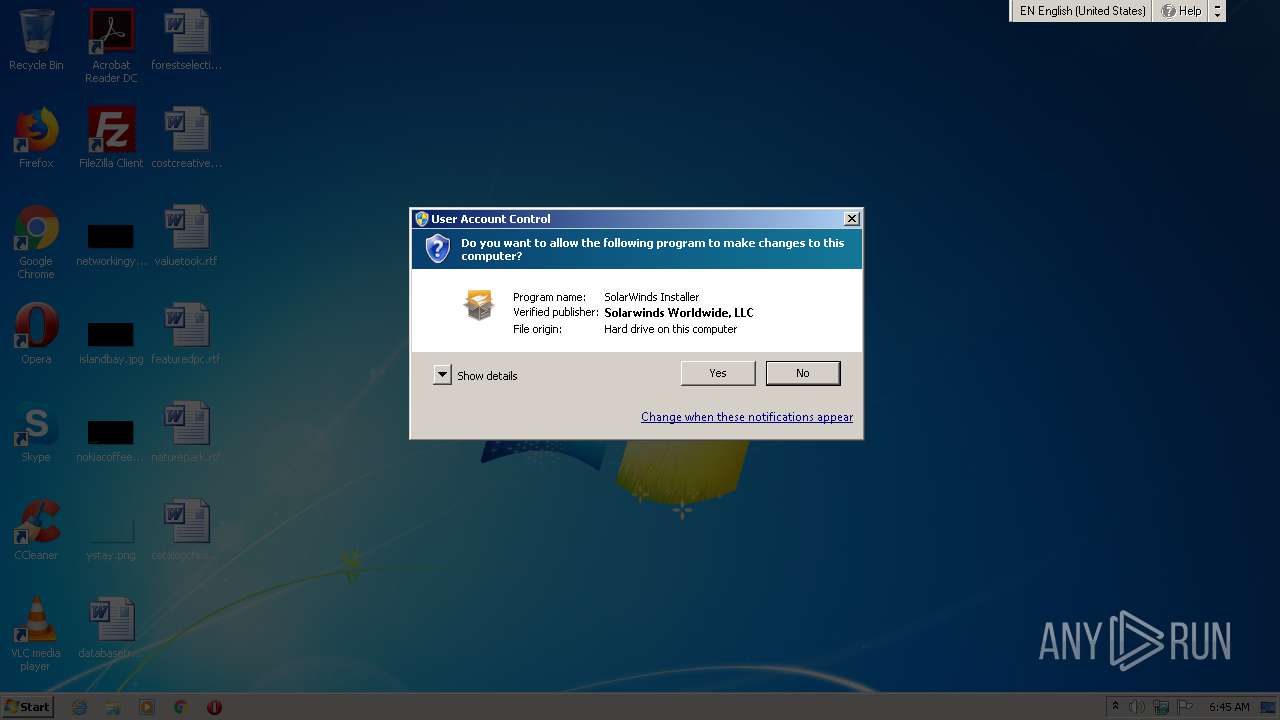
| File name: | SFTP-Server-Installer.exe |
| Full analysis: | https://app.any.run/tasks/264e8675-69a3-4e5d-ba8c-430253ec4c35 |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2021, 05:45:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 09FBFB5A8EBD816EA5F02811793FB06F |
| SHA1: | 701A9BDF4DF586FE239CEE0AEA0A70DA1DD75870 |
| SHA256: | 0517A512B65A672354F241707F74D8495EBC0196CFE7EEE605BE855C6D641BC1 |
| SSDEEP: | 98304:OoOcjLUjMtZlSSfjkAsOx8WEgtWyMaS0GGcio9lkV1oKdQZZNlKTPlHYud3Aq:Oo1jLPtZTfjkAsOggtXMPzGcrmFa3/KH |
MALICIOUS
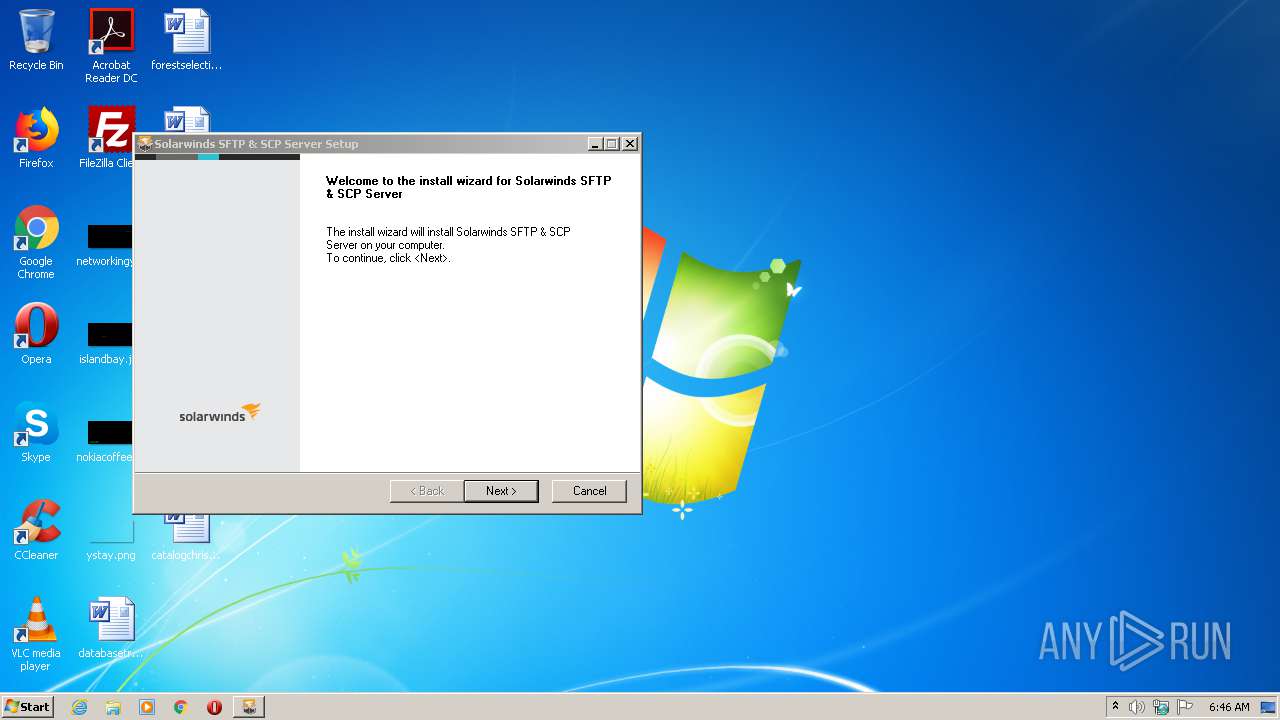
Application was dropped or rewritten from another process
- FT.Installer.exe (PID: 3020)
- FT.Installer.Bootstrapper.exe (PID: 4036)
- FT.Installer.Bootstrapper.exe (PID: 3028)
- SolarWindsSftpServer.exe (PID: 2904)
- ScpServerTray.exe (PID: 1972)
Changes settings of System certificates
- FT.Installer.Bootstrapper.exe (PID: 3028)
- FT.Installer.exe (PID: 3020)
- msiexec.exe (PID: 3372)
Loads dropped or rewritten executable
- FT.Installer.exe (PID: 3020)
- SFTP-Server-Installer.exe (PID: 3336)
- SolarWindsSftpServer.exe (PID: 2904)
Drops executable file immediately after starts
- msiexec.exe (PID: 3372)
Loads the Task Scheduler COM API
- ScpServerTray.exe (PID: 1972)
SUSPICIOUS
Drops a file that was compiled in debug mode
- SFTP-Server-Installer.exe (PID: 3336)
- msiexec.exe (PID: 3372)
Executable content was dropped or overwritten
- SFTP-Server-Installer.exe (PID: 3336)
- FT.Installer.exe (PID: 3020)
- msiexec.exe (PID: 3372)
- SolarWindsSftpServer.exe (PID: 2904)
Creates files in the program directory
- FT.Installer.exe (PID: 3020)
- SolarWindsSftpServer.exe (PID: 2904)
Adds / modifies Windows certificates
- FT.Installer.exe (PID: 3020)
- FT.Installer.Bootstrapper.exe (PID: 3028)
- msiexec.exe (PID: 3372)
Reads Environment values
- FT.Installer.exe (PID: 3020)
Reads internet explorer settings
- FT.Installer.exe (PID: 3020)
Creates a directory in Program Files
- msiexec.exe (PID: 3372)
Uses TASKKILL.EXE to kill process
- MsiExec.exe (PID: 2140)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 3372)
Drops a file with too old compile date
- msiexec.exe (PID: 3372)
Creates files in the Windows directory
- msiexec.exe (PID: 3372)
- SolarWindsSftpServer.exe (PID: 2904)
Executed as Windows Service
- SolarWindsSftpServer.exe (PID: 2904)
Removes files from Windows directory
- SolarWindsSftpServer.exe (PID: 2904)
INFO
Reads settings of System Certificates
- msiexec.exe (PID: 3372)
- FT.Installer.exe (PID: 3020)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2140)
- msiexec.exe (PID: 3372)
- MsiExec.exe (PID: 792)
Creates files in the program directory
- msiexec.exe (PID: 3372)
Creates a software uninstall entry
- msiexec.exe (PID: 3372)
Application launched itself
- msiexec.exe (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x320c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 20.4.1.0 |
| ProductVersionNumber: | 20.4.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
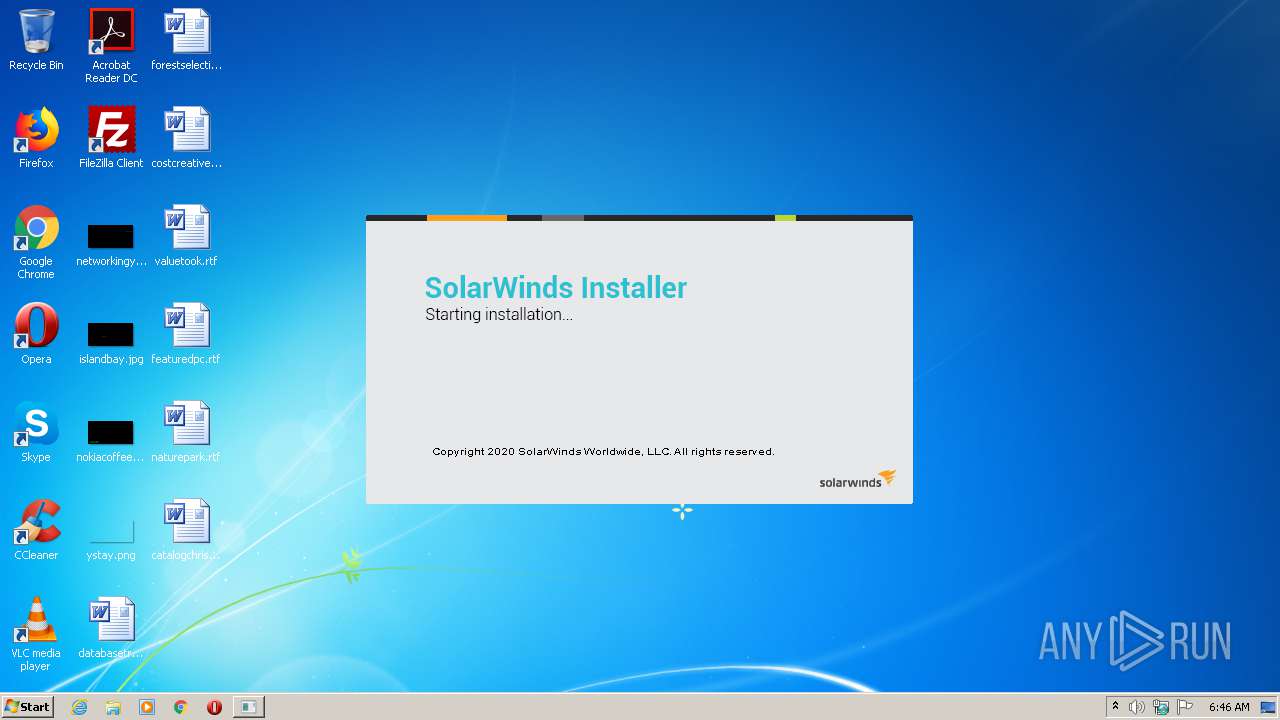
| FileDescription: | Installs SolarWinds Installer |
| FileVersion: | 20.4.1.0 |
| LegalCopyright: | Copyright SolarWinds Worldwide, LLC. All rights reserved. |
| ProductName: | SolarWinds Installer |
| ProductVersion: | 20.4.1.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:45 |
| Detected languages: |
|
| FileDescription: | Installs SolarWinds Installer |
| FileVersion: | 20.4.1.0 |
| LegalCopyright: | Copyright SolarWinds Worldwide, LLC. All rights reserved. |
| ProductName: | SolarWinds Installer |
| ProductVersion: | 20.4.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000628F | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4422 |
.rdata | 0x00008000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23627 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04938 |
.ndata | 0x00030000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x000063D8 | 0x00006400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.96032 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2963 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.59759 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.58635 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.01128 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.41233 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 5.78619 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.69913 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
51
Monitored processes
9
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 792 | C:\Windows\system32\MsiExec.exe -Embedding A439245E6A2732D005BDC403F48C9A5C M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1972 | "C:\Program Files\SolarWinds\SFTP & SCP Server\ScpServerTray.exe" | C:\Program Files\SolarWinds\SFTP & SCP Server\ScpServerTray.exe | FT.Installer.exe | ||||||||||||
User: admin Company: SolarWinds Worldwide, LLC. Integrity Level: HIGH Description: ScpServerTray Exit code: 0 Version: 20.4.1.99 Modules
| |||||||||||||||
| 2140 | C:\Windows\system32\MsiExec.exe -Embedding A18124D90033D0A757CFDE744D0EF5C0 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | "C:\Program Files\SolarWinds\SFTP & SCP Server\SolarWindsSftpServer.exe" | C:\Program Files\SolarWinds\SFTP & SCP Server\SolarWindsSftpServer.exe | services.exe | ||||||||||||
User: SYSTEM Company: SolarWinds Worldwide, LLC. Integrity Level: SYSTEM Description: SolarWindsSftpServer Exit code: 0 Version: 20.4.1.99 Modules
| |||||||||||||||
| 3020 | FT.Installer.exe -SESSIONID=480EFD0B-E537-45B7-82CA-061F3C537942 | C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\FT.Installer.exe | FT.Installer.Bootstrapper.exe | ||||||||||||
User: admin Company: SolarWinds Worldwide, LLC. Integrity Level: HIGH Description: FTInstaller Exit code: 0 Version: 2020.4.0.83 Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\FT.Installer.Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\FT.Installer.Bootstrapper.exe | SFTP-Server-Installer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SolarWinds Installer Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3336 | "C:\Users\admin\AppData\Local\Temp\SFTP-Server-Installer.exe" | C:\Users\admin\AppData\Local\Temp\SFTP-Server-Installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Installs SolarWinds Installer Exit code: 0 Version: 20.4.1.0 Modules
| |||||||||||||||
| 3372 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4036 | "C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\FT.Installer.Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\FT.Installer.Bootstrapper.exe | — | SFTP-Server-Installer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SolarWinds Installer Exit code: 3221226540 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 380
Read events
1 000
Write events
368
Delete events
12
Modification events
| (PID) Process: | (3336) SFTP-Server-Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3336) SFTP-Server-Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3028) FT.Installer.Bootstrapper.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\SolarWinds\FreeTools\Improvement |
| Operation: | write | Name: | UserID |
Value: 479FE7F5-CBB5-46E1-89E7-C134C5BDE4E0 | |||
| (PID) Process: | (3028) FT.Installer.Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3028) FT.Installer.Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A6000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3028) FT.Installer.Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3028) FT.Installer.Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3028) FT.Installer.Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3028) FT.Installer.Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3028) FT.Installer.Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
32
Suspicious files
9
Text files
38
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | FT.Installer.Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Cab30AE.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | FT.Installer.Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\Tar30AF.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF3369C514775E31F0.TMP | — | |
MD5:— | SHA256:— | |||
| 3336 | SFTP-Server-Installer.exe | C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\FT.Installer.Bootstrapper.exe | executable | |
MD5:— | SHA256:— | |||
| 3372 | msiexec.exe | C:\Windows\Installer\MSI72C1.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | SFTP-Server-Installer.exe | C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:— | SHA256:— | |||
| 3372 | msiexec.exe | C:\Windows\Installer\MSI737E.tmp | — | |
MD5:— | SHA256:— | |||
| 3336 | SFTP-Server-Installer.exe | C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\OrionInstallerLib.dll | executable | |
MD5:— | SHA256:— | |||
| 3336 | SFTP-Server-Installer.exe | C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\SubInstallers\SftpServerInstaller.msi | executable | |
MD5:— | SHA256:— | |||
| 3336 | SFTP-Server-Installer.exe | C:\Users\admin\AppData\Local\Temp\SolarWinds\FreeTools\SFTP-Server\Newtonsoft.Json.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2904 | SolarWindsSftpServer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | US | der | 471 b | whitelisted |
2904 | SolarWindsSftpServer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEALTGDK5W7JawKuZU18w7mU%3D | US | der | 471 b | whitelisted |
3028 | FT.Installer.Bootstrapper.exe | GET | 302 | 104.111.229.105:80 | http://downloads.solarwinds.com/solarwinds/OrionInstaller/SolarWinds/bootstrapper.xml | NL | — | — | suspicious |
1972 | ScpServerTray.exe | GET | 200 | 78.159.97.6:80 | http://servedbyadbutler.com/adserve/;ID=175238;size=728x90;setID=389470;type=json;click=CLICK_MACRO_PLACEHOLDER | DE | text | 1.10 Kb | whitelisted |
3028 | FT.Installer.Bootstrapper.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
1972 | ScpServerTray.exe | GET | 200 | 78.159.97.6:80 | http://servedbyadbutler.com/getad.img/;libID=642435 | DE | image | 13.8 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.111.229.105:80 | downloads.solarwinds.com | Akamai International B.V. | NL | unknown |
3020 | FT.Installer.exe | 74.115.13.127:443 | api.solarwinds.com | SolarWinds, Inc. | US | unknown |
3028 | FT.Installer.Bootstrapper.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1972 | ScpServerTray.exe | 78.159.97.6:80 | servedbyadbutler.com | Leaseweb Deutschland GmbH | DE | suspicious |
2904 | SolarWindsSftpServer.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3028 | FT.Installer.Bootstrapper.exe | 104.111.229.105:443 | downloads.solarwinds.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloads.solarwinds.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
www.solarwinds.com |
| suspicious |
api.solarwinds.com |
| unknown |
servedbyadbutler.com |
| whitelisted |
Threats
Process | Message |
|---|---|
FT.Installer.Bootstrapper.exe | OrionImprovementClient::TrackEvent('FT.Installer.BootStrapper', 'Started', '', 1, 0)
|
FT.Installer.Bootstrapper.exe | OrionImprovementClient::TrackEvent('FT.Installer.BootStrapper', 'Version', '2020.4.0.83', 1, 0)
|
FT.Installer.Bootstrapper.exe | OrionImprovementClient::TrackEvent('FT.Installer.BootStrapper', 'Detected OS', 'Running on Ver 6.1.1.0 type=48', 1, 0)
|
FT.Installer.Bootstrapper.exe | OrionImprovementClient::TrackEvent('FT.Installer.BootStrapper', 'Start', 'Launching main installer, command line: FT.Installer.exe -SESSIONID=480EFD0B-E537-45B7-82CA-061F3C537942', 1, 0)
|
FT.Installer.Bootstrapper.exe | OrionImprovementClient::TrackEvent('FT.Installer.BootStrapper', 'Started', 'Launched main installer', 1, 0)
|