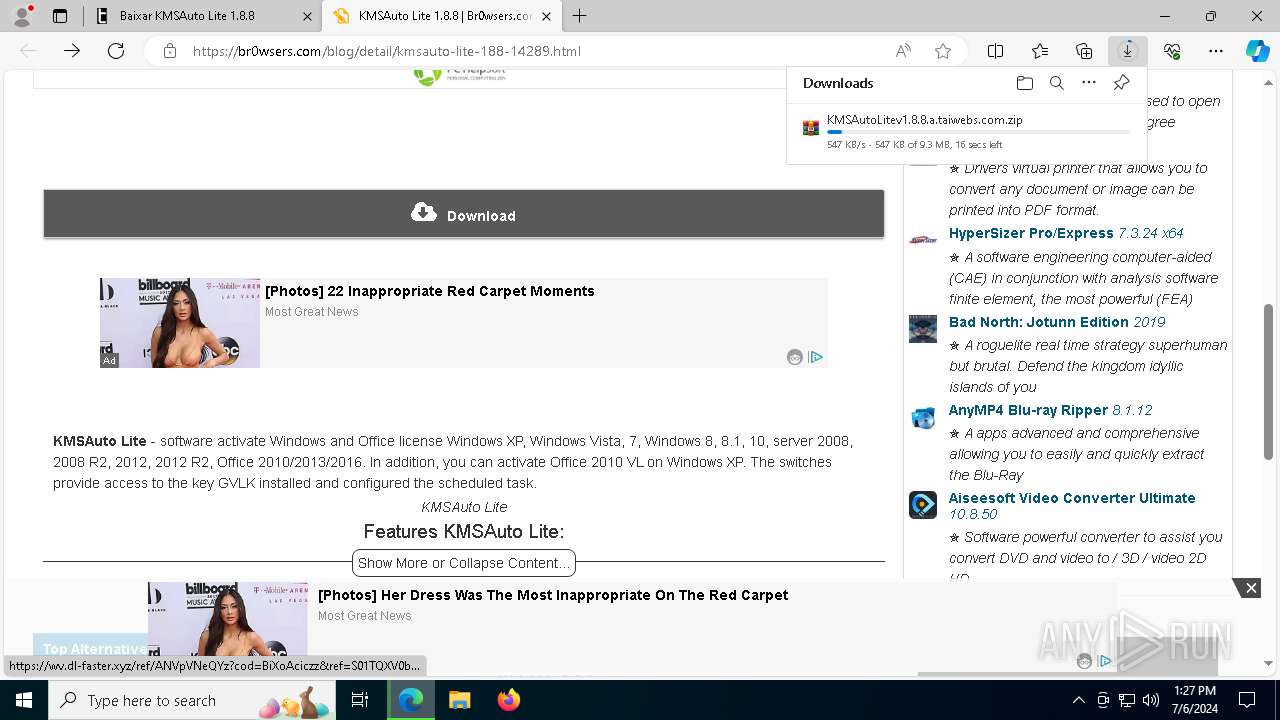
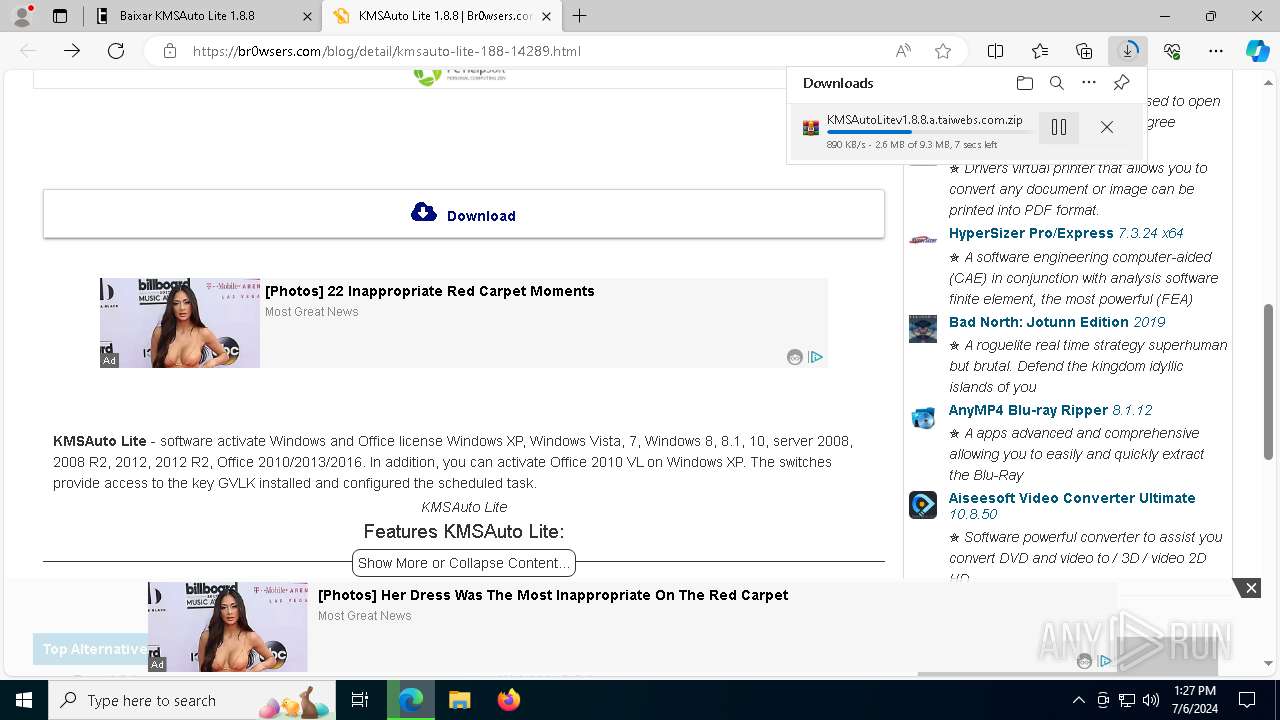
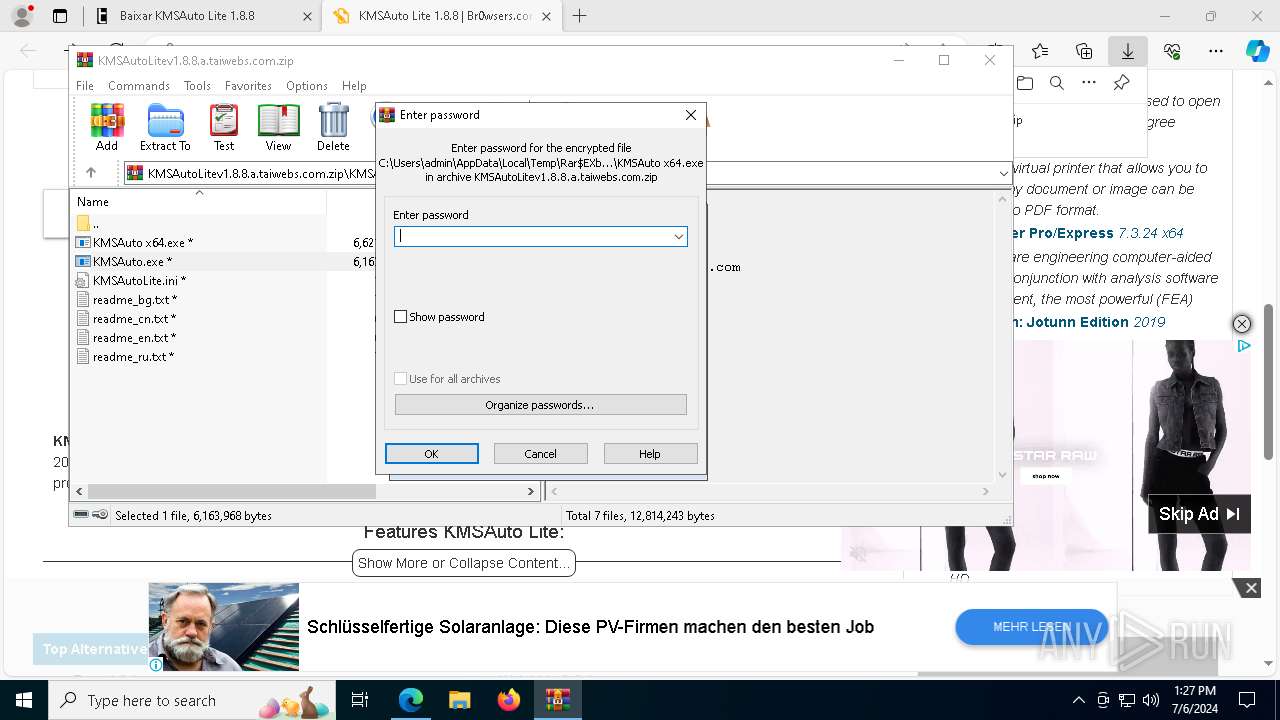
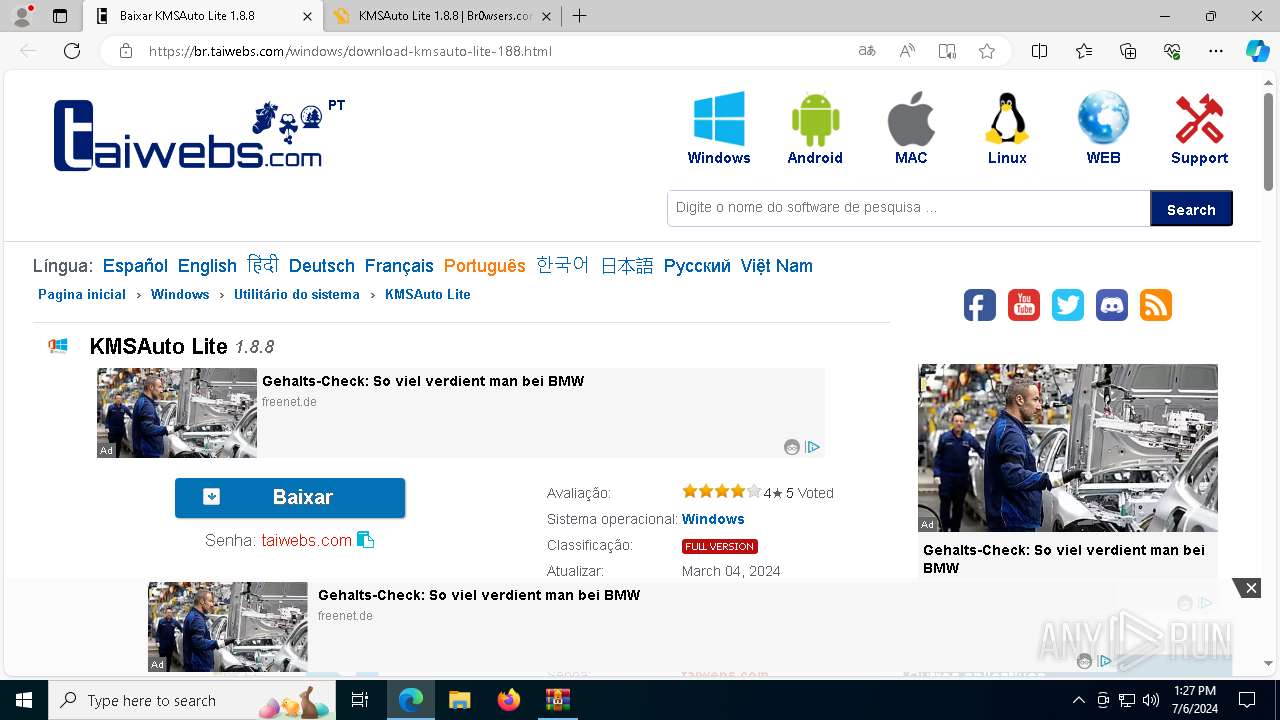
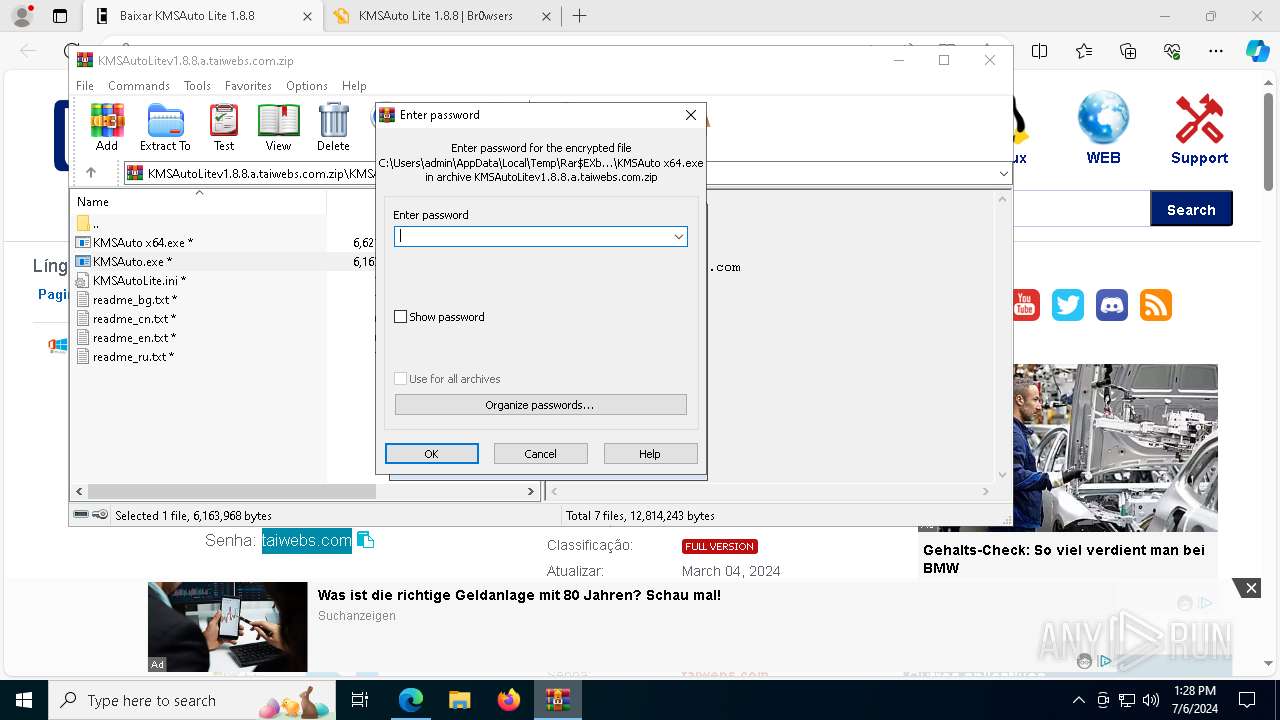
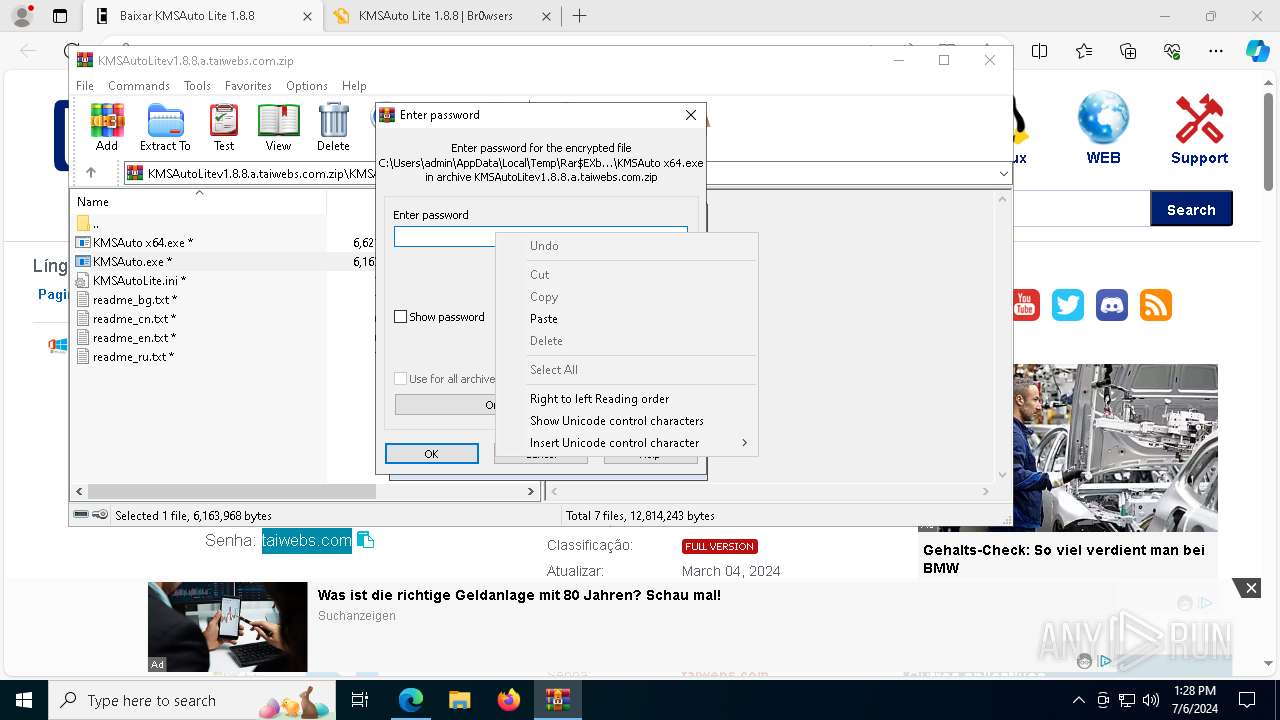
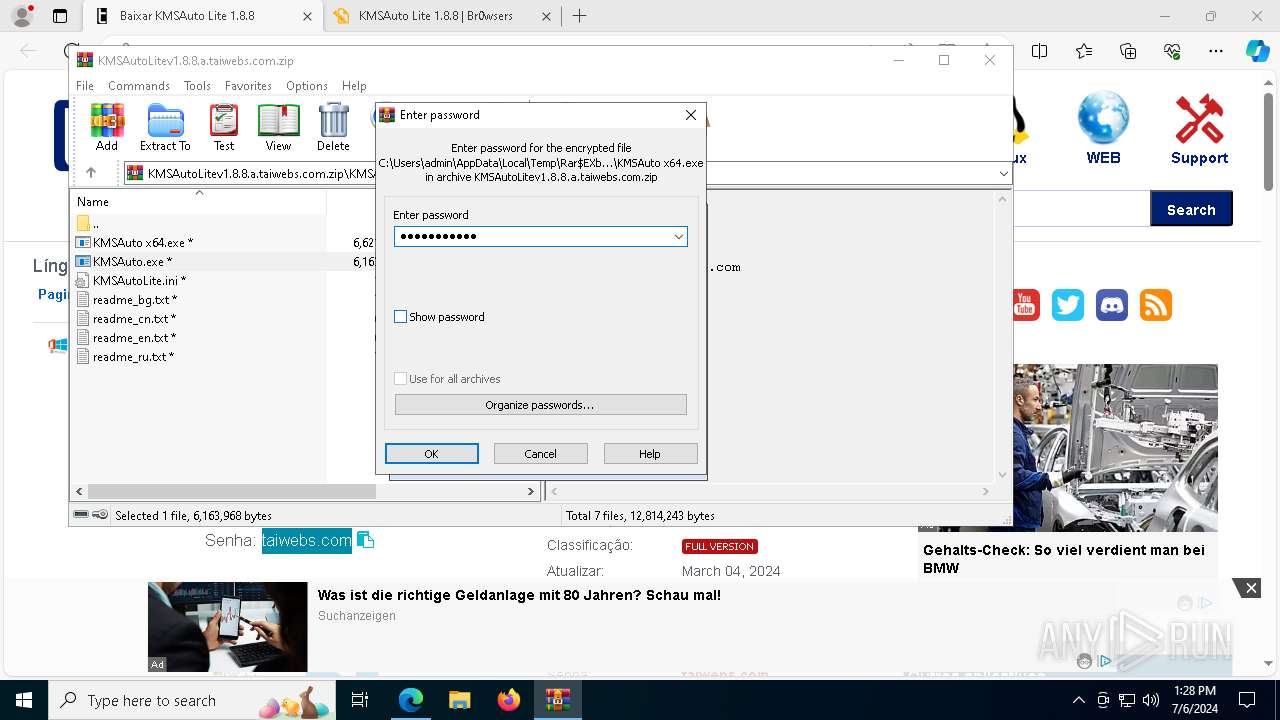
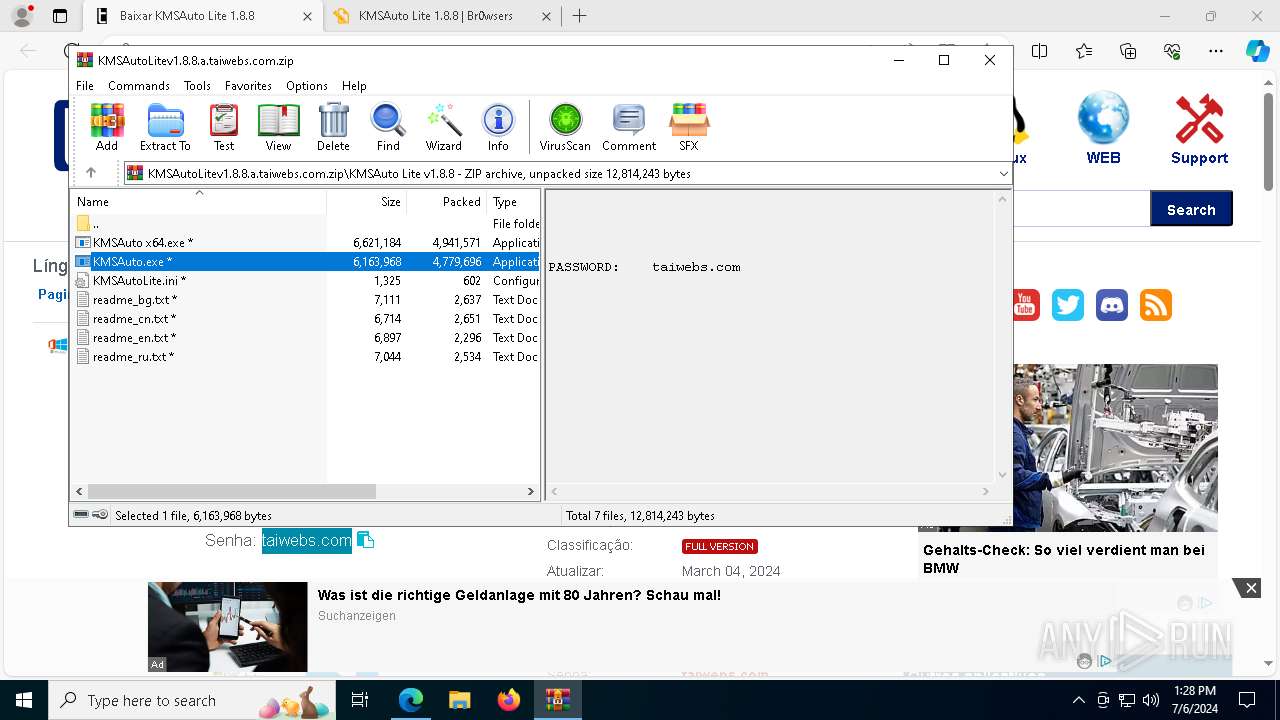
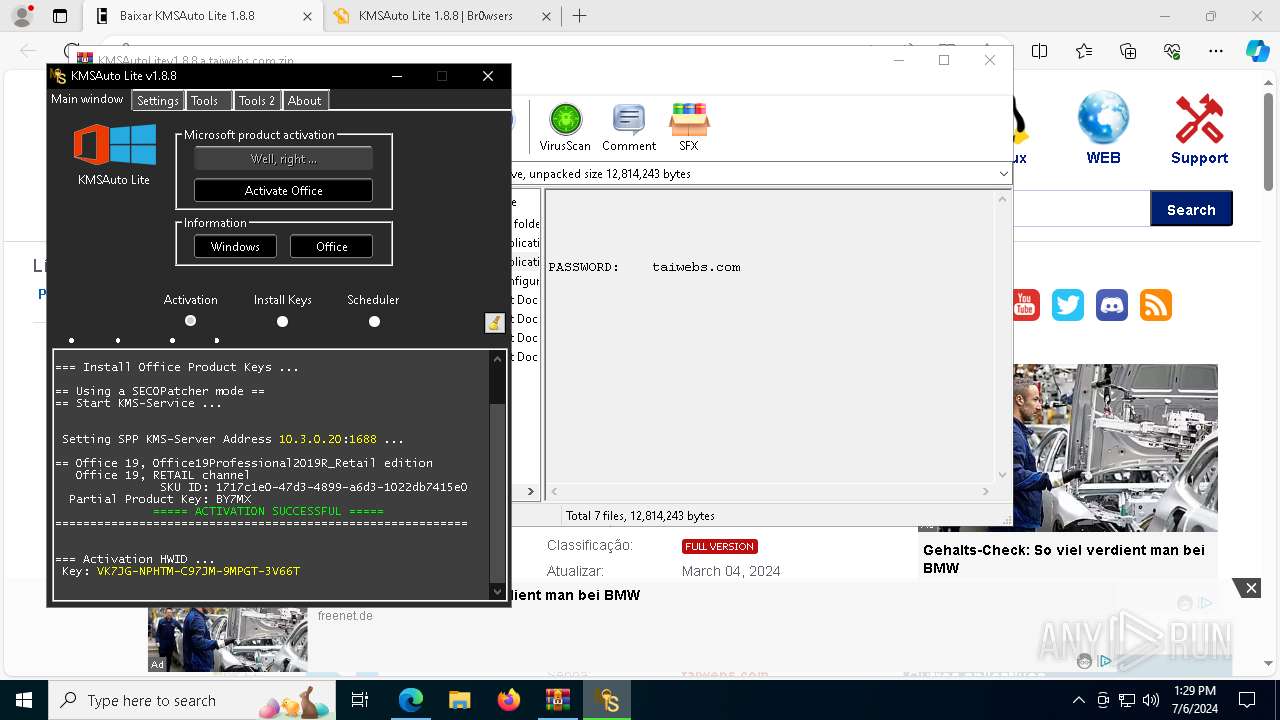
| URL: | https://br.taiwebs.com/windows/download-kmsauto-lite-188.html |
| Full analysis: | https://app.any.run/tasks/272054e1-298c-40eb-8e4b-eddb6b944f44 |
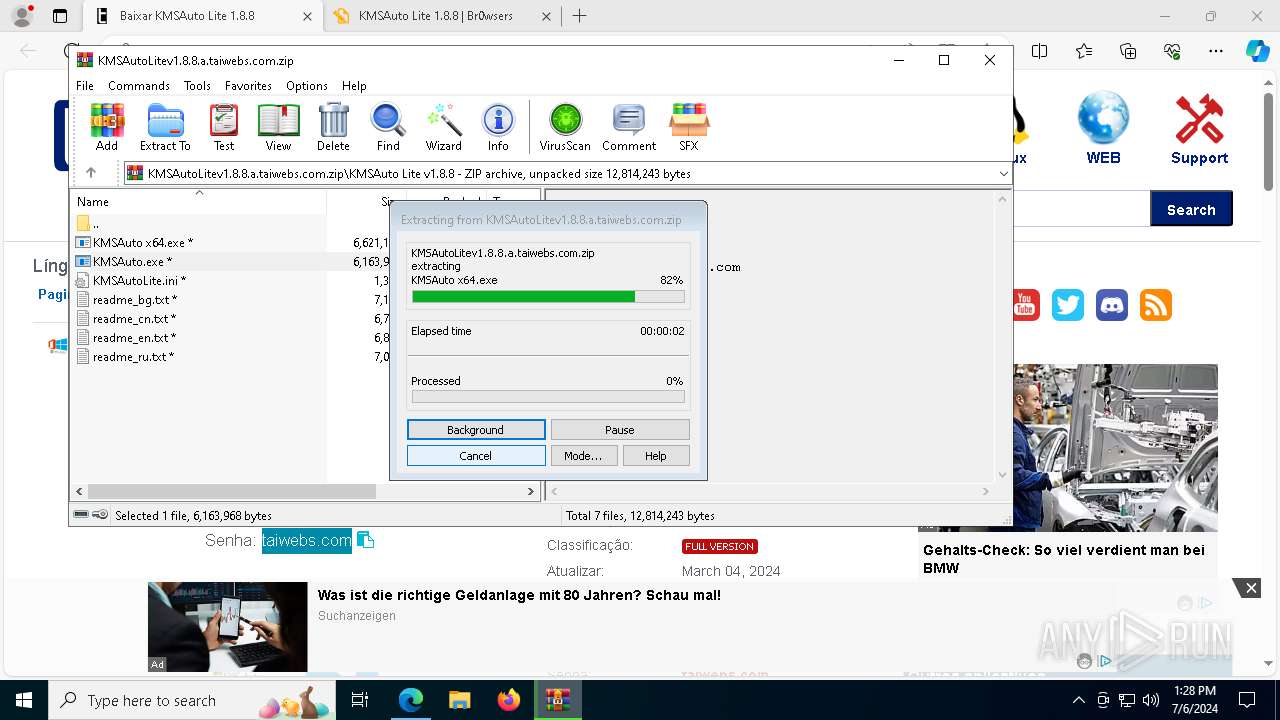
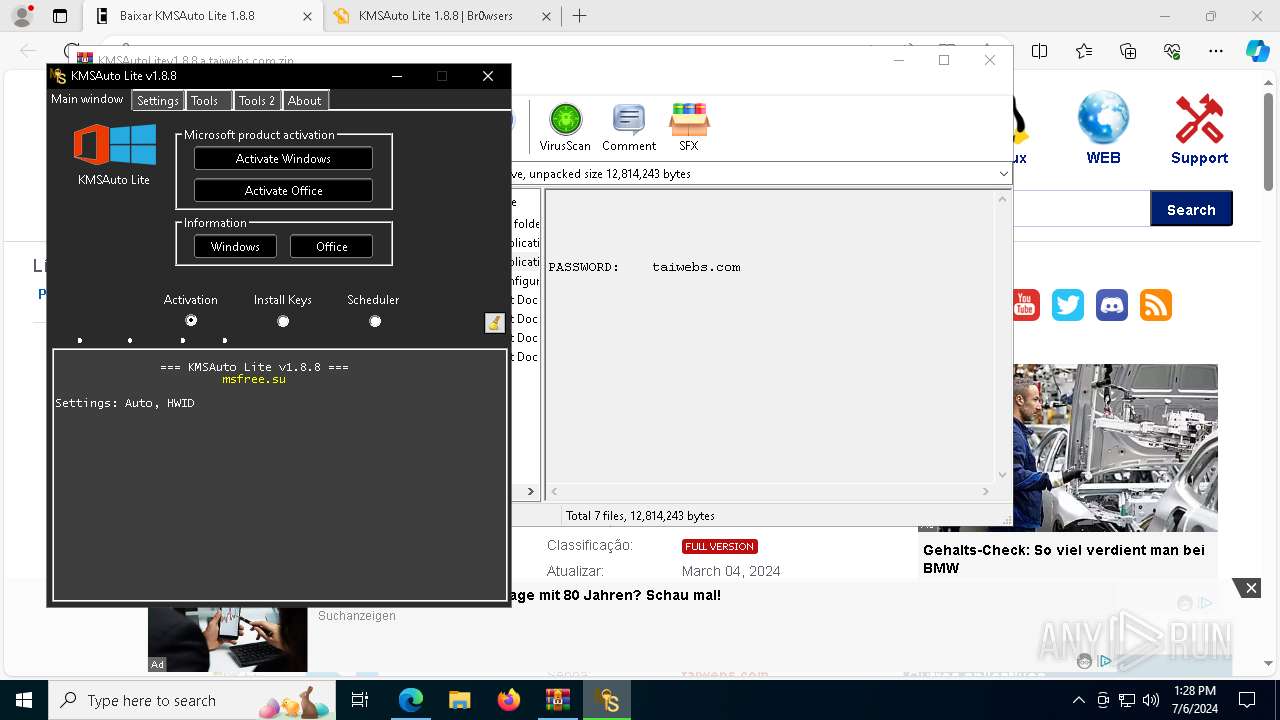
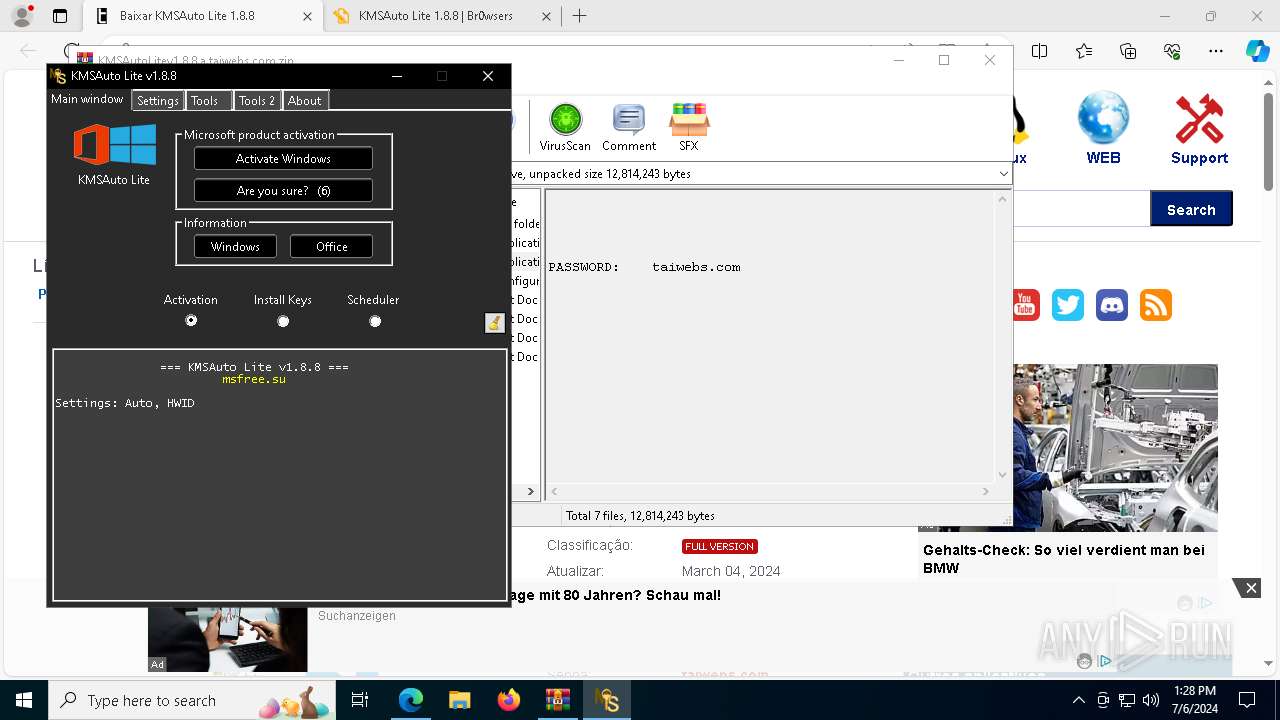
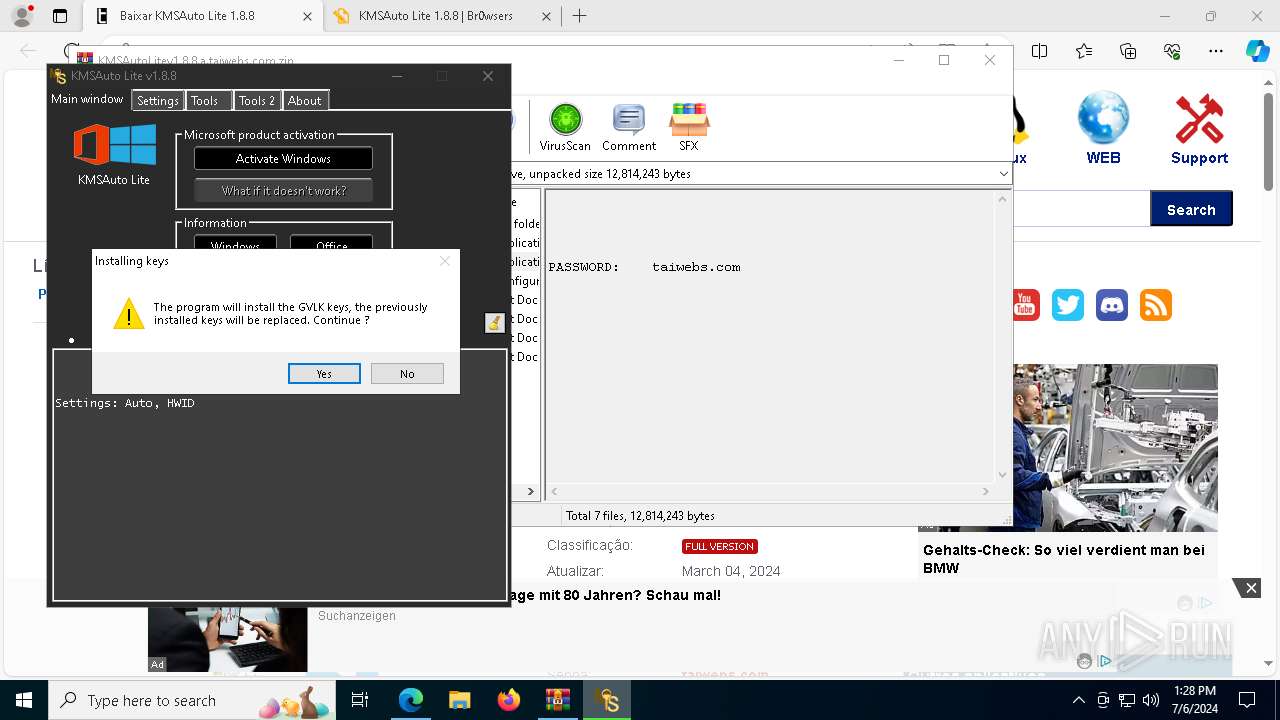
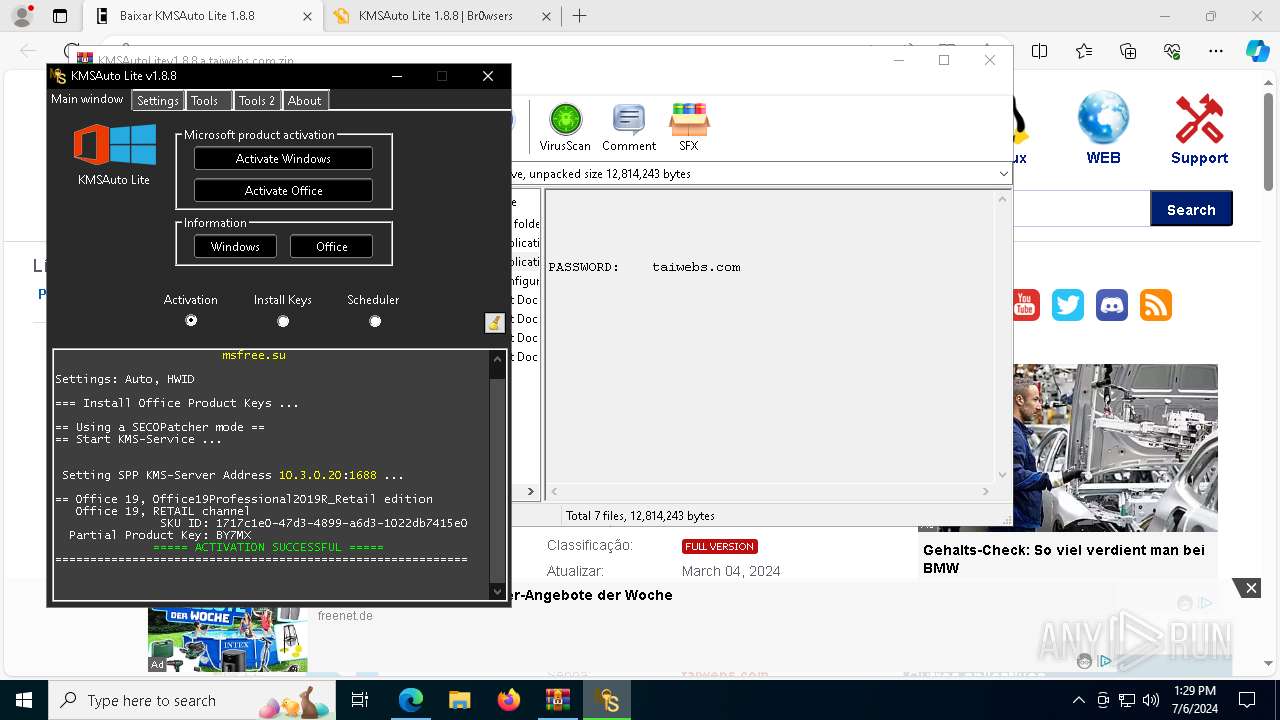
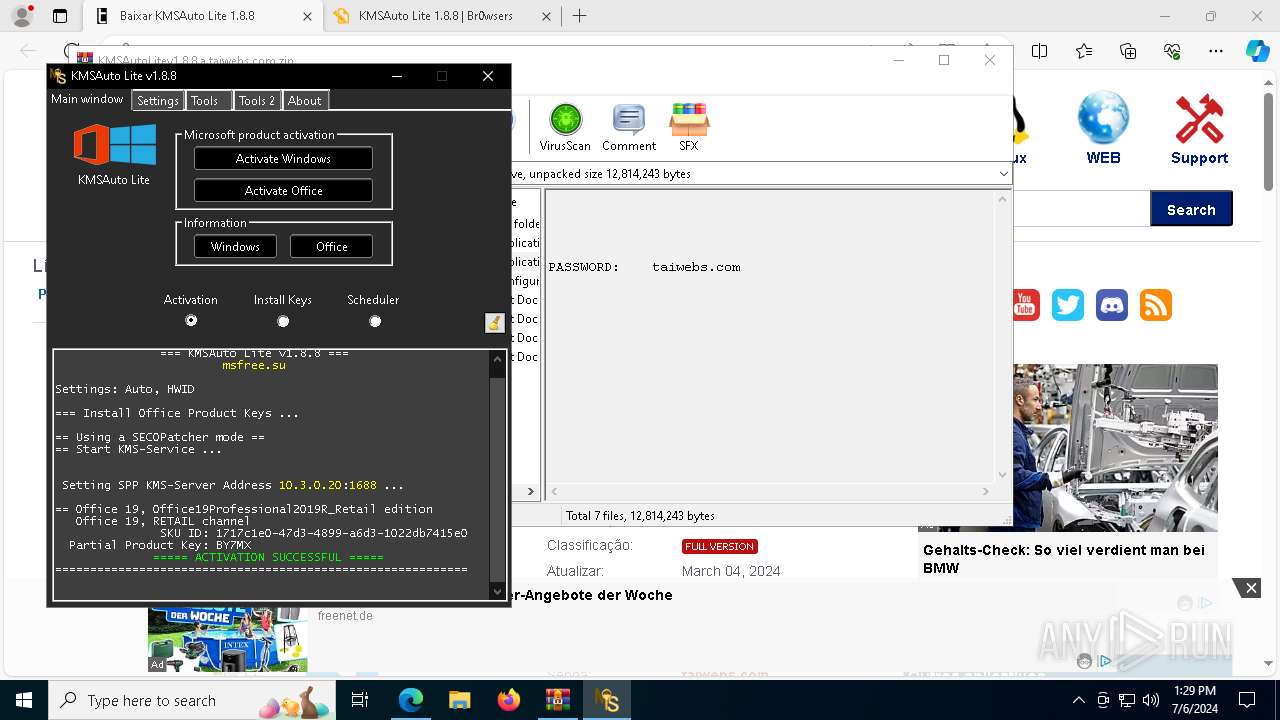
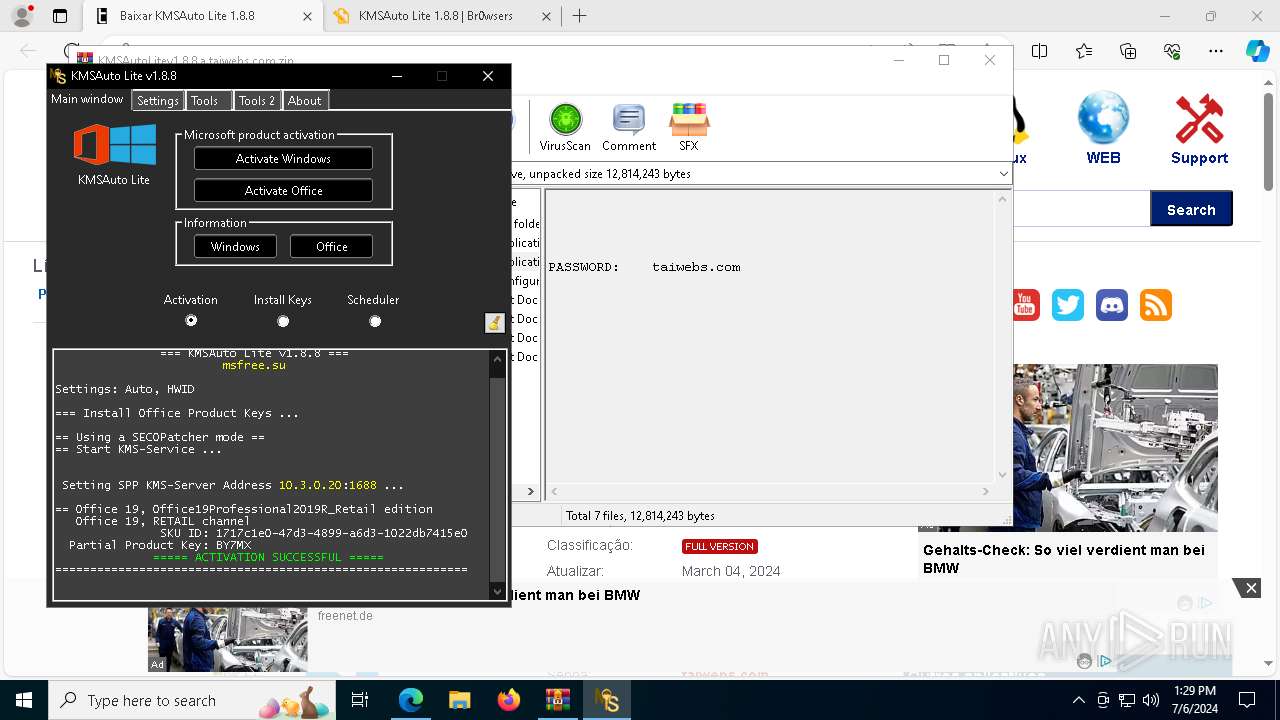
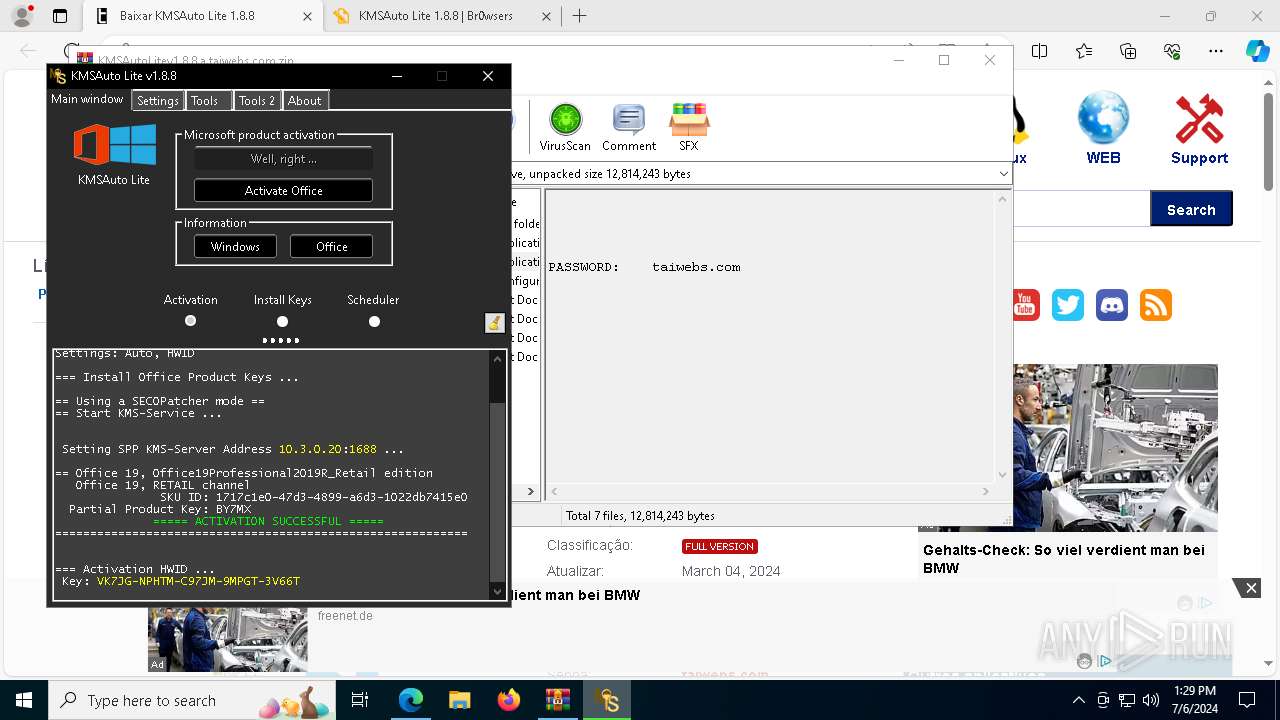
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2024, 13:26:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E24234DEB02B512BBCC78D41C84BA157 |
| SHA1: | D54979CCFB0D2AD6FB38A4FDDE61ECB289FCC2B9 |
| SHA256: | 051E65B8050EF8ECB0BCEAF98FDD756C4BDC1858FA8ACA4460D2D01AF62DD91D |
| SSDEEP: | 3:N8uGFMjKJOIDQRKbAO:2u0pAIDEKf |
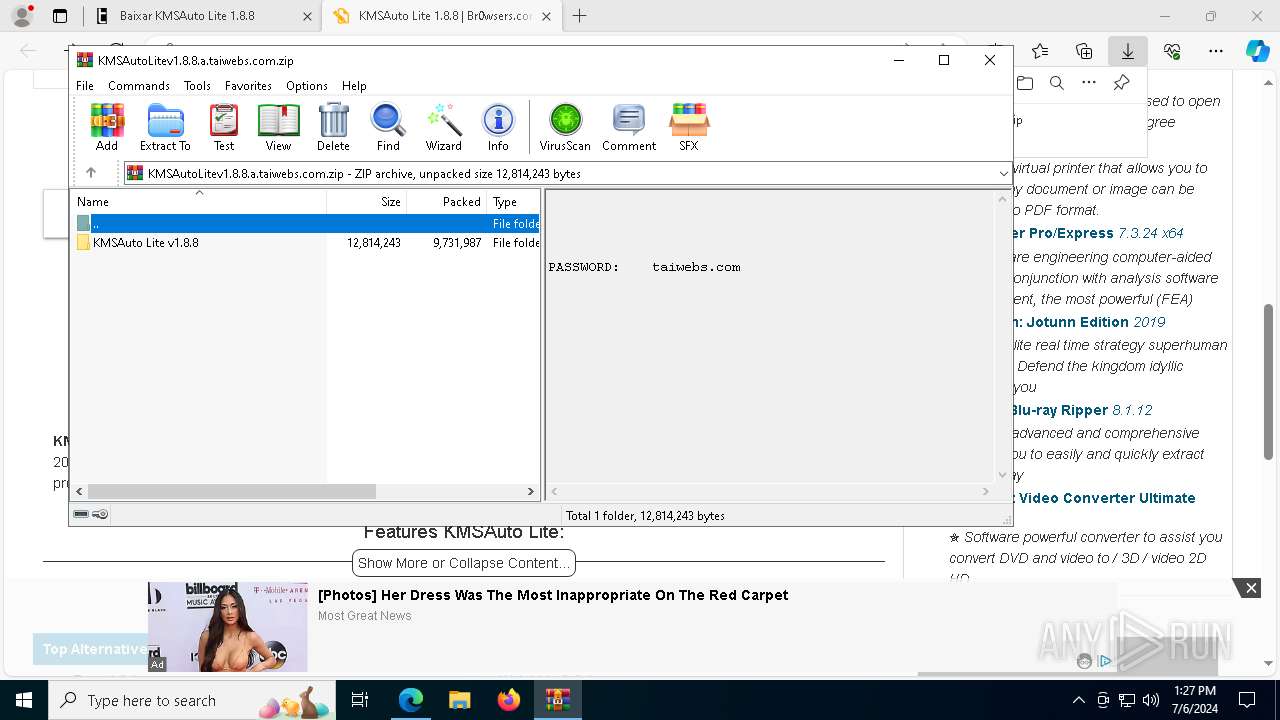
MALICIOUS
Drops the executable file immediately after the start
- KMSAuto.exe (PID: 8344)
Creates a writable file in the system directory
- cmd.exe (PID: 3580)
Changes image file execution options
- reg.exe (PID: 8296)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8928)
Starts SC.EXE for service management
- KMSAuto.exe (PID: 8344)
- cmd.exe (PID: 9020)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 8804)
- cmd.exe (PID: 8656)
- cmd.exe (PID: 3136)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 7552)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 7120)
- cmd.exe (PID: 8904)
Uses WMIC.EXE
- KMSAuto.exe (PID: 8344)
Starts CMD.EXE for commands execution
- KMSAuto.exe (PID: 8344)
- cmd.exe (PID: 8904)
Uses WMIC.EXE to obtain Windows Installer data
- KMSAuto.exe (PID: 8344)
- cmd.exe (PID: 8904)
- cmd.exe (PID: 2052)
Uses WMIC.EXE to obtain service application data
- KMSAuto.exe (PID: 8344)
- cmd.exe (PID: 8904)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6952)
- cmd.exe (PID: 6752)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2652)
- cmd.exe (PID: 9084)
- cmd.exe (PID: 5736)
- cmd.exe (PID: 5980)
- cmd.exe (PID: 7088)
- cmd.exe (PID: 6888)
- cmd.exe (PID: 4400)
- cmd.exe (PID: 6628)
- cmd.exe (PID: 2124)
- cmd.exe (PID: 8352)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 1220)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 8904)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2436)
- cmd.exe (PID: 8640)
- cmd.exe (PID: 8416)
Executable content was dropped or overwritten
- KMSAuto.exe (PID: 8344)
- Dism.exe (PID: 8136)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 6044)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 9140)
- cmd.exe (PID: 7056)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 8984)
- cmd.exe (PID: 8092)
Creates or modifies Windows services
- KMSAuto.exe (PID: 8344)
Executes as Windows Service
- KMSSS.exe (PID: 5904)
The process executes VB scripts
- cmd.exe (PID: 5736)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 8904)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 1544)
- cscript.exe (PID: 7108)
- cscript.exe (PID: 4208)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 7108)
- cscript.exe (PID: 1544)
- cscript.exe (PID: 4208)
Process drops legitimate windows executable
- KMSAuto.exe (PID: 8344)
- Dism.exe (PID: 8136)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8904)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 1856)
- cmd.exe (PID: 4780)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 4308)
Application launched itself
- cmd.exe (PID: 8904)
- ClipUp.exe (PID: 4256)
Executing commands from ".cmd" file
- KMSAuto.exe (PID: 8344)
- cmd.exe (PID: 8904)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8904)
Hides command output
- cmd.exe (PID: 2072)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 1856)
- cmd.exe (PID: 916)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 1784)
- cmd.exe (PID: 2072)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 2052)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8904)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 5736)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1856)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2072)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1856)
The process creates files with name similar to system file names
- Dism.exe (PID: 8136)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 3828)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 4208)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 8424)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8352)
INFO
Application launched itself
- msedge.exe (PID: 5652)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5652)
Checks supported languages
- identity_helper.exe (PID: 8640)
- KMSAuto.exe (PID: 8344)
- KMSSS.exe (PID: 5904)
- DismHost.exe (PID: 3828)
Reads the computer name
- identity_helper.exe (PID: 8640)
- KMSAuto.exe (PID: 8344)
- KMSSS.exe (PID: 5904)
- DismHost.exe (PID: 3828)
The process uses the downloaded file
- msedge.exe (PID: 8732)
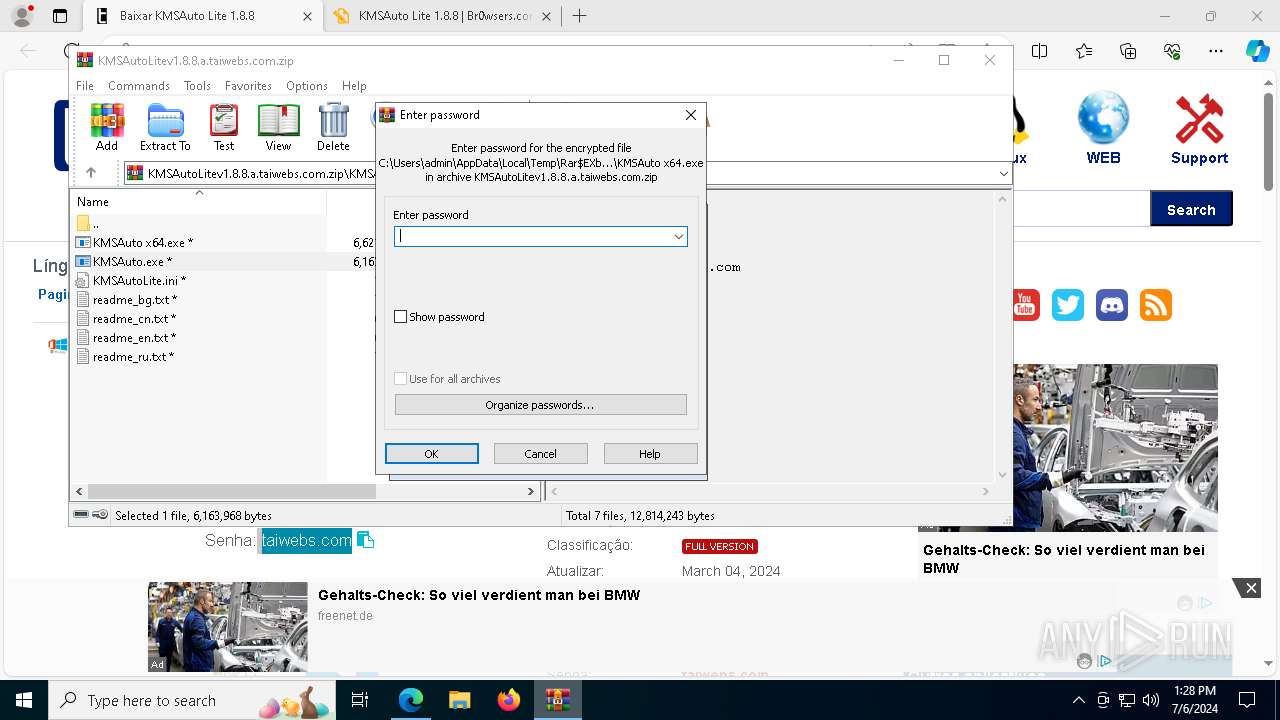
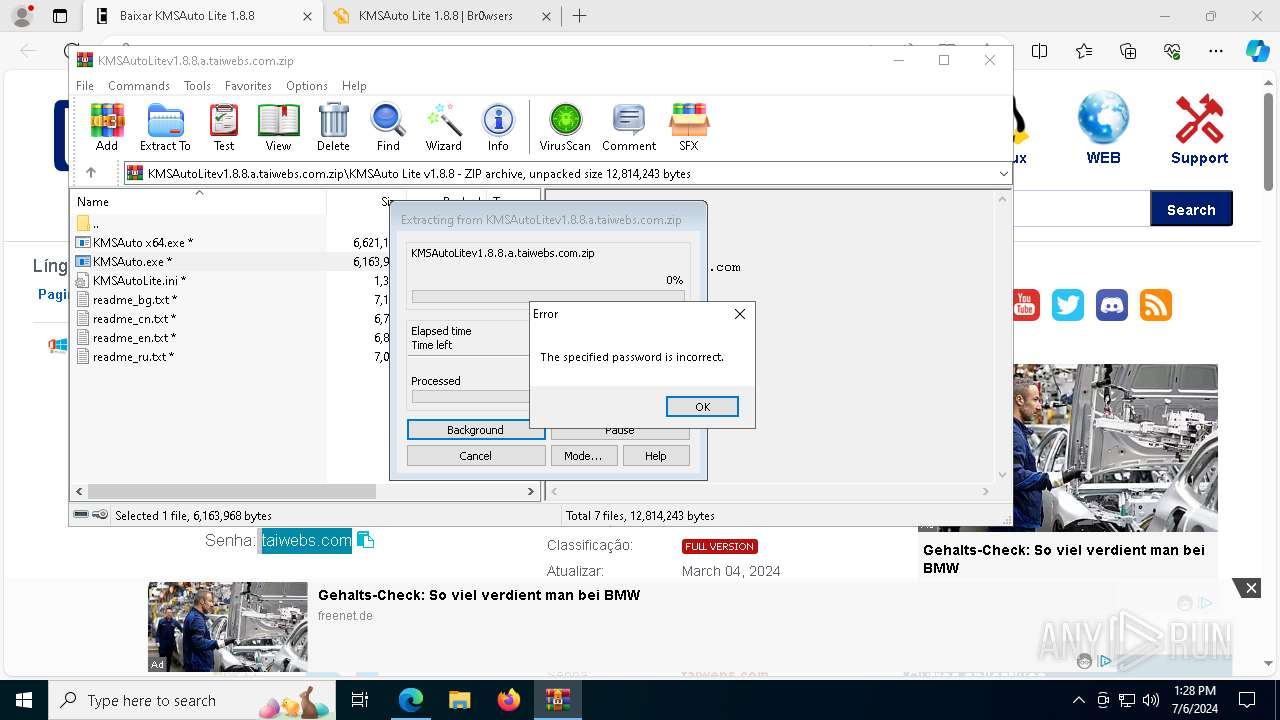
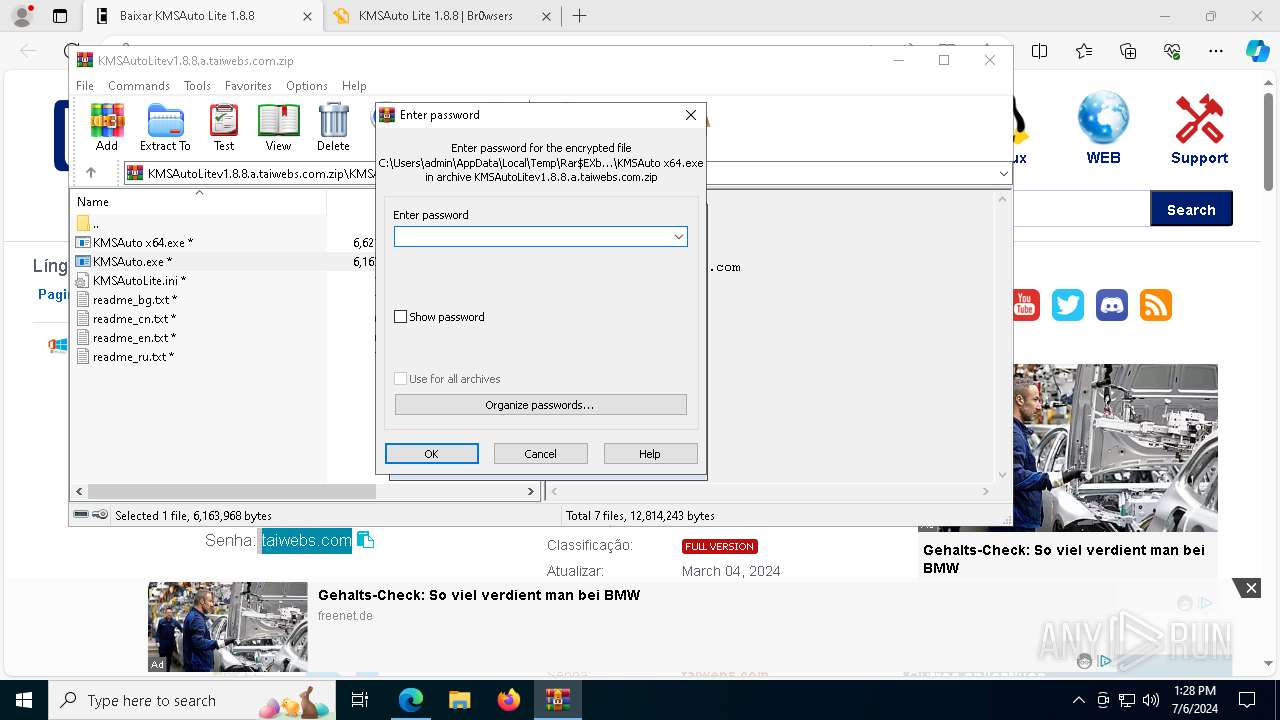
- WinRAR.exe (PID: 8928)
- msedge.exe (PID: 5652)
Reads the software policy settings
- slui.exe (PID: 9144)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 8928)
- msedge.exe (PID: 1452)
- Dism.exe (PID: 8136)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8928)
Reads product name
- KMSAuto.exe (PID: 8344)
Reads Environment values
- KMSAuto.exe (PID: 8344)
- DismHost.exe (PID: 3828)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7076)
- WMIC.exe (PID: 4448)
- WMIC.exe (PID: 7016)
- WMIC.exe (PID: 1204)
- WMIC.exe (PID: 1052)
- WMIC.exe (PID: 8564)
- WMIC.exe (PID: 8552)
- WMIC.exe (PID: 1700)
- WMIC.exe (PID: 3948)
- WMIC.exe (PID: 3580)
- WMIC.exe (PID: 6908)
- WMIC.exe (PID: 8752)
- WMIC.exe (PID: 6272)
- WMIC.exe (PID: 8924)
- WMIC.exe (PID: 6972)
- WMIC.exe (PID: 9136)
- WMIC.exe (PID: 608)
- WMIC.exe (PID: 8140)
- WMIC.exe (PID: 5896)
- WMIC.exe (PID: 3052)
- cscript.exe (PID: 7108)
- cscript.exe (PID: 1544)
- WMIC.exe (PID: 8140)
- WMIC.exe (PID: 7552)
- WMIC.exe (PID: 6876)
- cscript.exe (PID: 4208)
- WMIC.exe (PID: 3940)
- WMIC.exe (PID: 7156)
- WMIC.exe (PID: 1700)
- WMIC.exe (PID: 8828)
- WMIC.exe (PID: 1496)
Create files in a temporary directory
- KMSAuto.exe (PID: 8344)
- KMSSS.exe (PID: 5904)
- Dism.exe (PID: 8136)
- ClipUp.exe (PID: 8092)
Reads the machine GUID from the registry
- KMSSS.exe (PID: 5904)
UPX packer has been detected
- KMSAuto.exe (PID: 8344)
Checks operating system version
- cmd.exe (PID: 8904)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4852)
Creates files in the program directory
- cmd.exe (PID: 8904)
- ClipUp.exe (PID: 8092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
688
Monitored processes
529
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=10000 --field-trial-handle=2340,i,16119920174001717197,14129167660494001518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 368 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | "wmic.exe" path SoftwareLicensingProduct where ID='1717c1e0-47d3-4899-a6d3-1022db7415e0' call SetKeyManagementServiceMachine MachineName="10.3.0.20" | C:\Windows\SysWOW64\wbem\WMIC.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | reg query HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowsUpdateSysprepInProgress | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 652 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=5952 --field-trial-handle=2340,i,16119920174001717197,14129167660494001518,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 696 | powershell.exe "Set-WinHomeLocation -GeoId 244" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=9192 --field-trial-handle=2340,i,16119920174001717197,14129167660494001518,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 836 | reg.exe delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.Exe" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | reg.exe delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.Exe" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
97 781
Read events
97 520
Write events
254
Delete events
7
Modification events
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5652) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
62
Suspicious files
517
Text files
210
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1cec3c.TMP | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1cec3c.TMP | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1cec3c.TMP | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1cec5b.TMP | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1cec6b.TMP | — | |
MD5:— | SHA256:— | |||
| 5652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
660
DNS requests
576
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3748 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
2220 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2220 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
6916 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
7008 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6148 | svchost.exe | HEAD | 200 | 23.48.23.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2160a134-ce8c-414e-9f8c-def62796bce9?P1=1720571068&P2=404&P3=2&P4=GWEtjjK4MLDPrDzb5qQFHOzFl0PzCbaR4ADb3%2f%2f8vatIPkUpsFYht0Vidc04dTLHGWY%2bChel%2boyoKkByvgHtmQ%3d%3d | unknown | — | — | unknown |
8884 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
8884 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
6148 | svchost.exe | GET | 206 | 23.48.23.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2160a134-ce8c-414e-9f8c-def62796bce9?P1=1720571068&P2=404&P3=2&P4=GWEtjjK4MLDPrDzb5qQFHOzFl0PzCbaR4ADb3%2f%2f8vatIPkUpsFYht0Vidc04dTLHGWY%2bChel%2boyoKkByvgHtmQ%3d%3d | unknown | — | — | unknown |
6148 | svchost.exe | GET | 206 | 23.48.23.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2160a134-ce8c-414e-9f8c-def62796bce9?P1=1720571068&P2=404&P3=2&P4=GWEtjjK4MLDPrDzb5qQFHOzFl0PzCbaR4ADb3%2f%2f8vatIPkUpsFYht0Vidc04dTLHGWY%2bChel%2boyoKkByvgHtmQ%3d%3d | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1856 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3164 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 188.114.96.3:443 | br.taiwebs.com | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5652 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
br.taiwebs.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
taiwebs.com |
| unknown |
maxcdn.bootstrapcdn.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6232 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
Dism.exe | PID=8136 TID=8308 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=8136 TID=8308 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=8136 TID=8308 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=8136 TID=8308 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=8136 TID=8308 Loading Provider from location C:\WINDOWS\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=8136 TID=8308 Connecting to the provider located at C:\WINDOWS\System32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |
DismHost.exe | PID=3828 TID=3020 Disconnecting the provider store - CDISMImageSession::Final_OnDisconnect |
DismHost.exe | PID=3828 TID=3020 Encountered a loaded provider DISMLogger. - CDISMProviderStore::Internal_DisconnectProvider |
DismHost.exe | PID=3828 TID=3020 Disconnecting Provider: DISMLogger - CDISMProviderStore::Internal_DisconnectProvider |
Dism.exe | PID=8136 TID=8308 Disconnecting the provider store - CDISMImageSession::Final_OnDisconnect |