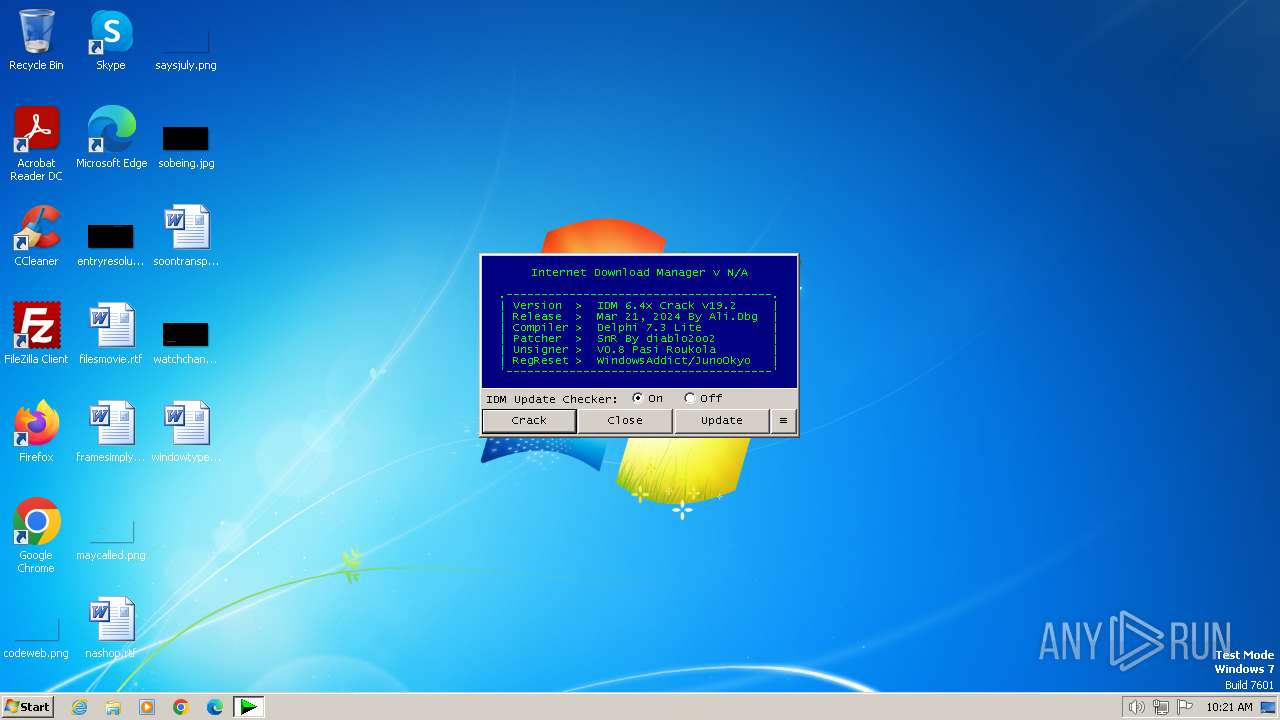
| File name: | IDM_6.4x_Crack_v19.2.exe |
| Full analysis: | https://app.any.run/tasks/272a6ac8-0acb-4aa8-b308-8382e331bda4 |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2024, 10:21:08 |
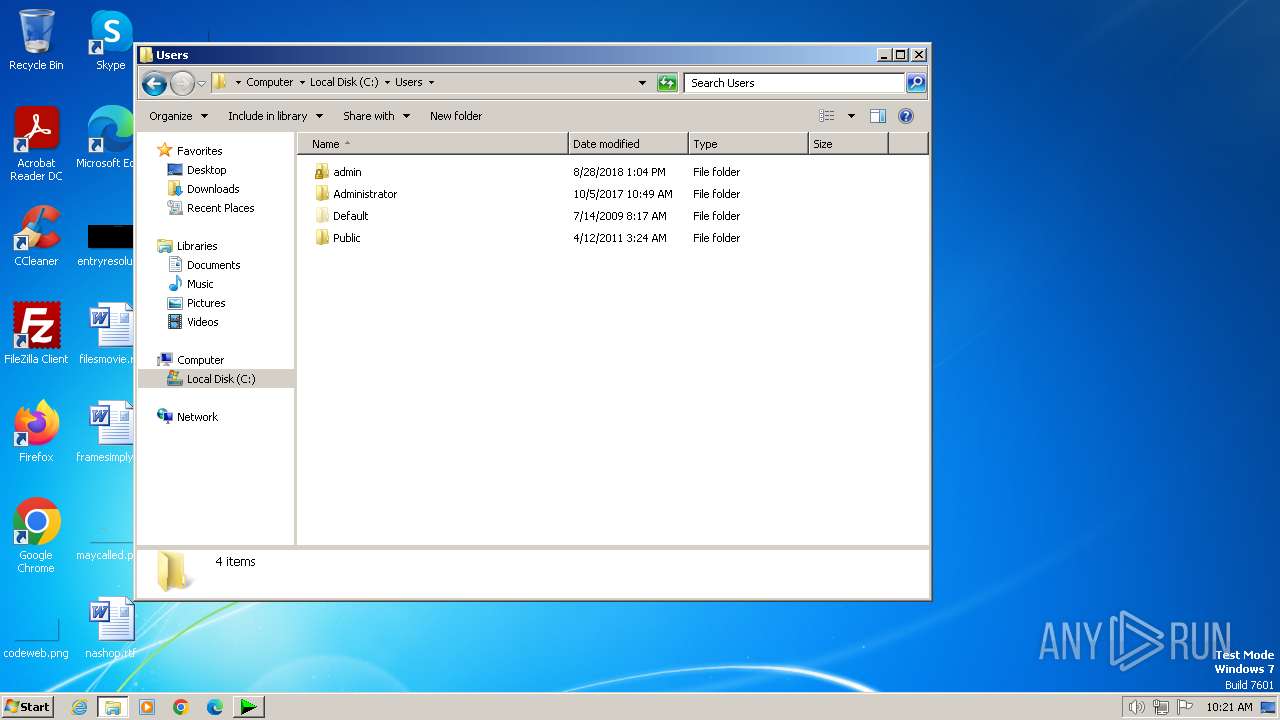
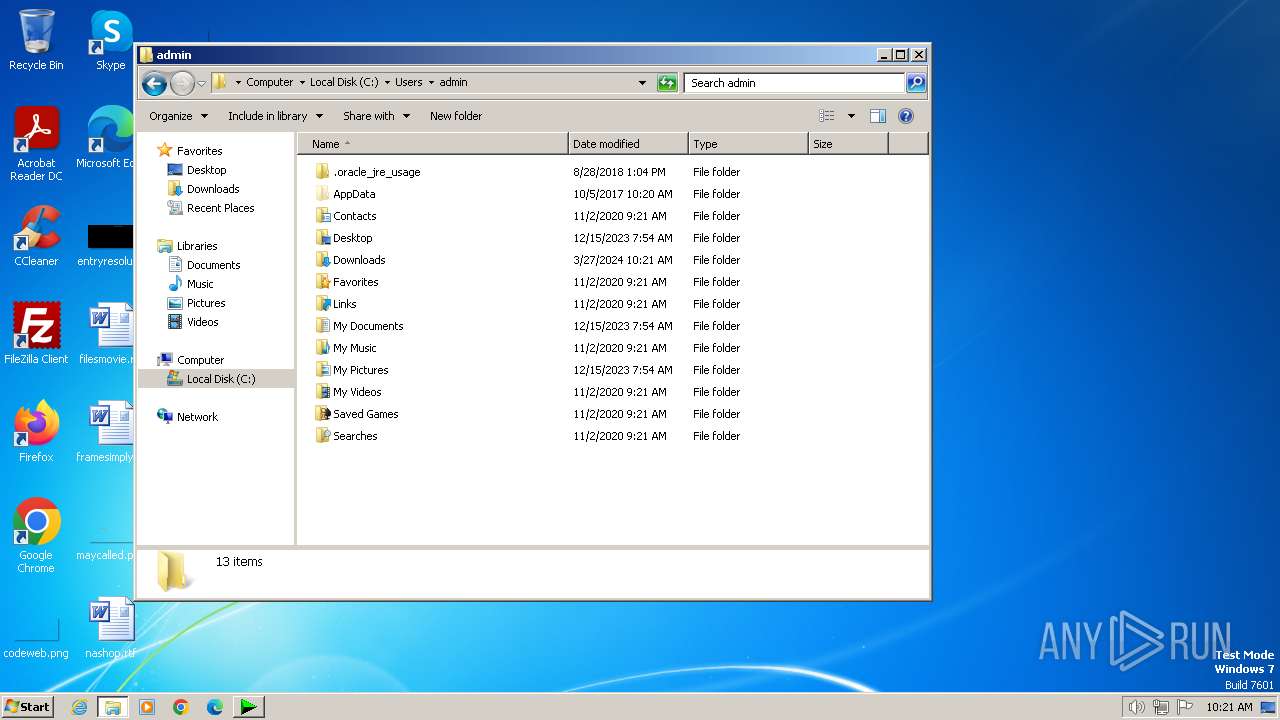
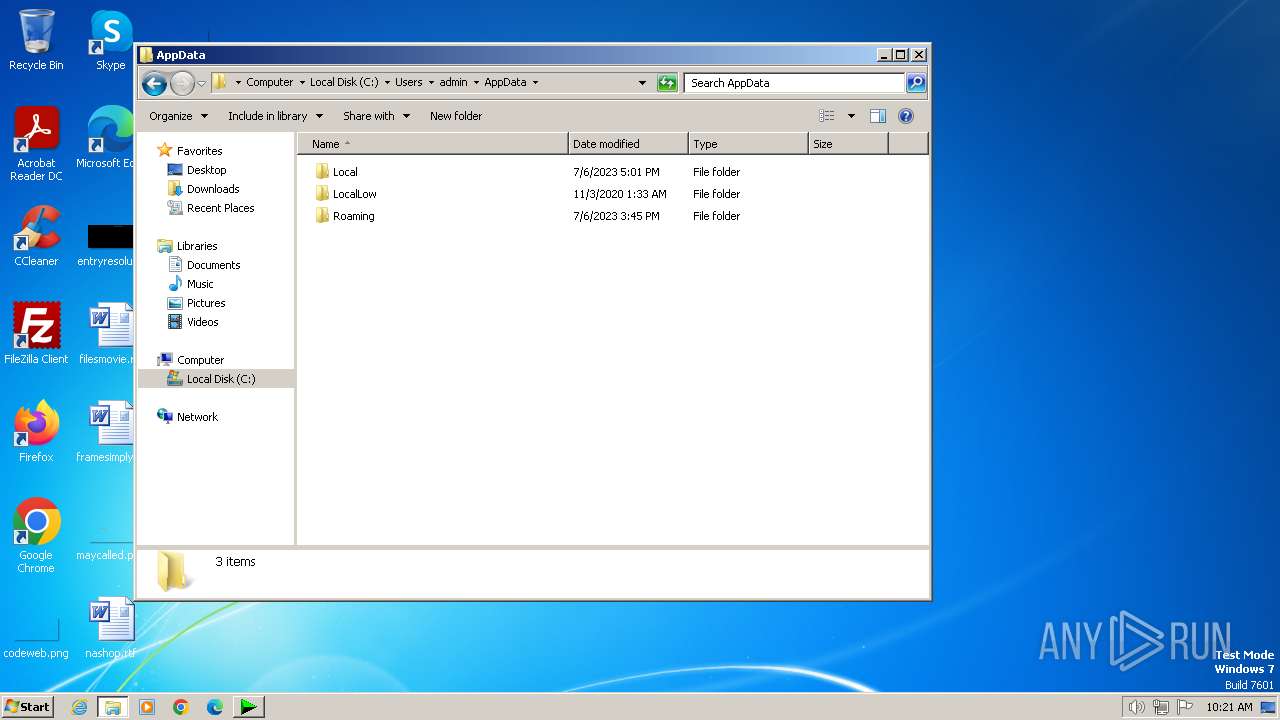
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FAA1605368BA9EC8485FF00673FB364B |
| SHA1: | 129AC7991B109627BA6683369E64975A14480BF2 |
| SHA256: | 05305D00C781F8924E6077131B47E87FA74FF88345983FEFB318547B7C1553BA |
| SSDEEP: | 768:LdrO5eFwhTrVS7dkVVpsul4Q3scN30Satlt2E1tyUxzBwPhao9oTFrqmf7jX2uzX:LdsekhMaVsul7scQIENB/VH2uzOAN |
MALICIOUS
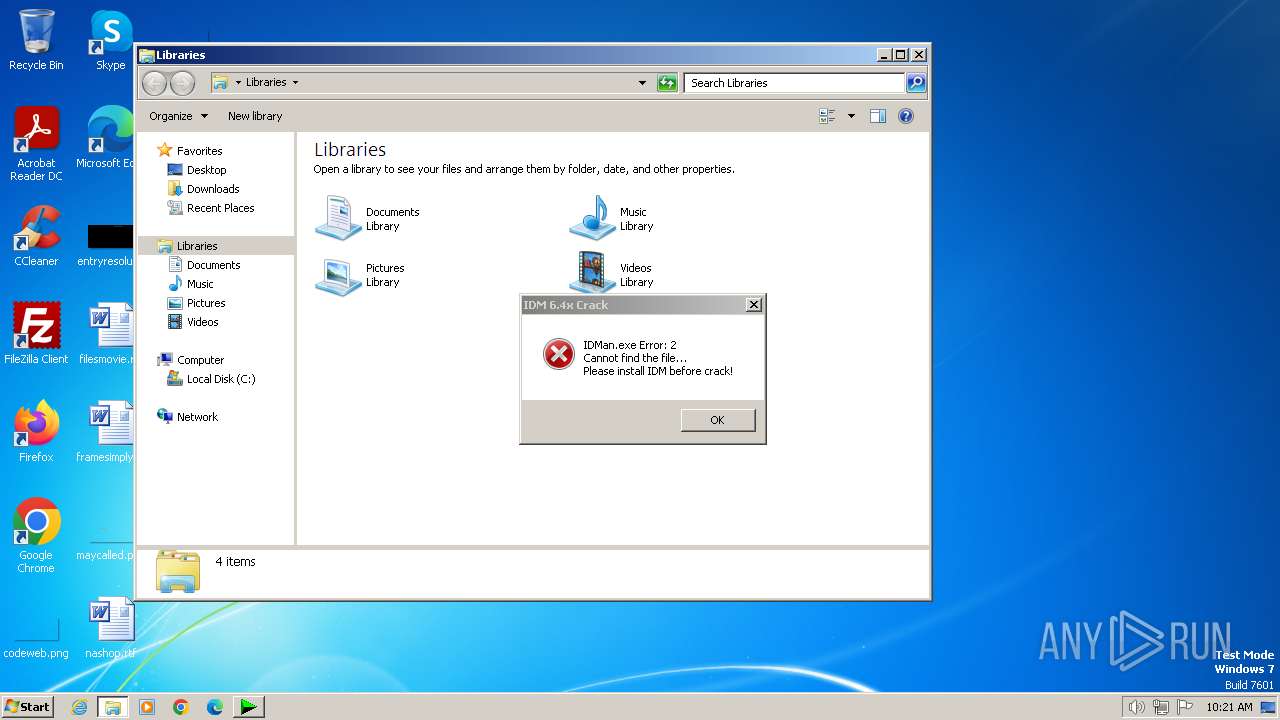
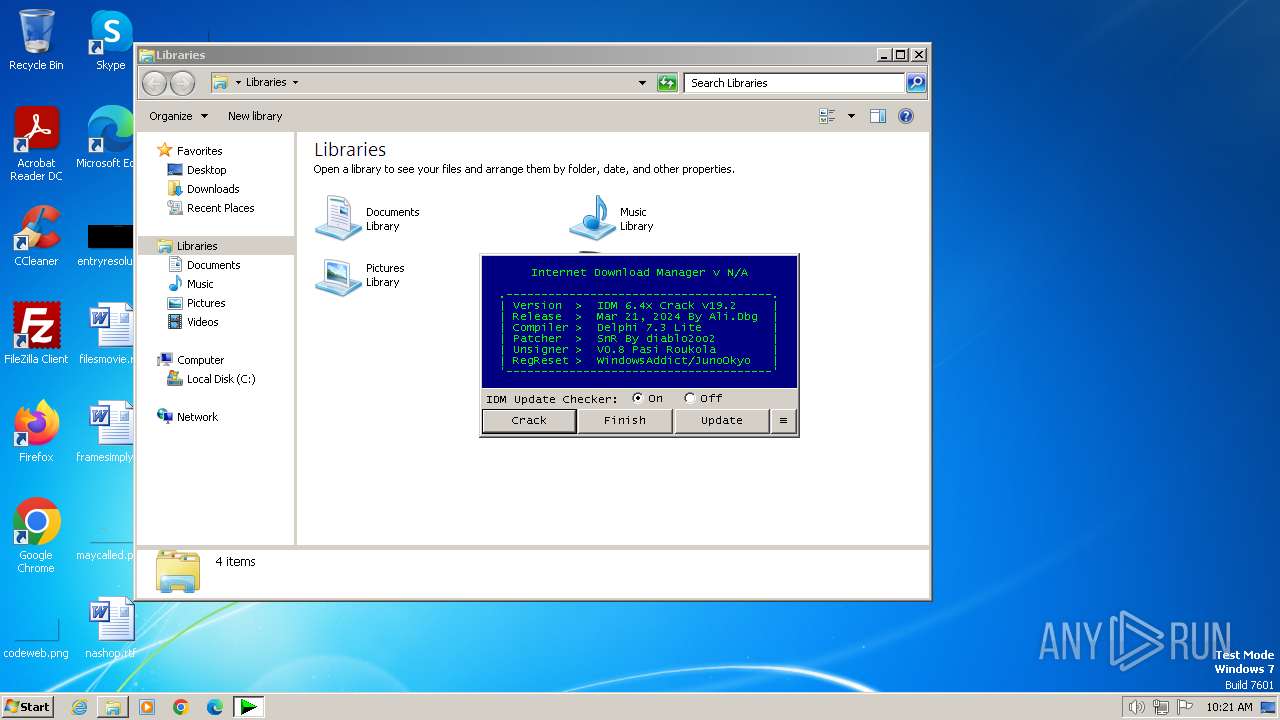
Drops the executable file immediately after the start
- IDM_6.4x_Crack_v19.2.exe (PID: 2292)
SUSPICIOUS
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v19.2.exe (PID: 2292)
- cmd.exe (PID: 1824)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v19.2.exe (PID: 2292)
- cmd.exe (PID: 1824)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v19.2.exe (PID: 2292)
- cmd.exe (PID: 1824)
- cmd.exe (PID: 448)
Application launched itself
- cmd.exe (PID: 1824)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1824)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1824)
Starts application with an unusual extension
- cmd.exe (PID: 1824)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1824)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 1584)
Hides command output
- cmd.exe (PID: 2804)
- cmd.exe (PID: 448)
INFO
Reads the computer name
- IDM_6.4x_Crack_v19.2.exe (PID: 2292)
Checks supported languages
- IDM_6.4x_Crack_v19.2.exe (PID: 2292)
- chcp.com (PID: 4092)
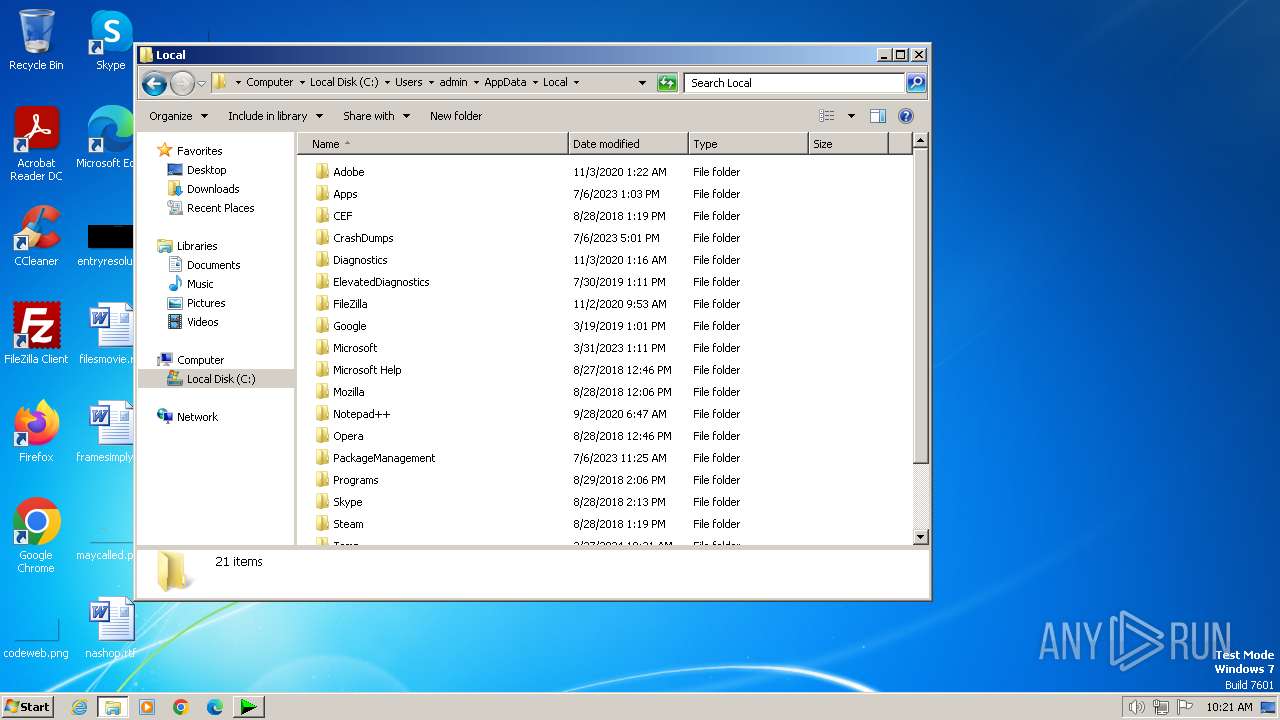
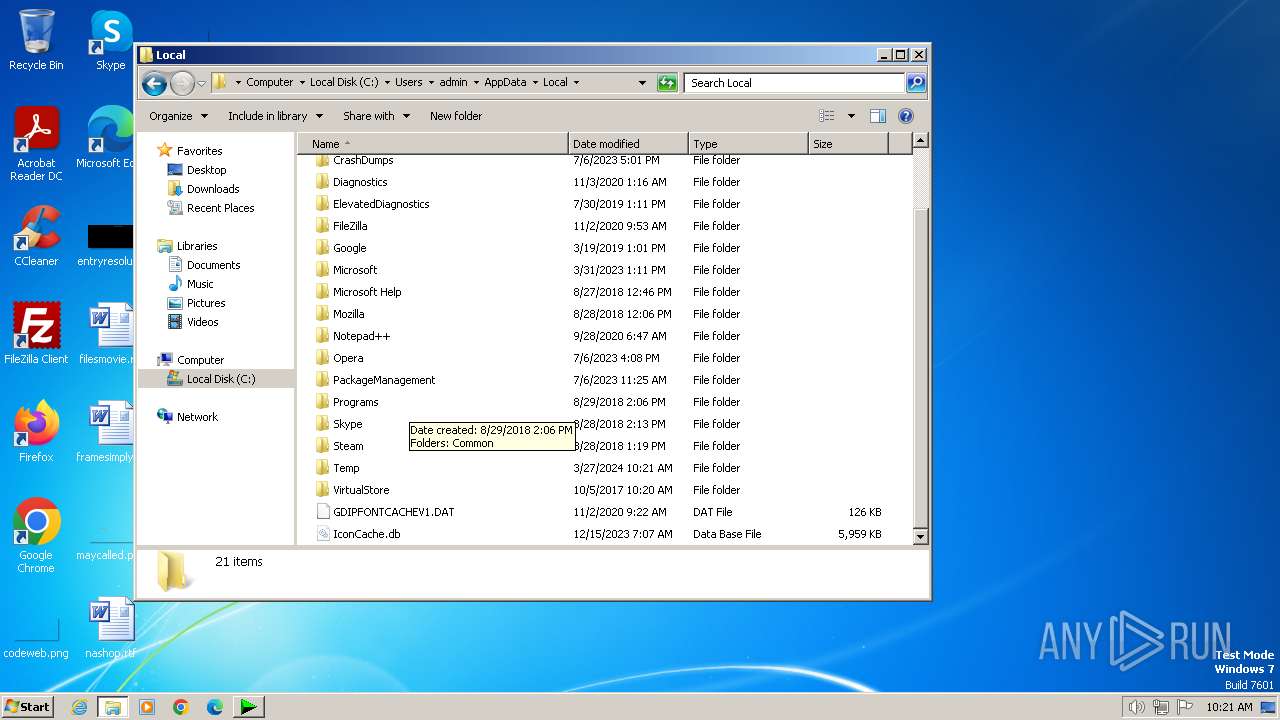
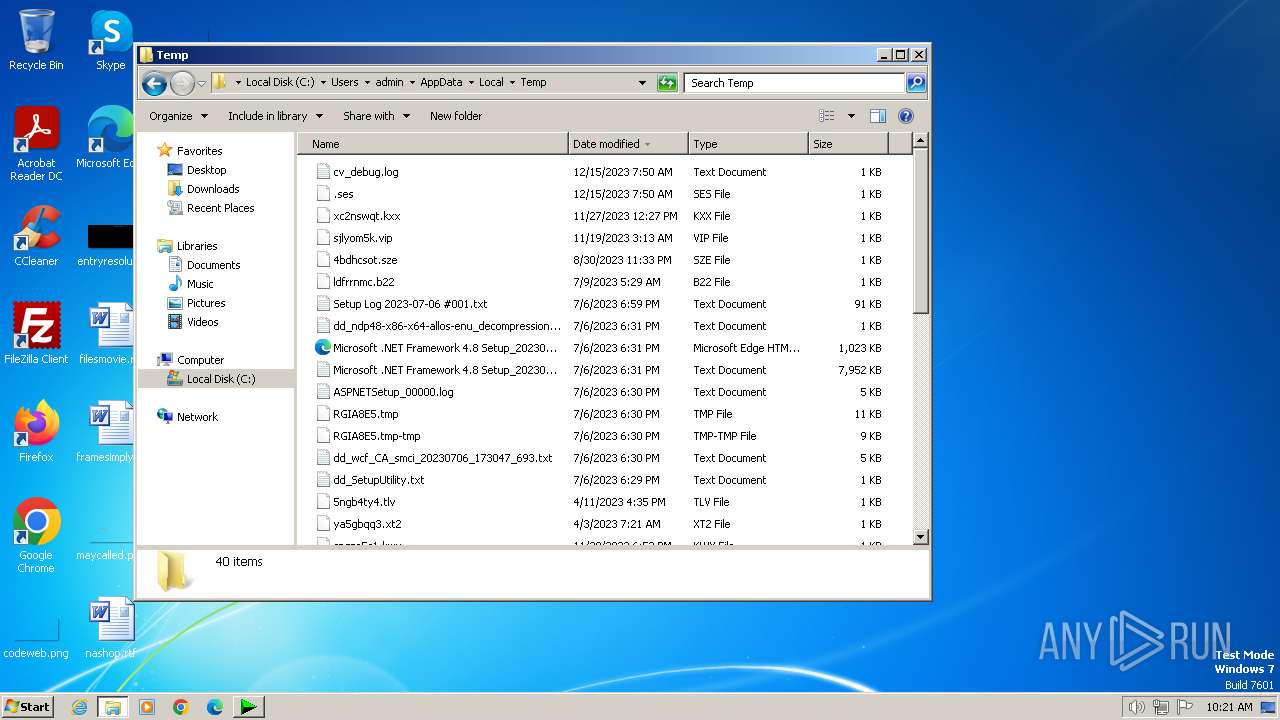
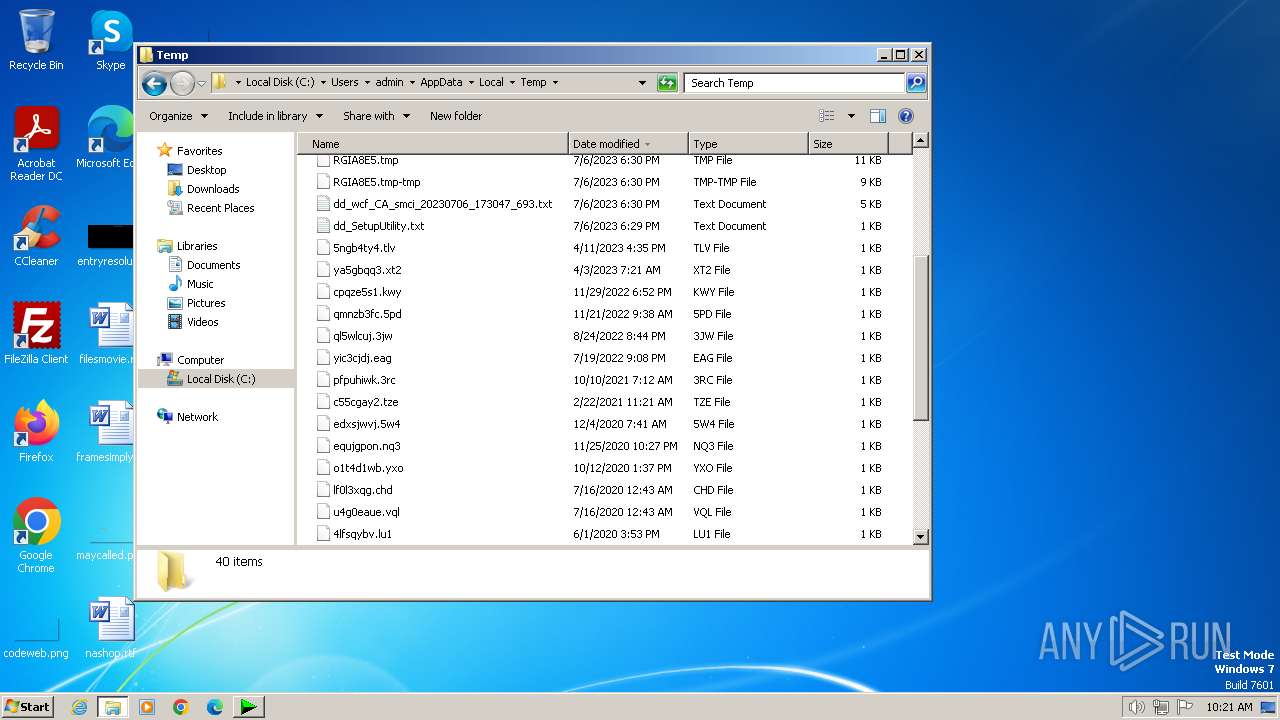
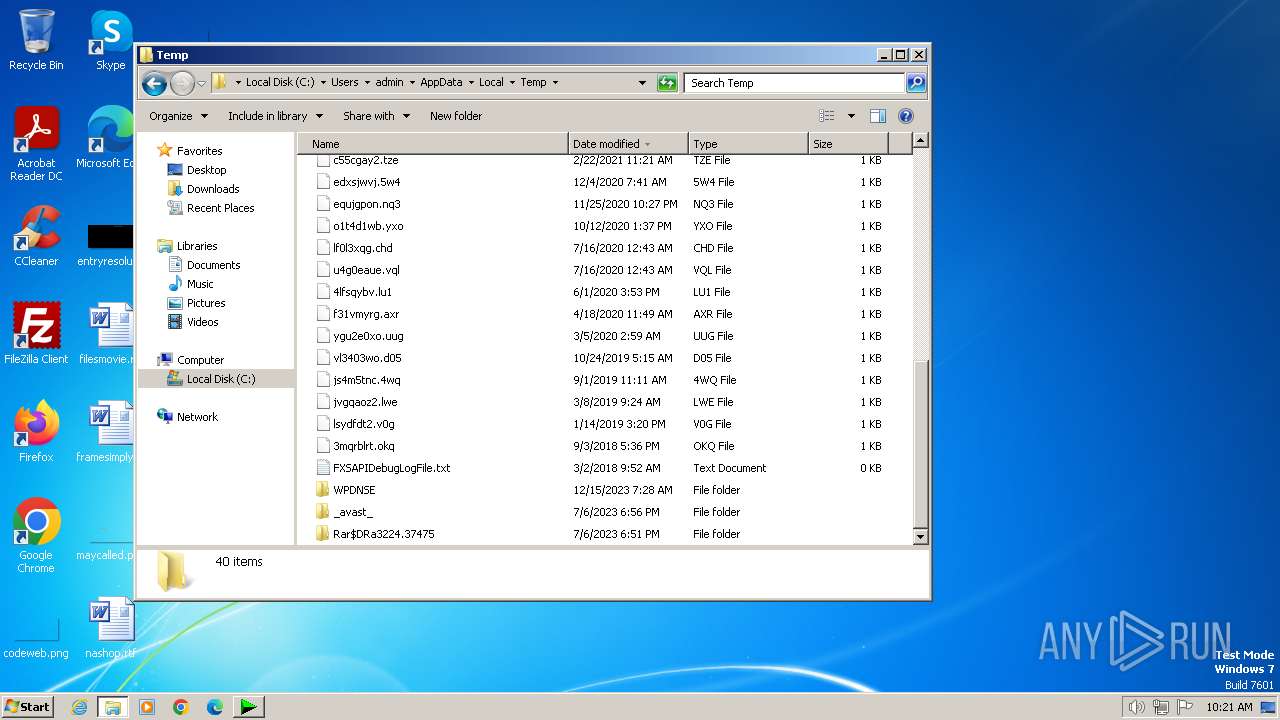
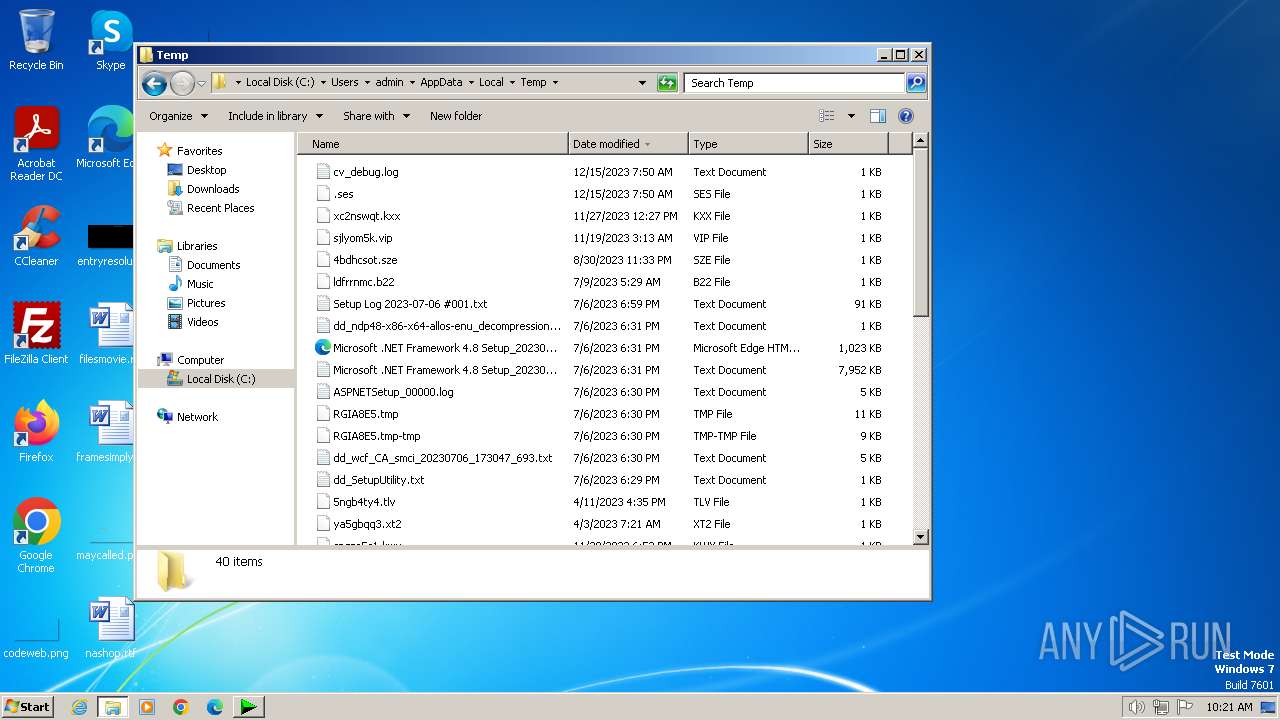
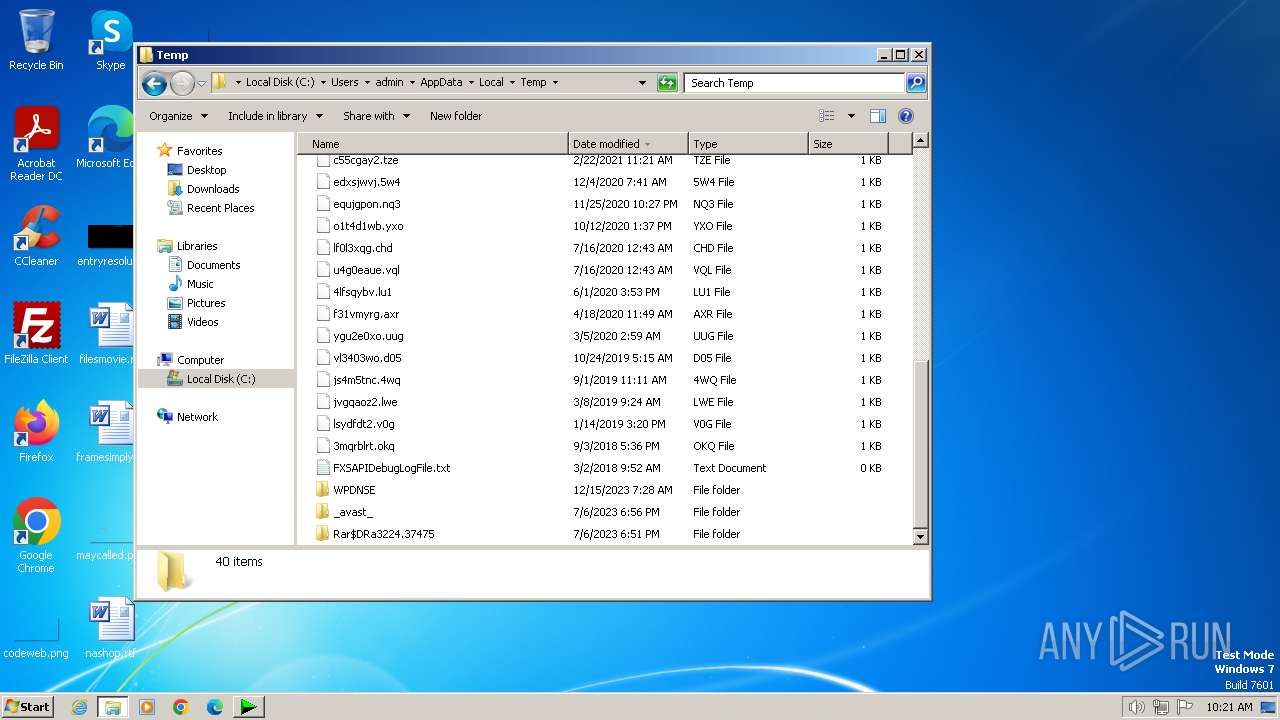
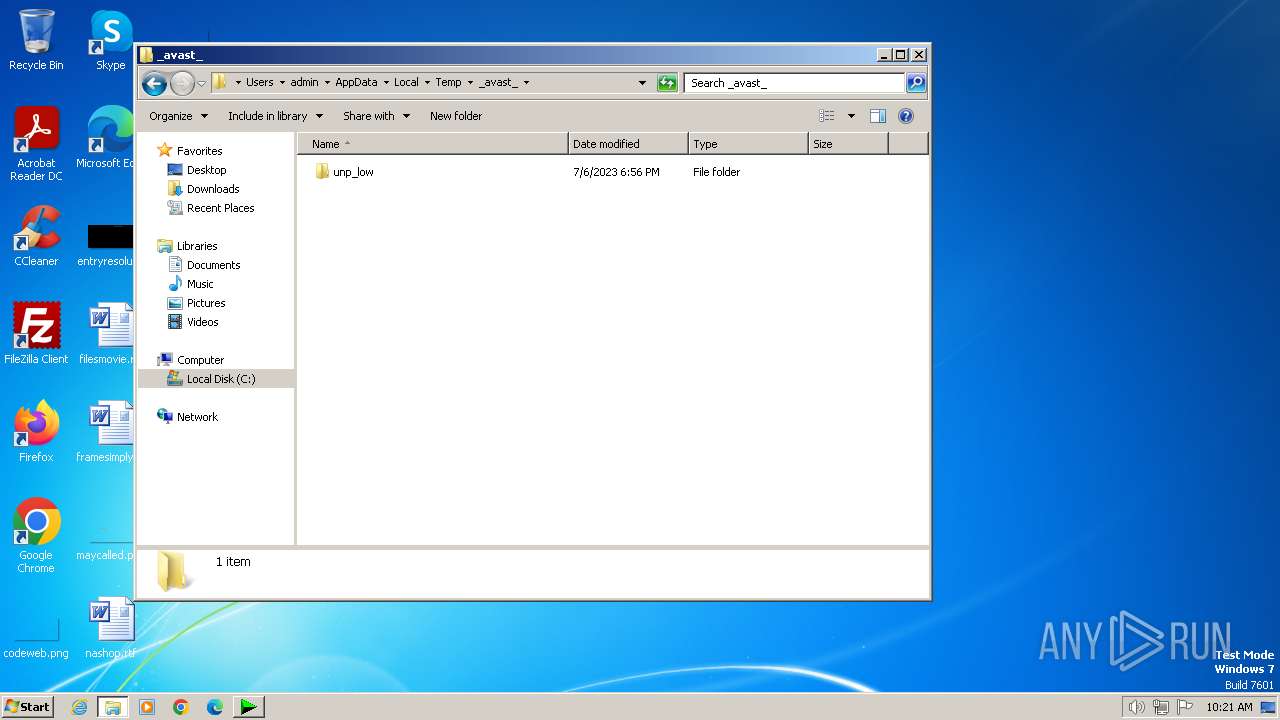
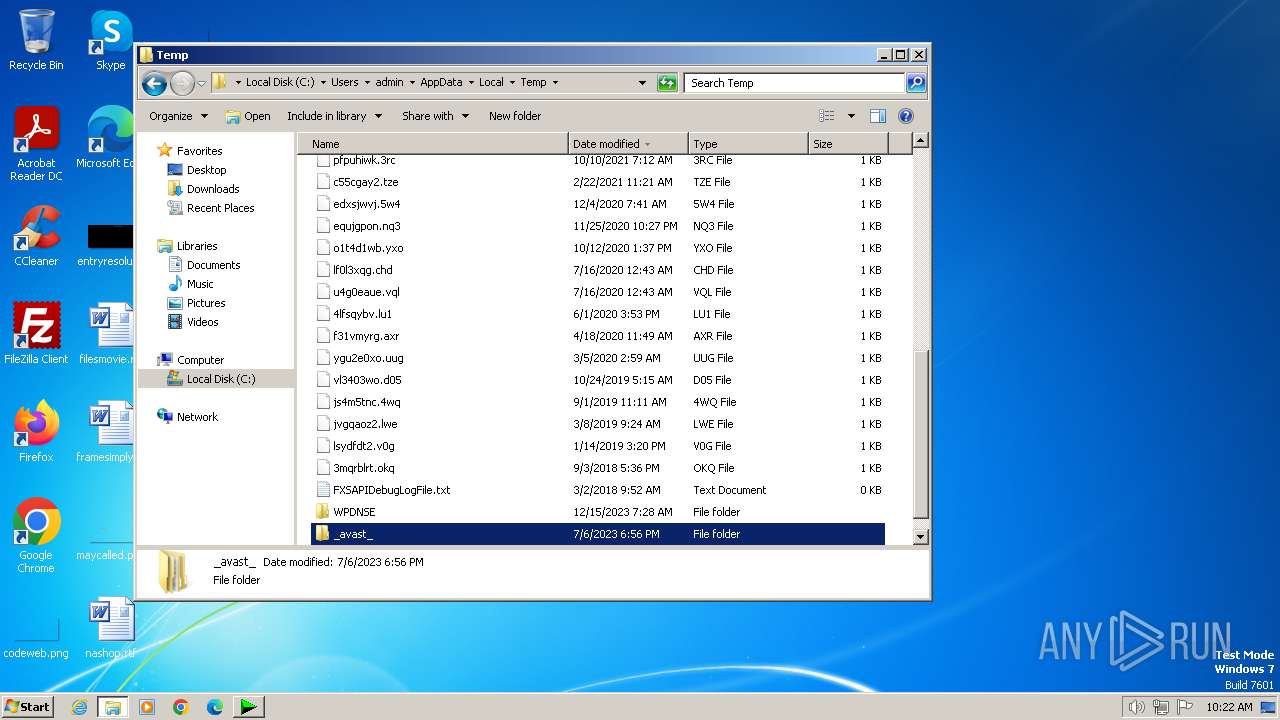
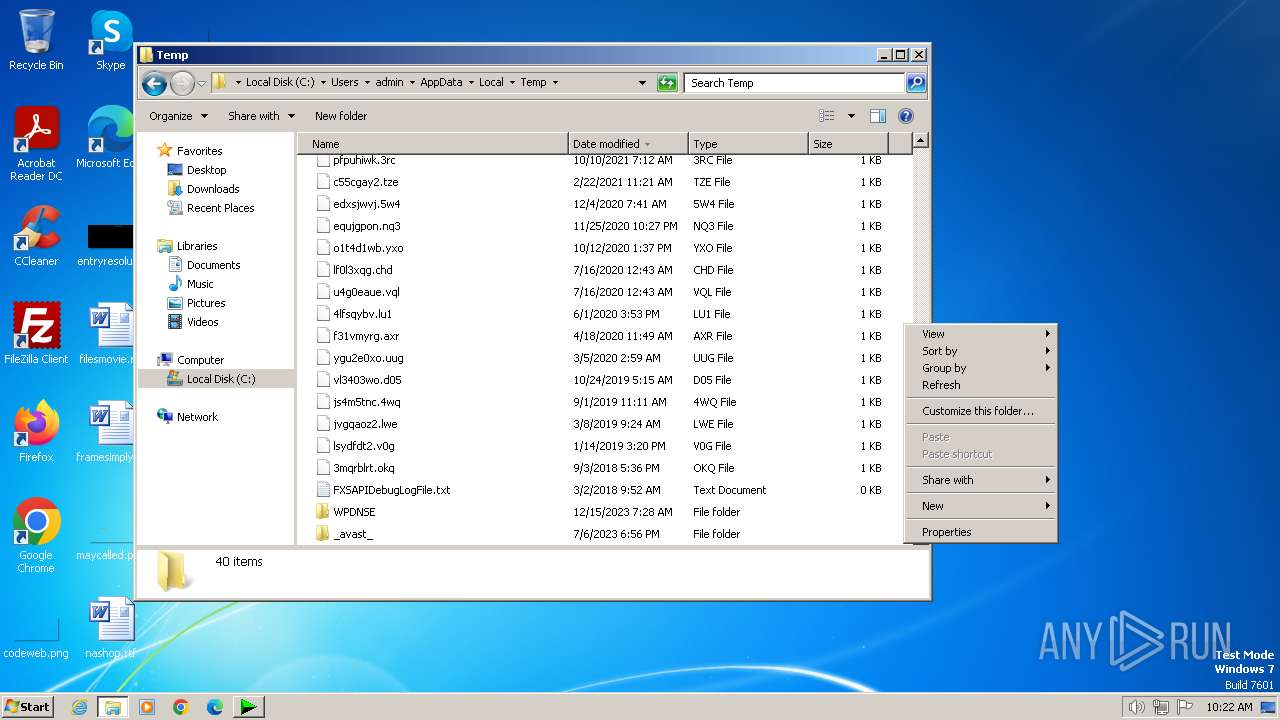
Create files in a temporary directory
- IDM_6.4x_Crack_v19.2.exe (PID: 2292)
- reg.exe (PID: 2516)
Checks operating system version
- cmd.exe (PID: 1824)
Manual execution by a user
- explorer.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 40960 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 86016 |
| EntryPoint: | 0x1f670 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
94
Monitored processes
51
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | reg query HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Classes\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | reg add HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Classes\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | C:\Windows\system32\cmd.exe /c reg query "HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software\DownloadManager" /v ExePath 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 480 | reg query "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Environment" /v PROCESSOR_ARCHITECTURE | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | REG ADD "HKCU\Software\DownloadManager" /v "nLst" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | powershell.exe "(Get-Date).ToString('yyyyMMdd-HHmmssfff')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 784 | reg query "HKCU\Software\DownloadManager" "/v" "scansk" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 840 | reg query HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | reg query "HKCU\Software\DownloadManager" "/v" "tvfrdt" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | REG ADD "HKLM\Software\WOW6432Node\Internet Download Manager" /v "AdvIntDriverEnabled2" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 040
Read events
17 001
Write events
24
Delete events
15
Modification events
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_CURRENT_USER\Software\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (2292) IDM_6.4x_Crack_v19.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | IDM_6.4x_Crack_v19.2.exe | C:\Users\admin\AppData\Local\Temp\IDMRegClean.reg | text | |
MD5:— | SHA256:— | |||
| 2292 | IDM_6.4x_Crack_v19.2.exe | C:\Users\admin\AppData\Local\Temp\BATCLEN.bat | text | |
MD5:— | SHA256:— | |||
| 3516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kas2ddgz.1np.ps1 | binary | |
MD5:— | SHA256:— | |||
| 3516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\21ixmdfm.2bs.psm1 | binary | |
MD5:— | SHA256:— | |||
| 3516 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:— | SHA256:— | |||
| 3400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jwudgcqi.j3g.ps1 | binary | |
MD5:— | SHA256:— | |||
| 3400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wwnk21th.wgq.psm1 | binary | |
MD5:— | SHA256:— | |||
| 2780 | powershell.exe | C:\Users\admin\AppData\Local\Temp\feh5cf1o.glv.ps1 | binary | |
MD5:— | SHA256:— | |||
| 2780 | powershell.exe | C:\Users\admin\AppData\Local\Temp\nuk3qabb.an2.psm1 | binary | |
MD5:— | SHA256:— | |||
| 764 | powershell.exe | C:\Users\admin\AppData\Local\Temp\xhcisqhk.iot.ps1 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |