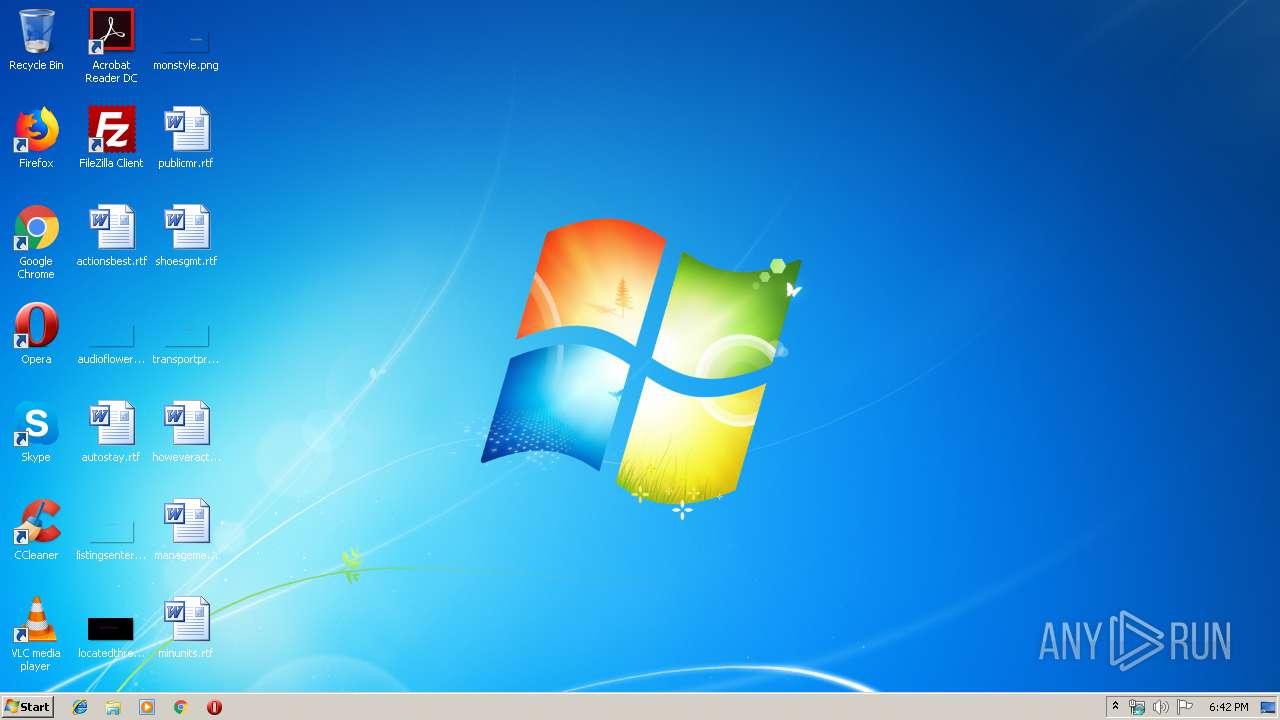
| File name: | growtopia spam bot(fixed).rar |
| Full analysis: | https://app.any.run/tasks/70cfd458-925c-4d85-9309-f9ca64f64659 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 18:42:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/jpeg |
| File info: | JPEG image data, Exif standard: [TIFF image data, little-endian, direntries=0], progressive, precision 8, 520x340, frames 3 |
| MD5: | 951C6DA05D75F53D81854F71C2164AA5 |
| SHA1: | 31332A3268F179802FA43DEFE06F4291537C0525 |
| SHA256: | 04FB0B0C1AB59A4B9C4C6163E74D1BB05082806AC20E07D45E89E4F8B0BC92D4 |
| SSDEEP: | 384:bbhVi+bNSNXMlZ/lKB1sk/F967ZRpCetibJDhskDJ9TDtp50oFmVVvNA:bbrns87/lIyeF87Hp/cHLl0qQA |
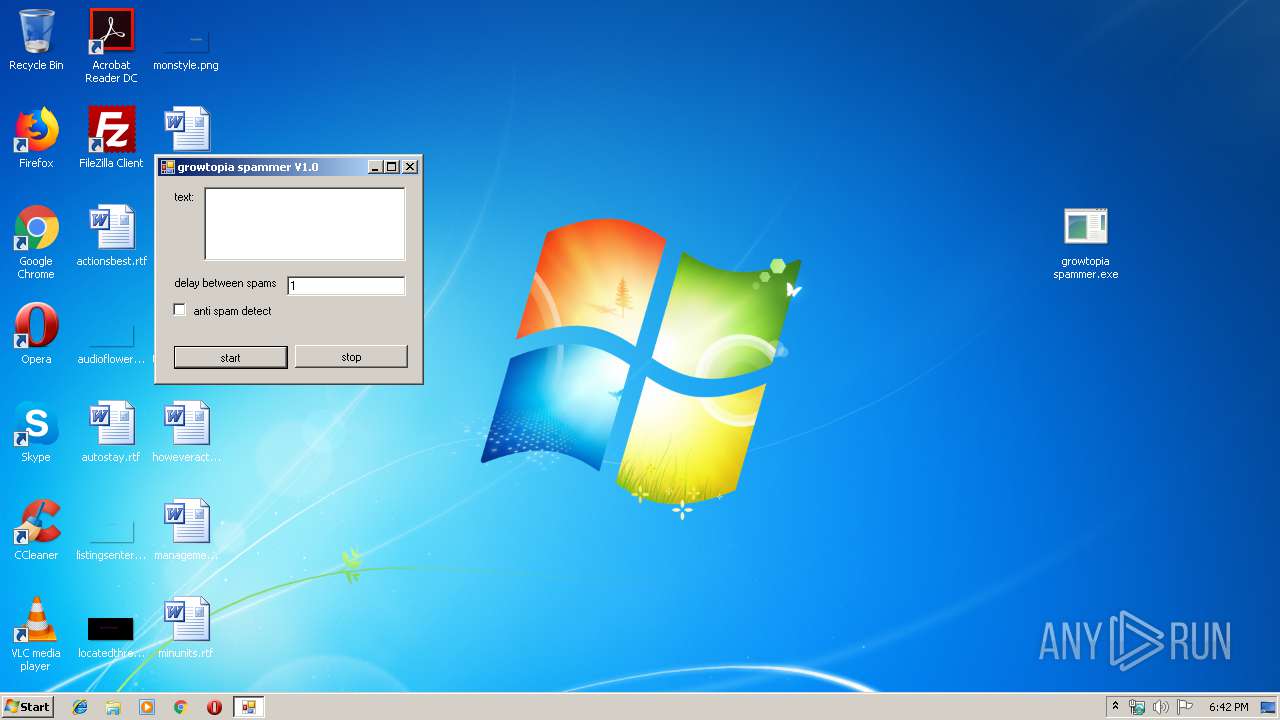
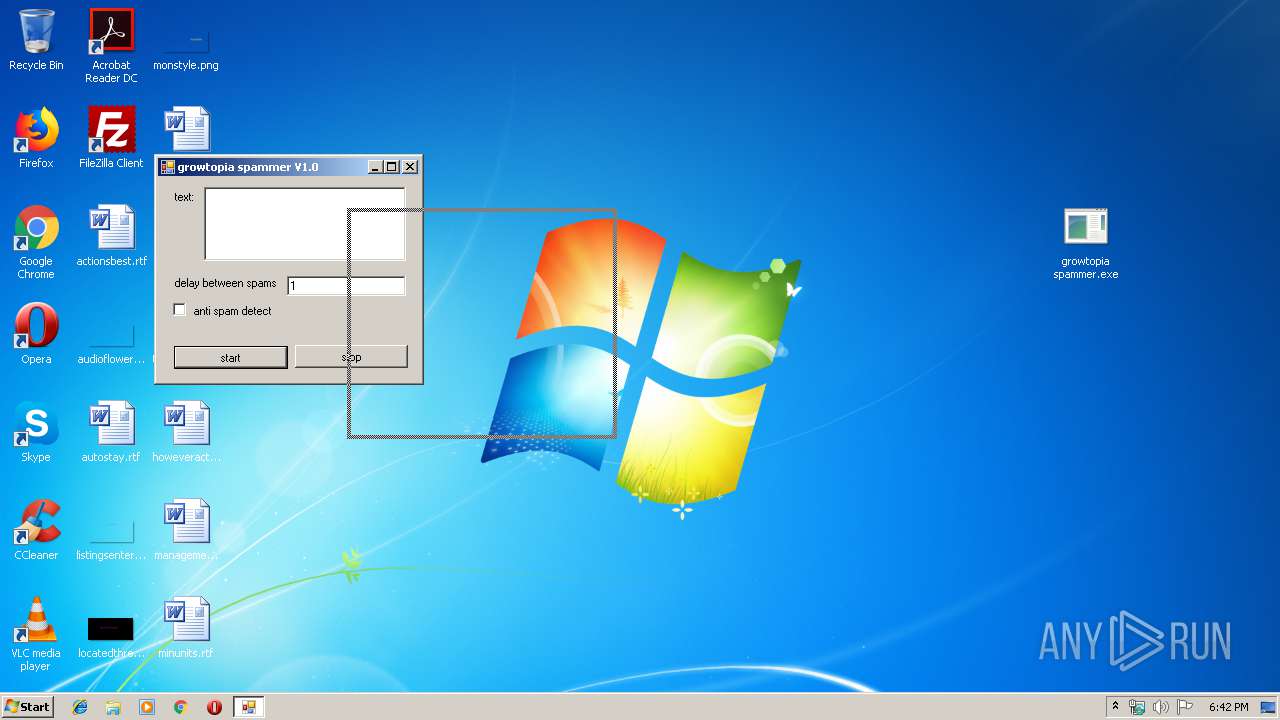
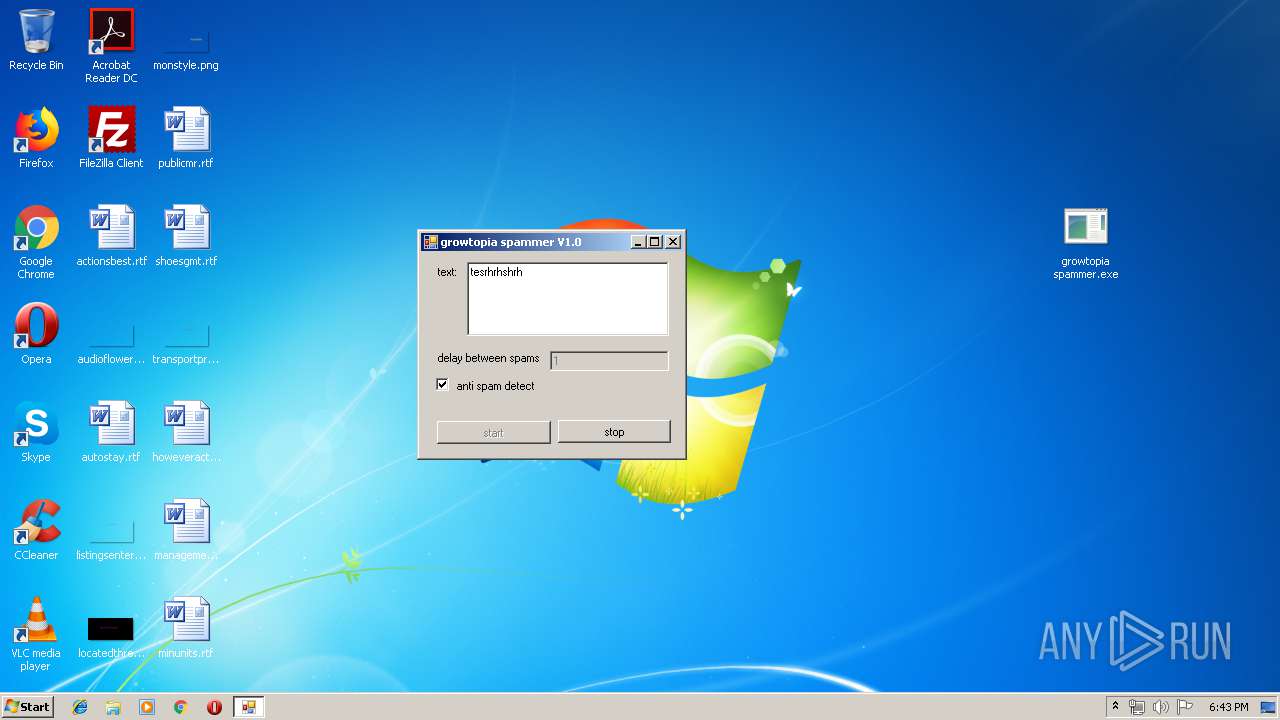
MALICIOUS
Application was dropped or rewritten from another process
- growtopia spammer.exe (PID: 2852)
SUSPICIOUS
No suspicious indicators.INFO
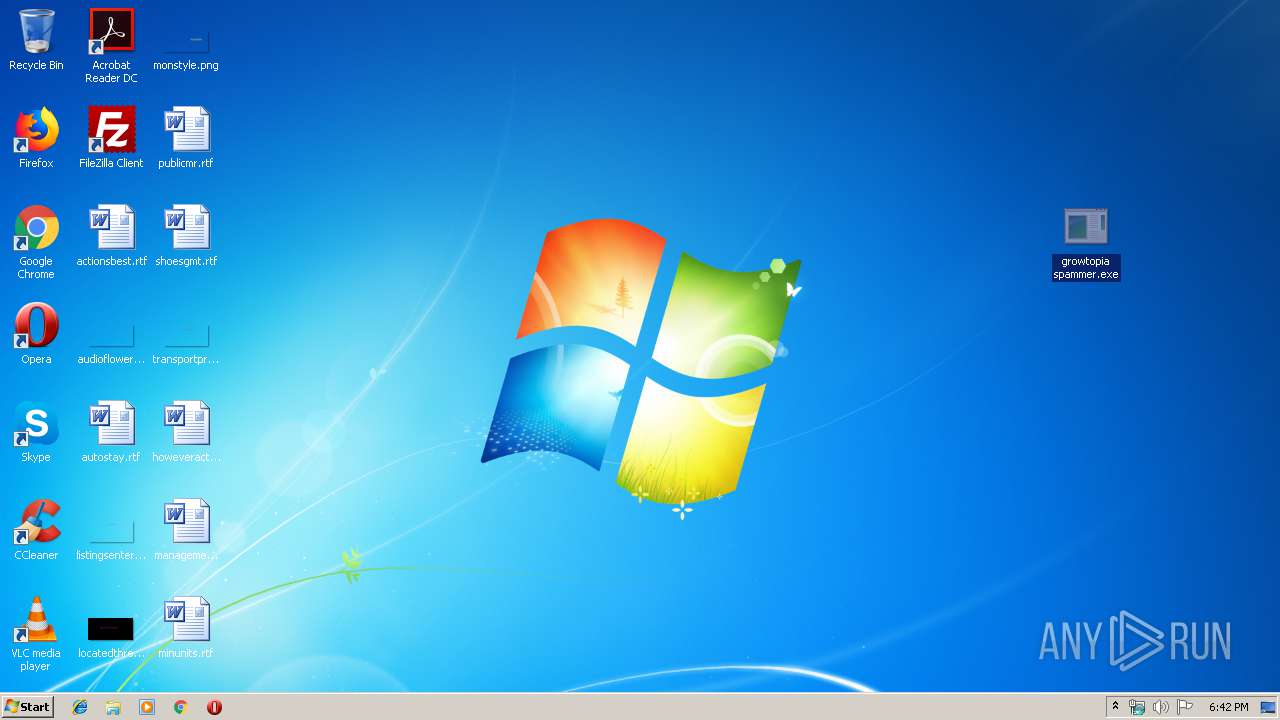
Manual execution by user
- growtopia spammer.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jpg | | | JFIF-EXIF JPEG Bitmap (55.5) |
|---|---|---|
| .jpg | | | JPEG bitmap (33.3) |
| .mp3 | | | MP3 audio (11.1) |
EXIF
Ducky
| Quality: | 60% |
|---|
APP14
| DCTEncodeVersion: | 100 |
|---|---|
| APP14Flags0: | [14], Encoded with Blend=1 downsampling |
| APP14Flags1: | (none) |
| ColorTransform: | YCbCr |
Composite
| ImageSize: | 520x340 |
|---|---|
| Megapixels: | 0.177 |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
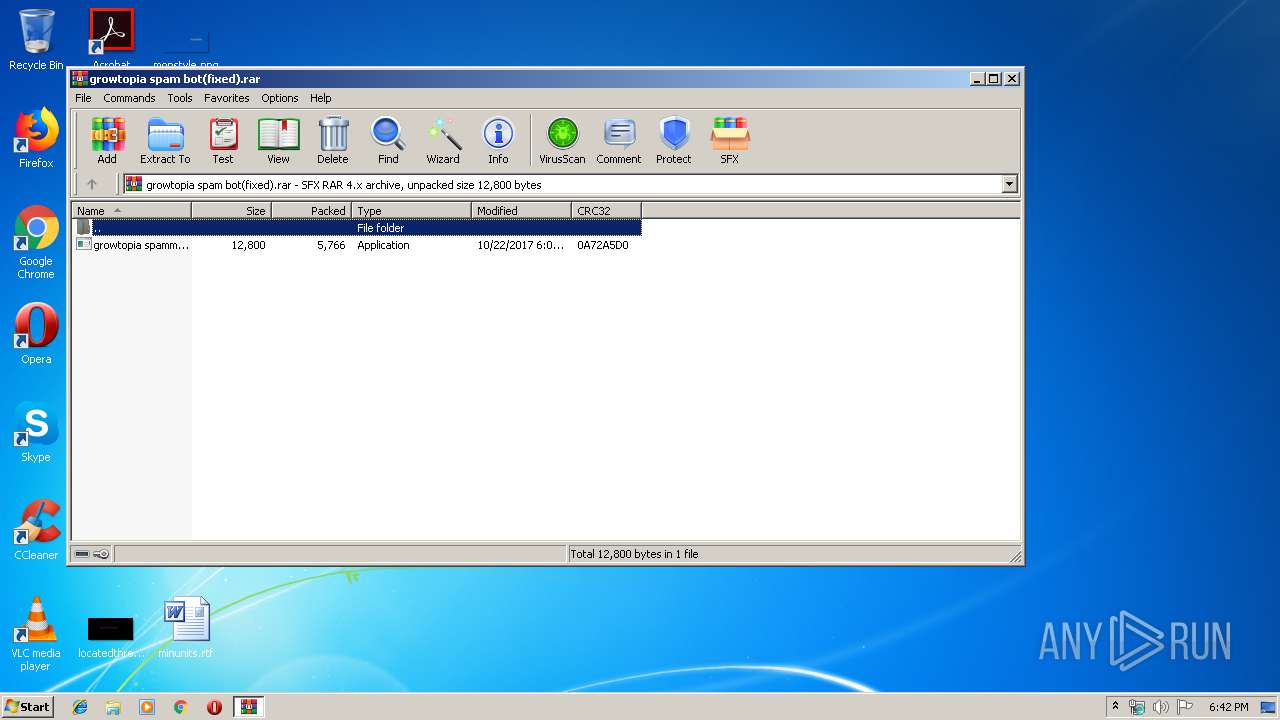
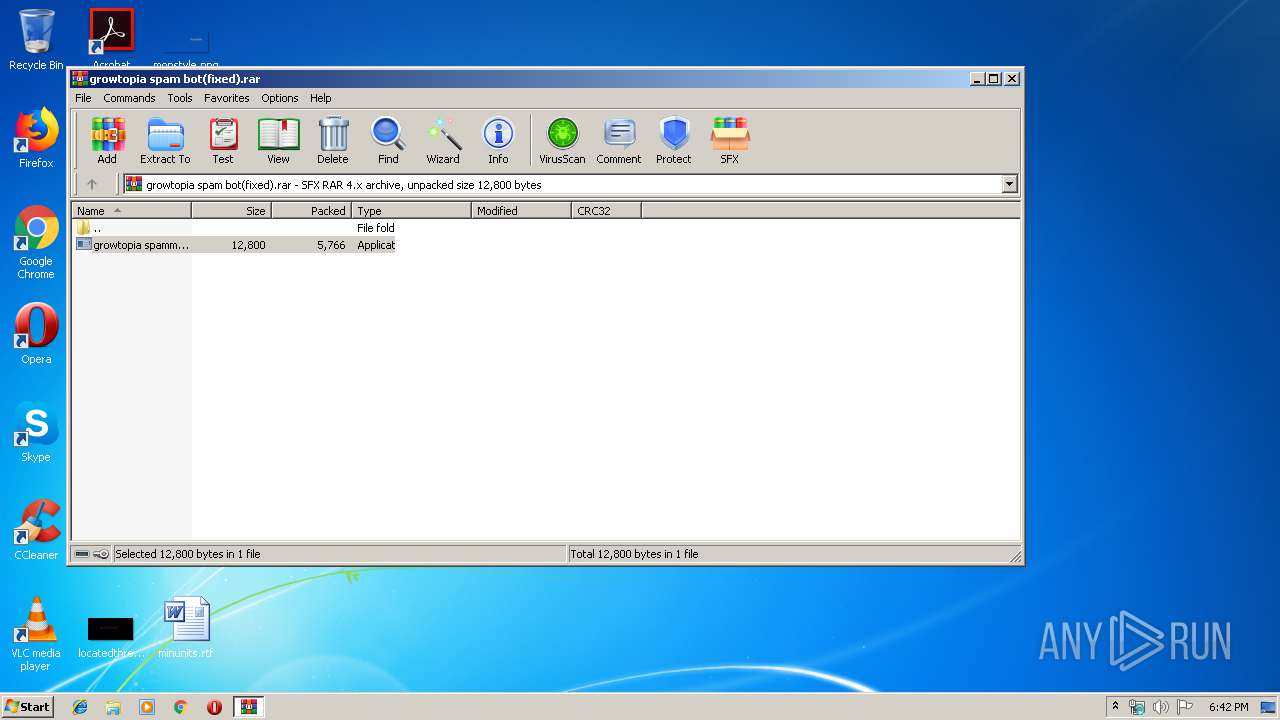
| 2264 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\growtopia spam bot(fixed).rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
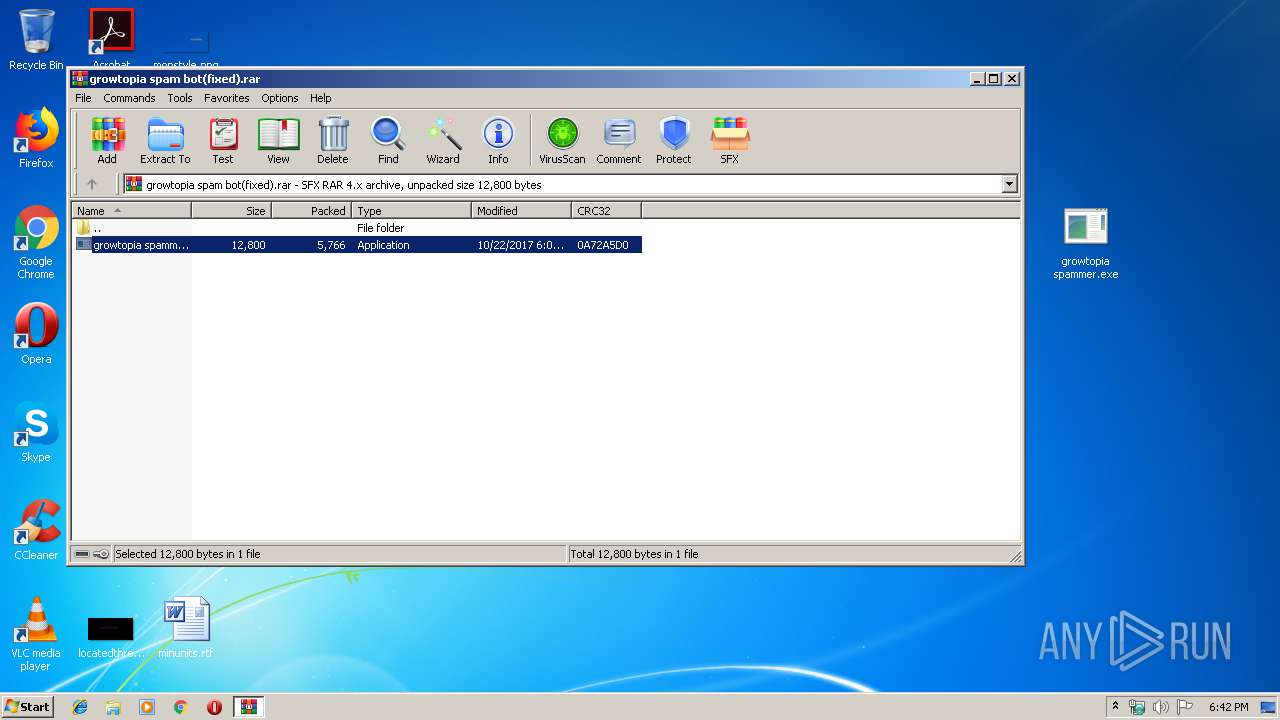
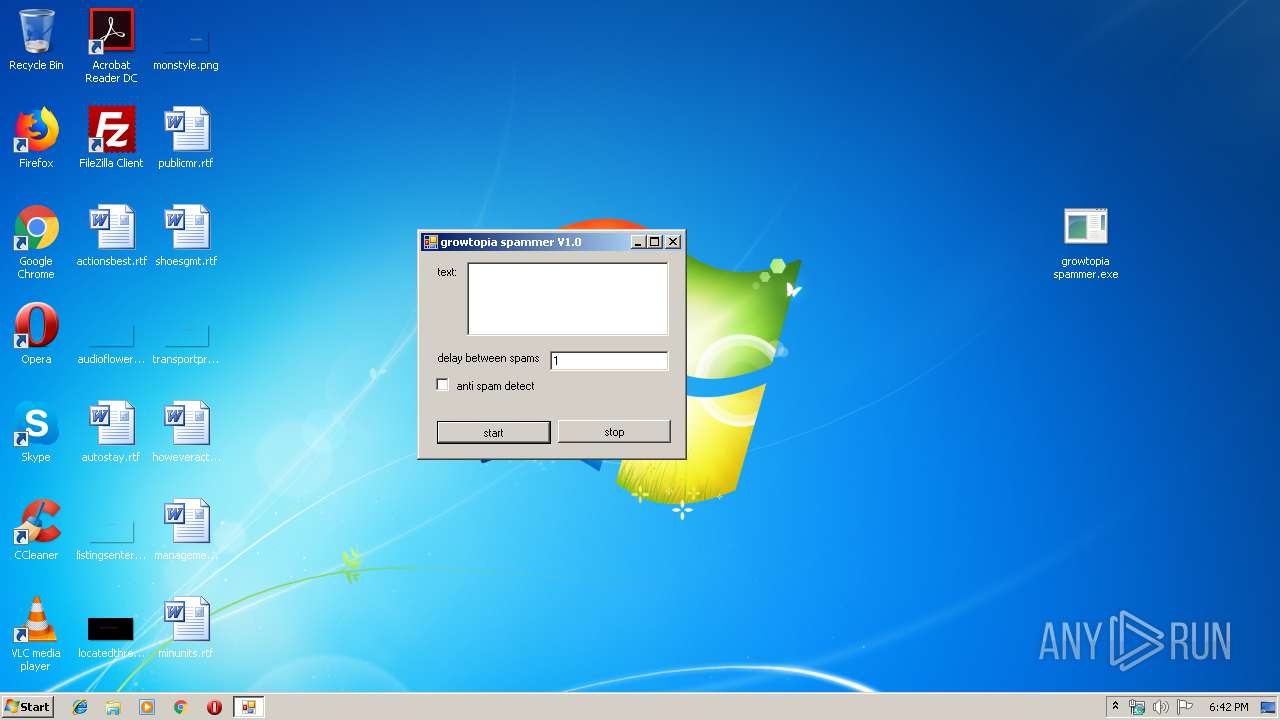
| 2852 | "C:\Users\admin\Desktop\growtopia spammer.exe" | C:\Users\admin\Desktop\growtopia spammer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: growtopia spammer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
478
Read events
443
Write events
35
Delete events
0
Modification events
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\growtopia spam bot(fixed).rar | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2264 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2264.6293\growtopia spammer.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2852 | growtopia spammer.exe | 64.233.184.109:587 | smtp.gmail.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
smtp.gmail.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2852 | growtopia spammer.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2852 | growtopia spammer.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2852 | growtopia spammer.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |