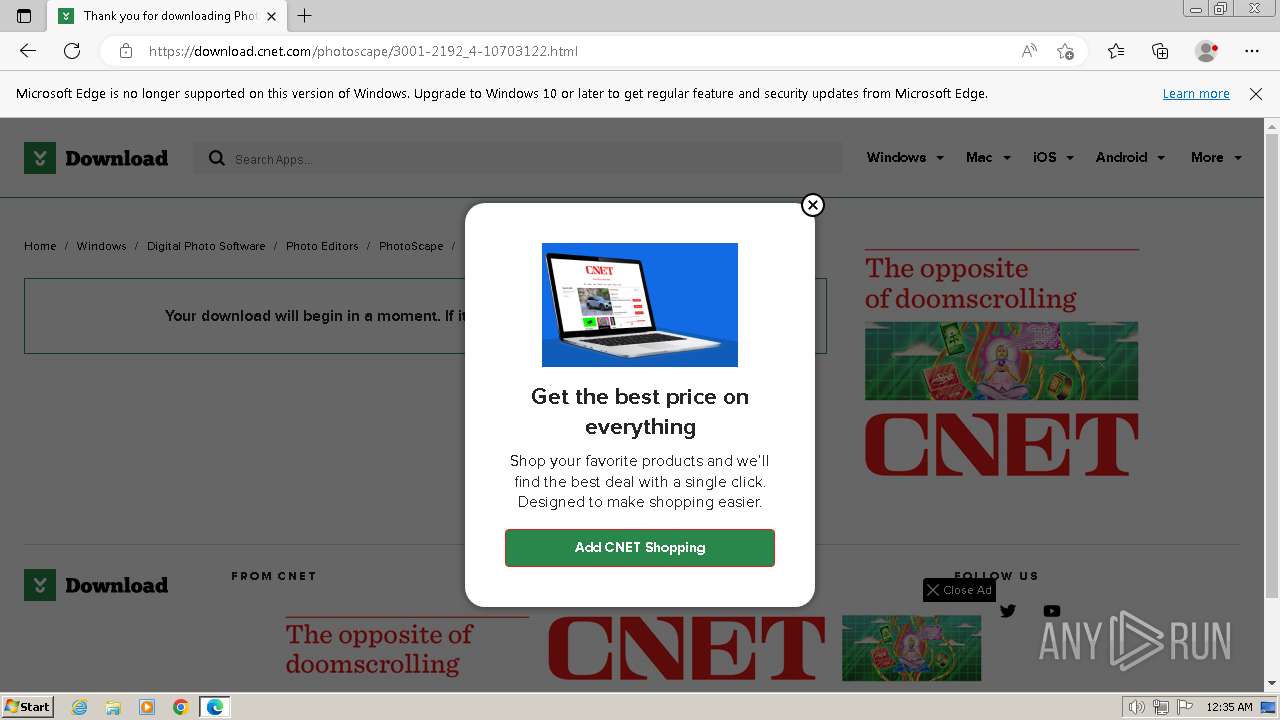
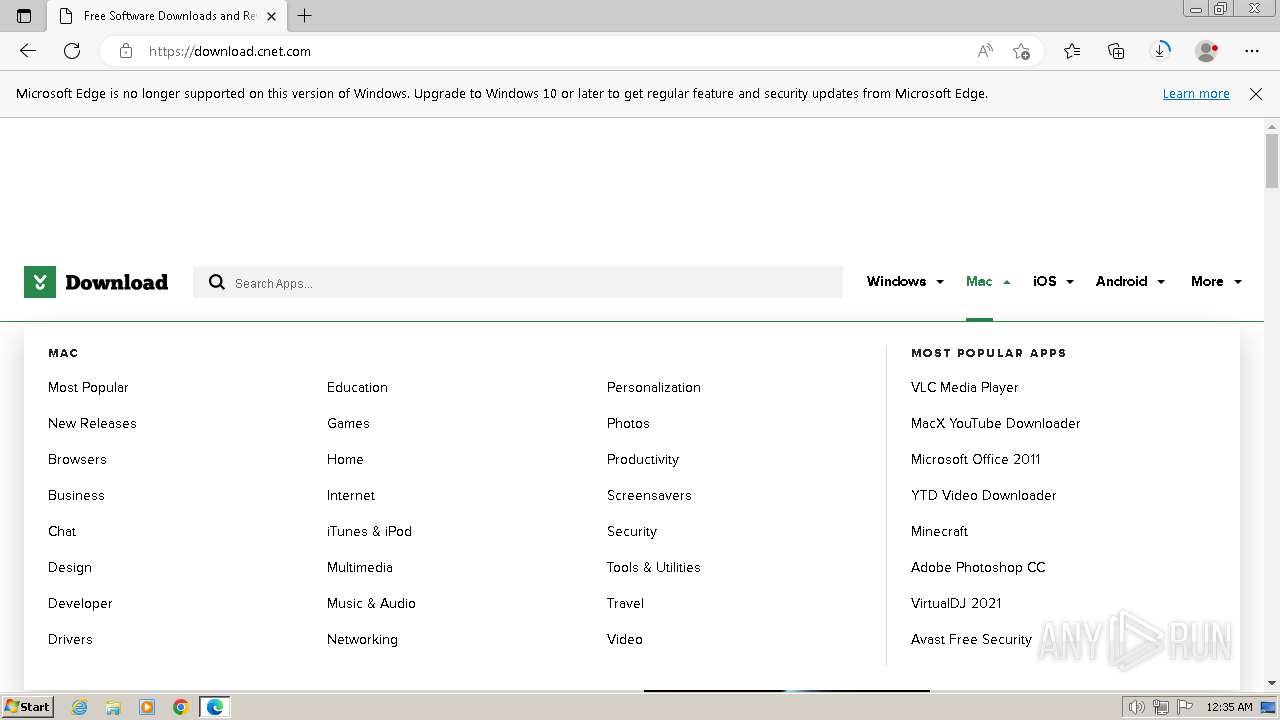
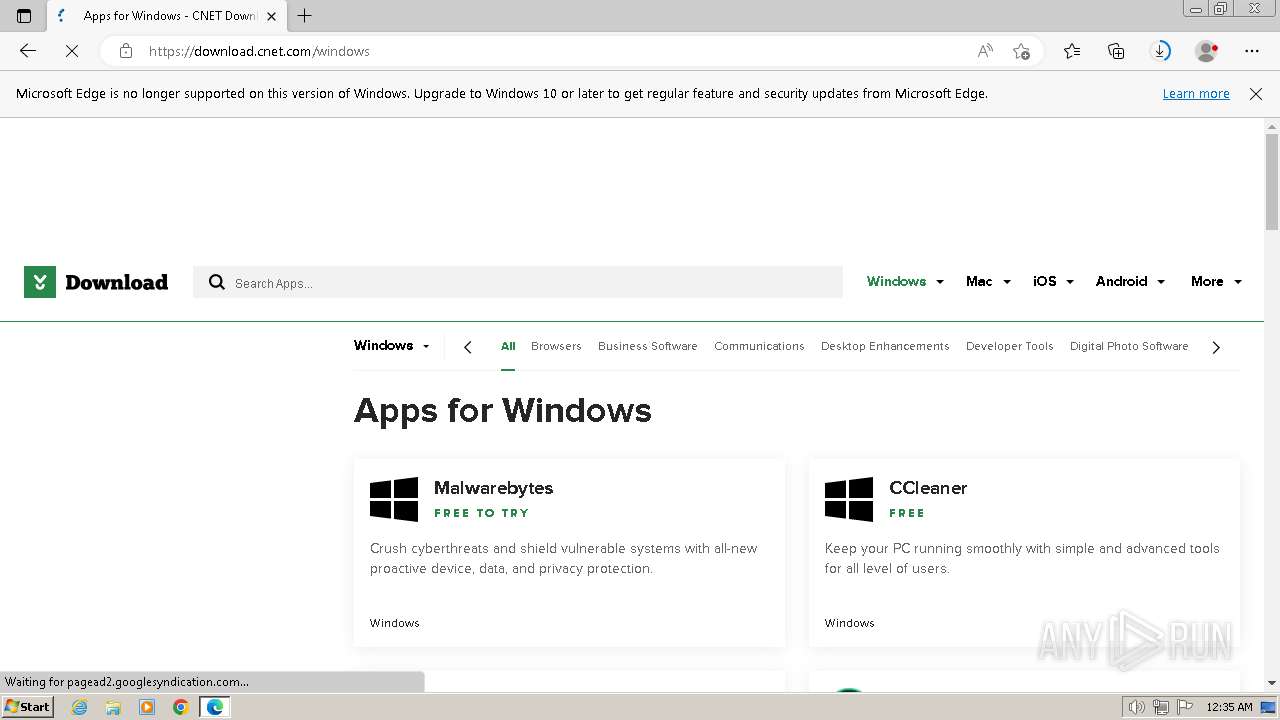
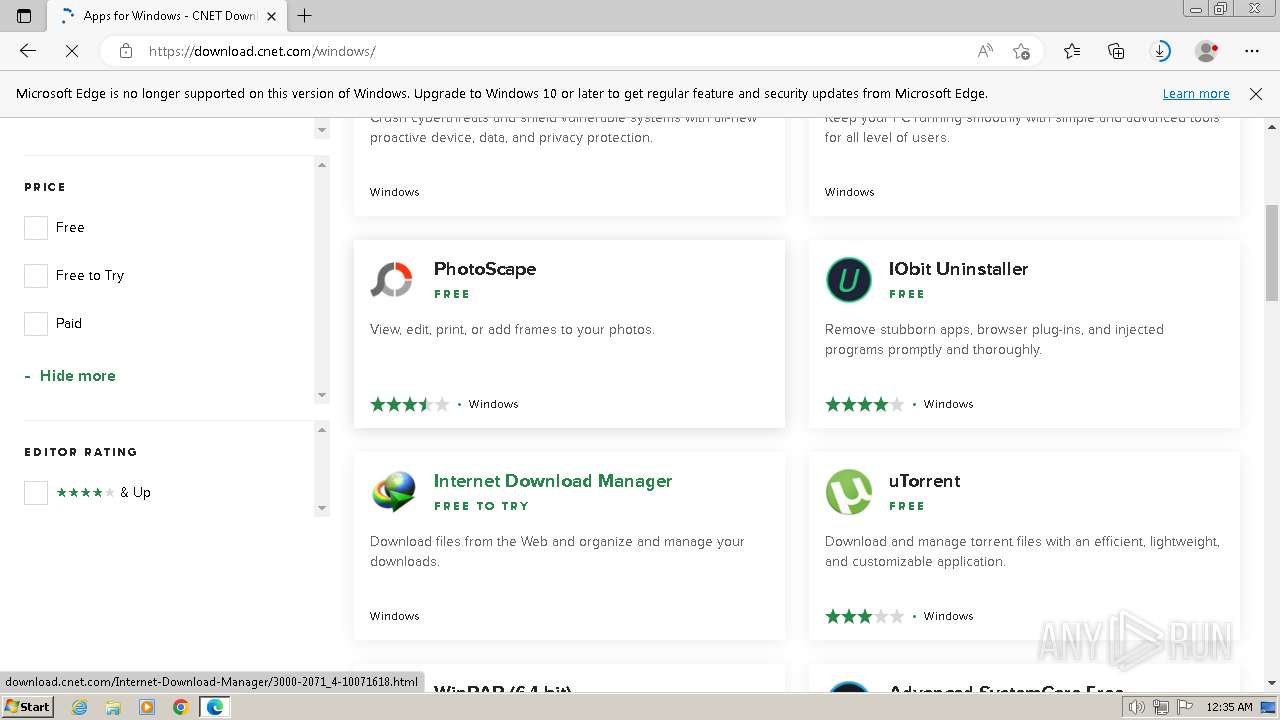
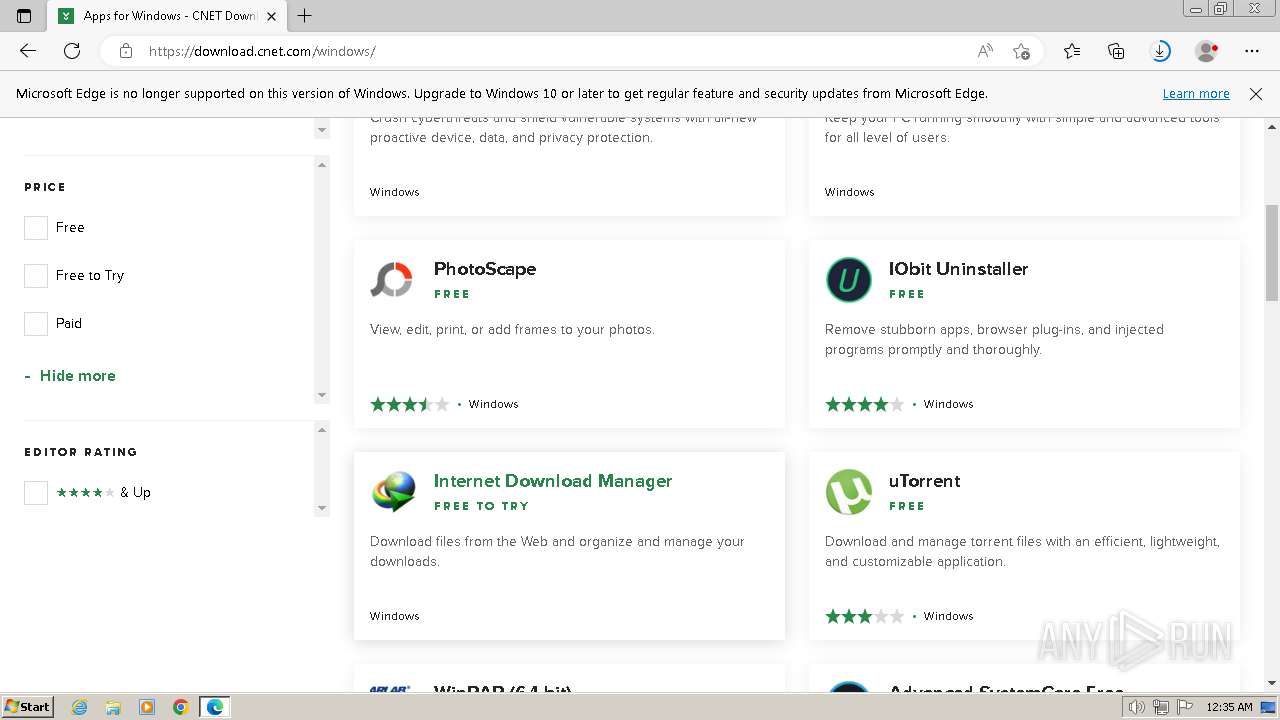
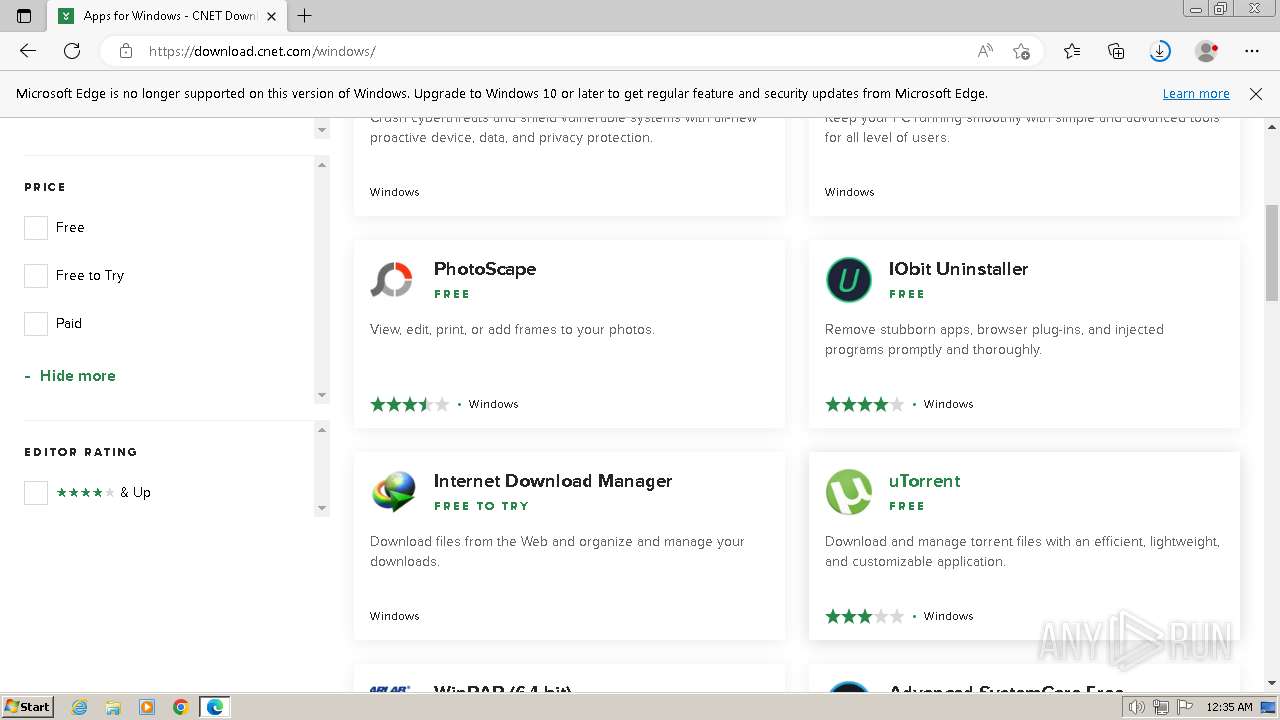
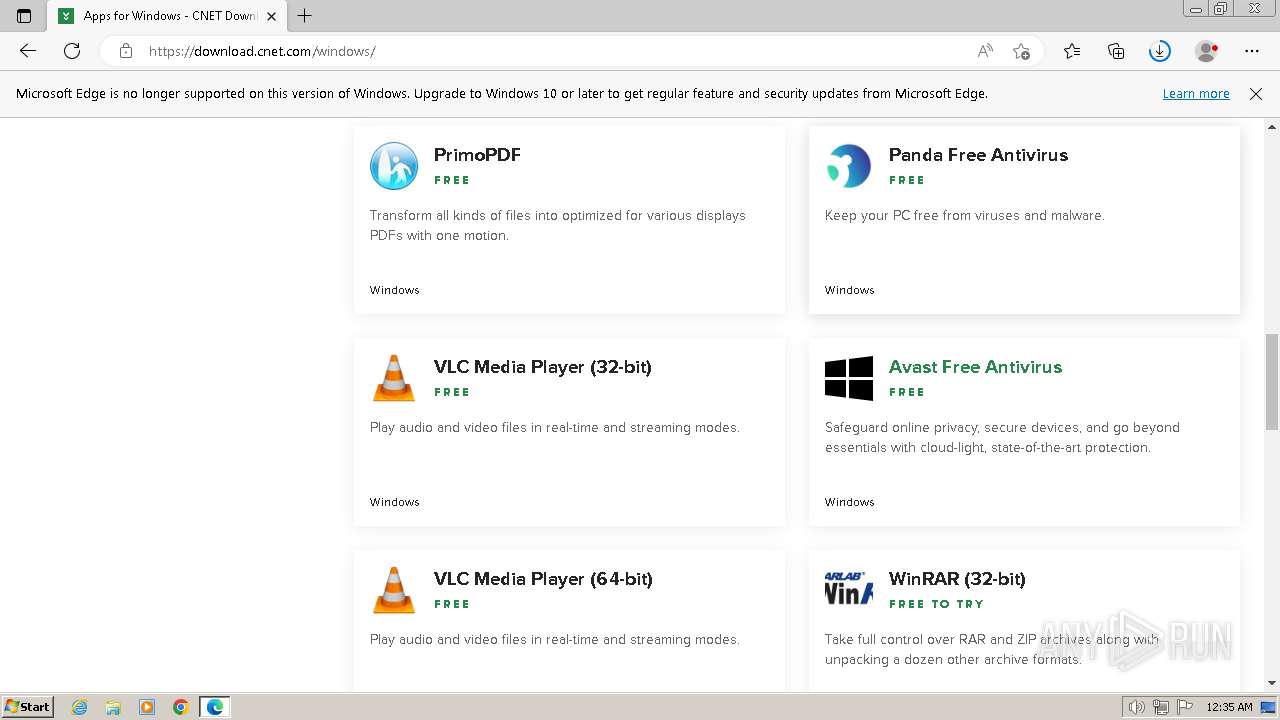
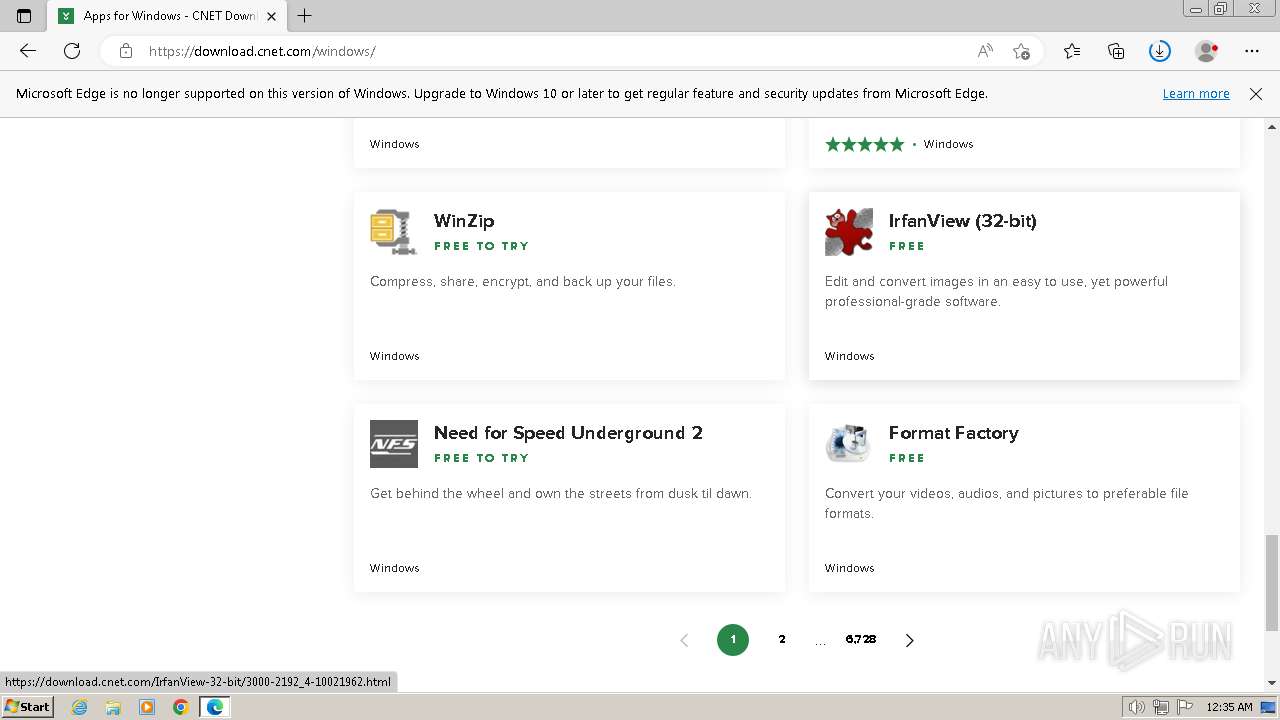
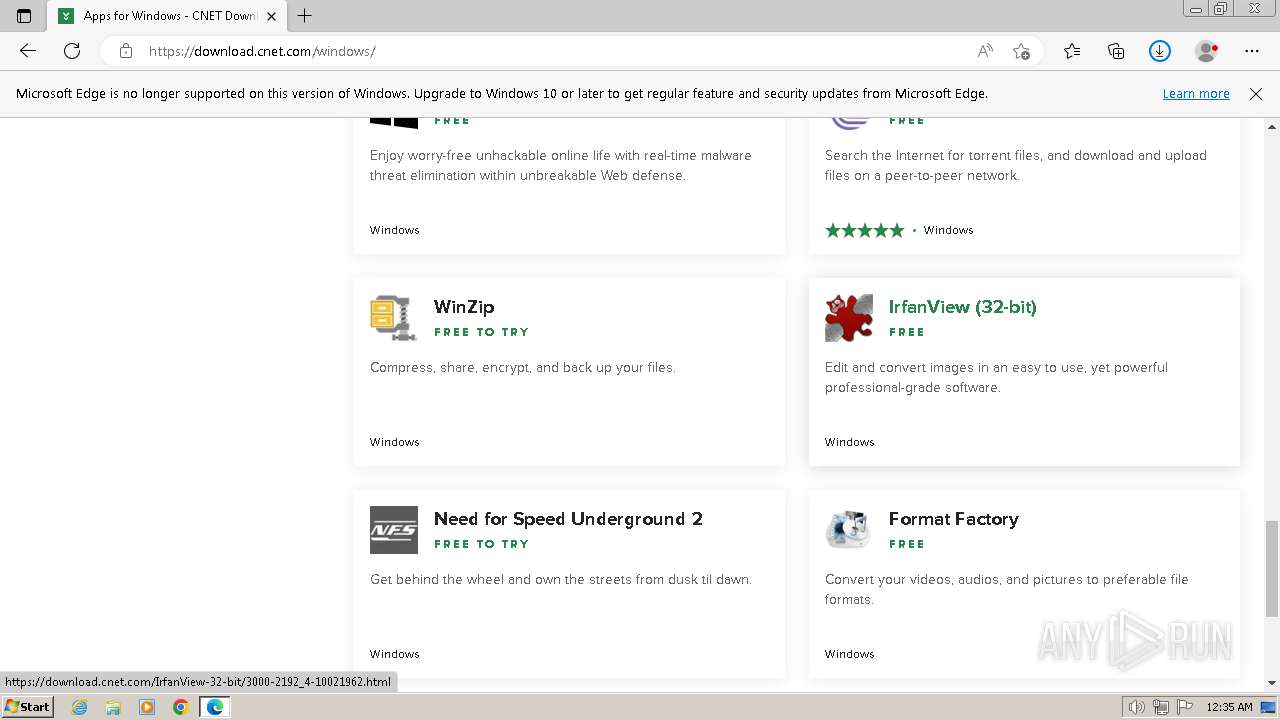
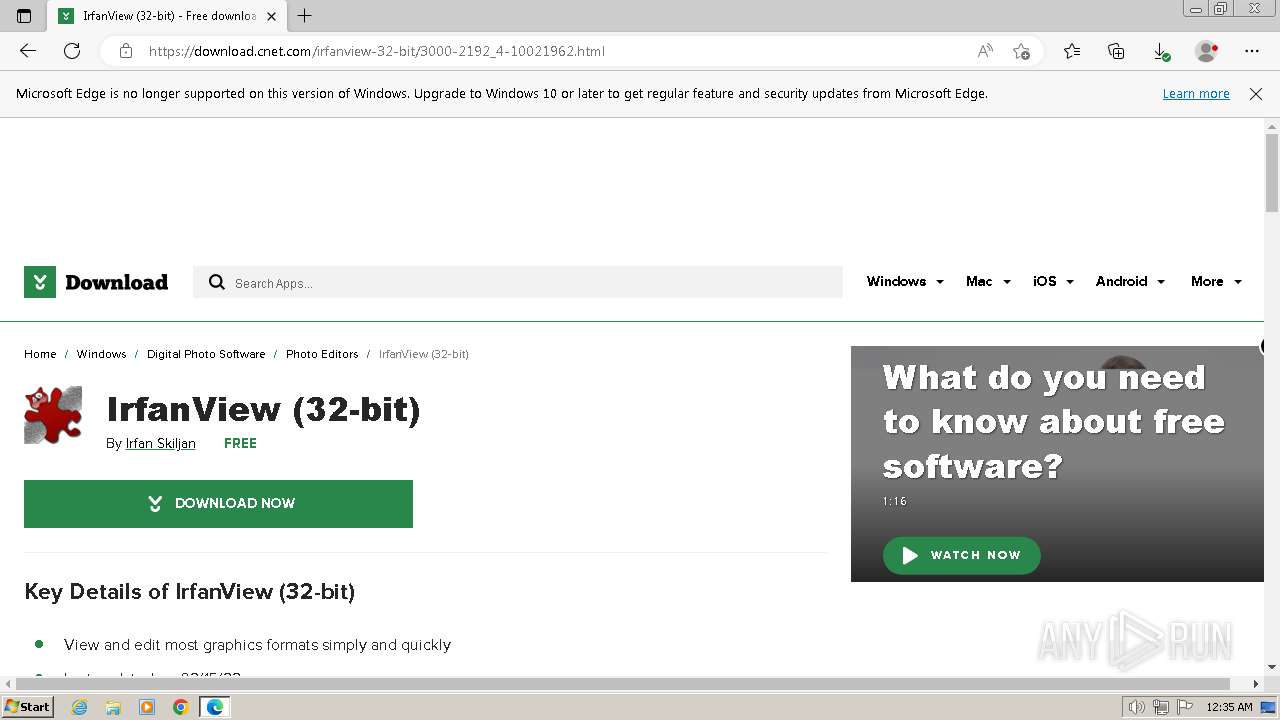
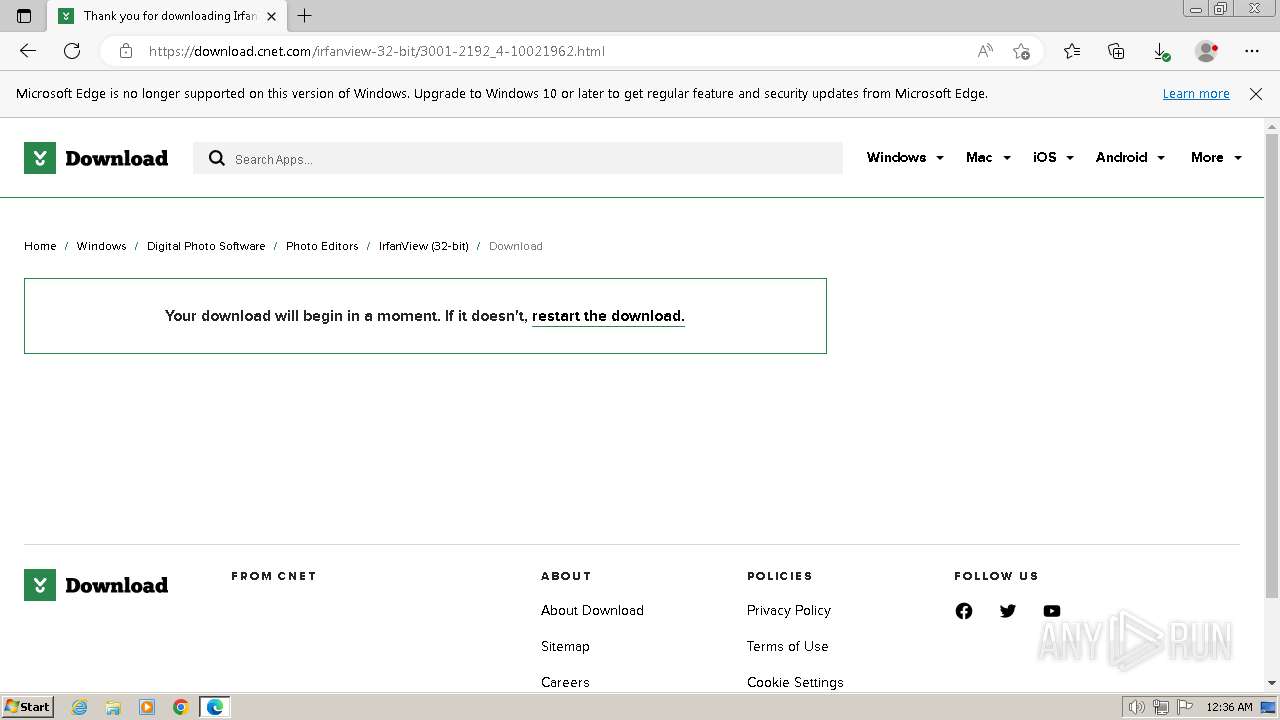
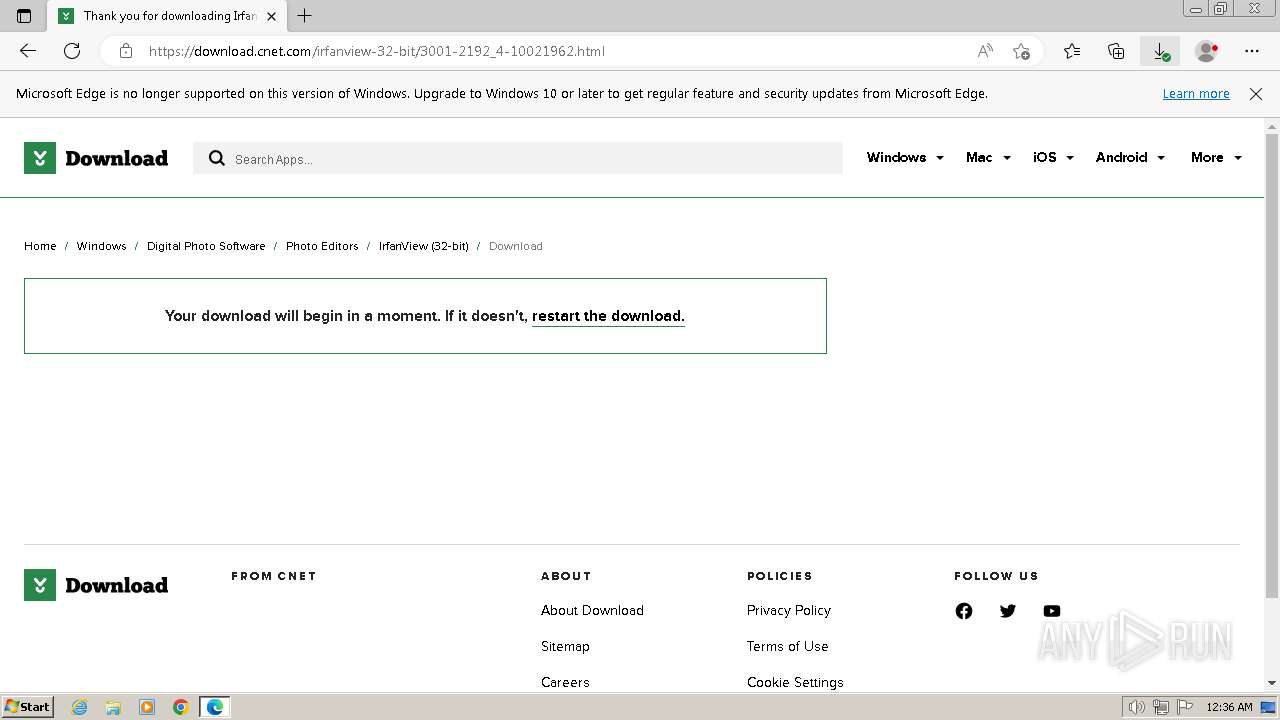
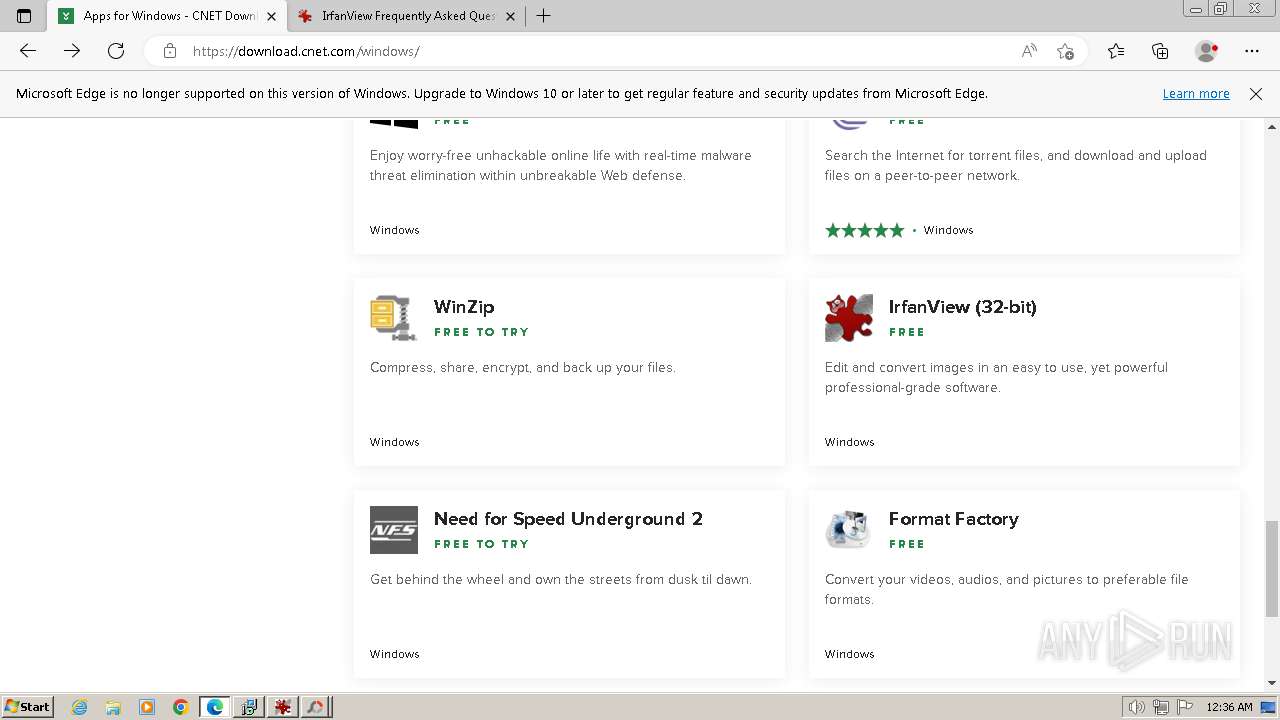
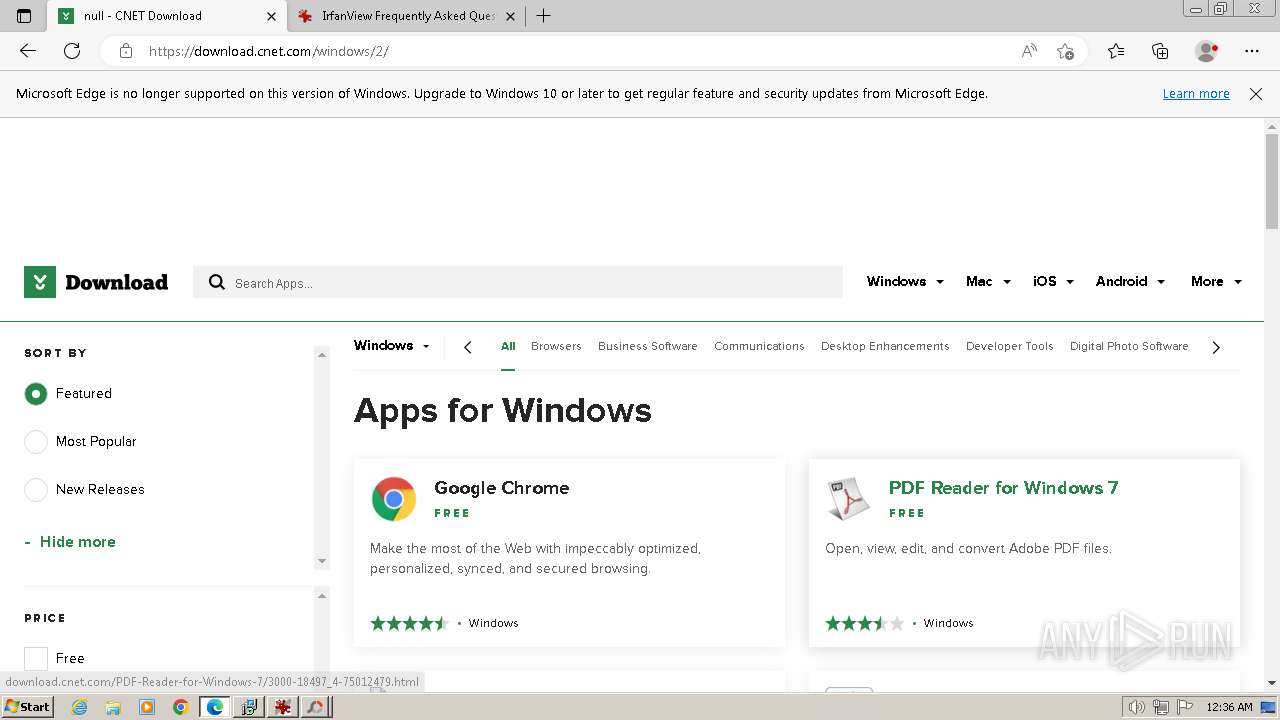
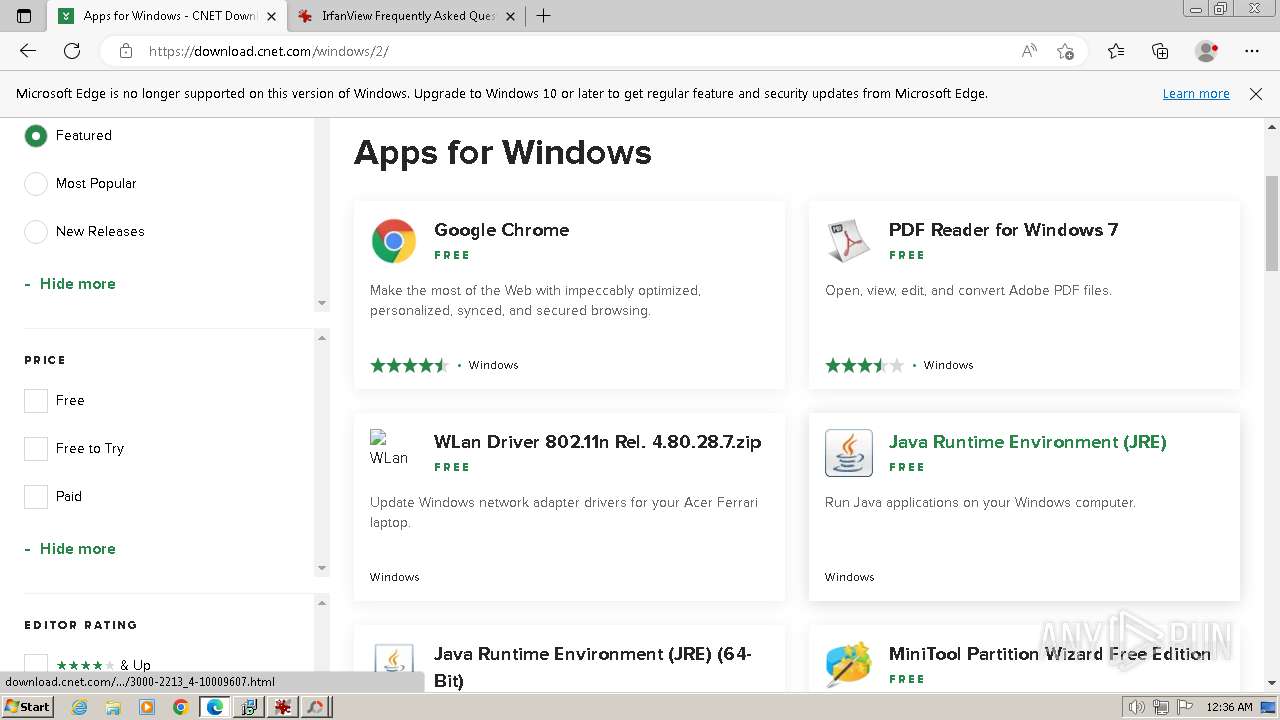
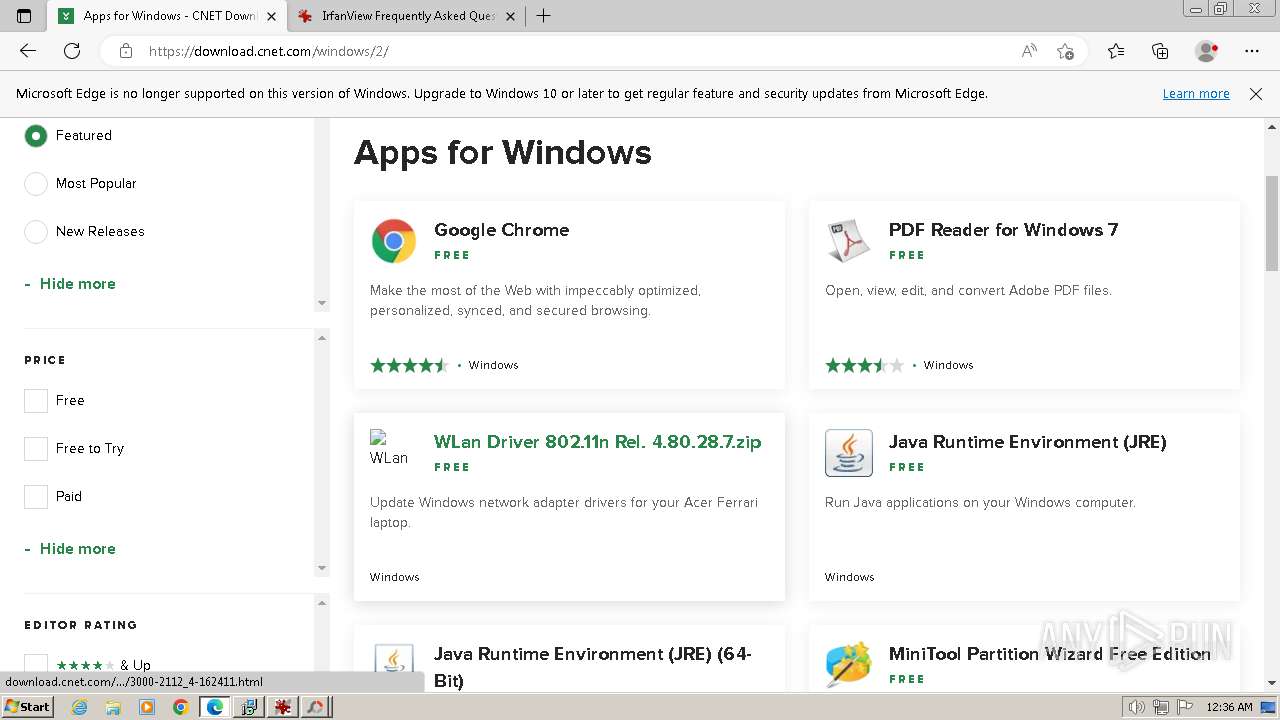
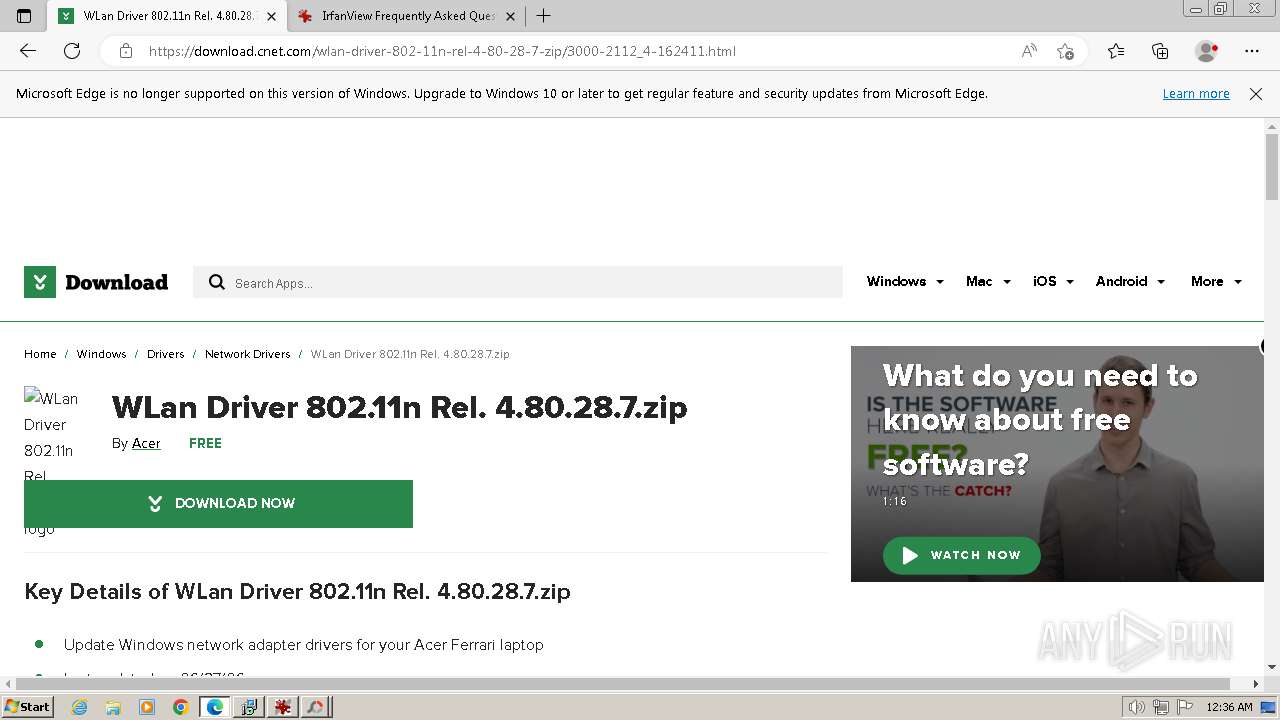
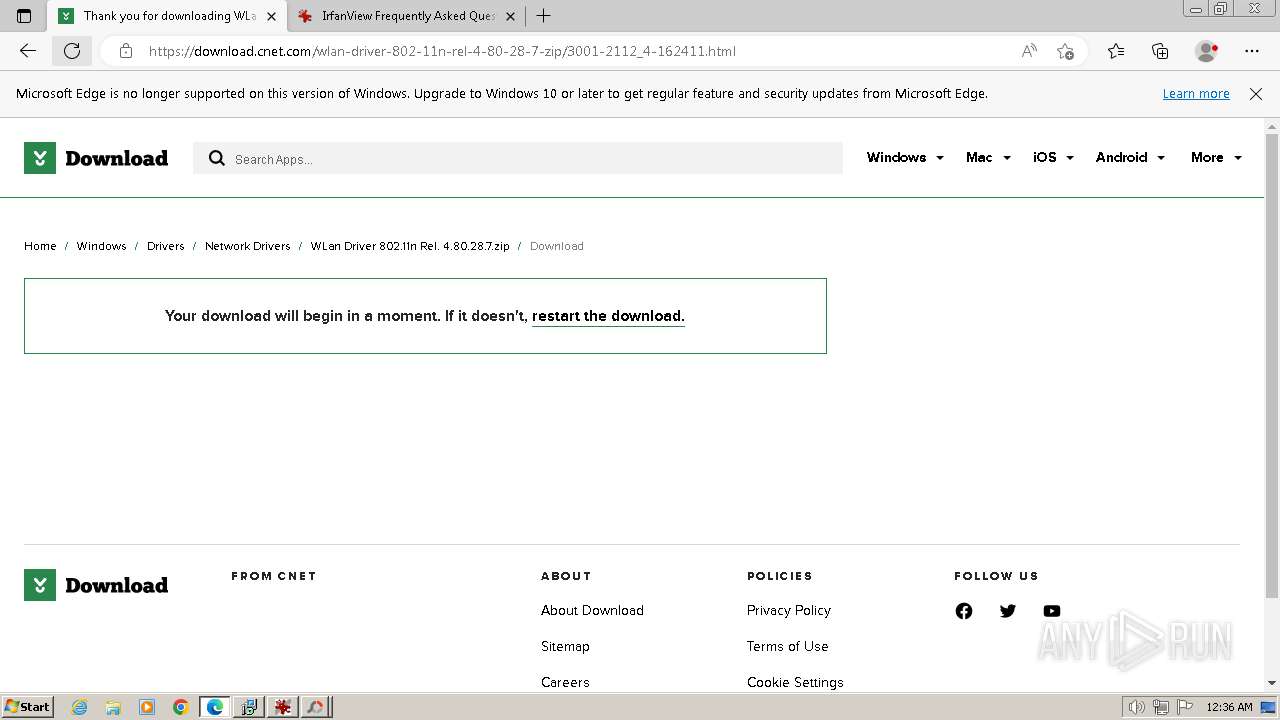
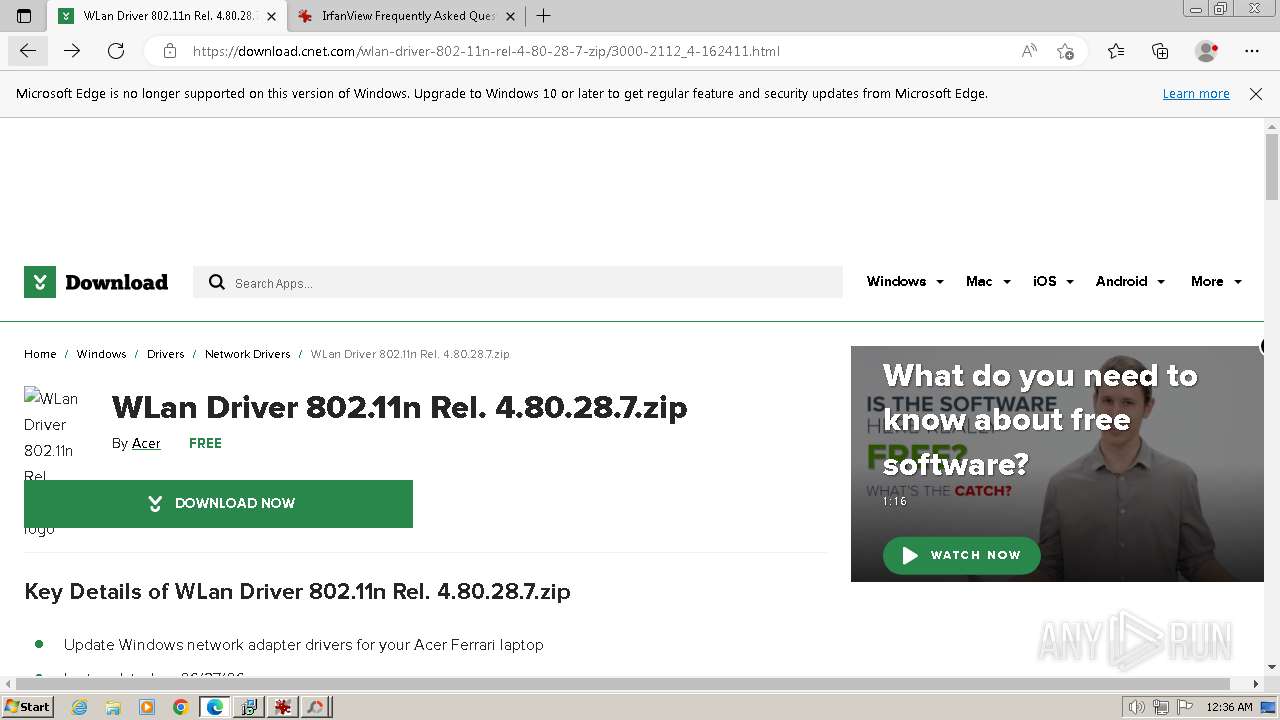
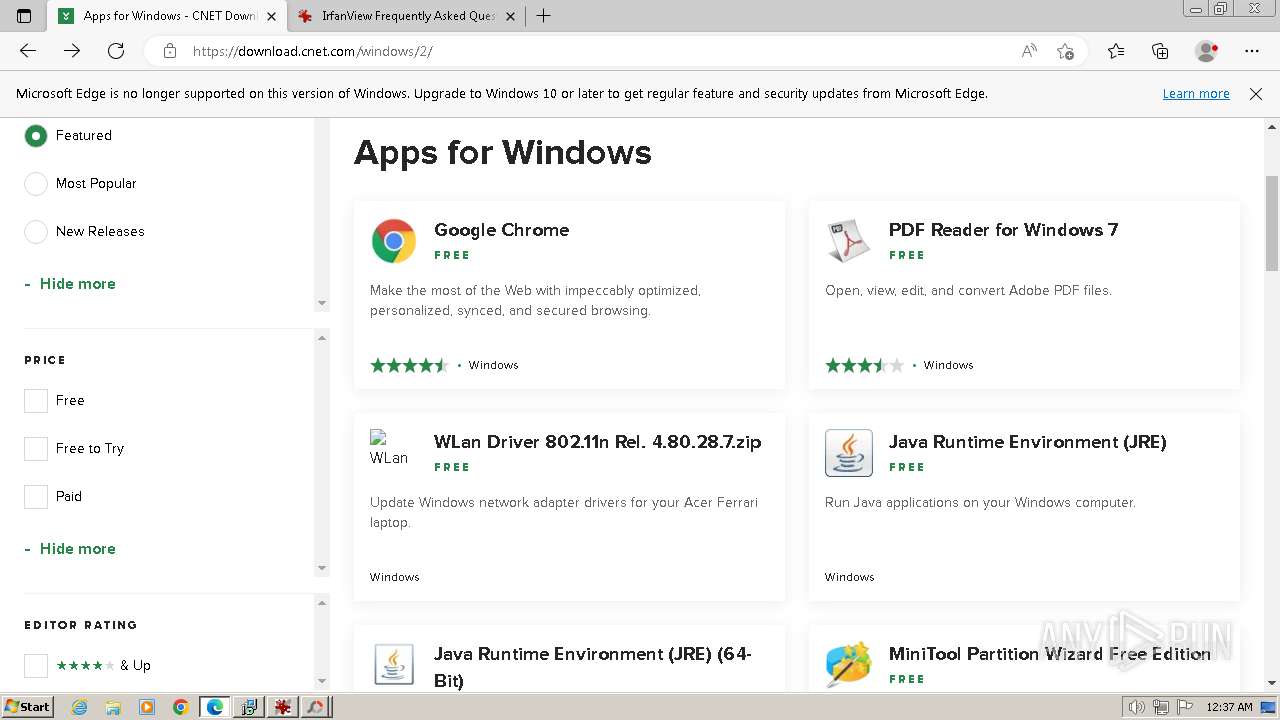
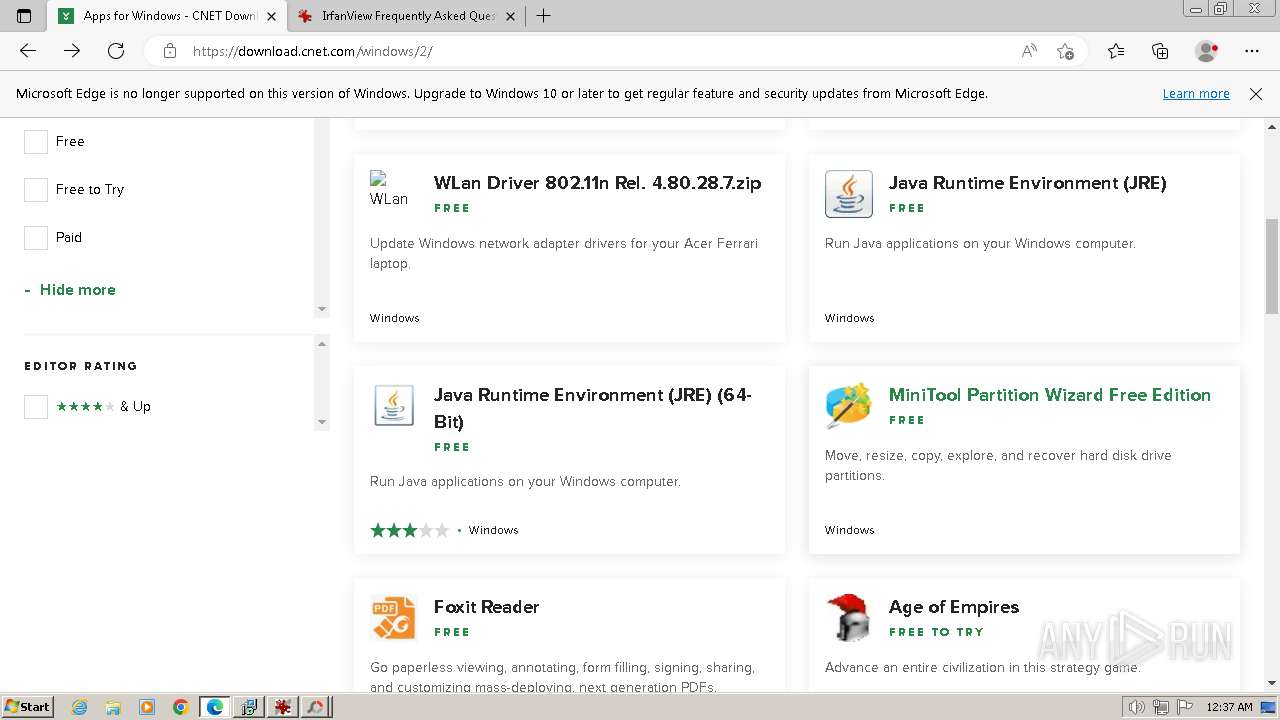
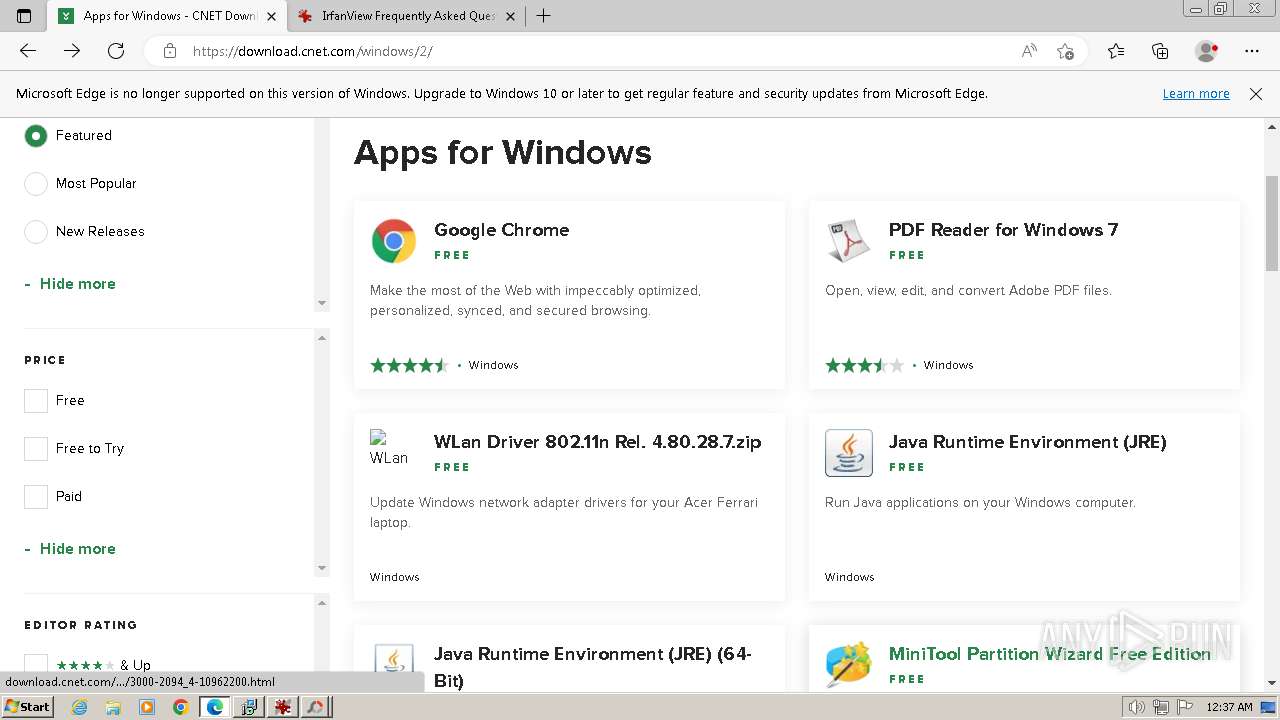
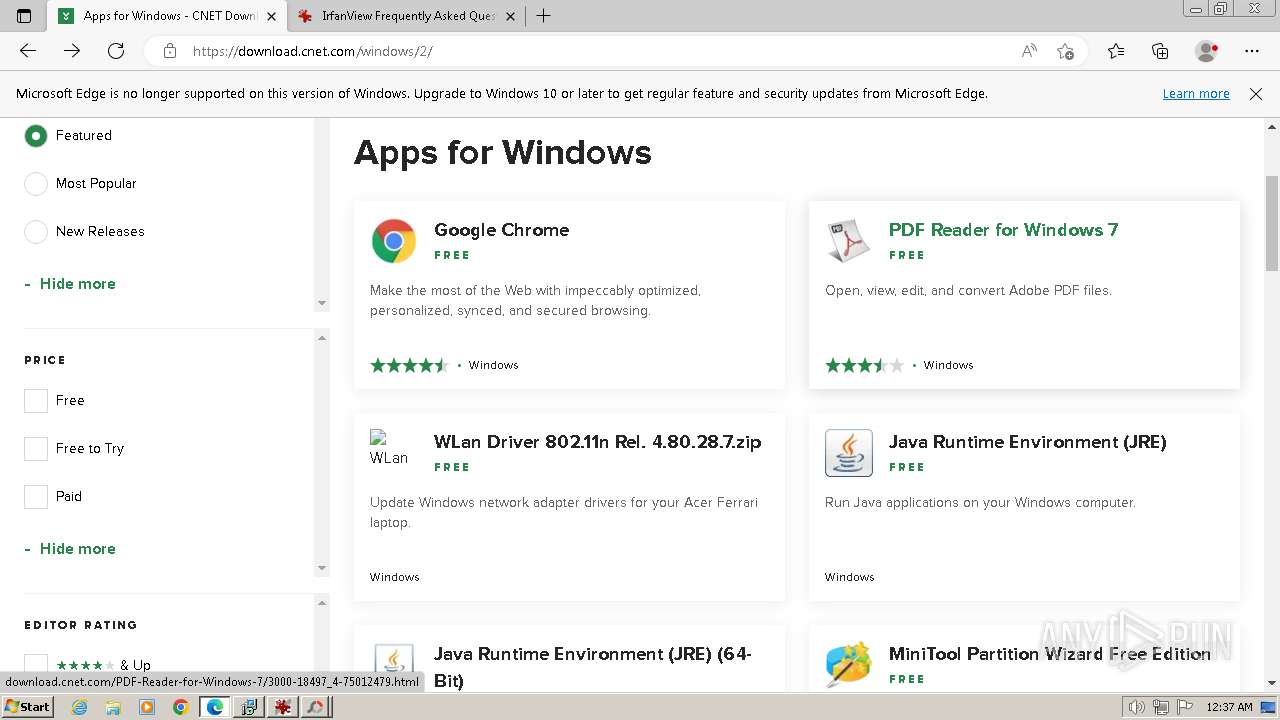
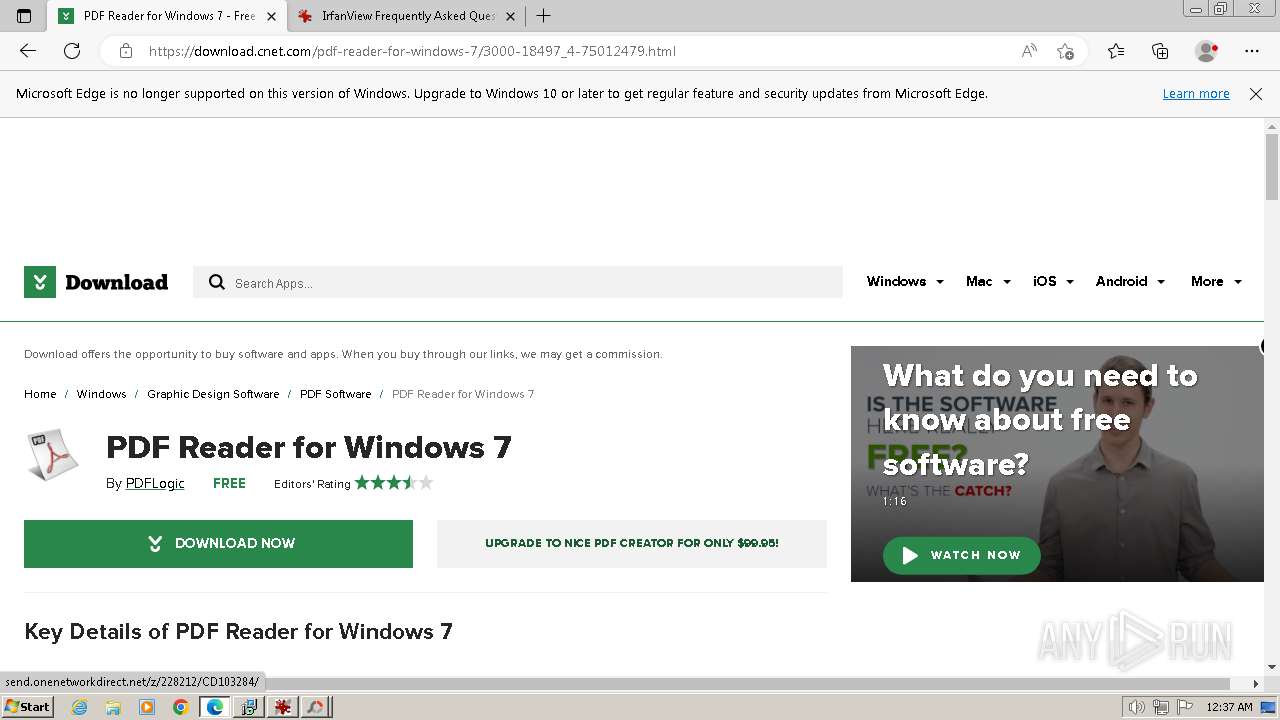
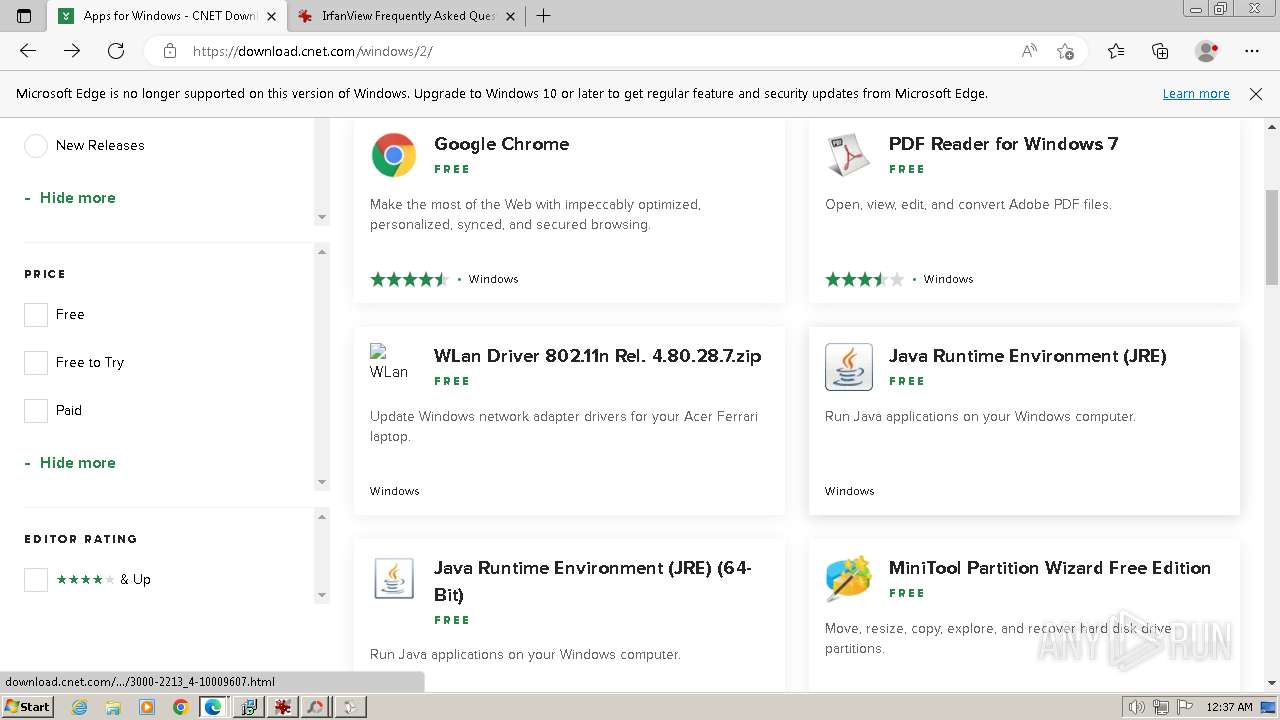
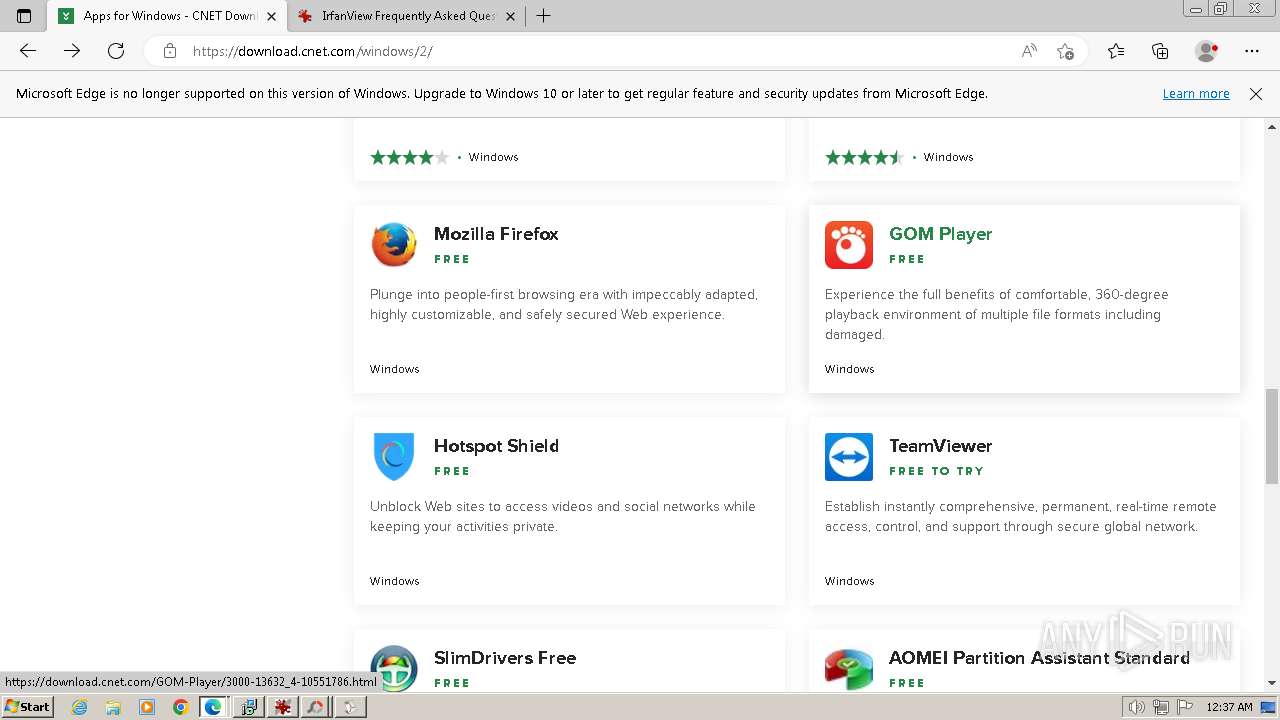
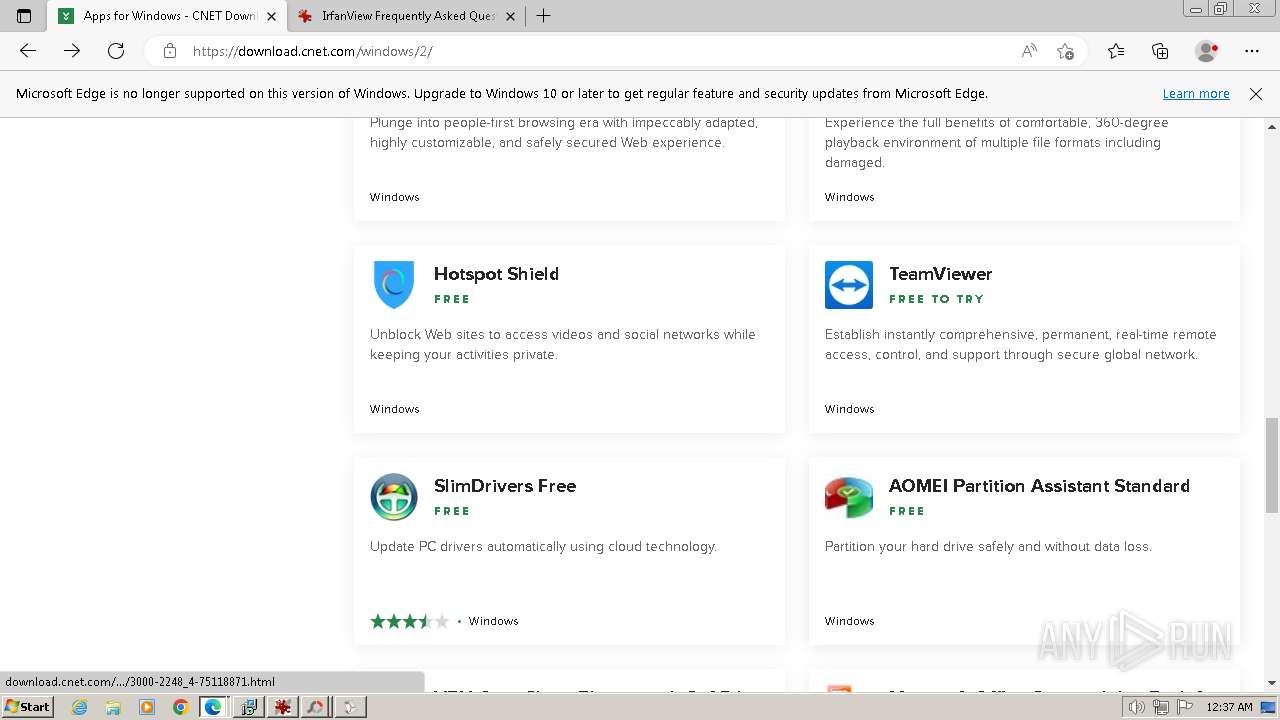
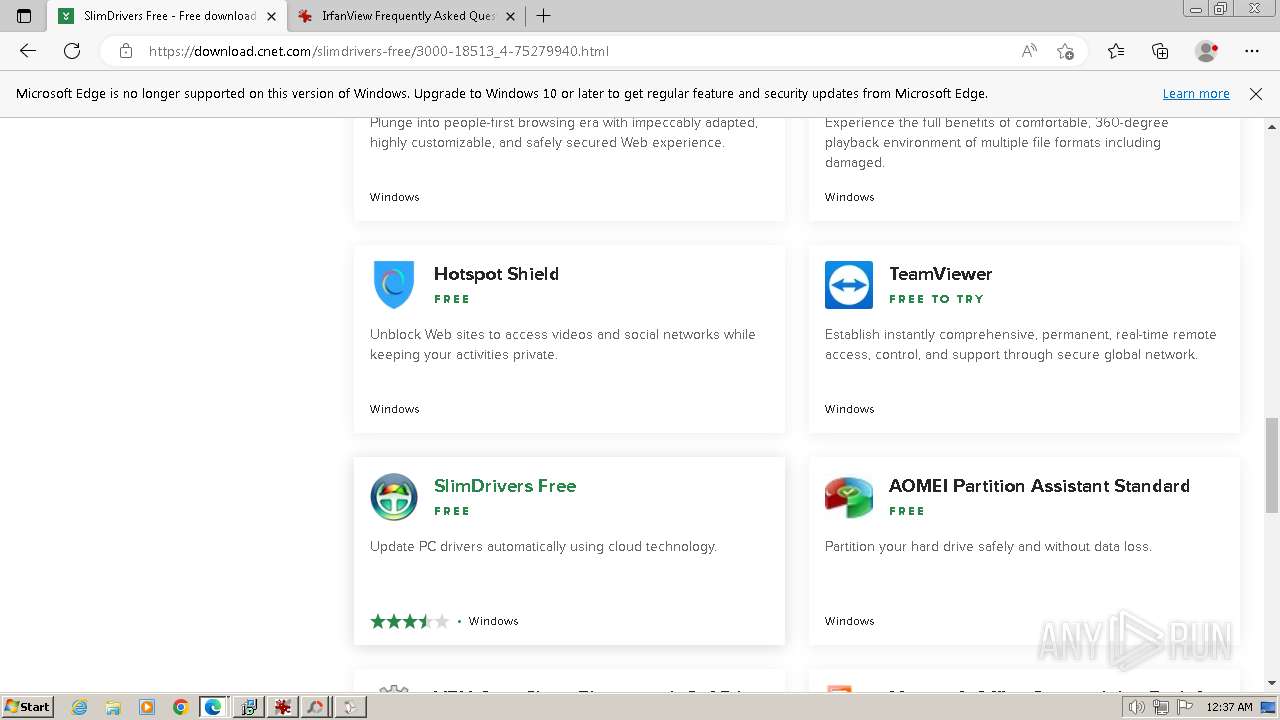
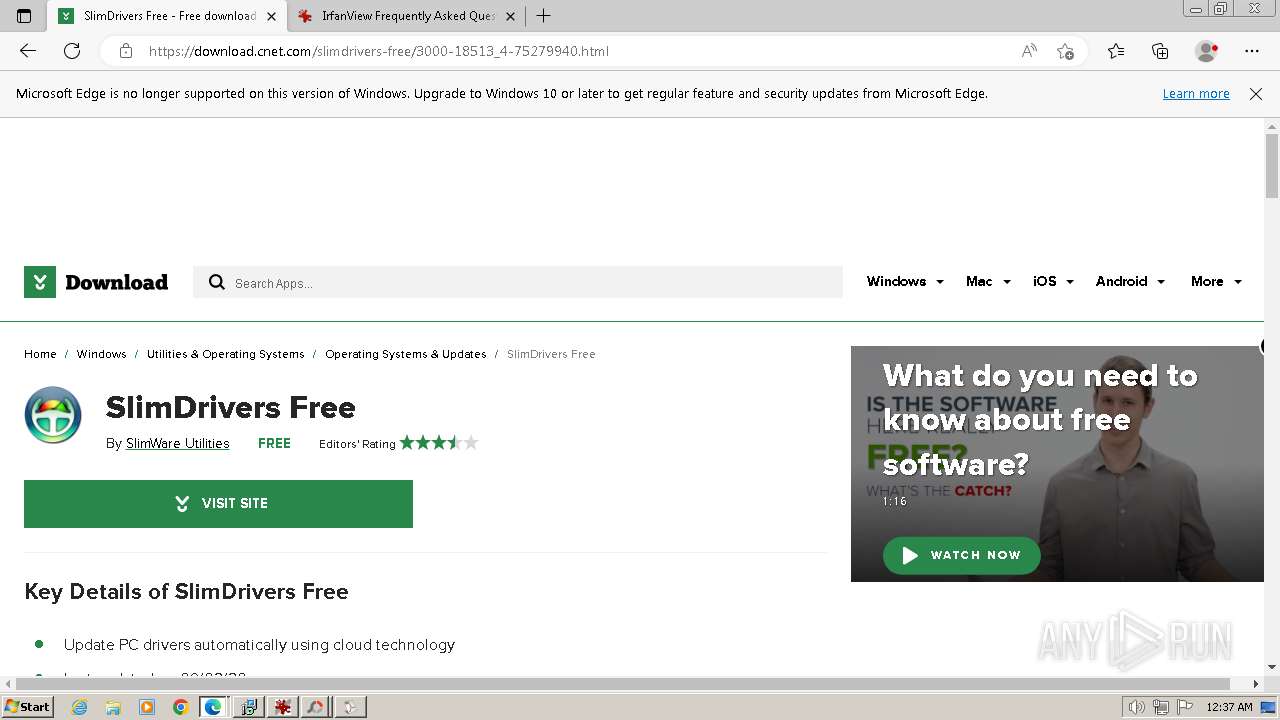
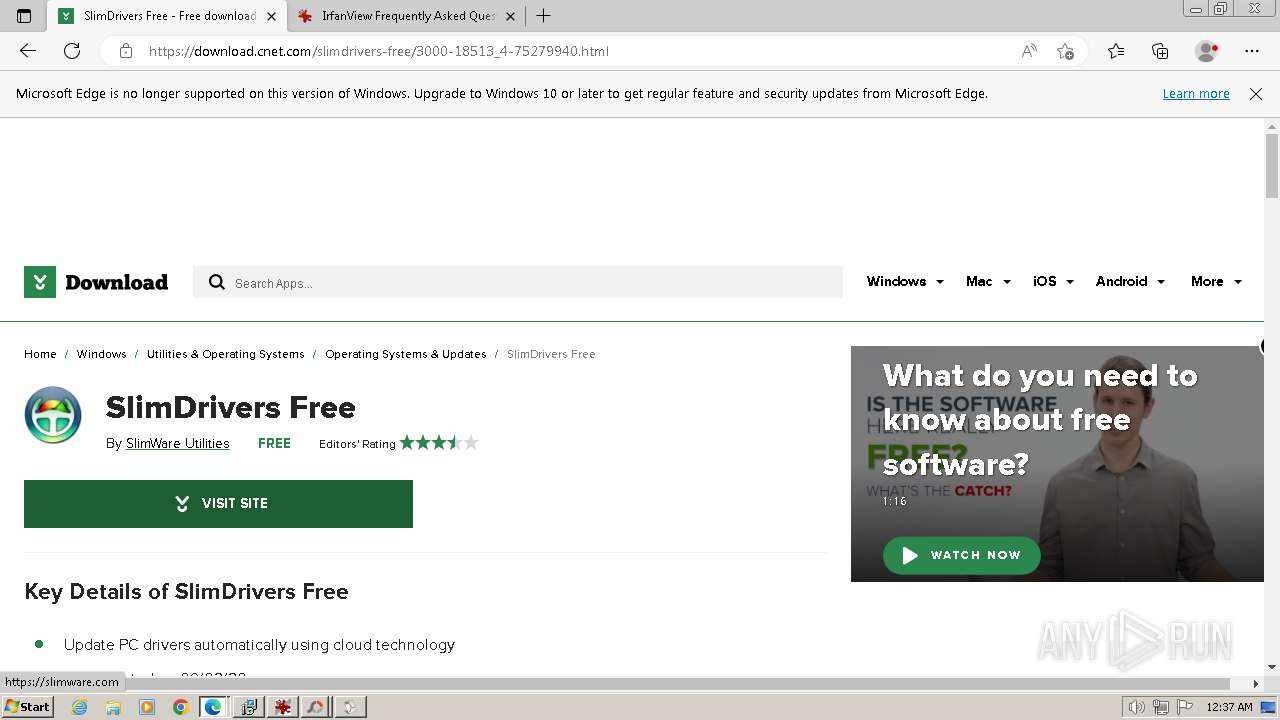
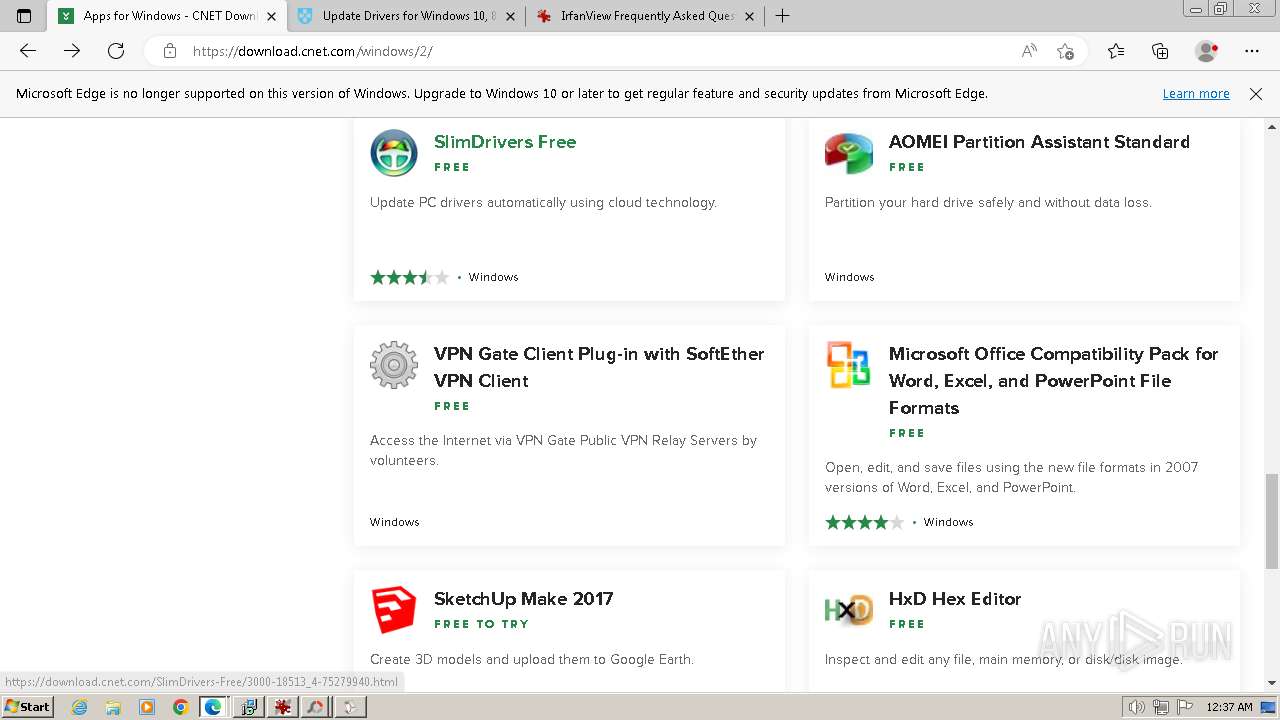
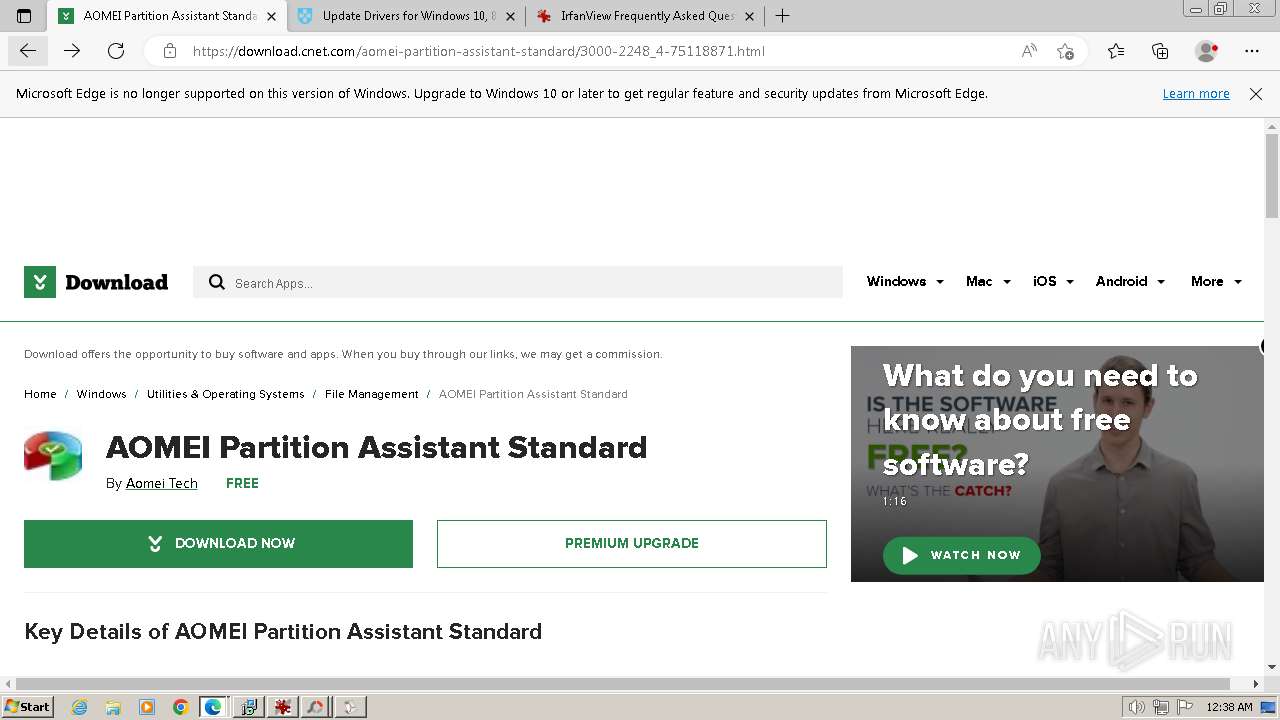
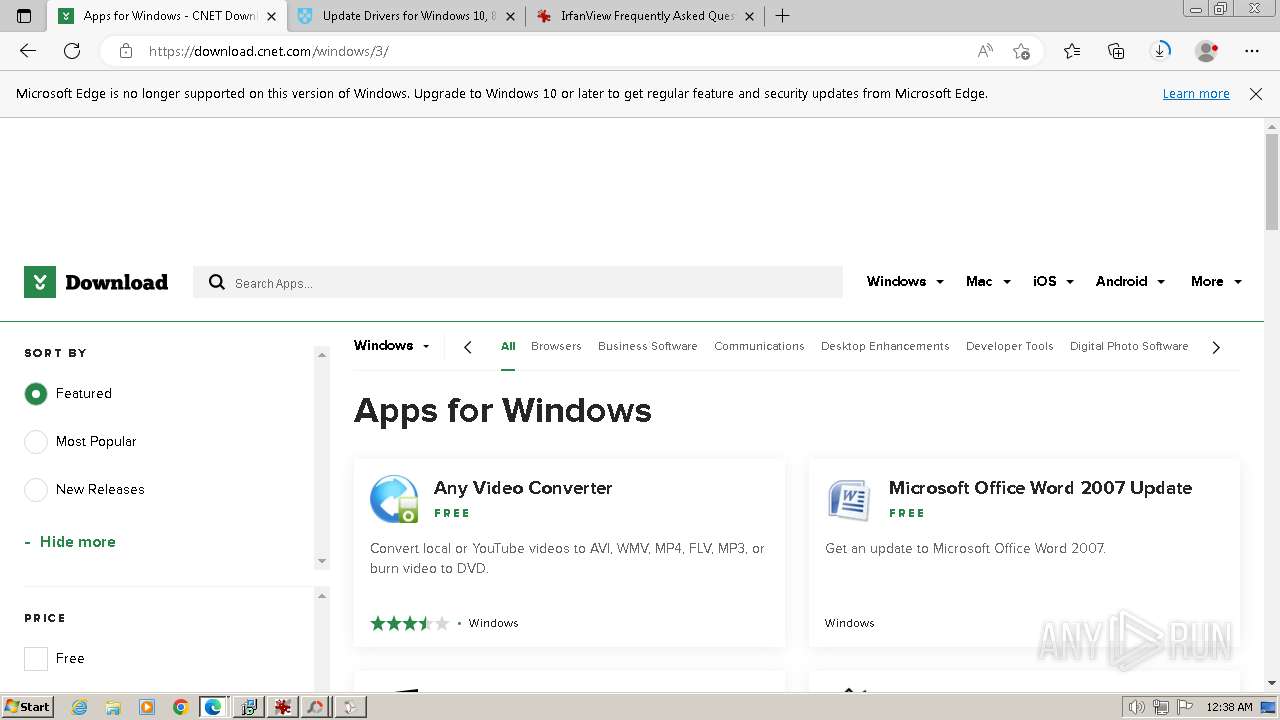
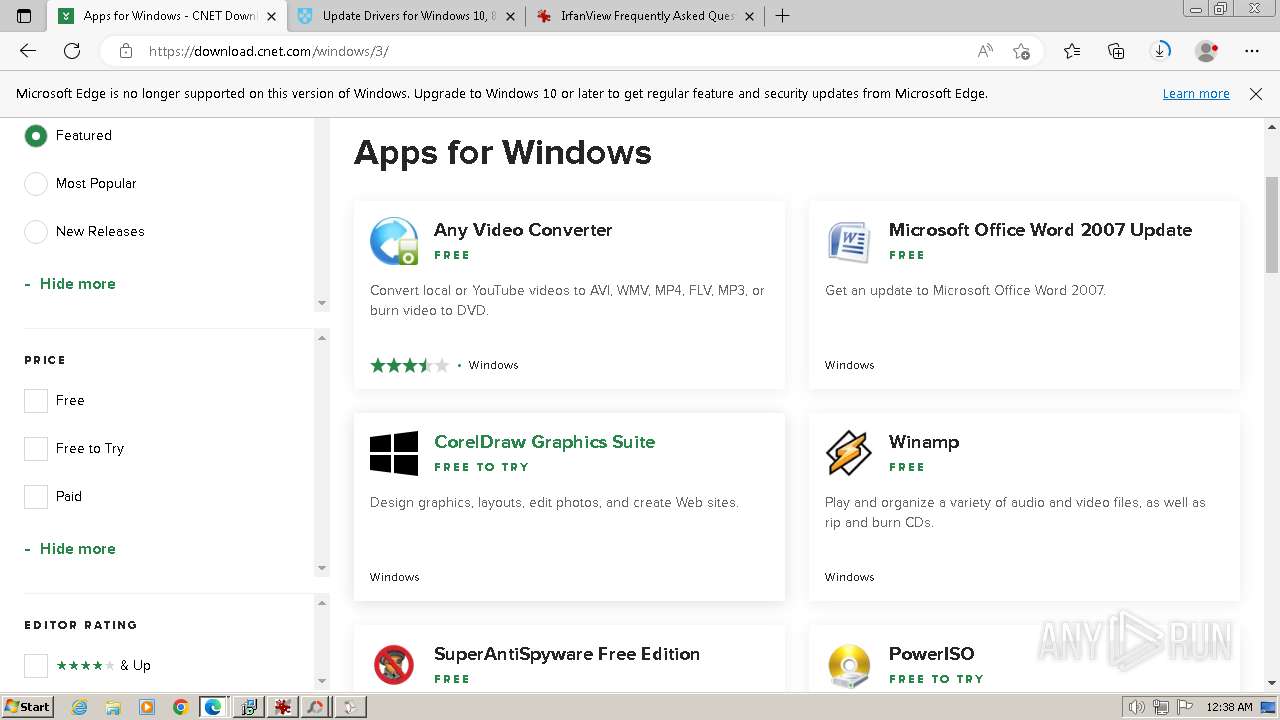
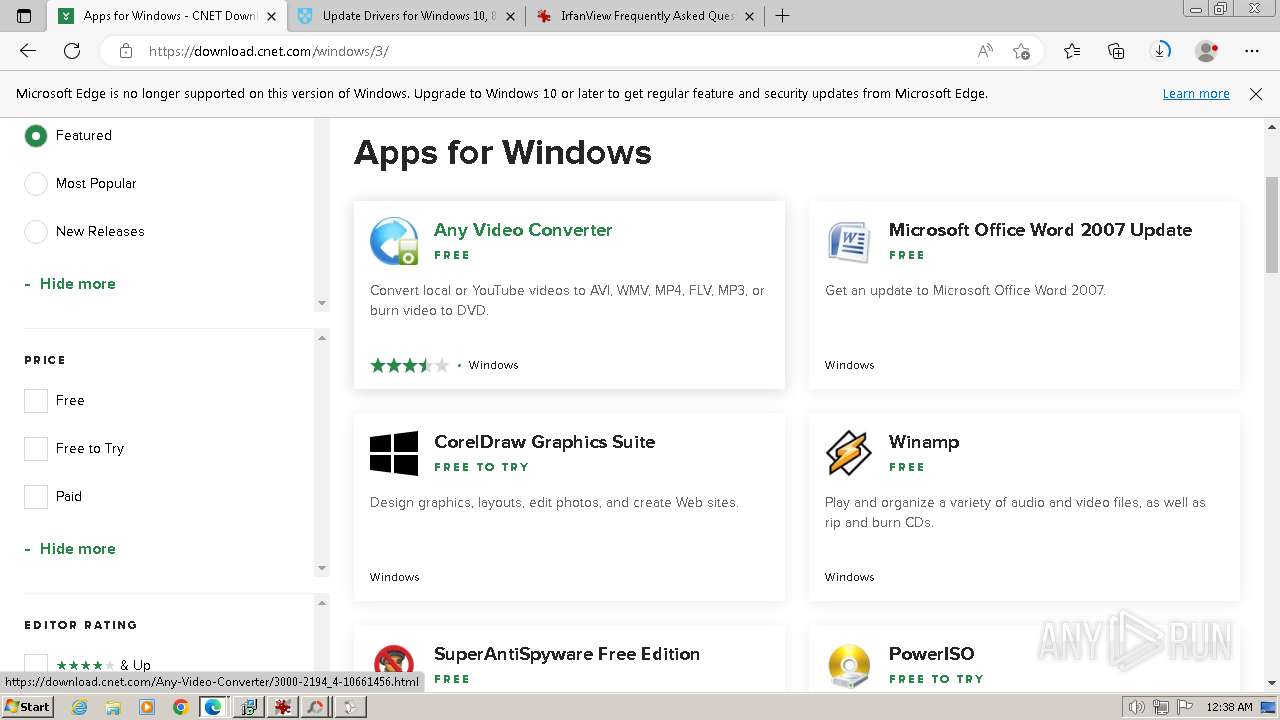
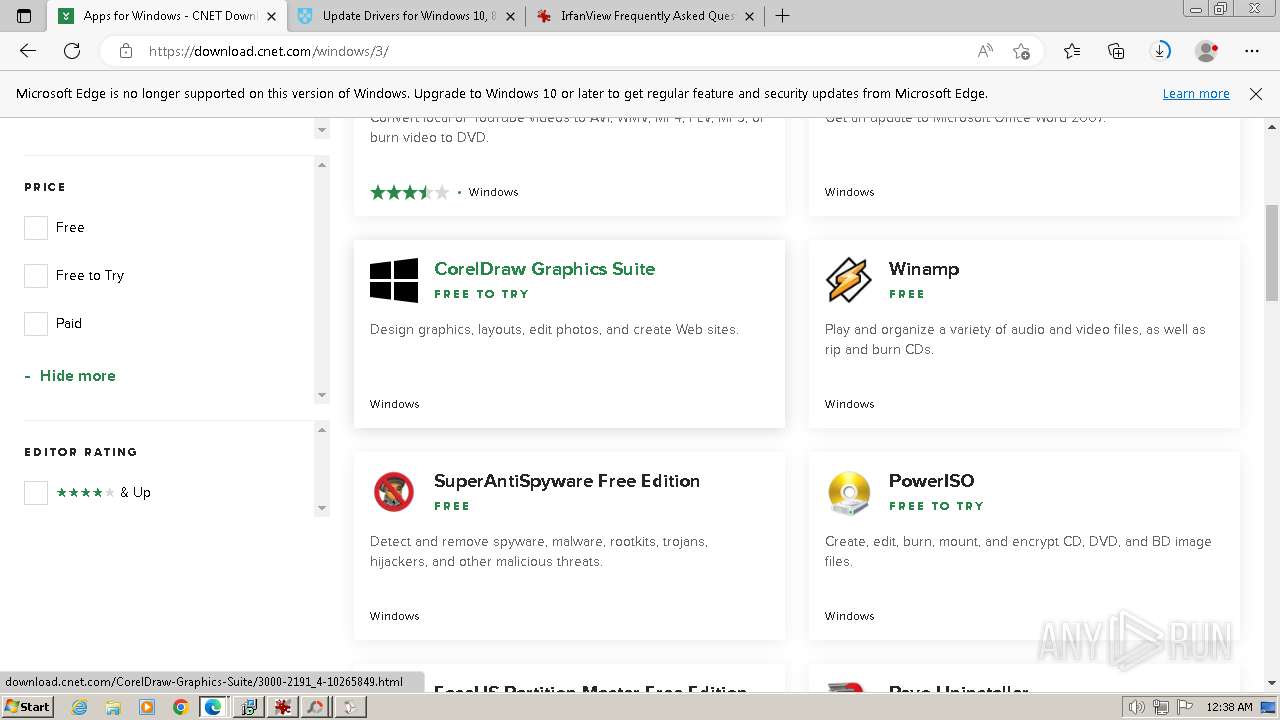
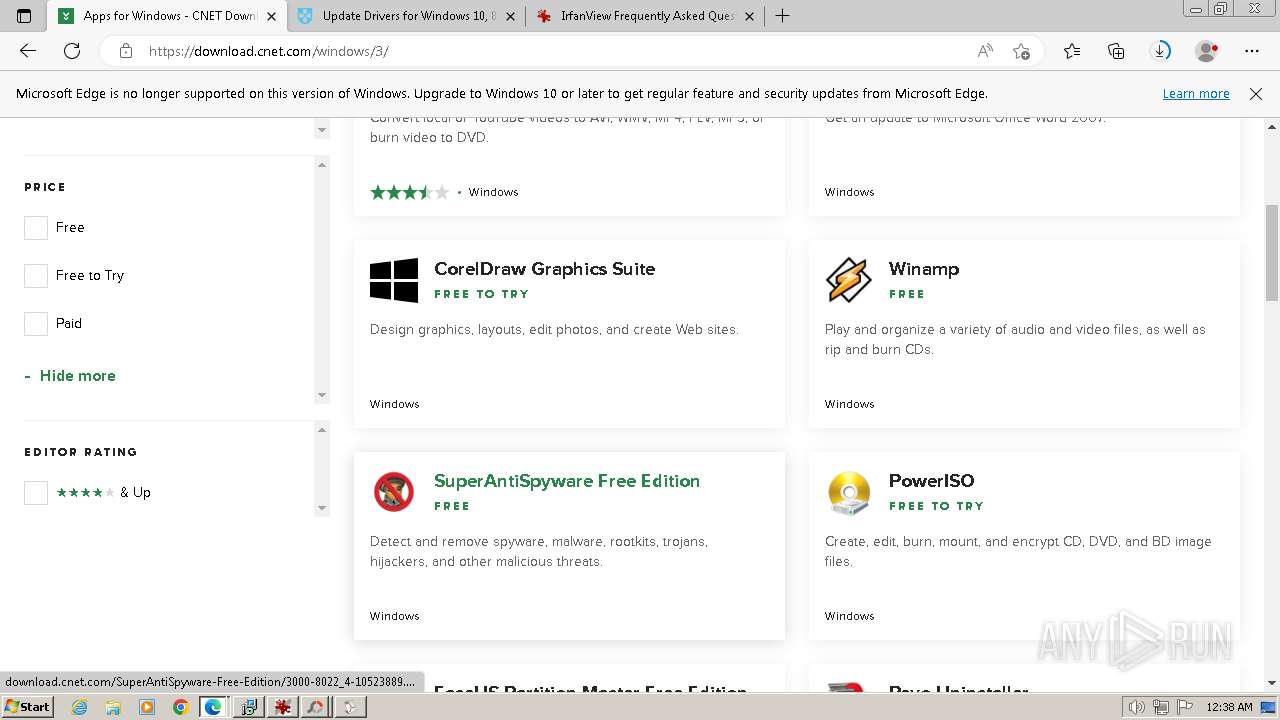
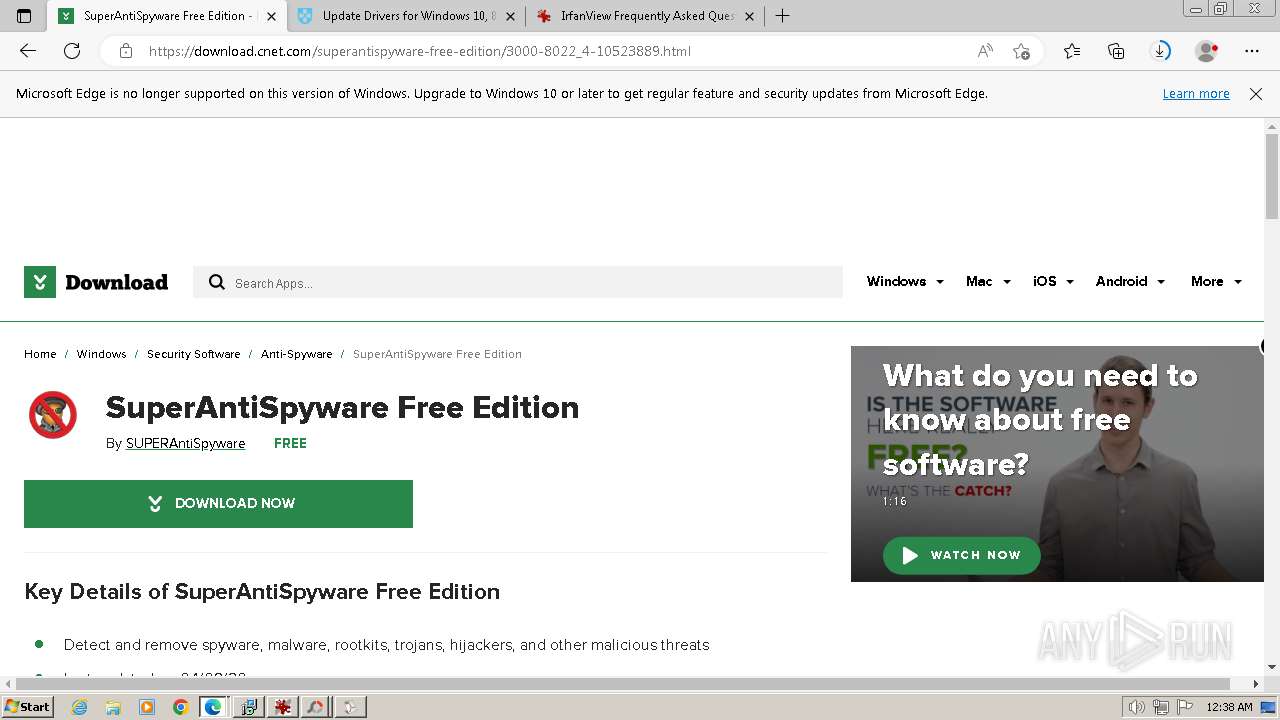
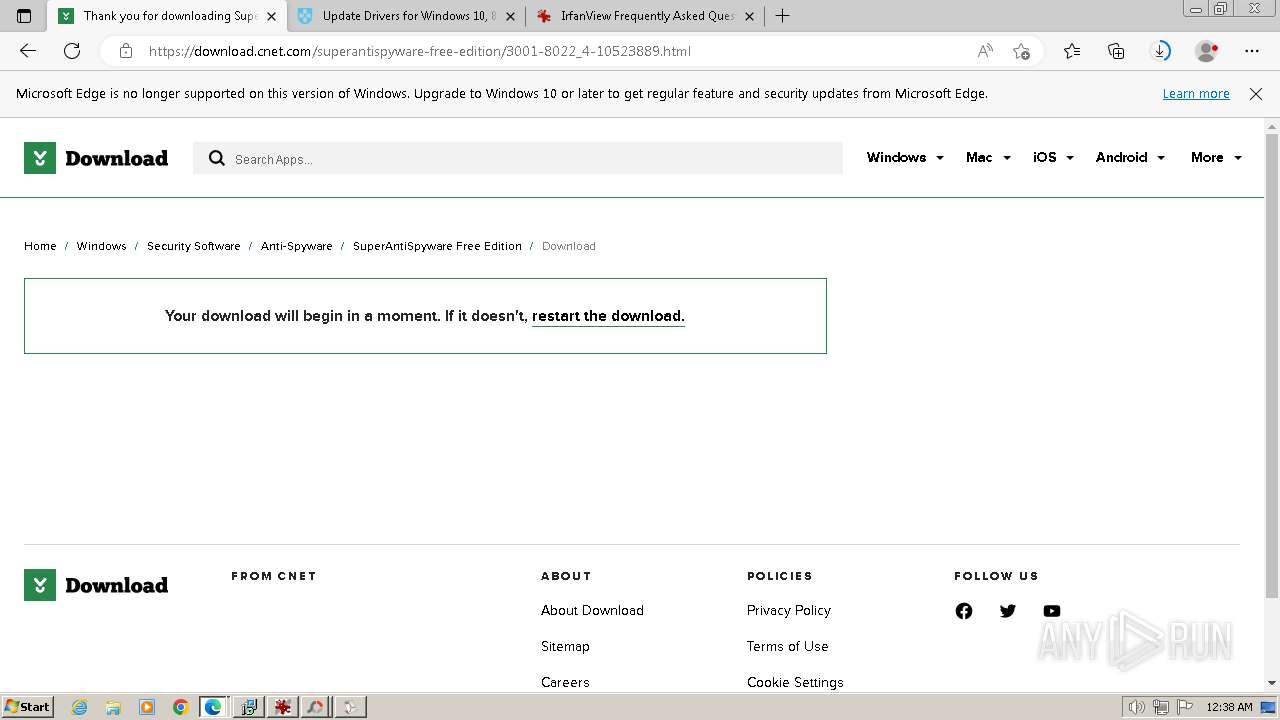
| URL: | download.com |
| Full analysis: | https://app.any.run/tasks/f70476a5-3993-4577-abab-246485176e05 |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2023, 00:34:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C522086C629CFCDE8F1840703045214D |
| SHA1: | CBA7F6FDD5505257049271FEACE4DDD028DBAAE2 |
| SHA256: | 05200EA3FAB111423B17CF0A4B8E1C86845961C535ED12A4D995EE729AF03BB0 |
| SSDEEP: | 3:ZKWKn:ZlKn |
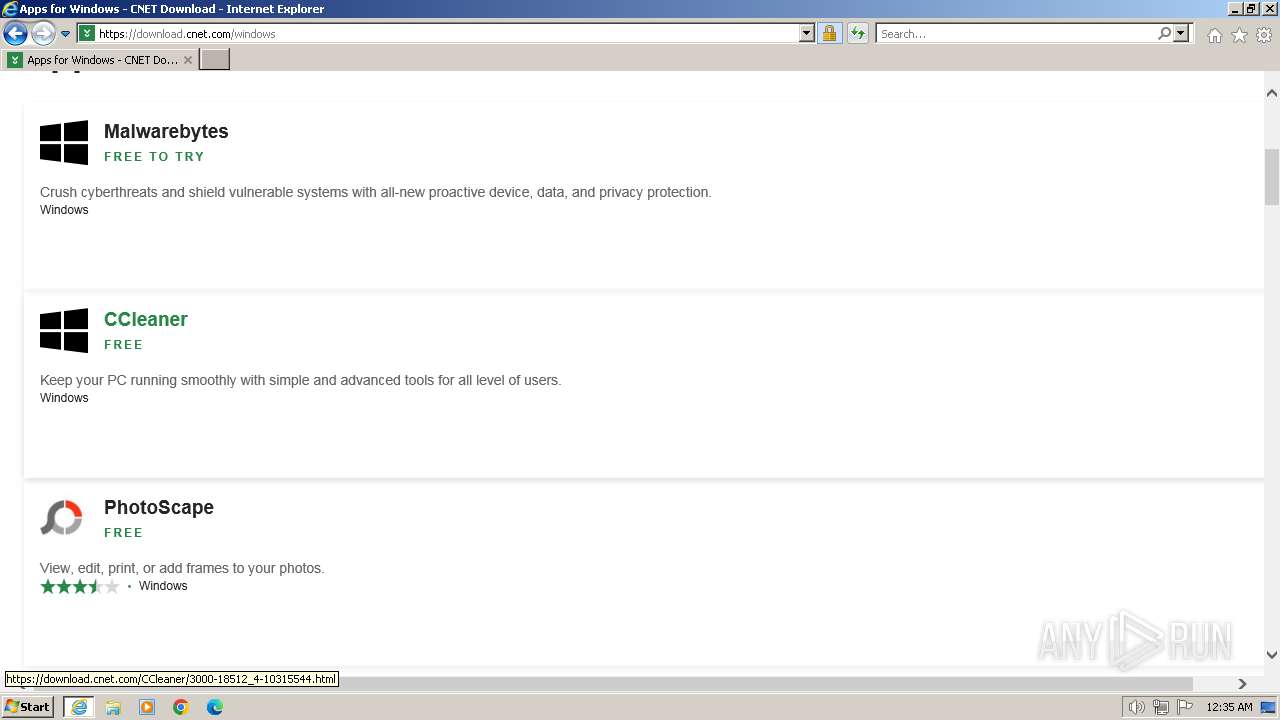
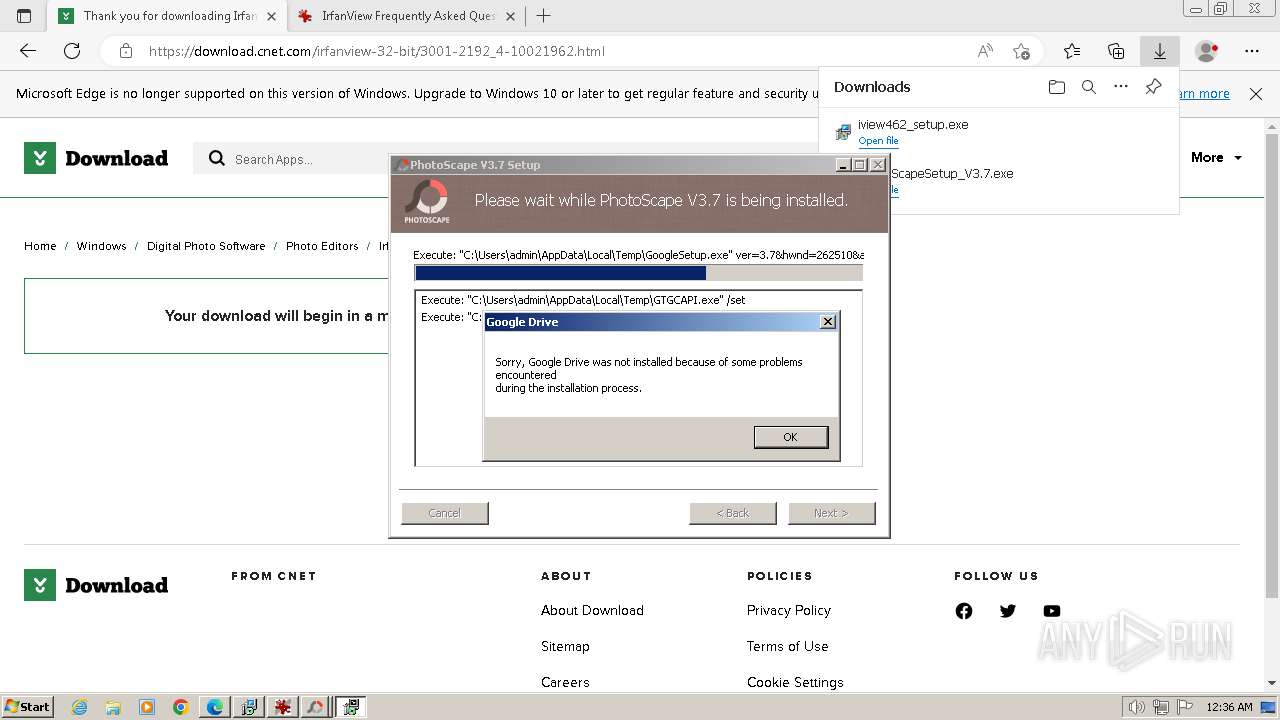
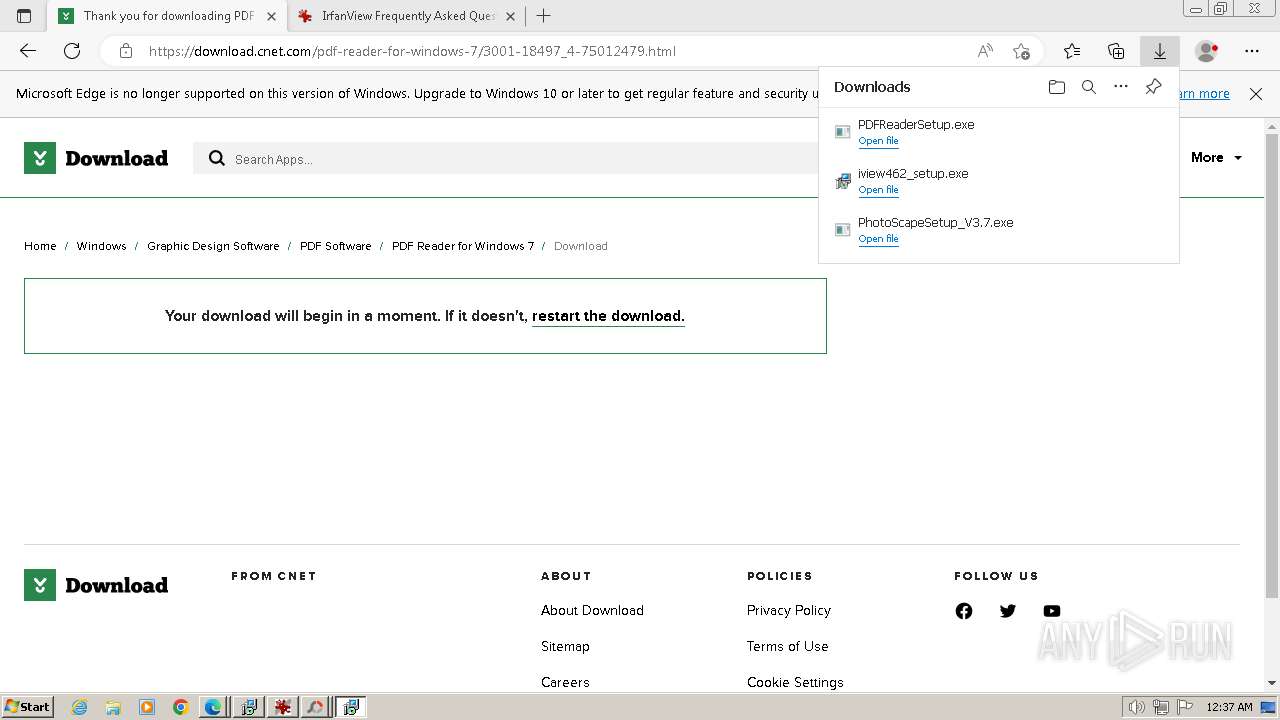
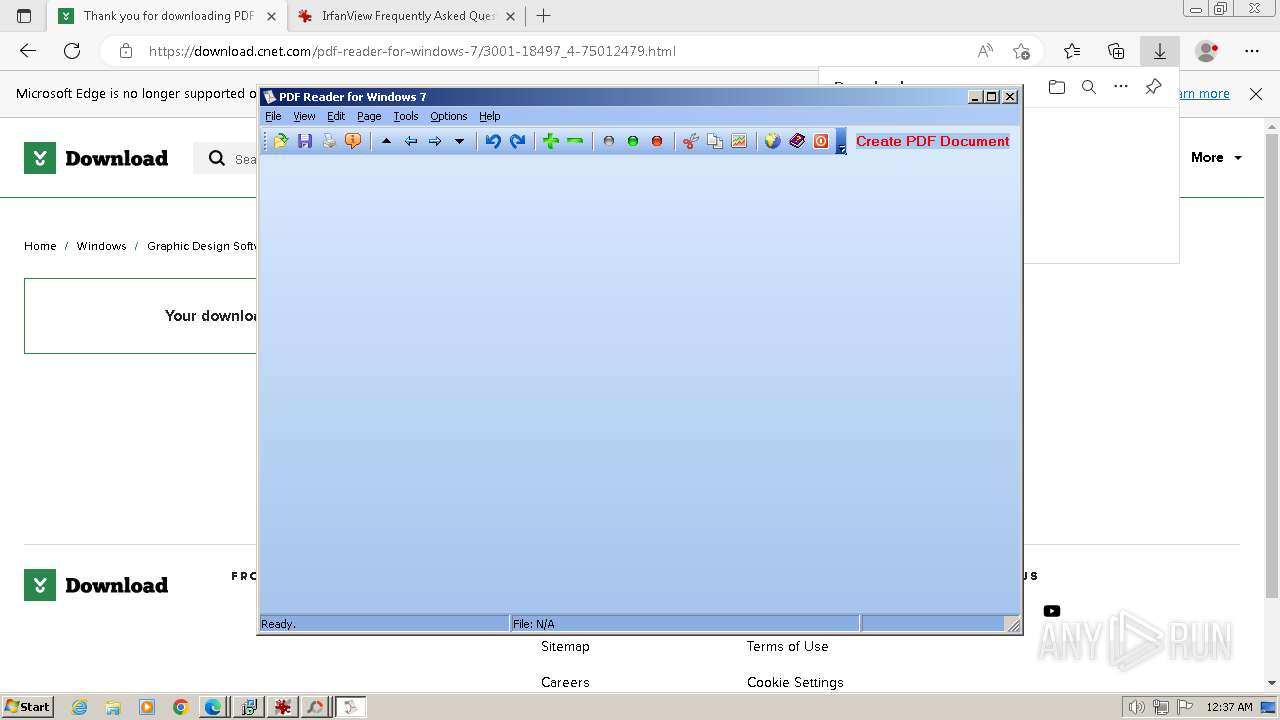
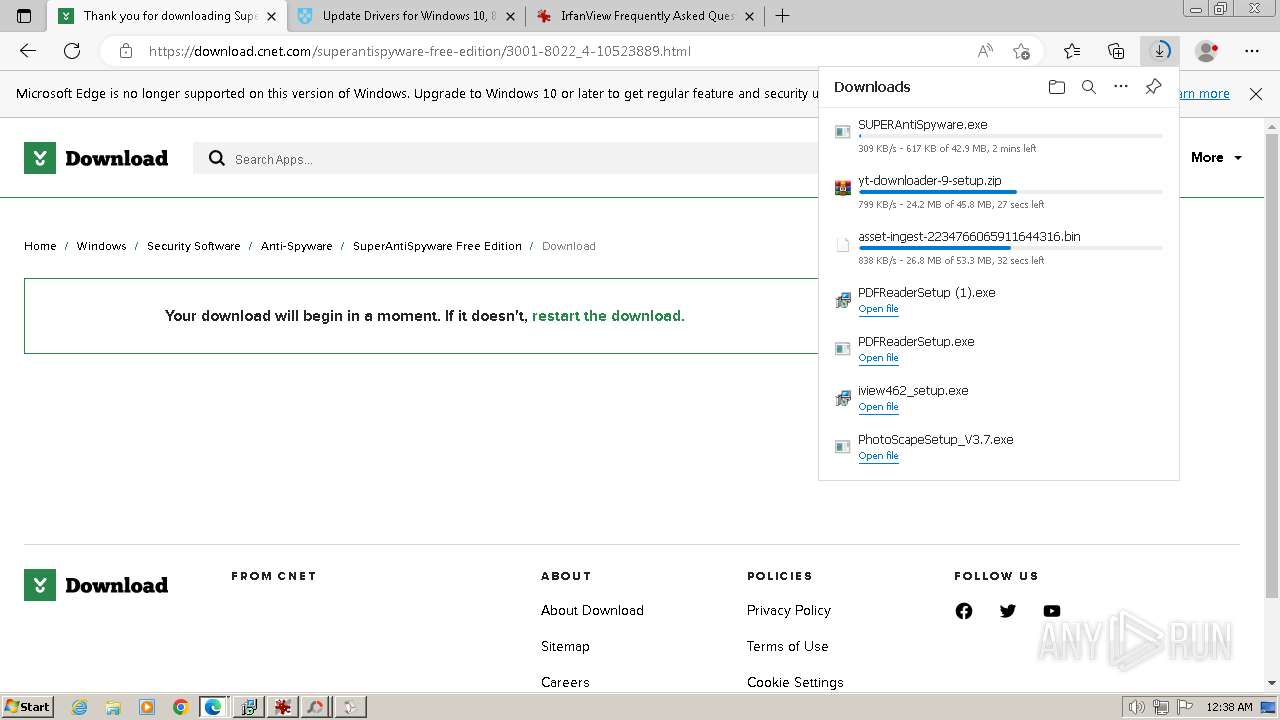
MALICIOUS
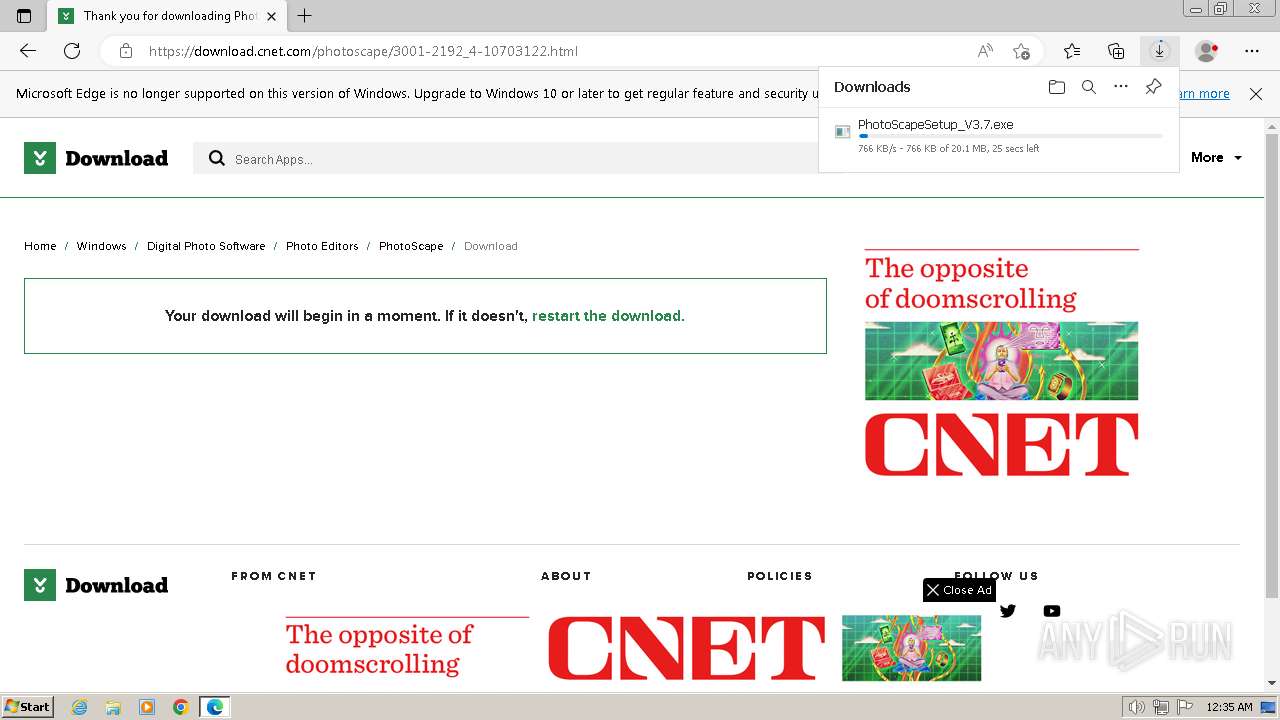
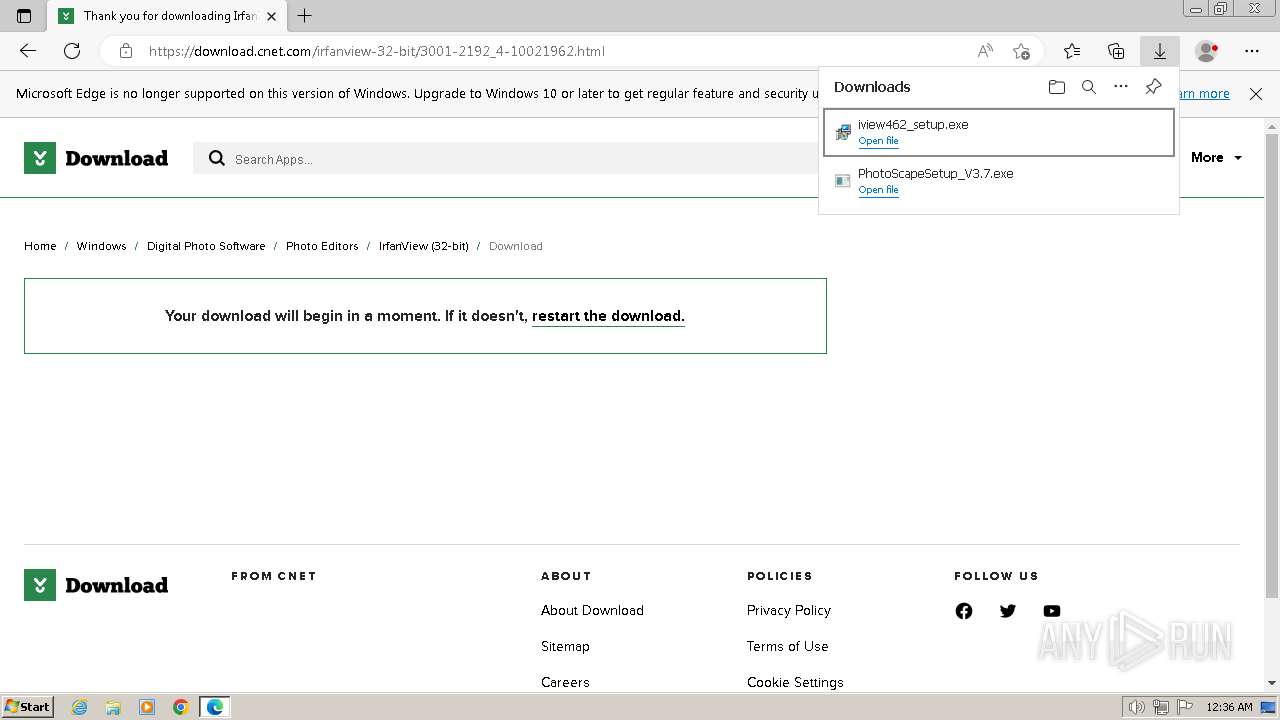
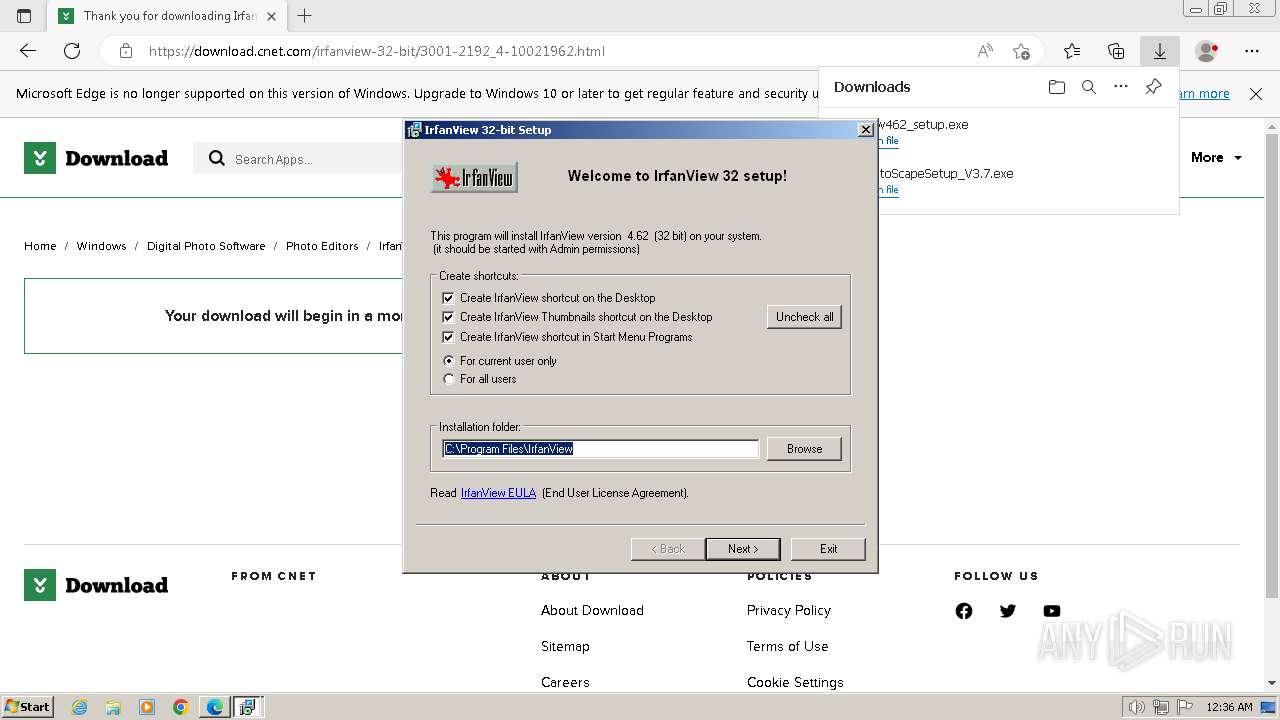
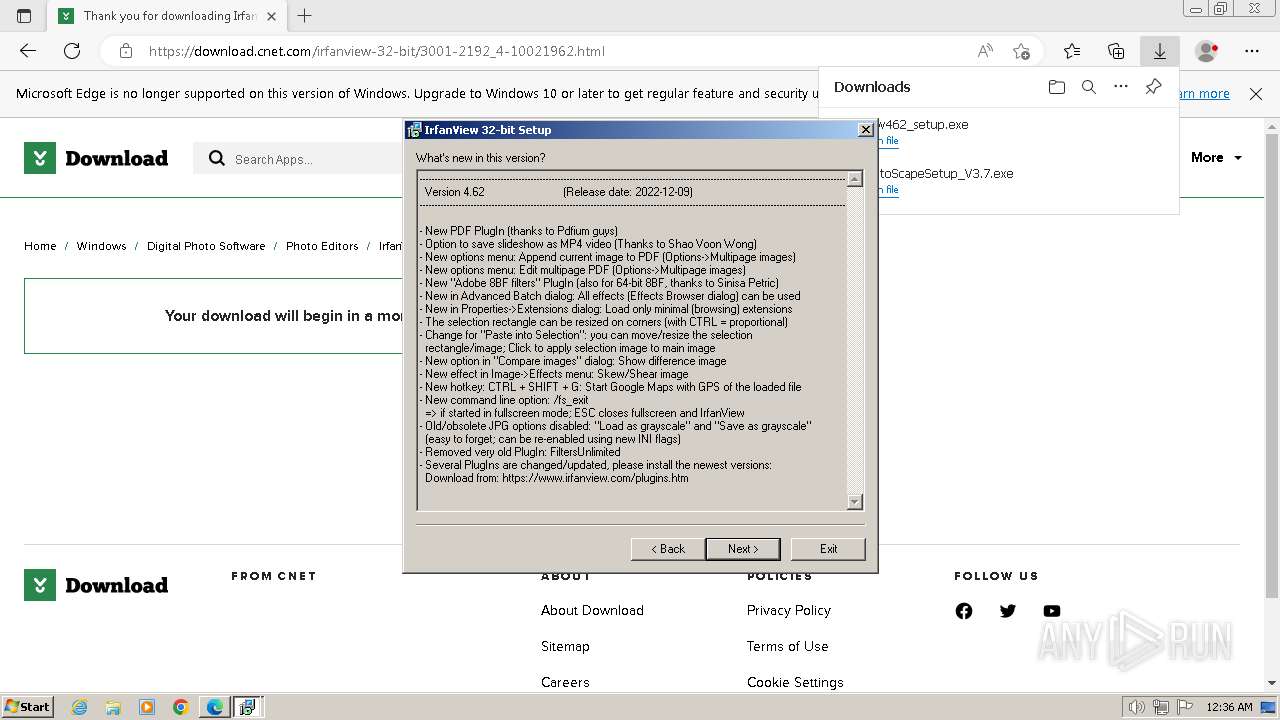
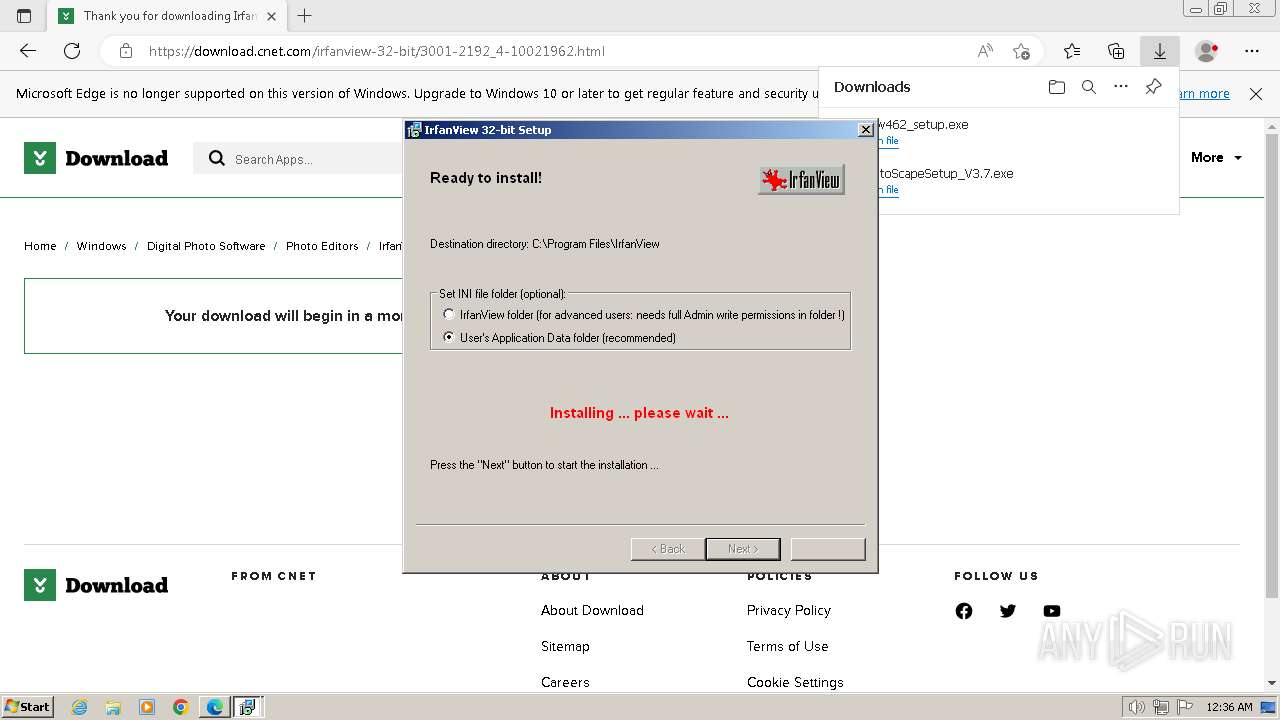
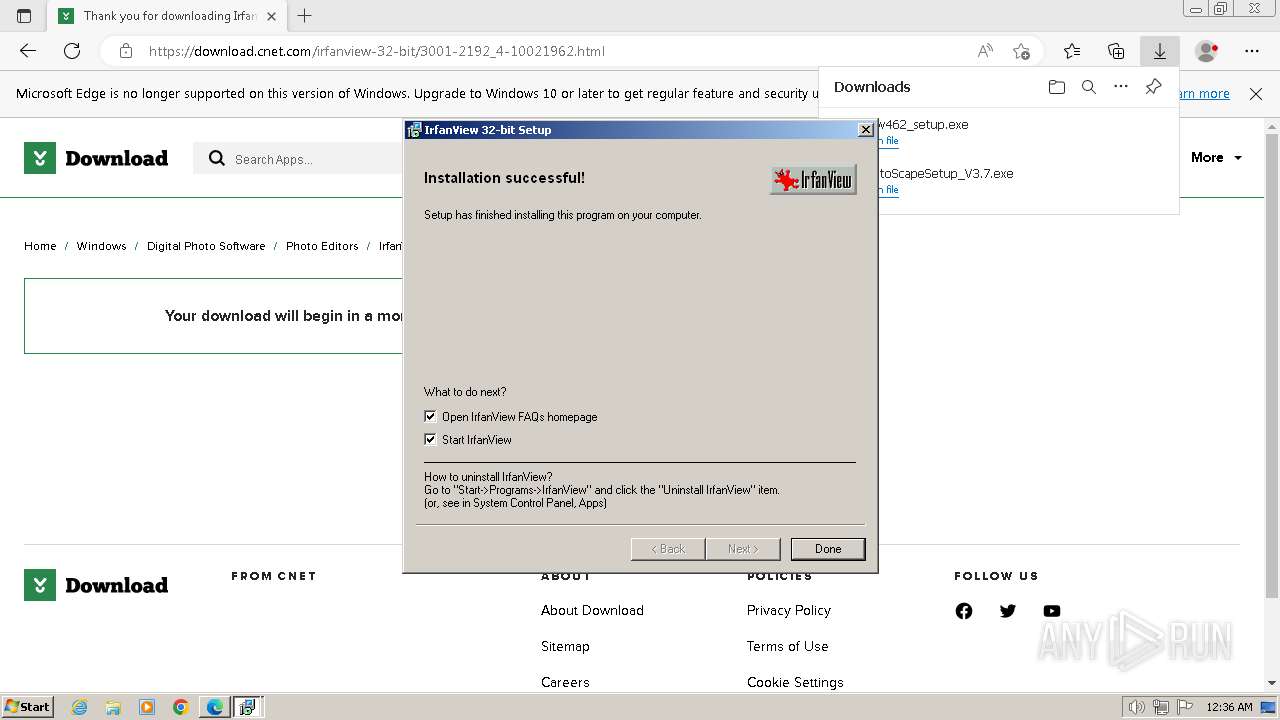
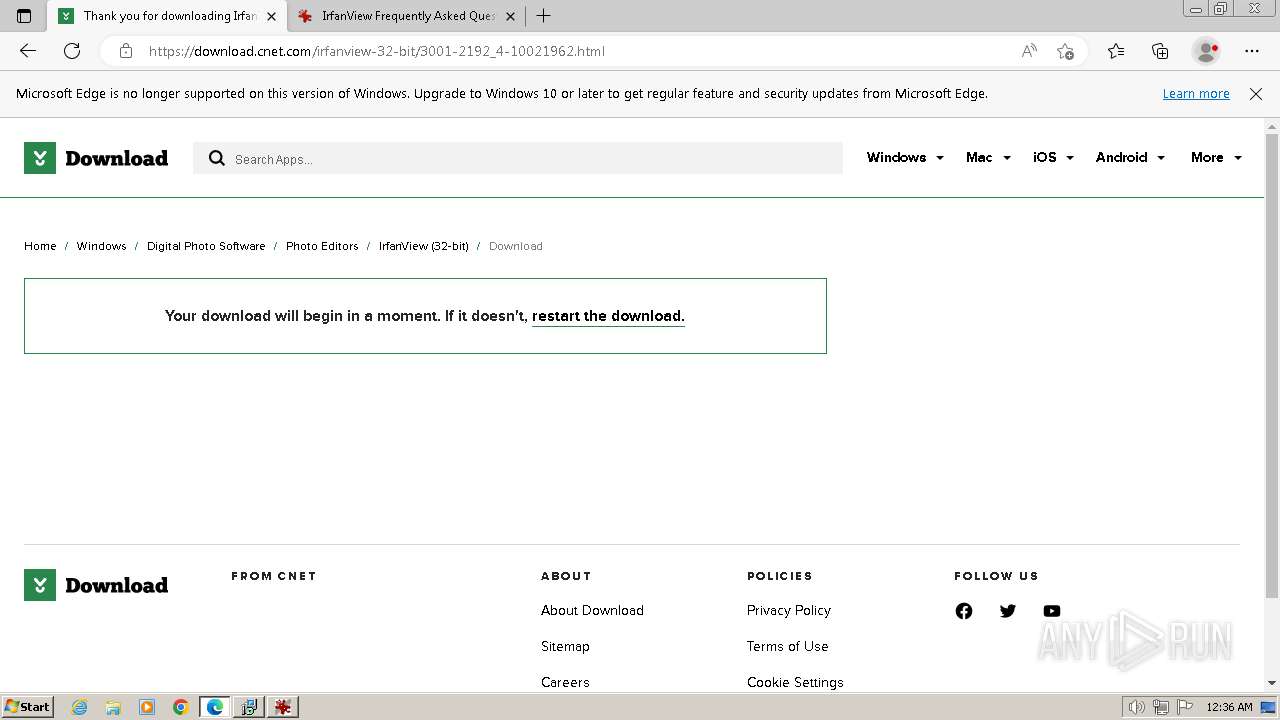
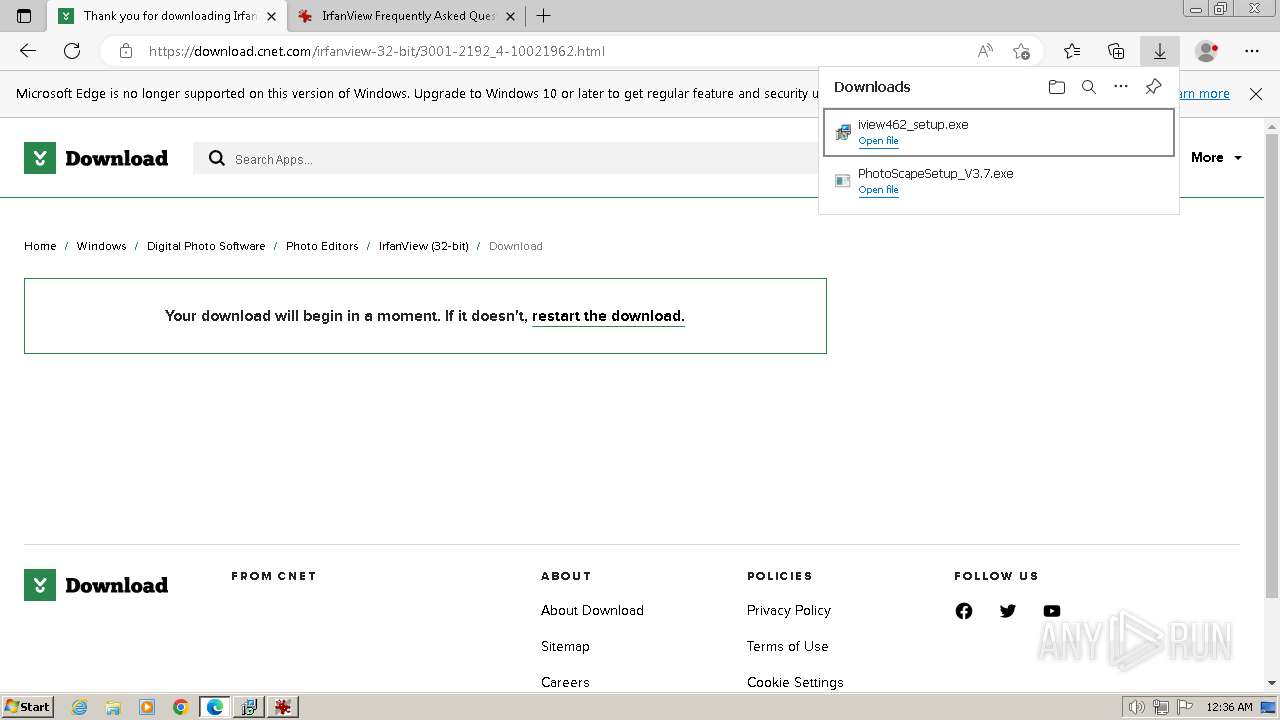
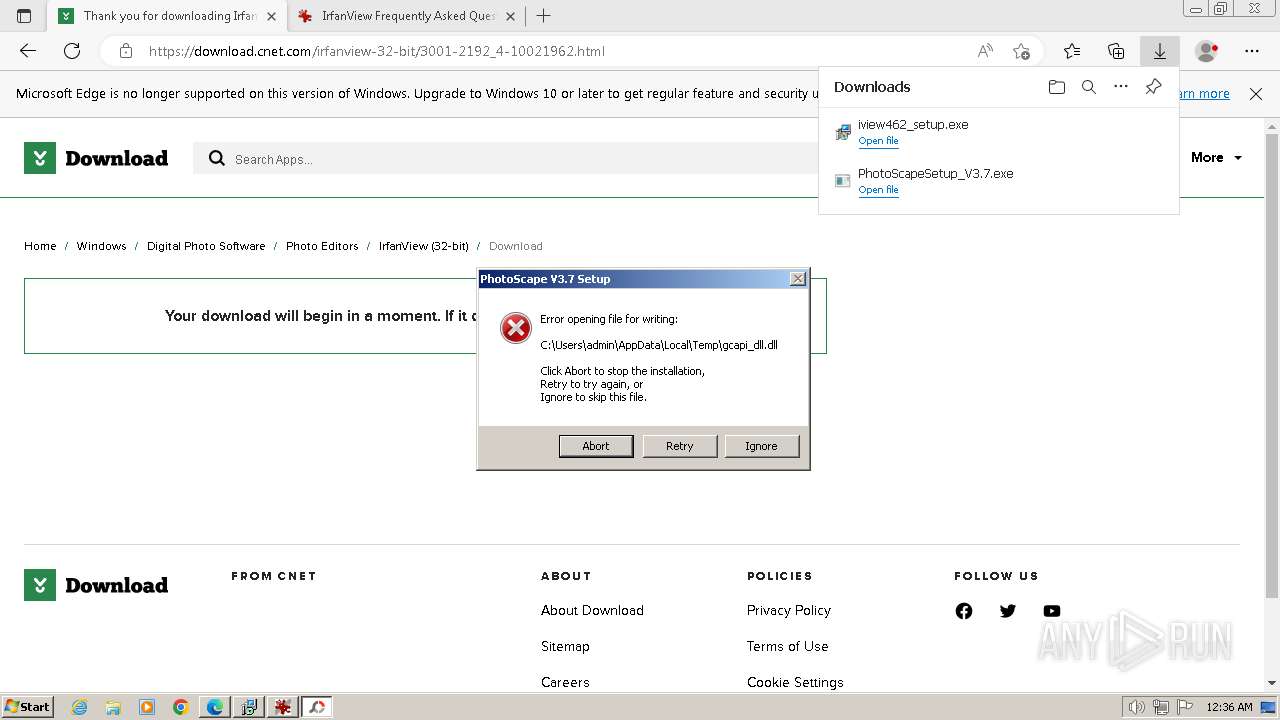
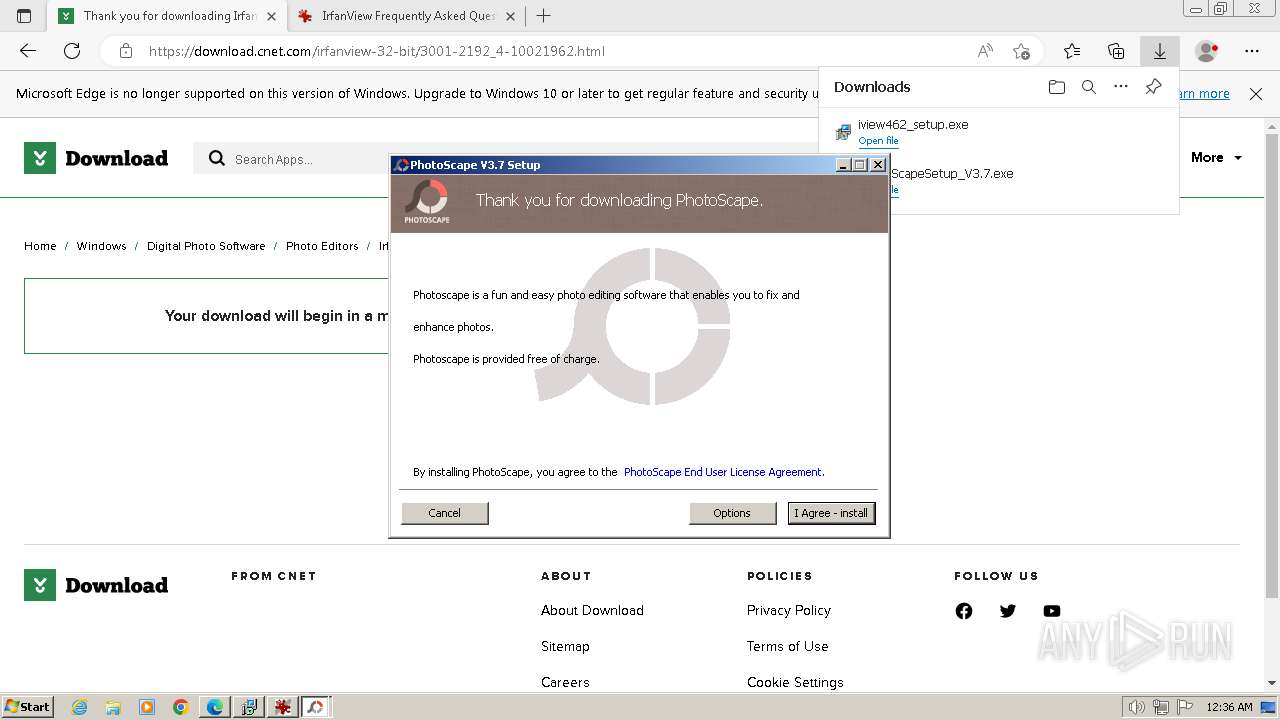
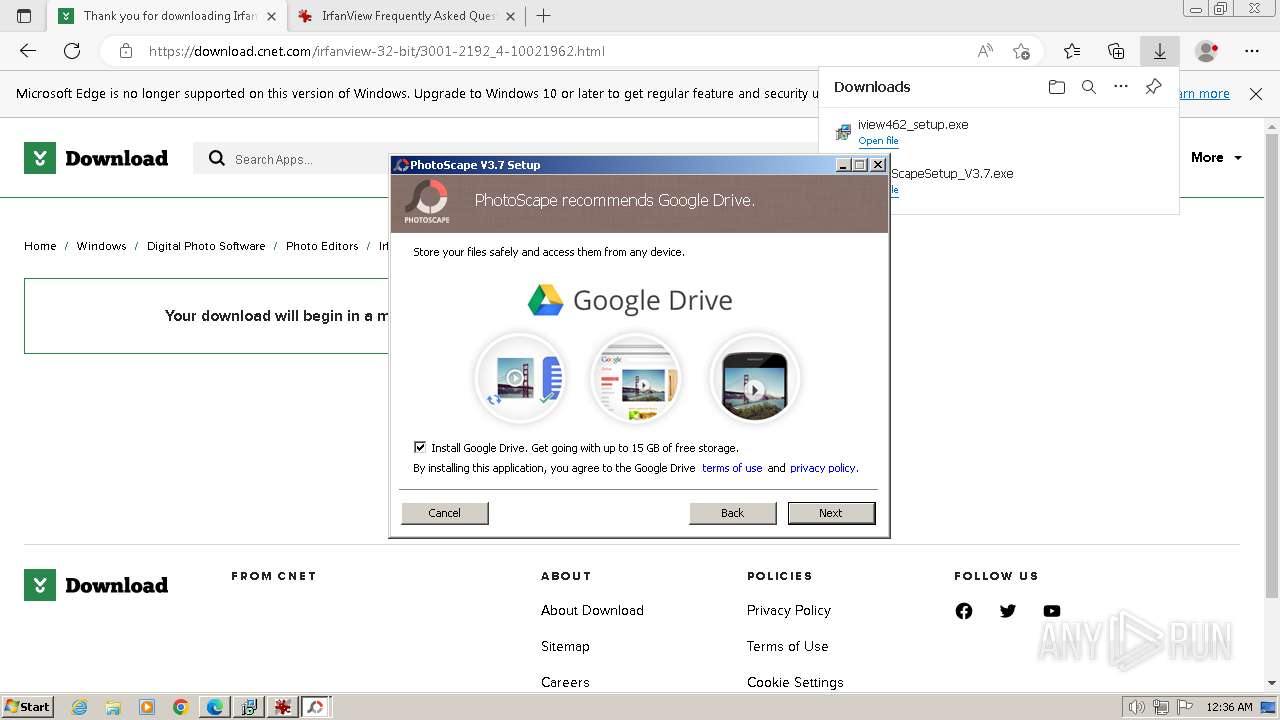
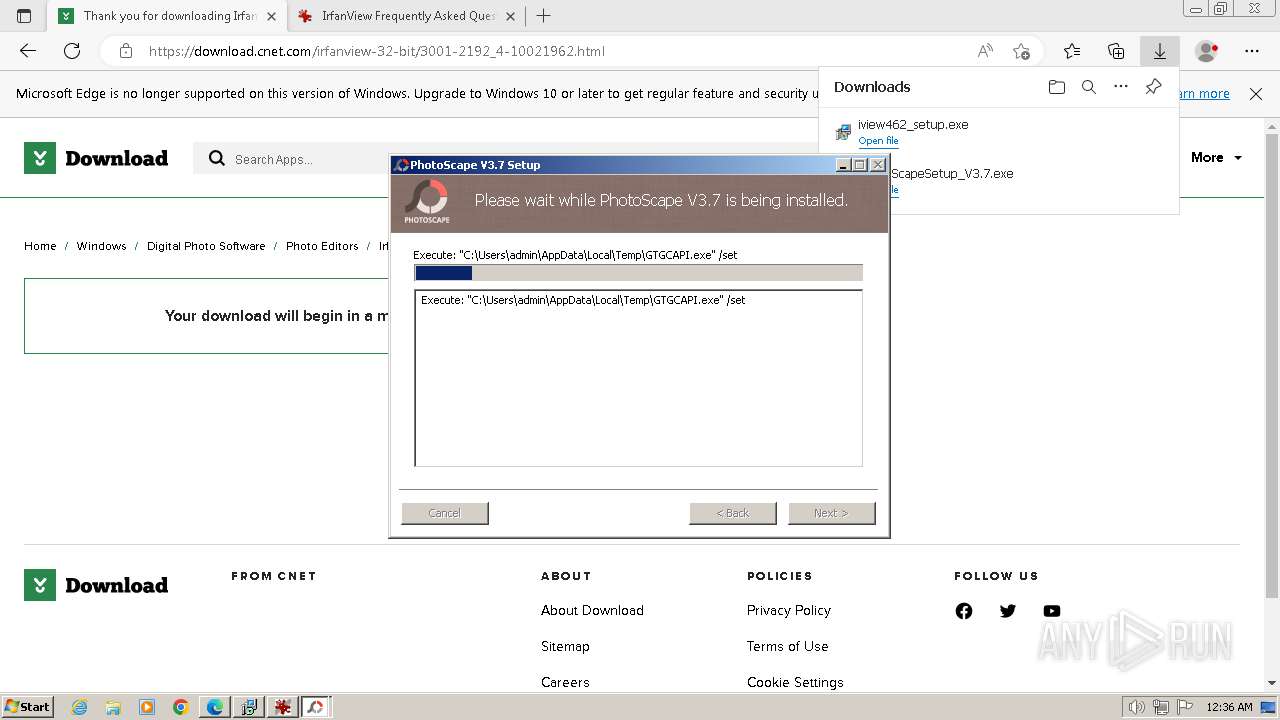
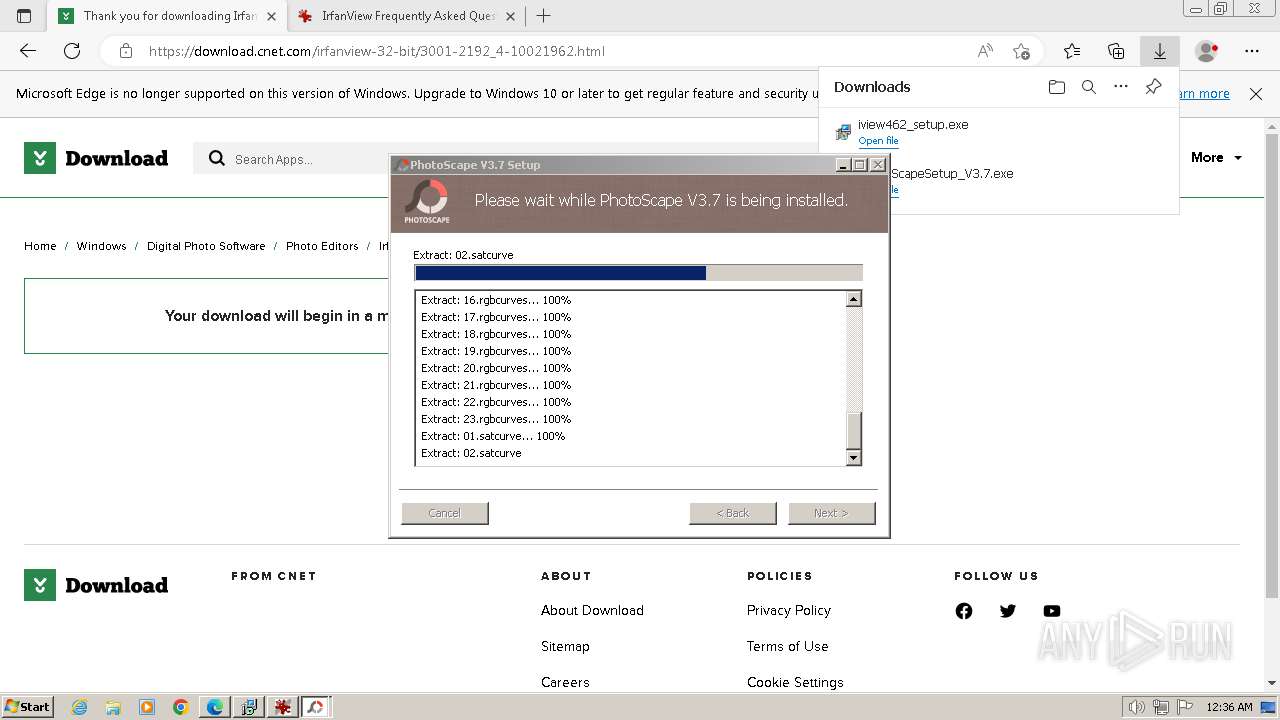
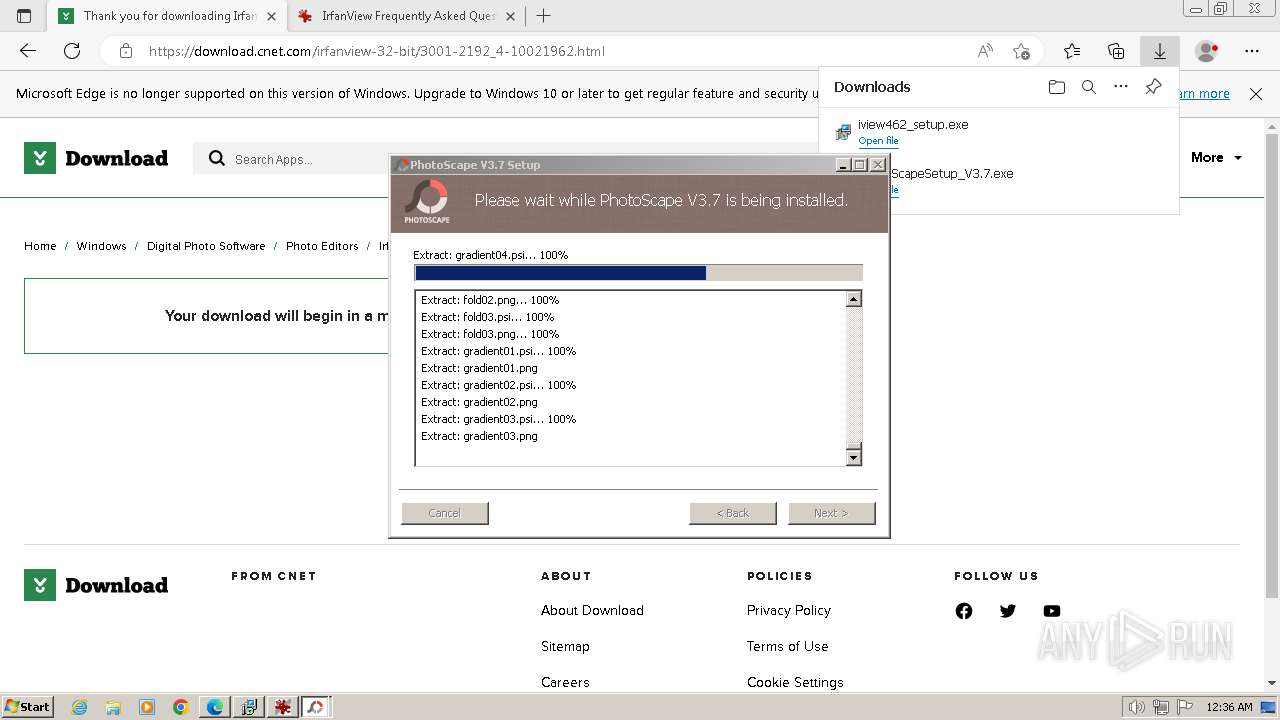
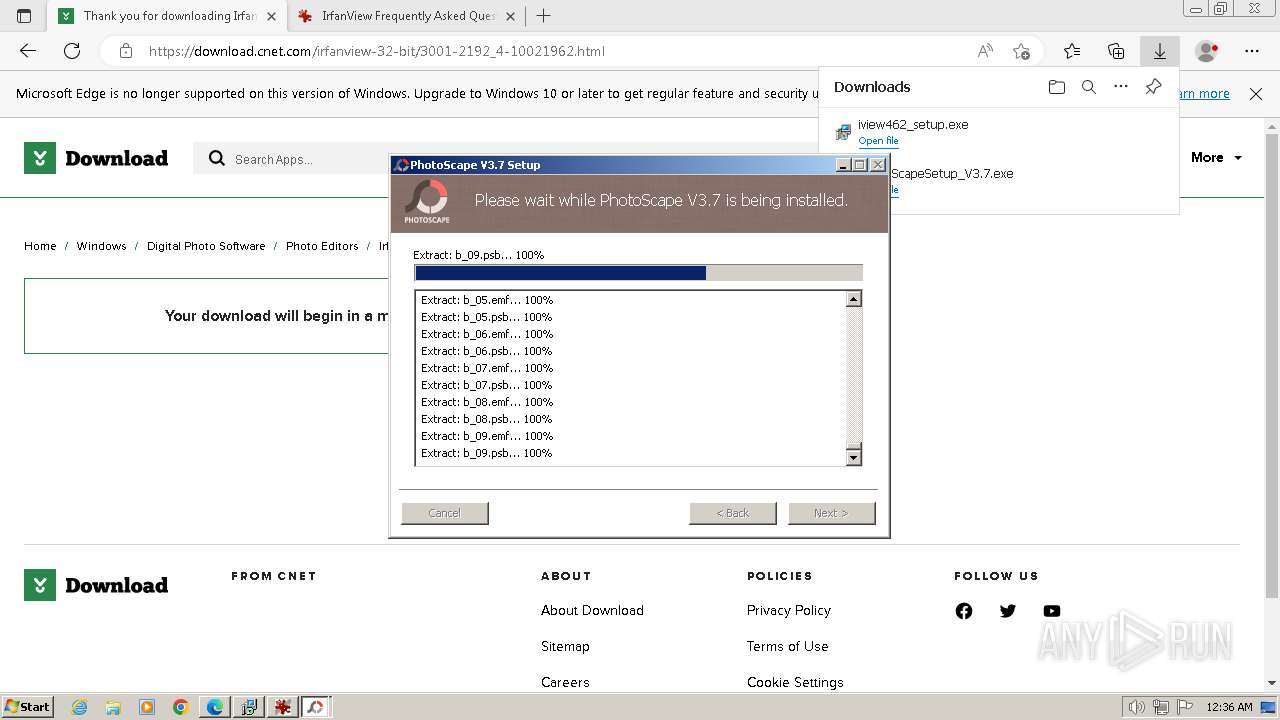
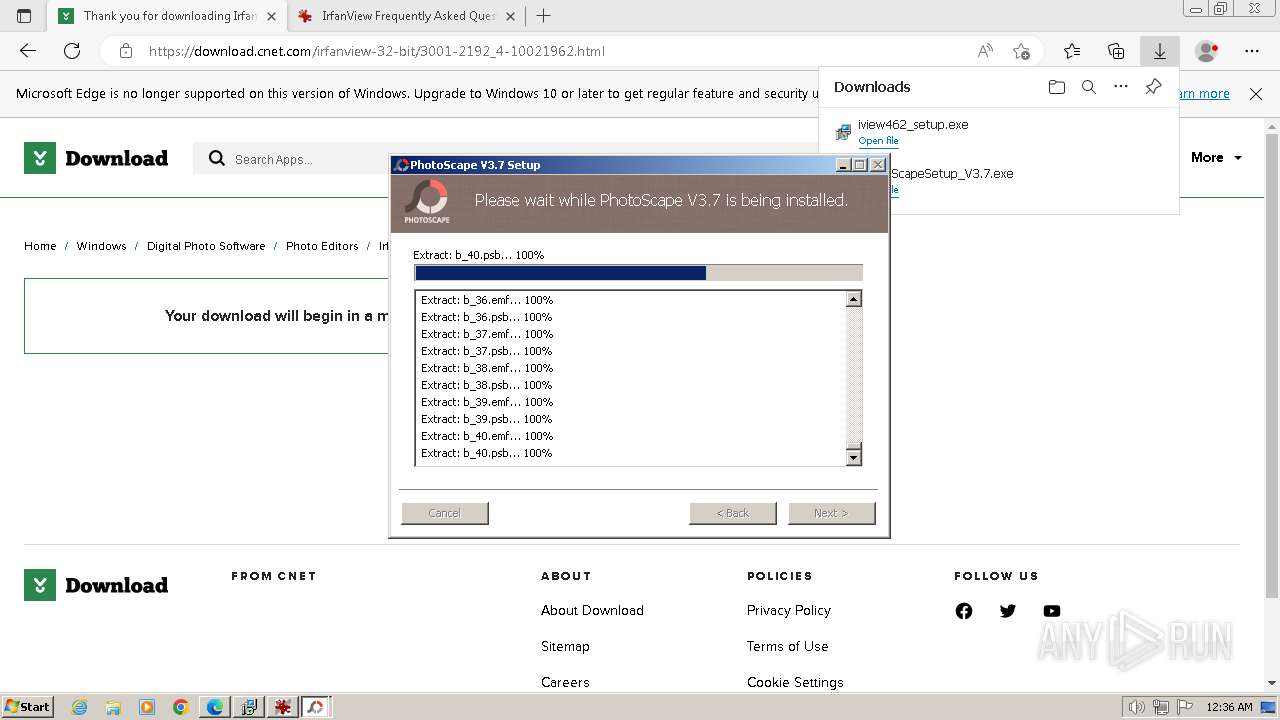
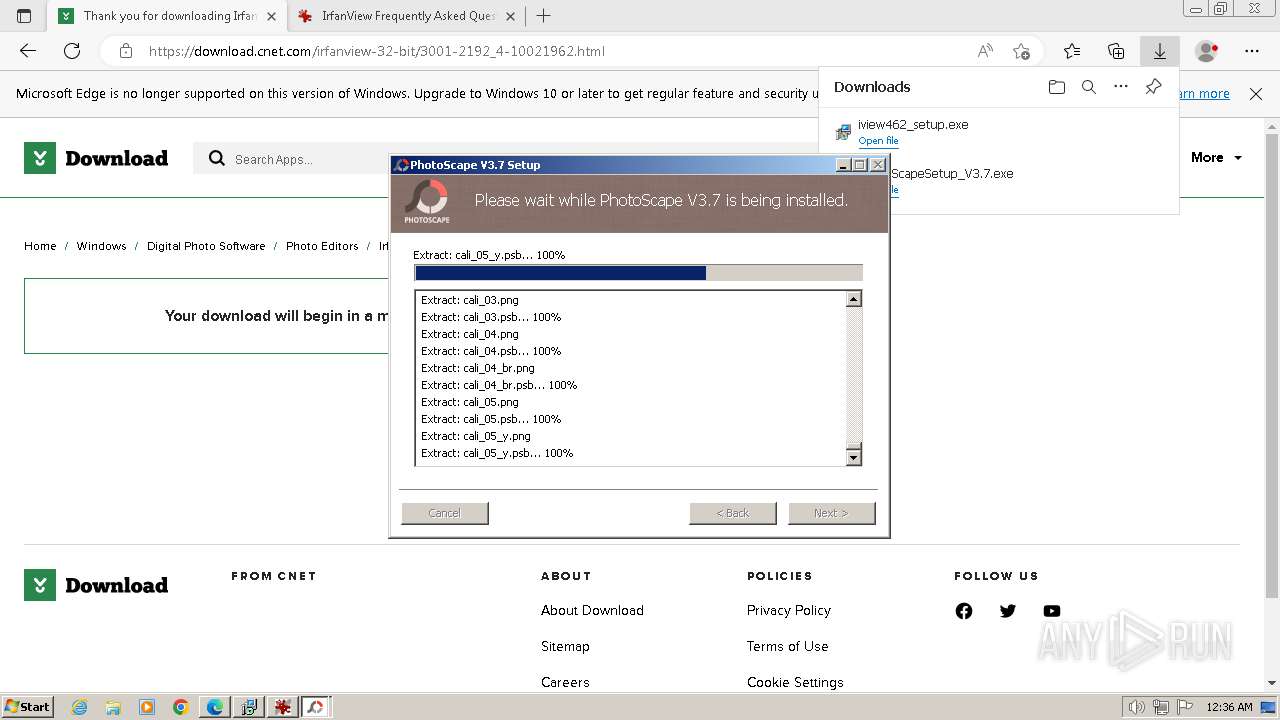
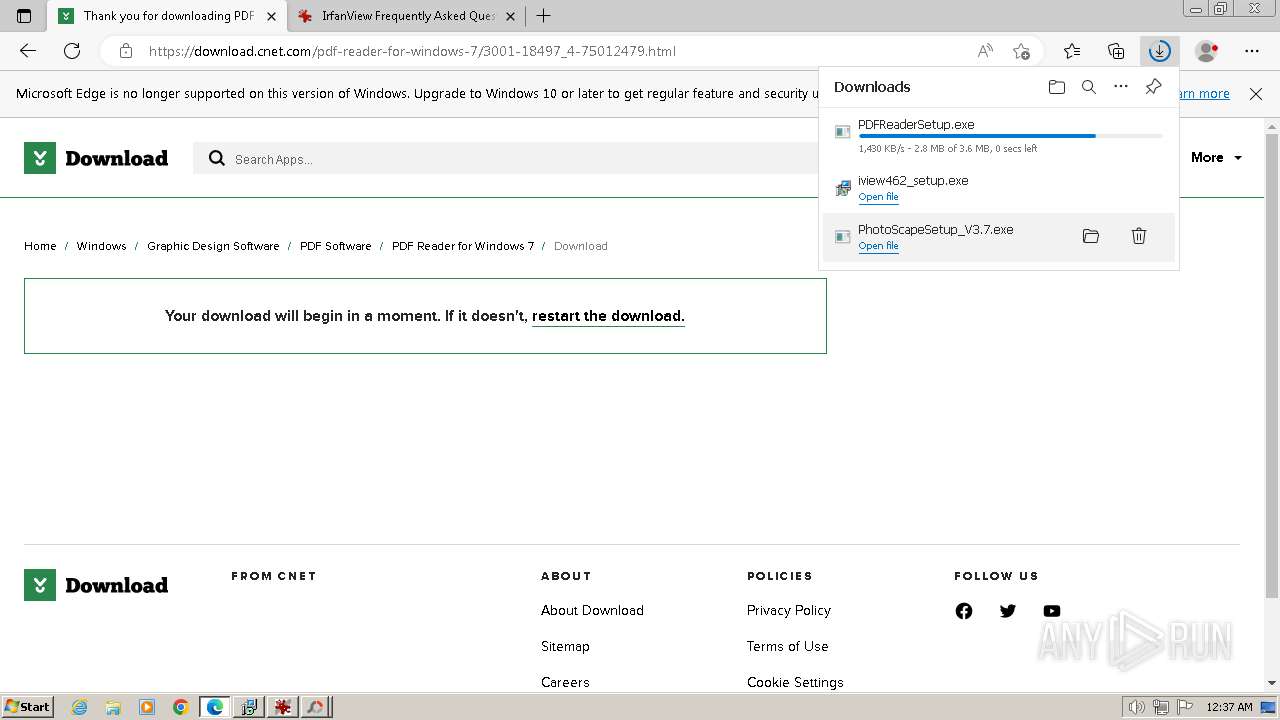
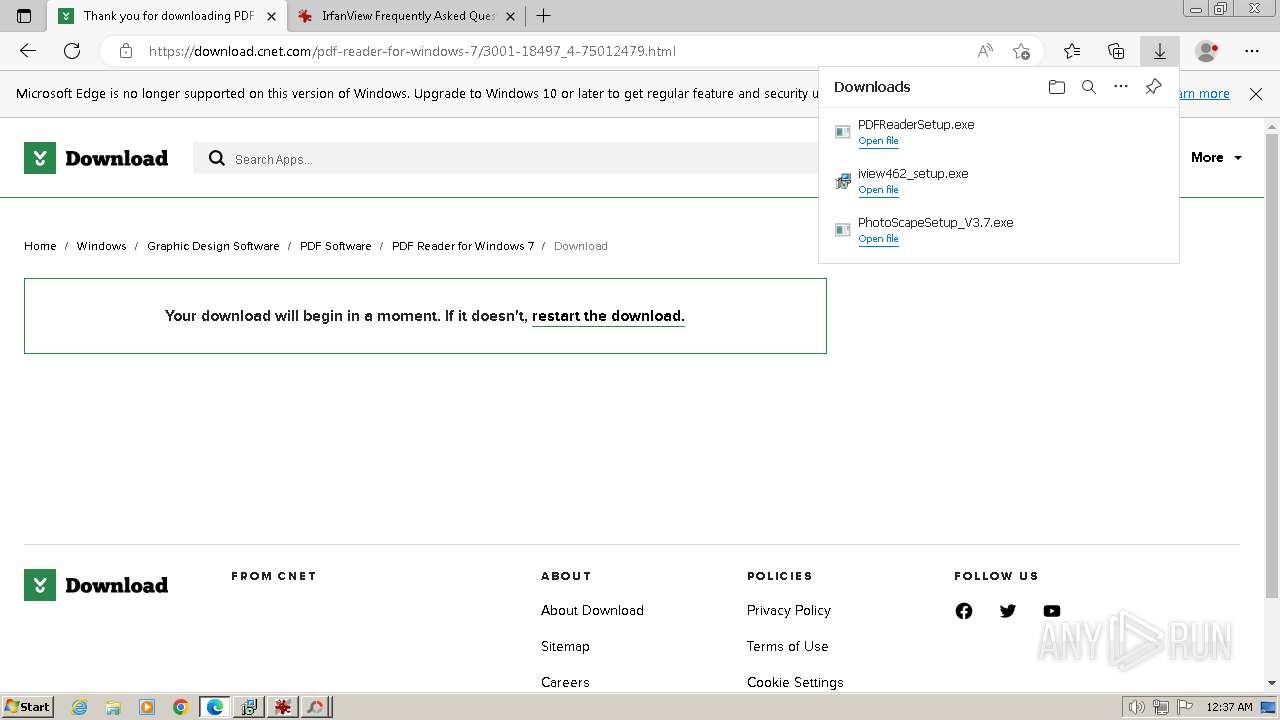
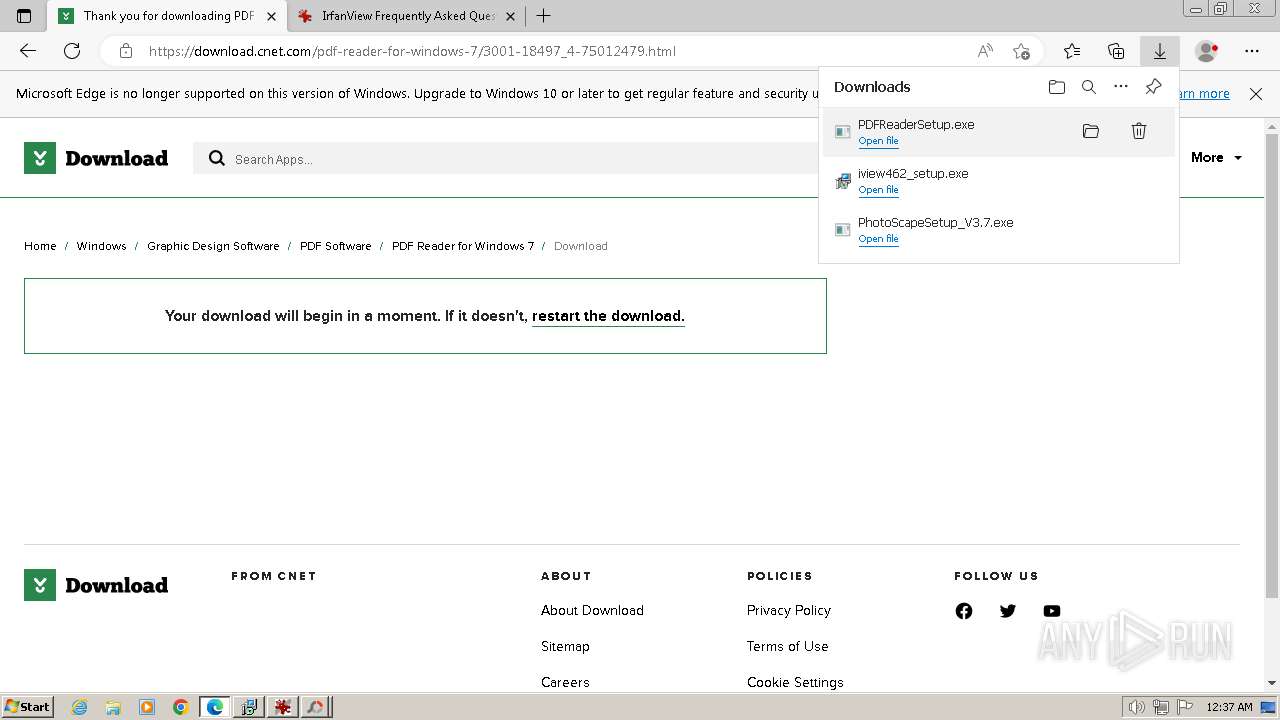
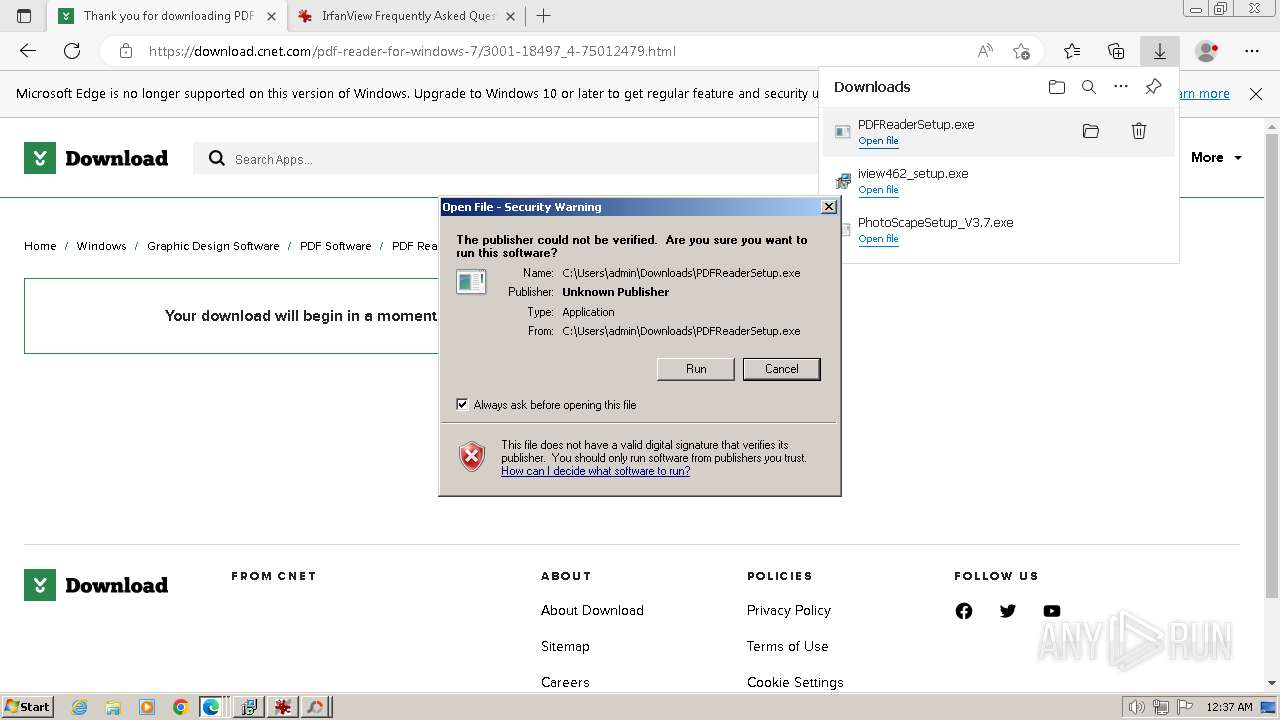
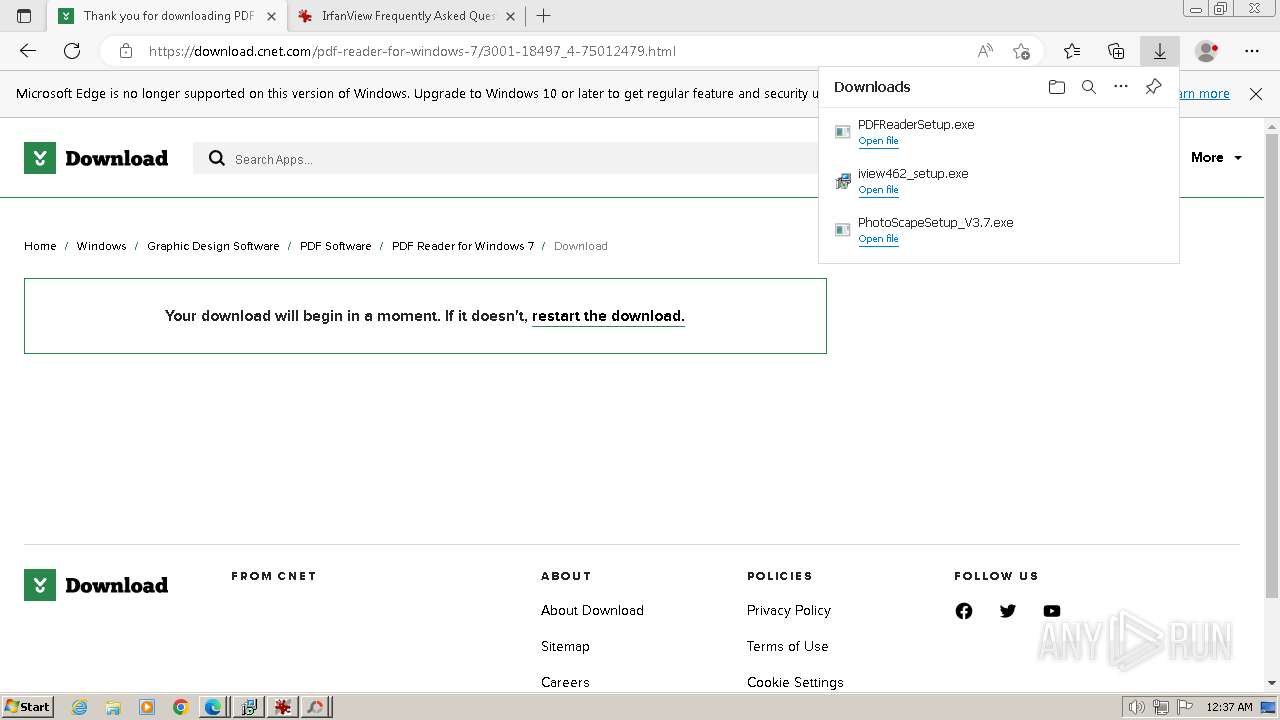
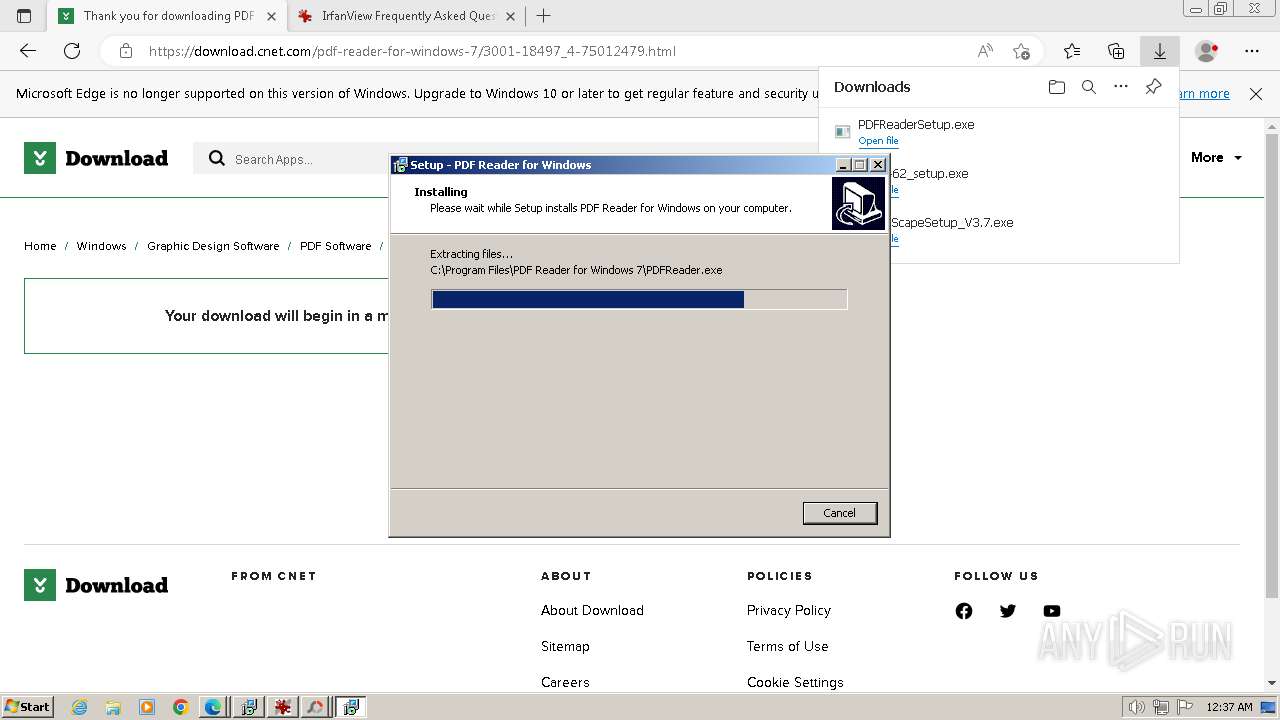
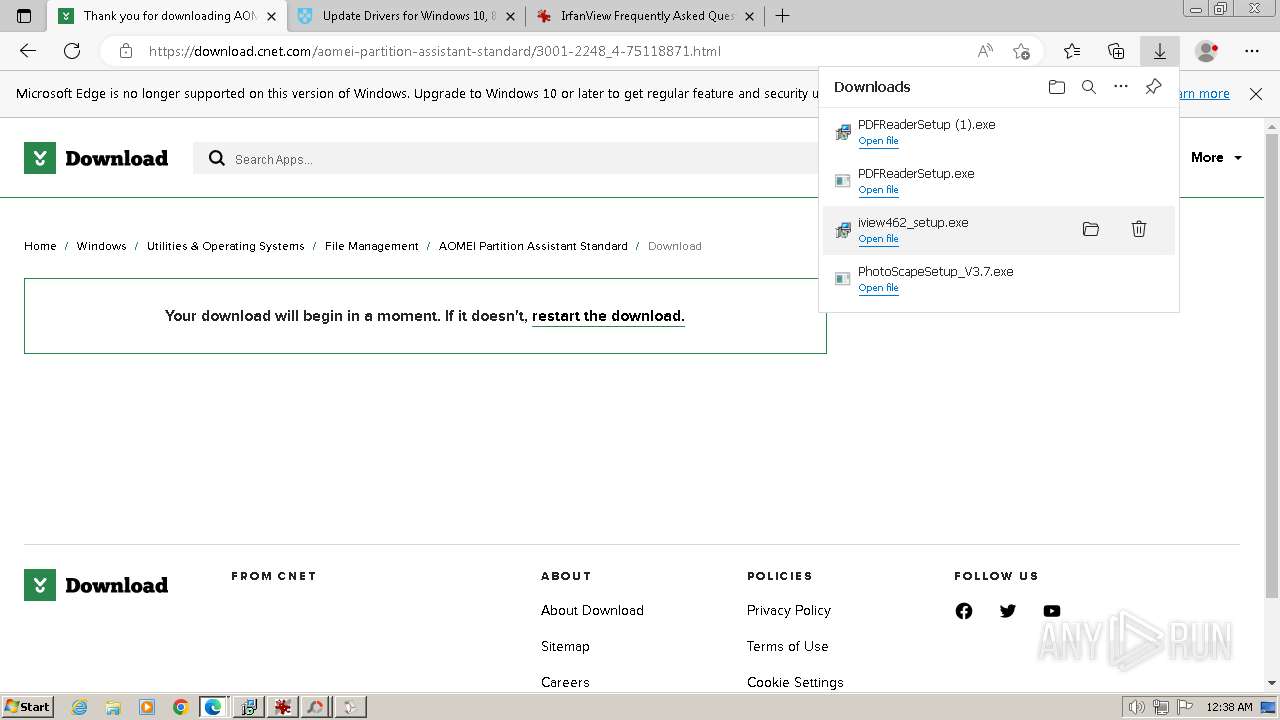
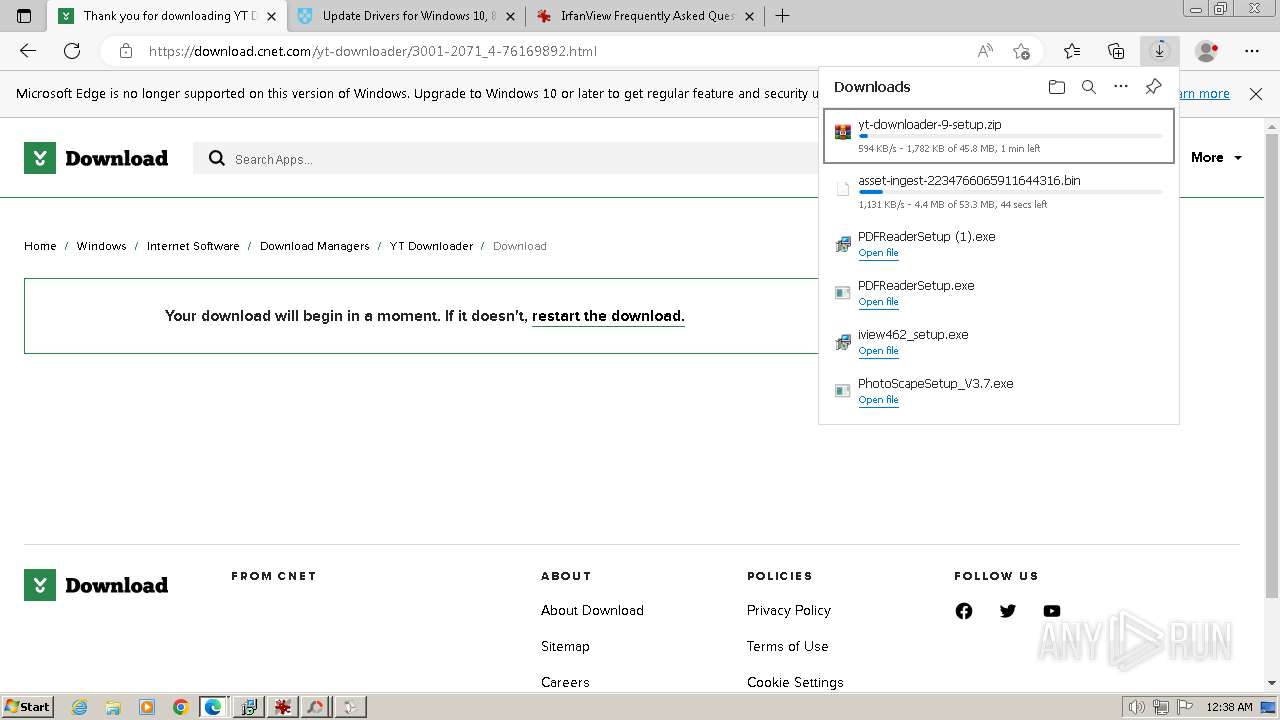
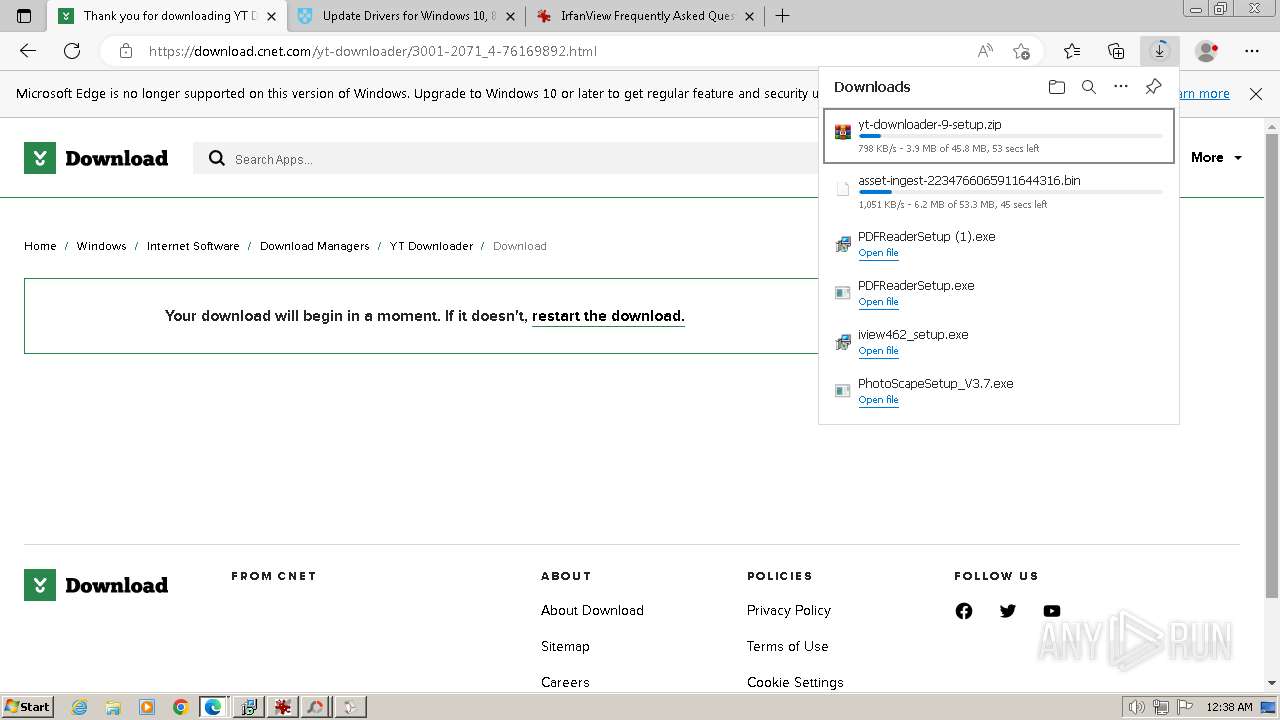
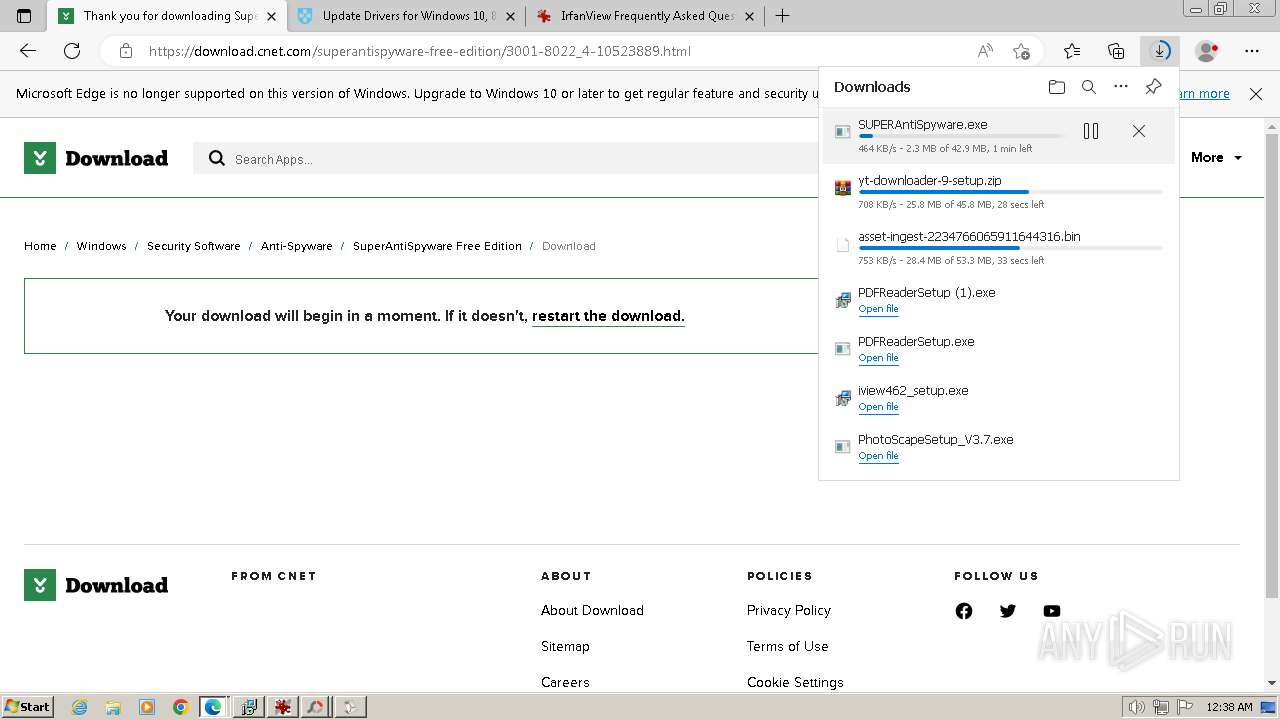
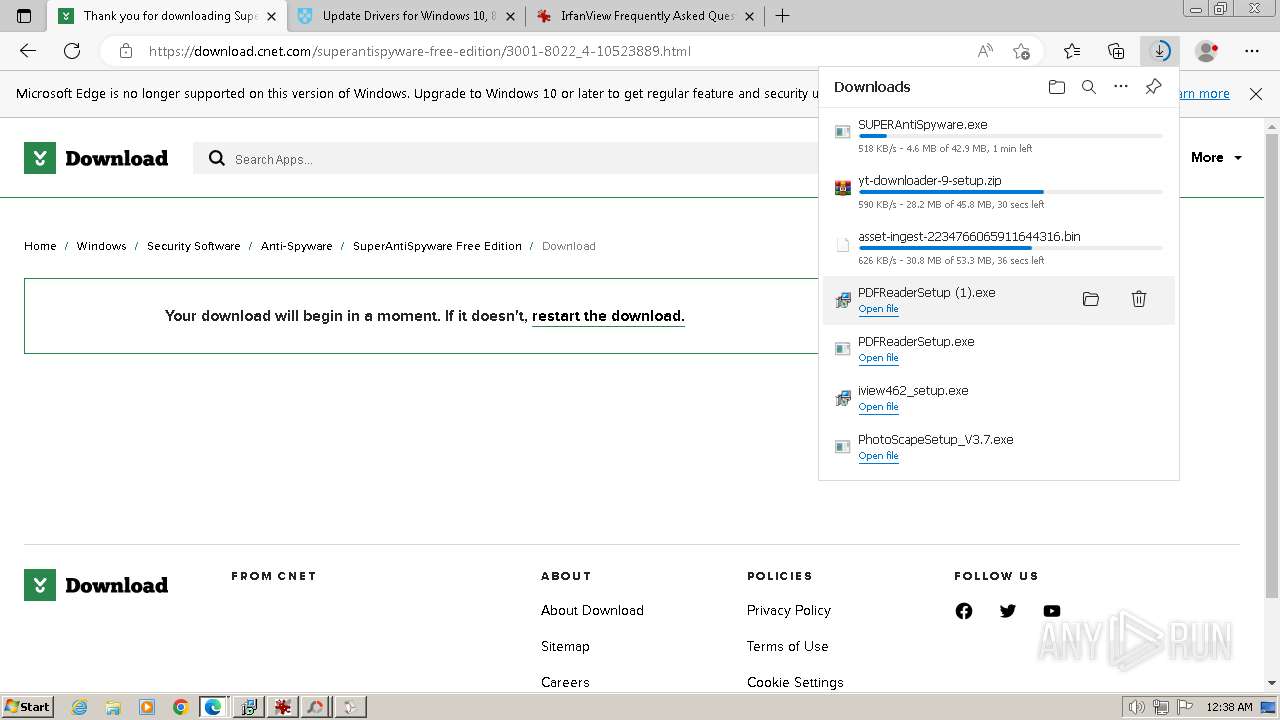
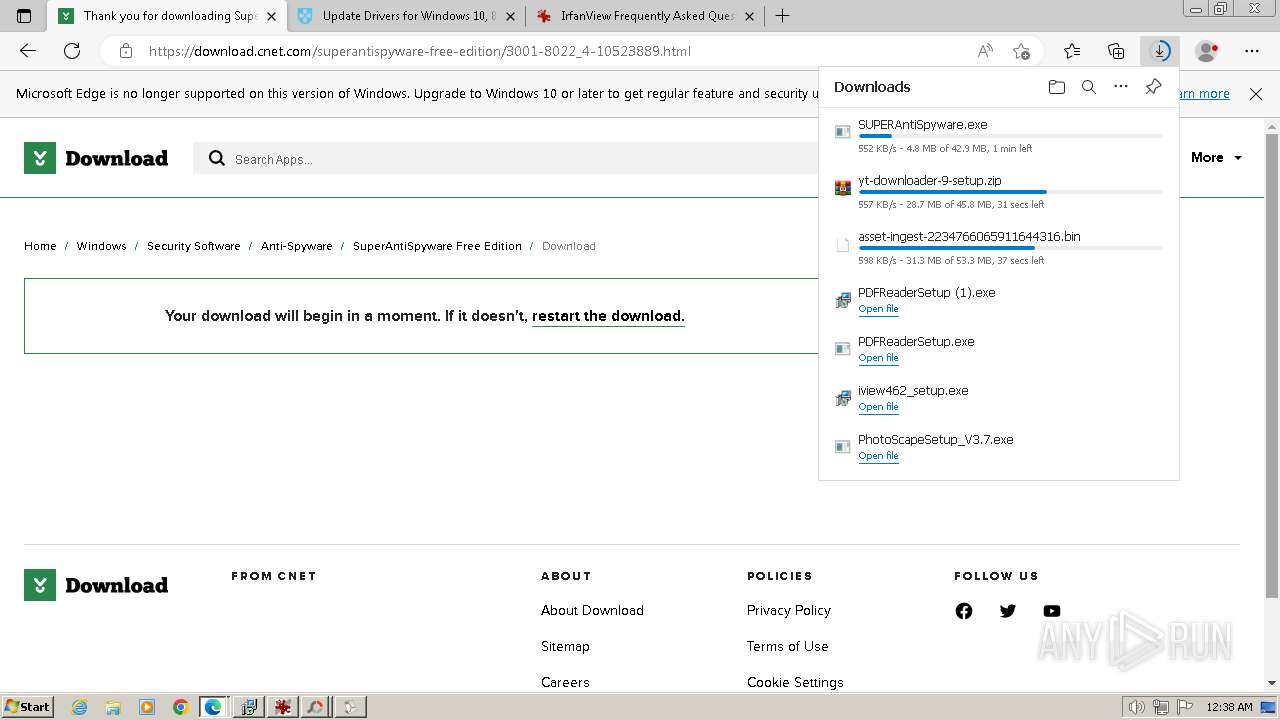
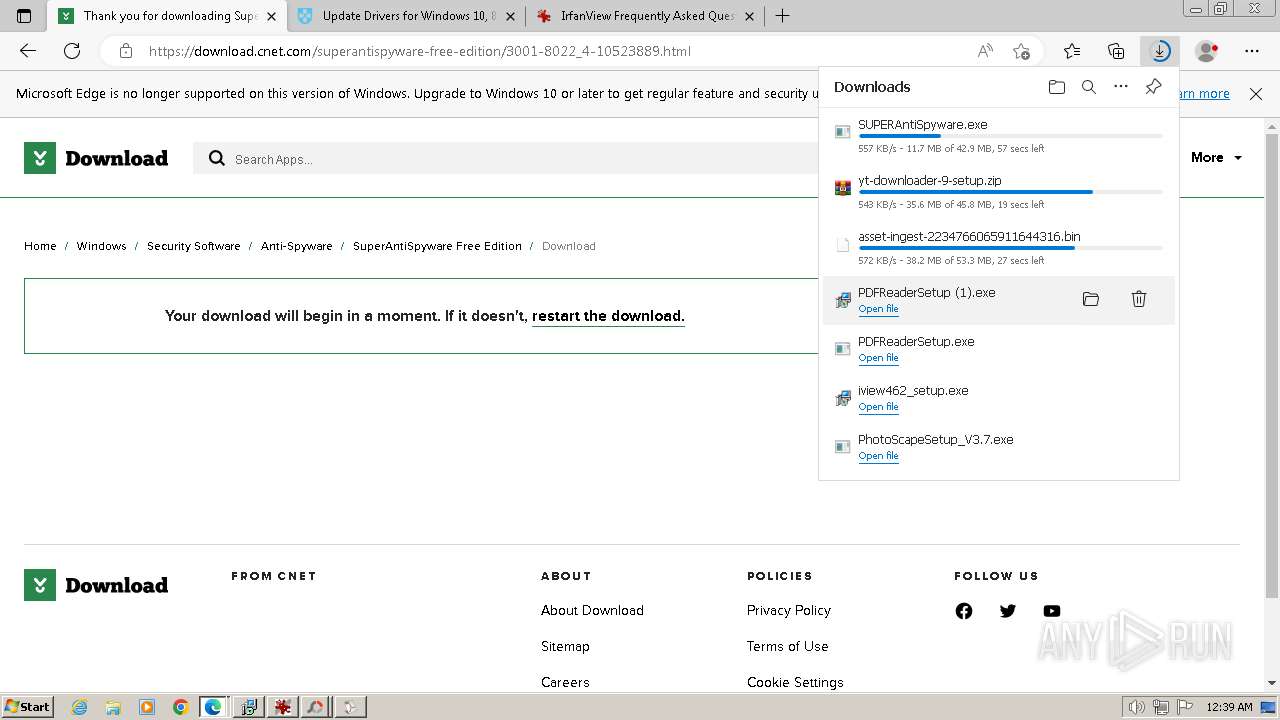
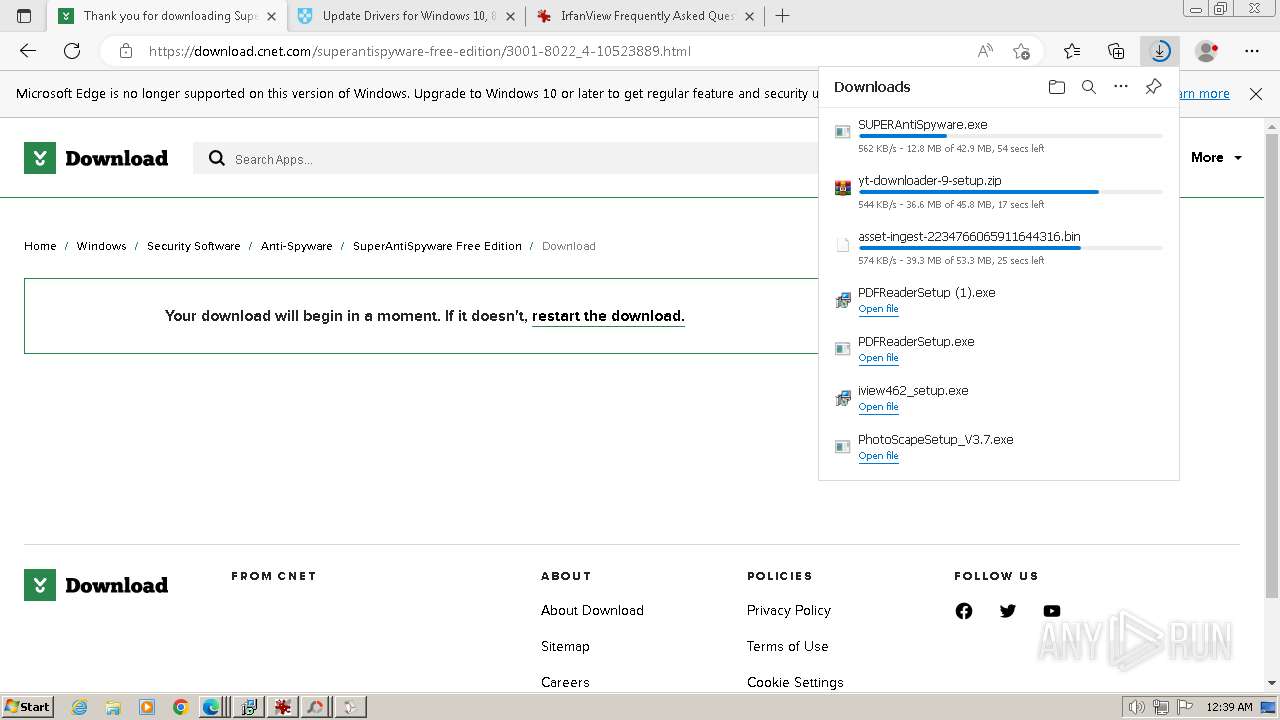
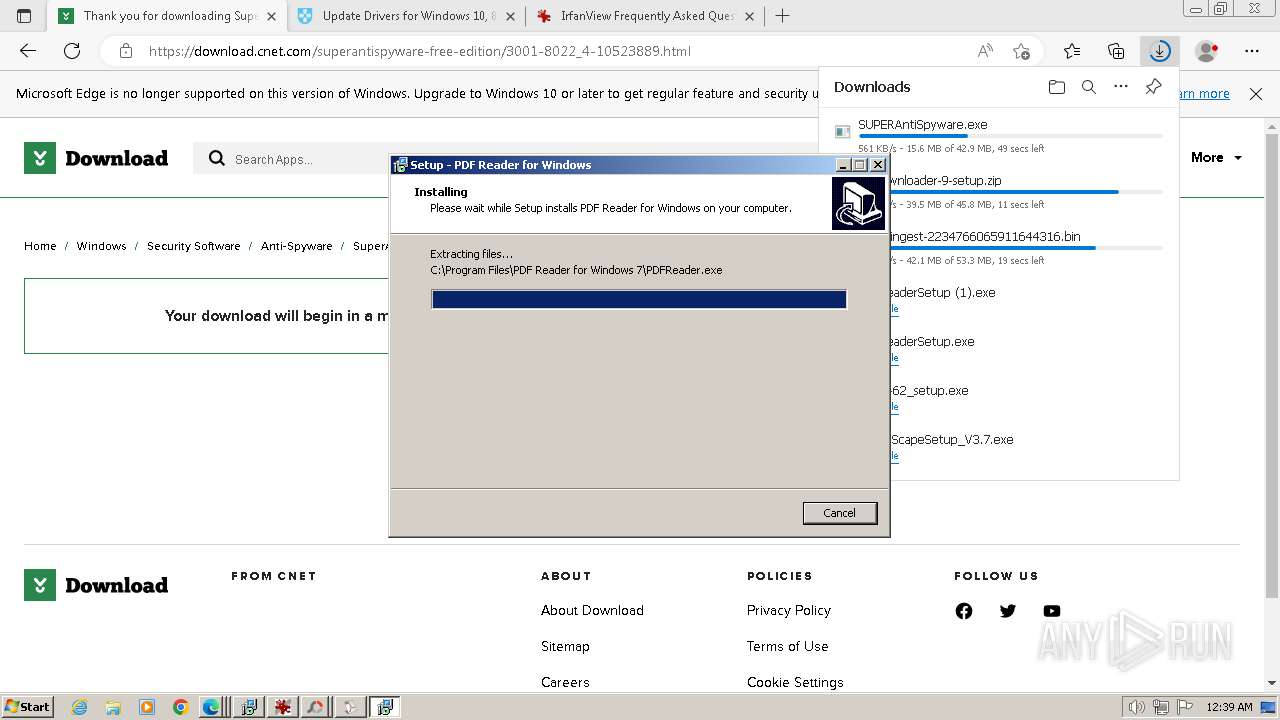
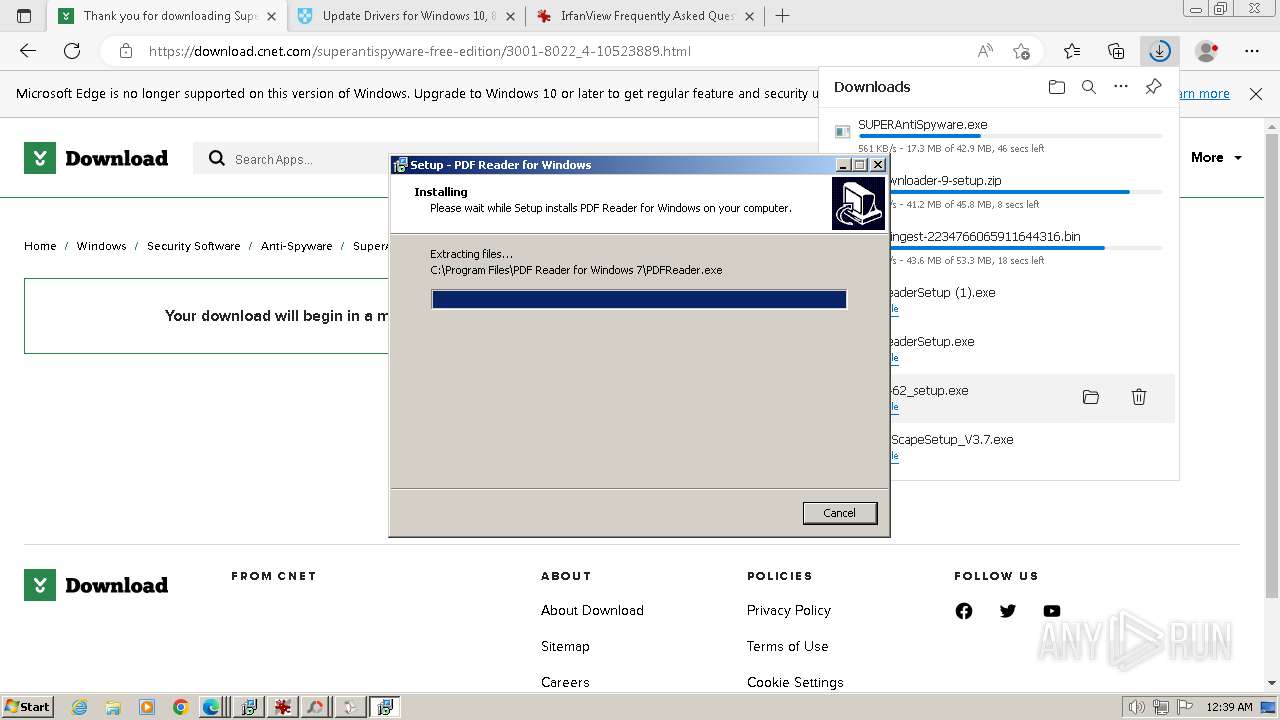
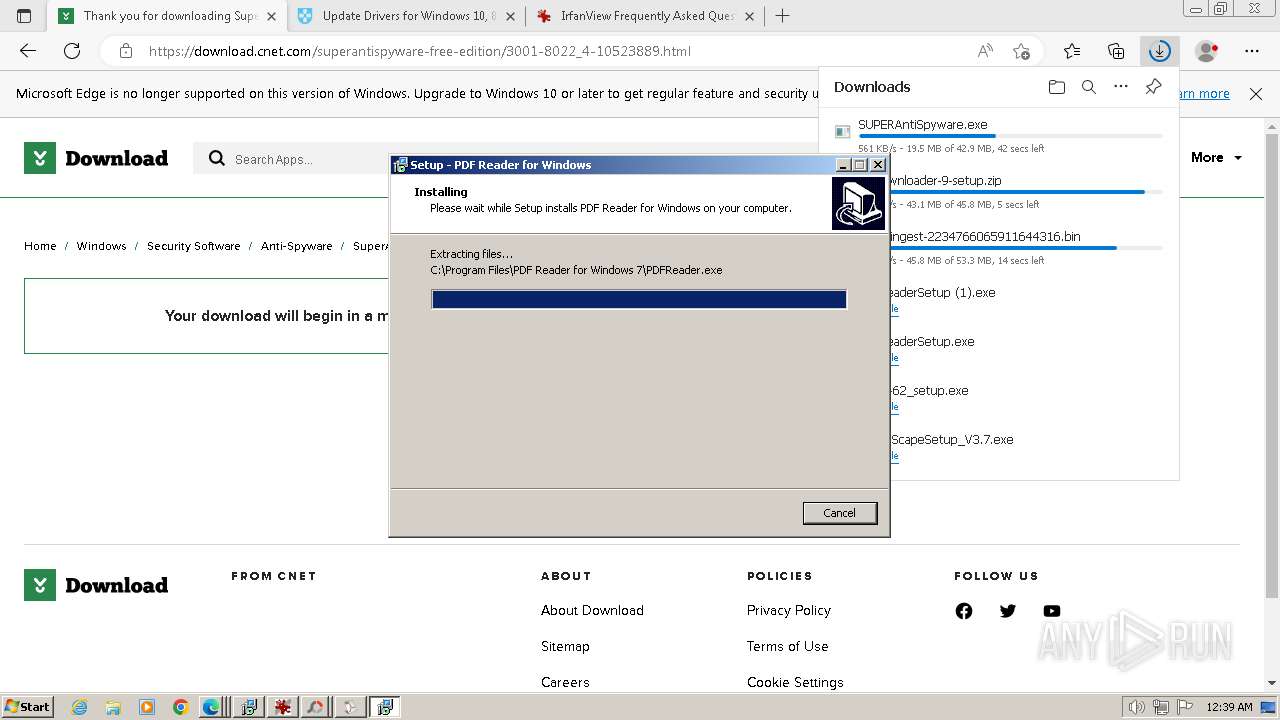
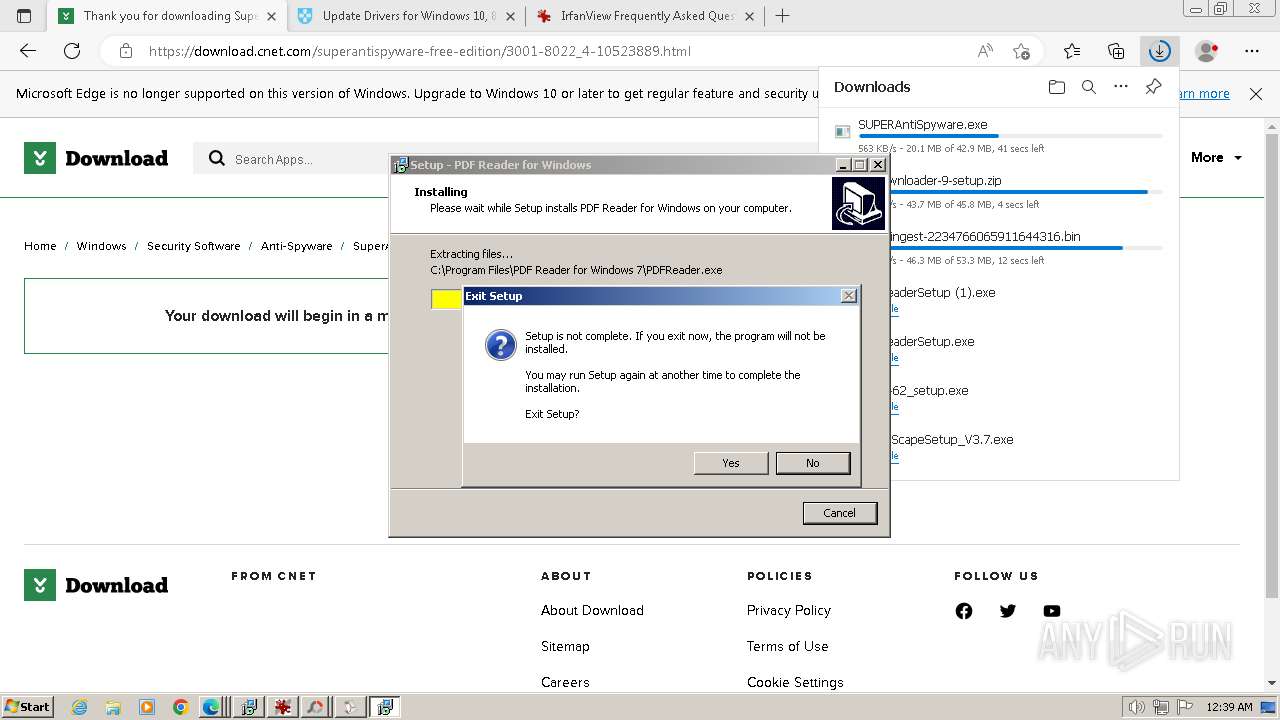
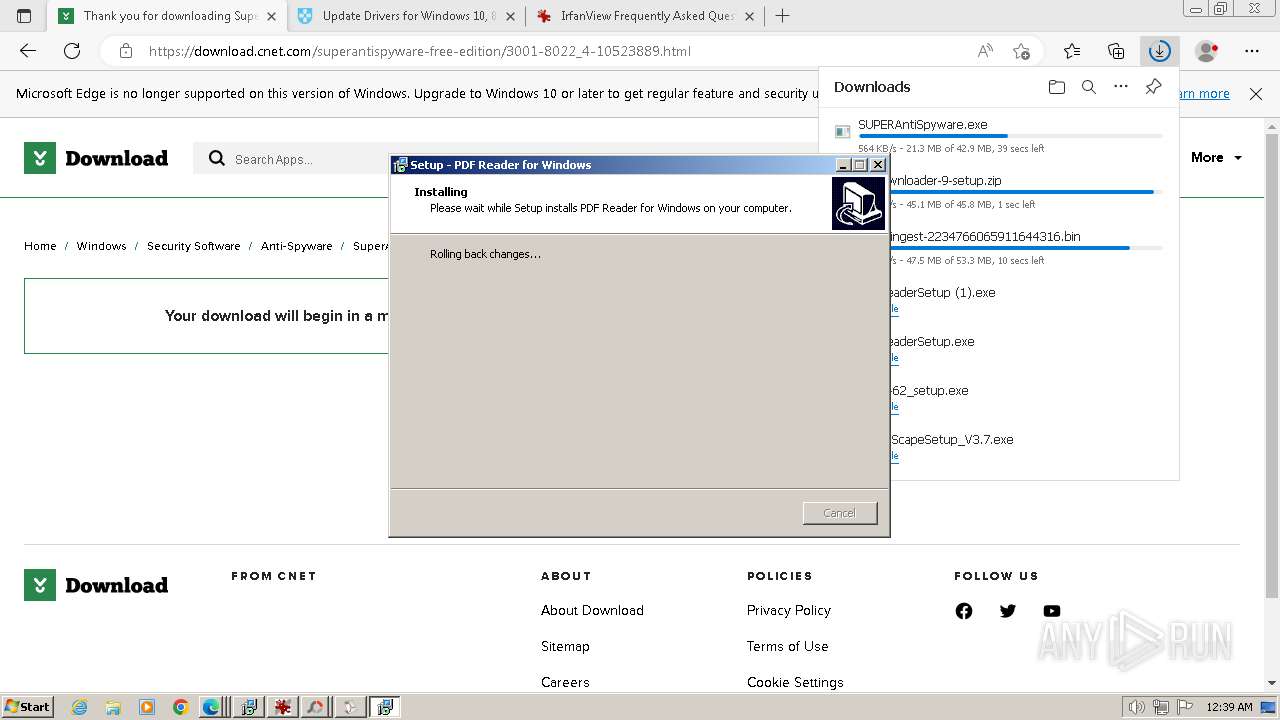
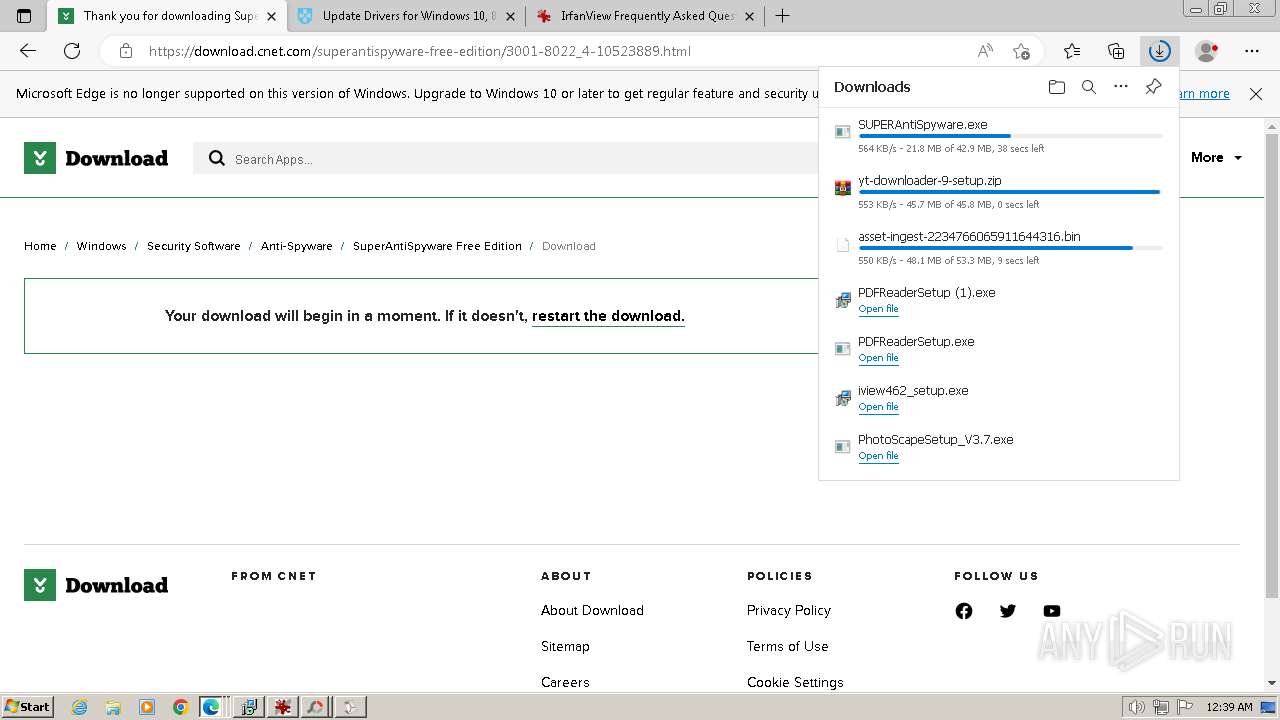
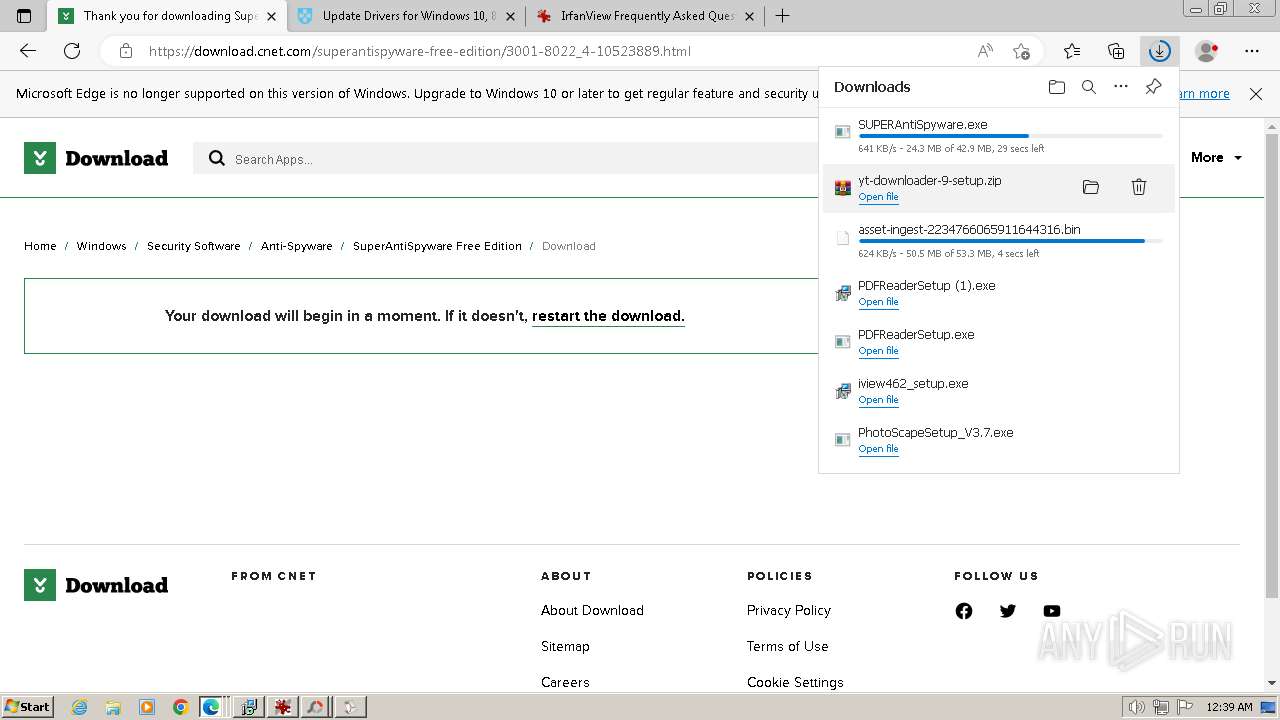
Drops the executable file immediately after the start
- iview462_setup.exe (PID: 2636)
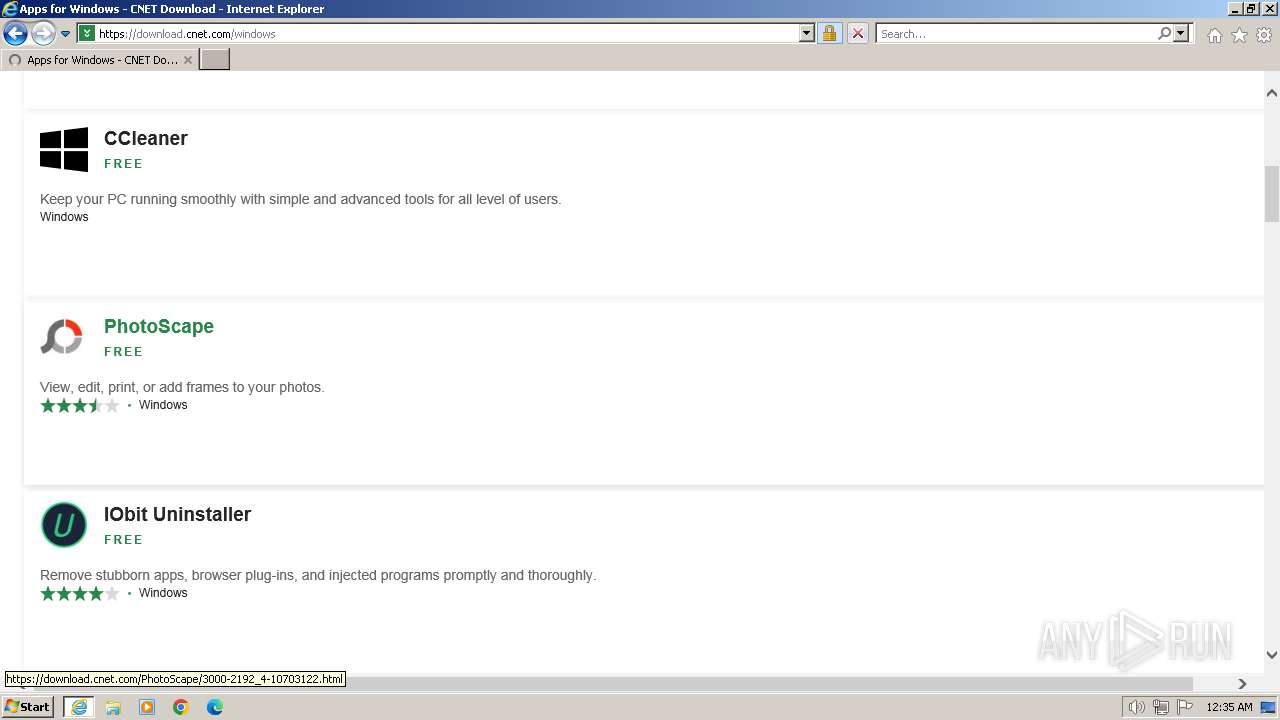
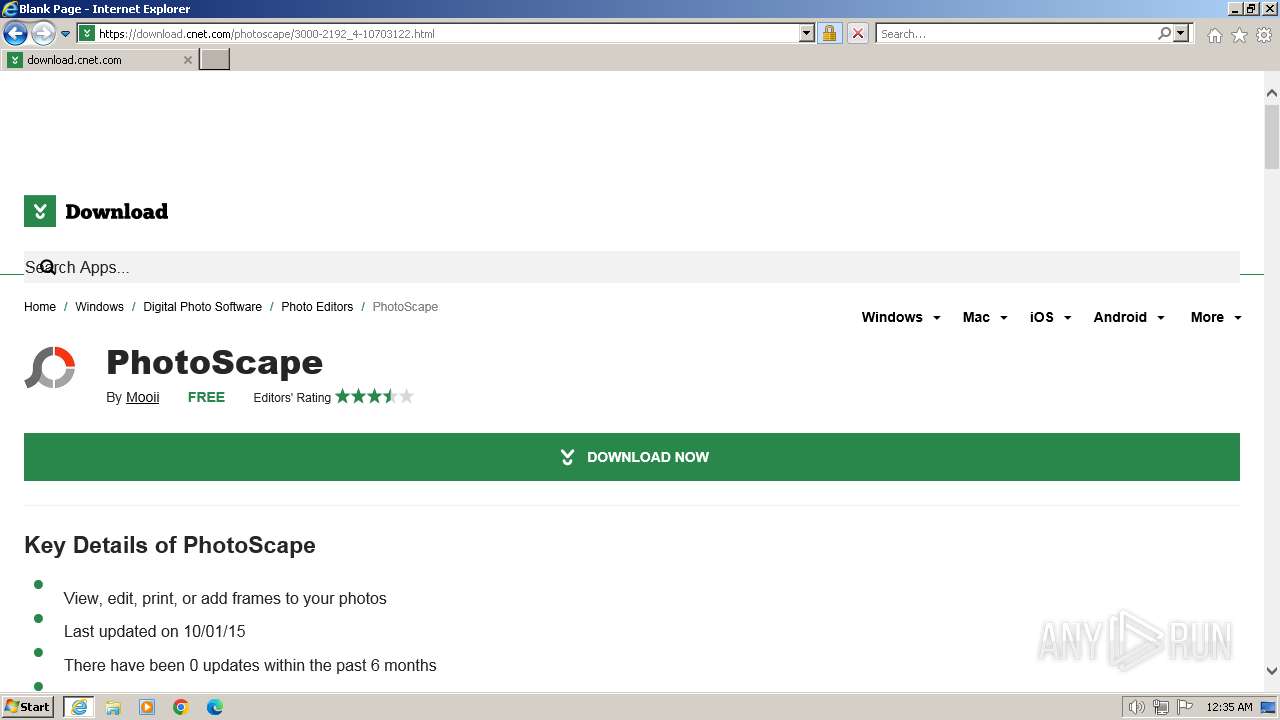
- PhotoScapeSetup_V3.7.exe (PID: 3892)
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- GoogleSetup.exe (PID: 4064)
- Mooii_GDrive.exe (PID: 3896)
- GoogleUpdateSetup_latest.exe (PID: 1172)
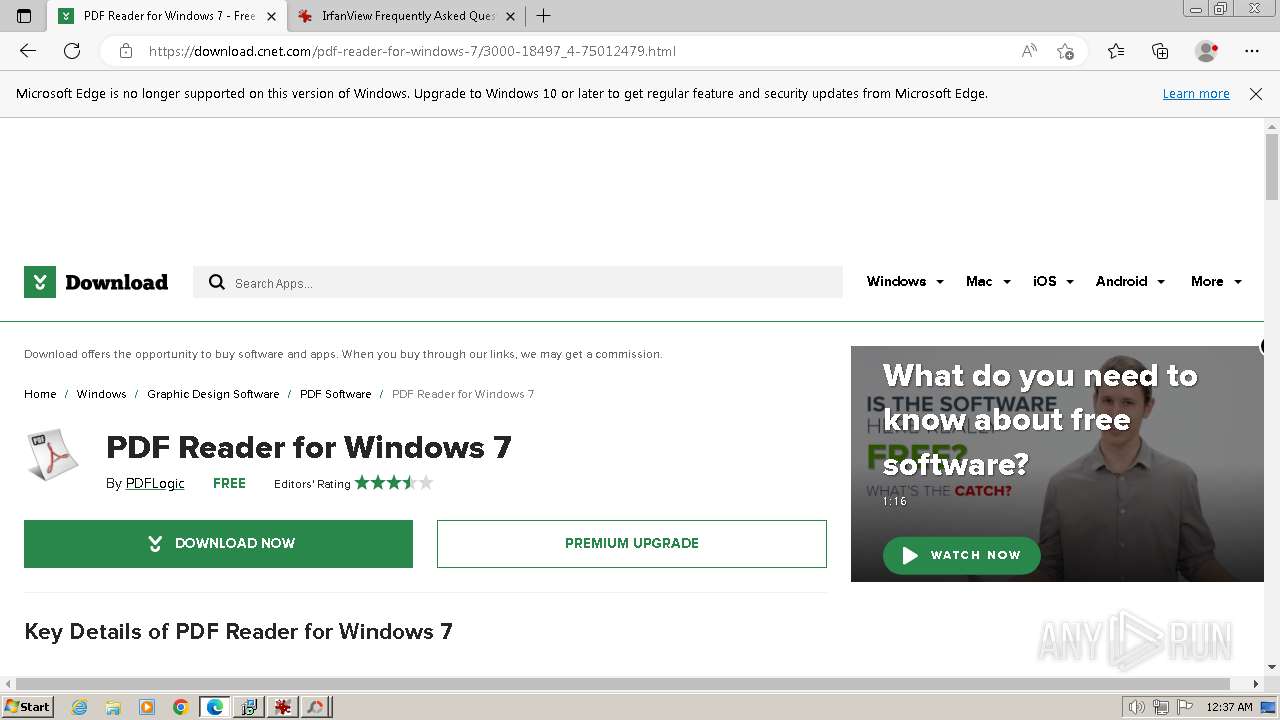
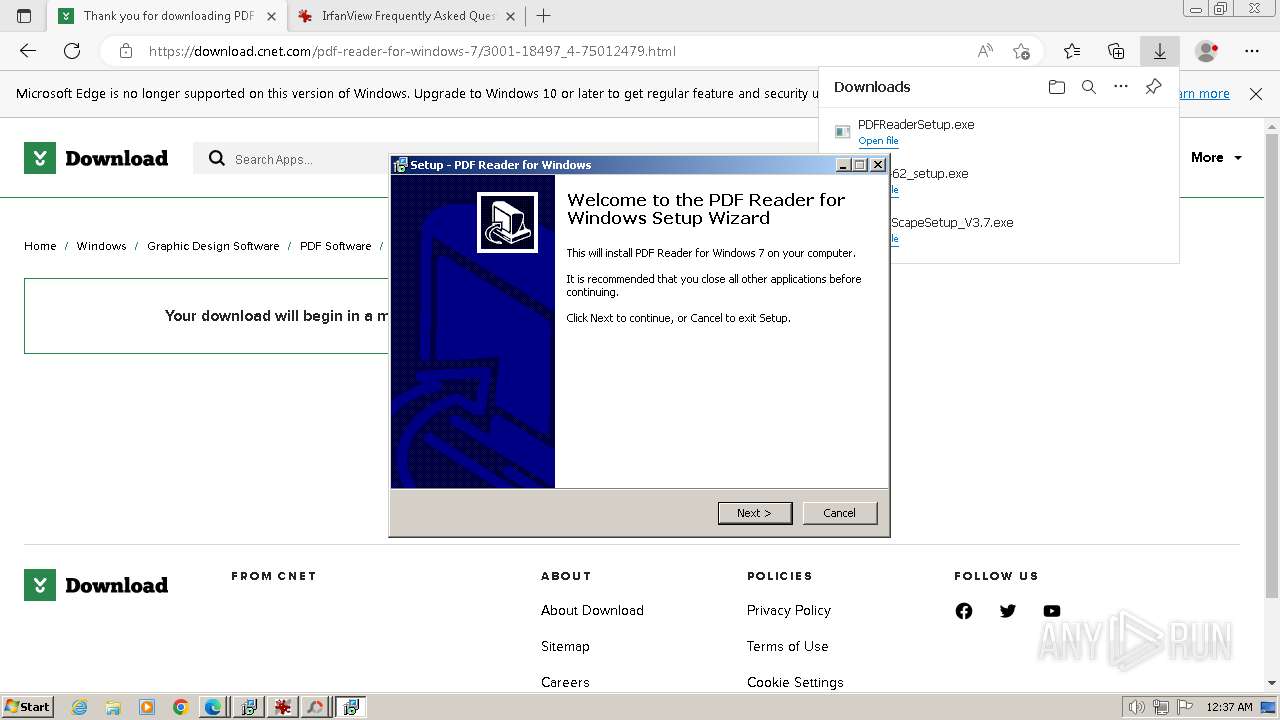
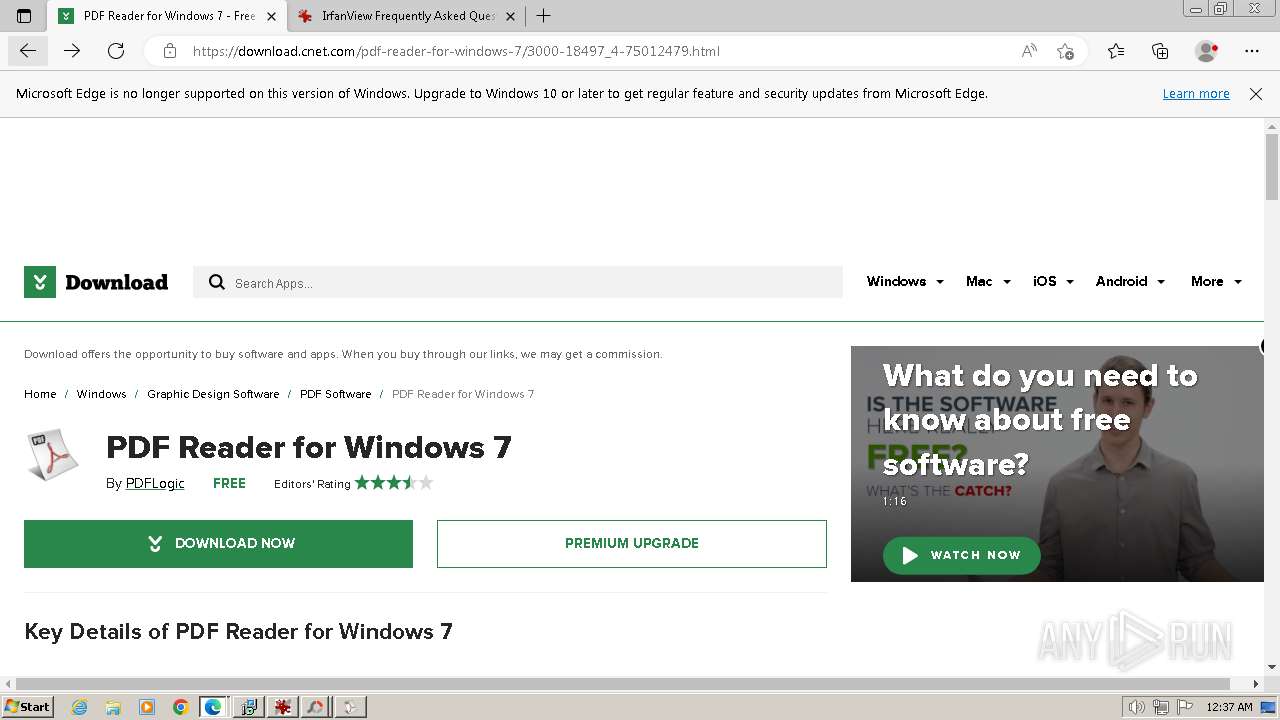
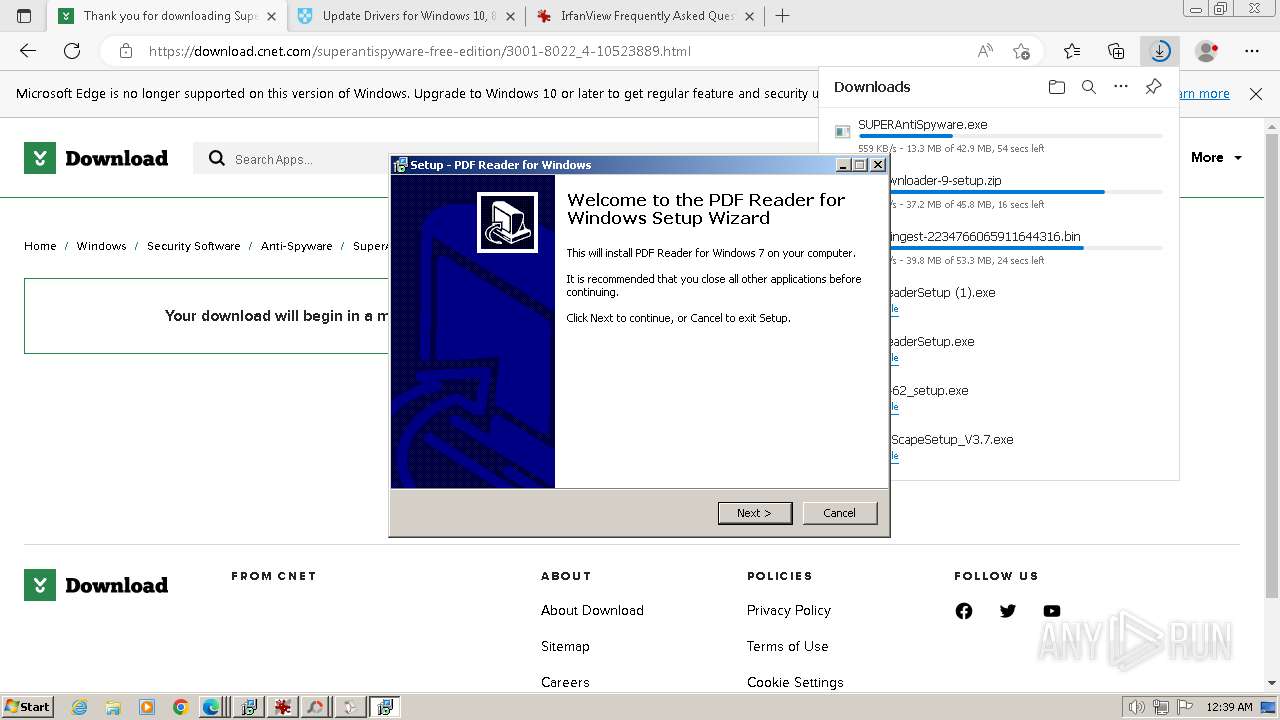
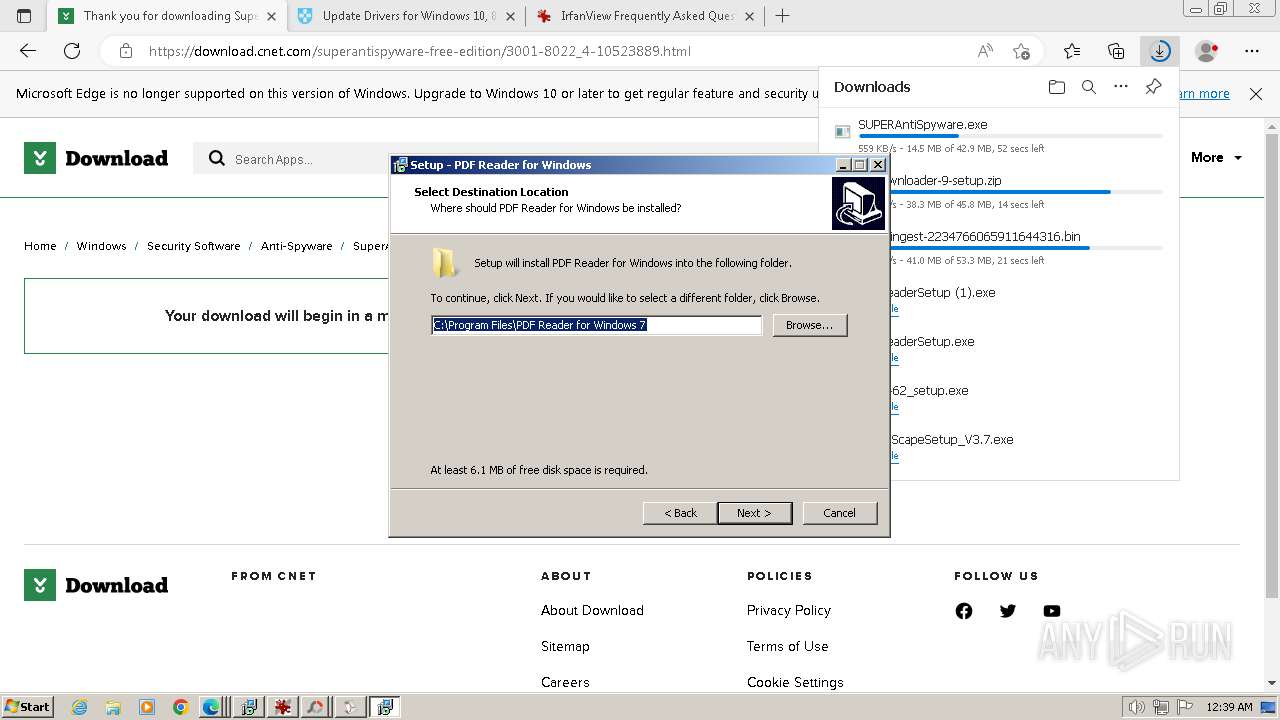
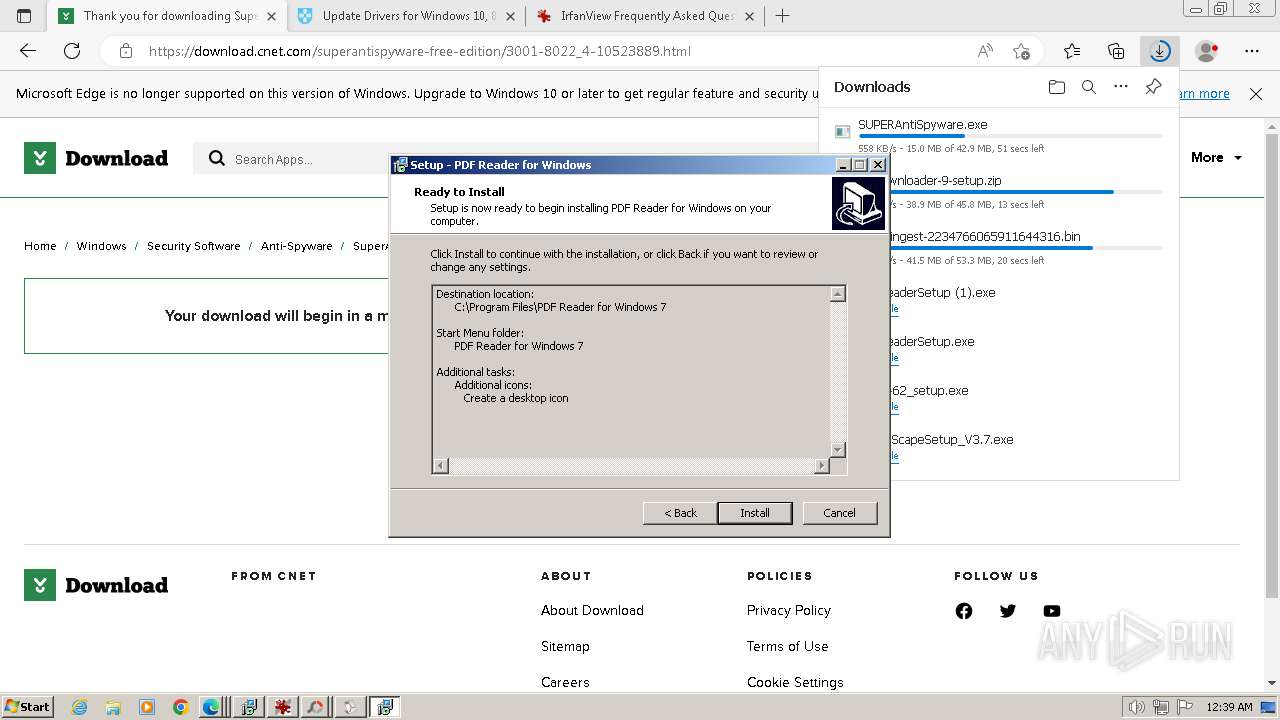
- PDFReaderSetup.exe (PID: 2316)
- PDFReaderSetup.exe (PID: 1820)
- PDFReaderSetup (1).exe (PID: 3744)
- PDFReaderSetup.tmp (PID: 3628)
- PDFReaderSetup (1).tmp (PID: 3452)
- PDFReaderSetup (1).exe (PID: 2148)
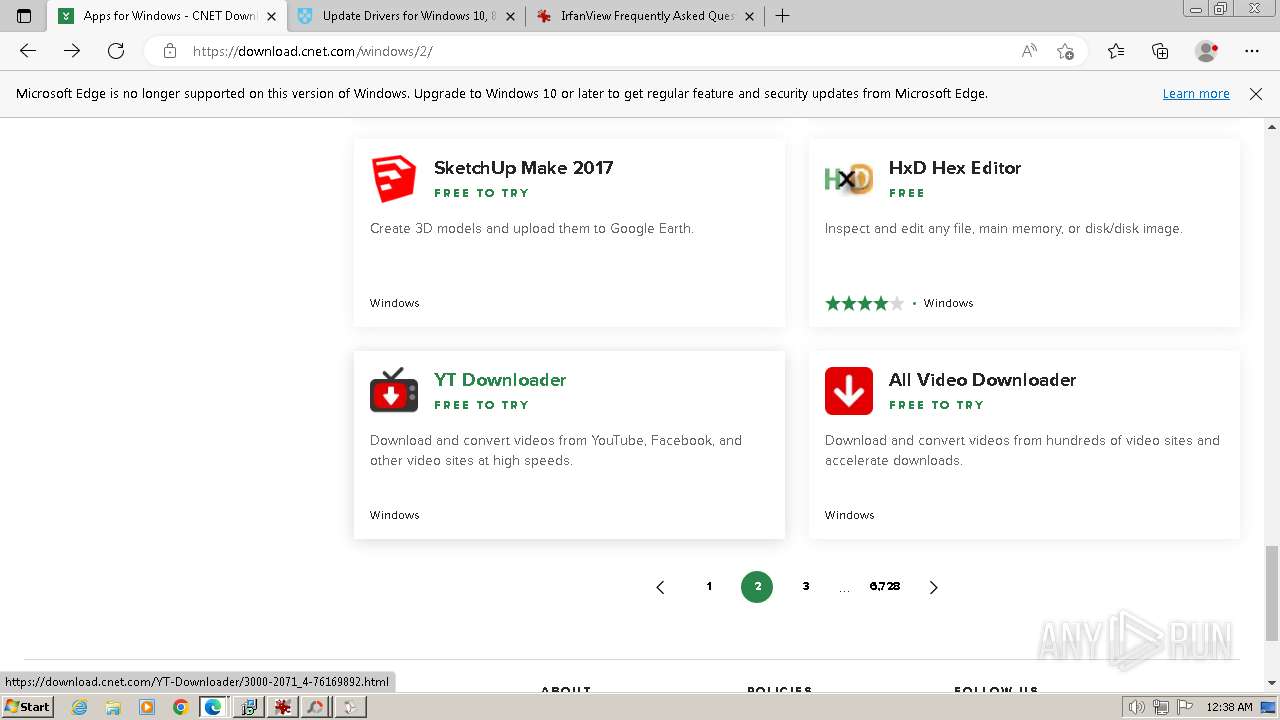
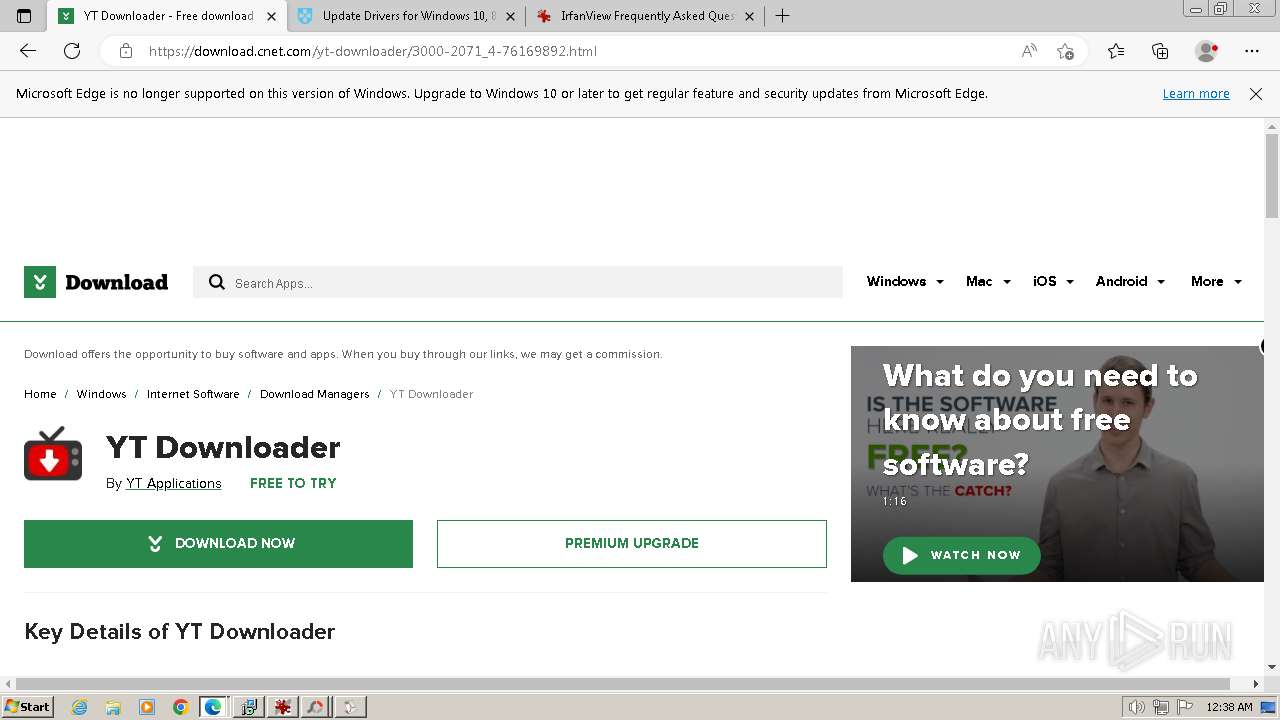
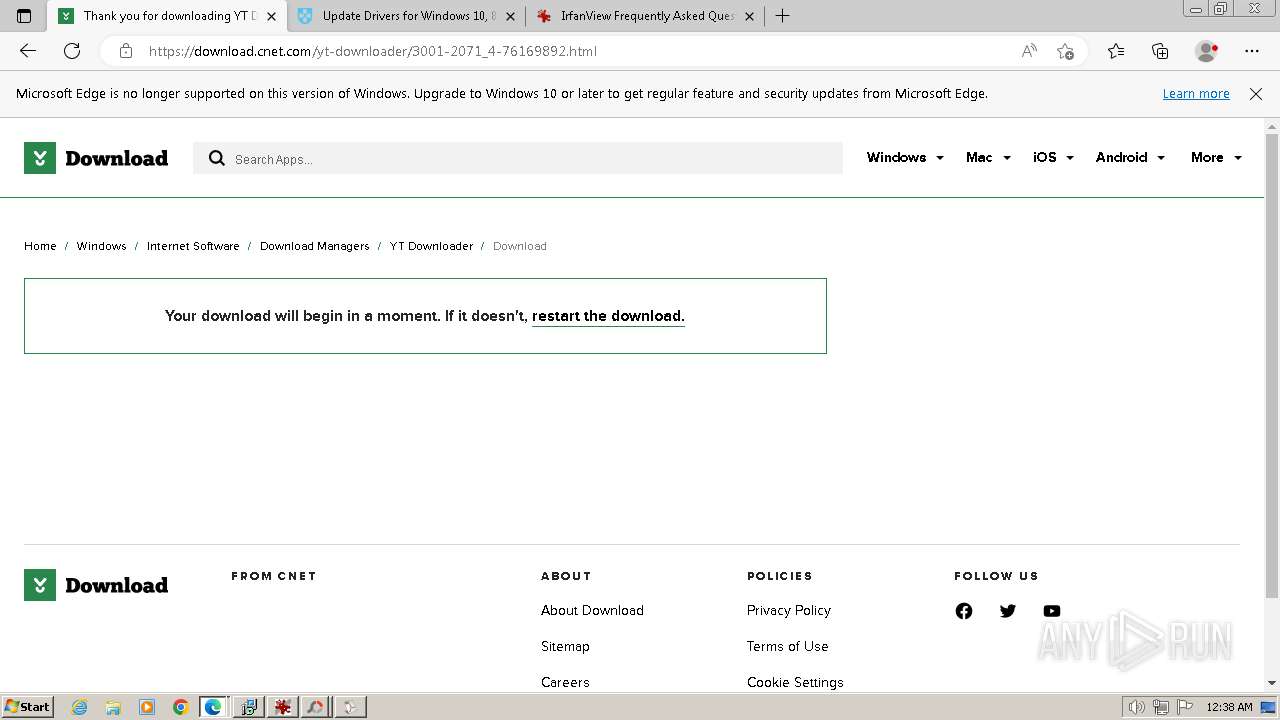
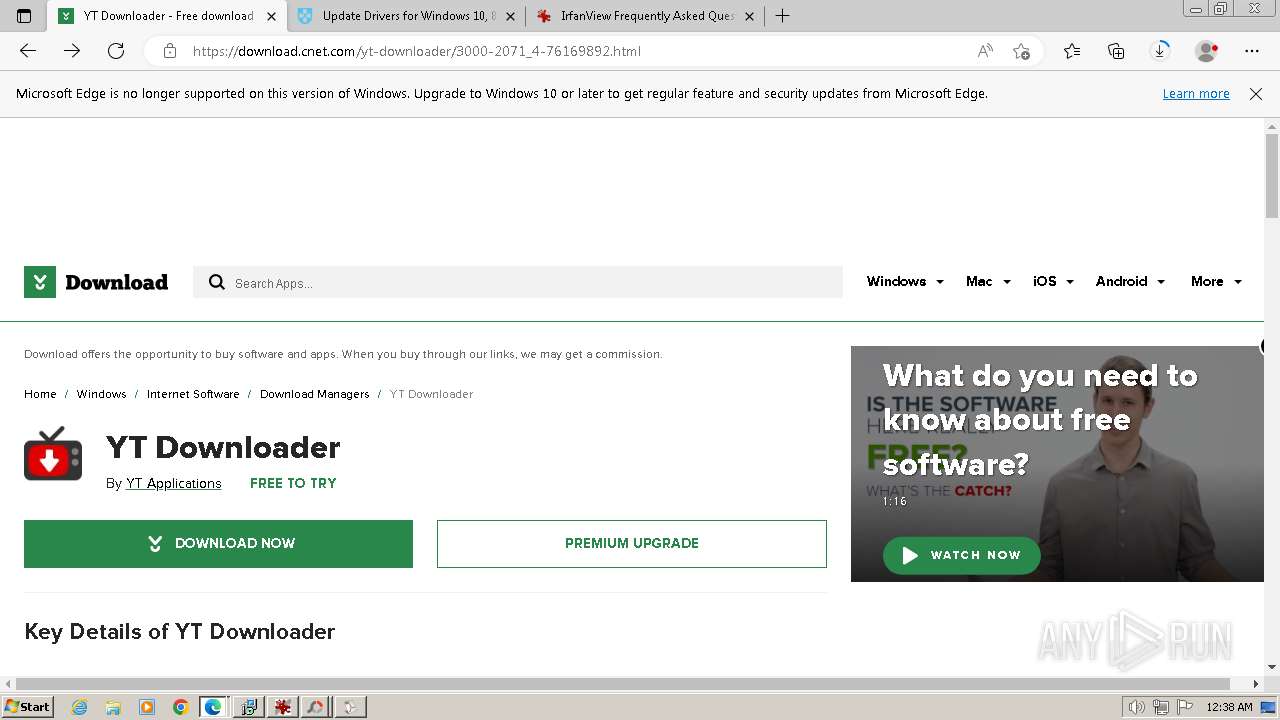
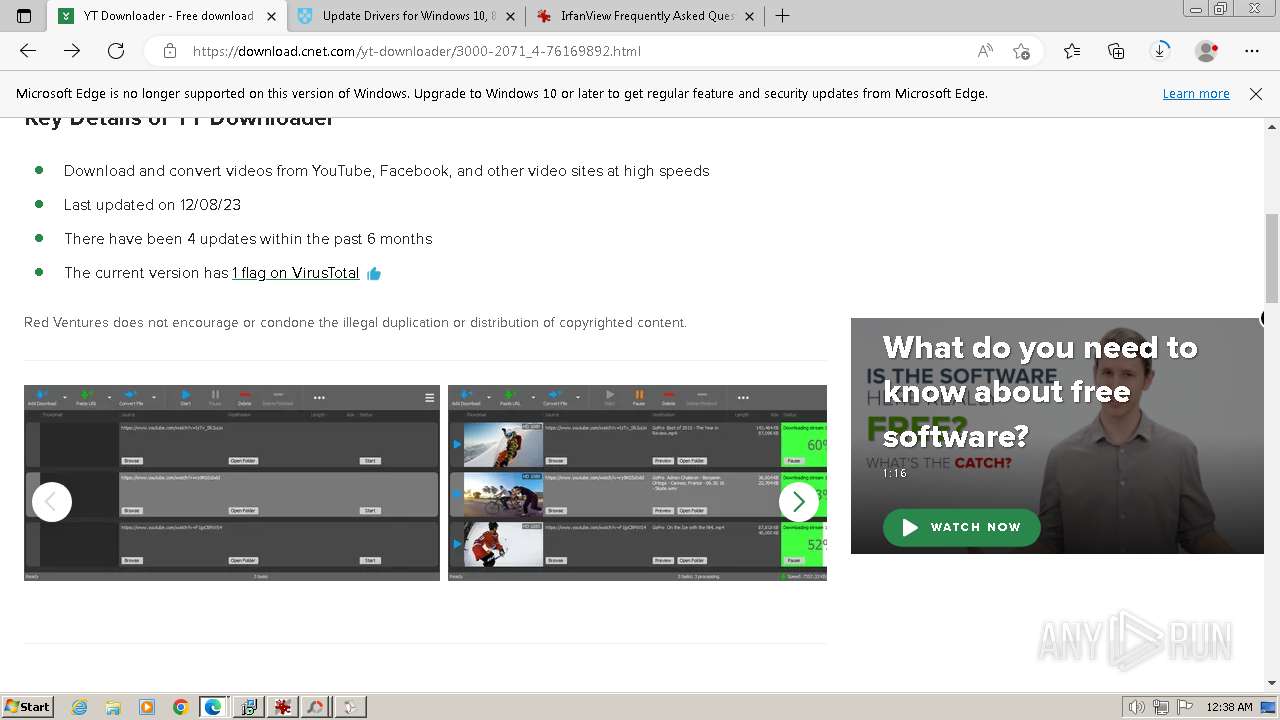
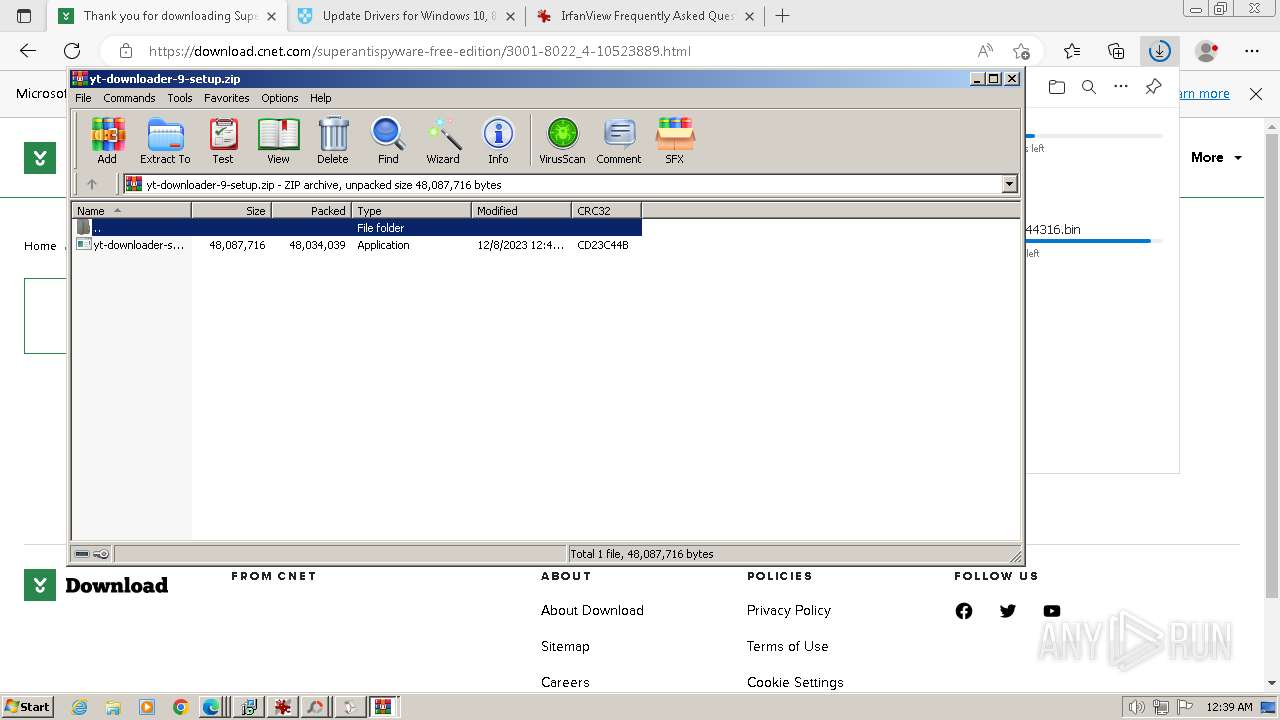
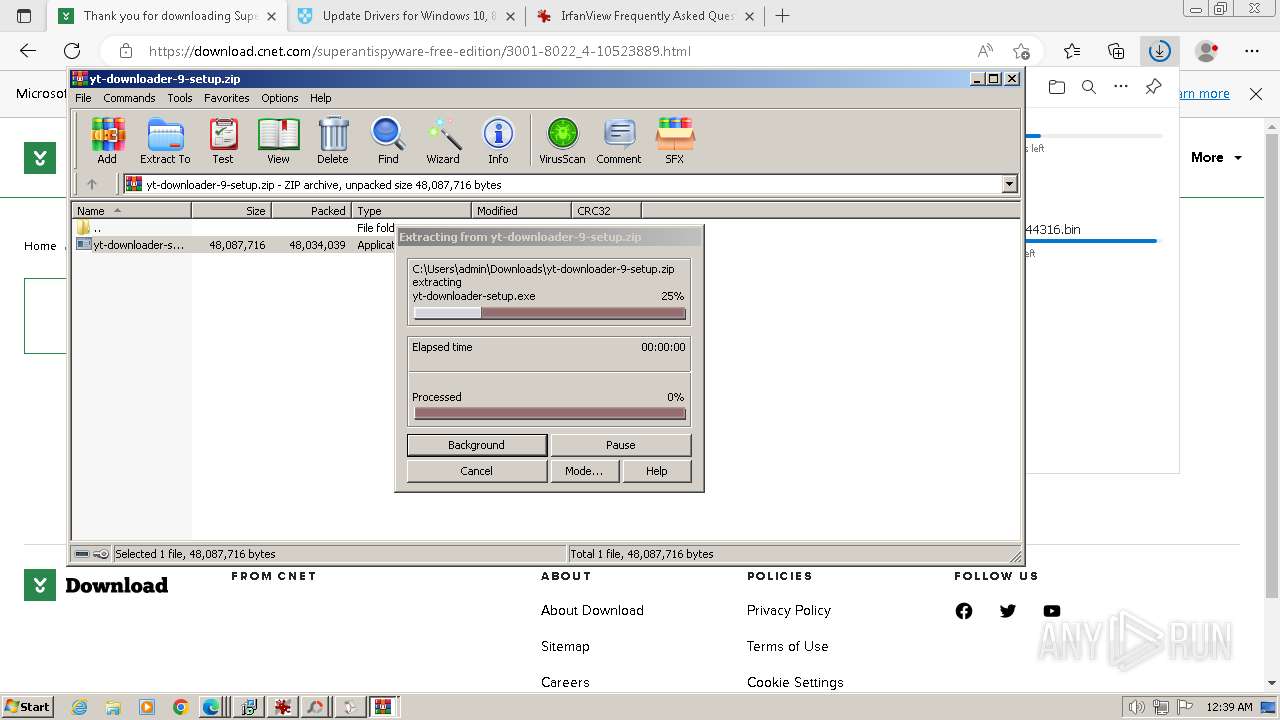
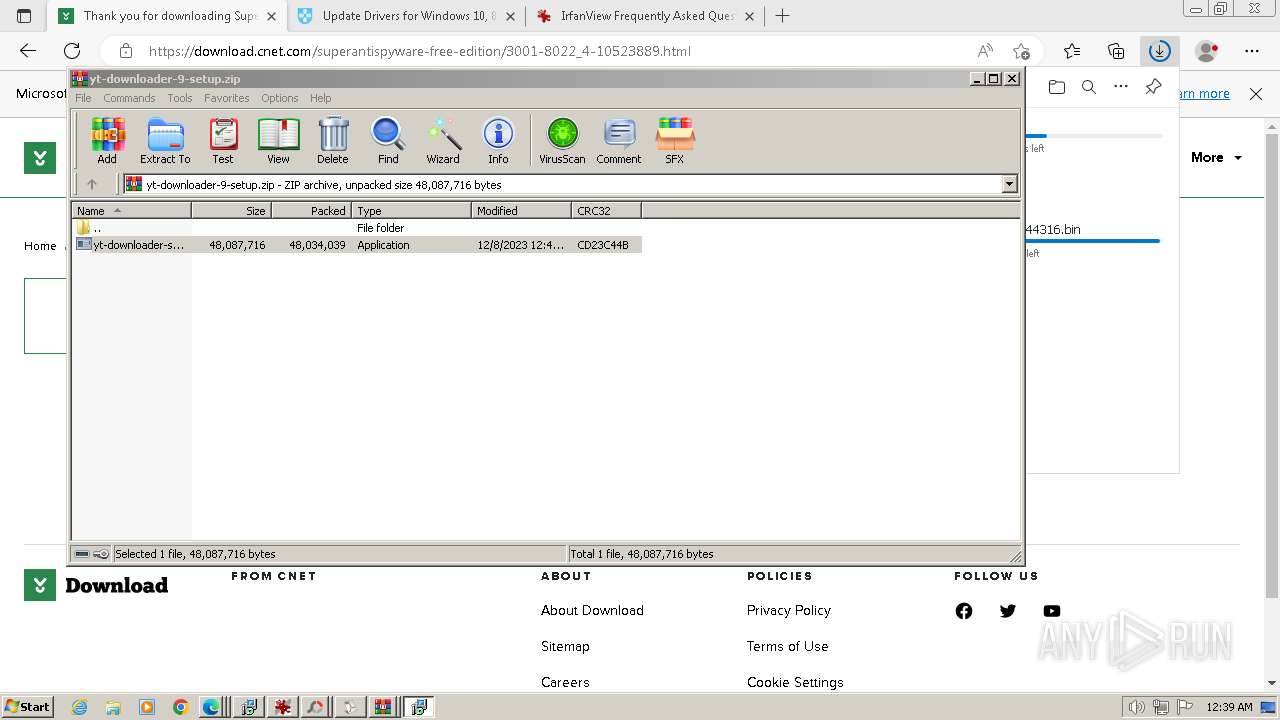
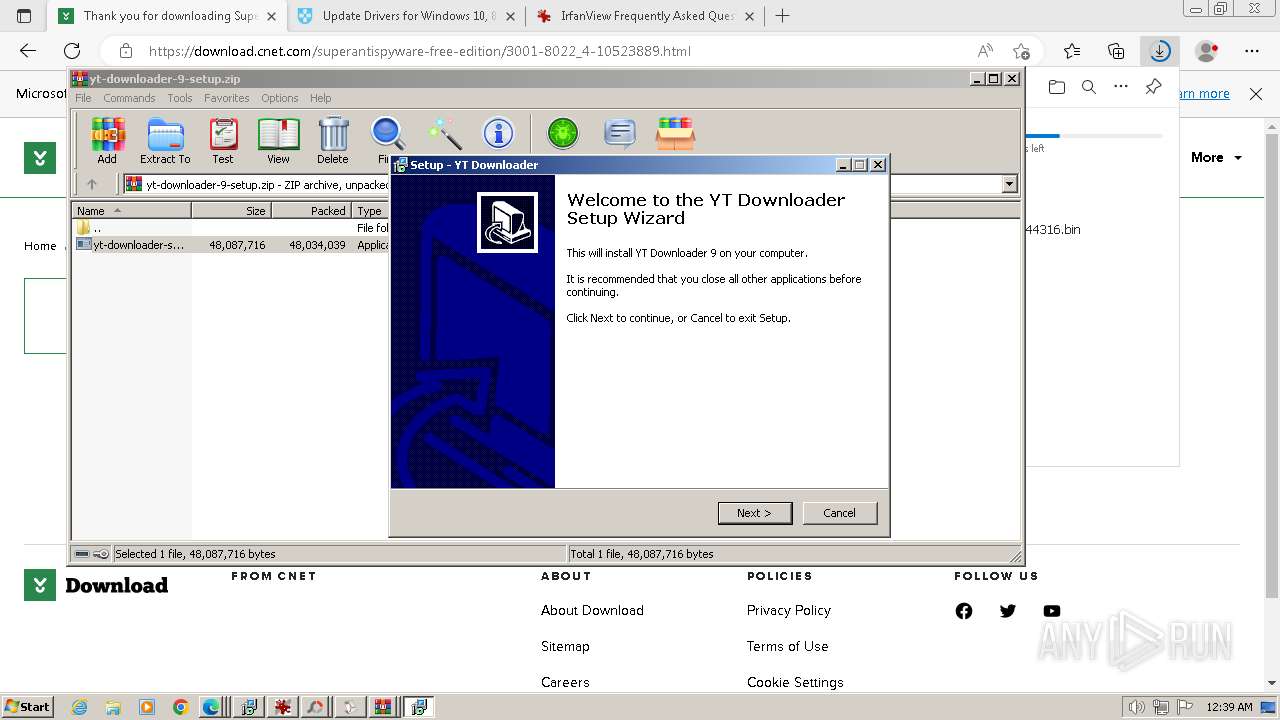
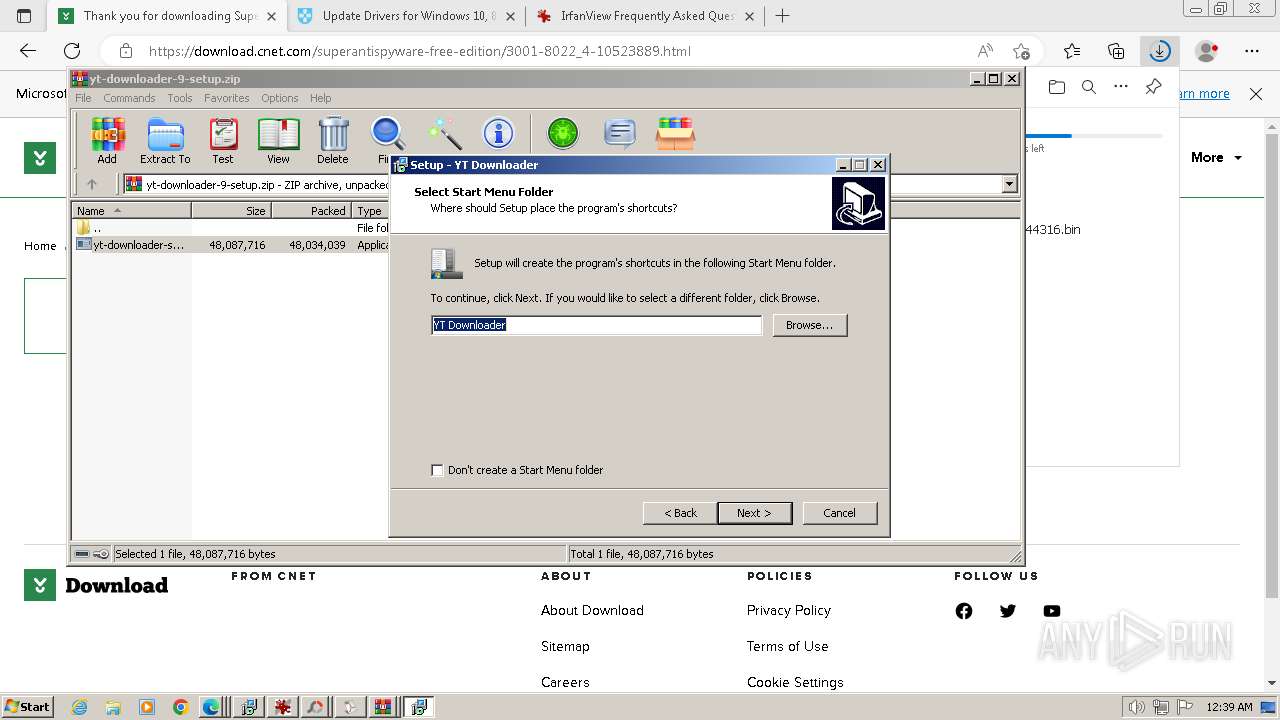
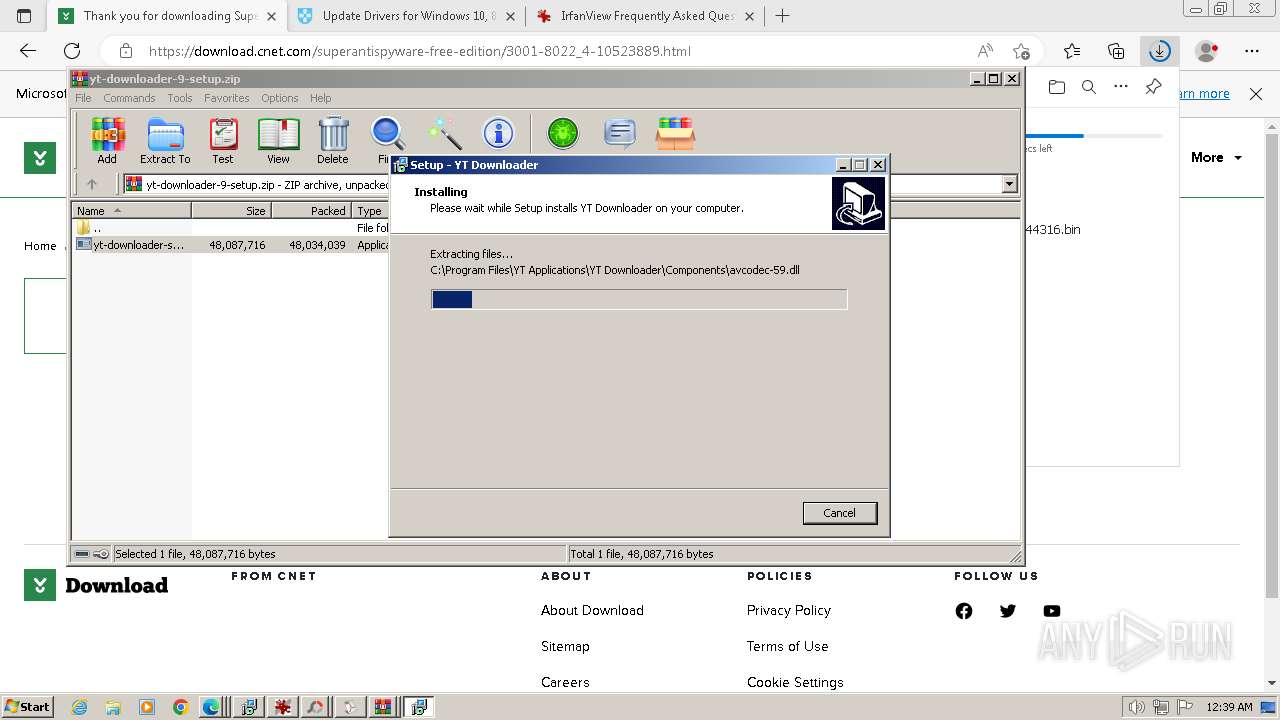
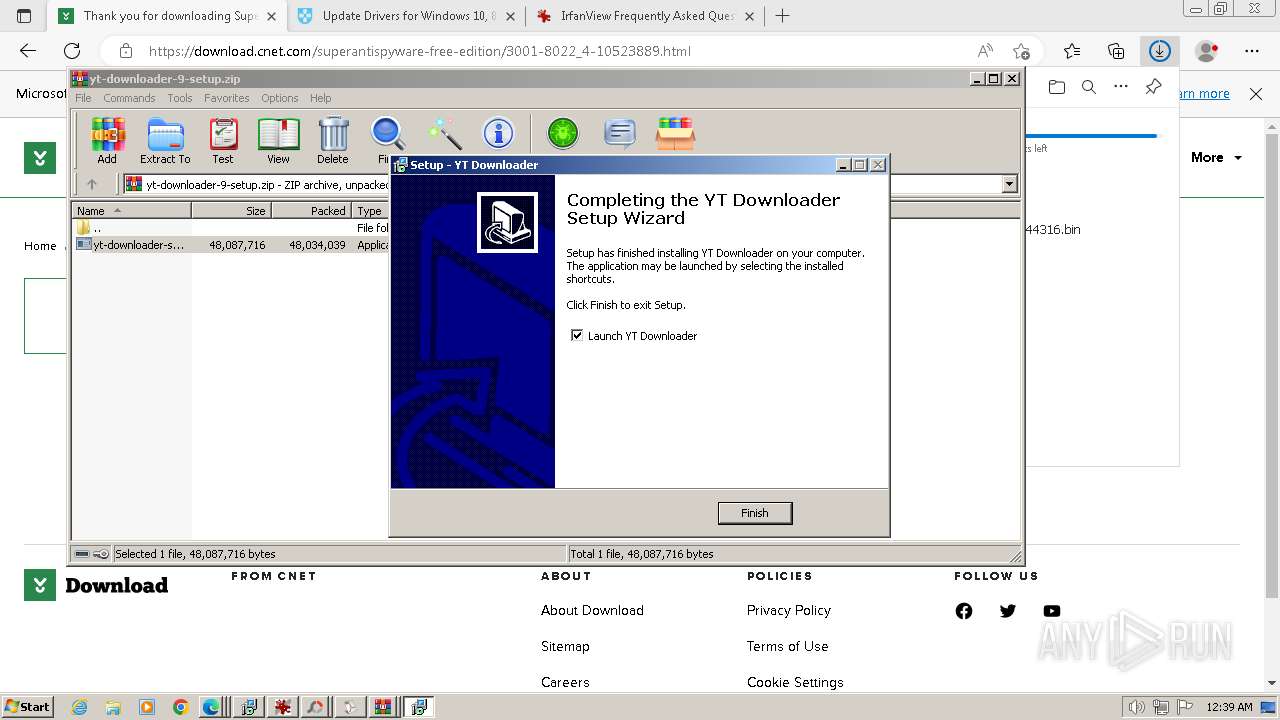
- yt-downloader-setup.exe (PID: 3260)
- yt-downloader-setup.exe (PID: 3008)
- yt-downloader-setup.tmp (PID: 3372)
SUSPICIOUS
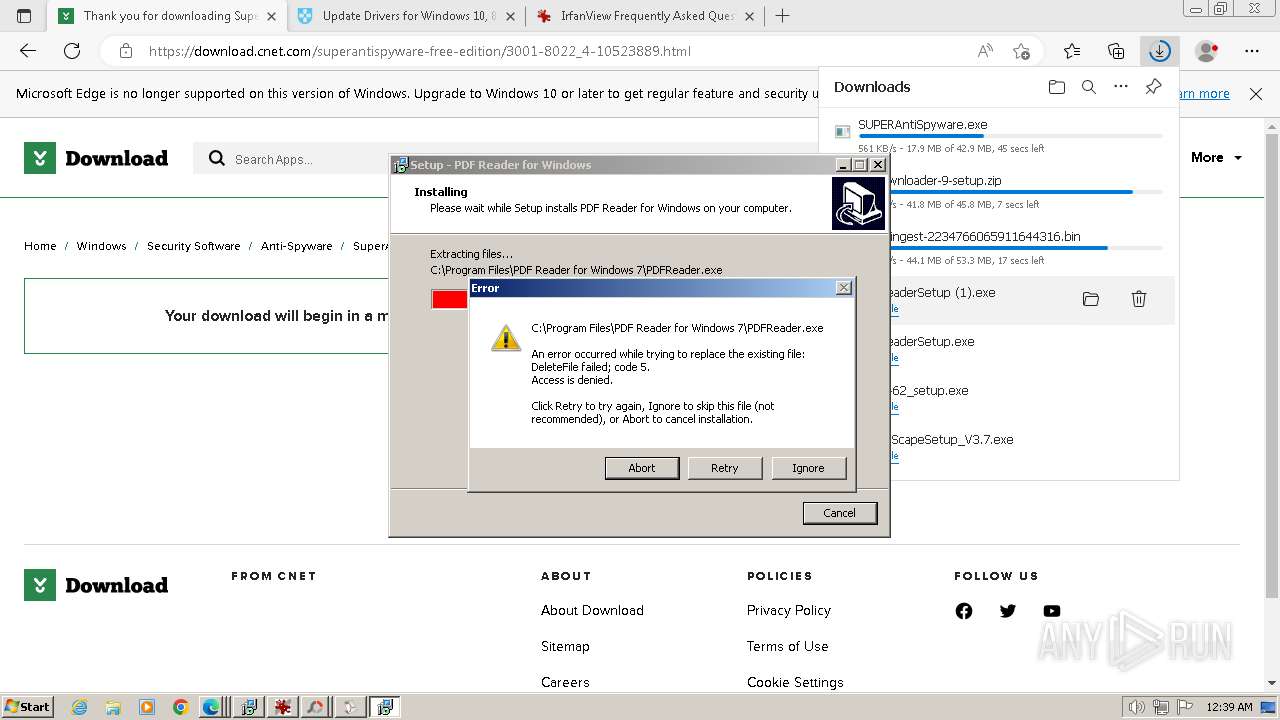
The process creates files with name similar to system file names
- iview462_setup.exe (PID: 2636)
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- GoogleSetup.exe (PID: 4064)
- Mooii_GDrive.exe (PID: 3896)
Reads the Internet Settings
- iview462_setup.exe (PID: 2636)
- GoogleUpdate.exe (PID: 1044)
- GoogleUpdate.exe (PID: 1168)
- GoogleUpdate.exe (PID: 2248)
- GoogleSetup.exe (PID: 4064)
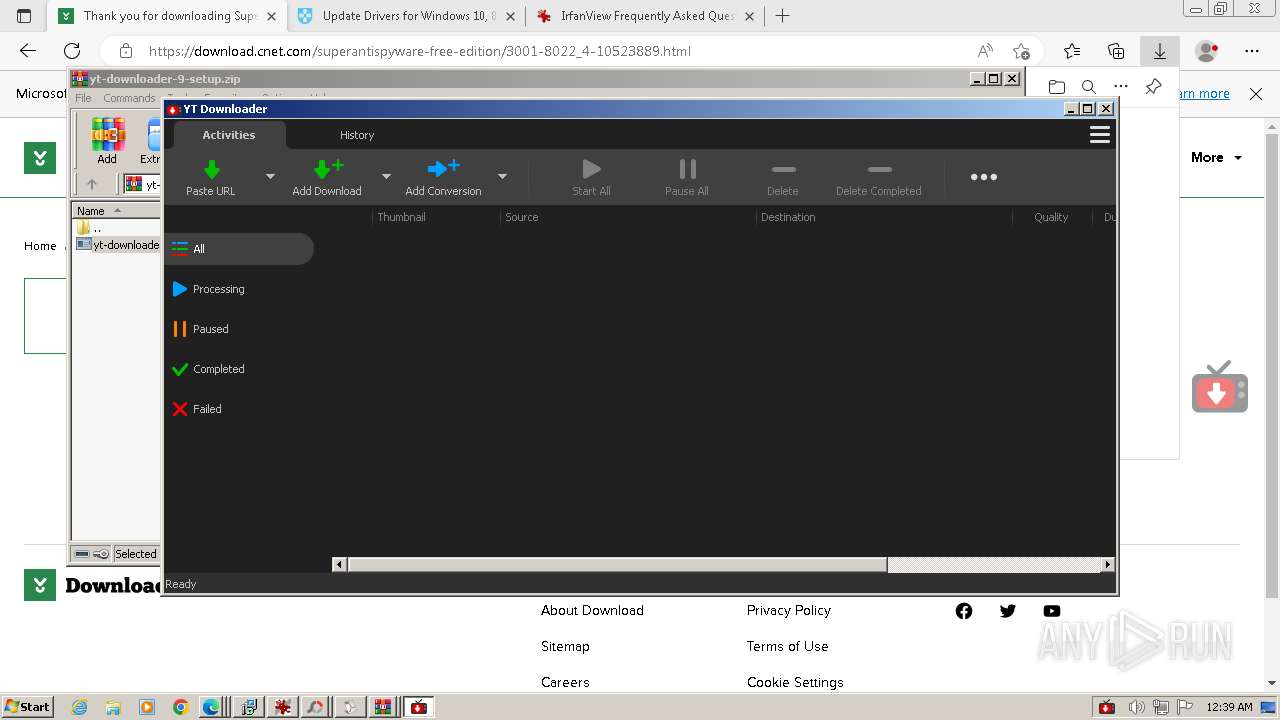
- YTDownloader.exe (PID: 1344)
Process drops legitimate windows executable
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- PDFReaderSetup.tmp (PID: 3628)
- PDFReaderSetup (1).tmp (PID: 3452)
Malware-specific behavior (creating "System.dll" in Temp)
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- Mooii_GDrive.exe (PID: 3896)
- GoogleSetup.exe (PID: 4064)
The process drops C-runtime libraries
- PhotoScapeSetup_V3.7.exe (PID: 3884)
Reads settings of System Certificates
- GoogleUpdate.exe (PID: 2248)
- GoogleUpdate.exe (PID: 1168)
- GoogleUpdate.exe (PID: 1044)
- YTDownloader.exe (PID: 1344)
Application launched itself
- GoogleUpdate.exe (PID: 2248)
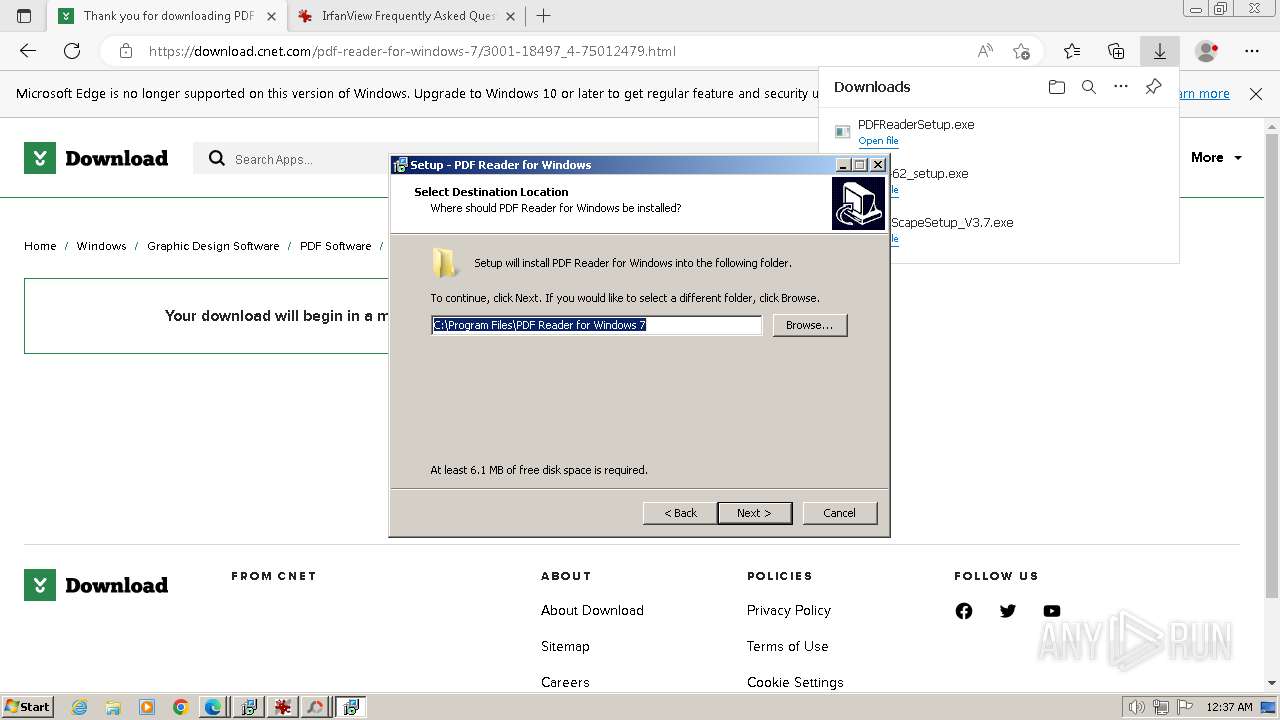
Reads the Windows owner or organization settings
- PDFReaderSetup.tmp (PID: 3628)
- PDFReaderSetup (1).tmp (PID: 3452)
- yt-downloader-setup.tmp (PID: 3372)
Searches for installed software
- PDFReaderSetup (1).tmp (PID: 3452)
Adds/modifies Windows certificates
- YTDownloader.exe (PID: 1344)
INFO
Application launched itself
- iexplore.exe (PID: 2040)
- msedge.exe (PID: 1600)
- msedge.exe (PID: 2592)
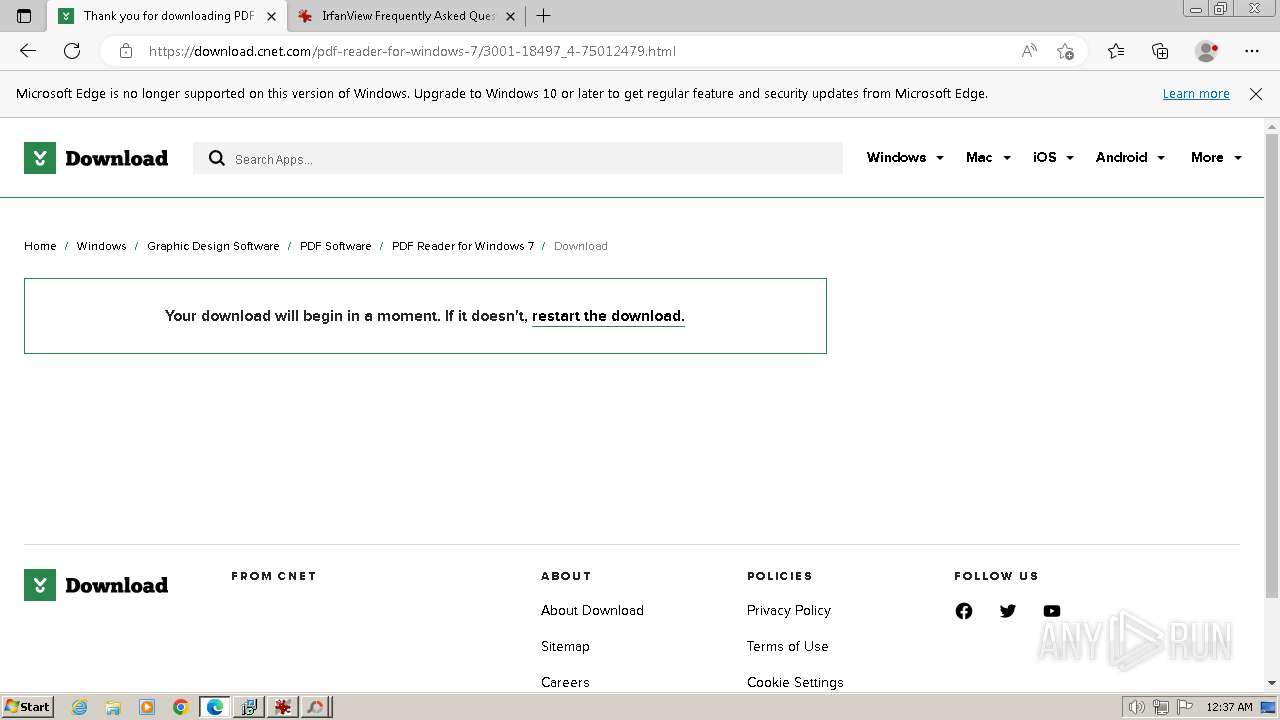
Manual execution by a user
- msedge.exe (PID: 1600)
Checks supported languages
- iview462_setup.exe (PID: 1796)
- iview462_setup.exe (PID: 2636)
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- PhotoScapeSetup_V3.7.exe (PID: 3892)
- GTGCAPI.exe (PID: 2848)
- GTGCAPI.exe (PID: 2744)
- GTGCAPI.exe (PID: 3708)
- GTGCAPI.exe (PID: 3792)
- GTGCAPI.exe (PID: 3908)
- i_view32.exe (PID: 2576)
- Mooii_GDrive.exe (PID: 3896)
- GoogleUpdateSetup_latest.exe (PID: 1172)
- GoogleUpdate.exe (PID: 3860)
- GoogleSetup.exe (PID: 4064)
- GoogleUpdate.exe (PID: 1044)
- GoogleUpdate.exe (PID: 1168)
- GoogleUpdate.exe (PID: 2248)
- PDFReaderSetup.exe (PID: 2316)
- PDFReaderSetup.tmp (PID: 2240)
- PDFReaderSetup.exe (PID: 1820)
- PDFReaderSetup.tmp (PID: 3628)
- GTGCAPI.exe (PID: 1880)
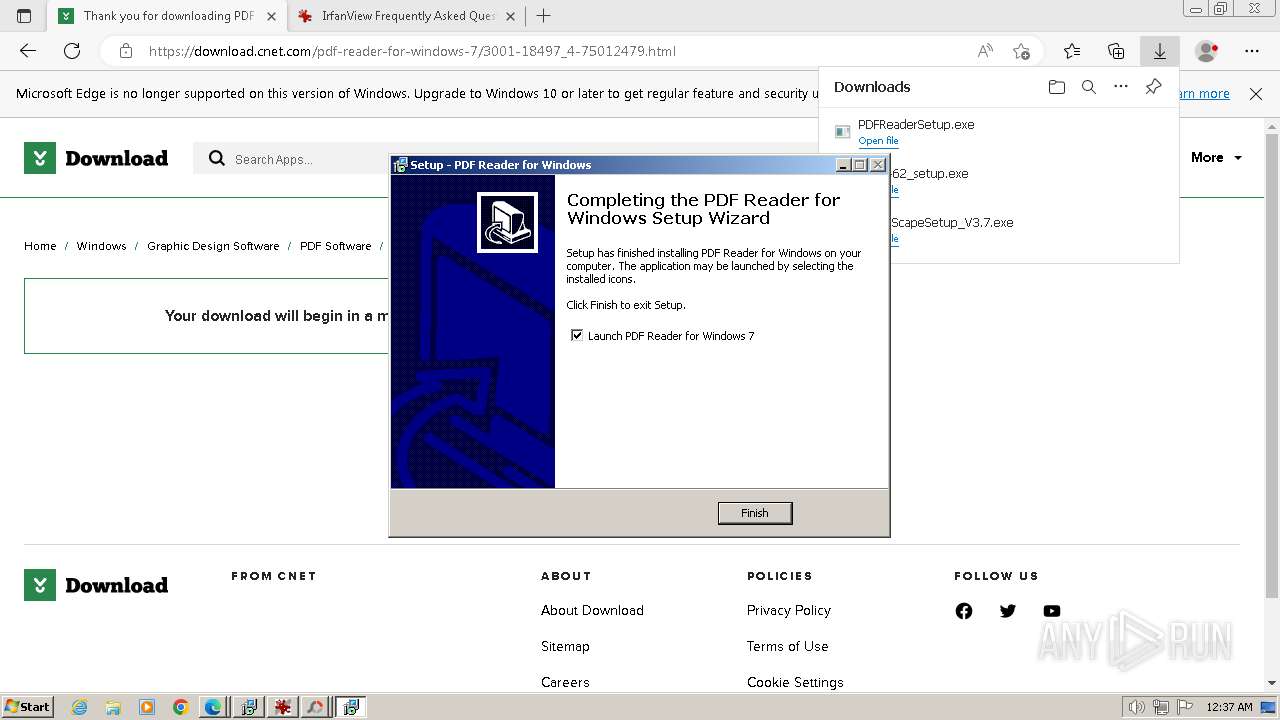
- PDFReader.exe (PID: 3388)
- PDFReaderSetup (1).exe (PID: 3744)
- PDFReaderSetup (1).tmp (PID: 3648)
- PDFReaderSetup (1).tmp (PID: 3452)
- PDFReaderSetup (1).exe (PID: 2148)
- yt-downloader-setup.exe (PID: 3260)
- yt-downloader-setup.tmp (PID: 3372)
- yt-downloader-setup.exe (PID: 3008)
- yt-downloader-setup.tmp (PID: 3652)
- YTDownloader.exe (PID: 1344)
- MediaPlay.exe (PID: 2736)
Create files in a temporary directory
- iview462_setup.exe (PID: 2636)
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- PhotoScapeSetup_V3.7.exe (PID: 3892)
- GoogleSetup.exe (PID: 4064)
- Mooii_GDrive.exe (PID: 3896)
- PDFReaderSetup.exe (PID: 2316)
- PDFReaderSetup.exe (PID: 1820)
- PDFReaderSetup (1).exe (PID: 3744)
- PDFReaderSetup.tmp (PID: 3628)
- PDFReaderSetup (1).tmp (PID: 3452)
- PDFReaderSetup (1).exe (PID: 2148)
- yt-downloader-setup.exe (PID: 3260)
- yt-downloader-setup.exe (PID: 3008)
The process uses the downloaded file
- msedge.exe (PID: 1608)
- msedge.exe (PID: 1316)
- msedge.exe (PID: 1600)
- msedge.exe (PID: 2172)
- msedge.exe (PID: 3040)
- msedge.exe (PID: 3512)
- WinRAR.exe (PID: 3536)
- msedge.exe (PID: 2244)
- msedge.exe (PID: 2744)
Creates files in the program directory
- iview462_setup.exe (PID: 2636)
- GoogleUpdateSetup_latest.exe (PID: 1172)
- GoogleUpdate.exe (PID: 3860)
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- PDFReaderSetup.tmp (PID: 3628)
- yt-downloader-setup.tmp (PID: 3372)
- PDFReaderSetup (1).tmp (PID: 3452)
Reads product name
- iview462_setup.exe (PID: 2636)
Reads Environment values
- iview462_setup.exe (PID: 2636)
Drops the executable file immediately after the start
- msedge.exe (PID: 2800)
- msedge.exe (PID: 1600)
Reads the computer name
- iview462_setup.exe (PID: 2636)
- PhotoScapeSetup_V3.7.exe (PID: 3892)
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- Mooii_GDrive.exe (PID: 3896)
- GoogleUpdate.exe (PID: 3860)
- GoogleSetup.exe (PID: 4064)
- GoogleUpdate.exe (PID: 1168)
- GoogleUpdate.exe (PID: 2248)
- GoogleUpdate.exe (PID: 1044)
- PDFReaderSetup.tmp (PID: 2240)
- PDFReaderSetup.tmp (PID: 3628)
- PDFReaderSetup (1).tmp (PID: 3648)
- yt-downloader-setup.tmp (PID: 3372)
- PDFReaderSetup (1).tmp (PID: 3452)
- yt-downloader-setup.tmp (PID: 3652)
- YTDownloader.exe (PID: 1344)
Creates files or folders in the user directory
- iview462_setup.exe (PID: 2636)
- GoogleSetup.exe (PID: 4064)
- PhotoScapeSetup_V3.7.exe (PID: 3884)
- yt-downloader-setup.tmp (PID: 3372)
Reads the machine GUID from the registry
- GoogleUpdate.exe (PID: 3860)
- GoogleUpdate.exe (PID: 2248)
- GoogleUpdate.exe (PID: 1168)
- GoogleUpdate.exe (PID: 1044)
- GoogleSetup.exe (PID: 4064)
- YTDownloader.exe (PID: 1344)
- MediaPlay.exe (PID: 2736)
Checks proxy server information
- GoogleSetup.exe (PID: 4064)
- YTDownloader.exe (PID: 1344)
Dropped object may contain TOR URL's
- yt-downloader-setup.tmp (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
166
Monitored processes
109
Malicious processes
19
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1640 --field-trial-handle=1336,i,6824194214733965973,14769674723039847921,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=4280 --field-trial-handle=1336,i,6824194214733965973,14769674723039847921,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=48 --mojo-platform-channel-handle=4212 --field-trial-handle=1336,i,6824194214733965973,14769674723039847921,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6e51f598,0x6e51f5a8,0x6e51f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --mojo-platform-channel-handle=1180 --field-trial-handle=1336,i,6824194214733965973,14769674723039847921,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=1556 --field-trial-handle=1336,i,6824194214733965973,14769674723039847921,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4zNi4zMiIgc2hlbGxfdmVyc2lvbj0iMS4zLjMzLjIzIiBpc21hY2hpbmU9IjEiIHNlc3Npb25pZD0ie0MwODcxNzZGLTAwRjEtNDFCNC05OERCLTVBNzgxMjVDMkUyOX0iIGluc3RhbGxzb3VyY2U9Im90aGVyaW5zdGFsbGNtZCIgcmVxdWVzdGlkPSJ7REYxRjk4NTQtRTY3Ri00RDUyLTgyM0QtMEE4MkNERTAwMEE0fSIgZGVkdXA9ImNyIiBkb21haW5qb2luZWQ9IjAiPjxodyBwaHlzbWVtb3J5PSIzIiBzc2U9IjEiIHNzZTI9IjEiIHNzZTM9IjEiIHNzc2UzPSIxIiBzc2U0MT0iMSIgc3NlNDI9IjEiIGF2eD0iMSIvPjxvcyBwbGF0Zm9ybT0id2luIiB2ZXJzaW9uPSI2LjEuNzYwMS4yNDU0NiIgc3A9IlNlcnZpY2UgUGFjayAxIiBhcmNoPSJ4ODYiLz48YXBwIGFwcGlkPSJ7M0MxMjI0NDUtQUVDRS00MzA5LTkwQjctODVBNkFFRjQyQUMwfSIgdmVyc2lvbj0iIiBuZXh0dmVyc2lvbj0iIiBsYW5nPSIiIGJyYW5kPSJKWFNKIiBjbGllbnQ9IiIgaW5zdGFsbGFnZT0iLTEiIGluc3RhbGxkYXRlPSItMSI-PGV2ZW50IGV2ZW50dHlwZT0iMiIgZXZlbnRyZXN1bHQ9IjAiIGVycm9yY29kZT0iLTIxNDcyMTk0NDciIGV4dHJhY29kZTE9IjI2ODQzNTQ1OSIgdXBkYXRlX2NoZWNrX3RpbWVfbXM9IjIyMSIvPjwvYXBwPjwvcmVxdWVzdD4 | C:\Program Files\Google\Update\GoogleUpdate.exe | GoogleUpdate.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2040 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB2ZXJzaW9uPSIxLjMuMjEuMTIzIiBzaGVsbF92ZXJzaW9uPSIxLjMuMjEuMTAzIiBpc21hY2hpbmU9IjEiIHNlc3Npb25pZD0ie0MwODcxNzZGLTAwRjEtNDFCNC05OERCLTVBNzgxMjVDMkUyOX0iIGluc3RhbGxzb3VyY2U9Im90aGVyaW5zdGFsbGNtZCIgcmVxdWVzdGlkPSJ7RkU1RUEyNDQtNDA4QS00NUU0LUI0ODUtRTVGRjI4REU0MUQ5fSI-PG9zIHBsYXRmb3JtPSJ3aW4iIHZlcnNpb249IjYuMSIgc3A9IlNlcnZpY2UgUGFjayAxIiBhcmNoPSJ4ODYiLz48YXBwIGFwcGlkPSJ7NDMwRkQ0RDAtQjcyOS00RjYxLUFBMzQtOTE1MjY0ODE3OTlEfSIgdmVyc2lvbj0iMS4zLjM2LjMyIiBuZXh0dmVyc2lvbj0iMS4zLjIxLjEyMyIgbGFuZz0iIiBicmFuZD0iSlhTSiIgY2xpZW50PSIiPjxldmVudCBldmVudHR5cGU9IjIiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiLz48L2FwcD48L3JlcXVlc3Q- | C:\Program Files\Google\Update\GoogleUpdate.exe | GoogleUpdate.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 1172 | C:\Users\admin\AppData\Local\Temp\GoogleUpdateSetup_latest.exe /silent /install "appguid={3C122445-AECE-4309-90B7-85A6AEF42AC0}&appname=Google%20Drive&needsadmin=true&brand=JXSJ" | C:\Users\admin\AppData\Local\Temp\GoogleUpdateSetup_latest.exe | — | Mooii_GDrive.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Update Setup Exit code: 2147747849 Version: 1.3.21.123 Modules
| |||||||||||||||
Total events
55 112
Read events
54 702
Write events
374
Delete events
36
Modification events
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
223
Suspicious files
1 273
Text files
1 744
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFA3F.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:659B59DB9303EA2ED1B5C7B1AF089A4A | SHA256:DC8D4678C91F56959C05F32230F41A9804D086D299E9DB0D653A03F8D8FA2116 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\3XG1DOXF.htm | html | |
MD5:DD64A9C850A6345A30B27A8604839F58 | SHA256:D66728FE81FD8767BEA6EFB50C6651BC92F2A8DA2D441C148F6C726531EC3A26 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:978B4AF17C8BEE99958F1360CCC90CE7 | SHA256:D30B6191D1AB75B06ADA8930C476E4D2A616312B78EC4D4241D1260DE7CC46FD | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFA40.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFA50.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFA51.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\samsung-mg11t5018cc-microwave[1].jpg | image | |
MD5:B07BCF702AC528D5CAC2495F688B73E7 | SHA256:A93BE08B7AA77F43548B38739E3906D4ECB7983917A7D46FE6386B4EC4B7F2BB | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\stsci-k218b[1].jpg | image | |
MD5:6022784AF0BC8AA285D89FB2C20E99B7 | SHA256:E48FCBEE8D9F8BD5E703F8239B99E6DC312A23E067D5FDD0AA19500AB7B2EF78 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
302
DNS requests
309
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
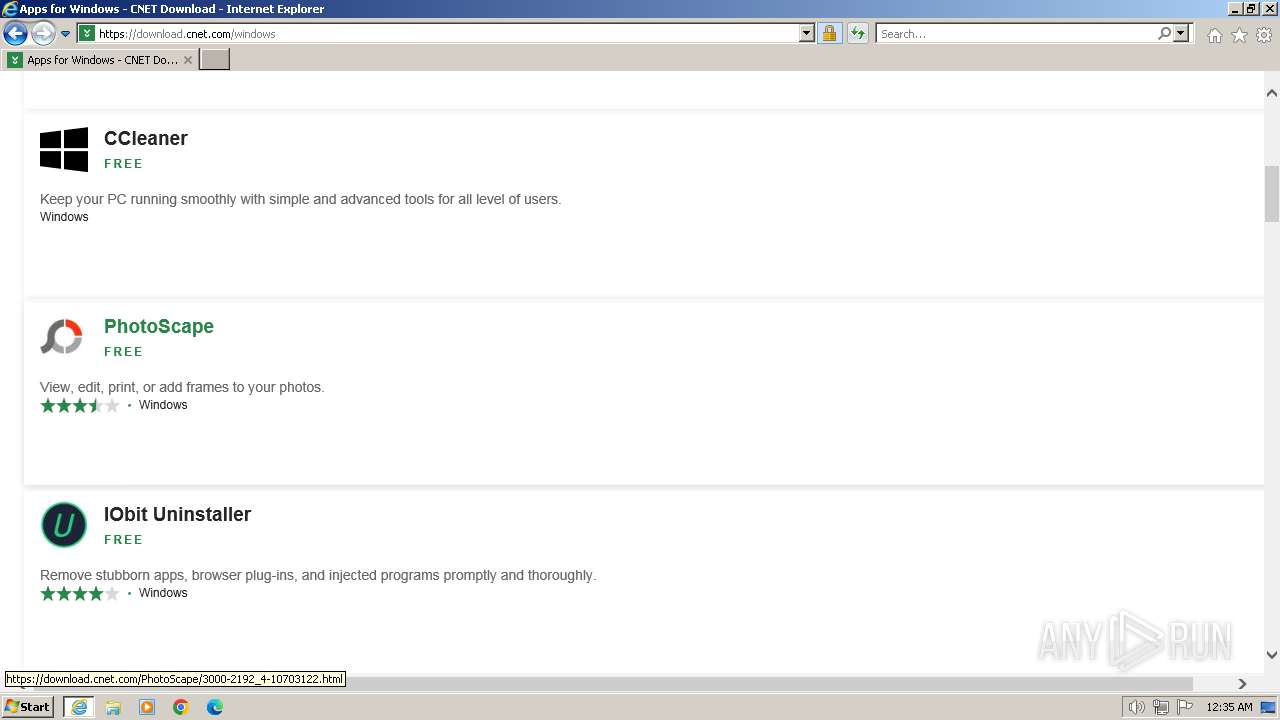
1056 | iexplore.exe | GET | 301 | 34.149.2.250:80 | http://download.com/ | unknown | html | 169 b | unknown |
1056 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?608cb4ab6d3f68d3 | unknown | compressed | 65.2 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?16e53a13f7f2d96f | unknown | compressed | 4.66 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?08963e2848236aa7 | unknown | compressed | 4.66 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7a9d8baceff24343 | unknown | compressed | 65.2 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1056 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 108.138.2.195:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1056 | iexplore.exe | 34.149.2.250:80 | download.com | GOOGLE | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1056 | iexplore.exe | 199.232.194.154:443 | download.cnet.com | FASTLY | US | unknown |
1056 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1056 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
1056 | iexplore.exe | 151.101.194.154:443 | at.adtech.redventures.io | FASTLY | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1056 | iexplore.exe | 172.64.149.180:443 | js-sec.indexww.com | CLOUDFLARENET | US | unknown |
1056 | iexplore.exe | 151.101.1.91:443 | spn-v1.revampcdn.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
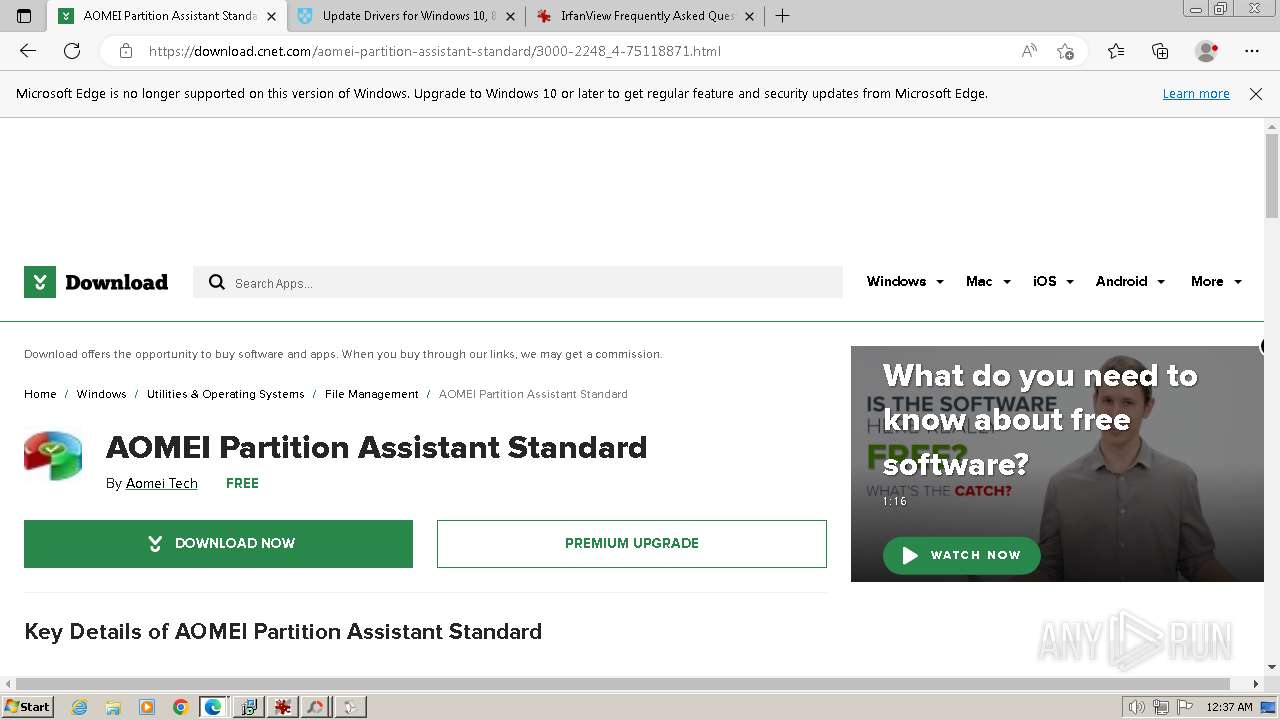
download.com |
| whitelisted |
download.cnet.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
spn-v1.revampcdn.com |
| unknown |
at.adtech.redventures.io |
| unknown |
securepubads.g.doubleclick.net |
| whitelisted |
js-sec.indexww.com |
| whitelisted |
c.amazon-adsystem.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4064 | GoogleSetup.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
Process | Message |
|---|---|
GoogleUpdate.exe | LOG_SYSTEM: [GoogleUpdate:goopdate]: ERROR - Cannot create ETW log writer |