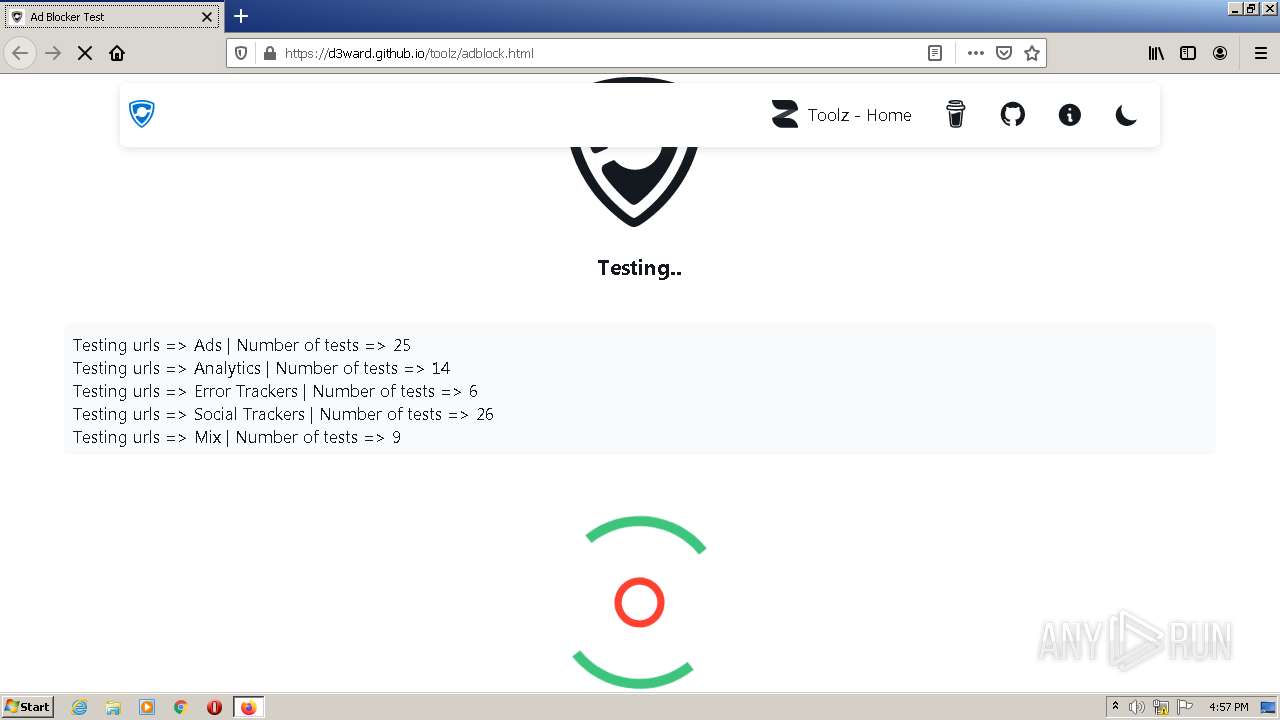
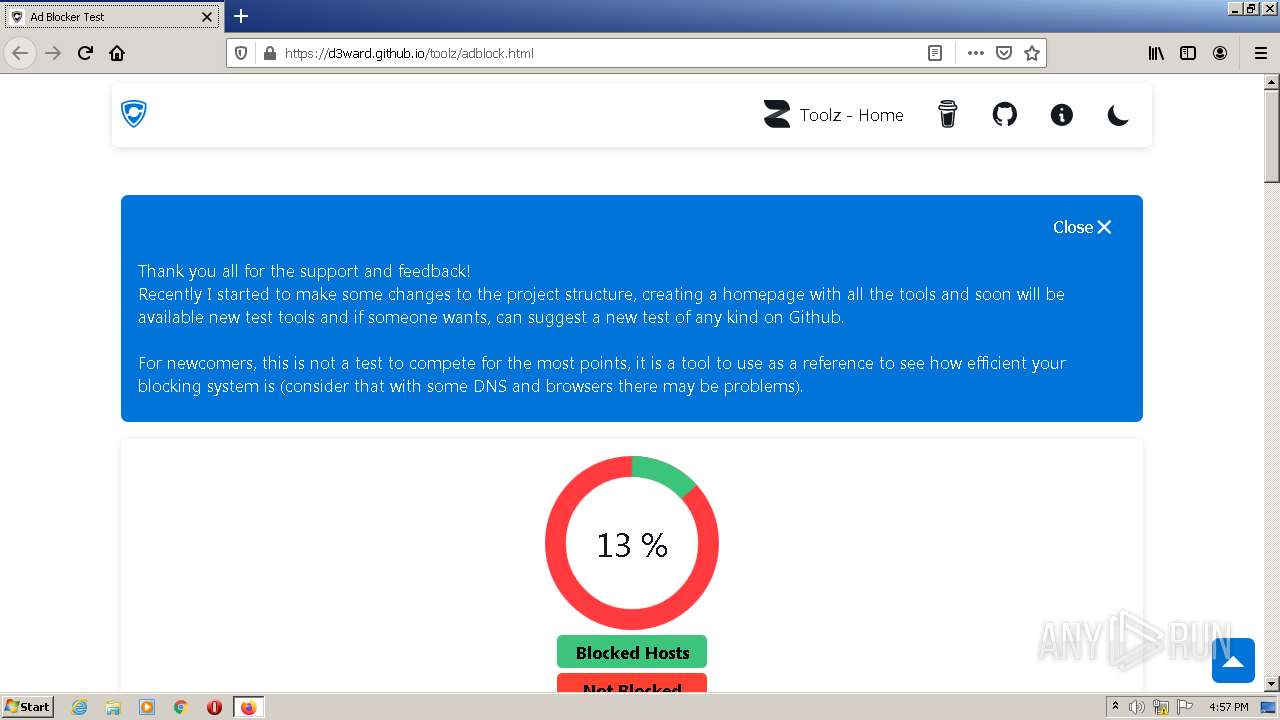
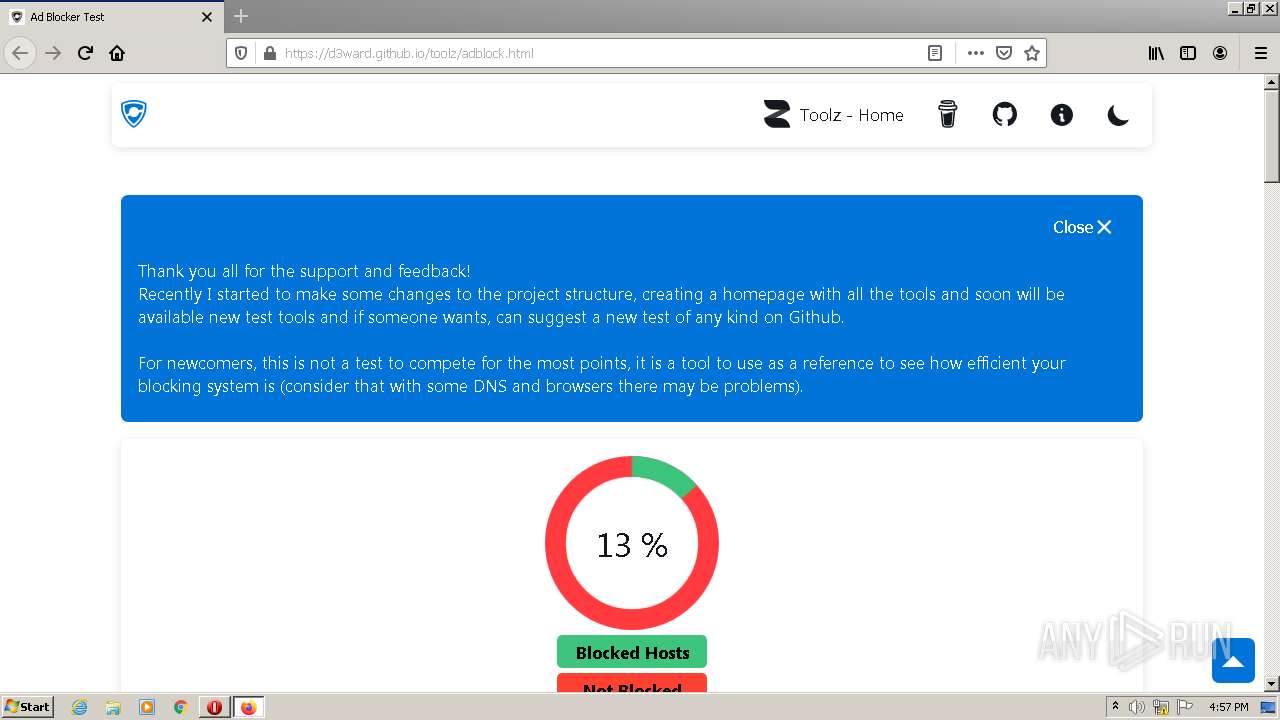
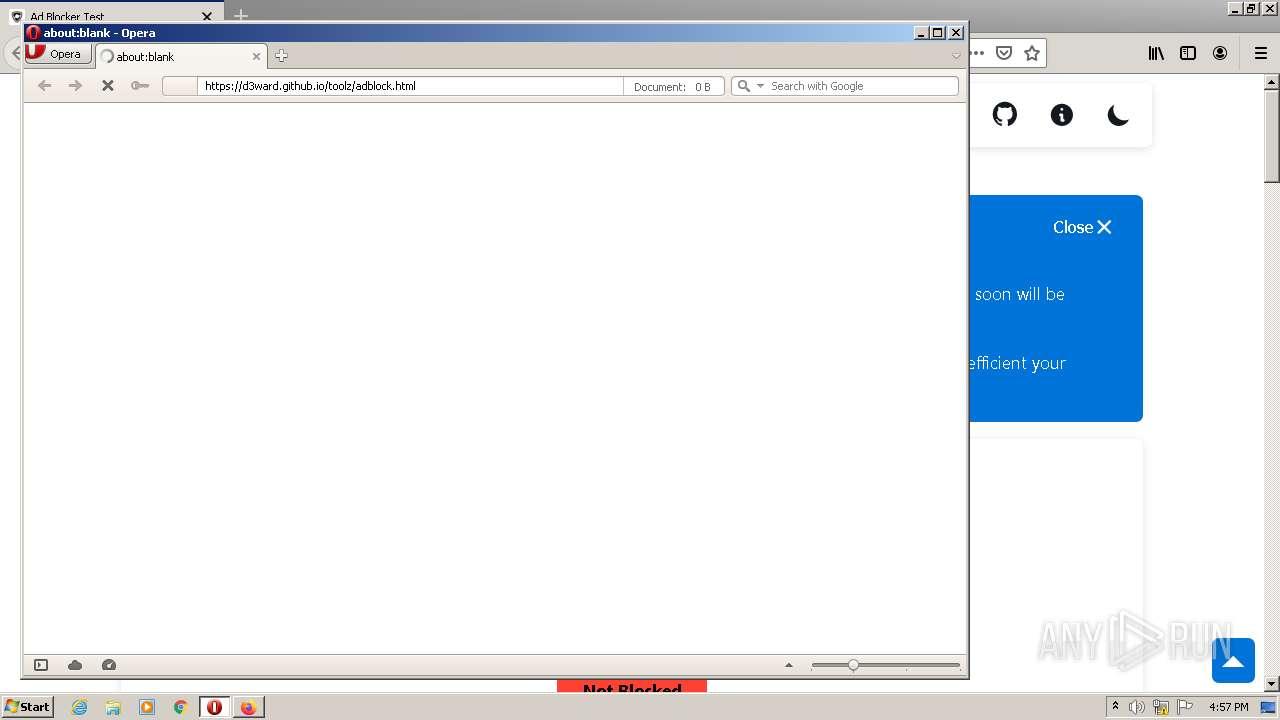
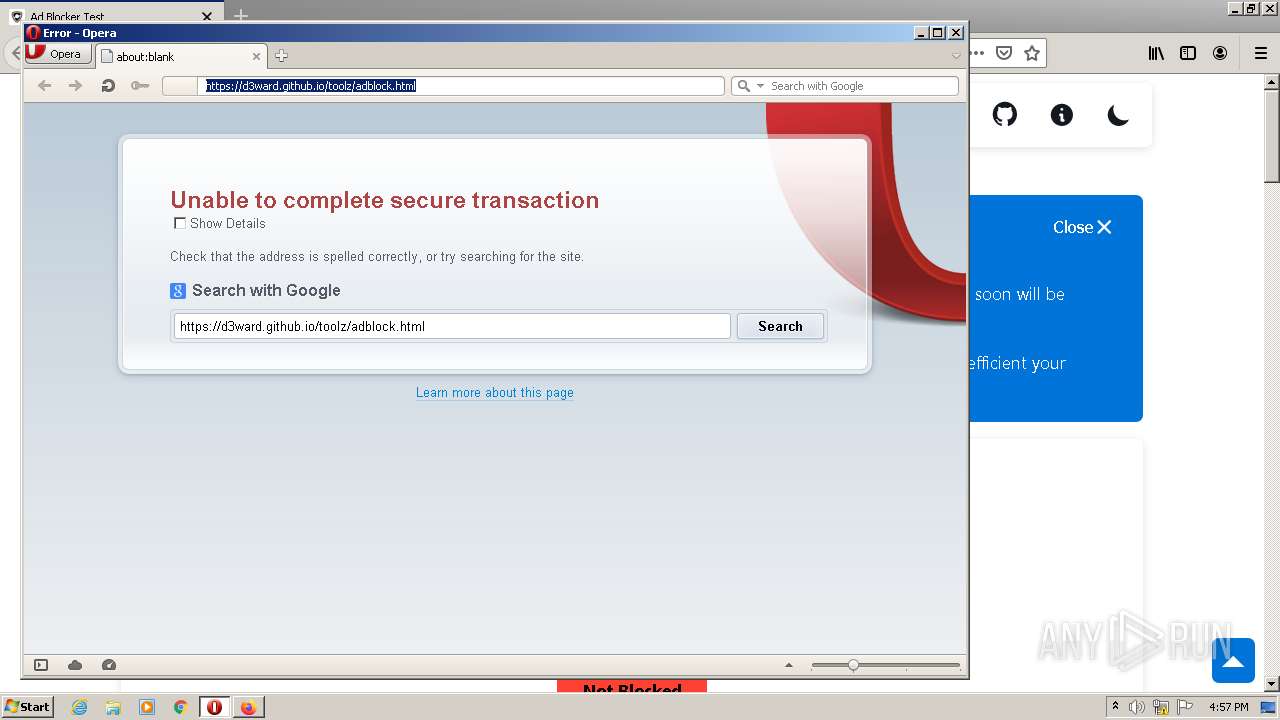
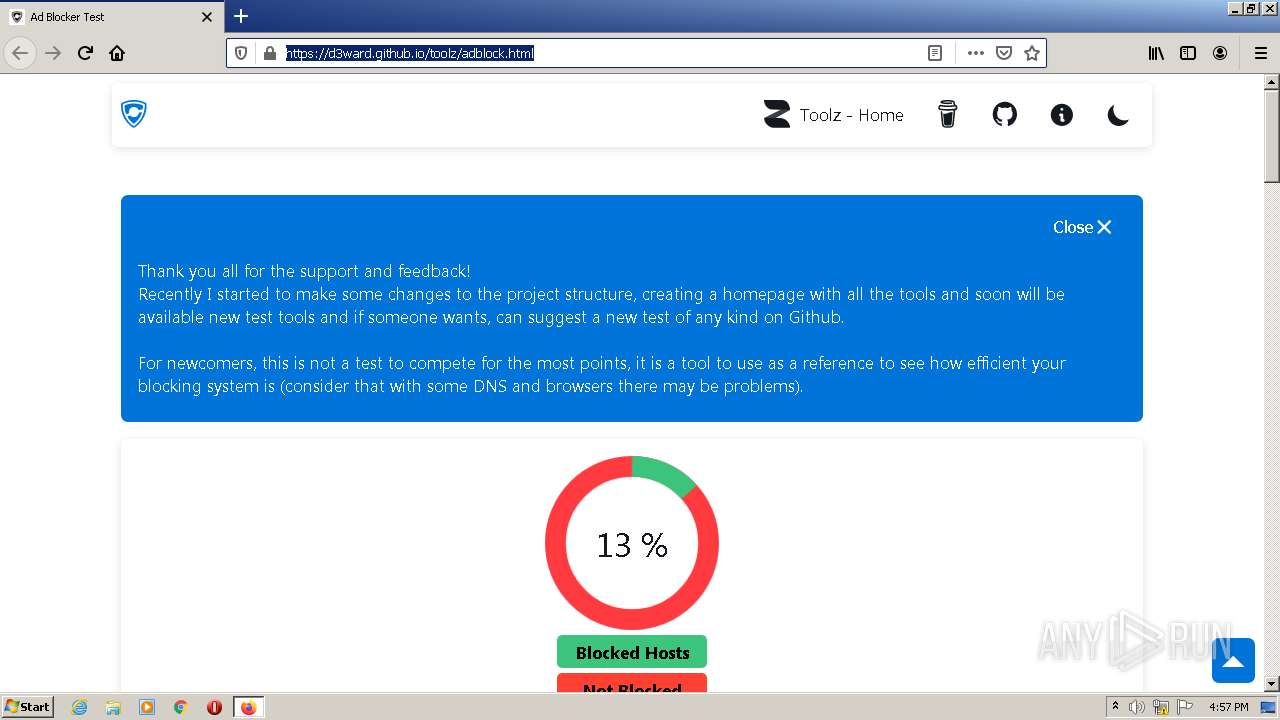
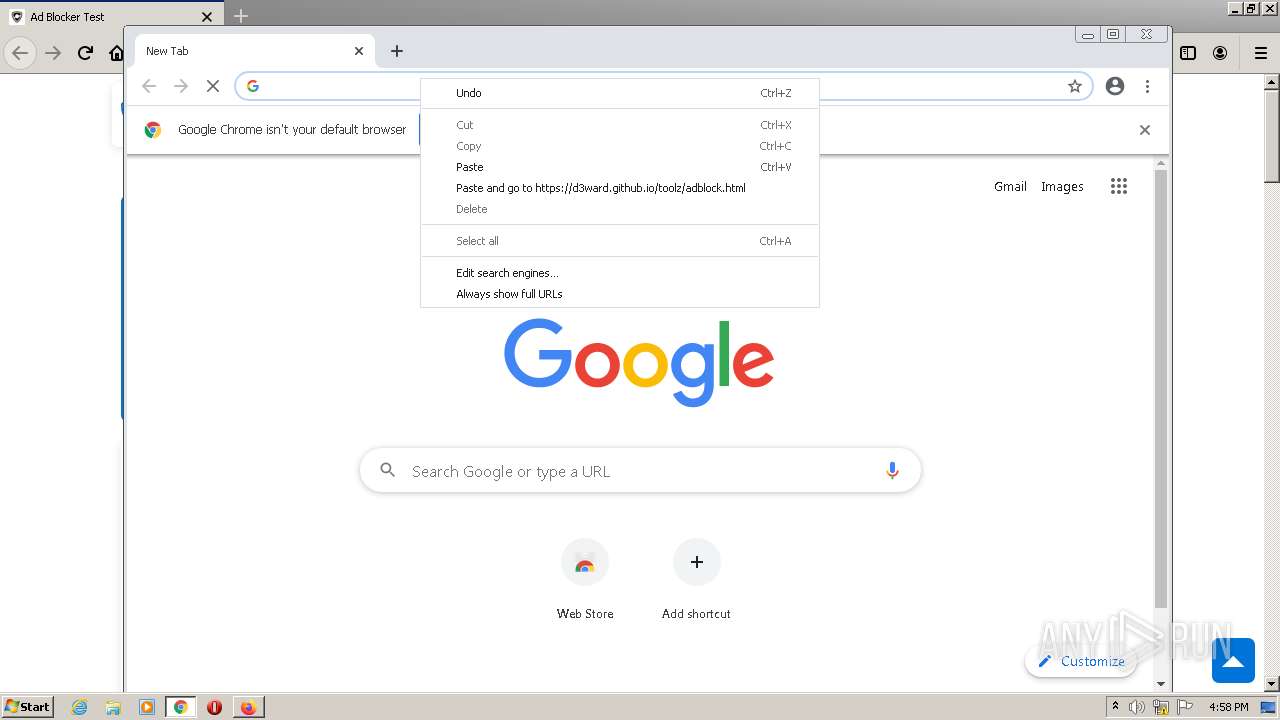
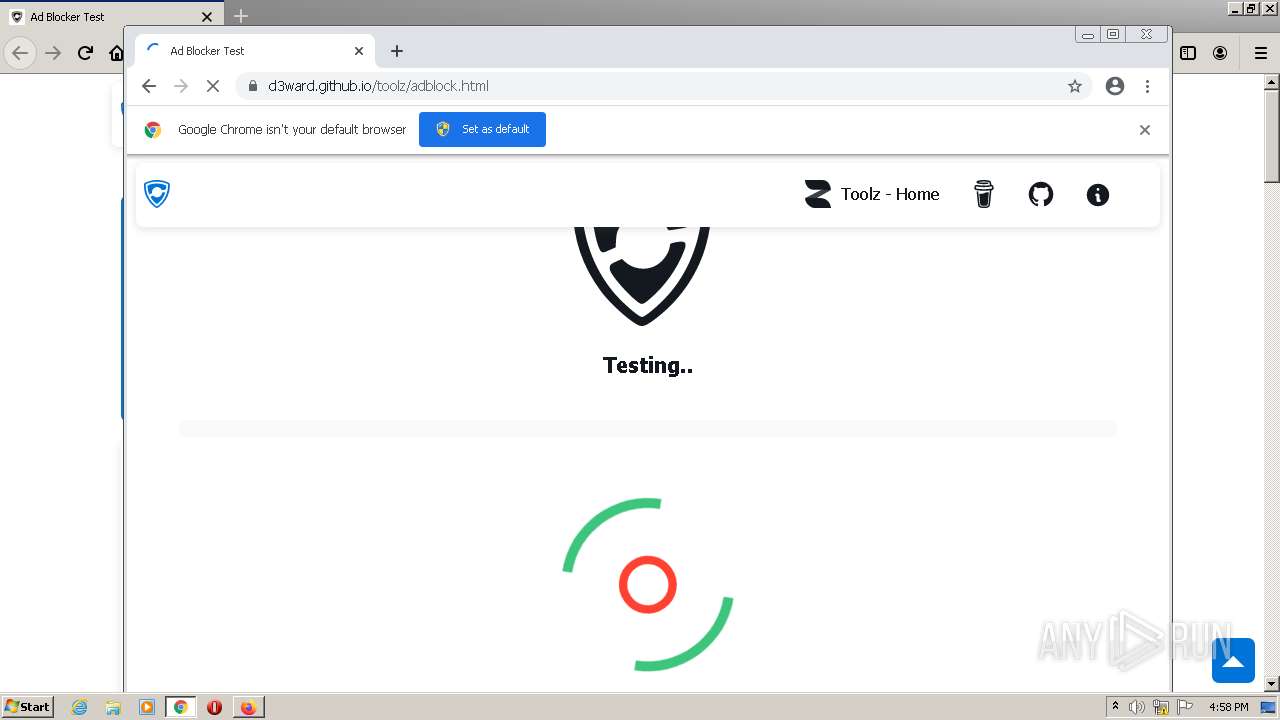
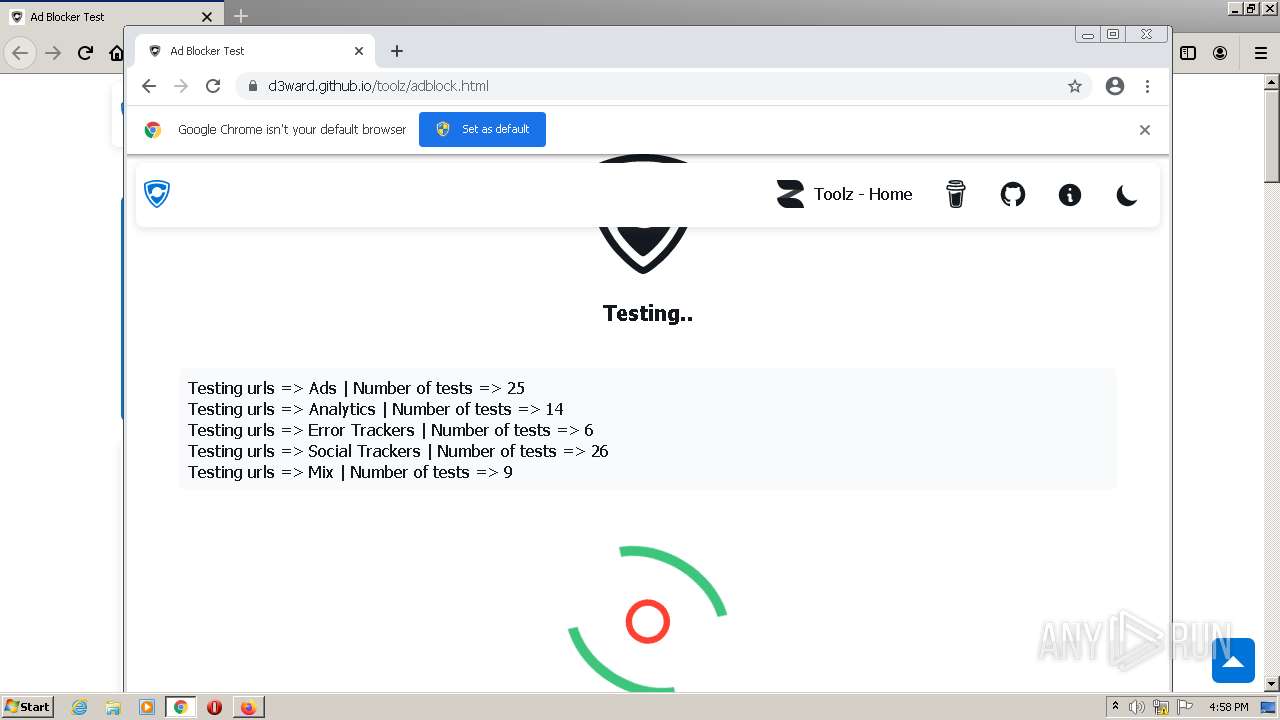
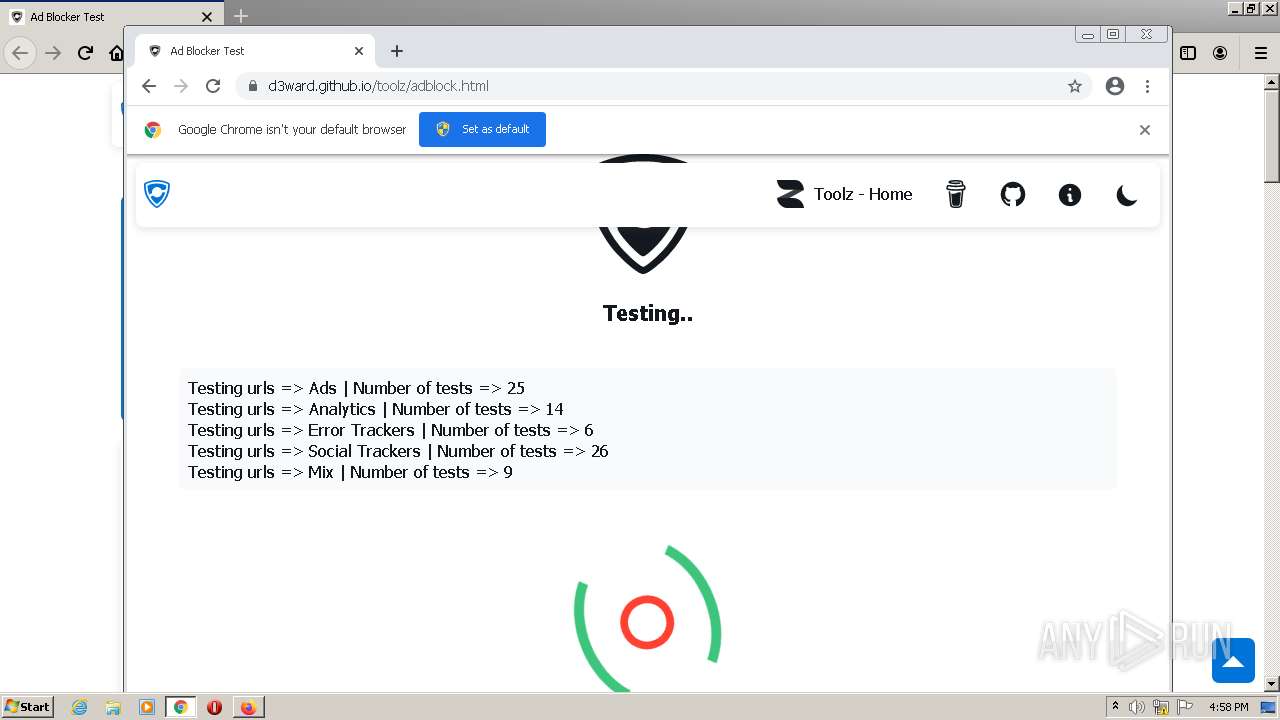
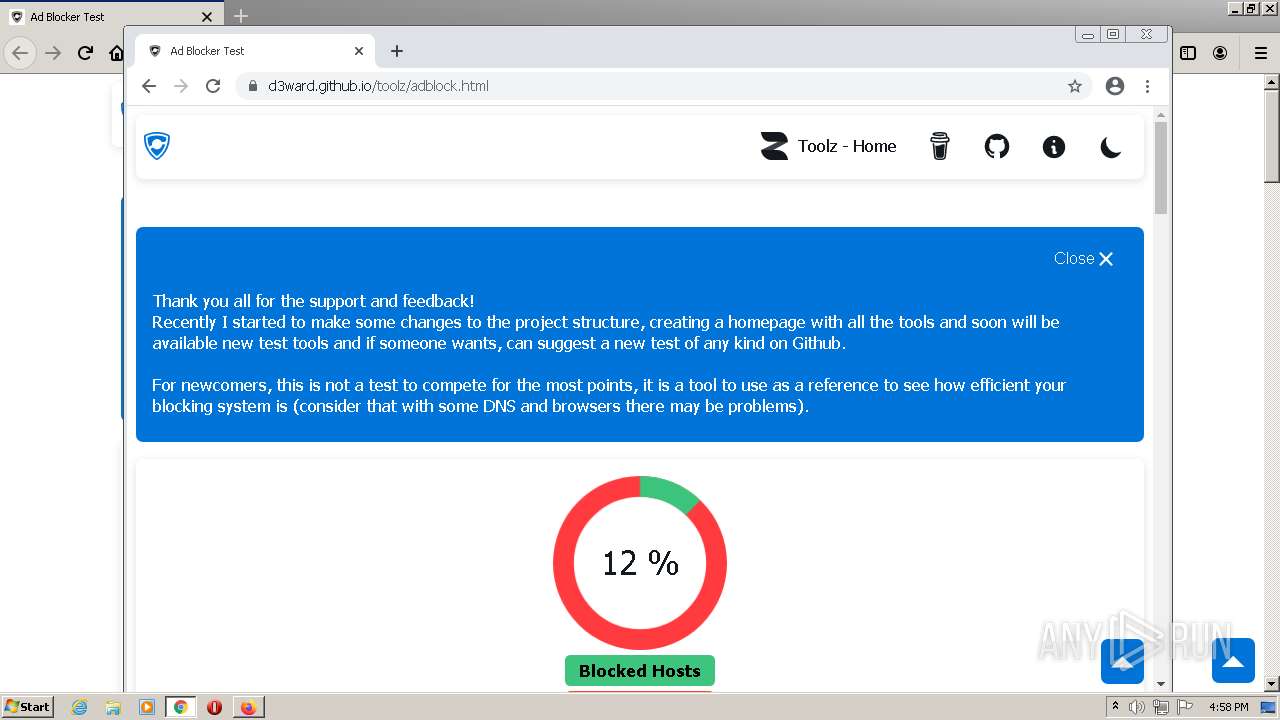
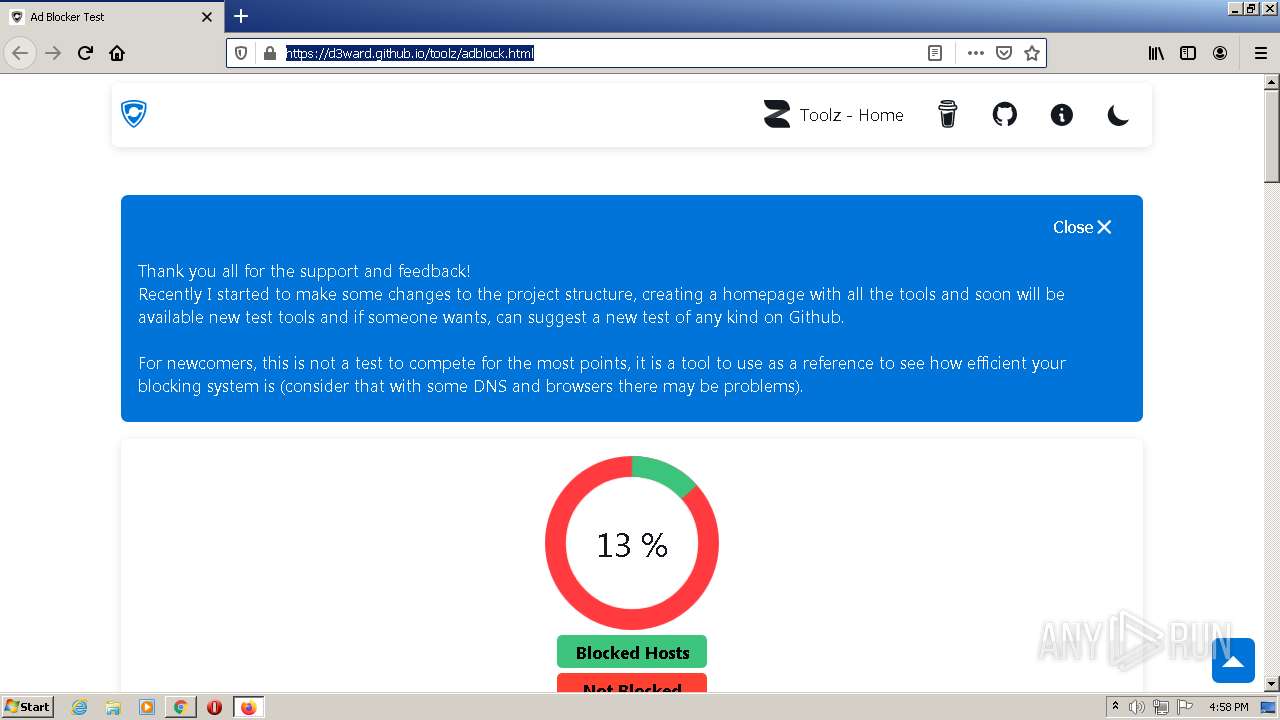
| URL: | https://d3ward.github.io/toolz/adblock.html |
| Full analysis: | https://app.any.run/tasks/710aafc2-402e-4b94-b7a4-a8baa37040a6 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 16:56:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F7C7ED885771067068A0139C14259CAC |
| SHA1: | 591B3428A7F4BD4BF771A2AB884CE471E0273FAC |
| SHA256: | 04BABF6BF5923847EDE1ADB9E09DD42A15E3AFE987A48F84604EC84DF1A08E35 |
| SSDEEP: | 3:N8OBLPErFraL:2OBrEYL |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file that was compiled in debug mode
- firefox.exe (PID: 2564)
Executable content was dropped or overwritten
- firefox.exe (PID: 2564)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3300)
INFO
Reads CPU info
- firefox.exe (PID: 2564)
Checks supported languages
- firefox.exe (PID: 4076)
- firefox.exe (PID: 2564)
- firefox.exe (PID: 2256)
- firefox.exe (PID: 3536)
- firefox.exe (PID: 188)
- firefox.exe (PID: 3524)
- firefox.exe (PID: 2276)
- chrome.exe (PID: 3300)
- opera.exe (PID: 1148)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 828)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 1384)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 1800)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 1872)
- chrome.exe (PID: 3696)
Application launched itself
- firefox.exe (PID: 2256)
- firefox.exe (PID: 2564)
- chrome.exe (PID: 3300)
Reads the computer name
- firefox.exe (PID: 2564)
- firefox.exe (PID: 4076)
- firefox.exe (PID: 3536)
- firefox.exe (PID: 2276)
- firefox.exe (PID: 188)
- firefox.exe (PID: 3524)
- opera.exe (PID: 1148)
- chrome.exe (PID: 3300)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 1800)
- chrome.exe (PID: 3696)
Creates files in the program directory
- firefox.exe (PID: 2564)
Check for Java to be installed
- opera.exe (PID: 1148)
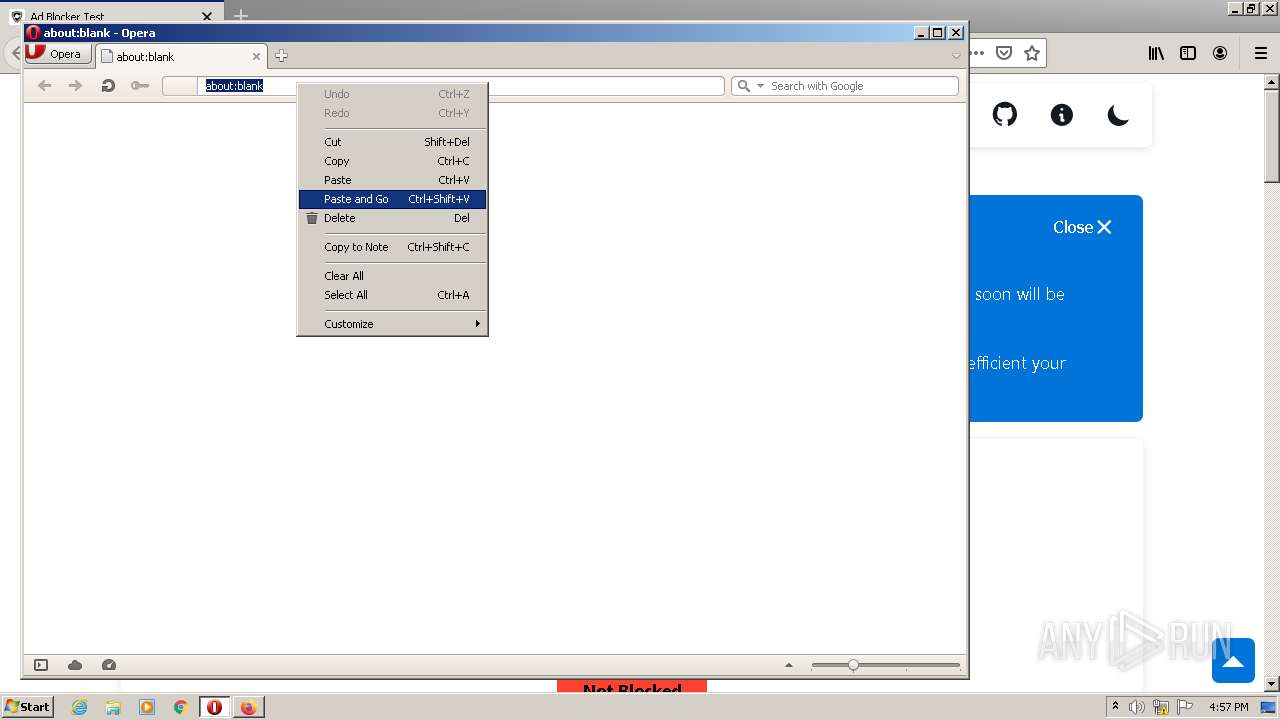
Manual execution by user
- opera.exe (PID: 1148)
- chrome.exe (PID: 3300)
Creates files in the user directory
- opera.exe (PID: 1148)
- firefox.exe (PID: 2564)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 1148)
Reads the date of Windows installation
- opera.exe (PID: 1148)
- firefox.exe (PID: 2564)
Reads the hosts file
- chrome.exe (PID: 3300)
- chrome.exe (PID: 3224)
Reads settings of System Certificates
- chrome.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
23
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2564.6.2122202073\9987182" -childID 1 -isForBrowser -prefsHandle 2804 -prefMapHandle 2800 -prefsLen 181 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2564 "\\.\pipe\gecko-crash-server-pipe.2564" 2816 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x719bd988,0x719bd998,0x719bd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9077042438051377523,17643804645747287854,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://d3ward.github.io/toolz/adblock.html" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2564.27.361076304\741876878" -childID 4 -isForBrowser -prefsHandle 3900 -prefMapHandle 3896 -prefsLen 8189 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 2564 "\\.\pipe\gecko-crash-server-pipe.2564" 3912 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
34 212
Read events
34 031
Write events
181
Delete events
0
Modification events
| (PID) Process: | (2256) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: A7D757656E010000 | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: E2DF57656E010000 | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2564) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
392
Text files
139
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:— | SHA256:— | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_9xLHV5wWaK79m1H | binary | |
MD5:— | SHA256:— | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:— | SHA256:— | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\settings\main\ms-language-packs\asrouter.ftl | text | |
MD5:— | SHA256:— | |||
| 2564 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\settings\main\ms-language-packs\asrouter.ftl.tmp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
100
TCP/UDP connections
619
DNS requests
642
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2564 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2564 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
2564 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
2564 | firefox.exe | POST | 200 | 143.204.101.188:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
2564 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
2564 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2564 | firefox.exe | POST | 200 | 2.16.186.9:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
2564 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2564 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
2564 | firefox.exe | 185.199.108.153:443 | d3ward.github.io | GitHub, Inc. | NL | shared |
2564 | firefox.exe | 143.204.98.33:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
2564 | firefox.exe | 35.82.27.113:443 | location.services.mozilla.com | Merit Network Inc. | US | unknown |
2564 | firefox.exe | 142.250.185.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2564 | firefox.exe | 46.137.15.86:443 | aurora-d3.herokuapp.com | Amazon.com, Inc. | IE | suspicious |
2564 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2564 | firefox.exe | 143.204.98.36:443 | content-signature-2.cdn.mozilla.net | — | US | suspicious |
2564 | firefox.exe | 34.217.3.234:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2564 | firefox.exe | 143.204.98.122:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
d3ward.github.io |
| malicious |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potential Corporate Privacy Violation | ET POLICY possible OnePlus phone data leakage DNS |
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2564 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |