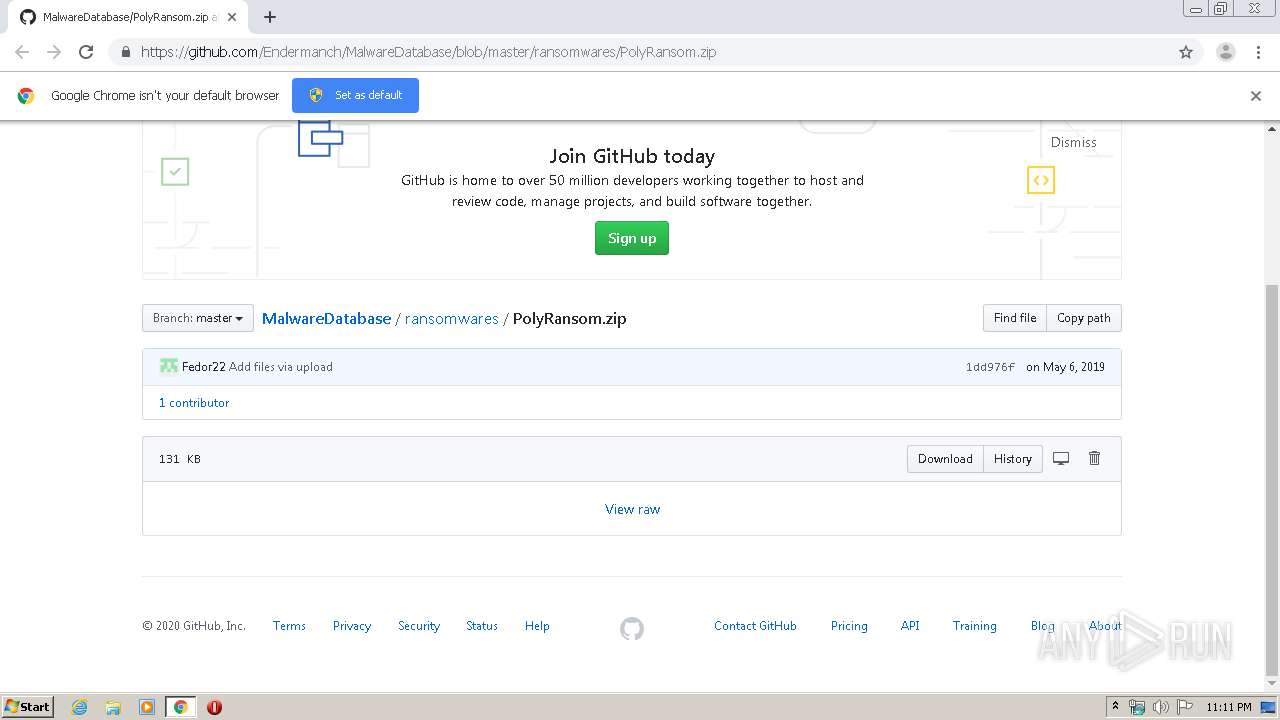
| URL: | https://github.com/Endermanch/MalwareDatabase/blob/master/ransomwares/PolyRansom.zip |
| Full analysis: | https://app.any.run/tasks/4a3f511c-659e-40c8-9a45-506bbbb5e7ec |
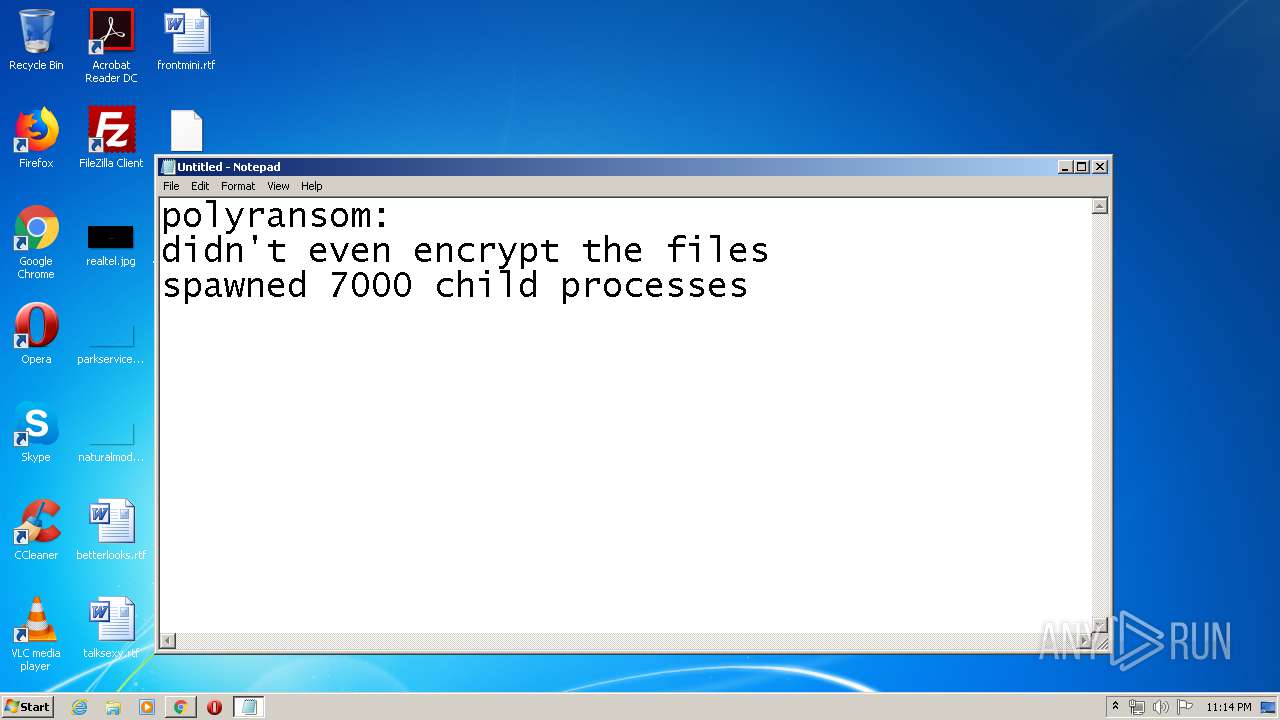
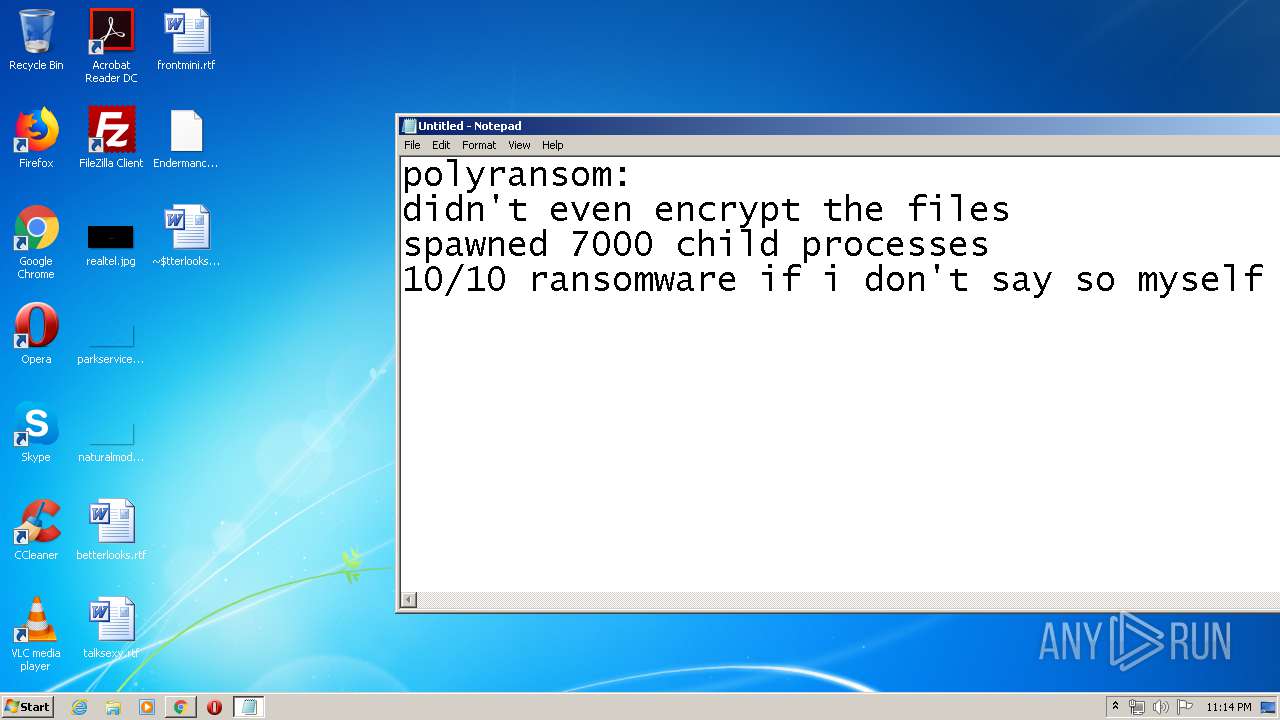
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2020, 22:10:53 |
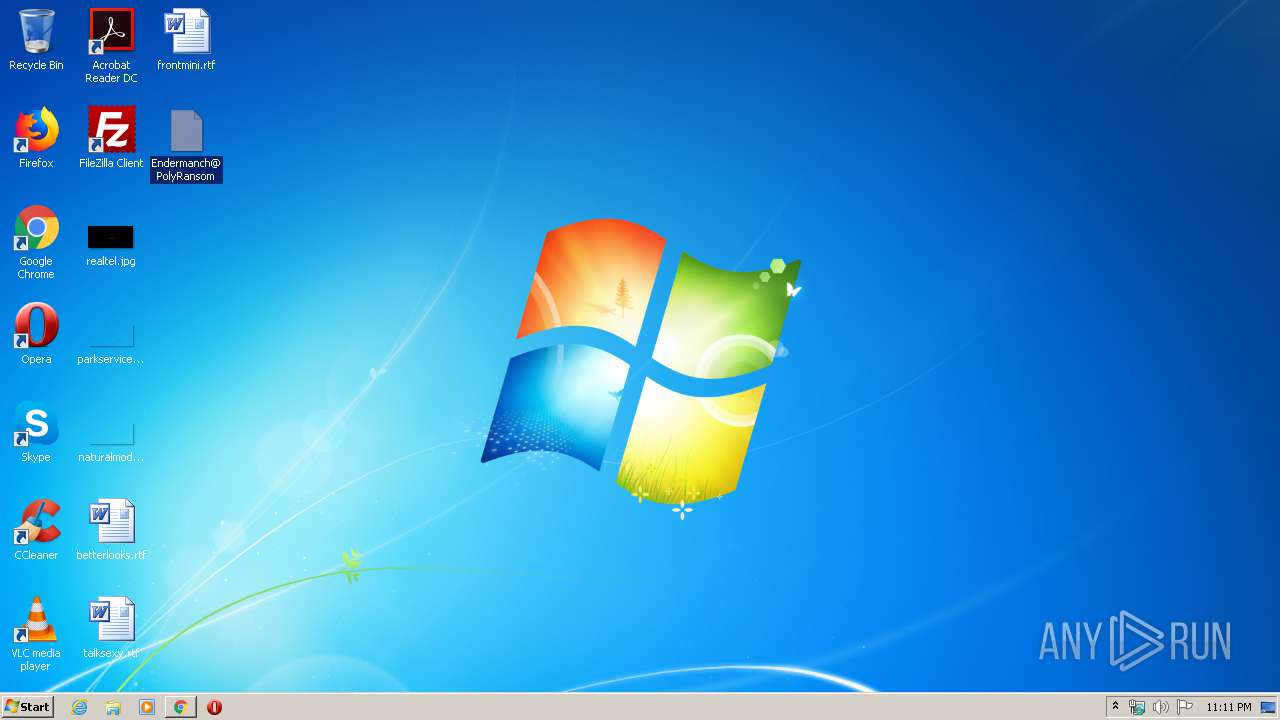
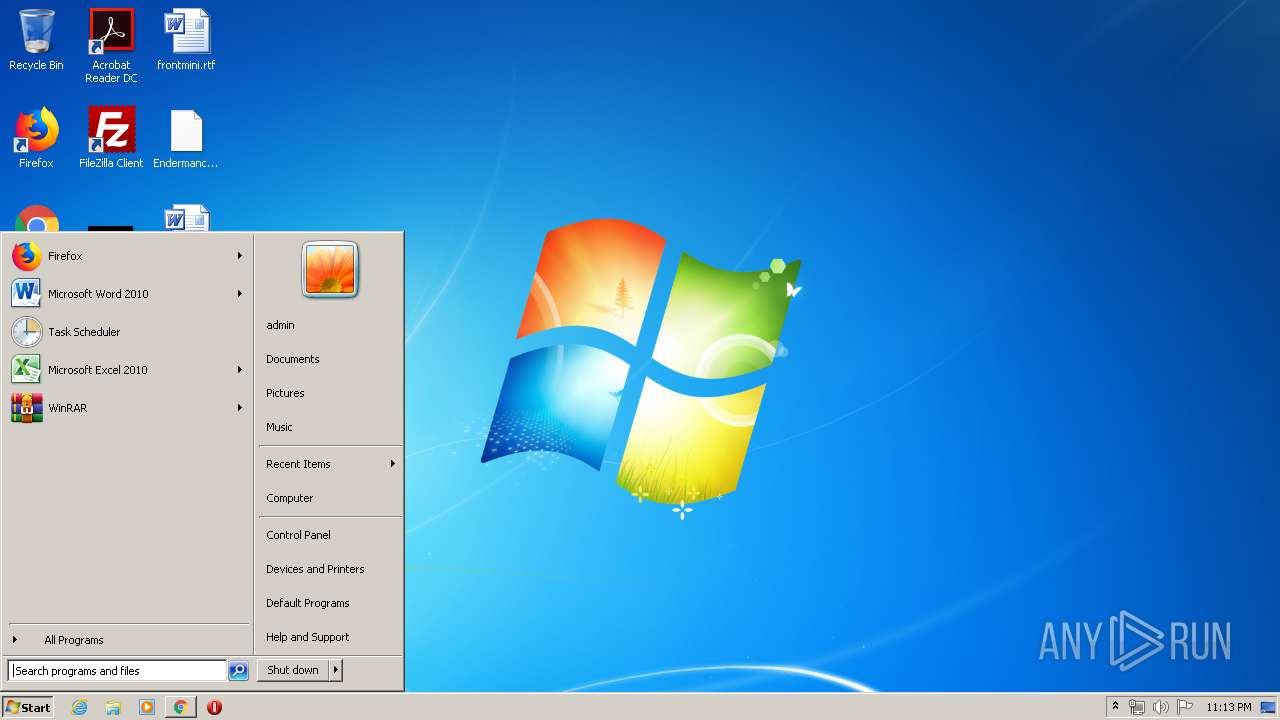
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
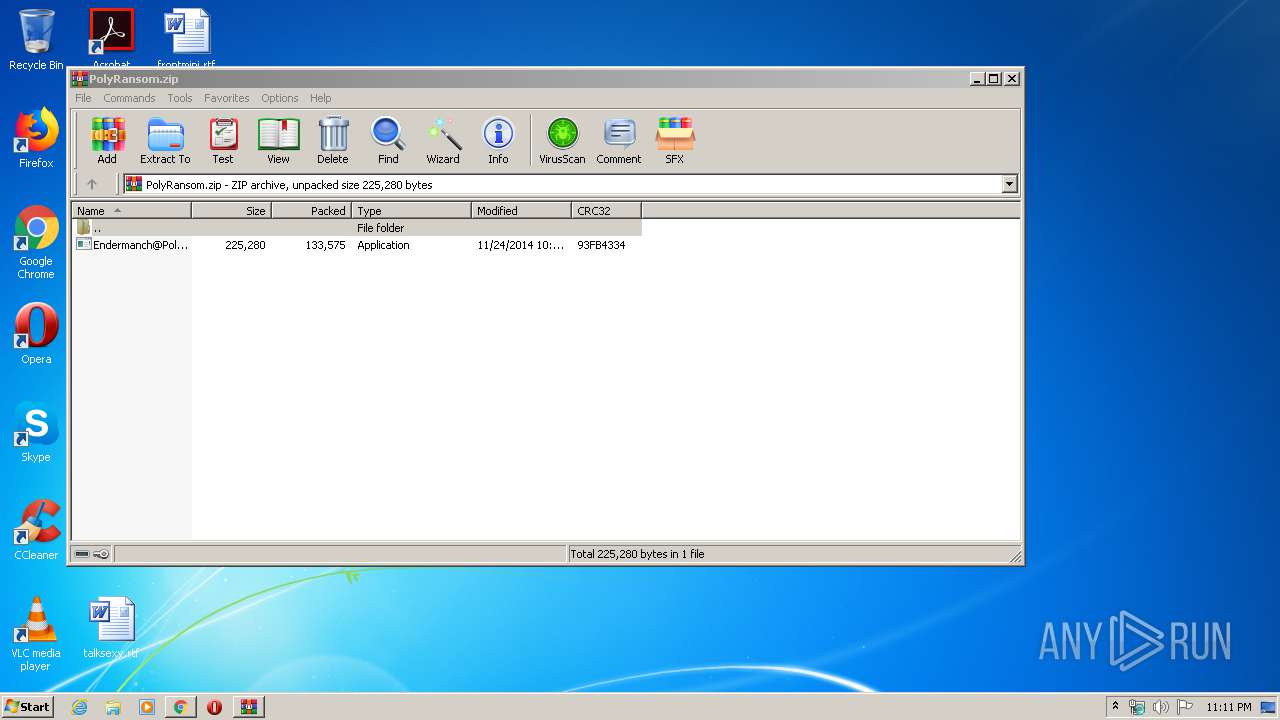
| MD5: | 7A02EEF57057D1F96FA58B6D8E2297C3 |
| SHA1: | 9C1D1C9EBB3E428847FFACA057D8A89BF92684FA |
| SHA256: | 04C88CB9D3D40C8A4DD9C3175DA9CA120F8D992B4FF26EA078ED8A1898F20DBE |
| SSDEEP: | 3:N8tEdegLaKoEJ3PqkzEHcEie+m1KIMV:2ufLtfnz+cEizm1JMV |
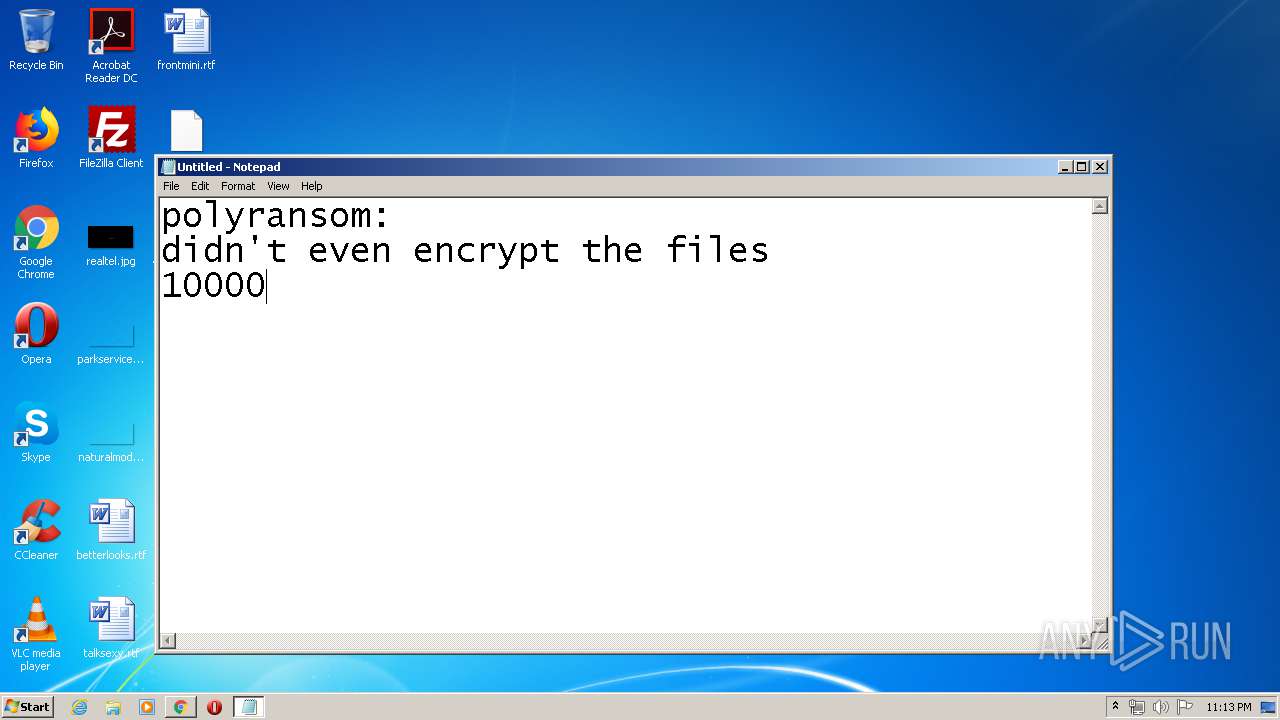
MALICIOUS
Changes the autorun value in the registry
- Endermanch@PolyRansom.exe (PID: 2284)
- UoQoIUws.exe (PID: 2536)
- tQoIUcQA.exe (PID: 1532)
- tQoIUcQA.exe (PID: 5852)
- UoQoIUws.exe (PID: 4504)
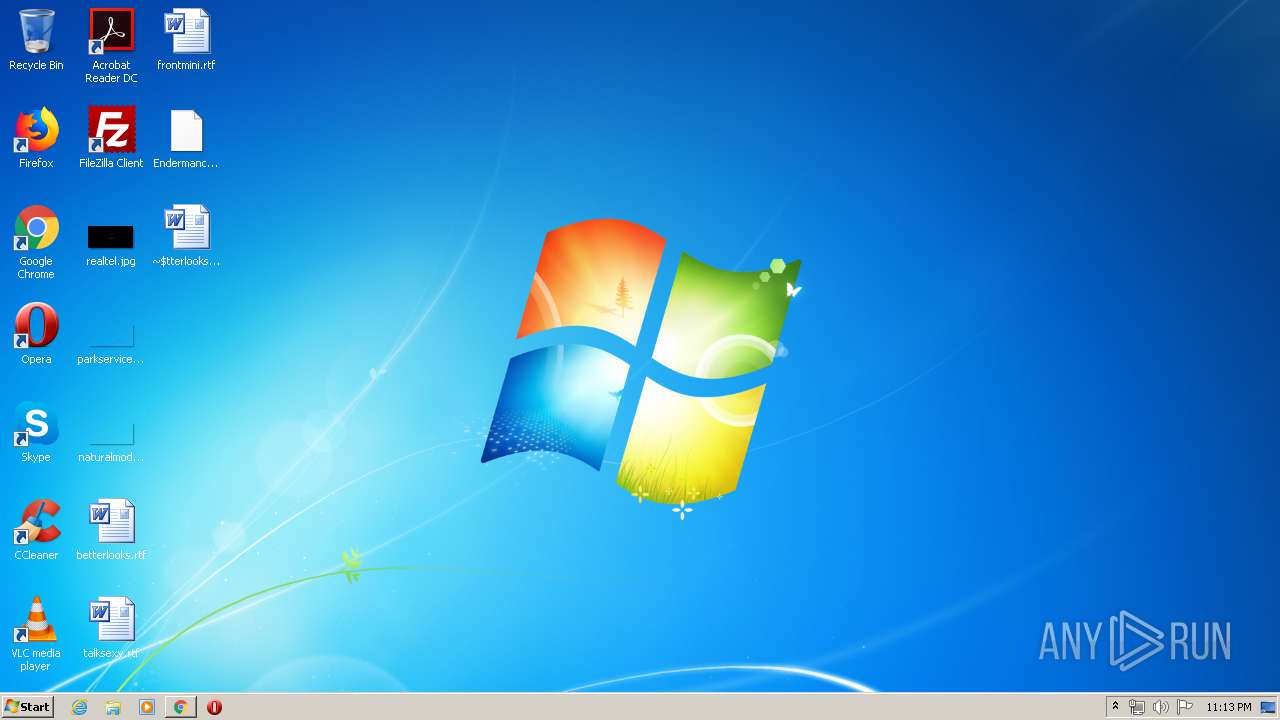
Application was dropped or rewritten from another process
- Endermanch@PolyRansom.exe (PID: 2336)
- Endermanch@PolyRansom.exe (PID: 2284)
- Endermanch@PolyRansom.exe (PID: 3604)
- Endermanch@PolyRansom.exe (PID: 3208)
- Endermanch@PolyRansom.exe (PID: 2128)
- UoQoIUws.exe (PID: 2536)
- Endermanch@PolyRansom.exe (PID: 3016)
- Endermanch@PolyRansom.exe (PID: 2432)
- Endermanch@PolyRansom.exe (PID: 2604)
- tQoIUcQA.exe (PID: 1532)
- Endermanch@PolyRansom.exe (PID: 2488)
- Endermanch@PolyRansom.exe (PID: 2556)
- Endermanch@PolyRansom.exe (PID: 3444)
- Endermanch@PolyRansom.exe (PID: 2584)
- Endermanch@PolyRansom.exe (PID: 2564)
- Endermanch@PolyRansom.exe (PID: 2668)
- Endermanch@PolyRansom.exe (PID: 724)
- Endermanch@PolyRansom.exe (PID: 2544)
- Endermanch@PolyRansom.exe (PID: 4052)
- Endermanch@PolyRansom.exe (PID: 5100)
- Endermanch@PolyRansom.exe (PID: 5640)
- Endermanch@PolyRansom.exe (PID: 5456)
- Endermanch@PolyRansom.exe (PID: 4804)
- Endermanch@PolyRansom.exe (PID: 5496)
- Endermanch@PolyRansom.exe (PID: 4744)
- tQoIUcQA.exe (PID: 5852)
- UoQoIUws.exe (PID: 4504)
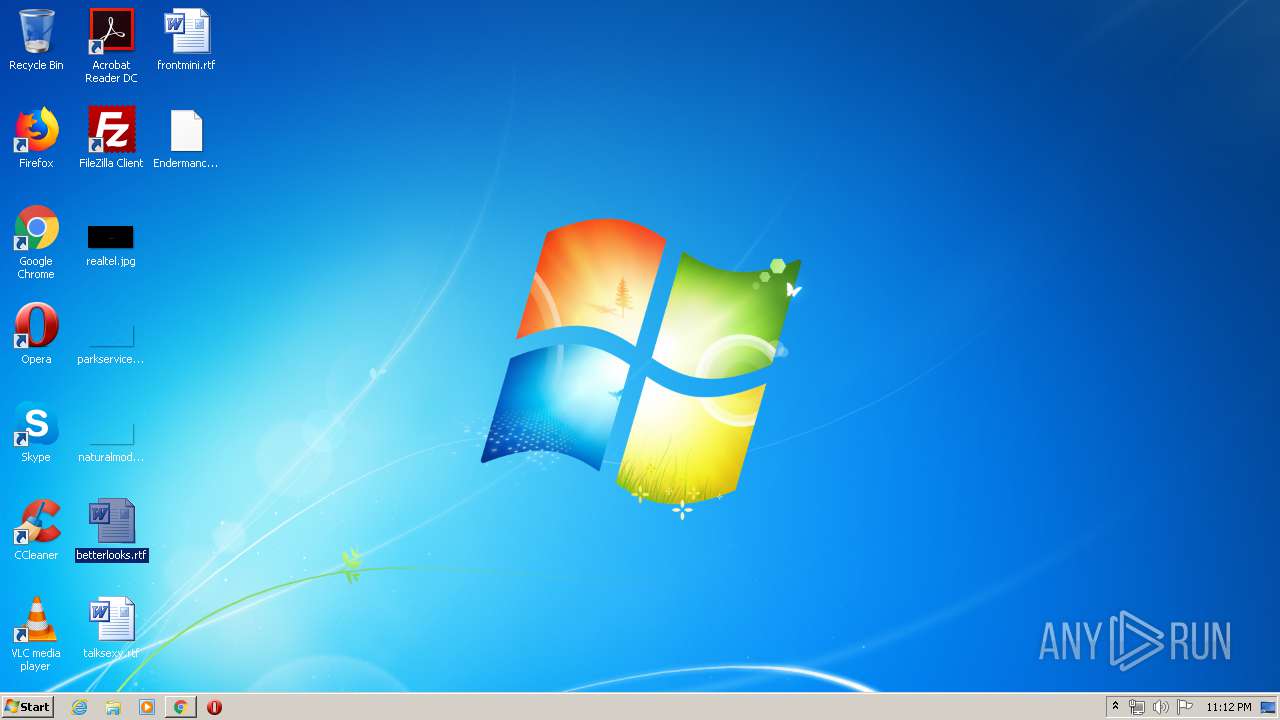
Modifies files in Chrome extension folder
- UoQoIUws.exe (PID: 2536)
Actions looks like stealing of personal data
- DllHost.exe (PID: 3688)
- UoQoIUws.exe (PID: 2536)
SUSPICIOUS
Executable content was dropped or overwritten
- Endermanch@PolyRansom.exe (PID: 2284)
- UoQoIUws.exe (PID: 2536)
- tQoIUcQA.exe (PID: 5852)
Creates files in the program directory
- Endermanch@PolyRansom.exe (PID: 2284)
- UoQoIUws.exe (PID: 2536)
Starts CMD.EXE for commands execution
- Endermanch@PolyRansom.exe (PID: 2284)
- Endermanch@PolyRansom.exe (PID: 2336)
- Endermanch@PolyRansom.exe (PID: 3604)
- Endermanch@PolyRansom.exe (PID: 2128)
- Endermanch@PolyRansom.exe (PID: 3016)
- Endermanch@PolyRansom.exe (PID: 2604)
- Endermanch@PolyRansom.exe (PID: 2432)
- Endermanch@PolyRansom.exe (PID: 3208)
- Endermanch@PolyRansom.exe (PID: 3444)
- Endermanch@PolyRansom.exe (PID: 2556)
- Endermanch@PolyRansom.exe (PID: 2584)
- Endermanch@PolyRansom.exe (PID: 2564)
- Endermanch@PolyRansom.exe (PID: 2488)
- Endermanch@PolyRansom.exe (PID: 2668)
- Endermanch@PolyRansom.exe (PID: 2544)
- Endermanch@PolyRansom.exe (PID: 4052)
- Endermanch@PolyRansom.exe (PID: 724)
- Endermanch@PolyRansom.exe (PID: 5100)
- Endermanch@PolyRansom.exe (PID: 4804)
- Endermanch@PolyRansom.exe (PID: 5456)
- Endermanch@PolyRansom.exe (PID: 5496)
- Endermanch@PolyRansom.exe (PID: 4744)
- Endermanch@PolyRansom.exe (PID: 5640)
Uses REG.EXE to modify Windows registry
- Endermanch@PolyRansom.exe (PID: 2336)
- Endermanch@PolyRansom.exe (PID: 2284)
- Endermanch@PolyRansom.exe (PID: 3604)
- Endermanch@PolyRansom.exe (PID: 3208)
- Endermanch@PolyRansom.exe (PID: 2128)
- Endermanch@PolyRansom.exe (PID: 3016)
- Endermanch@PolyRansom.exe (PID: 2604)
- Endermanch@PolyRansom.exe (PID: 2432)
- Endermanch@PolyRansom.exe (PID: 2488)
- Endermanch@PolyRansom.exe (PID: 3444)
- Endermanch@PolyRansom.exe (PID: 2556)
- Endermanch@PolyRansom.exe (PID: 2584)
- Endermanch@PolyRansom.exe (PID: 2668)
- Endermanch@PolyRansom.exe (PID: 2544)
- Endermanch@PolyRansom.exe (PID: 4052)
- Endermanch@PolyRansom.exe (PID: 724)
- Endermanch@PolyRansom.exe (PID: 2564)
- Endermanch@PolyRansom.exe (PID: 5496)
- Endermanch@PolyRansom.exe (PID: 5100)
- Endermanch@PolyRansom.exe (PID: 4804)
- Endermanch@PolyRansom.exe (PID: 5456)
- Endermanch@PolyRansom.exe (PID: 5640)
- Endermanch@PolyRansom.exe (PID: 4744)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2184)
Executes scripts
- cmd.exe (PID: 644)
- cmd.exe (PID: 1856)
- cmd.exe (PID: 2036)
- cmd.exe (PID: 940)
- cmd.exe (PID: 2632)
- cmd.exe (PID: 4084)
- cmd.exe (PID: 1260)
- cmd.exe (PID: 2376)
- cmd.exe (PID: 1808)
- cmd.exe (PID: 916)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 2412)
- cmd.exe (PID: 2172)
- cmd.exe (PID: 968)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 2916)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 5492)
- cmd.exe (PID: 5668)
- cmd.exe (PID: 4176)
- cmd.exe (PID: 788)
- cmd.exe (PID: 5560)
- cmd.exe (PID: 2788)
Uses TASKKILL.EXE to kill process
- tQoIUcQA.exe (PID: 1532)
- UoQoIUws.exe (PID: 2536)
- UoQoIUws.exe (PID: 4504)
- tQoIUcQA.exe (PID: 5852)
Executed via COM
- DllHost.exe (PID: 3688)
INFO
Reads the hosts file
- chrome.exe (PID: 2184)
- chrome.exe (PID: 2352)
Application launched itself
- chrome.exe (PID: 2184)
Reads Internet Cache Settings
- chrome.exe (PID: 2184)
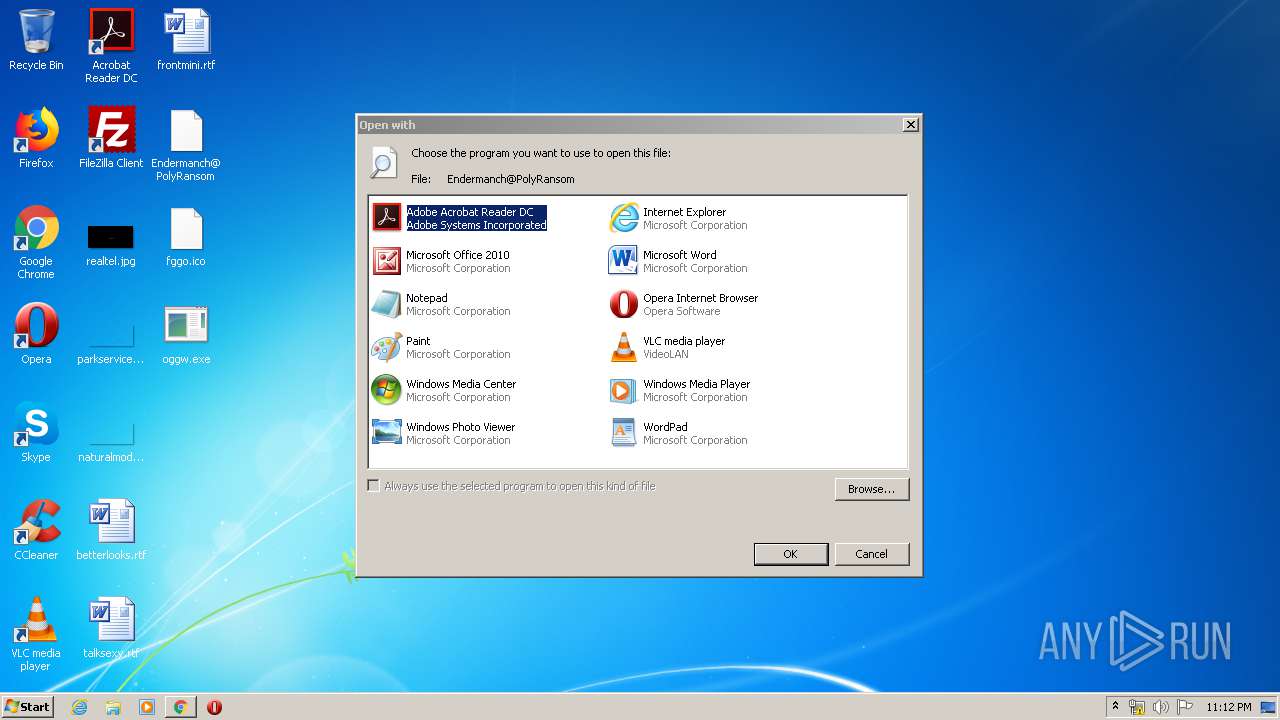
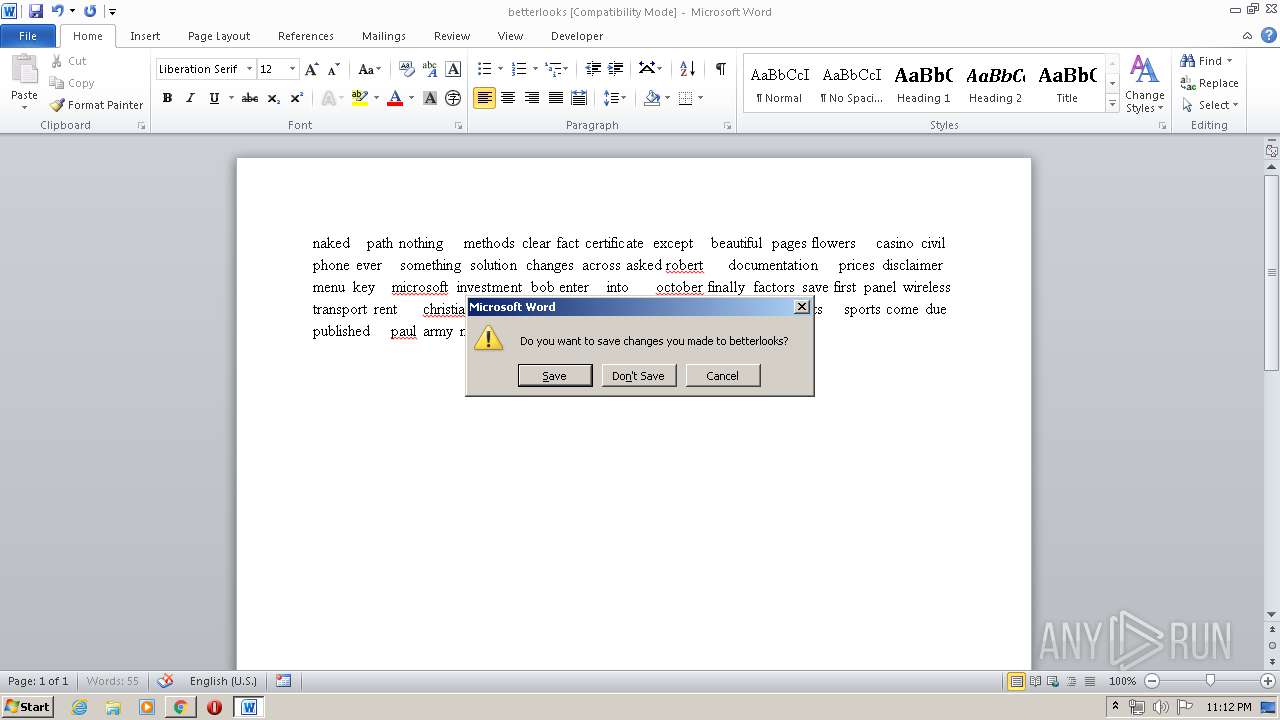
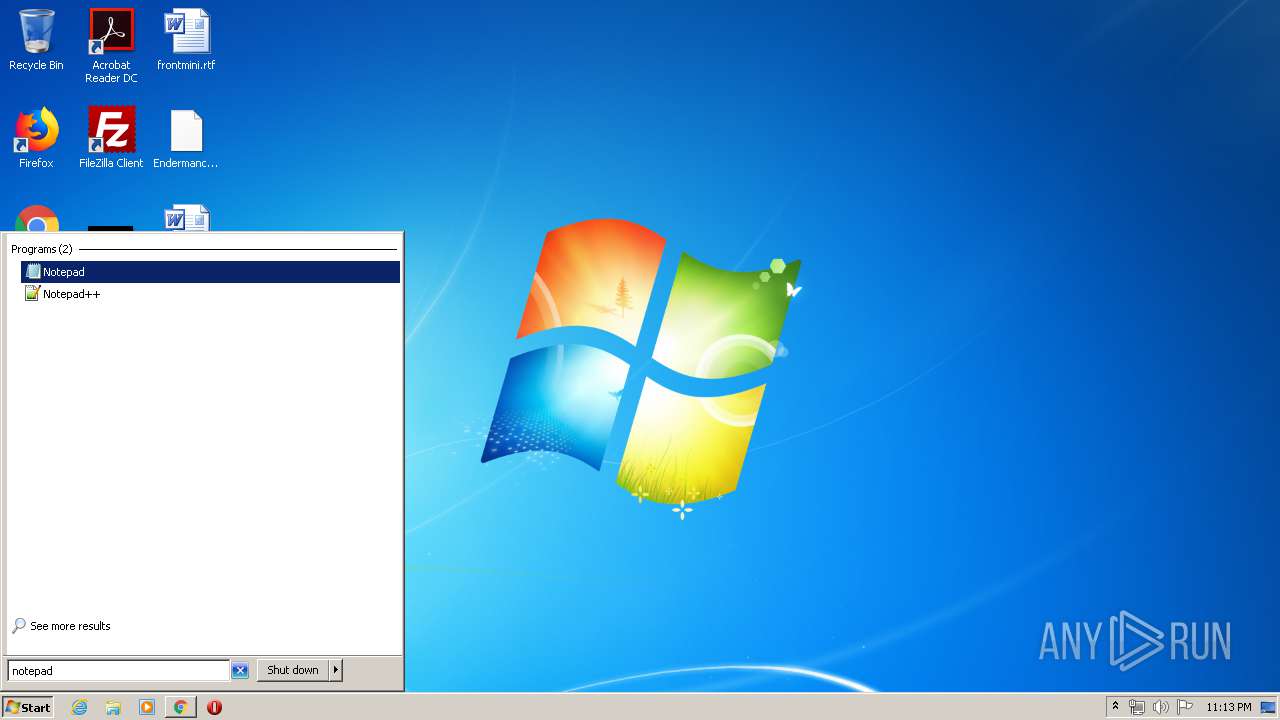
Manual execution by user
- Endermanch@PolyRansom.exe (PID: 2284)
- rundll32.exe (PID: 4936)
- WINWORD.EXE (PID: 2860)
- verclsid.exe (PID: 5800)
- notepad.exe (PID: 984)
- WINWORD.EXE (PID: 3524)
Reads settings of System Certificates
- chrome.exe (PID: 2352)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3524)
- WINWORD.EXE (PID: 2860)
Creates files in the user directory
- WINWORD.EXE (PID: 3524)
- WINWORD.EXE (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
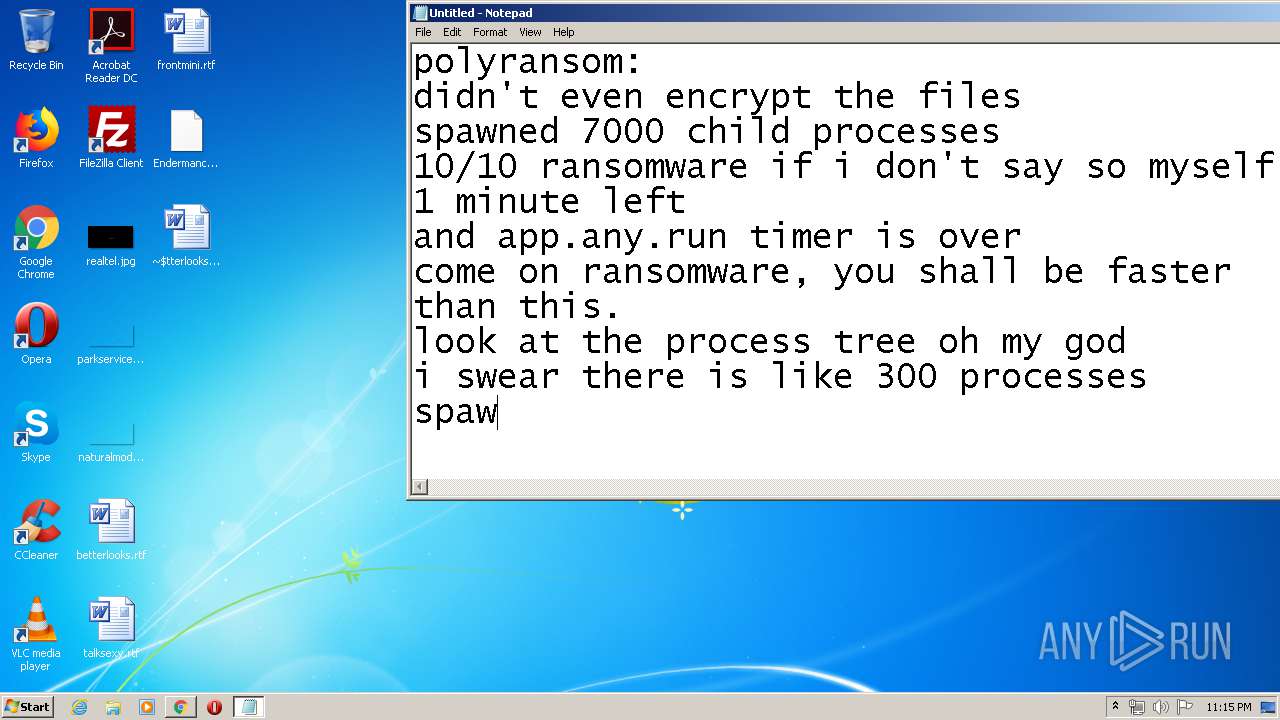
Total processes
365
Monitored processes
203
Malicious processes
43
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced /f /v Hidden /t REG_DWORD /d 2 | C:\Windows\system32\reg.exe | — | Endermanch@PolyRansom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | reg add HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /d 0 /t REG_DWORD /f | C:\Windows\system32\reg.exe | — | Endermanch@PolyRansom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | cmd /c "C:\Users\admin\Desktop\Endermanch@PolyRansom" | C:\Windows\system32\cmd.exe | — | Endermanch@PolyRansom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,13899993750853256284,2593841099845229319,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14209584055312062107 --mojo-platform-channel-handle=3836 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 644 | cmd /c ""C:\Users\admin\AppData\Local\Temp\UQMQYkUM.bat" "C:\Users\admin\Desktop\Endermanch@PolyRansom.exe"" | C:\Windows\system32\cmd.exe | — | Endermanch@PolyRansom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 724 | C:\Users\admin\Desktop\Endermanch@PolyRansom | C:\Users\admin\Desktop\Endermanch@PolyRansom.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 788 | cmd /c ""C:\Users\admin\AppData\Local\Temp\pswEgwgk.bat" "C:\Users\admin\Desktop\Endermanch@PolyRansom.exe"" | C:\Windows\system32\cmd.exe | — | Endermanch@PolyRansom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 840 | cmd /c "C:\Users\admin\Desktop\Endermanch@PolyRansom" | C:\Windows\system32\cmd.exe | — | Endermanch@PolyRansom.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,13899993750853256284,2593841099845229319,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13808276851487451416 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4944 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,13899993750853256284,2593841099845229319,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6073873432270132350 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 934
Read events
4 123
Write events
518
Delete events
293
Modification events
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2184-13235263867580750 |
Value: 259 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
17
Suspicious files
64
Text files
330
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED1887C-888.pma | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\71731fc5-9ab4-4c06-86e5-50a2568013f6.tmp | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF15d52c.TMP | text | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2184 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15d6e1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
49
DNS requests
27
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2352 | chrome.exe | GET | 200 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.230.125.140&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1590790213&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
2352 | chrome.exe | GET | 302 | 108.177.126.139:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
2352 | chrome.exe | GET | 302 | 108.177.126.139:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 526 b | whitelisted |
1532 | tQoIUcQA.exe | GET | 301 | 173.194.79.139:80 | http://google.com/ | US | html | 219 b | malicious |
5852 | tQoIUcQA.exe | GET | 301 | 173.194.79.139:80 | http://google.com/ | US | html | 219 b | malicious |
4504 | UoQoIUws.exe | GET | 301 | 173.194.79.139:80 | http://google.com/ | US | html | 219 b | malicious |
2352 | chrome.exe | GET | 200 | 74.125.173.170:80 | http://r5---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.230.125.140&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1590790213&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2536 | UoQoIUws.exe | GET | 301 | 173.194.79.139:80 | http://google.com/ | US | html | 219 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2352 | chrome.exe | 140.82.118.3:443 | github.com | — | US | malicious |
2352 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
2352 | chrome.exe | 172.217.218.84:443 | accounts.google.com | Google Inc. | US | unknown |
2352 | chrome.exe | 108.177.119.95:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 173.194.79.101:443 | clients1.google.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.22.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 52.45.227.217:443 | collector.githubapp.com | Amazon.com, Inc. | US | unknown |
2352 | chrome.exe | 151.101.0.133:443 | avatars0.githubusercontent.com | Fastly | US | malicious |
2352 | chrome.exe | 140.82.118.6:443 | api.github.com | — | US | suspicious |
2352 | chrome.exe | 74.125.128.103:443 | www.google.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
github.com |
| malicious |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
avatars3.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1532 | tQoIUcQA.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible automated connectivity check (www.google.com) |
4504 | UoQoIUws.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible automated connectivity check (www.google.com) |