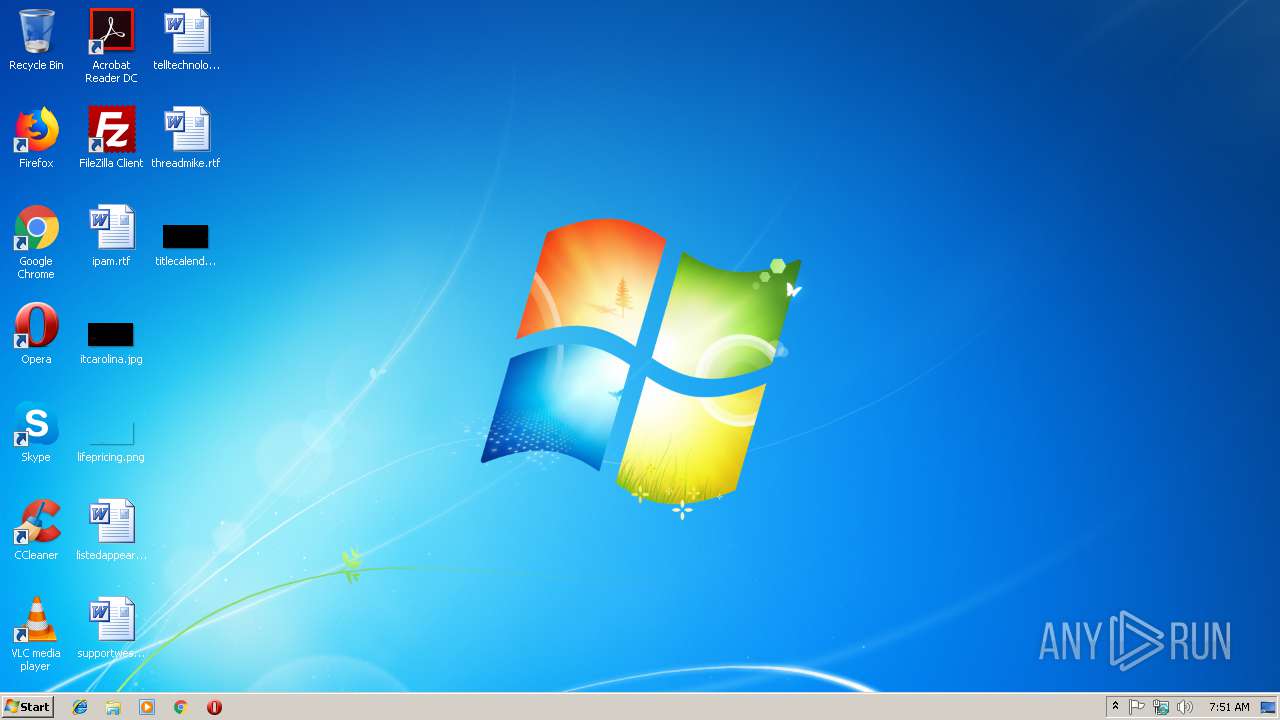
| File name: | yacspeel.exe |
| Full analysis: | https://app.any.run/tasks/85a1ac7f-a228-4298-9f7c-47aa73ed2da7 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 07:51:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | E5C06BD78DF948D15268F41A11499667 |
| SHA1: | 0954620BA64081F1800B3713B3690FFFC66BECAD |
| SHA256: | 050EE6C08F2498EDC7CC46B23217D0CD5D054066F58DEA1F07DF43CB4F330A38 |
| SSDEEP: | 1536:9qSoyYo5o2NQV9TcmviTvLKUZRm5VVY87uoXO3p:GE2JGLN34jb7uoXOZ |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 2028)
- svchost.exe (PID: 844)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 2028)
INFO
Loads main object executable
- rundll32.exe (PID: 2924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:06:26 10:46:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 61440 |
| InitializedDataSize: | 40960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8539 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jun-2007 08:46:11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 26-Jun-2007 08:46:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000E57A | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.38469 |
.rdata | 0x00010000 | 0x00001896 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43998 |
.data | 0x00012000 | 0x00005B04 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.43548 |
.reloc | 0x00018000 | 0x00001A9E | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.48776 |
Imports
ADVAPI32.dll |
KERNEL32.dll |
RPCRT4.dll |
USER32.dll |
WS2_32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
Entry | 1 | 0x00003550 |
InstallM | 2 | 0x000035B0 |
Total processes
32
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2028 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2924 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\Downloads\yacspeel.exe", Entry | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3720 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
424
Read events
322
Write events
102
Delete events
0
Modification events
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 000000000700000009000000A8D90300000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFC0AEBE0B28C8D40100000000 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002E0000003D000000B34B1500090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000F000000E21705007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E006500780065000000D201B0E536027CE43602A532DC75BCE4360294E5360200000000B432DC75F4E536020145DC756A00CA028C00CA02B8ACCA0278E336020001000101000000000100000000000028FCA802C8E53602E0E2BF02A4E53602CAFEBF02A0E33602D4E536026000CA022B0000006A00CA0228FCA802000000008C00CA025CE536020A00CA020000000005000500A823D3016601CA022B0000000F000000F4E53602BCE5360228FCA8021000000074FFA802050017004E1ED301BCE436021600000002000000B8ACCA020400360228FCA80203000000000000000909090009090909000911110000000011000000B8452700B04527000000000000000000000000000000000000000000000000001CE400005A743083D0E336028291F5751CE43602CCB700002E743083E4E33602B69CF575D0B7DD024C060000FCE3360240B3DD0208E43602789CF57511000000B8452700B045270060B3DD026CE40000E67330831CE436028291F5756CE4360220E436022795F57500000000CCB7DD0248E43602CD94F575CCB7DD02F4E4360240B3DD02E194F5750000000040B3DD02F4E4360250E43602090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000070000000000000006000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFC0AEBE0B28C8D40100000000 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000025000000000000002400000009000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D02 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000070000000000000007000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFC0AEBE0B28C8D40100000000 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000025000000000000002500000009000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D02 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000000000000010000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (2028) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
1
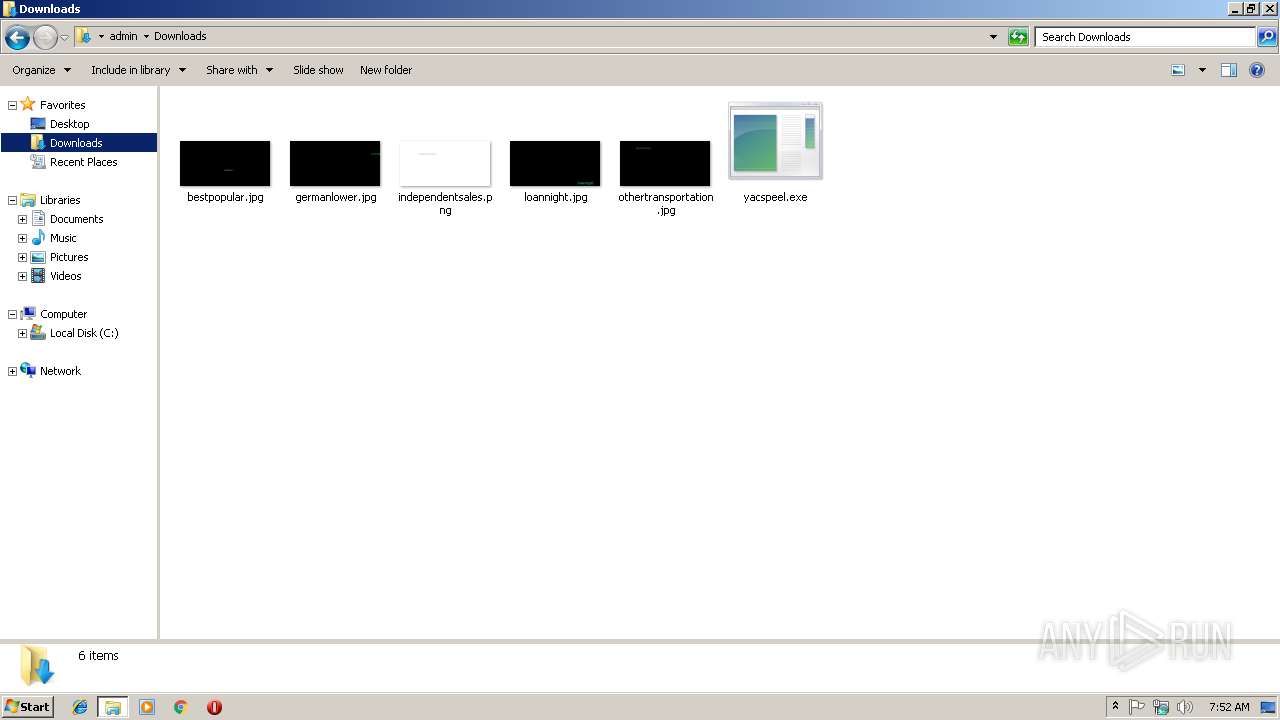
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2924 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\6D73776D706461742E746C62FA.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report