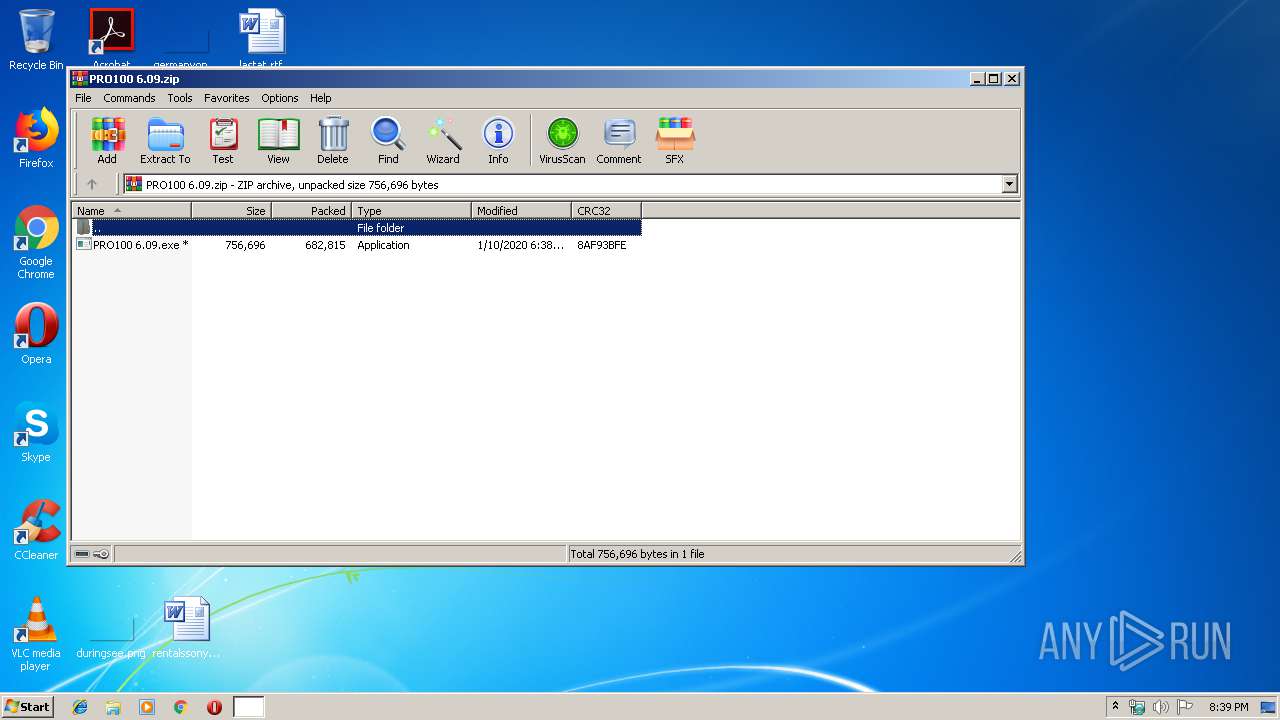
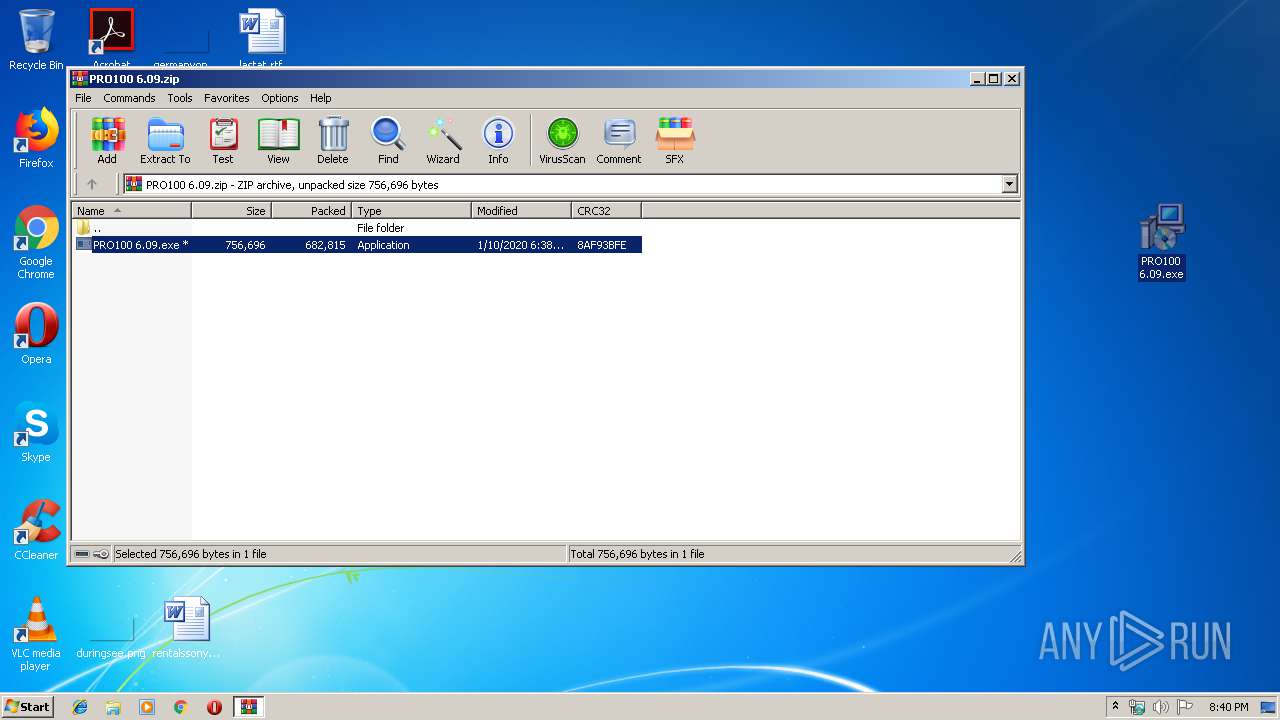
| File name: | PRO100 6.09.zip |
| Full analysis: | https://app.any.run/tasks/ae0e9c5f-52a8-47bb-989a-5115720d6380 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2020, 20:39:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F4FDFA217460296B7884D69C6F5861E1 |
| SHA1: | D898D475233C6D699B94476B4BD2D5DB2F3DF567 |
| SHA256: | 04E011A4154035AA1524640FD12FDD8744A4D55E32118AF11EFCCC19F47E1CCF |
| SSDEEP: | 12288:ARfXwuAXN+d0pF3uFs3M1dP0iLnmoY2t78nBhioA7nGKcA9FlXVtYXnnnTJkPJhk:AqvXsAsQUP0OmoHWBhjAJ/9FlltY2fk |
MALICIOUS
Application was dropped or rewritten from another process
- PRO100 6.09.exe (PID: 2952)
SUSPICIOUS
Executable content was dropped or overwritten
- PRO100 6.09.exe (PID: 2952)
- PRO100 6.09.tmp (PID: 2576)
- 7za.exe (PID: 4004)
Reads the Windows organization settings
- PRO100 6.09.tmp (PID: 2576)
Reads Windows owner or organization settings
- PRO100 6.09.tmp (PID: 2576)
Creates files in the user directory
- PRO100 6.09.tmp (PID: 2576)
INFO
Application was dropped or rewritten from another process
- PRO100 6.09.tmp (PID: 2576)
- 7za.exe (PID: 2344)
- 7za.exe (PID: 836)
- 7za.exe (PID: 4004)
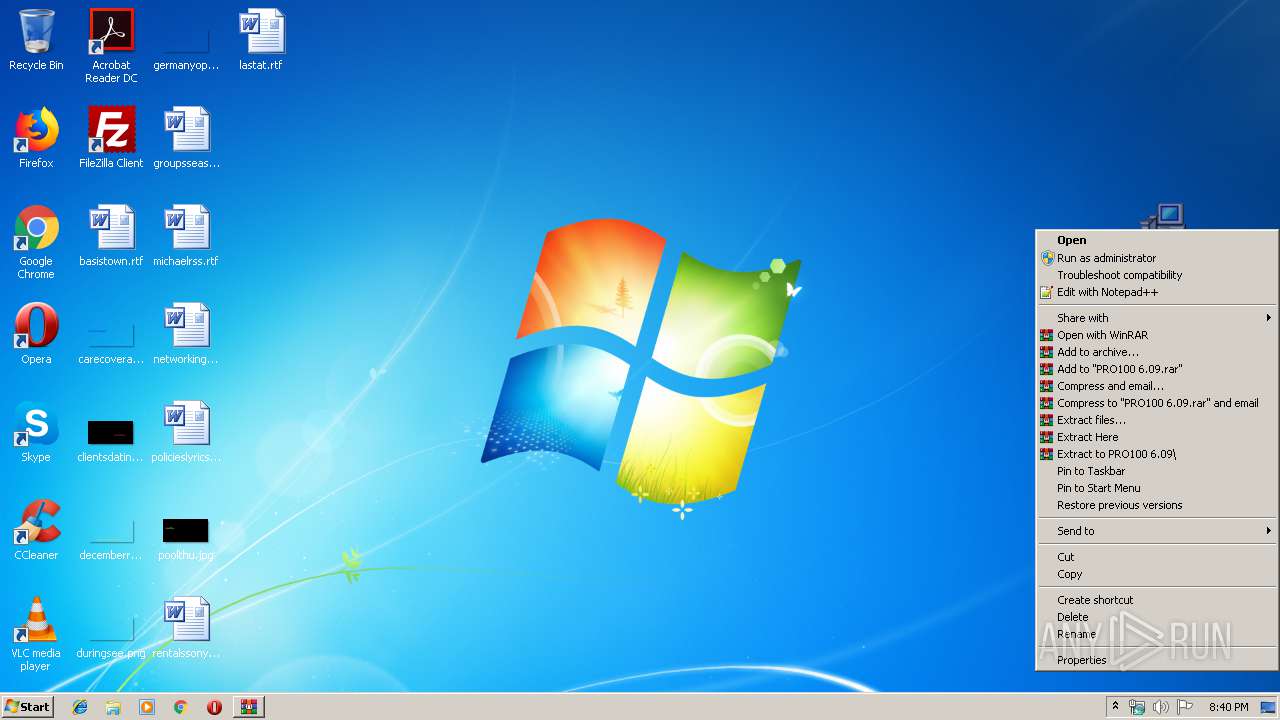
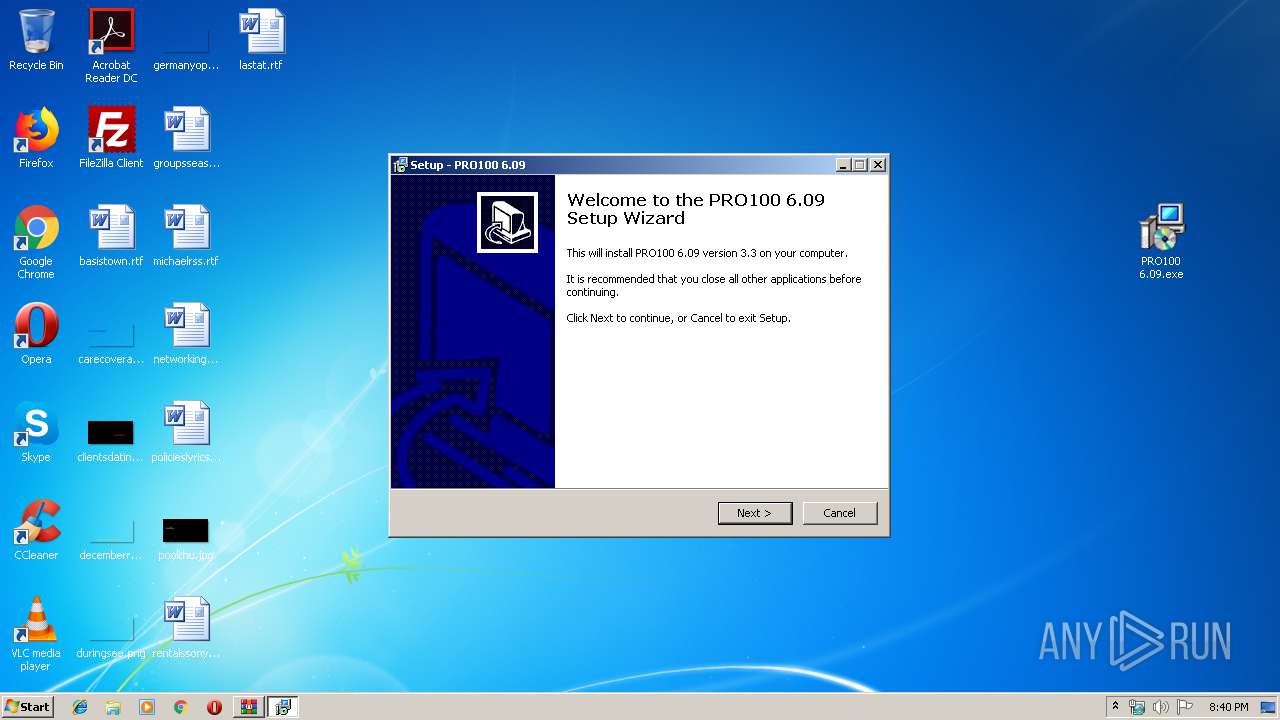
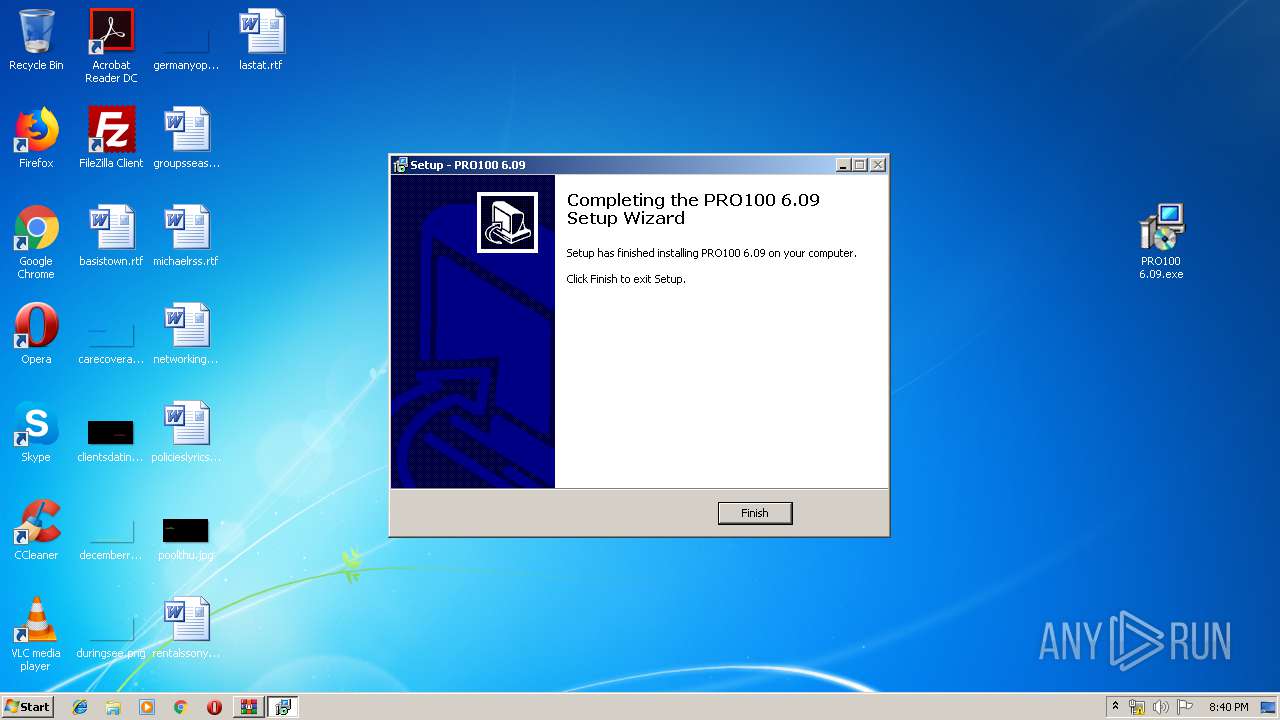
Manual execution by user
- PRO100 6.09.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
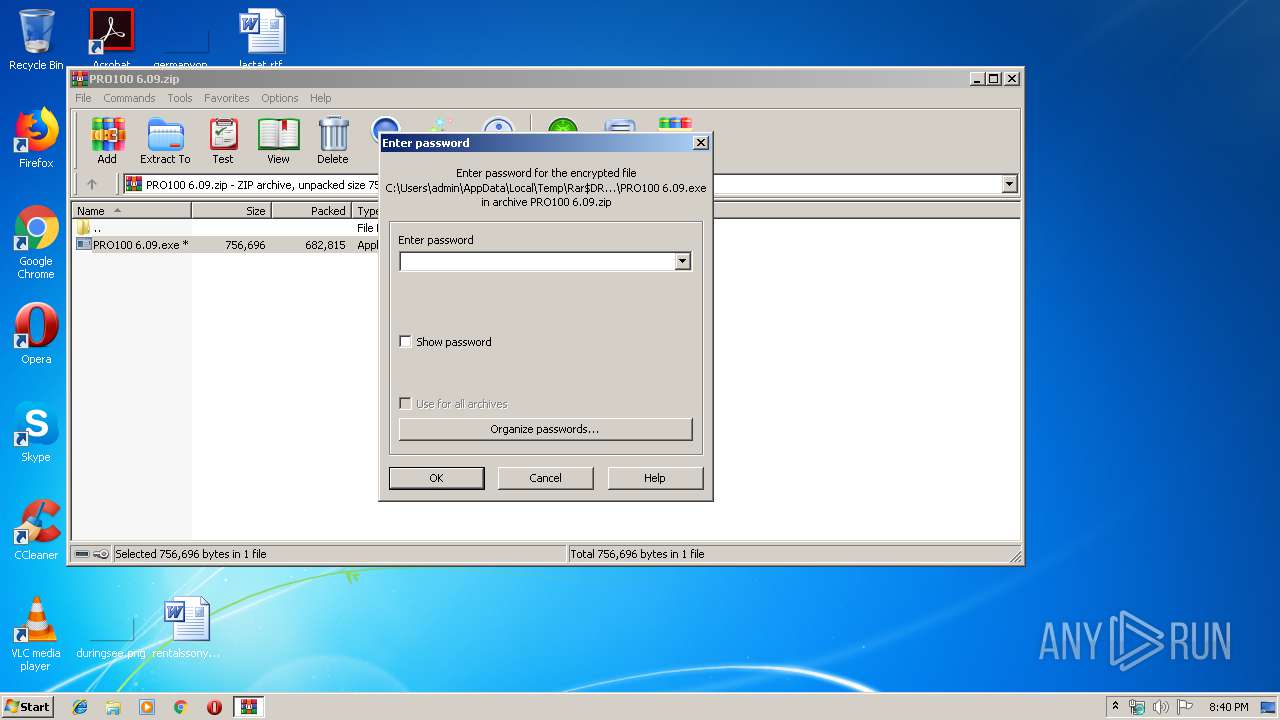
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:10 21:38:15 |
| ZipCRC: | 0x8af93bfe |
| ZipCompressedSize: | 682815 |
| ZipUncompressedSize: | 756696 |
| ZipFileName: | PRO100 6.09.exe |
Total processes
47
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | "C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\misc.res" -p"b1lig@n_vl" | C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\7za.exe | — | PRO100 6.09.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
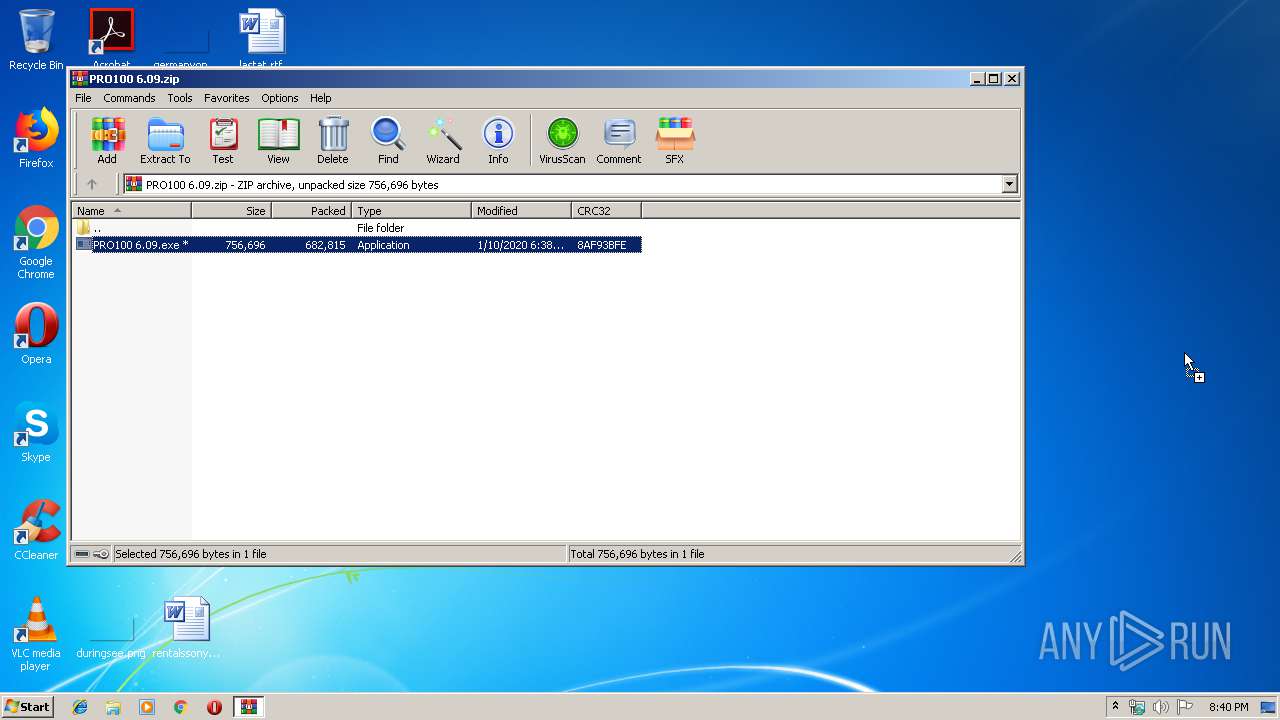
| 2168 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\PRO100 6.09.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\sub.res" -p"b1lig@n_vl" | C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\7za.exe | — | PRO100 6.09.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
| 2576 | "C:\Users\admin\AppData\Local\Temp\is-B20L9.tmp\PRO100 6.09.tmp" /SL5="$4018C,365962,121344,C:\Users\admin\Desktop\PRO100 6.09.exe" | C:\Users\admin\AppData\Local\Temp\is-B20L9.tmp\PRO100 6.09.tmp | PRO100 6.09.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\Desktop\PRO100 6.09.exe" | C:\Users\admin\Desktop\PRO100 6.09.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 0 Version: 3.3 Modules
| |||||||||||||||
| 4004 | "C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\form.res" -p"b1lig@n_vl" | C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\7za.exe | PRO100 6.09.tmp | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
Total events
481
Read events
469
Write events
12
Delete events
0
Modification events
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PRO100 6.09.zip | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2576) PRO100 6.09.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 100A0000B0B89737F6C7D501 | |||
Executable files
4
Suspicious files
3
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2168 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2168.31307\PRO100 6.09.exe | — | |
MD5:— | SHA256:— | |||
| 2576 | PRO100 6.09.tmp | C:\Users\admin\AppData\Local\Temp\{AC9B36B1-F0DA-4C70-BEBD-E3A5983BBD3E}\is-DVL2O.tmp | — | |
MD5:— | SHA256:— | |||
| 2576 | PRO100 6.09.tmp | C:\Users\admin\AppData\Local\Temp\{AC9B36B1-F0DA-4C70-BEBD-E3A5983BBD3E}\license.txt | — | |
MD5:— | SHA256:— | |||
| 2576 | PRO100 6.09.tmp | C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\form.res | compressed | |
MD5:— | SHA256:— | |||
| 2576 | PRO100 6.09.tmp | C:\Users\admin\Desktop\PRO100 6.09\license.txt | text | |
MD5:— | SHA256:— | |||
| 4004 | 7za.exe | C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\form.exe | executable | |
MD5:— | SHA256:— | |||
| 2576 | PRO100 6.09.tmp | C:\Users\admin\AppData\Roaming\UtcTimer\utc.exe | executable | |
MD5:— | SHA256:— | |||
| 2576 | PRO100 6.09.tmp | C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\7za.exe | executable | |
MD5:E92604E043F51C604B6D1AC3BCD3A202 | SHA256:FA252E501332B7486A972E7E471CF6915DAA681AF35C6AA102213921093EB2A3 | |||
| 2576 | PRO100 6.09.tmp | C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\sub.res | compressed | |
MD5:AE50AD46B7EF3517F5DF5EDF2B96443E | SHA256:F4A2B3FA7460606D58AD078D320AFCEAD400285304DC49E8F2BA3FA9800854DC | |||
| 2344 | 7za.exe | C:\Users\admin\AppData\Local\Temp\is-2I5DF.tmp\sub.xml | xml | |
MD5:C047508A4A1F583B7ED31EC7B0DF9695 | SHA256:CD999BAA036D44D442FE43A541D69F04BA206C58938F3C22EC0F226493C63E35 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2576 | PRO100 6.09.tmp | GET | — | 104.27.141.42:80 | http://crackdownloadz.com/provider | US | — | — | shared |
2576 | PRO100 6.09.tmp | POST | 200 | 216.58.207.46:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2576 | PRO100 6.09.tmp | 216.58.207.46:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2576 | PRO100 6.09.tmp | 104.27.141.42:80 | crackdownloadz.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
crackdownloadz.com |
| unknown |