| File name: | setup.exe.zip |
| Full analysis: | https://app.any.run/tasks/9431f060-13b6-4c6a-ae16-5c716cb0918f |
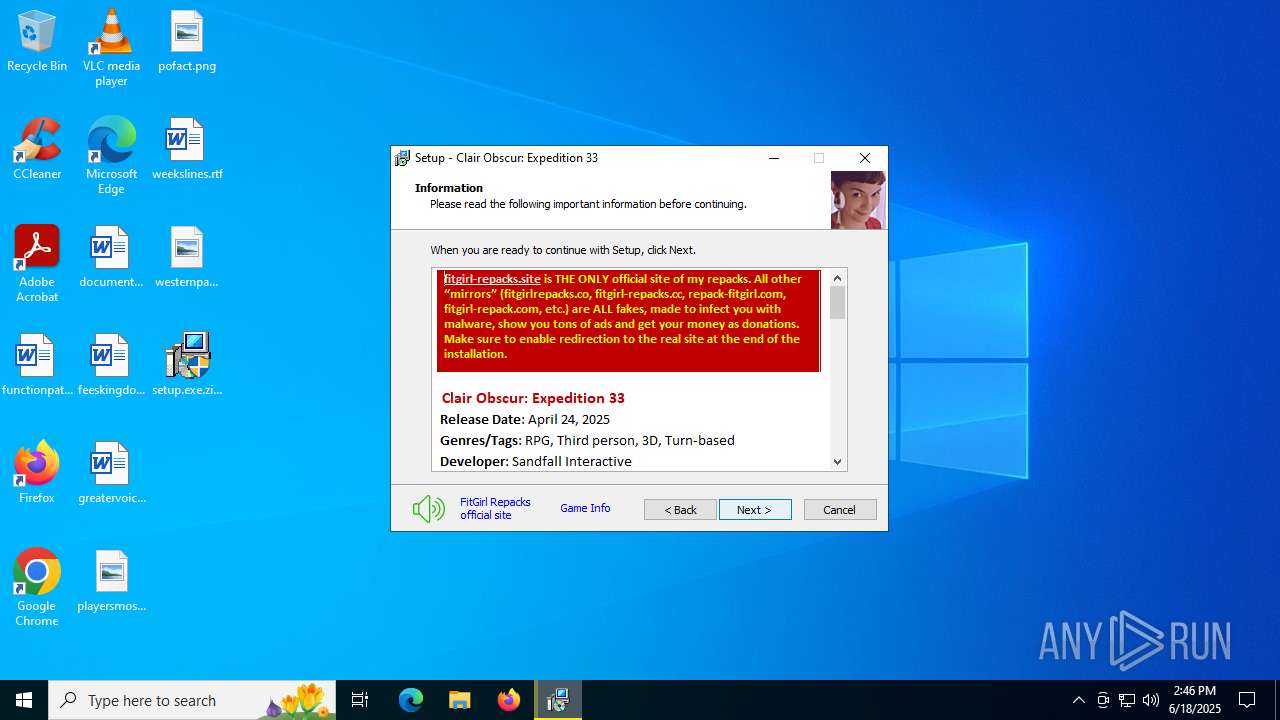
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2025, 14:45:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 042205F12F685B120400F836526593C8 |
| SHA1: | 450AC41561F2CE5648B7F4315C6A205E60328C2E |
| SHA256: | 04BF2EFCCCD537F40F69F827E598CC2536A992DB0496575AB4222980FB73AB68 |
| SSDEEP: | 98304:9Z/SMPUQ+/uMLYOCFpAOLX46e/h//oShmxel+YxjyqcQmJQoUa2X8zJneB+peJNO:VRgmfFbOQ |
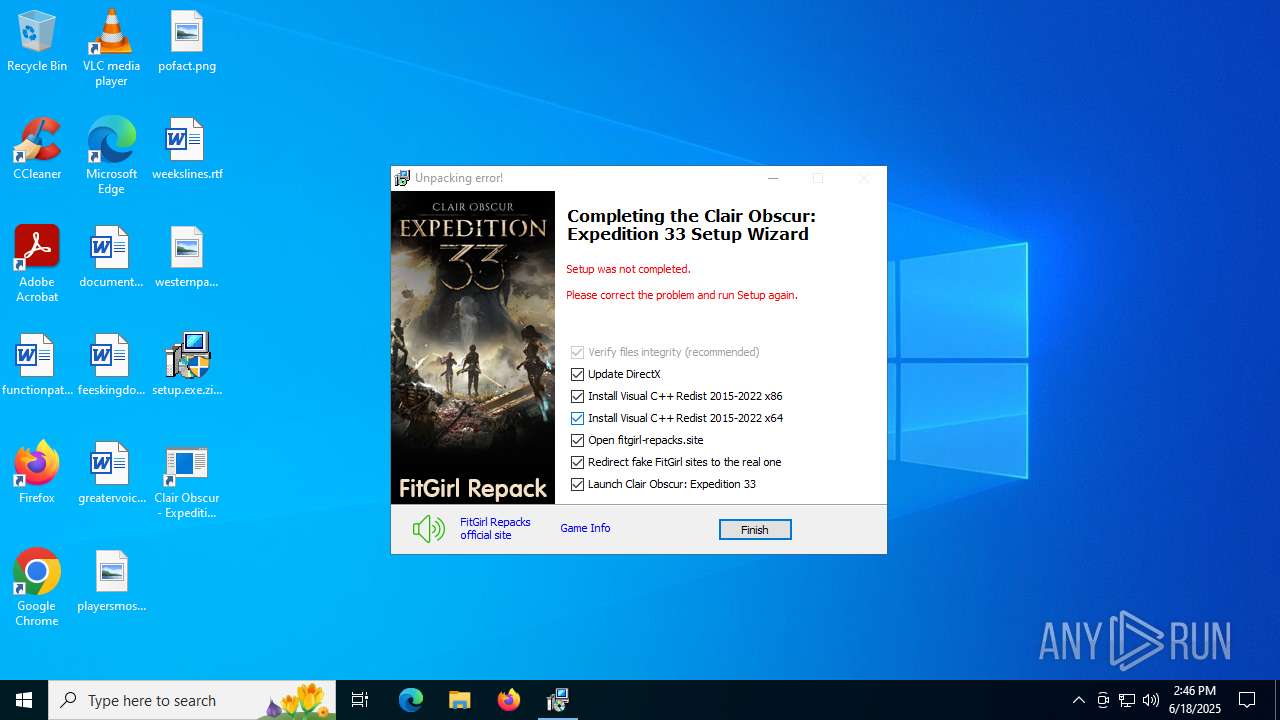
MALICIOUS
No malicious indicators.SUSPICIOUS
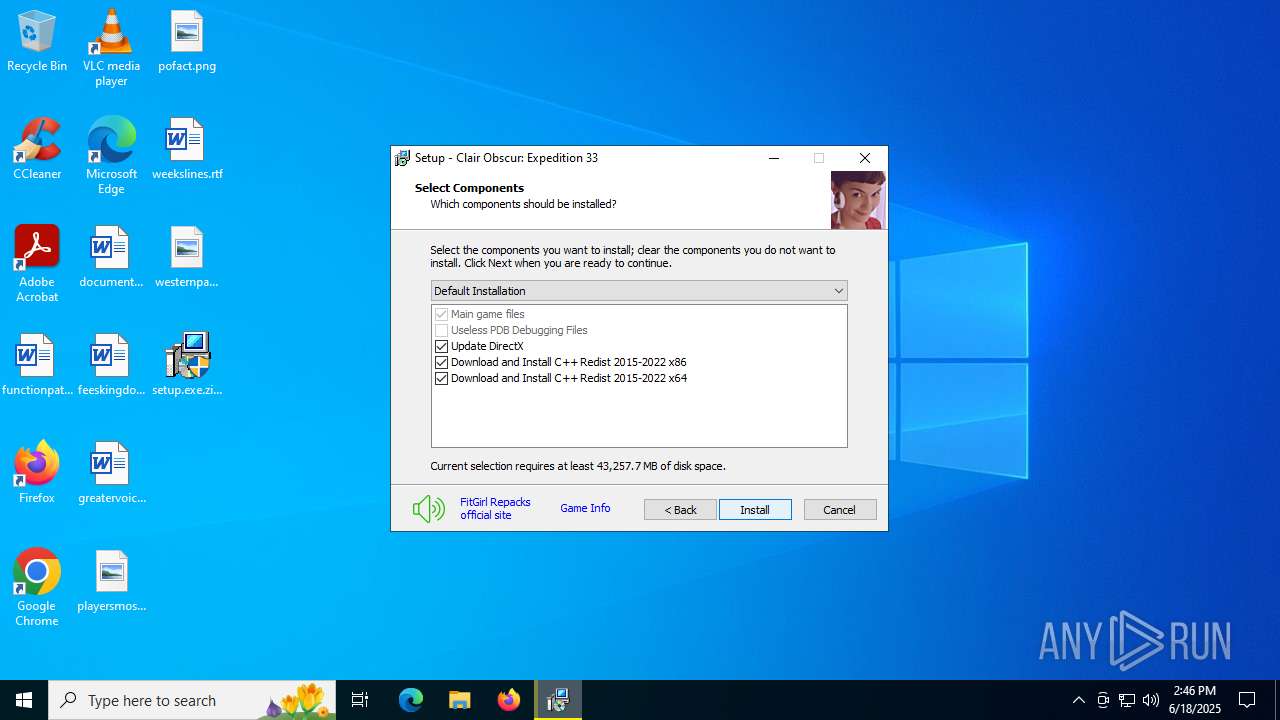
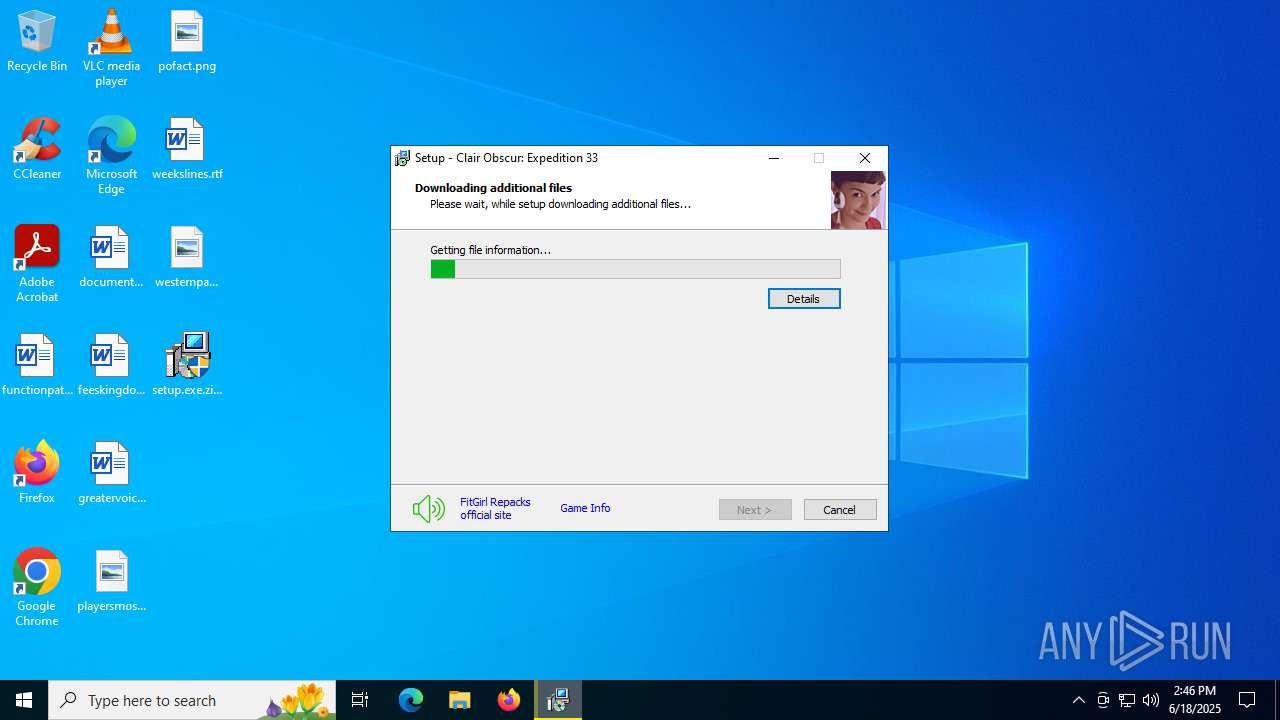
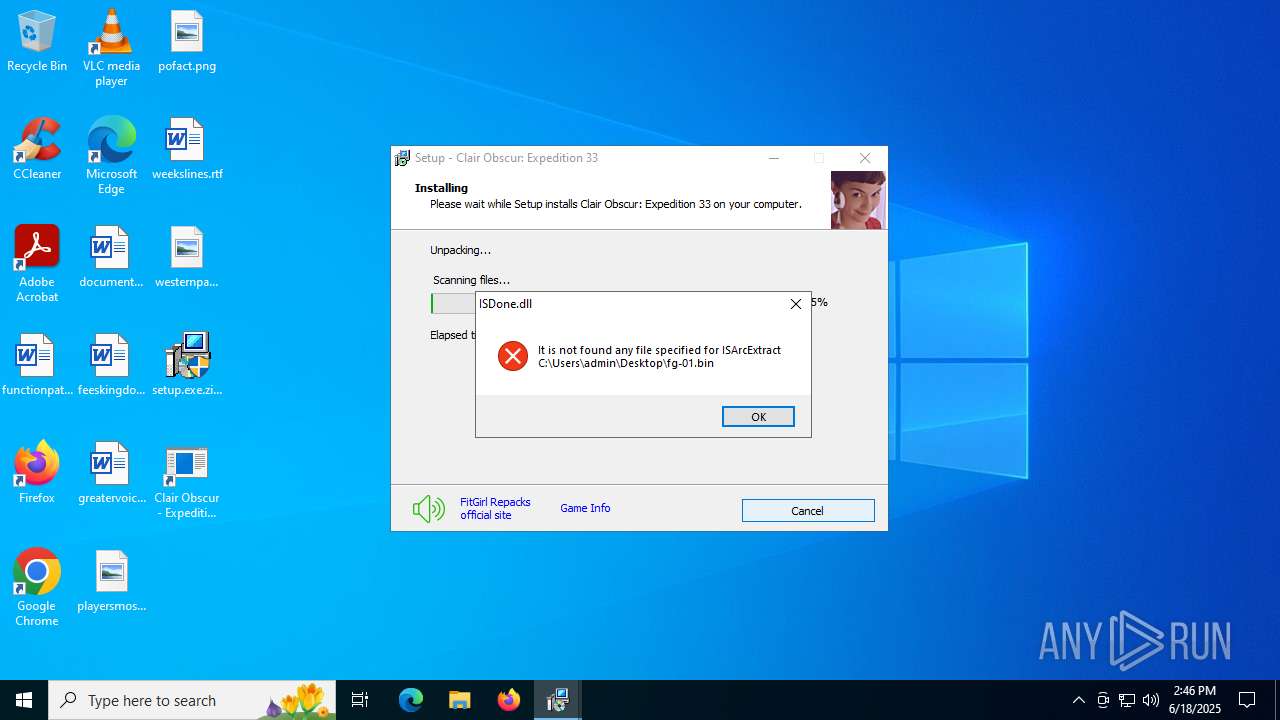
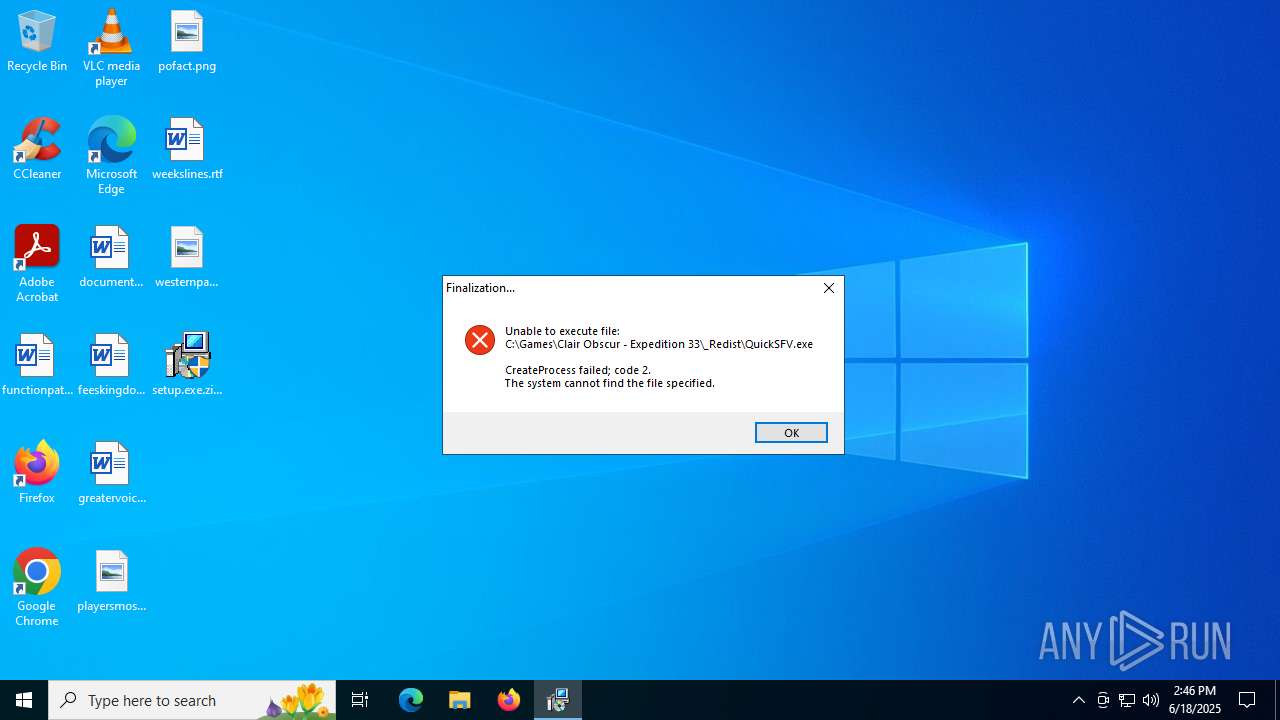
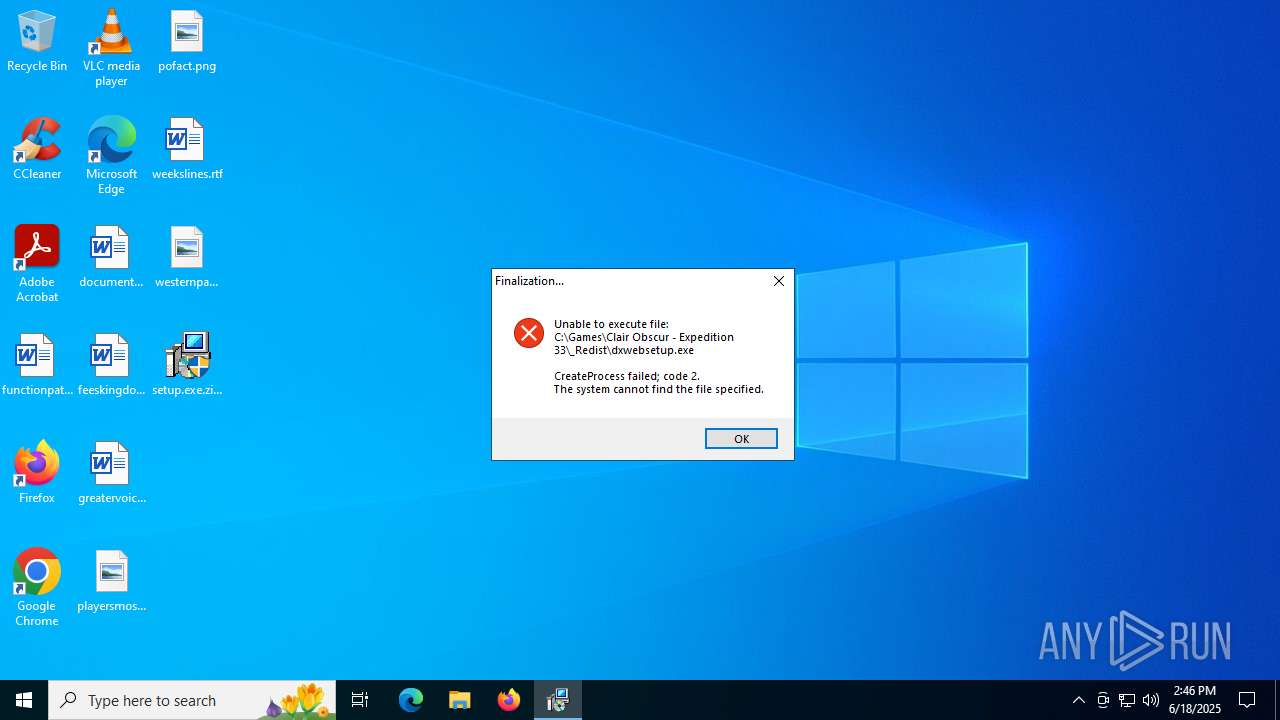
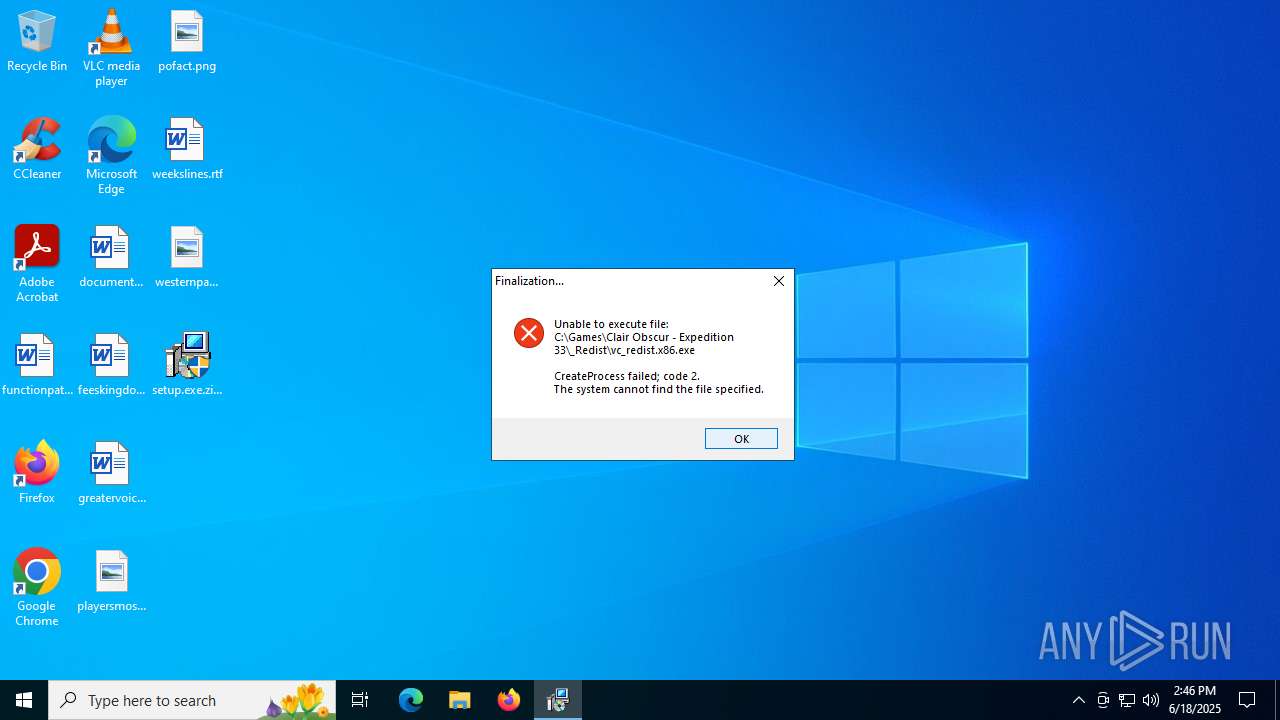
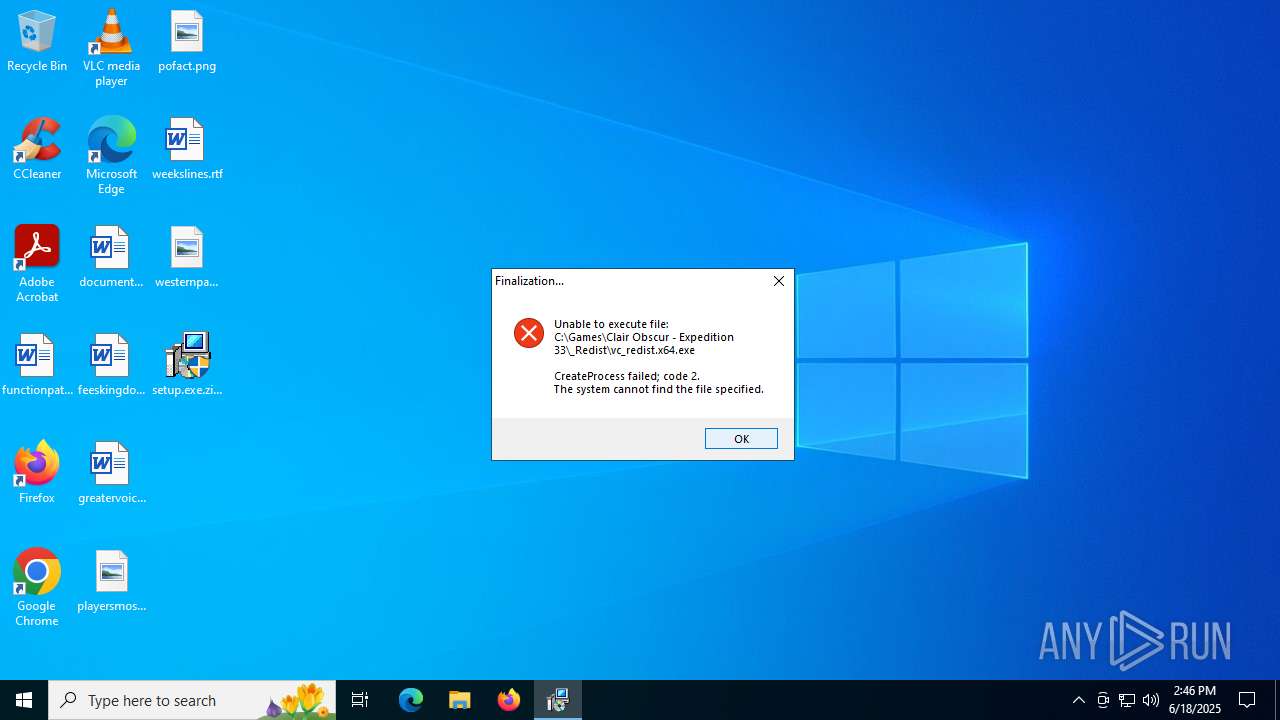
Executable content was dropped or overwritten
- setup.exe.zip.exe (PID: 5772)
- setup.exe.zip.tmp (PID: 4880)
- unins000.exe (PID: 3964)
- _iu14D2N.tmp (PID: 4708)
Process drops legitimate windows executable
- setup.exe.zip.tmp (PID: 4880)
- _iu14D2N.tmp (PID: 4708)
Reads the Windows owner or organization settings
- setup.exe.zip.tmp (PID: 4880)
- _iu14D2N.tmp (PID: 4708)
There is functionality for taking screenshot (YARA)
- setup.exe.zip.tmp (PID: 4880)
Starts application with an unusual extension
- unins000.exe (PID: 3964)
Starts itself from another location
- unins000.exe (PID: 3964)
Detected use of alternative data streams (AltDS)
- _iu14D2N.tmp (PID: 4708)
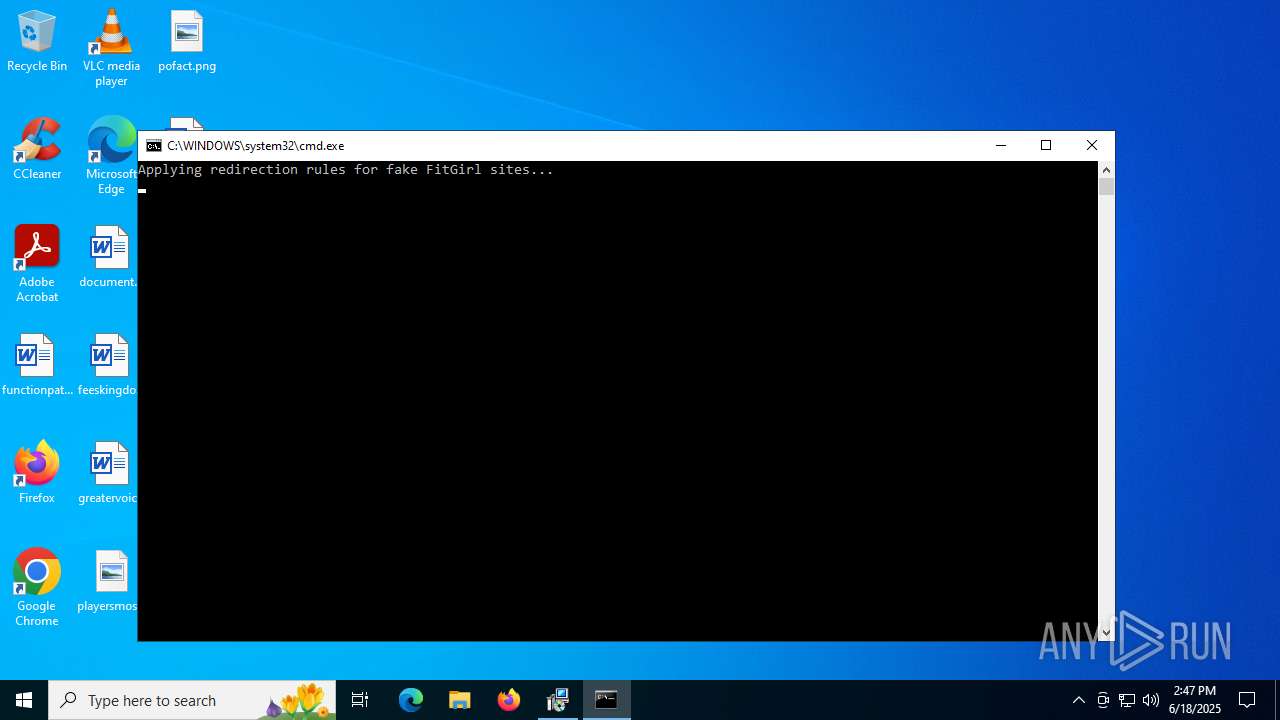
Executing commands from ".cmd" file
- setup.exe.zip.tmp (PID: 4880)
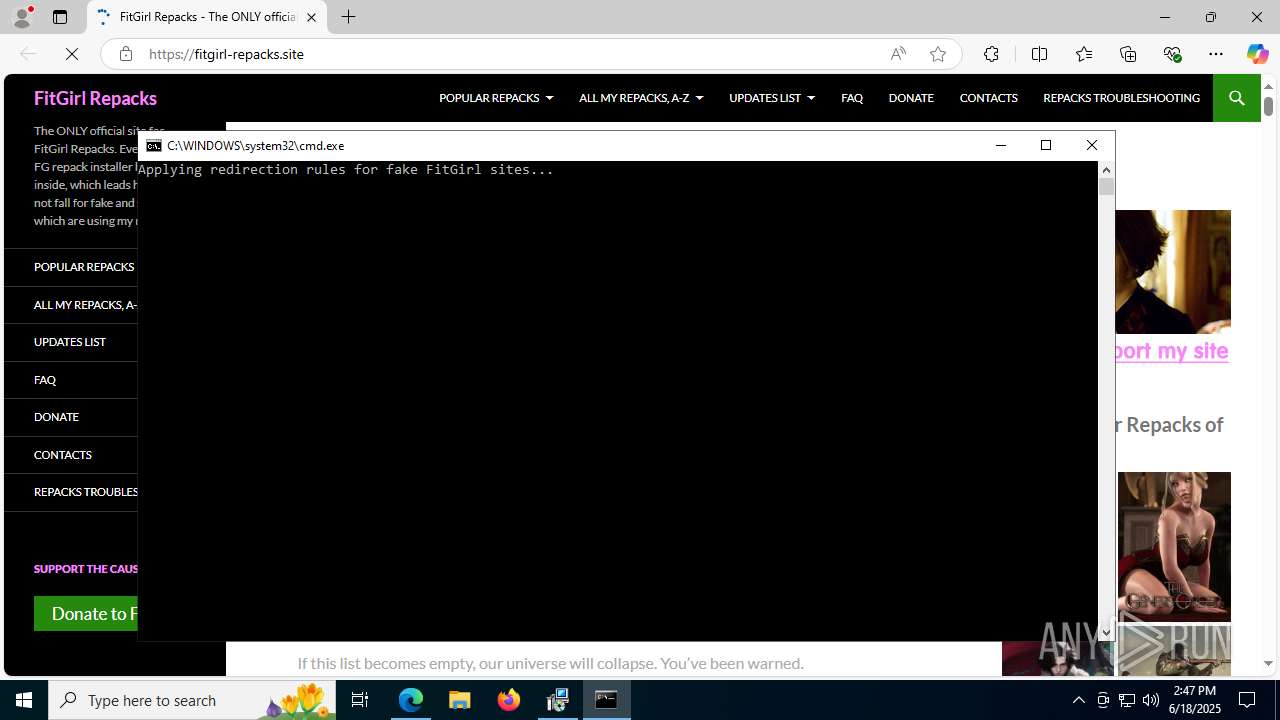
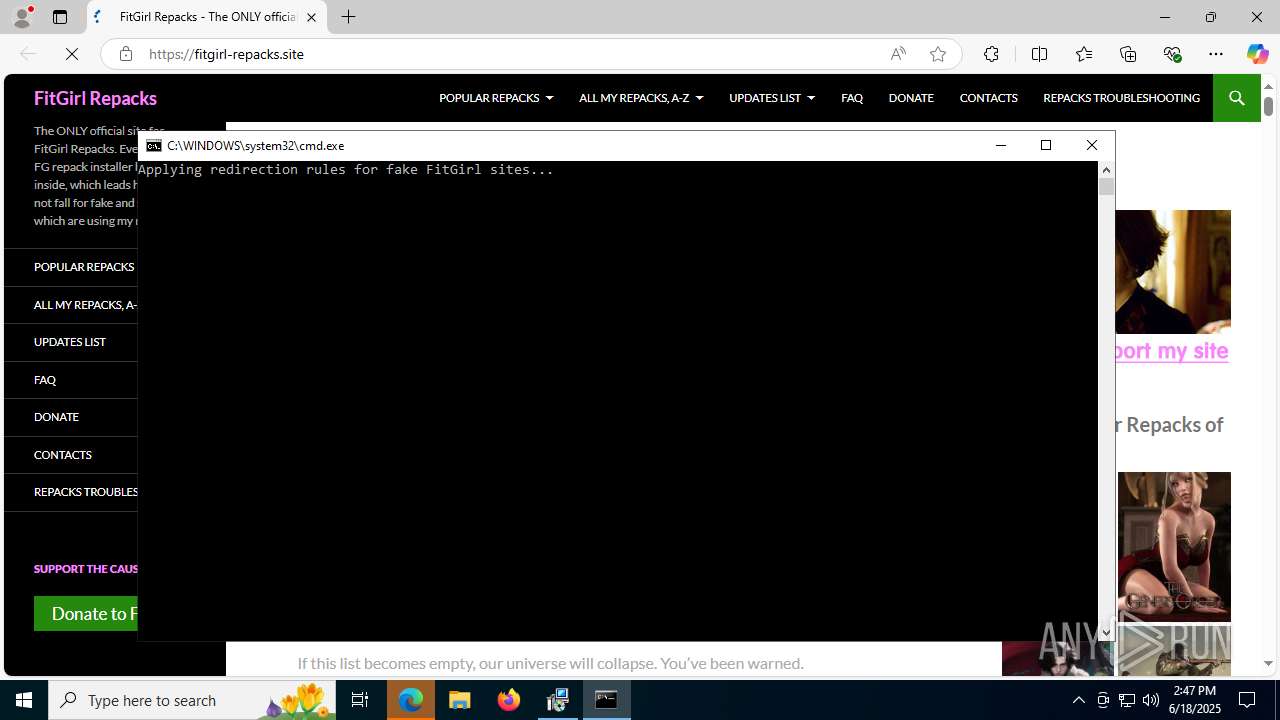
Starts CMD.EXE for commands execution
- setup.exe.zip.tmp (PID: 4880)
Reads security settings of Internet Explorer
- setup.exe.zip.tmp (PID: 4880)
The executable file from the user directory is run by the CMD process
- hosts.exe (PID: 5720)
Modifies hosts file to alter network resolution
- hosts.exe (PID: 5720)
Creates files in the driver directory
- hosts.exe (PID: 5720)
INFO
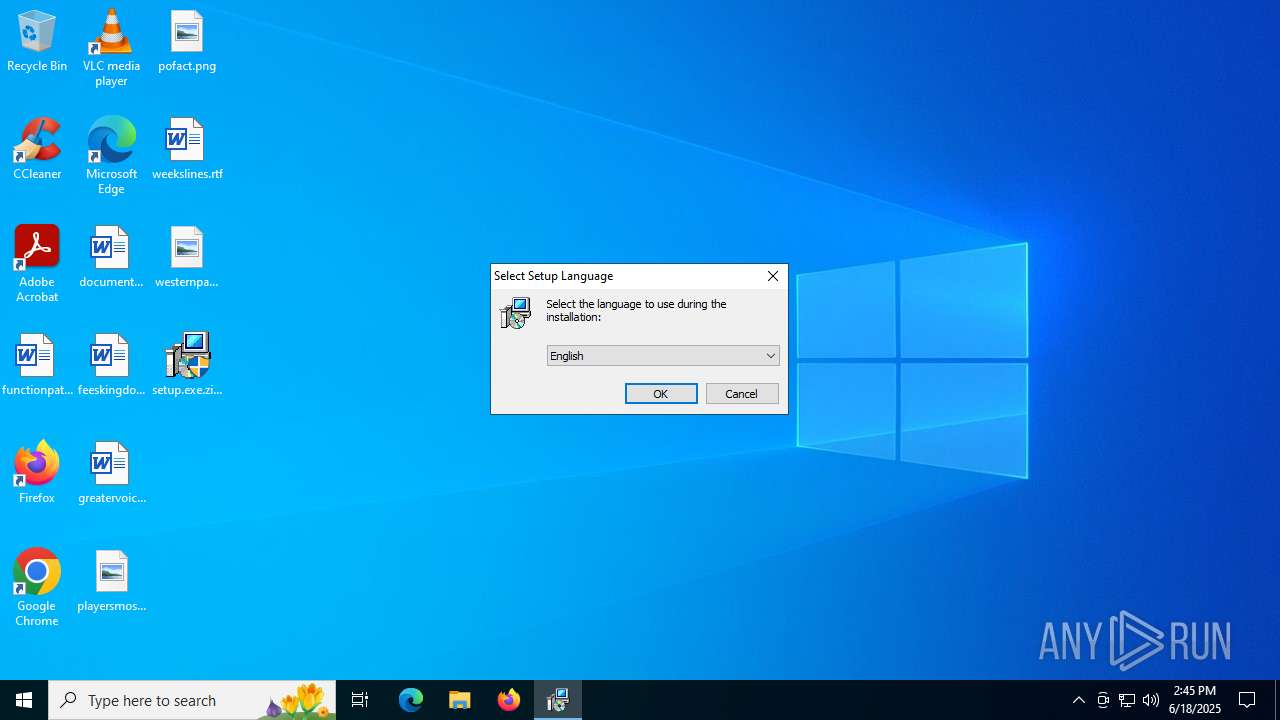
Checks supported languages
- setup.exe.zip.exe (PID: 5772)
- setup.exe.zip.tmp (PID: 4880)
- unins000.exe (PID: 3964)
- _iu14D2N.tmp (PID: 4708)
- hosts.exe (PID: 5720)
Reads the computer name
- setup.exe.zip.tmp (PID: 4880)
- _iu14D2N.tmp (PID: 4708)
Create files in a temporary directory
- setup.exe.zip.exe (PID: 5772)
- setup.exe.zip.tmp (PID: 4880)
- unins000.exe (PID: 3964)
- _iu14D2N.tmp (PID: 4708)
The sample compiled with english language support
- setup.exe.zip.tmp (PID: 4880)
- _iu14D2N.tmp (PID: 4708)
The sample compiled with russian language support
- setup.exe.zip.tmp (PID: 4880)
Detects InnoSetup installer (YARA)
- setup.exe.zip.exe (PID: 5772)
- setup.exe.zip.tmp (PID: 4880)
Compiled with Borland Delphi (YARA)
- setup.exe.zip.tmp (PID: 4880)
- setup.exe.zip.exe (PID: 5772)
The sample compiled with chinese language support
- setup.exe.zip.tmp (PID: 4880)
Reads the machine GUID from the registry
- setup.exe.zip.tmp (PID: 4880)
- hosts.exe (PID: 5720)
Checks proxy server information
- setup.exe.zip.tmp (PID: 4880)
- slui.exe (PID: 432)
Creates files or folders in the user directory
- setup.exe.zip.tmp (PID: 4880)
Creates a software uninstall entry
- setup.exe.zip.tmp (PID: 4880)
Process checks computer location settings
- _iu14D2N.tmp (PID: 4708)
Reads the software policy settings
- setup.exe.zip.tmp (PID: 4880)
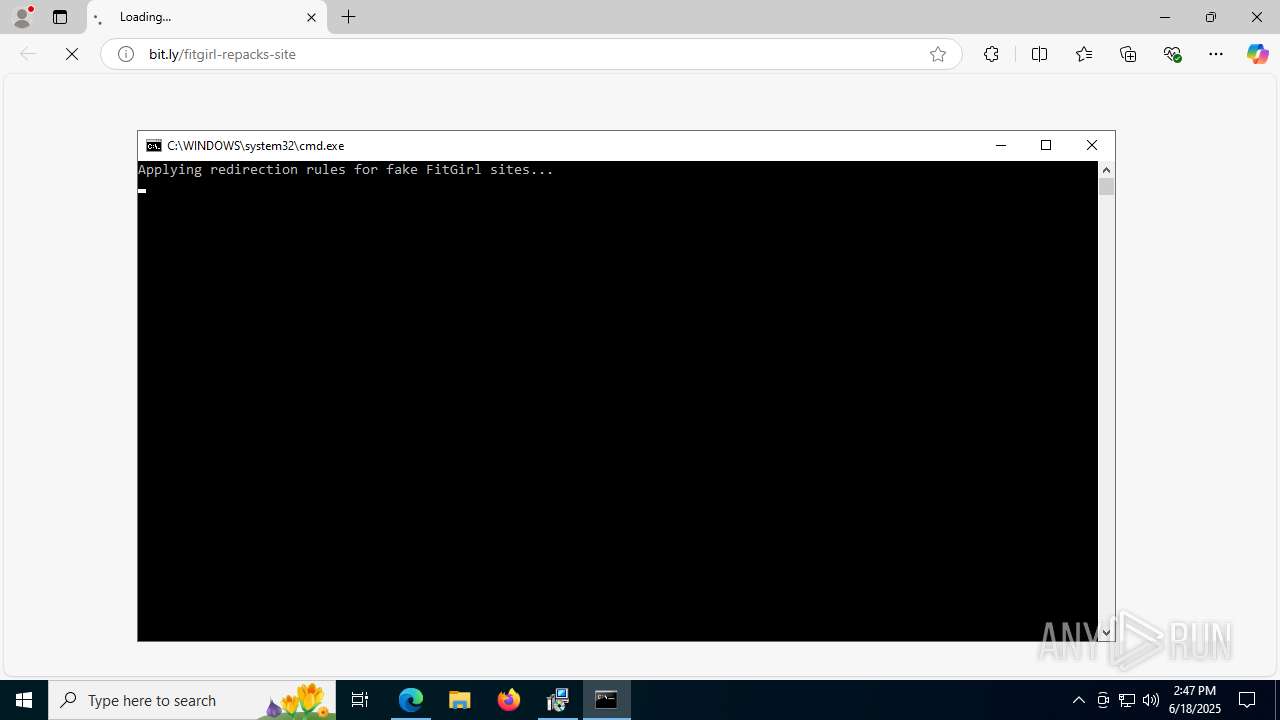
Application launched itself
- msedge.exe (PID: 6264)
- msedge.exe (PID: 2292)
- msedge.exe (PID: 4312)
- msedge.exe (PID: 3108)
Manual execution by a user
- msedge.exe (PID: 6264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 05:04:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
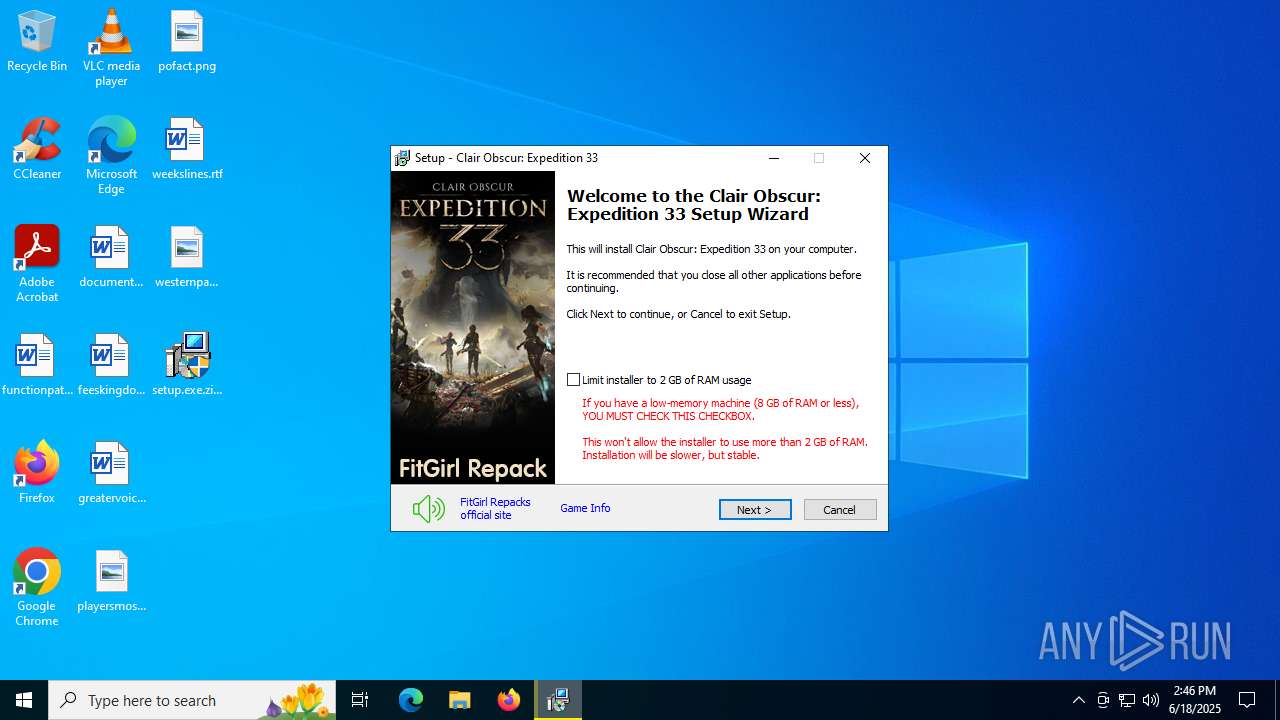
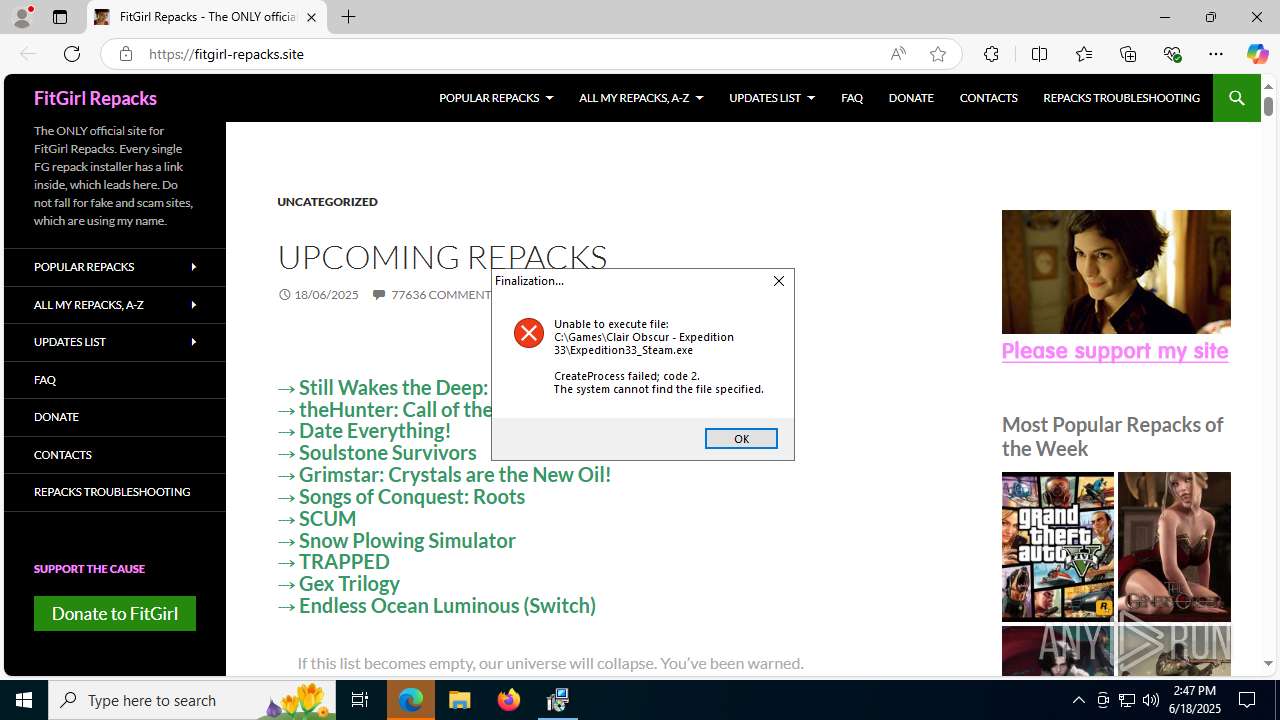
| FileDescription: | Clair Obscur: Expedition 33 Setup |
| FileVersion: | |
| LegalCopyright: | FitGirl |
| ProductName: | Clair Obscur: Expedition 33 |
| ProductVersion: |
Total processes
177
Monitored processes
40
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | "cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\host.cmd" | C:\Windows\SysWOW64\cmd.exe | — | setup.exe.zip.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 504 | "C:\Users\admin\Desktop\setup.exe.zip.exe" | C:\Users\admin\Desktop\setup.exe.zip.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Clair Obscur: Expedition 33 Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | FlushFileCache.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3632,i,3066140968636780335,14205680700567796166,262144 --variations-seed-version --mojo-platform-channel-handle=3696 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3600,i,3066140968636780335,14205680700567796166,262144 --variations-seed-version --mojo-platform-channel-handle=3620 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5740,i,3066140968636780335,14205680700567796166,262144 --variations-seed-version --mojo-platform-channel-handle=6184 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1576 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffc4544f208,0x7ffc4544f214,0x7ffc4544f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2332,i,6382218697620348696,15791964634223154260,262144 --variations-seed-version --mojo-platform-channel-handle=2284 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2736,i,6382218697620348696,15791964634223154260,262144 --variations-seed-version --mojo-platform-channel-handle=2628 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
8 524
Read events
8 460
Write events
59
Delete events
5
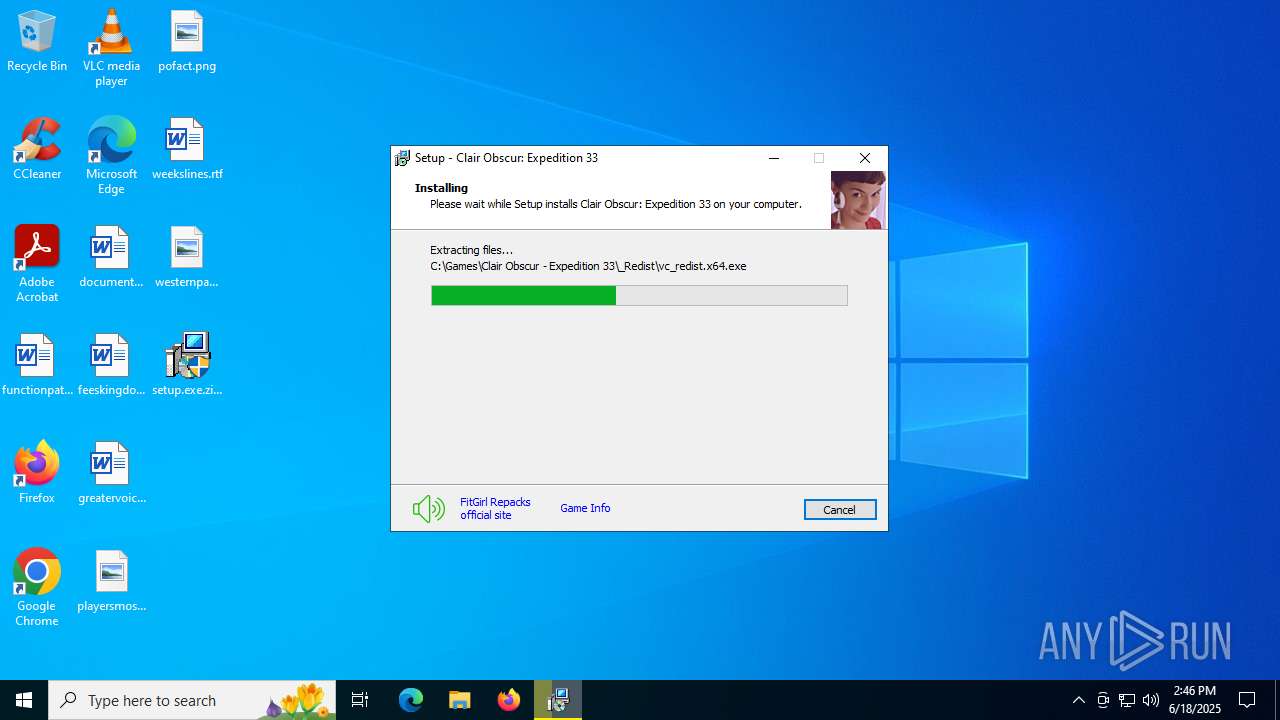
Modification events
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
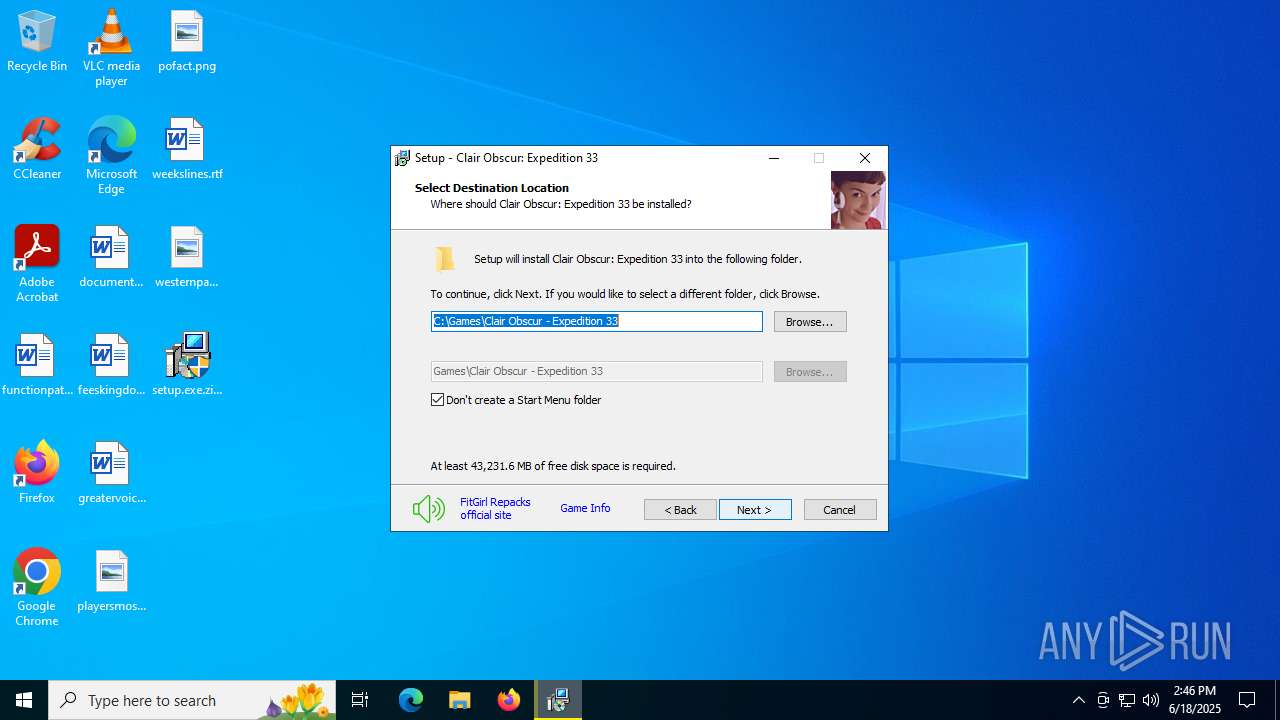
| Operation: | write | Name: | C:\Games\Clair Obscur - Expedition 33\Expedition33_Steam.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Games\Clair Obscur - Expedition 33\Expedition33_Steam.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Clair Obscur: Expedition 33_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1.ee2 (u) | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Clair Obscur: Expedition 33_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Games\Clair Obscur - Expedition 33 | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Clair Obscur: Expedition 33_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Games\Clair Obscur - Expedition 33\ | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Clair Obscur: Expedition 33_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Games\Clair Obscur - Expedition 33 | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Clair Obscur: Expedition 33_is1 |
| Operation: | write | Name: | Inno Setup: No Icons |
Value: 1 | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Clair Obscur: Expedition 33_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (4880) setup.exe.zip.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Clair Obscur: Expedition 33_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: custom | |||
Executable files
49
Suspicious files
125
Text files
163
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5772 | setup.exe.zip.exe | C:\Users\admin\AppData\Local\Temp\is-O9PM4.tmp\setup.exe.zip.tmp | executable | |
MD5:AE9890548F2FCAB56A4E9AE446F55B3F | SHA256:09AF8004B85478E1ECA09FA4CB5E3081DDDCB2F68A353F3EF6849D92BE47B449 | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\ISDone.dll | executable | |
MD5:63DC27B7BC65243EFAA59A9797A140BA | SHA256:C652B4B564B3C85C399155CBB45C6FB5A9F56F074E566BFD20F01DA6E0412C74 | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\idp.dll | executable | |
MD5:AF555AC9C073F88FE5BF0D677F085025 | SHA256:F4FC0187491A9CB89E233197FF72C2405B5EC02E8B8EA640EE68D034DDBC44BB | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\innocallback.dll | executable | |
MD5:1C55AE5EF9980E3B1028447DA6105C75 | SHA256:6AFA2D104BE6EFE3D9A2AB96DBB75DB31565DAD64DD0B791E402ECC25529809F | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\wintb.dll | executable | |
MD5:9436DF49E08C83BAD8DDC906478C2041 | SHA256:1910537AA95684142250CA0C7426A0B5F082E39F6FBDBDBA649AECB179541435 | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\BASS.dll | executable | |
MD5:8005750EC63EB5292884AD6183AE2E77 | SHA256:DF9F56C4DA160101567B0526845228EE481EE7D2F98391696FA27FE41F8ACF15 | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\cls-lollypop_x64.exe | executable | |
MD5:5B848A24126F54A2C3C7B7393B536D33 | SHA256:2D32C4F4522BC62F63C7949313434F6CA0EAA6B65B44EE5AA8B6B877988B1AA8 | |||
| 4880 | setup.exe.zip.tmp | C:\Users\admin\AppData\Local\Temp\is-HL5DR.tmp\cls-srep_x64.exe | executable | |
MD5:6AE2ADD85EC2B642D865FFAAA391D5BB | SHA256:ED8A485B9984997306EA6B5C6D98B5026A5B7903C1DF4C229BF93BF113C78EE9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
154
DNS requests
138
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1948 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1948 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4168 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4880 | setup.exe.zip.tmp | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
4880 | setup.exe.zip.tmp | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5172 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:dKh_FA2voj4uO3AIVwaJEqAdjE3Ajgv5zc9Pd4qWnxE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5172 | msedge.exe | GET | 301 | 190.115.31.179:80 | http://fitgirl-repacks.site/wp-content/uploads/2016/08/cropped-icon-192x192.jpg | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3572 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1948 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
aka.ms |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5172 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (bit .ly) |
5172 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (bit .ly) |
5172 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (bit .ly) |
5172 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (bit .ly) |