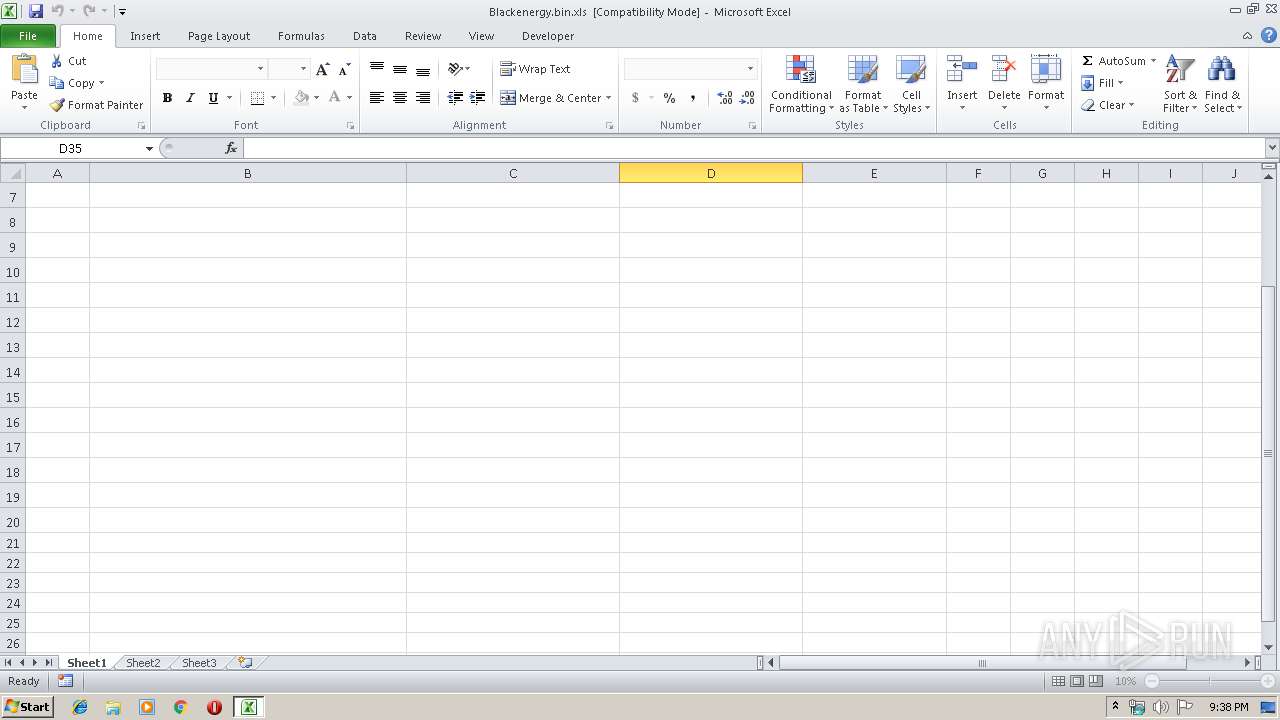
| File name: | Blackenergy.bin |
| Full analysis: | https://app.any.run/tasks/9cc3989b-ddb2-4902-804f-473cd3c97b20 |
| Verdict: | Malicious activity |
| Analysis date: | November 28, 2019, 21:37:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
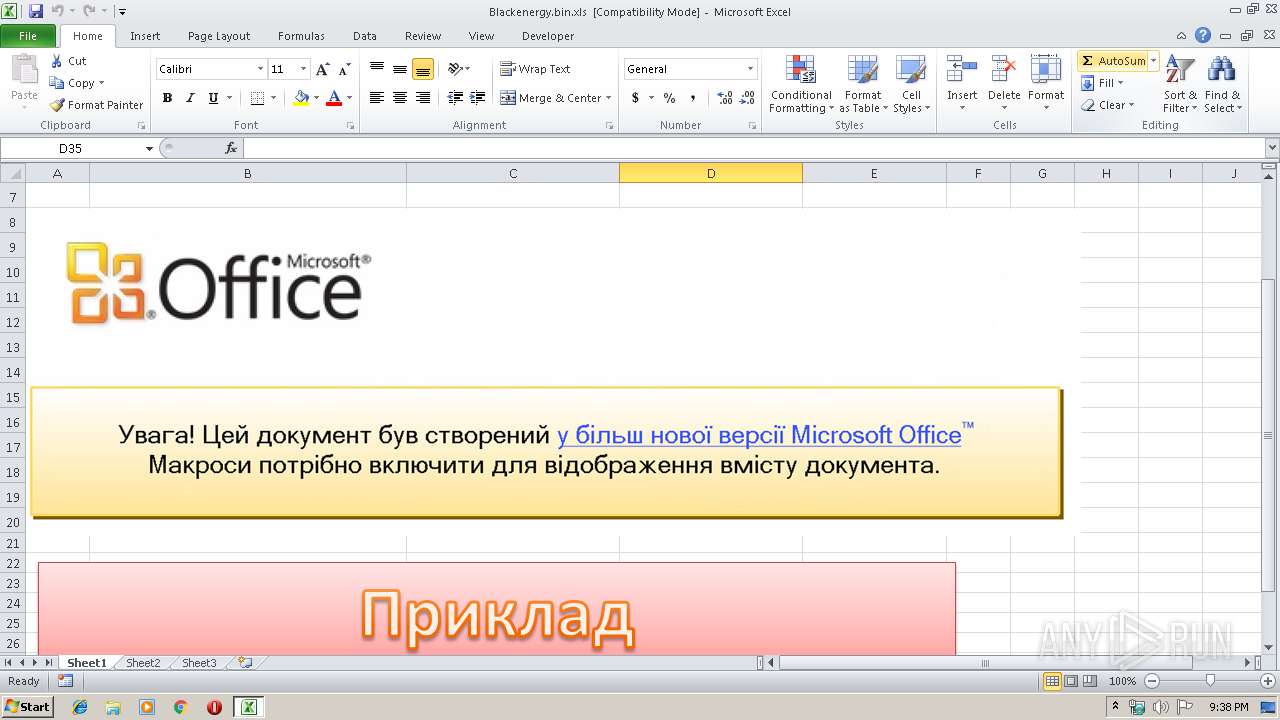
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Author: user1, Last Saved By: LSW, Name of Creating Application: Microsoft Excel, Create Time/Date: Wed Feb 4 06:35:08 2015, Last Saved Time/Date: Wed Mar 18 06:41:04 2015, Security: 0 |
| MD5: | 97B7577D13CF5E3BF39CBE6D3F0A7732 |
| SHA1: | AA67CA4FB712374F5301D1D2BAB0AC66107A4DF1 |
| SHA256: | 052EBC9A518E5AE02BBD1BD3A5A86C3560AEFC9313C18D81F6670C3430F1D4D4 |
| SSDEEP: | 12288:WfghhODBvtntqnRwEtjaeIPsmx5Lgc31DH:W43ODBvtntqnRwEtOeIEmDDj |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2108)
Writes to a start menu file
- vba_macro.exe (PID: 2280)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1980)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3200)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2108)
Application was dropped or rewritten from another process
- vba_macro.exe (PID: 2280)
SUSPICIOUS
Creates files in the user directory
- vba_macro.exe (PID: 2280)
Executable content was dropped or overwritten
- vba_macro.exe (PID: 2280)
Uses RUNDLL32.EXE to load library
- vba_macro.exe (PID: 2280)
Starts CMD.EXE for commands execution
- vba_macro.exe (PID: 2280)
Modifies the phishing filter of IE
- rundll32.exe (PID: 3200)
Executed via COM
- iexplore.exe (PID: 2212)
Connects to server without host name
- iexplore.exe (PID: 2744)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2108)
Changes internet zones settings
- iexplore.exe (PID: 2212)
Reads Internet Cache Settings
- iexplore.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | user1 |
|---|---|
| LastModifiedBy: | LSW |
| Software: | Microsoft Excel |
| CreateDate: | 2015:02:04 06:35:08 |
| ModifyDate: | 2015:03:18 06:41:04 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
41
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1980 | /s /c "for /L %i in (1,1,100) do (del /F "C:\Users\admin\AppData\Local\Temp\VBA_MA~1.EXE" & ping localhost -n 2 & if not exist "C:\Users\admin\AppData\Local\Temp\VBA_MA~1.EXE" Exit 1)" | C:\Windows\system32\cmd.exe | — | vba_macro.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2280 | C:\Users\admin\AppData\Local\Temp\vba_macro.exe | C:\Users\admin\AppData\Local\Temp\vba_macro.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft IME Exit code: 0 Version: 8.1.4202.0 Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2212 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3200 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\FONTCACHE.DAT",#1 | C:\Windows\System32\rundll32.exe | — | vba_macro.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3448 | ping localhost -n 2 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 489
Read events
1 161
Write events
317
Delete events
11
Modification events
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | a&f |
Value: 612666003C080000010000000000000000000000 | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2108) EXCEL.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1333526553 | |||
Executable files
2
Suspicious files
0
Text files
5
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRBA61.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2280 | vba_macro.exe | C:\Users\admin\AppData\Local\FONTCACHE.DAT | executable | |
MD5:CDFB4CDA9144D01FB26B5449F9D189FF | SHA256:F5785842682BC49A69B2CBC3FDED56B8B4A73C8FD93E35860ECD1B9A88B9D3D8 | |||
| 2744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFJUTN4N\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2280 | vba_macro.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\{4040CF00-1B3E-486A-B407-FA14C56B6FC0}.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2108 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\vba_macro.exe | executable | |
MD5:ABEAB18EBAE2C3E445699D256D5F5FB1 | SHA256:07E726B21E27EEFB2B2887945AA8BDEC116B09DBD4E1A54E1C137AE8C7693660 | |||
| 2744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\840EC59H\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2744 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\NULXOBCU\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2744 | iexplore.exe | POST | — | 5.149.254.114:80 | http://5.149.254.114/Microsoft/Update/KC074913.php | NL | — | — | malicious |
2212 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2212 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2744 | iexplore.exe | 5.149.254.114:80 | — | HZ Hosting Ltd | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |