| URL: | http://walli.shanga.co/ |
| Full analysis: | https://app.any.run/tasks/cca7f3ba-6488-4191-a955-bb5949f97bde |
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2023, 06:55:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D2C531D7A4A2327A8DA0E5B49FD41799 |
| SHA1: | 558CCD6CBF44A69124C7D0B49A474A95CA9E9320 |
| SHA256: | 04A1964B150368B675489984BD55B08D2E8B84EAEB7EBCEB5119262AAC7AA1E2 |
| SSDEEP: | 3:N1KJEK5Kn:CKK5Kn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://walli.shanga.co/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3484 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1000 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
12 996
Read events
12 941
Write events
55
Delete events
0
Modification events
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
44
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bouncy[1].htm | html | |
MD5:588BB3A6EEBA585BB733DCA1AB257B54 | SHA256:A2B70CCD46F7D19767C8F3C304B9D57EA33765177E8E563DE60576364A6484C4 | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:4B45042ADD73431F748B8A09E604F65C | SHA256:0A81F85EFD397617CD0D9AE2AF5B5D10BA31604685E247E2437DA06915EF7917 | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\6SCMQHI1.htm | html | |
MD5:F2C282DF9BE78F67A1EB813C09F83364 | SHA256:E531CD6E97C26CB8E8974E837135773C1DB23C95B9D7B458B8A2FC70B58C6A3C | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:1222AF942B0EDD566587703B03BC31AC | SHA256:B54B5AF6A4D38494FEC191F940D10691D441161A51425D4E3F4884EFFD819AB5 | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:DEC6BBE308EB44937F77160A25EE32DB | SHA256:68A71DE28F488586C2B169F4652347E0A1FD632D48A6D6725393607BFA18BC7E | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0LHCI2JB.txt | text | |
MD5:066B7961C6ACC42CFEAE6411551DCD89 | SHA256:9834820074A53BDF9648216173FA1A37FDF0FC25399AEF5D7570596CC66AC29D | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:557E718063B5E8027DBB7A6A784EF19D | SHA256:9E568EF4D126108D5642D94A5C5E72B65236C8D296962A43EEA96F5A76340302 | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
50
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | iexplore.exe | GET | 302 | 116.202.135.114:80 | http://activerevenue.trckswrm.com/recommendation?rec_link_id=2&pub_id=3&pub_sub_id=kif_fill | IN | — | — | suspicious |
1000 | iexplore.exe | GET | 200 | 67.27.235.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?acf177189d249af9 | US | compressed | 4.70 Kb | whitelisted |
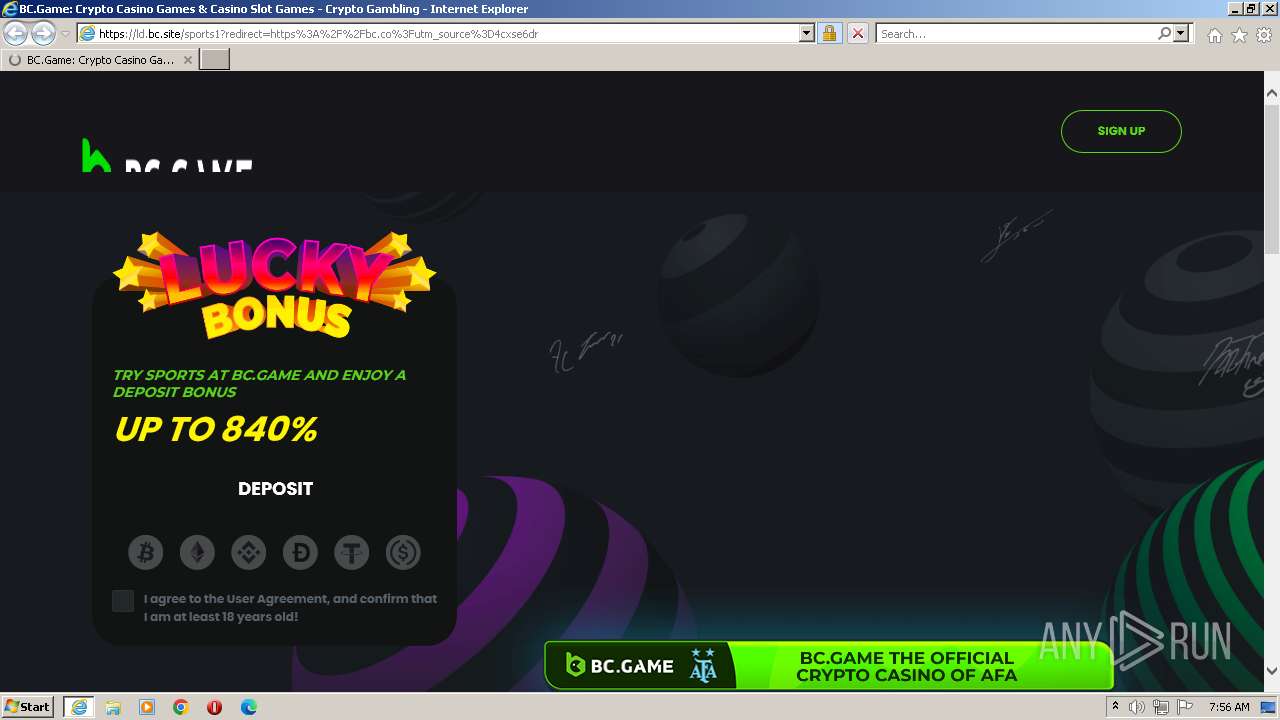
3484 | iexplore.exe | GET | 200 | 67.225.218.6:80 | http://walli.shanga.co/ | US | html | 2.10 Kb | suspicious |
3484 | iexplore.exe | GET | 200 | 67.225.218.6:80 | http://walli.shanga.co/page/bouncy.php?&bpae=GbhGdzsno1x%2FjksXMaynrhTBYOAMO3djsXWq3f%2FunBkcPlmNrZ3Z7bsRxJqU5BIb7Z%2F6KafSdrh9GIQxiHYY0ujvjKwdphJbTGviET5X80Fm2WGBNTFTnSD9KL%2Fc8CmjMuZ4thEcPHb9aJ2kdc2tdmyEknb%2FubkNoa6Xh8cOKjxmEUfSJMDv0GhE31Pkw%2BBEtndZztPFPbzGIfXgD%2BgFX%2FWMHLCL5BU6r%2FUWiGbaZ0YAuBOWI7Iq7rIXjPRdRrRMqEJ2Ai%2B4g4ZEYAzaBX5zvXlJ780lbTNQe0cmD2TOldYI5rjy5yQavE1gKdoFmKkbjwGbDXd8BTjrZ6fcrF%2BnyOk9fd9HmY6yQ8DWU5Ei5m9GcZYqdAoya3QSkJ41cZiJeND2XZnT%2BifhDVtKQW00wublox0t8zXmqfJhba%2FT1hdI5nw9TRnCAk9EioF8ok6sm7n5mjbIKS82uKxrJIGCfA%3D%3D&redirectType=js&inIframe=false&inPopUp=false | US | html | 766 b | suspicious |
1088 | svchost.exe | GET | 200 | 67.27.235.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?56bb05fd186d0c6e | US | compressed | 62.3 Kb | whitelisted |
1088 | svchost.exe | GET | 304 | 67.27.235.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c93f4204a486a0a4 | US | compressed | 62.3 Kb | whitelisted |
1000 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3484 | iexplore.exe | GET | 302 | 3.33.192.145:80 | http://sysguaard-1.live/api/v1/px?xmlid=CnGstJfBNV0zjvzLU2LRU2AFrWurS09cPGvJh0sJ | US | html | 242 b | suspicious |
3484 | iexplore.exe | GET | 200 | 23.201.254.55:80 | http://x2.c.lencr.org/ | CH | binary | 300 b | whitelisted |
3484 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3484 | iexplore.exe | 67.225.218.6:80 | walli.shanga.co | LIQUIDWEB | US | malicious |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3484 | iexplore.exe | 15.197.224.234:80 | sysguaard-1.live | AMAZON-02 | US | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1000 | iexplore.exe | 2.23.209.150:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
1000 | iexplore.exe | 67.27.235.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3484 | iexplore.exe | 3.33.192.145:80 | sysguaard-1.live | AMAZON-02 | US | suspicious |
1000 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
walli.shanga.co |
| suspicious |
sysguaard-1.live |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
activerevenue.trckswrm.com |
| suspicious |
partnerbcgame.com |
| malicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |