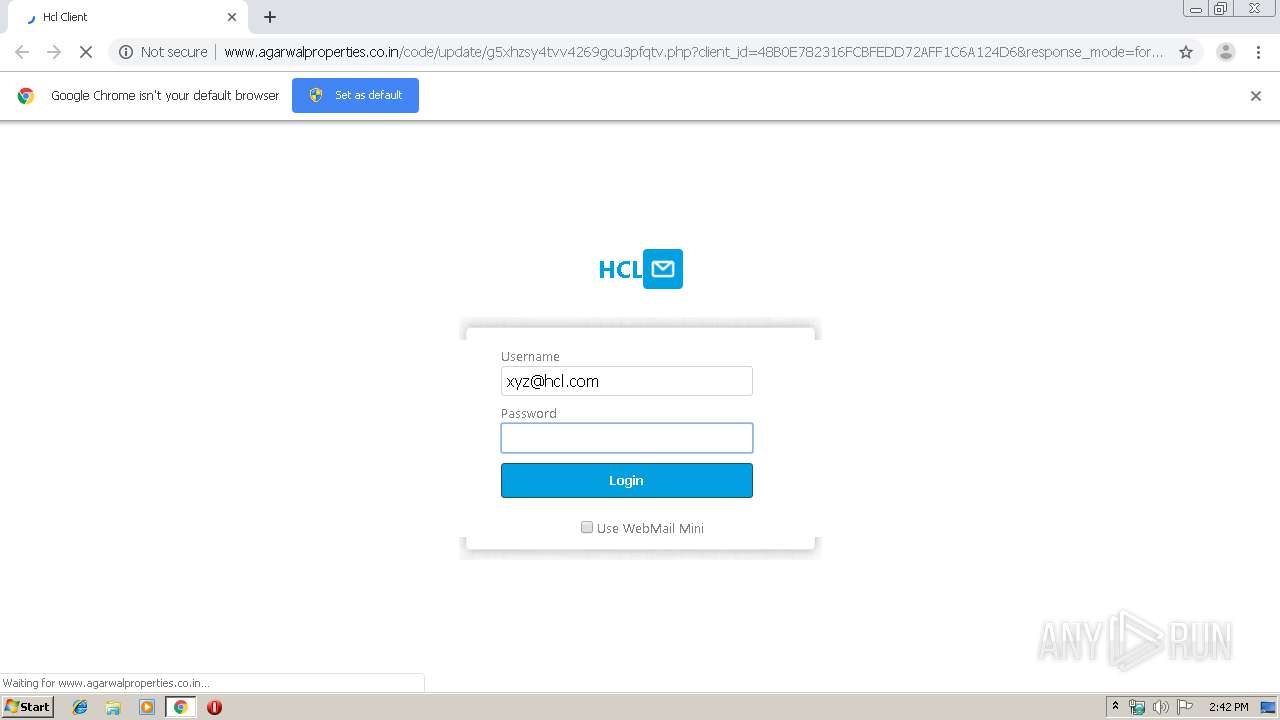
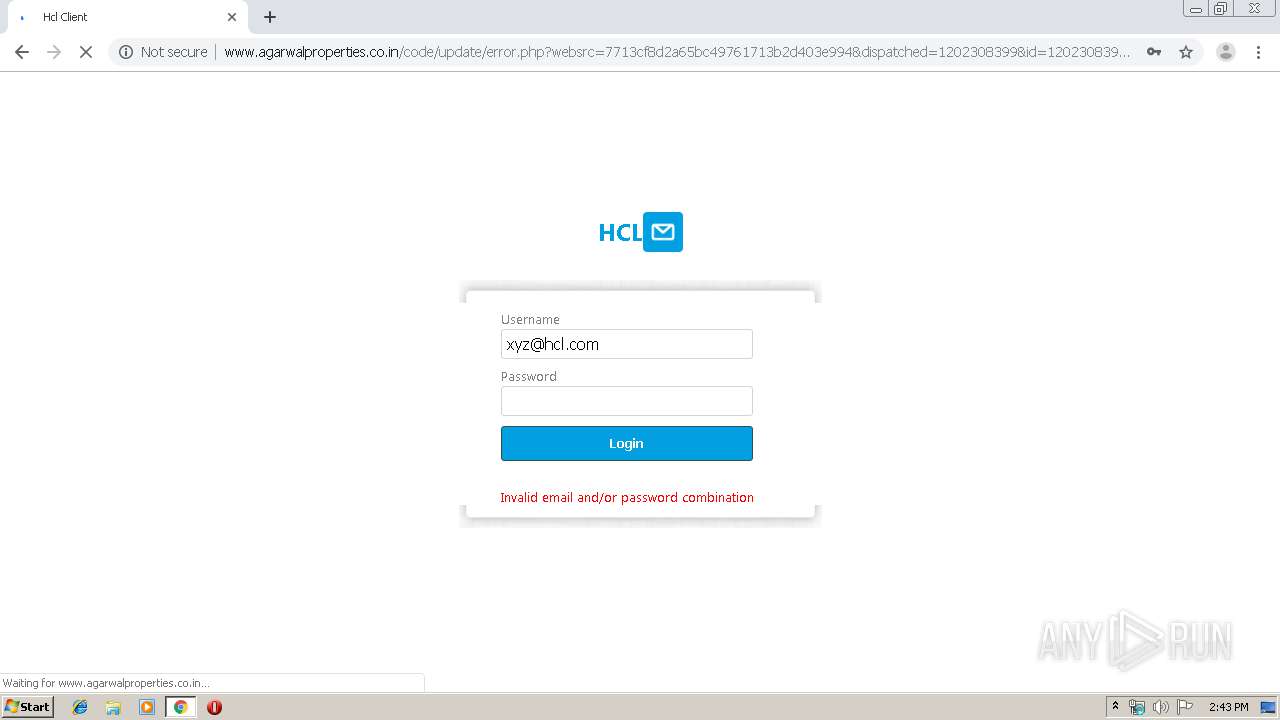
| URL: | http://www.agarwalproperties.co.in/code/update/?email=xyz@hcl.com |
| Full analysis: | https://app.any.run/tasks/f00d70ae-4632-4e09-be63-d0f6ac0e0c25 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 13:42:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F5F907260B74D10E8D6EAD24B9E494D3 |
| SHA1: | 3BB34AED1FDF00505A769D127F9226B1833A1636 |
| SHA256: | 04D34A7EE5192490F845A1F443BD603CF5CA7BEBC89C8B0180843292FD0DF5A2 |
| SSDEEP: | 3:N1KJS4QX3JICk9IpBA5MJwcflNGs:Cc4QX2IZwuWs |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2924)
INFO
Application launched itself
- chrome.exe (PID: 2924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10807436555278202277 --mojo-platform-channel-handle=3768 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11035592073337268910 --mojo-platform-channel-handle=3520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11010442956452736815 --mojo-platform-channel-handle=3764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2985376128745422929 --mojo-platform-channel-handle=3380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11013972534997006752 --mojo-platform-channel-handle=3516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8807549163377187702 --mojo-platform-channel-handle=3328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6907110366633538841 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17121436720272636343 --mojo-platform-channel-handle=3760 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.agarwalproperties.co.in/code/update/?email=xyz@hcl.com | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,16045173077835346543,5191892743981973060,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13846451119504927885 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
585
Read events
514
Write events
67
Delete events
4
Modification events
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2924-13207326148438375 |
Value: 259 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
Executable files
0
Suspicious files
12
Text files
145
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\80337341-7e6a-4c67-be4e-4c8d963eb630.tmp | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF15393a.TMP | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1538fb.TMP | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15390b.TMP | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF153988.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
22
DNS requests
13
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3292 | chrome.exe | GET | 302 | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/?email=xyz@hcl.com | US | — | — | suspicious |
3292 | chrome.exe | GET | 404 | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/login_files/img/middle.png | US | html | 365 b | suspicious |
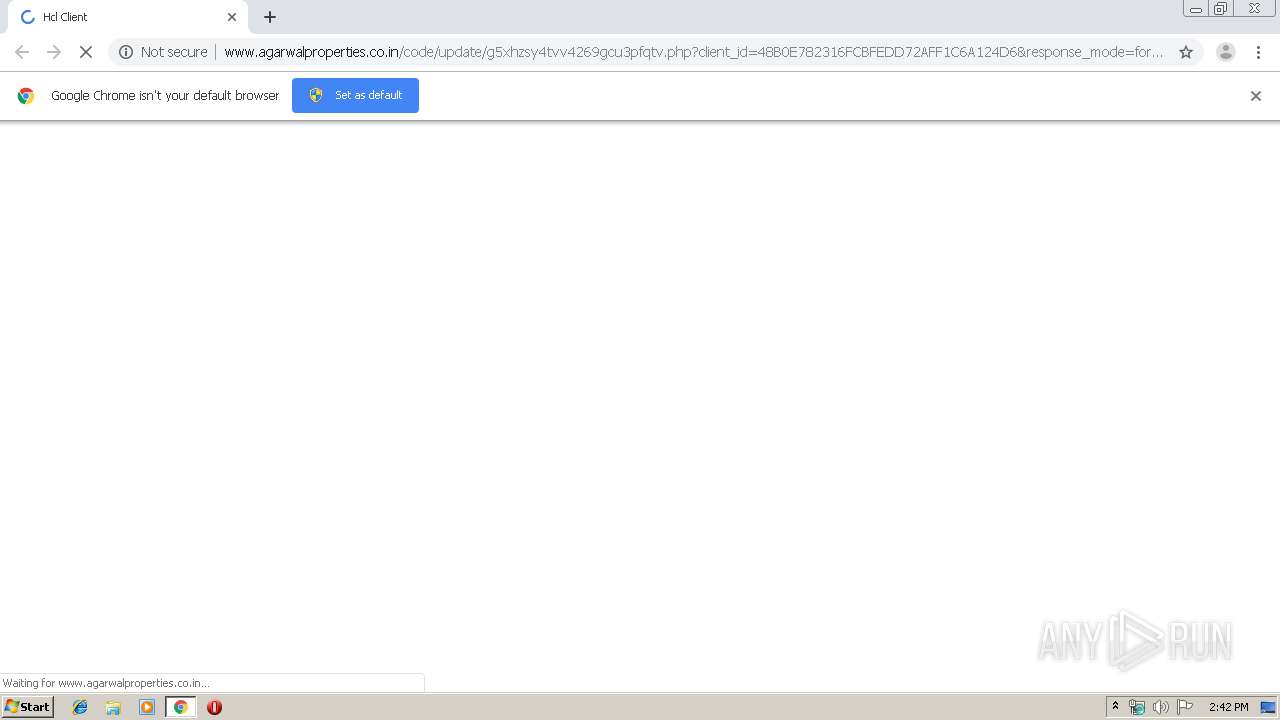
3292 | chrome.exe | GET | 200 | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/g5xhzsy4tvv4269gcu3pfqtv.php?client_id=48B0E782316FCBFEDD72AFF1C6A124D6&response_mode=form_post&response_type=code+id_token&scope=openid+profile&email=xyz@hcl.com&Connect_Authentication_Properties&&nonce=12503221148b0e782316fcbfedd72aff1c6a124d6&redirect_uri=&ui_locales=en-US&mkt=en-US | US | html | 1.12 Kb | suspicious |
3292 | chrome.exe | GET | 404 | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/login_files/img/middle.png | US | html | 1.41 Kb | suspicious |
3292 | chrome.exe | GET | 404 | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/login_files/img/background.png | US | html | 369 b | suspicious |
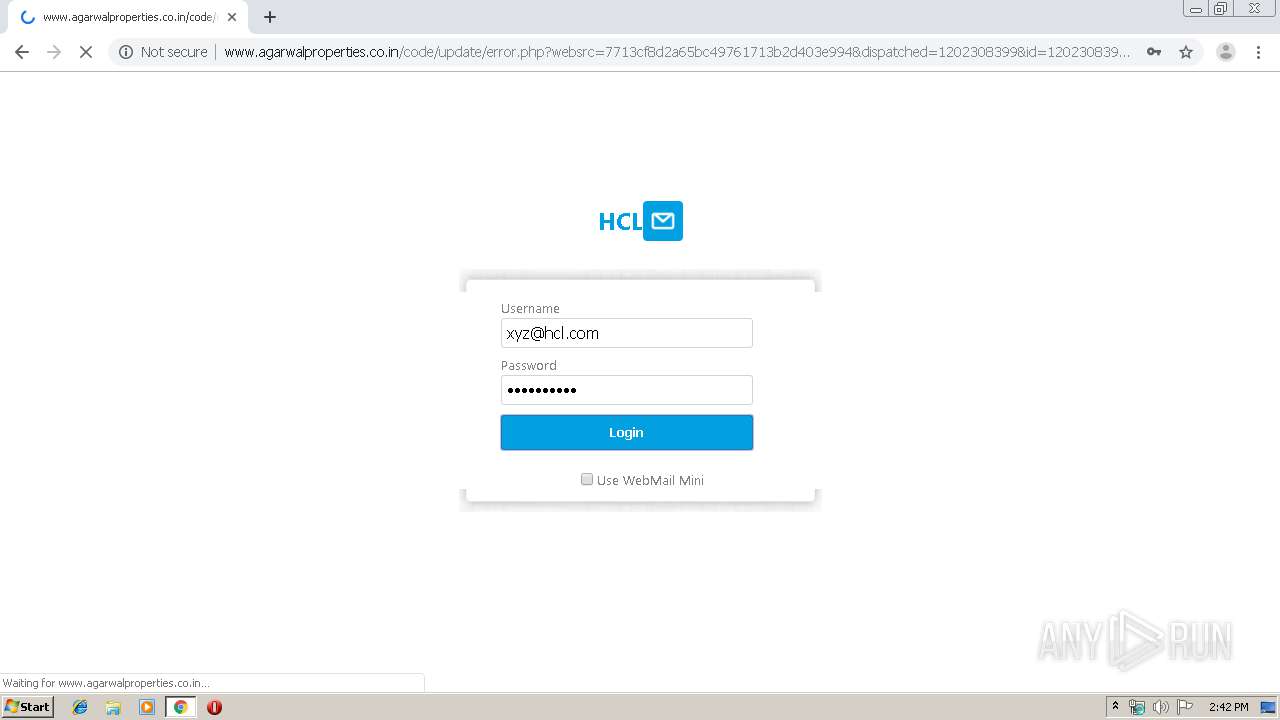
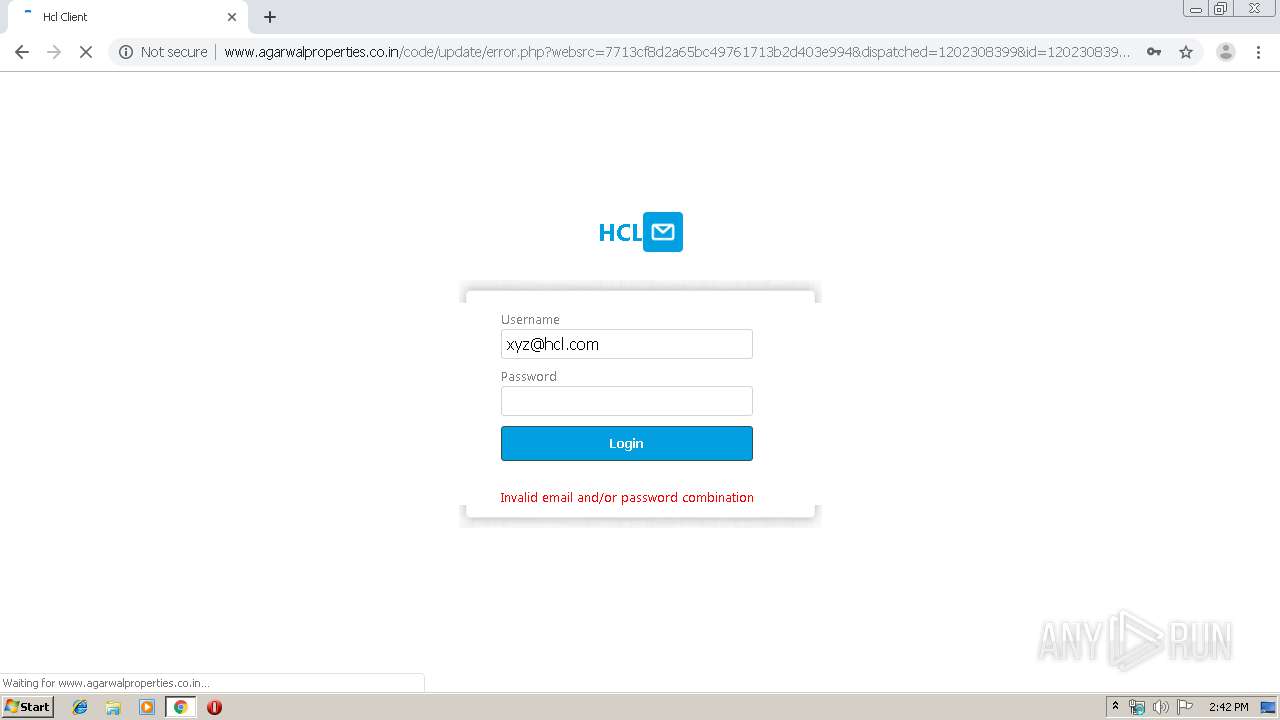
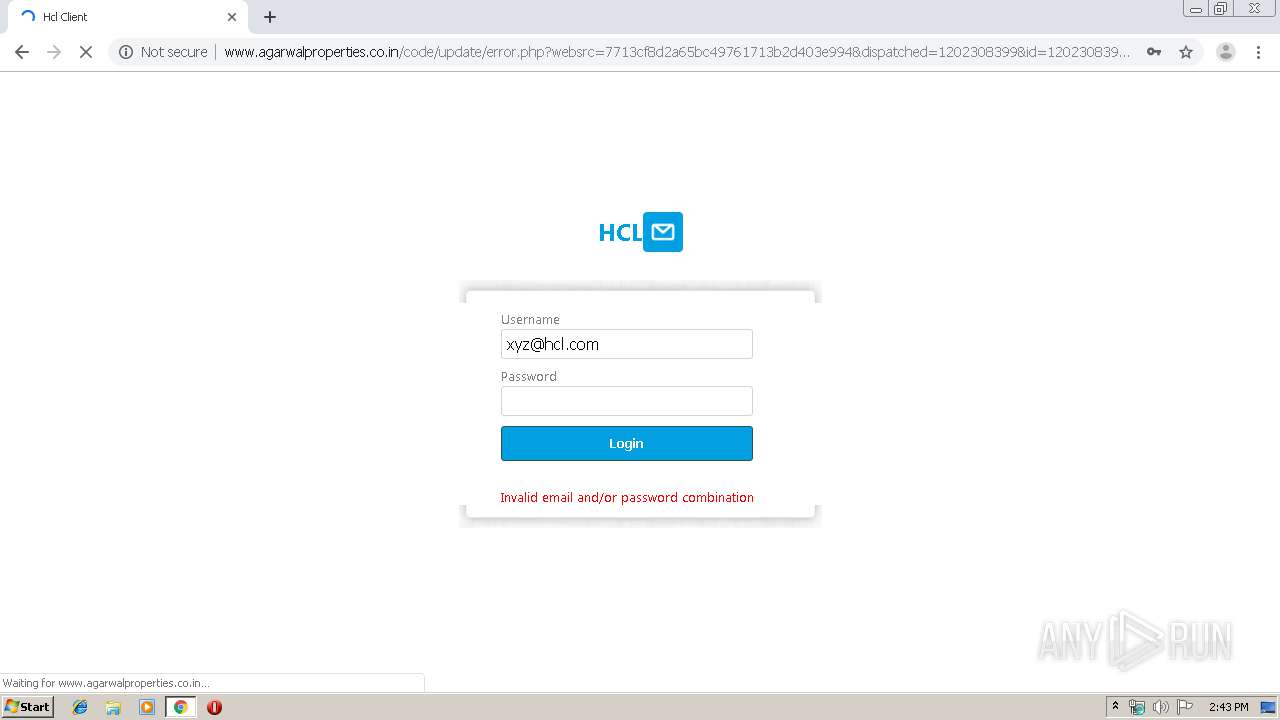
3292 | chrome.exe | POST | — | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/login.php | US | — | — | suspicious |
3292 | chrome.exe | POST | — | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/login.php | US | — | — | suspicious |
3292 | chrome.exe | POST | — | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/login.php | US | — | — | suspicious |
3292 | chrome.exe | POST | — | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/login.php | US | — | — | suspicious |
3292 | chrome.exe | POST | 302 | 160.153.47.71:80 | http://www.agarwalproperties.co.in/code/update/login.php | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3292 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 160.153.47.71:80 | www.agarwalproperties.co.in | GoDaddy.com, LLC | US | suspicious |
3292 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.23.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 172.217.22.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3292 | chrome.exe | 173.194.7.89:80 | r3---sn-p5qs7n7e.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.agarwalproperties.co.in |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-p5qs7n7e.gvt1.com |
| whitelisted |
Threats
8 ETPRO signatures available at the full report