| File name: | AndroidSideloader v2.30.0.exe |
| Full analysis: | https://app.any.run/tasks/5912d619-44e4-4b63-a3f9-45e13f7e86f9 |
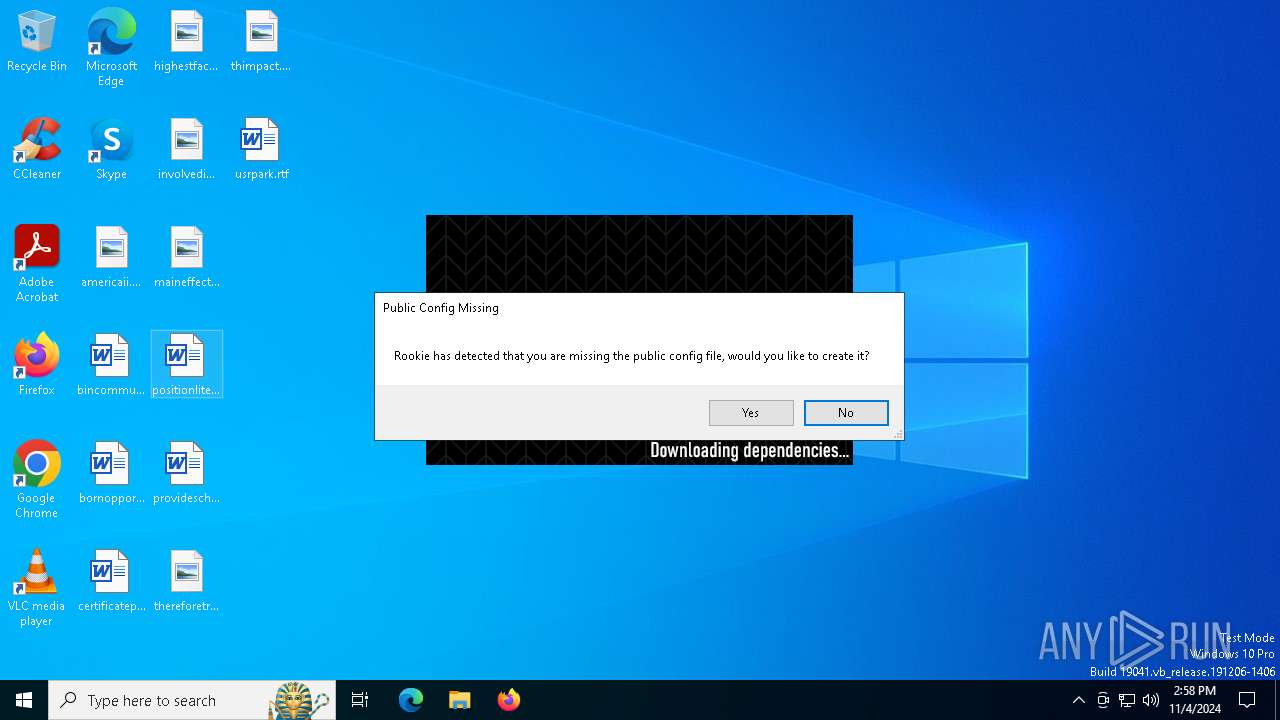
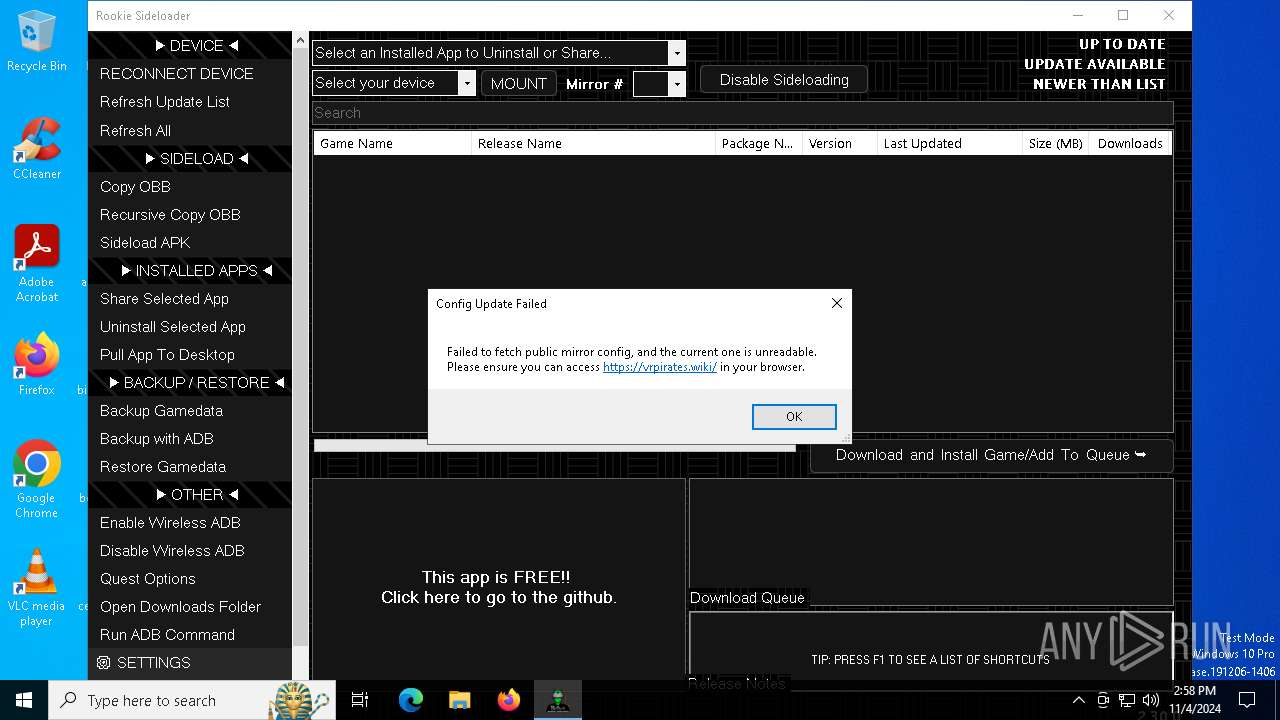
| Verdict: | Malicious activity |
| Analysis date: | November 04, 2024, 14:57:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 7E2B918A866B24B1FAF8CF3AD9292A6E |
| SHA1: | 798C5D509DFAD39EE7384ED604E34A01BA8BD5CB |
| SHA256: | 04CE50B0CF7FDDAAAC3E1940E21234DDFC6F05D352891989F8067310F4EC6A69 |
| SSDEEP: | 98304:ozscEQQLhicXQ+9nWuWqVM5XflB2bz14ZPt:ozw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops 7-zip archiver for unpacking
- AndroidSideloader v2.30.0.exe (PID: 6828)
Executable content was dropped or overwritten
- AndroidSideloader v2.30.0.exe (PID: 6828)
- 7z.exe (PID: 616)
Application launched itself
- adb.exe (PID: 5324)
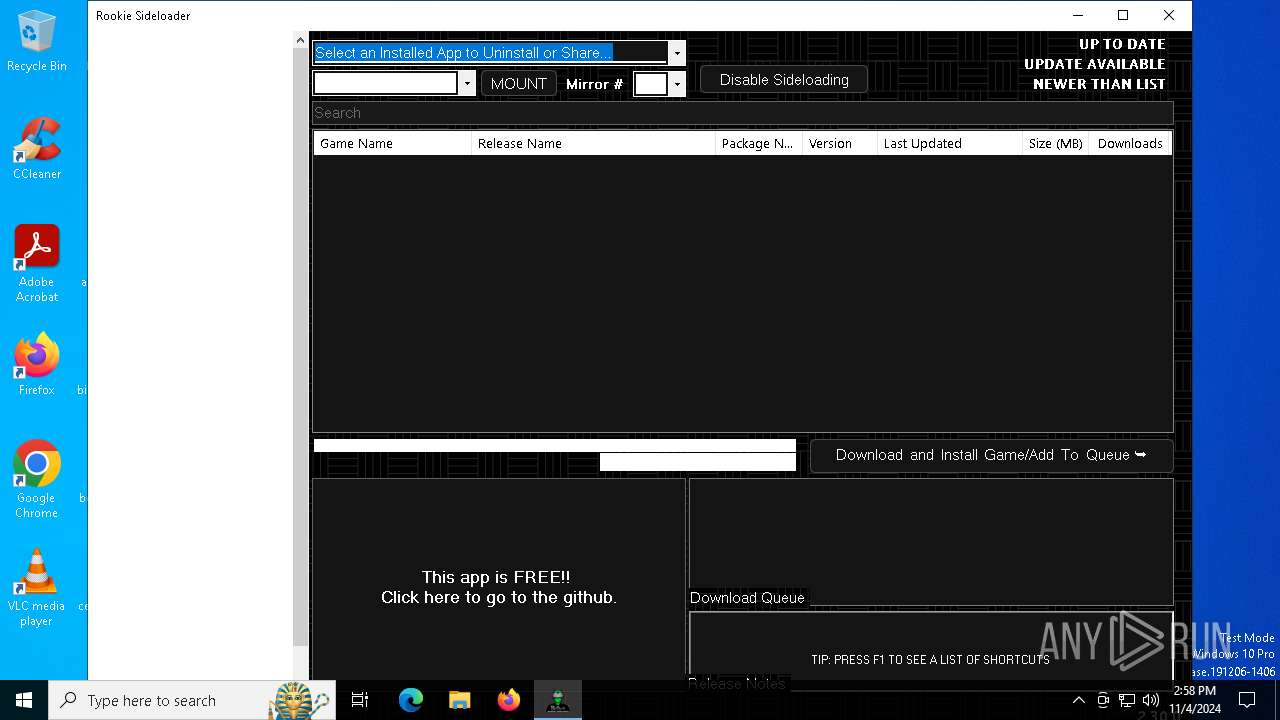
RCLONE has been detected
- rclone.exe (PID: 6720)
- rclone.exe (PID: 6840)
- rclone.exe (PID: 3608)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2084:06:09 06:12:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 3967488 |
| InitializedDataSize: | 413184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3ca94e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Rookie Sideloader |
| CompanyName: | Rookie.AndroidSideloader |
| FileDescription: | AndroidSideloader |
| FileVersion: | 2.0.0.0 |
| InternalName: | AndroidSideloader.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | AndroidSideloader.exe |
| ProductName: | AndroidSideloader |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Total processes
146
Monitored processes
18
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "7z.exe" x "C:\Users\admin\AppData\Local\Temp\dependencies.7z" -y -o"C:\RSL\platform-tools" -bsp1 | C:\Users\admin\AppData\Local\Temp\7z.exe | AndroidSideloader v2.30.0.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 23.01 Modules
| |||||||||||||||
| 1784 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | adb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3076 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rclone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3608 | "C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe" listremotes --config vrp.download.config --inplace | C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe | AndroidSideloader v2.30.0.exe | ||||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rclone Exit code: 0 Version: 1.67.0 Modules
| |||||||||||||||
| 3944 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | adb.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rclone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5324 | "C:\RSL\platform-tools\adb.exe" start-server | C:\RSL\platform-tools\adb.exe | — | AndroidSideloader v2.30.0.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
10 662
Read events
10 648
Write events
14
Delete events
0
Modification events
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6828) AndroidSideloader v2.30.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader v2_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
16
Suspicious files
1
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Temp\dependencies.7z | — | |
MD5:— | SHA256:— | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Rookie.AndroidSideloader\AndroidSideloader_v2.30.0_Url_j522t2rc0mex5gotxv22wepuzpah2b2g\2.0.0.0\user.config | xml | |
MD5:6DC22626C68E39D1F7A92BC247D064FA | SHA256:5B1CFB327E8E4F605CDB650526AB442CC846CE97CFDC51D1DA23DFECB3ABDF60 | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Temp\CleanupInstall.cmd | text | |
MD5:239D9321BECFBBD0987E6BFD2F541C4C | SHA256:08899D7F1FF00C2482CED57325D4FEF0C23BF7F827F8DC26494760DBFCC0FF82 | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Rookie.AndroidSideloader\AndroidSideloader_v2.30.0_Url_j522t2rc0mex5gotxv22wepuzpah2b2g\2.0.0.0\ttohj21x.newcfg | xml | |
MD5:6DC22626C68E39D1F7A92BC247D064FA | SHA256:5B1CFB327E8E4F605CDB650526AB442CC846CE97CFDC51D1DA23DFECB3ABDF60 | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Temp\Sideloader Launcher.exe | executable | |
MD5:A53A5E70248EB3DA58DEFA74B0554704 | SHA256:98BC8CF1C6A59EF70D6431E1E92887984E5B21C8FBC85B4AD23CCC70589C4B1F | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Rookie.AndroidSideloader\AndroidSideloader_v2.30.0_Url_j522t2rc0mex5gotxv22wepuzpah2b2g\2.0.0.0\lwf0isty.newcfg | xml | |
MD5:853207CA70D7A90ED710C5EC30C17E61 | SHA256:7DB9B306652D4F86F7431CDF22B4309D3EE89E971B2F1308B8B8A3CAD2E4D47E | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Temp\7z.exe | executable | |
MD5:1A7EAA1DAB7867E15D7800AE0B5AF5E3 | SHA256:356BEA8B6E9EB84DFA0DD8674E7C03428C641A47789DF605C5BEA0730DE4AED2 | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Rookie.AndroidSideloader\AndroidSideloader_v2.30.0_Url_j522t2rc0mex5gotxv22wepuzpah2b2g\2.0.0.0\hkghgkca.newcfg | xml | |
MD5:281777B6097FADB58D8502F162987B91 | SHA256:7EC357ACD795CFF84C799A9549487FB330D474FCB3CBC671F8D18F2158BB1834 | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Temp\Rookie Offline.cmd | text | |
MD5:513248E44025E42FD2B8F9280501A8BB | SHA256:7DD245A6267A6D9500EE6B13A29FBDD80CEF9A020162C0E24A228558C58FA092 | |||
| 6828 | AndroidSideloader v2.30.0.exe | C:\Users\admin\AppData\Local\Temp\7z.dll | executable | |
MD5:71EBAC040D32560BB9D76A552A7CB986 | SHA256:1AA51AA9BB50B26BB652D9C442208DB76546286B0DB169C8882DE97D1117029D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
45
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | BR | binary | 973 b | whitelisted |
5588 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
3948 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6612 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | BR | binary | 418 b | whitelisted |
6612 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | BR | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4360 | SearchApp.exe | 2.23.209.176:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1248 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3948 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6828 | AndroidSideloader v2.30.0.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |