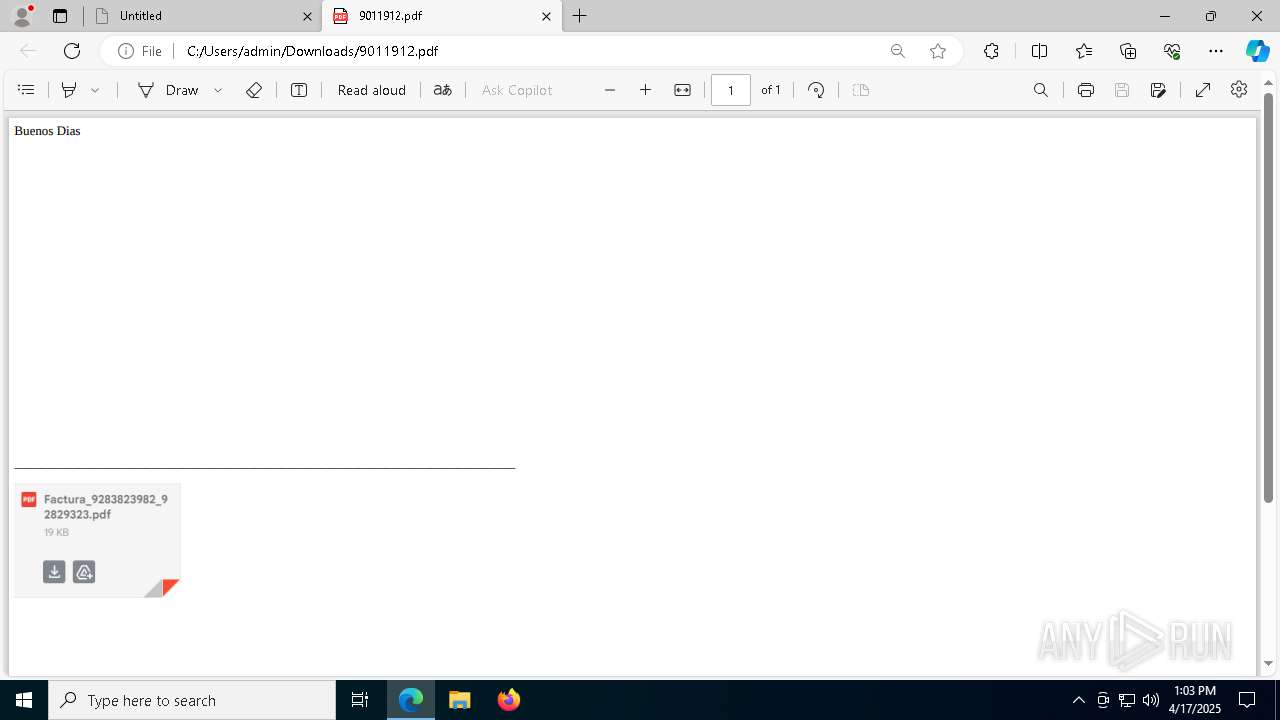
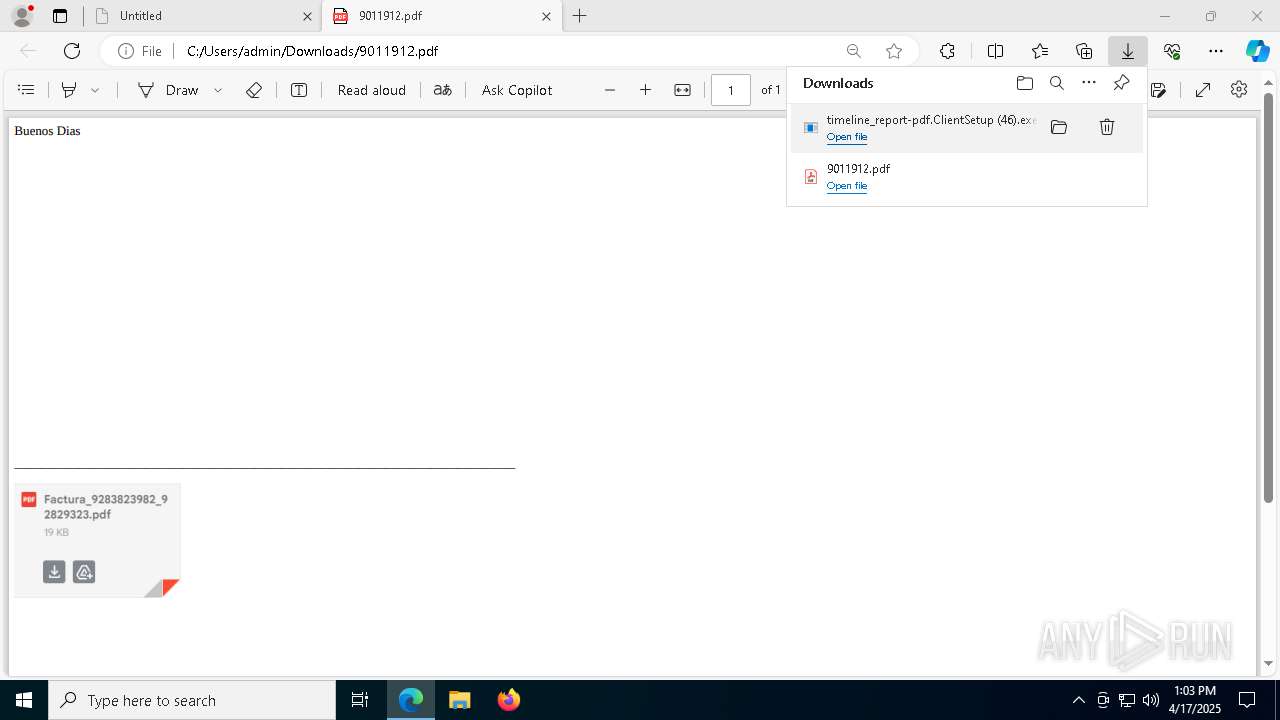
| URL: | https://hidrive.ionos.com/api/sharelink/download?id=IaizImgKW |
| Full analysis: | https://app.any.run/tasks/c0bdceef-d80a-4460-aa7d-ad472d41eca8 |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2025, 13:03:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 39BF6108CF94B2D3996A88A8401AAC35 |
| SHA1: | D12F04466964913E5F1601B67887B49024B39B5A |
| SHA256: | 052813E40CF7D02989ABD503807832E924F86C8F59EE9CB435D4FB1791D6F6DD |
| SSDEEP: | 3:N8whMTAJyK09KBjE09n:2whMTiyK00BjZn |
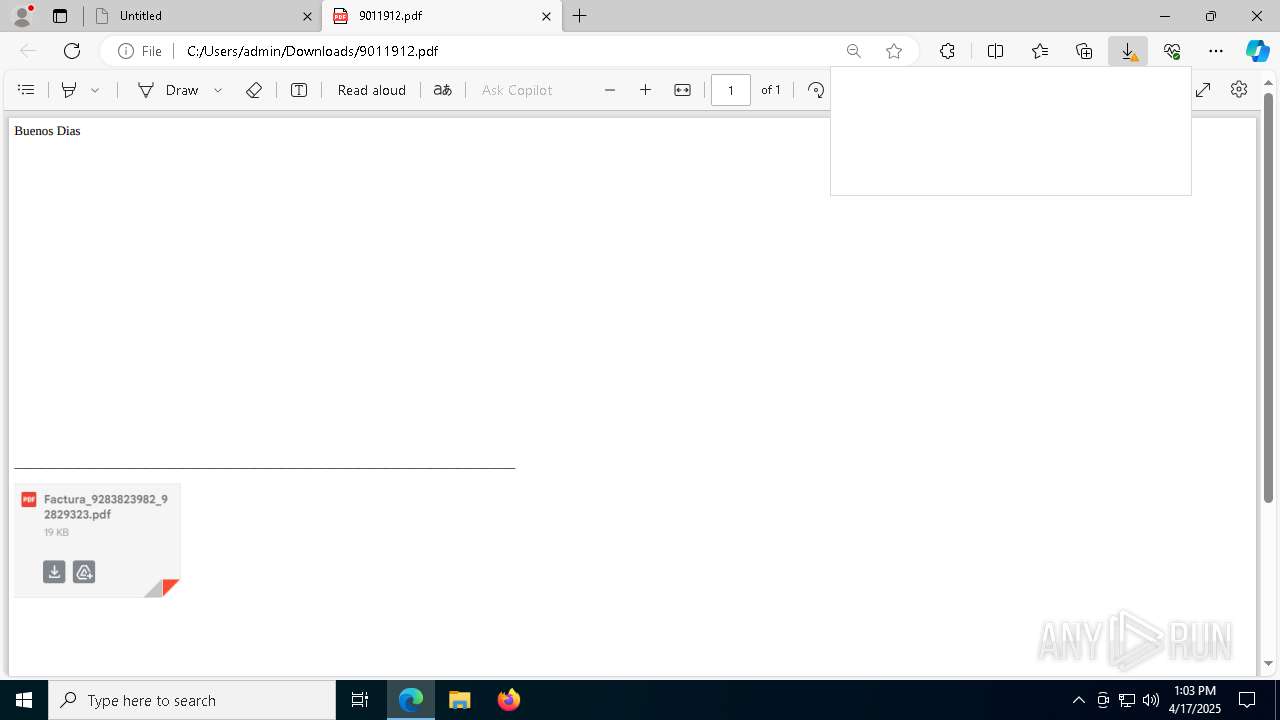
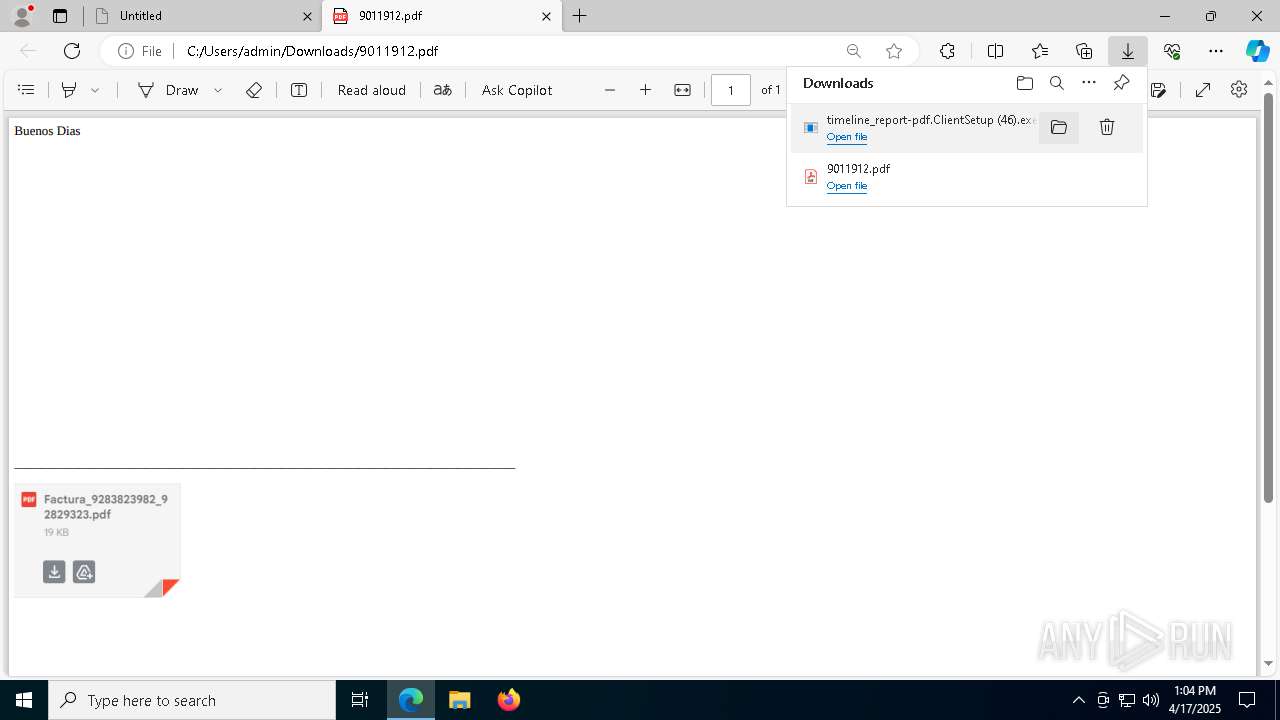
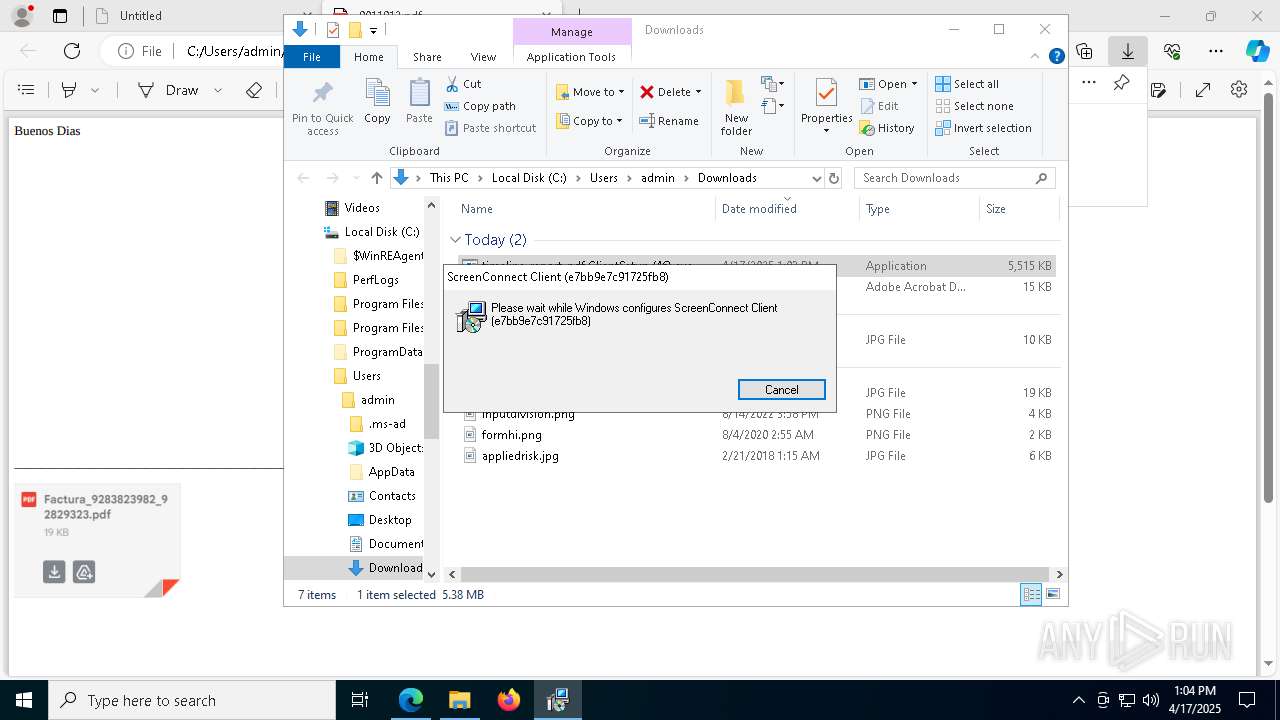
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6656)
SUSPICIOUS
Reads security settings of Internet Explorer
- timeline_report-pdf.ClientSetup (46).exe (PID: 8812)
- ScreenConnect.ClientService.exe (PID: 6656)
- ScreenConnect.WindowsClient.exe (PID: 8780)
- ScreenConnect.WindowsClient.exe (PID: 7052)
- timeline_report-pdf.ClientSetup (46).exe (PID: 924)
Executes application which crashes
- timeline_report-pdf.ClientSetup (46).exe (PID: 8896)
- timeline_report-pdf.ClientSetup (46).exe (PID: 5260)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8196)
- timeline_report-pdf.ClientSetup (46).exe (PID: 6676)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8344)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8436)
Executable content was dropped or overwritten
- rundll32.exe (PID: 1228)
- rundll32.exe (PID: 8900)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 9040)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 9040)
Executes as Windows Service
- VSSVC.exe (PID: 6744)
- ScreenConnect.ClientService.exe (PID: 6656)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 6656)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 6656)
- ScreenConnect.ClientService.exe (PID: 6656)
- rundll32.exe (PID: 8900)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 6656)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 6656)
INFO
Create files in a temporary directory
- timeline_report-pdf.ClientSetup (46).exe (PID: 8812)
- rundll32.exe (PID: 1228)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8964)
- msedge.exe (PID: 7648)
- msedge.exe (PID: 7340)
- msiexec.exe (PID: 9040)
- msiexec.exe (PID: 8384)
Checks supported languages
- timeline_report-pdf.ClientSetup (46).exe (PID: 8896)
- identity_helper.exe (PID: 664)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8812)
- timeline_report-pdf.ClientSetup (46).exe (PID: 5260)
- msiexec.exe (PID: 9040)
- msiexec.exe (PID: 8004)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8196)
- timeline_report-pdf.ClientSetup (46).exe (PID: 6676)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8436)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8344)
- ScreenConnect.ClientService.exe (PID: 6656)
- msiexec.exe (PID: 1188)
- ScreenConnect.WindowsClient.exe (PID: 8780)
- timeline_report-pdf.ClientSetup (46).exe (PID: 924)
Reads the computer name
- timeline_report-pdf.ClientSetup (46).exe (PID: 8812)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8896)
- identity_helper.exe (PID: 664)
- timeline_report-pdf.ClientSetup (46).exe (PID: 5260)
- timeline_report-pdf.ClientSetup (46).exe (PID: 6676)
- ScreenConnect.ClientService.exe (PID: 6656)
- msiexec.exe (PID: 1188)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8344)
- timeline_report-pdf.ClientSetup (46).exe (PID: 924)
Reads the machine GUID from the registry
- timeline_report-pdf.ClientSetup (46).exe (PID: 8896)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8812)
- timeline_report-pdf.ClientSetup (46).exe (PID: 5260)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8196)
- timeline_report-pdf.ClientSetup (46).exe (PID: 6676)
- ScreenConnect.ClientService.exe (PID: 6656)
- ScreenConnect.WindowsClient.exe (PID: 8780)
- ScreenConnect.WindowsClient.exe (PID: 7052)
- timeline_report-pdf.ClientSetup (46).exe (PID: 8344)
- timeline_report-pdf.ClientSetup (46).exe (PID: 924)
Reads Environment values
- identity_helper.exe (PID: 664)
Application launched itself
- msedge.exe (PID: 7340)
Process checks computer location settings
- timeline_report-pdf.ClientSetup (46).exe (PID: 8812)
CONNECTWISE has been detected
- msiexec.exe (PID: 8964)
- msiexec.exe (PID: 9040)
- ScreenConnect.ClientService.exe (PID: 6656)
- ScreenConnect.WindowsClient.exe (PID: 8780)
- ScreenConnect.WindowsClient.exe (PID: 7052)
- msiexec.exe (PID: 8384)
Manages system restore points
- SrTasks.exe (PID: 2908)
Creates files or folders in the user directory
- WerFault.exe (PID: 8636)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 6656)
- rundll32.exe (PID: 8900)
Creates a software uninstall entry
- msiexec.exe (PID: 9040)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 7052)
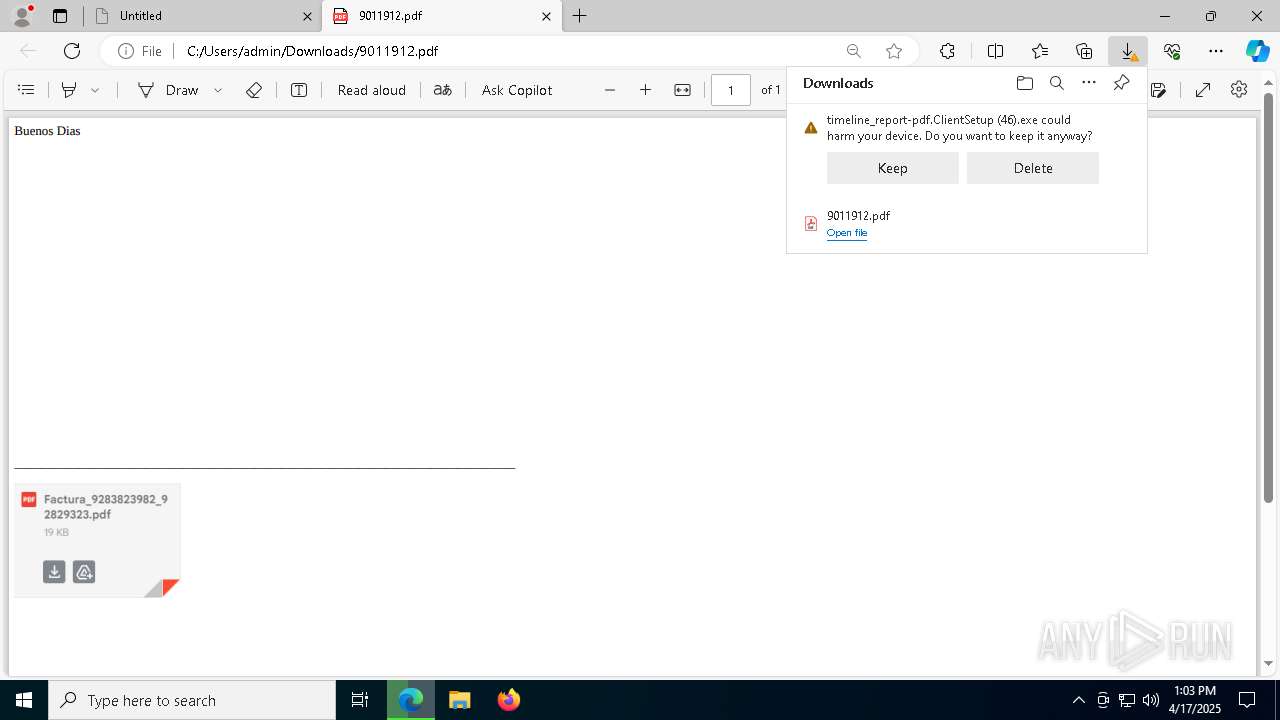
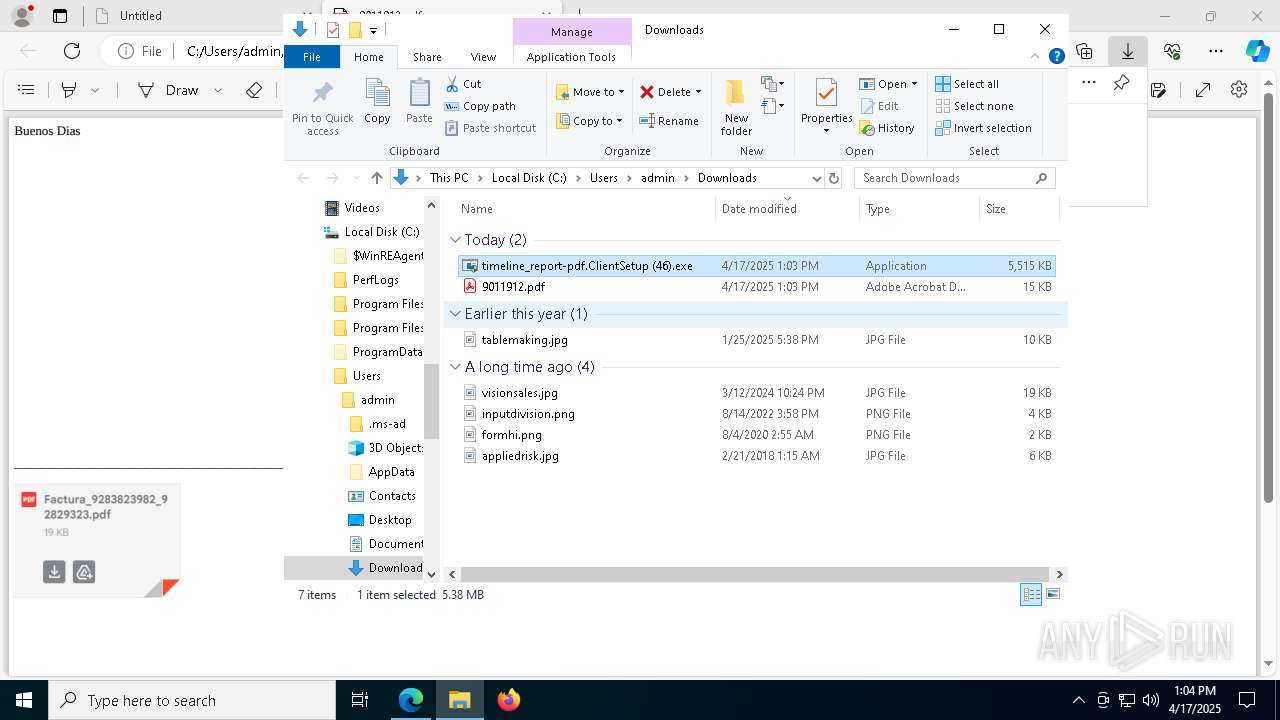
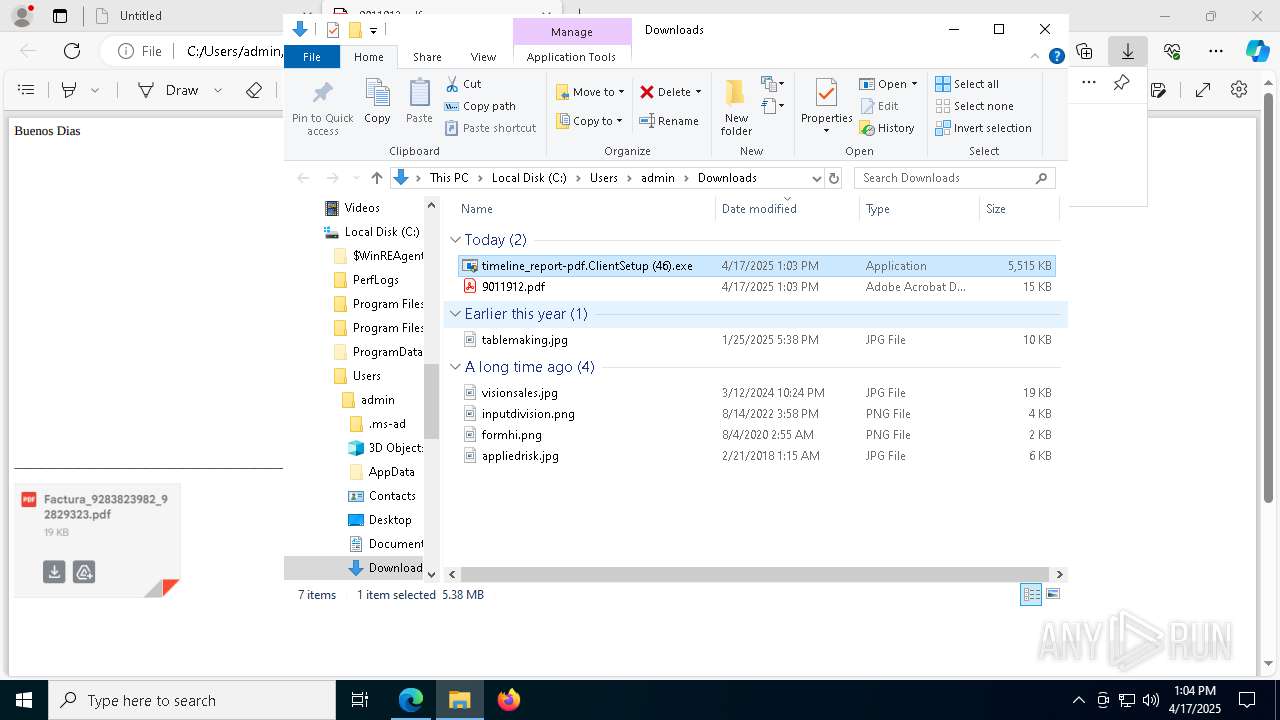
Manual execution by a user
- timeline_report-pdf.ClientSetup (46).exe (PID: 2064)
- timeline_report-pdf.ClientSetup (46).exe (PID: 924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
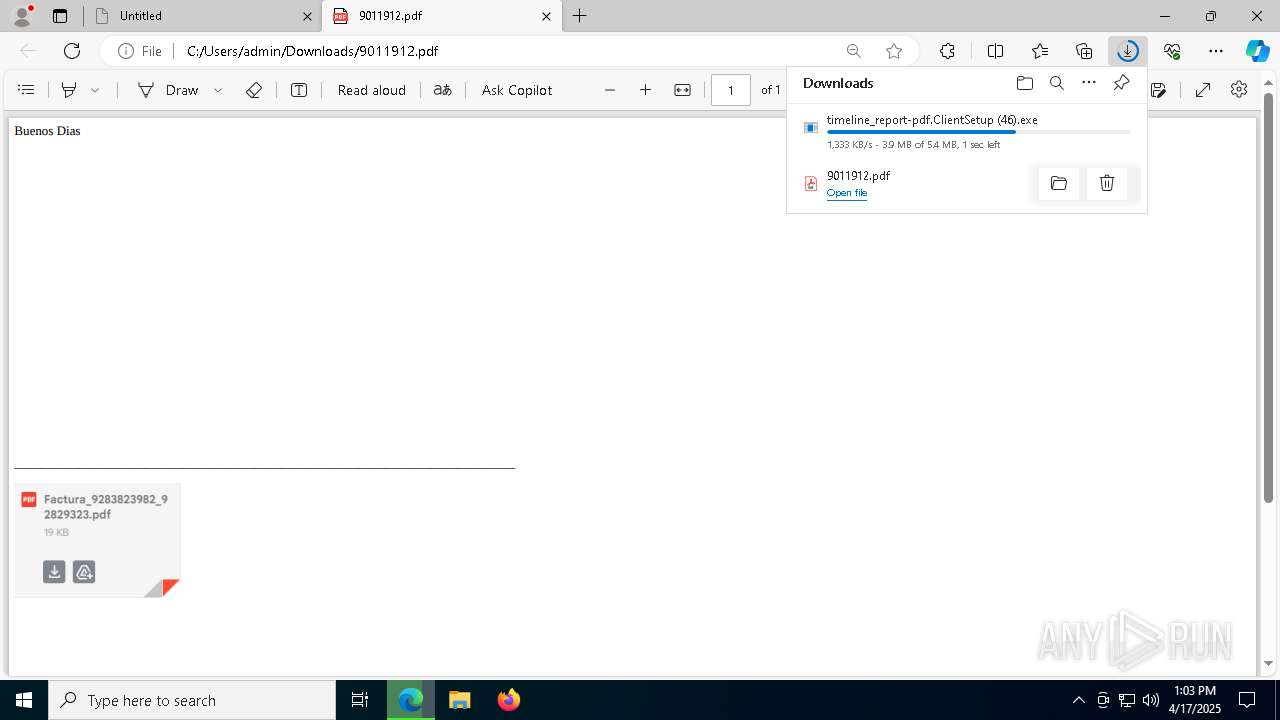
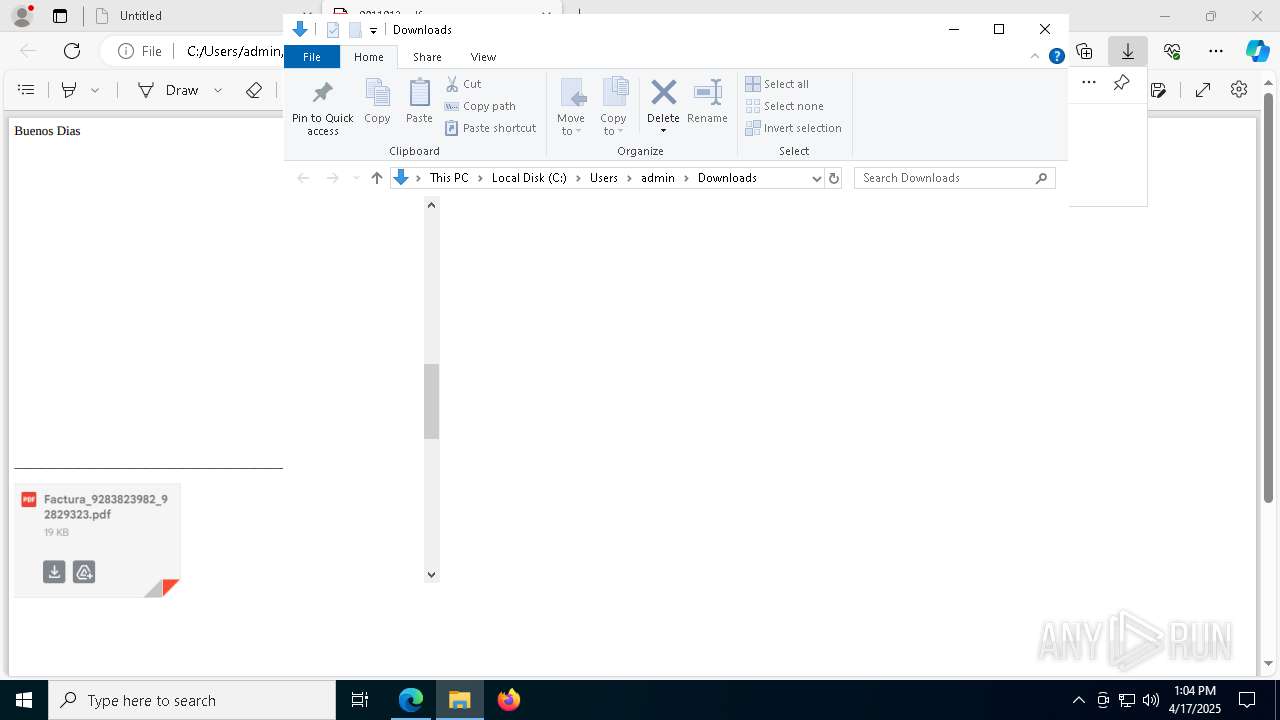
Total processes
222
Monitored processes
74
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
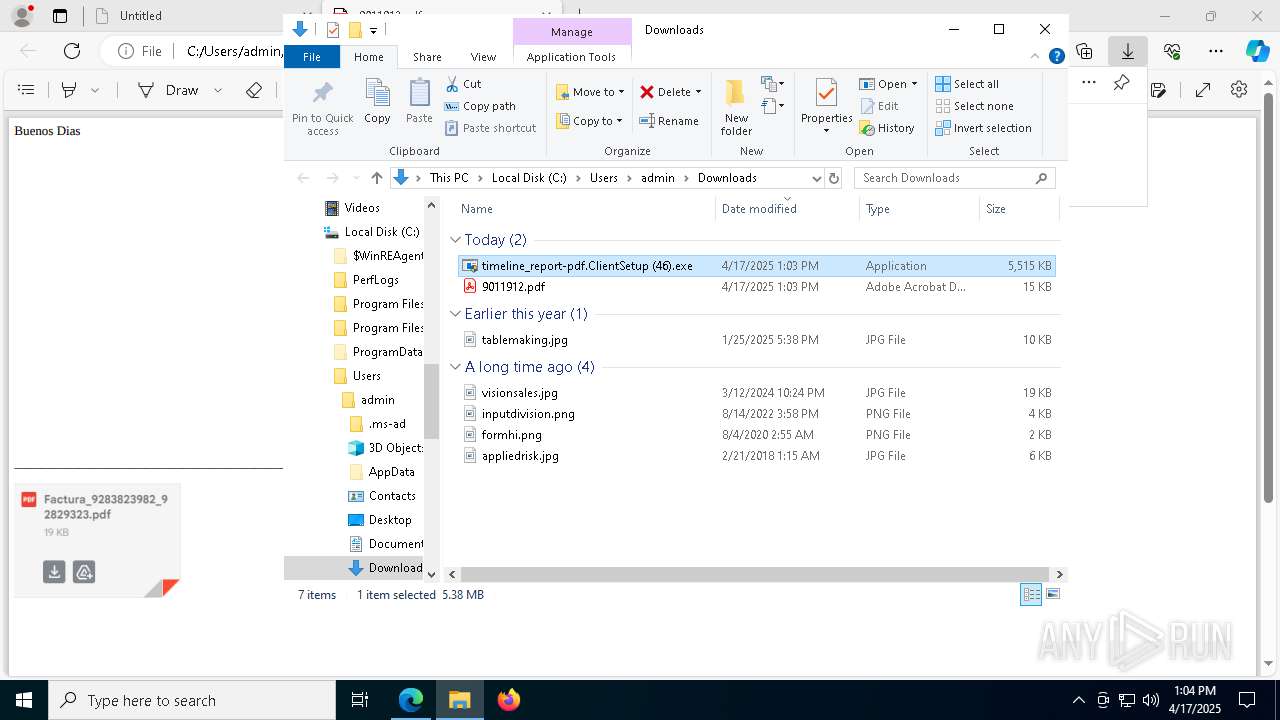
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6572 --field-trial-handle=2388,i,6678346774736110105,10811757166556722069,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6572 --field-trial-handle=2388,i,6678346774736110105,10811757166556722069,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 840 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "C:\Users\admin\Downloads\timeline_report-pdf.ClientSetup (46).exe" | C:\Users\admin\Downloads\timeline_report-pdf.ClientSetup (46).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=ppapi --lang=en-US --device-scale-factor=1 --ppapi-antialiased-text-enabled=0 --ppapi-subpixel-rendering-setting=0 --no-appcompat-clear --mojo-platform-channel-handle=6872 --field-trial-handle=2388,i,6678346774736110105,10811757166556722069,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5832 --field-trial-handle=2388,i,6678346774736110105,10811757166556722069,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | C:\Windows\syswow64\MsiExec.exe -Embedding 2DECF6FC18E459EE88DEBB5AC9CEBE49 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSI126.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1114500 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6536 --field-trial-handle=2388,i,6678346774736110105,10811757166556722069,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 276
Read events
23 923
Write events
307
Delete events
46
Modification events
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393890 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8DE3C34F-B13B-47DC-AA50-6284061AFB52} | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EDBFA94F8F912F00 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D4F1844F8F912F00 | |||
| (PID) Process: | (7340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C0488D4F8F912F00 | |||
Executable files
38
Suspicious files
102
Text files
47
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bc2e.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bc2e.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bc3d.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bc4d.TMP | — | |
MD5:— | SHA256:— | |||
| 7340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
44
DNS requests
39
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8436 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8436 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7648 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7648 | msedge.exe | 85.214.3.95:443 | hidrive.ionos.com | Strato AG | DE | malicious |
7648 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7648 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
hidrive.ionos.com |
| malicious |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7648 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WordPress domains and hosting (hidrive .ionos .com) |
7648 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WordPress domains and hosting (hidrive .ionos .com) |
6656 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |