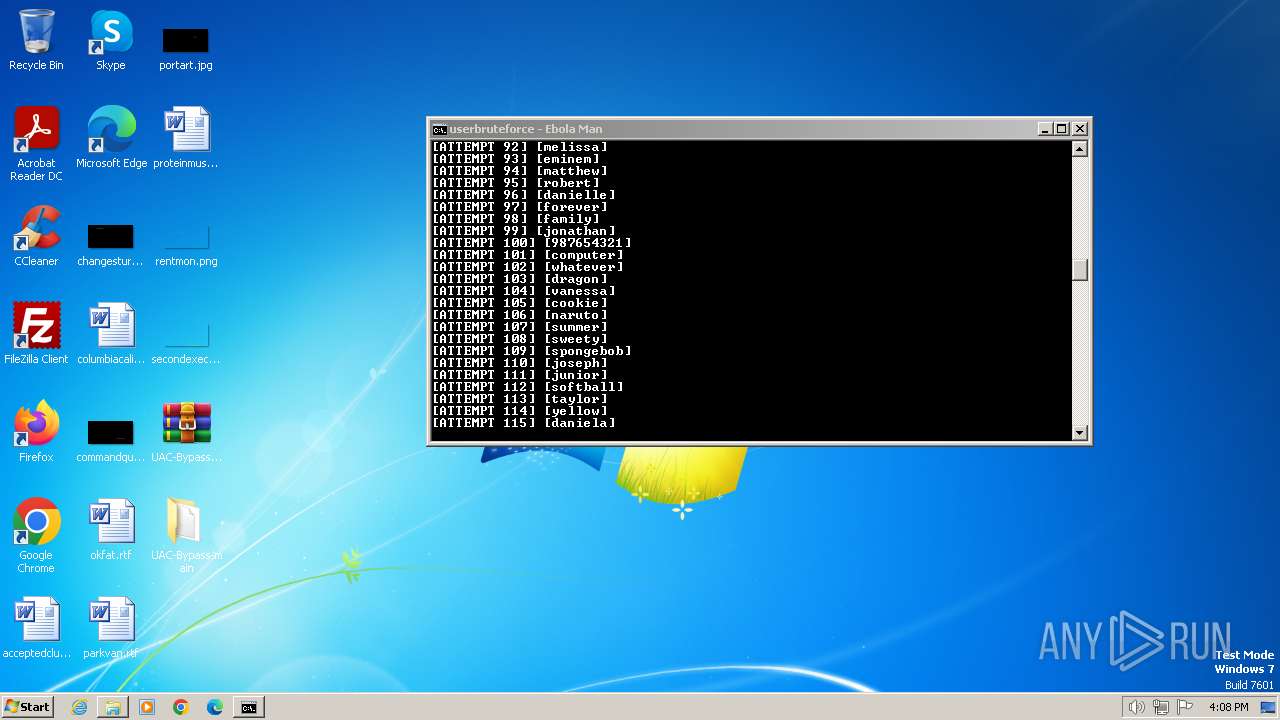
| 124 | WinRAR.exe | C:\Users\admin\Desktop\UAC-Bypass-main\bruteforce\userbruteforce.bat | text | |
MD5:F6A7786A20824DEC9890D3DBABC79853 | SHA256:C590A29C60E051E31982044314EC2E62D74236EF4DEFA8861760E45FEA6B412E | |||
| 124 | WinRAR.exe | C:\Users\admin\Desktop\UAC-Bypass-main\bruteforce\passlist.txt | text | |
MD5:FD3F87A41C506EB531A734B8631D7055 | SHA256:398BC3BFD18F8A9B859F1316F63DA42F15E40A16E182A6F6A7666B3B564C57AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |