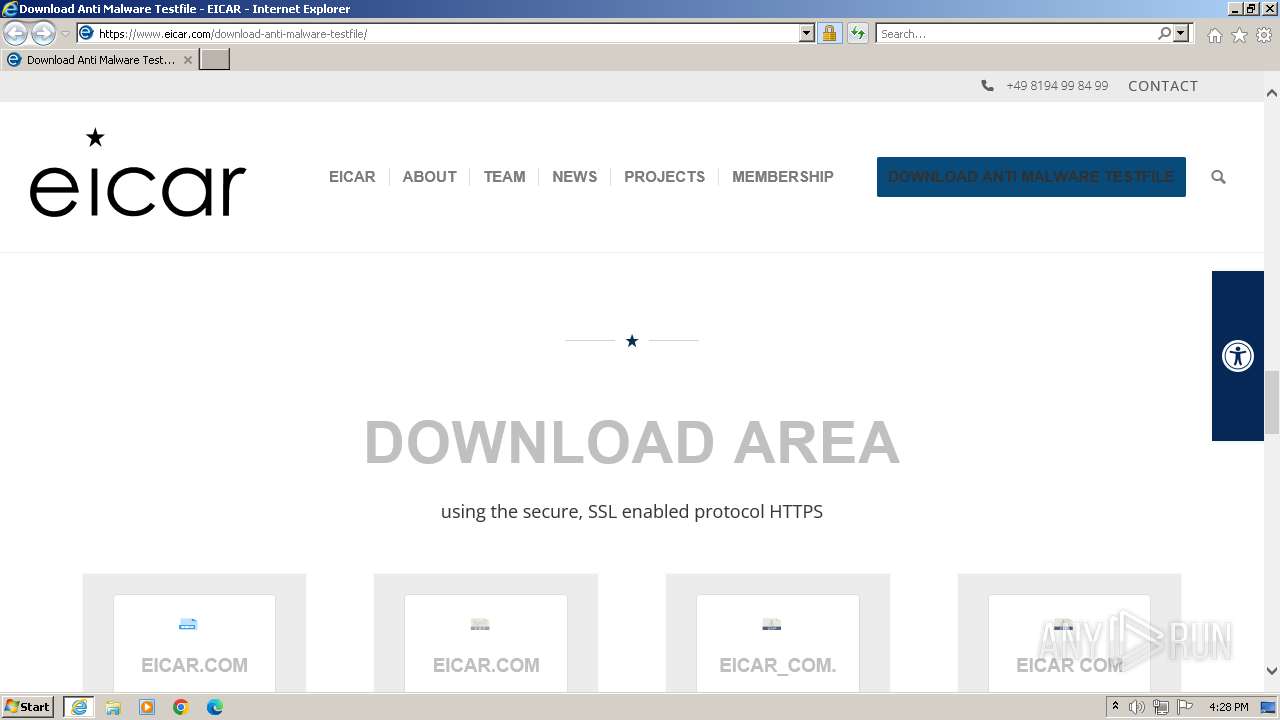
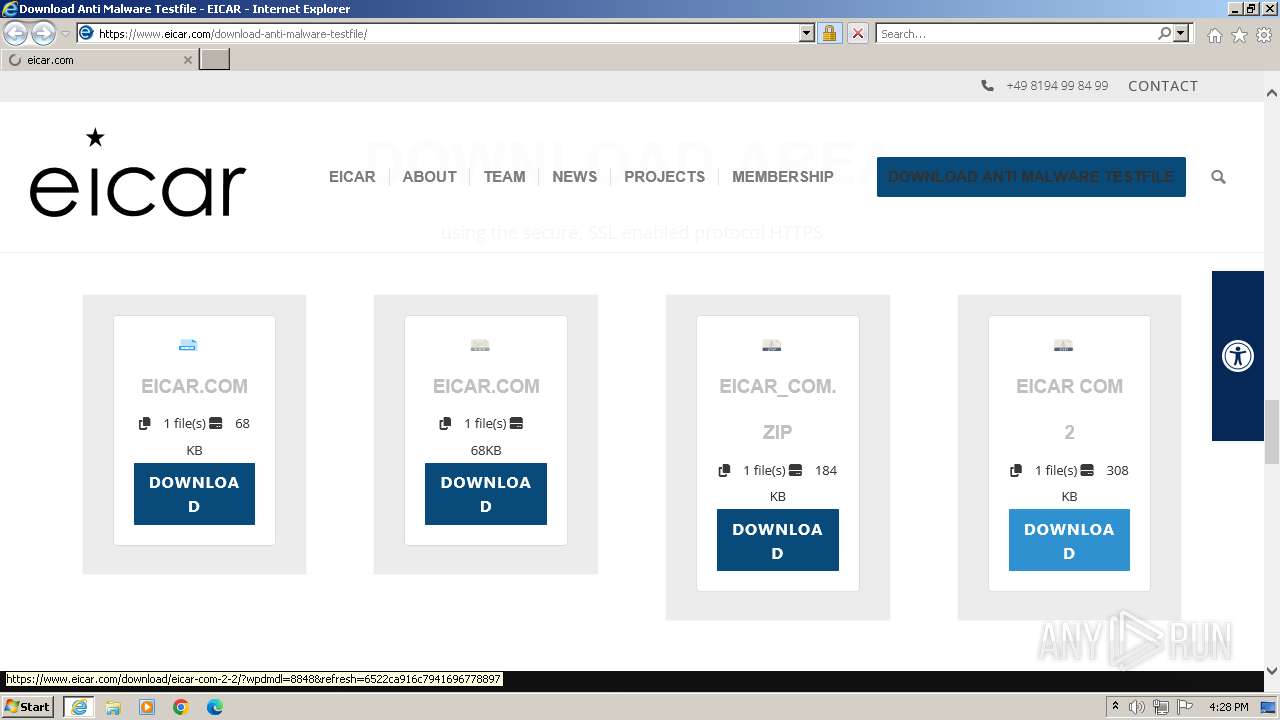
| URL: | https://www.eicar.com/download-anti-malware-testfile/ |
| Full analysis: | https://app.any.run/tasks/207f129d-3532-490c-b1bb-3d7f81222579 |
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2023, 15:28:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| SHA1: | F38DA1454D1001D60A8DC73AE98CF3CBE1133940 |
| SHA256: | 048D404EB3FDC34F063B7E2CB893B8EDB6052CD3A83B43FB956117465D428E95 |
| SSDEEP: | 3:N8DSLo+ZMJElMIIy9K:2OLoCMKPIN |
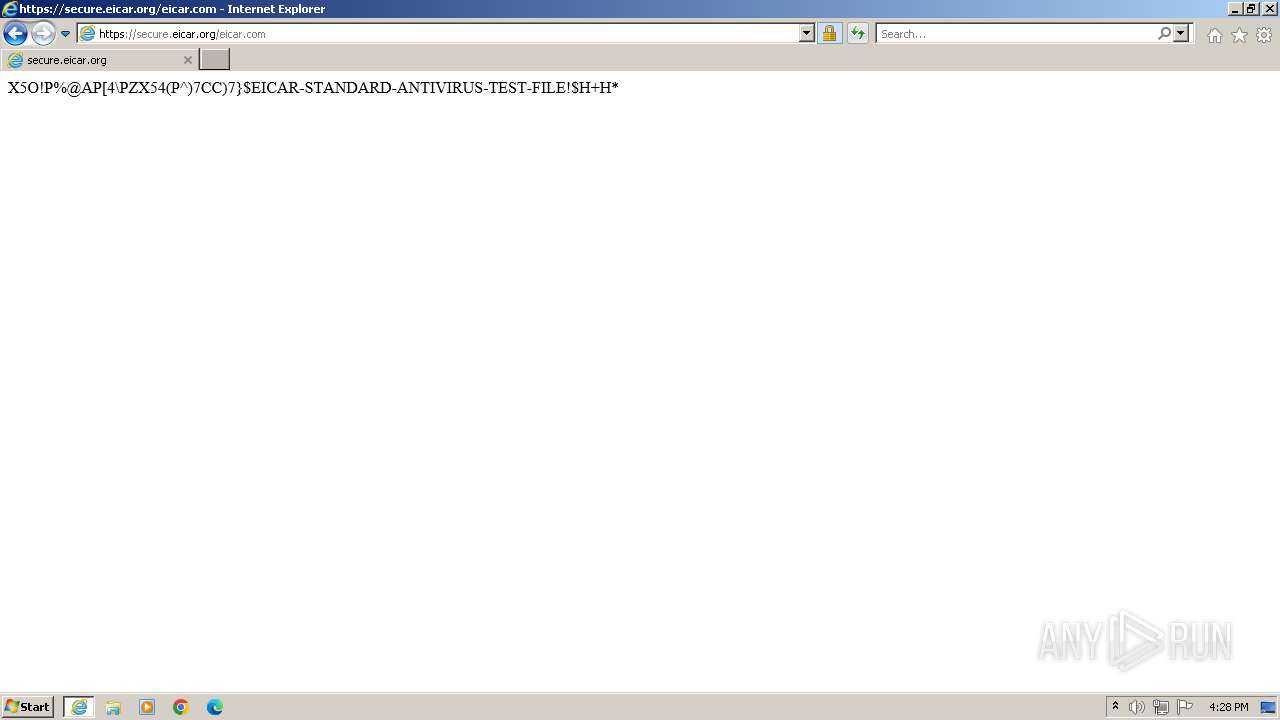
MALICIOUS
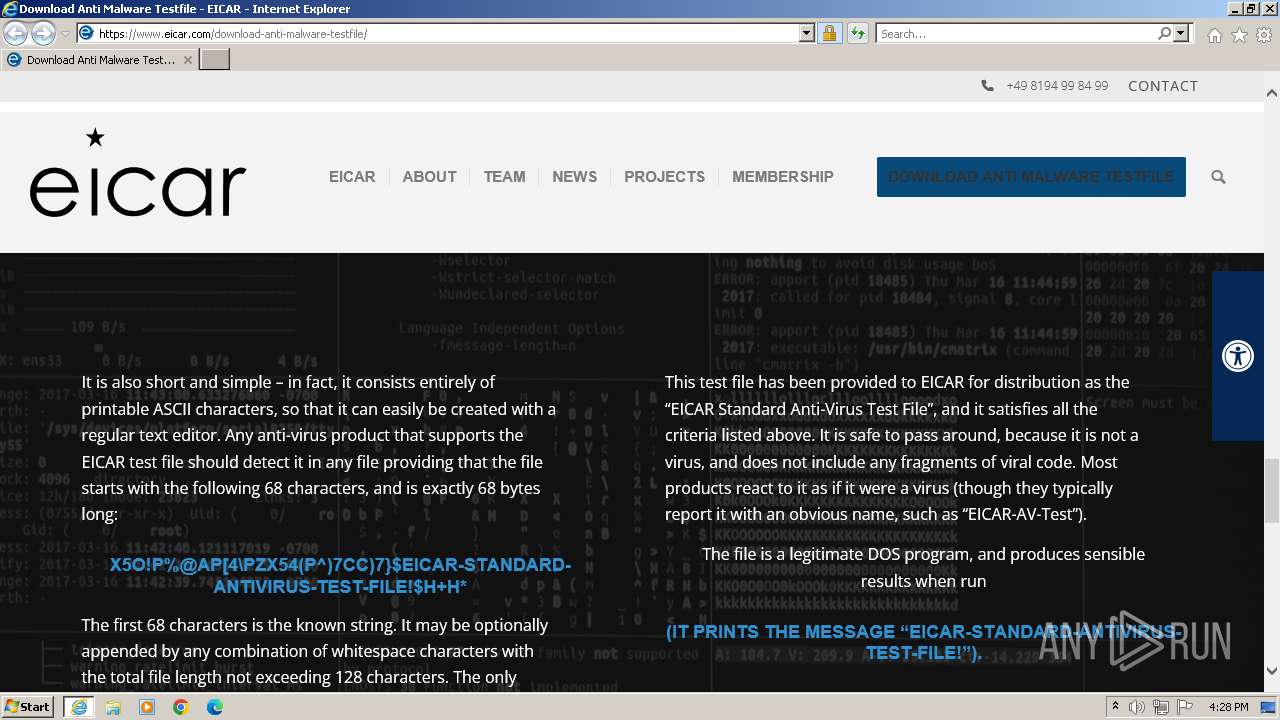
The EICAR Standard Anti-Virus Test File is detected
- iexplore.exe (PID: 2476)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2476 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3628 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3628 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.eicar.com/download-anti-malware-testfile/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 634
Read events
16 558
Write events
74
Delete events
2
Modification events
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
46
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab146C.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download-anti-malware-testfile[1].htm | html | |
MD5:F79CD2DBB283C9043CED52C078ABEA51 | SHA256:2608899680D011936D58639BFACDC3994C817B99891EB3EC2C25B780531F3504 | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EB1A80F4208DA0218F062456FF903BF8 | SHA256:3477E13A06BA4B2FC768F0B9FF5D4FD7471BE576866DA35D73F21C0BBAF0C86B | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:CE86E03B33B899F68DD08C69C5C7B497 | SHA256:1AA961B42C45B78C163BEC5846828DE6406E72F61B74224B9A9783BF984D02A4 | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab147E.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:D04B2DDFC7B405042458160C26B51C2C | SHA256:7597084C96B7ED53D7EF736E70EF10BF18BFA2300E3F799818947380E8FB0285 | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\autoptimize_e3c75247f16ed8dabe4caa8b6fd93df9[1].css | text | |
MD5:250CAFD6BBBAA81968789EF3408E1157 | SHA256:6FD9A88977E248C9686D5194418A36AFB379522D8A32BE07C5D66811B5B07992 | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4006F8EDBD80DCCEB279BC932D8E7B24 | binary | |
MD5:431BA0DD3D6A1EE7117C43C5D7945953 | SHA256:55E107F18011B9C01FAB9858B35C3B283C36241732E028C7A6FAF136BBF4B0A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
49
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2476 | iexplore.exe | GET | 200 | 67.27.159.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?717397429a10e56a | unknown | compressed | 61.6 Kb | unknown |
2476 | iexplore.exe | GET | 200 | 67.27.159.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?df2f081986e1c00c | unknown | compressed | 4.66 Kb | unknown |
2476 | iexplore.exe | GET | 200 | 23.56.202.135:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2476 | iexplore.exe | GET | 200 | 67.27.159.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?12fd62799eedc857 | unknown | compressed | 61.6 Kb | unknown |
2476 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
2476 | iexplore.exe | GET | 200 | 216.58.212.3:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
2476 | iexplore.exe | GET | 200 | 184.24.77.185:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgR3HedKCJdnTZvr%2F5ofP%2FafbA%3D%3D | unknown | binary | 503 b | unknown |
2476 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
2476 | iexplore.exe | GET | 200 | 23.56.202.135:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
2476 | iexplore.exe | GET | 200 | 184.24.77.185:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgOMb%2FjRoG32gtVtcK6PAM6Jpw%3D%3D | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2476 | iexplore.exe | 89.238.73.97:443 | secure.eicar.org | manitu GmbH | DE | unknown |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2476 | iexplore.exe | 67.27.159.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | malicious |
2476 | iexplore.exe | 23.56.202.135:80 | x1.c.lencr.org | AKAMAI-AS | GB | unknown |
2476 | iexplore.exe | 184.24.77.185:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2476 | iexplore.exe | 104.18.22.52:443 | kit.fontawesome.com | CLOUDFLARENET | — | unknown |
2476 | iexplore.exe | 152.199.5.152:443 | platform.linkedin.com | EDGECAST | US | unknown |
2476 | iexplore.exe | 188.114.97.3:443 | widget.tagembed.com | CLOUDFLARENET | NL | unknown |
2476 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2476 | iexplore.exe | 172.64.131.9:443 | ka-f.fontawesome.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
kit.fontawesome.com |
| whitelisted |
platform.linkedin.com |
| whitelisted |
widget.tagembed.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |