| File name: | vw0rm 18.36.vbs |
| Full analysis: | https://app.any.run/tasks/f2bfadfd-8f8c-4321-8940-9f93aaa2f0db |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 18:18:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 356A56EAA98CCC1C6C4ABB767193F1EA |
| SHA1: | 75A60386CFC2C2E75E5D0C5C3CB764EB9800B0FF |
| SHA256: | 047ECC4033BCCE6F2E811A36D2A945D23AACFBCB390E1BED7FEE904DD8FF694A |
| SSDEEP: | 96:5EABpaDSKzGIRgRA+g0zaMxBU6rvbstLy2Ll3lnxmXB:5pXS/B50zlvmLDGXB |
MALICIOUS
Writes to a start menu file
- WScript.exe (PID: 2636)
Uses Task Scheduler to run other applications
- WScript.exe (PID: 2636)
Changes the autorun value in the registry
- WScript.exe (PID: 2636)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1336)
SUSPICIOUS
Reads Internet Cache Settings
- WScript.exe (PID: 2636)
Creates files in the user directory
- WScript.exe (PID: 2636)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
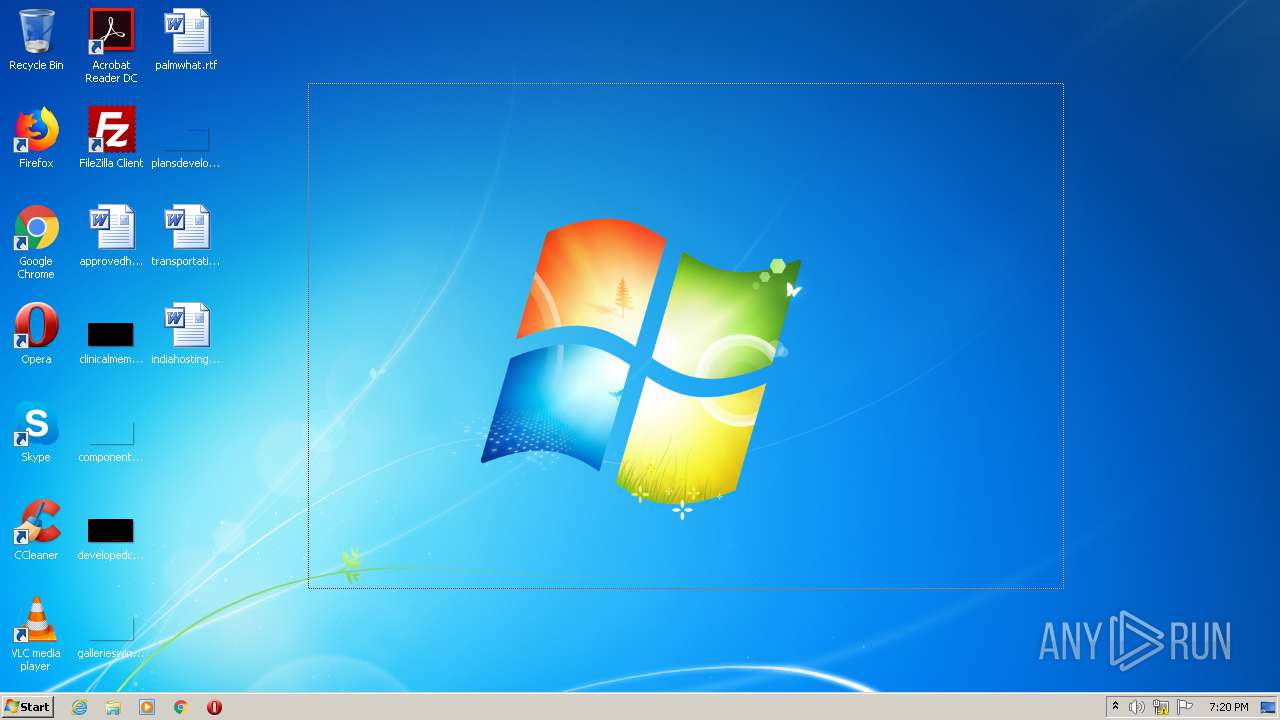
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1336 | "C:\Windows\System32\schtasks.exe" /create /sc minute /mo 1 /tn Skype /tr "C:\Users\admin\AppData\Local\Temp\vw0rm 18.36.vbs | C:\Windows\System32\schtasks.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\vw0rm 18.36.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
122
Read events
111
Write events
11
Delete events
0
Modification events
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER |
| Operation: | write | Name: | vw0rm |
Value: FALSE | |||
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 5DGTPX311A |
Value: "C:\Users\admin\AppData\Local\Temp\vw0rm 18.36.vbs" | |||
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2636) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2636 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\vw0rm 18.36.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2636 | WScript.exe | 194.5.98.46:4404 | xbu4vv8ayujduoon3a.ddns.net | — | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xbu4vv8ayujduoon3a.ddns.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |