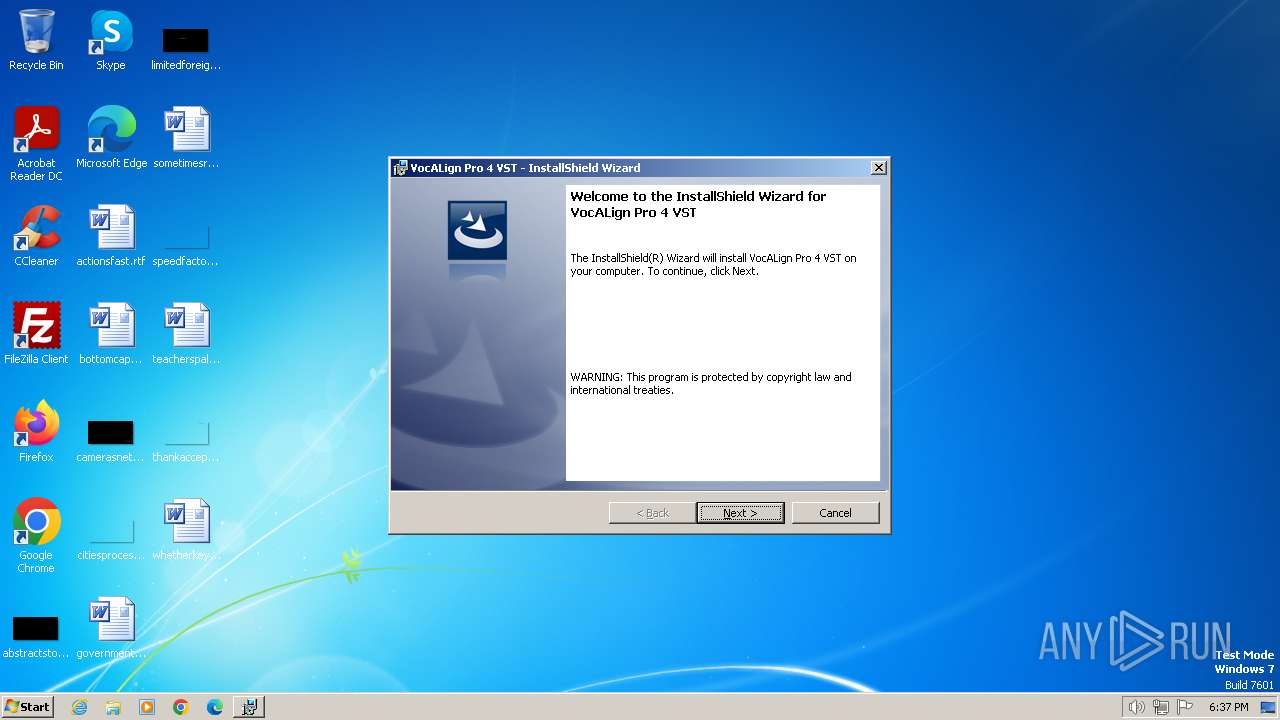
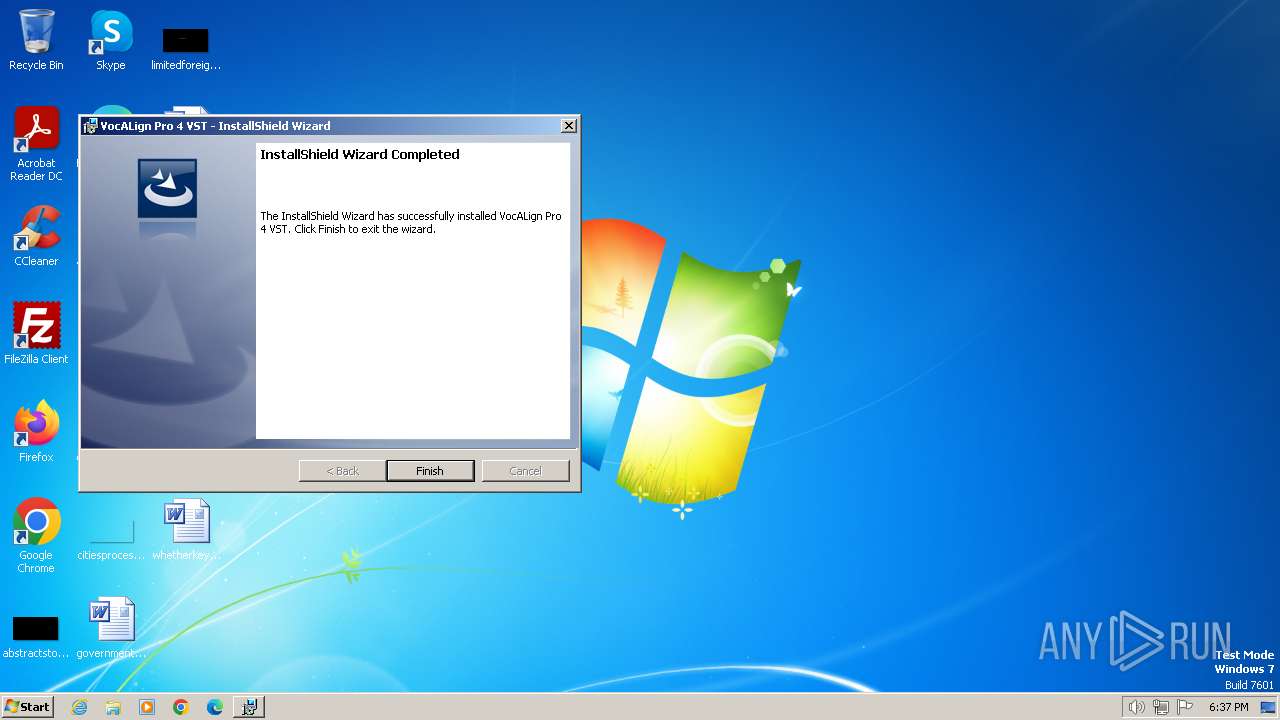
| File name: | VocAlign Pro 4 VST.msi |
| Full analysis: | https://app.any.run/tasks/876db4ad-b2bb-4612-8905-4207ec33c12e |
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2024, 18:36:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 5.1, MSI Installer, Number of Characters: 0, Title: Installation Database, Comments: Contact: Your local administrator, Keywords: Installer,MSI,Database, Subject: VocALign Pro 4 VST, Author: Synchro Arts Ltd, Security: 1, Number of Pages: 200, Name of Creating Application: InstallShield 2008 - Professional Edition 14, Create Time/Date: Wed Sep 22 10:43:23 2010, Revision Number: {4D93749C-2740-4D2D-B9E2-E70702F320DA}, Code page: 1252, Template: Intel;1033, Last Saved By: god, Last Printed: Mon Sep 27 15:23:54 2010, Last Saved Time/Date: Mon Sep 27 15:23:54 2010, Number of Words: 2 |
| MD5: | 25B22CECF4B68860927A4CE98605B58C |
| SHA1: | 68DC7F4A6ECE5204C1F41F422F85984CC183269A |
| SHA256: | 052D82F31E4AE756F7738405C3D6527D55117BE7A2FB38319E0D27022EB4F5CD |
| SSDEEP: | 98304:9RHr5Nw7V0a+3o00OtFdm3L+d2SVR9ztDb7wcwOSoIKRQ6DZCX0HwsaNtXeGX0gC:9WGcWxL |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 1056)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 2064)
Process drops legitimate windows executable
- msiexec.exe (PID: 1056)
INFO
Checks supported languages
- msiexec.exe (PID: 1056)
- wmpnscfg.exe (PID: 120)
Reads the computer name
- wmpnscfg.exe (PID: 120)
- msiexec.exe (PID: 1056)
Create files in a temporary directory
- msiexec.exe (PID: 1056)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1056)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Characters: | - |
|---|---|
| Title: | Installation Database |
| Comments: | Contact: Your local administrator |
| Keywords: | Installer,MSI,Database |
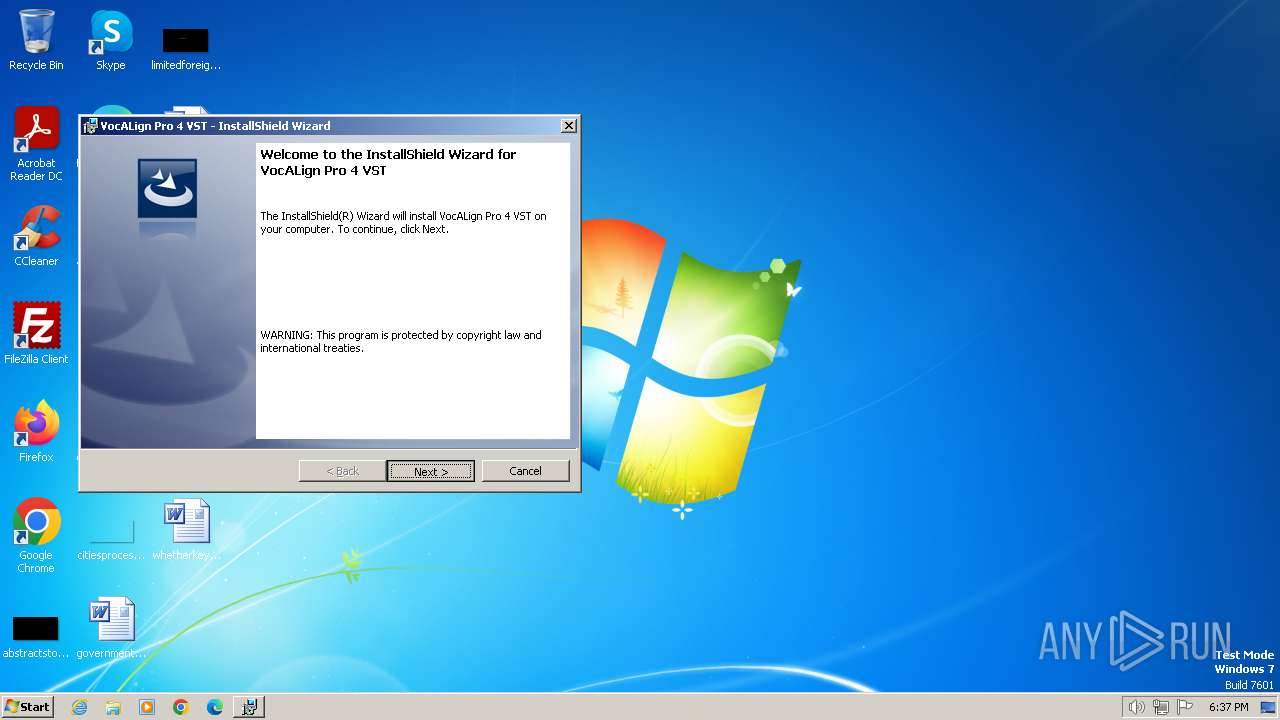
| Subject: | VocALign Pro 4 VST |
| Author: | Synchro Arts Ltd |
| Security: | Password protected |
| Pages: | 200 |
| Software: | InstallShield? 2008 - Professional Edition 14 |
| CreateDate: | 2010:09:22 09:43:23 |
| RevisionNumber: | {4D93749C-2740-4D2D-B9E2-E70702F320DA} |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| LastModifiedBy: | god |
| LastPrinted: | 2010:09:27 14:23:54 |
| ModifyDate: | 2010:09:27 14:23:54 |
| Words: | 2 |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1056 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2036 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\VocAlign Pro 4 VST.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 747
Read events
2 714
Write events
23
Delete events
10
Modification events
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000009F5A7BD72FB0D90164030000840D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000009F5A7BD72FB0D90164030000840D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 73 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000008543C5D72FB0D90164030000840D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 4000000000000000D1ABF1D82FB0D90164030000840D0000D3070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 4000000000000000D1ABF1D82FB0D90164030000840D0000D4070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 4000000000000000475C02D92FB0D90164030000840D0000D4070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Leave) |
Value: 4000000000000000E57701DA2FB0D90164030000840D0000D0070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Leave) |
Value: 4000000000000000E57701DA2FB0D90164030000840D0000D5070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1056) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore |
| Operation: | write | Name: | FirstRun |
Value: 0 | |||
Executable files
6
Suspicious files
9
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1056 | msiexec.exe | C:\Windows\Installer\e3851.msi | — | |
MD5:— | SHA256:— | |||
| 1056 | msiexec.exe | C:\Program Files\Synchro Arts Ltd\VocALign Pro 4 VST\VocALignPro4VST.pdf | — | |
MD5:— | SHA256:— | |||
| 1056 | msiexec.exe | C:\Windows\Installer\e3854.msi | — | |
MD5:— | SHA256:— | |||
| 1056 | msiexec.exe | C:\Windows\Installer\$PatchCache$\Managed\666C77BE943B6404B83D4E4911911EFE\4.0.0\Global_System_STDOLE_f1.8C0C59A0_7DC8_11D2_B95D_006097C4DE24 | executable | |
MD5:1B02577F0ADDEA32EB02A50D4A4CDD1E | SHA256:6EA525BFACE5467C1045C3708F339A4B92A3A273F70656E061C7F7322C56D667 | |||
| 1056 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:872976D4523A116DC7711E0B6FBF8F40 | SHA256:417A9765417AB6F2F23B4494F0E7F164BB4D7946D180FB238D08E4BC26ED3D7D | |||
| 1056 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFBF7F883879BCB471.TMP | binary | |
MD5:80015767544D48196A1AE1846D901F97 | SHA256:5A18EB839DFB6729C914CF389CD05BC3F32E187DD095D96E428C4714C362B6FB | |||
| 1056 | msiexec.exe | C:\Program Files\Common Files\VST3\VocALignPro.vst3 | executable | |
MD5:D4DB850C20CF02B166A712A36F7CF7FA | SHA256:4FB638950CDA9ACD9BEB4C9D2518A4B76F147F09D1DDC317FD72042E5097F6BE | |||
| 1056 | msiexec.exe | C:\Config.Msi\e3853.rbs | binary | |
MD5:9B420B648D213C4EF25DC46987102291 | SHA256:DAA9BA0C0BAB6C5DE864F97260641C570EB29A70C855F33501F5888113E259BD | |||
| 1056 | msiexec.exe | C:\Windows\Installer\e3852.ipi | binary | |
MD5:B19FDAD9CD5085352A5B9303412DF128 | SHA256:57E45672B8CDF5956E8D992A853BDD482C57520A83BB9678445A9898186EAA57 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |