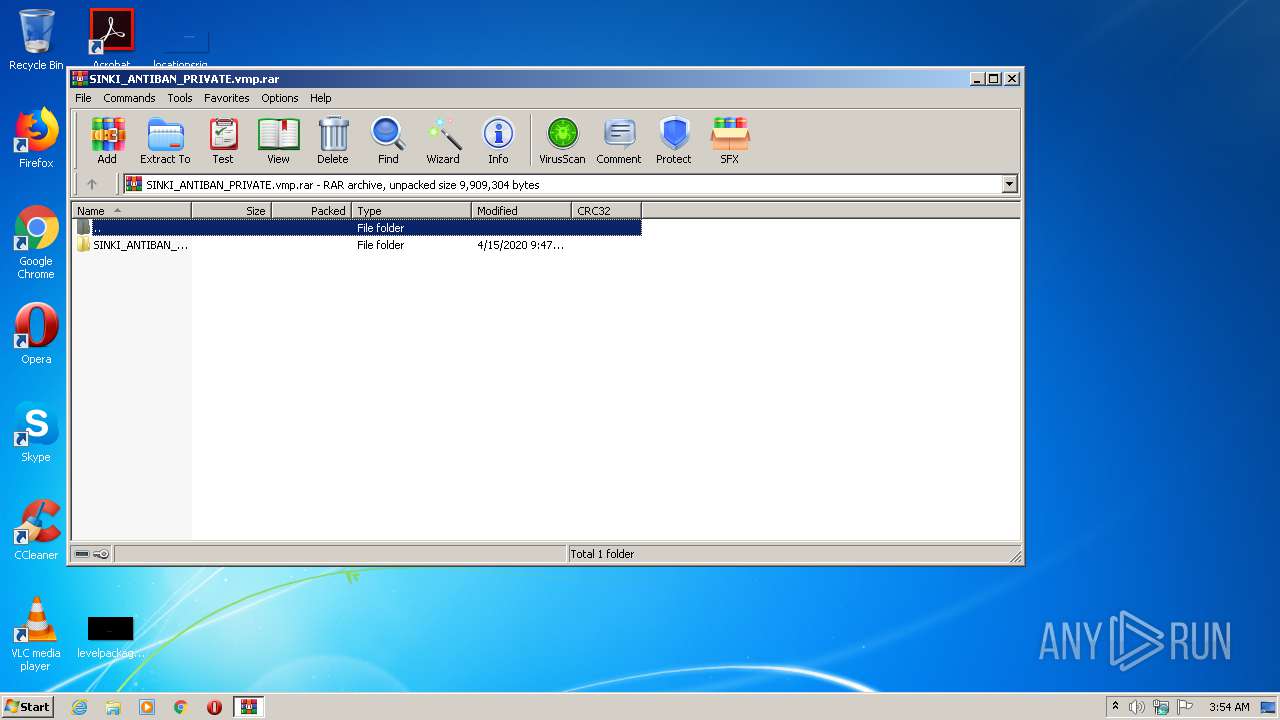
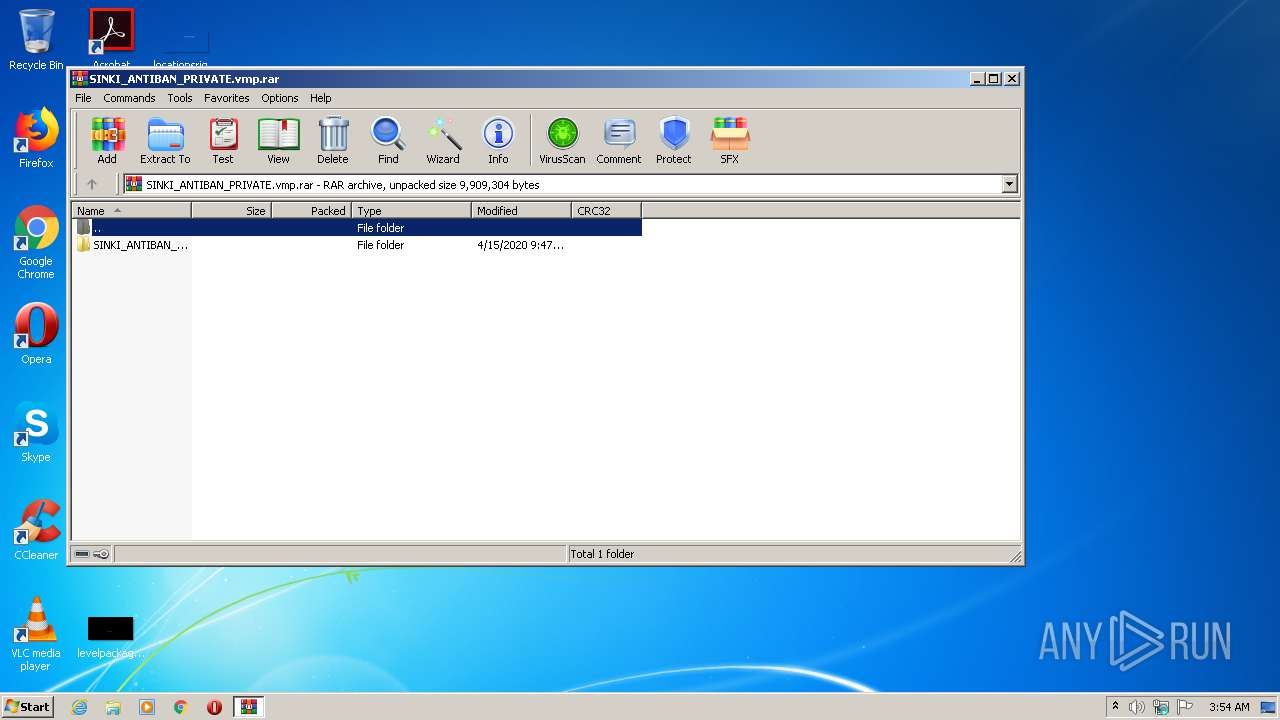
| File name: | SINKI_ANTIBAN_PRIVATE.vmp.rar |
| Full analysis: | https://app.any.run/tasks/98041186-34b0-4f87-94fc-4eb7e81323c0 |
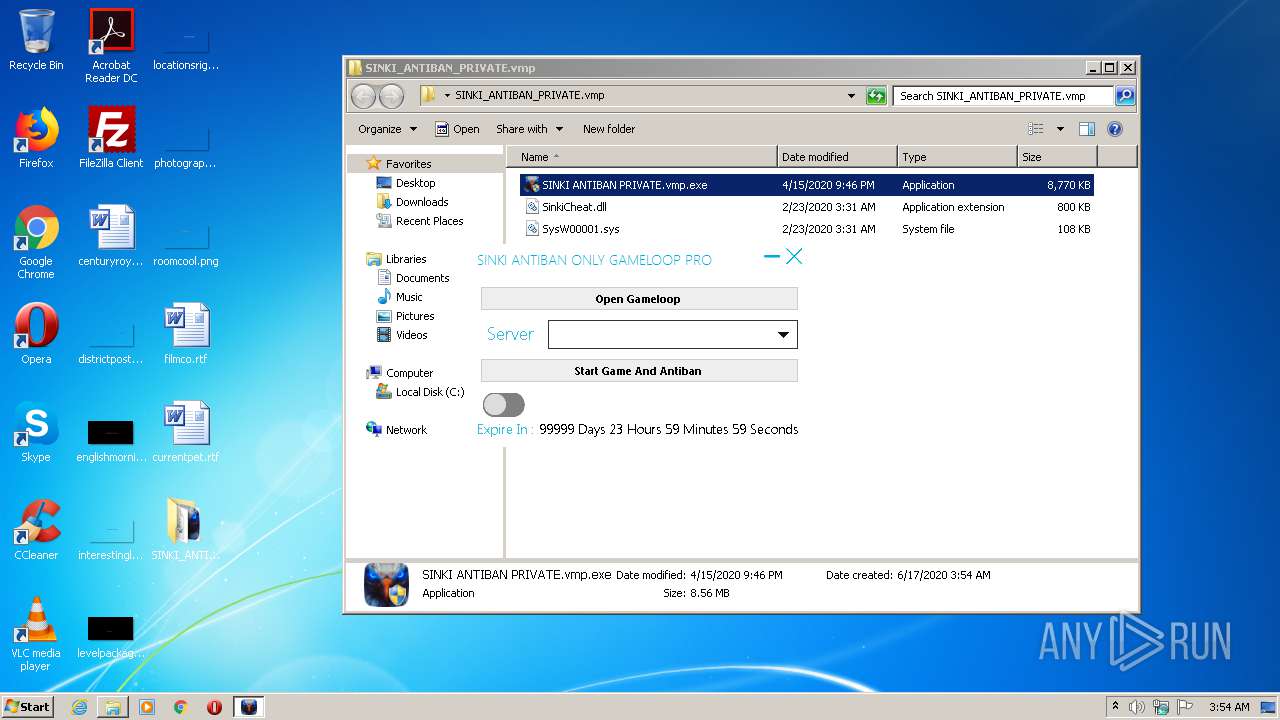
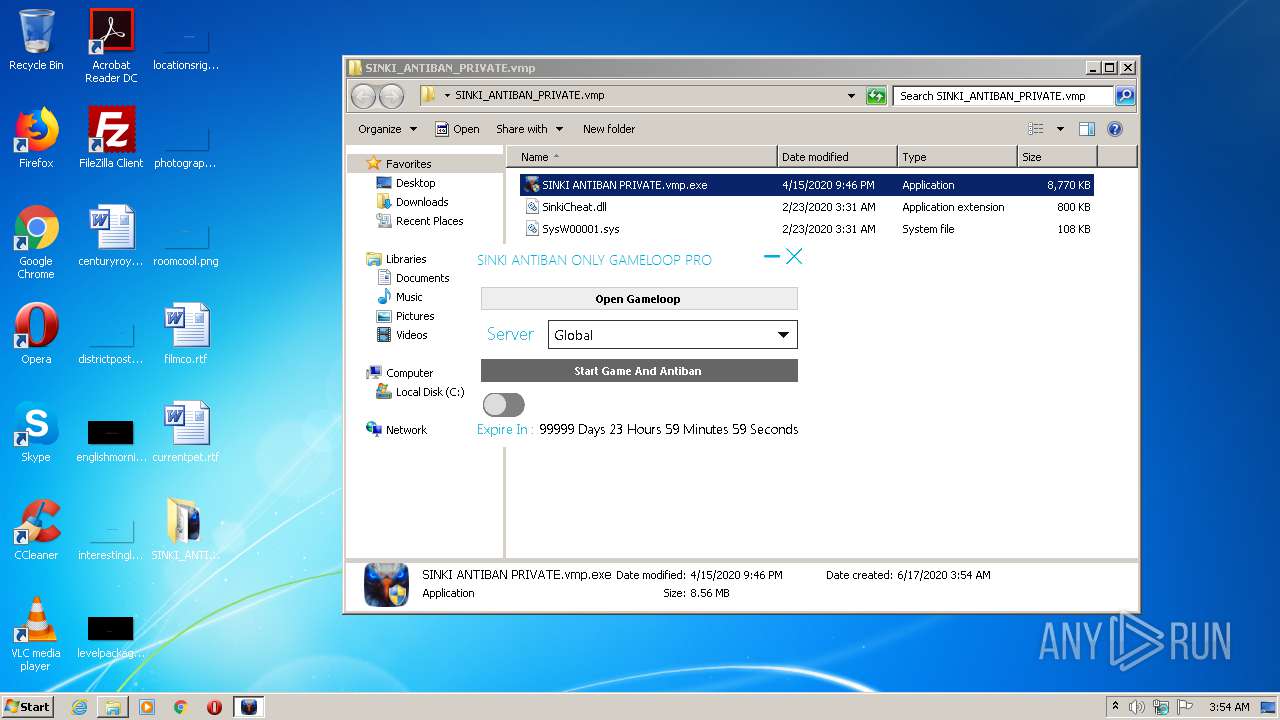
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2020, 02:54:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 28FB005184912E1711960B0776B68194 |
| SHA1: | 6B86716937A2235AD6BBB5AD40F16C914236DFD5 |
| SHA256: | 0483BD08982FC752FD2FA8E4FD453C0756F76B91F6E4E54248D107016C423DEF |
| SSDEEP: | 196608:AfAO2KoIn56fx6LC7yUPRulmbHeS4MeGeUSU:Afp2an5Yx6LCmpmbeS4FGes |
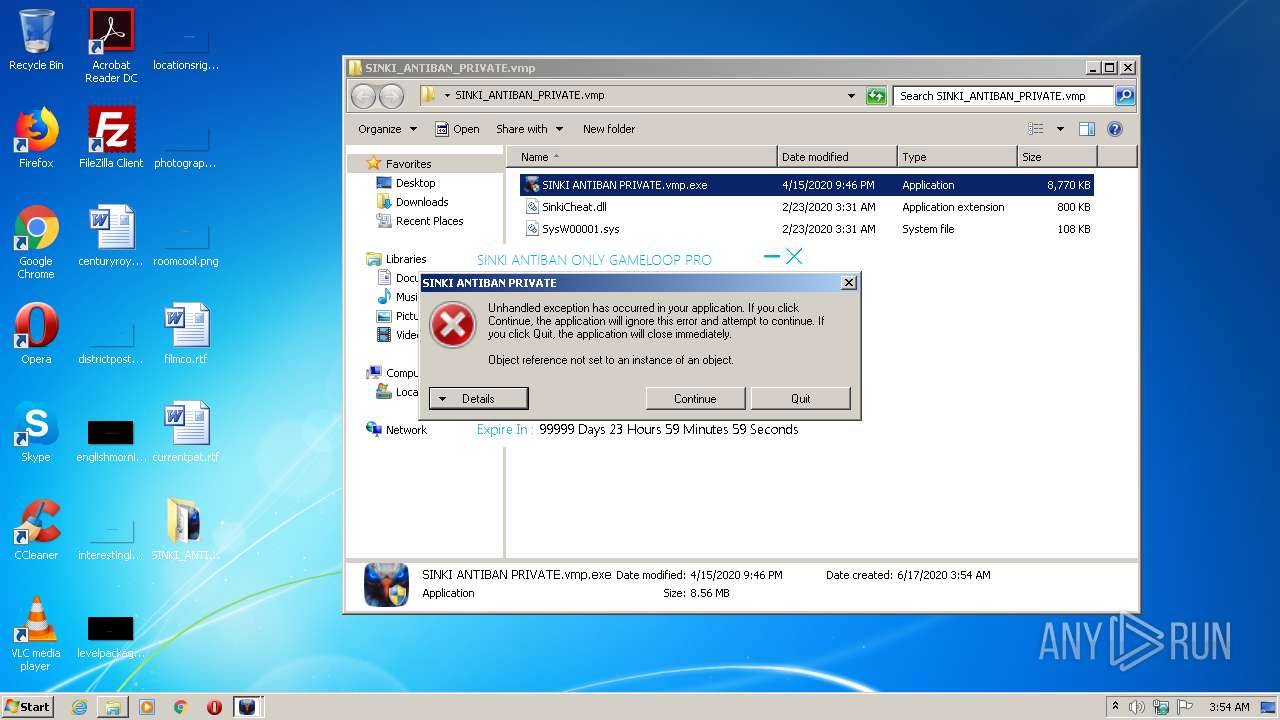
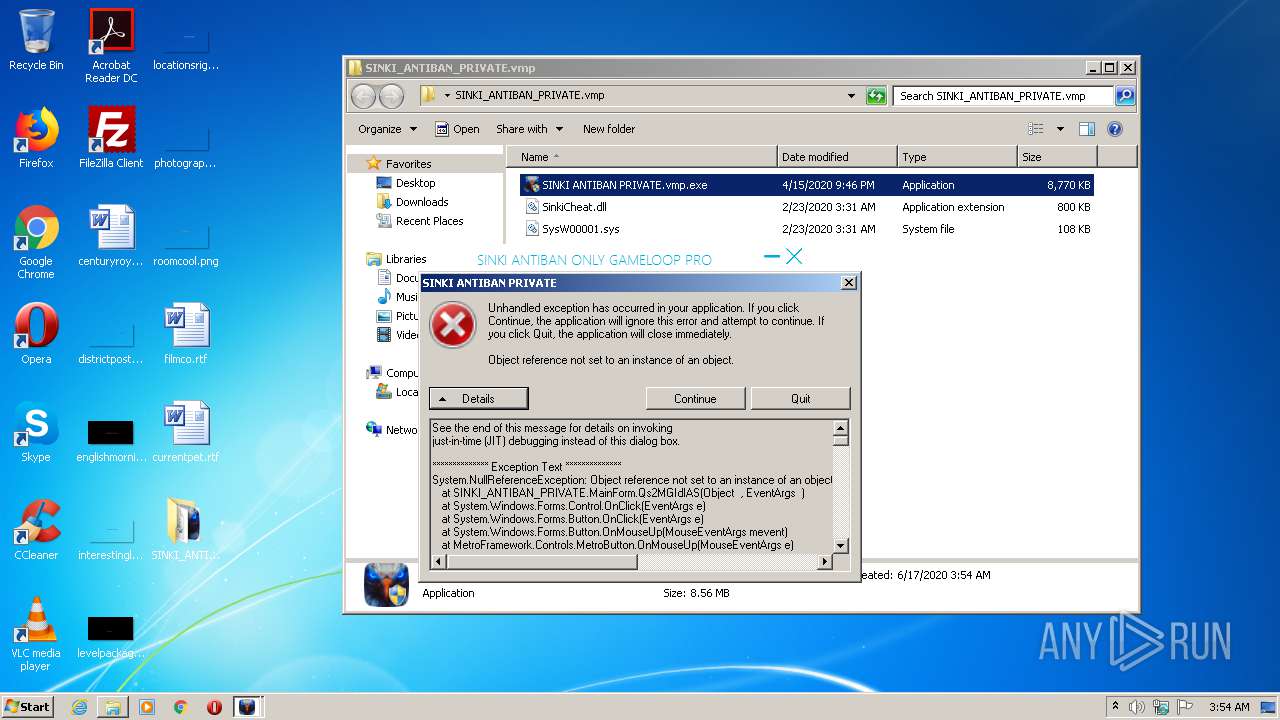
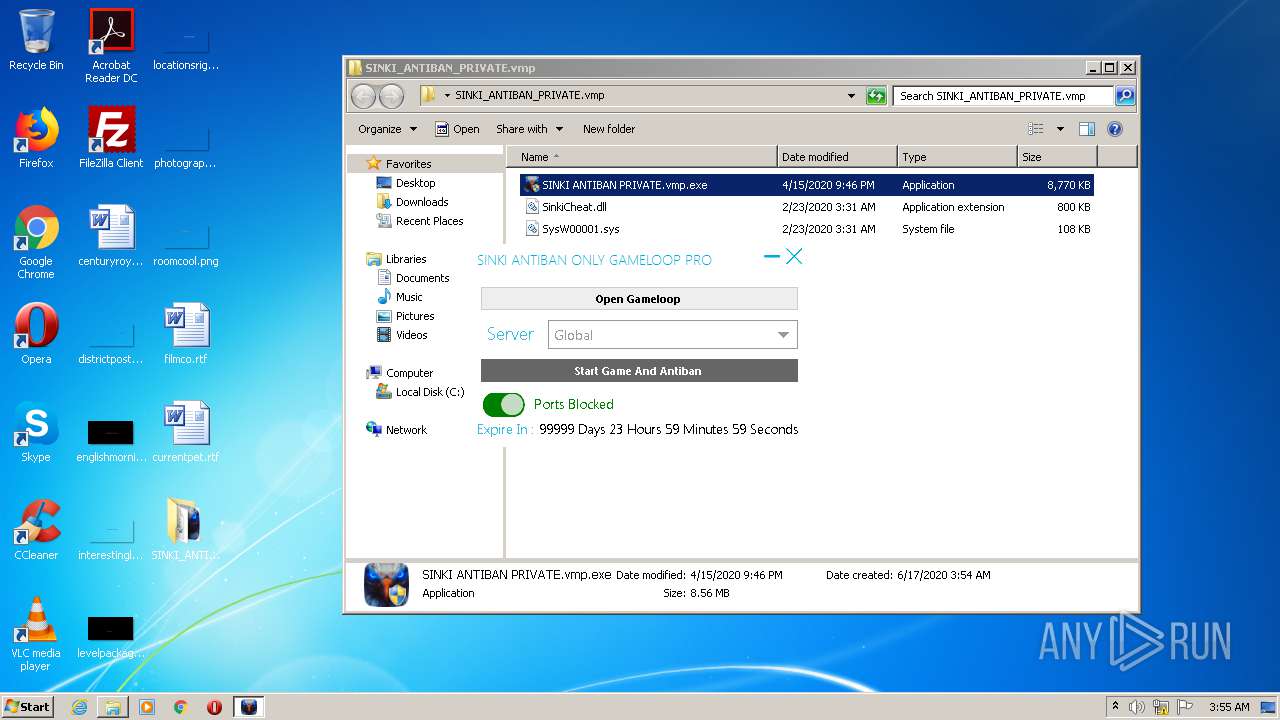
MALICIOUS
Application was dropped or rewritten from another process
- SINKI ANTIBAN PRIVATE.vmp.exe (PID: 2940)
- SINKI ANTIBAN PRIVATE.vmp.exe (PID: 2492)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1404)
Starts NET.EXE for service management
- cmd.exe (PID: 2464)
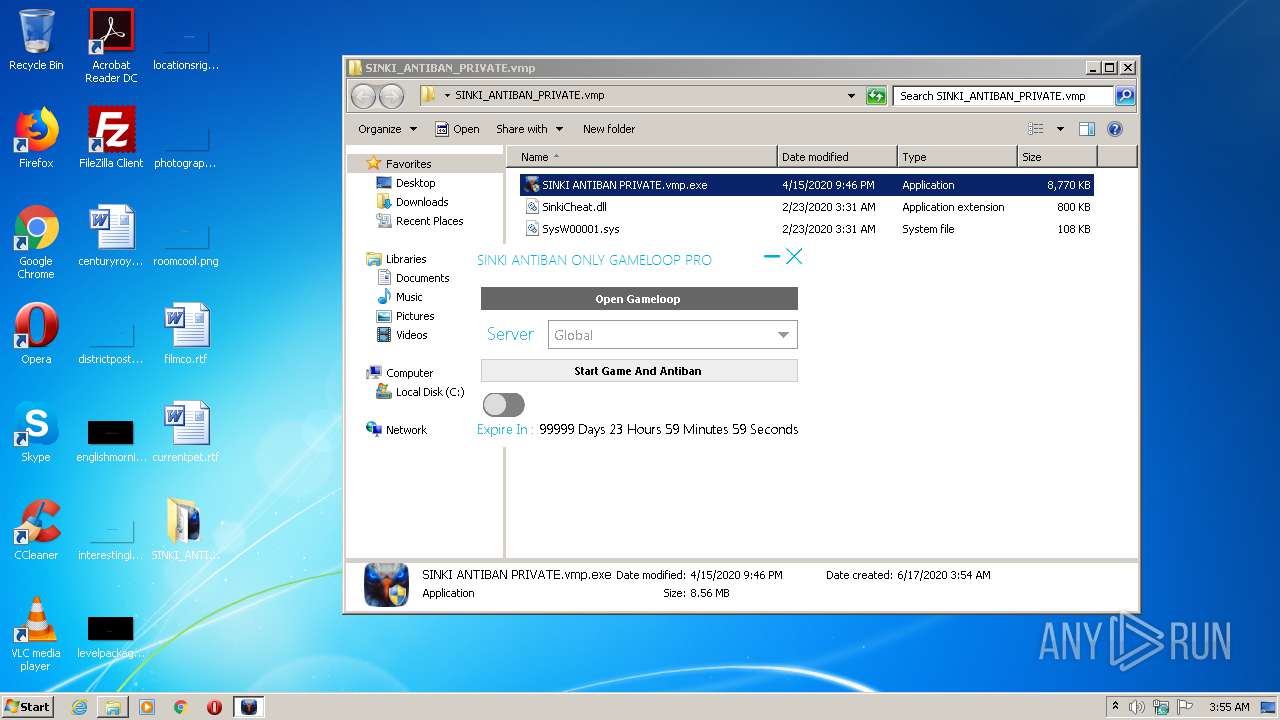
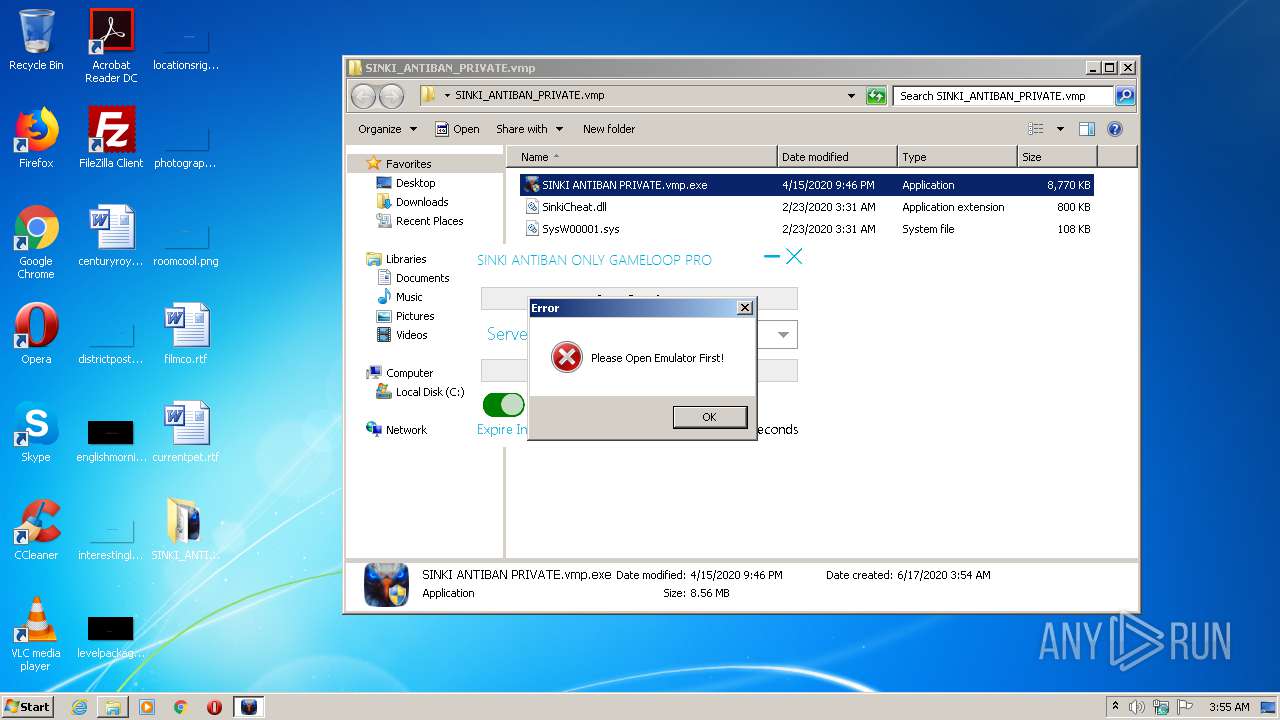
SUSPICIOUS
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3756)
- cmd.exe (PID: 2464)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2464)
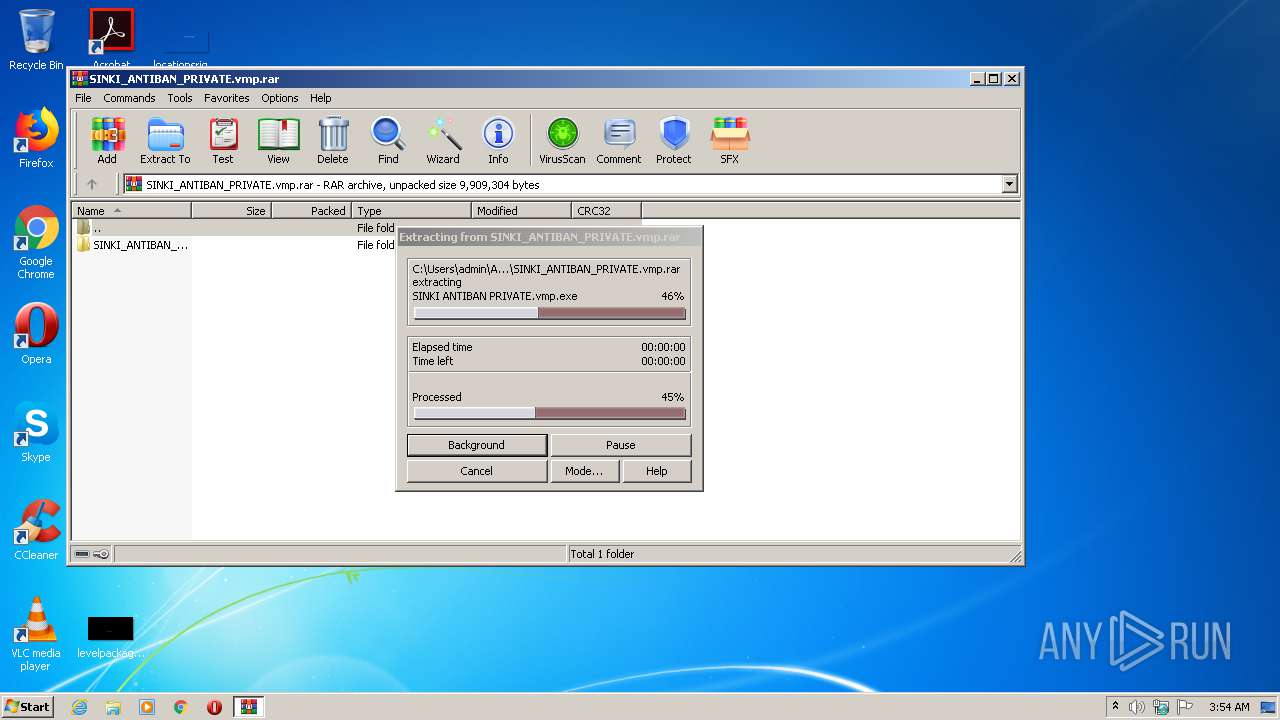
Executable content was dropped or overwritten
- SINKI ANTIBAN PRIVATE.vmp.exe (PID: 2940)
- WinRAR.exe (PID: 3144)
Creates files in the Windows directory
- SINKI ANTIBAN PRIVATE.vmp.exe (PID: 2940)
Starts CMD.EXE for commands execution
- SINKI ANTIBAN PRIVATE.vmp.exe (PID: 2940)
Removes files from Windows directory
- SINKI ANTIBAN PRIVATE.vmp.exe (PID: 2940)
INFO
Manual execution by user
- SINKI ANTIBAN PRIVATE.vmp.exe (PID: 2492)
- SINKI ANTIBAN PRIVATE.vmp.exe (PID: 2940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
56
Monitored processes
17
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | netsh advfirewall firewall set rule name=Gameloop new enable=no | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2464 | cmd /cnetsh advfirewall firewall delete rule name=SINKI & netsh advfirewall firewall set rule name=Gameloop new enable=yes & taskkill /t /f /im AndroidEmulator.exe & taskkill /t /f /im SystemX68.exe & taskkill /t /f /im aow_exe.exe & net stop aow_drv & net stop Tensafe | C:\Windows\system32\cmd.exe | — | SINKI ANTIBAN PRIVATE.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
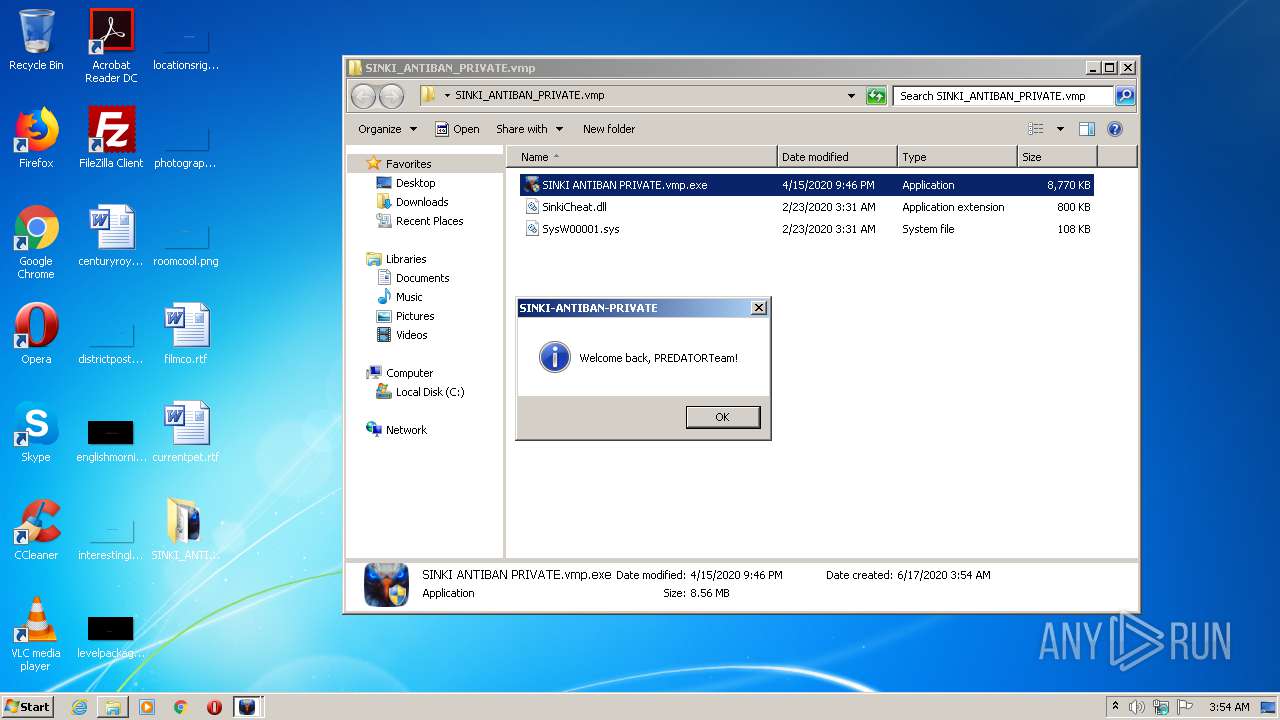
| 2492 | "C:\Users\admin\Desktop\SINKI_ANTIBAN_PRIVATE.vmp\SINKI ANTIBAN PRIVATE.vmp.exe" | C:\Users\admin\Desktop\SINKI_ANTIBAN_PRIVATE.vmp\SINKI ANTIBAN PRIVATE.vmp.exe | — | explorer.exe | |||||||||||
User: admin Company: sinkicheat.com Integrity Level: MEDIUM Description: SINKI ANTIBAN PRIVATE Exit code: 3221226540 Version: 1.0.0.5 Modules
| |||||||||||||||
| 2576 | net stop aow_drv | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2820 | C:\Windows\system32\net1 stop Tensafe | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2932 | netsh advfirewall firewall delete rule name=SINKI | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "C:\Users\admin\Desktop\SINKI_ANTIBAN_PRIVATE.vmp\SINKI ANTIBAN PRIVATE.vmp.exe" | C:\Users\admin\Desktop\SINKI_ANTIBAN_PRIVATE.vmp\SINKI ANTIBAN PRIVATE.vmp.exe | explorer.exe | ||||||||||||
User: admin Company: sinkicheat.com Integrity Level: HIGH Description: SINKI ANTIBAN PRIVATE Exit code: 0 Version: 1.0.0.5 Modules
| |||||||||||||||
| 2960 | netsh advfirewall firewall set rule name=Gameloop new enable=yes | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3132 | C:\Windows\system32\net1 stop aow_drv | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 009
Read events
803
Write events
206
Delete events
0
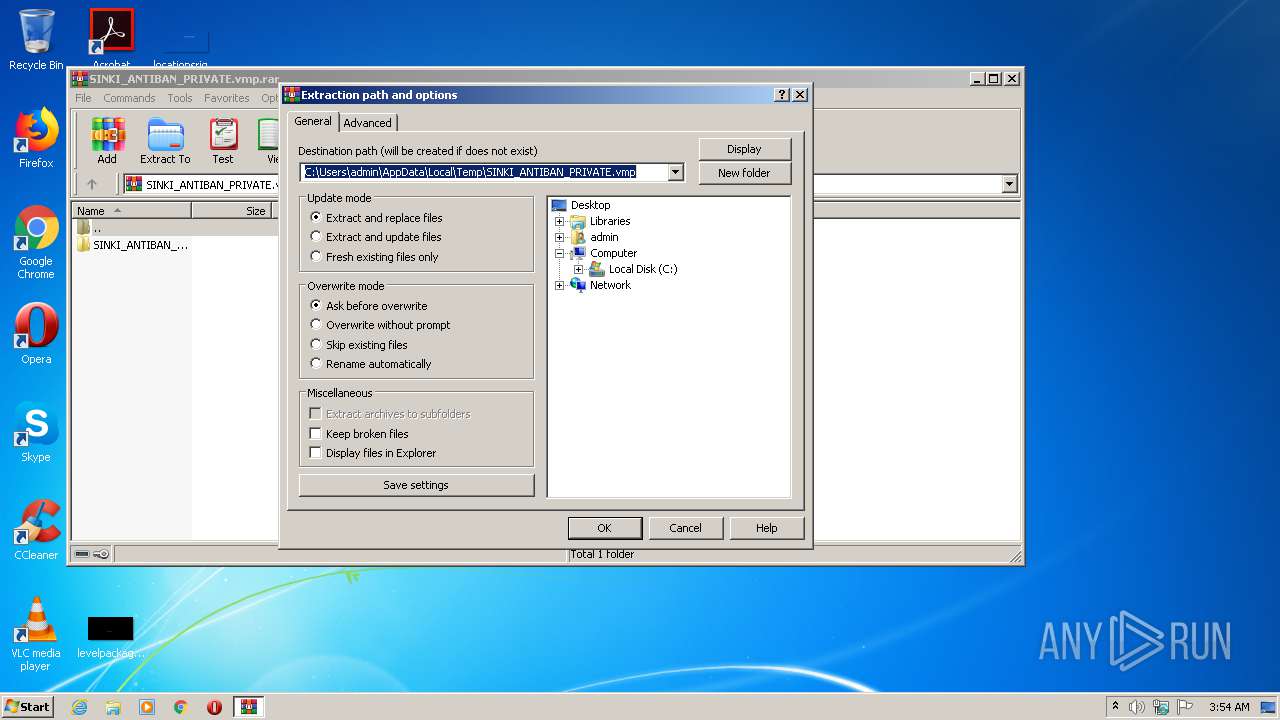
Modification events
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SINKI_ANTIBAN_PRIVATE.vmp.rar | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3144) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
23
Suspicious files
0
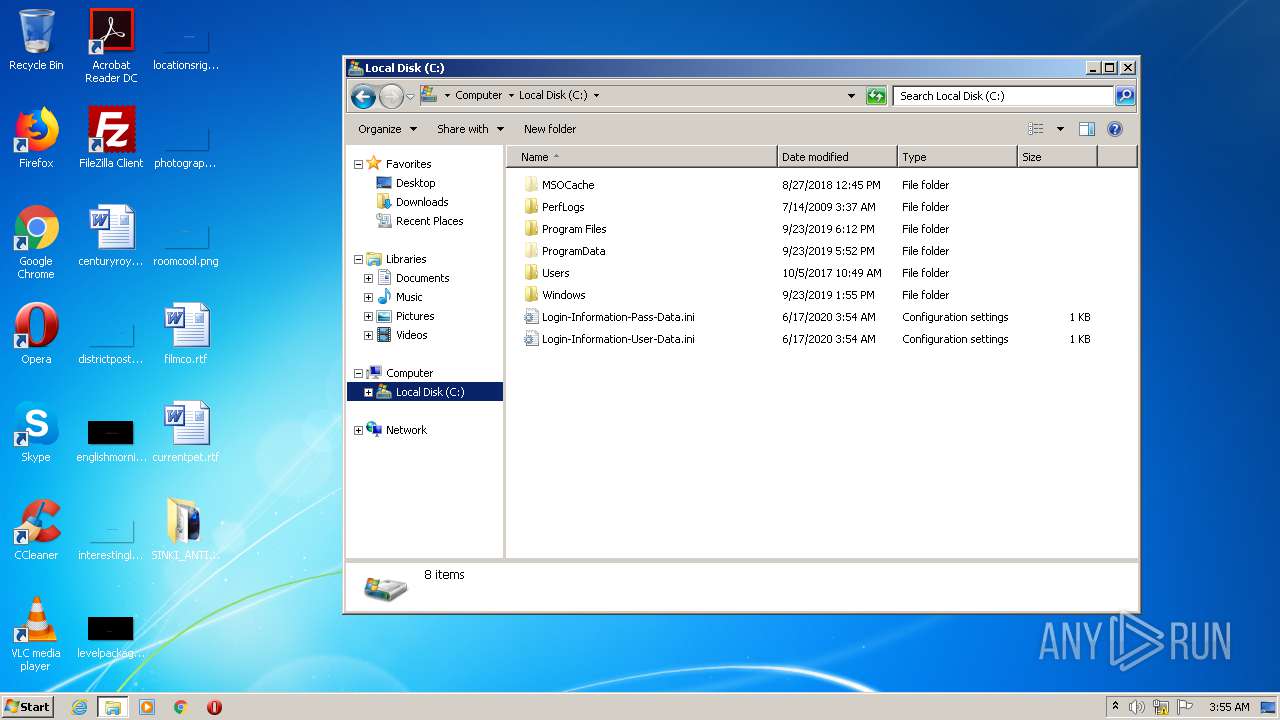
Text files
2
Unknown types
0
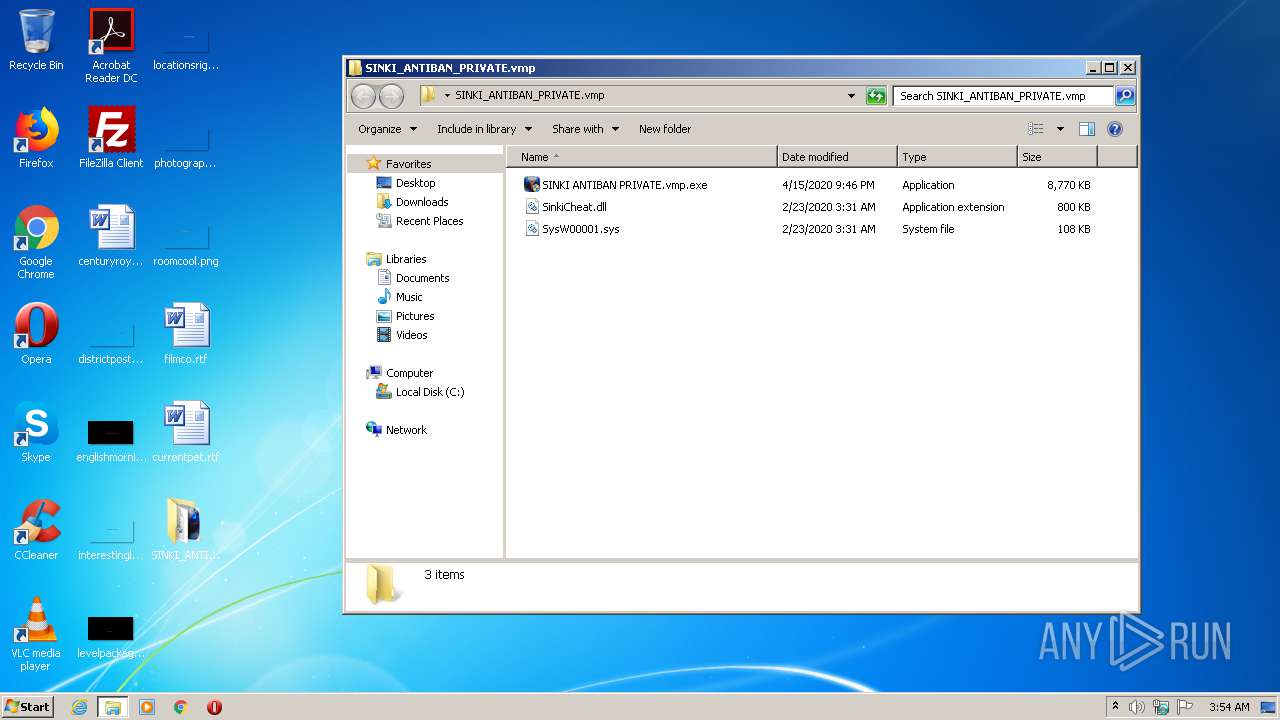
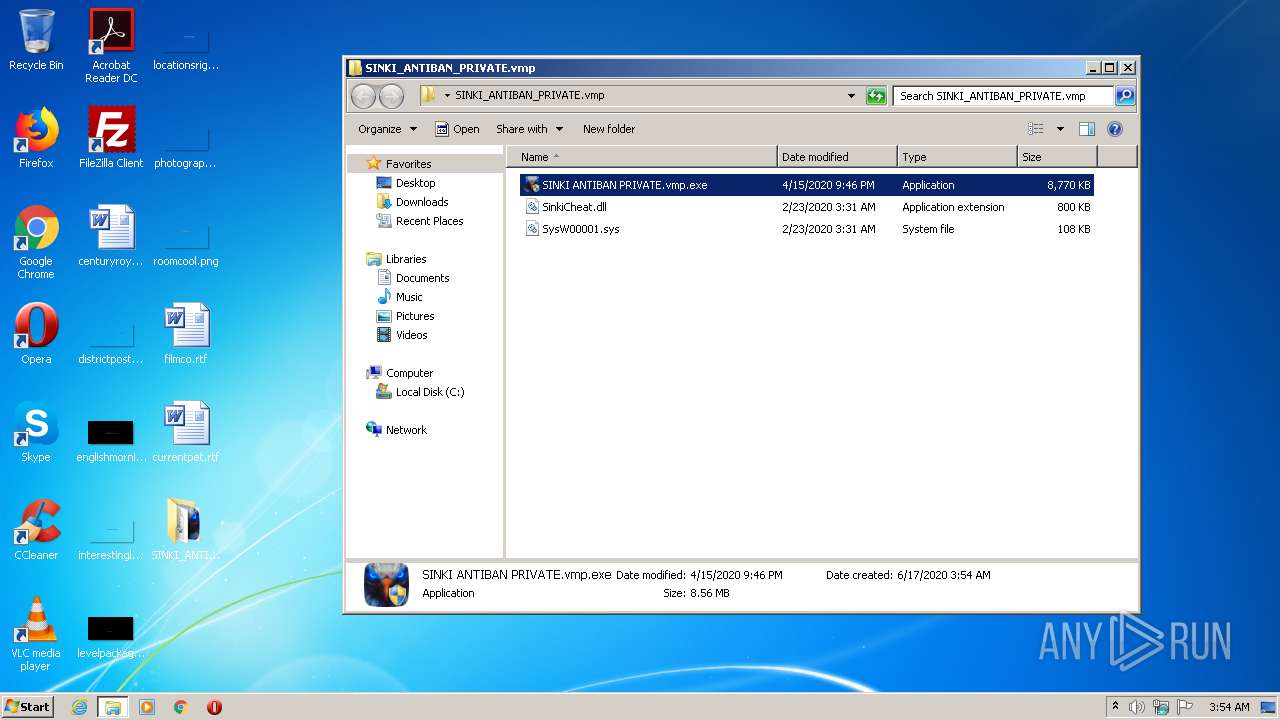
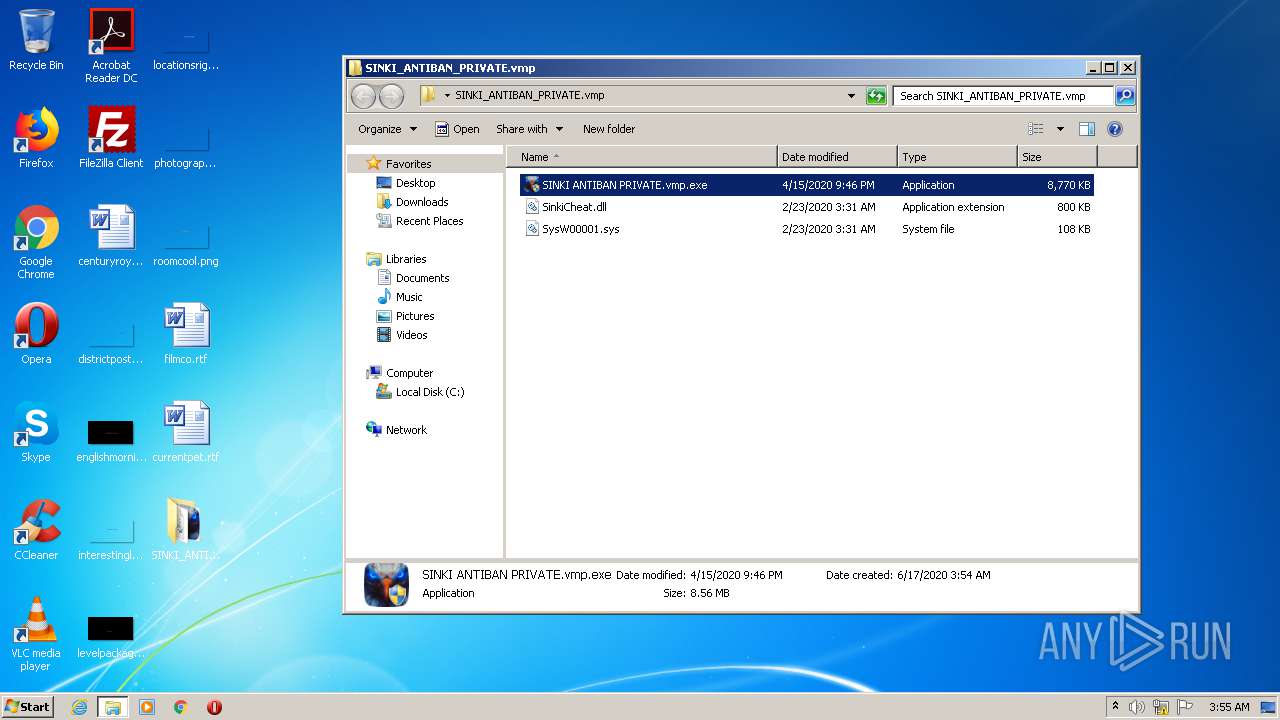
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | WinRAR.exe | C:\Users\admin\Desktop\SINKI_ANTIBAN_PRIVATE.vmp\SinkiCheat.dll | executable | |
MD5:— | SHA256:— | |||
| 3144 | WinRAR.exe | C:\Users\admin\Desktop\SINKI_ANTIBAN_PRIVATE.vmp\SINKI ANTIBAN PRIVATE.vmp.exe | executable | |
MD5:— | SHA256:— | |||
| 3144 | WinRAR.exe | C:\Users\admin\Desktop\SINKI_ANTIBAN_PRIVATE.vmp\SysW00001.sys | executable | |
MD5:— | SHA256:— | |||
| 2940 | SINKI ANTIBAN PRIVATE.vmp.exe | C:\Login-Information-User-Data.ini | text | |
MD5:— | SHA256:— | |||
| 2940 | SINKI ANTIBAN PRIVATE.vmp.exe | C:\Windows\Help\Windows\IndexStore\advapi32res.dll | executable | |
MD5:— | SHA256:— | |||
| 2940 | SINKI ANTIBAN PRIVATE.vmp.exe | C:\Windows\Help\Windows\IndexStore\DMAppsRes.dll | executable | |
MD5:— | SHA256:— | |||
| 2940 | SINKI ANTIBAN PRIVATE.vmp.exe | C:\Login-Information-Pass-Data.ini | text | |
MD5:— | SHA256:— | |||
| 2940 | SINKI ANTIBAN PRIVATE.vmp.exe | C:\Windows\Help\Windows\IndexStore\hnetmon.dll | executable | |
MD5:— | SHA256:— | |||
| 2940 | SINKI ANTIBAN PRIVATE.vmp.exe | C:\Windows\Help\Windows\IndexStore\WinSCardX86.dll | executable | |
MD5:— | SHA256:— | |||
| 2940 | SINKI ANTIBAN PRIVATE.vmp.exe | C:\Windows\Help\Windows\IndexStore\aeevts.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report