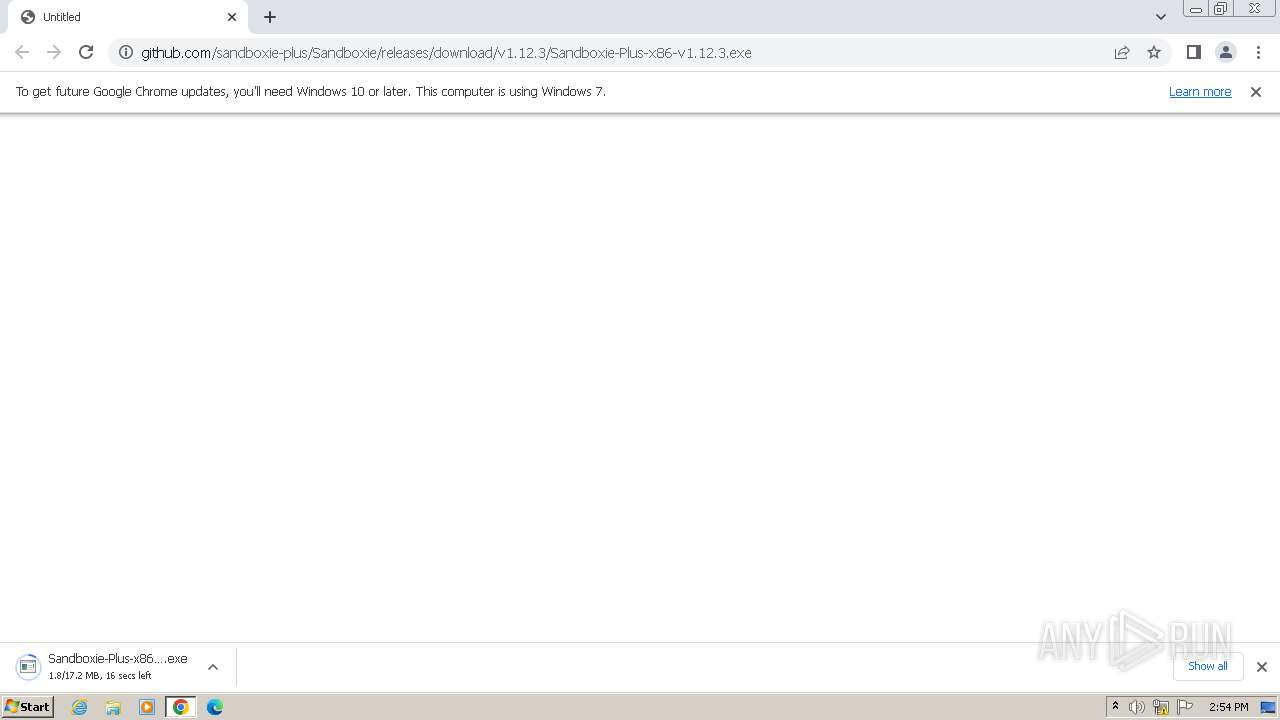
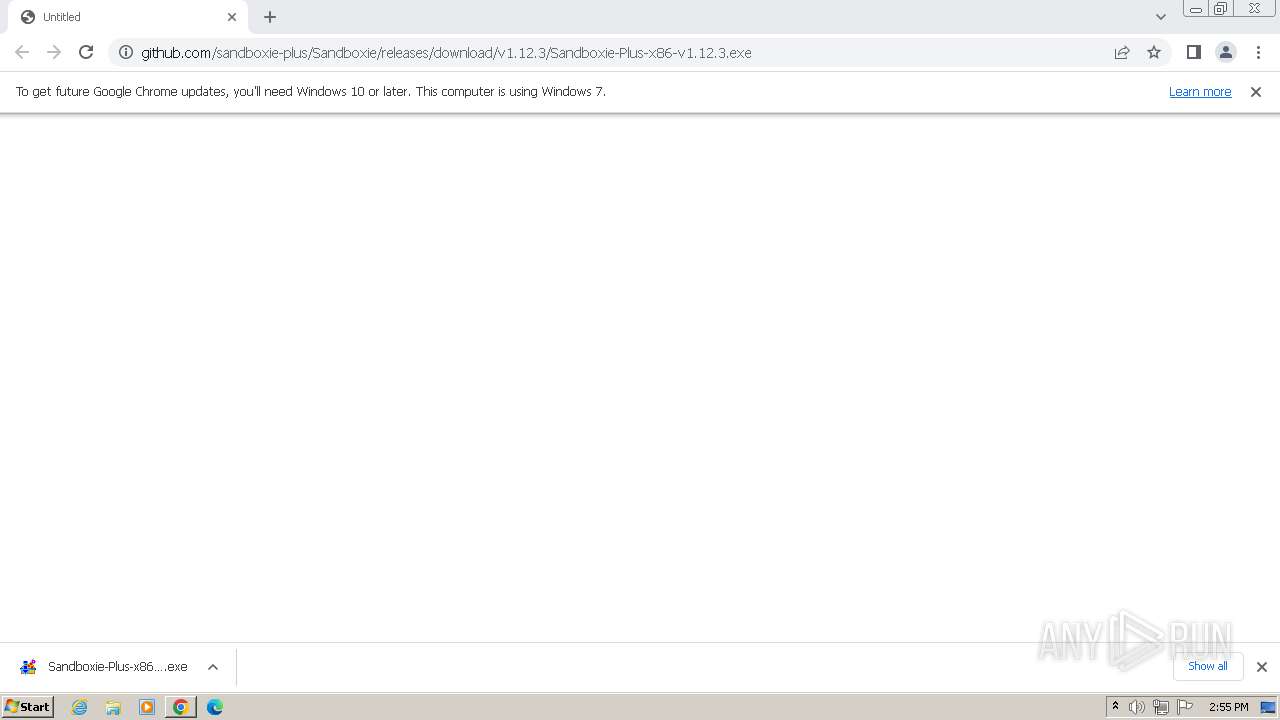
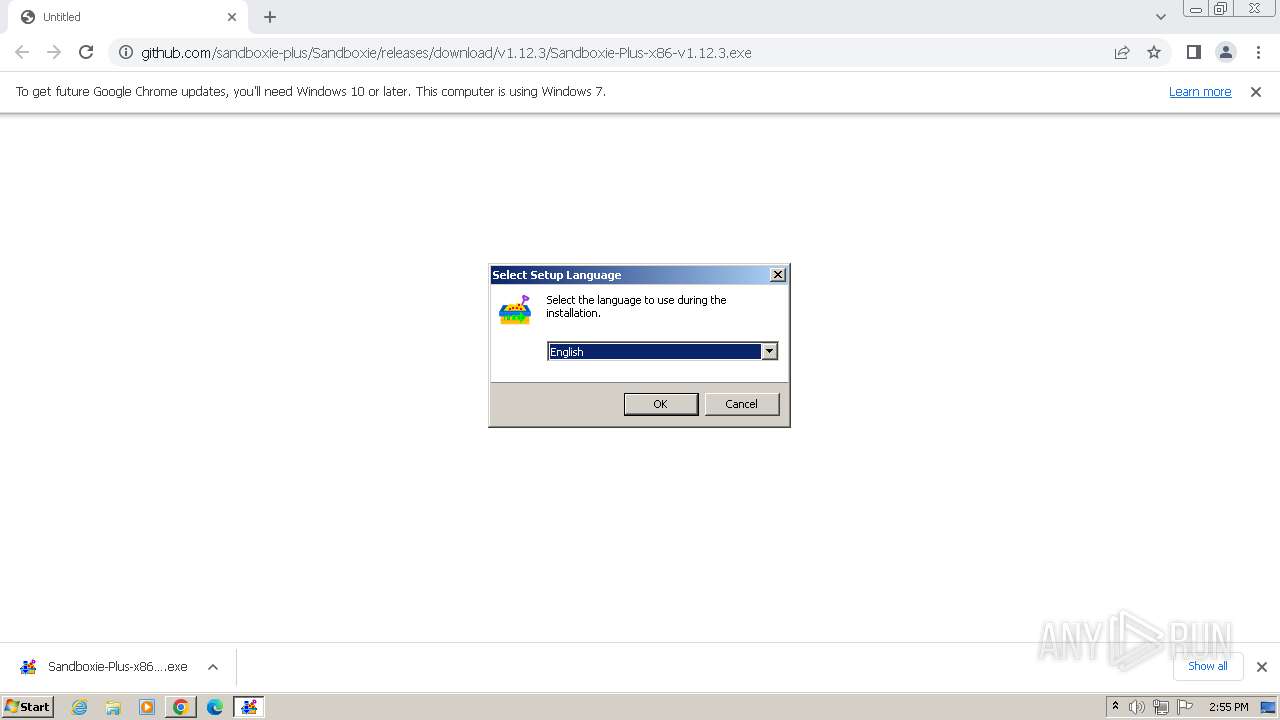
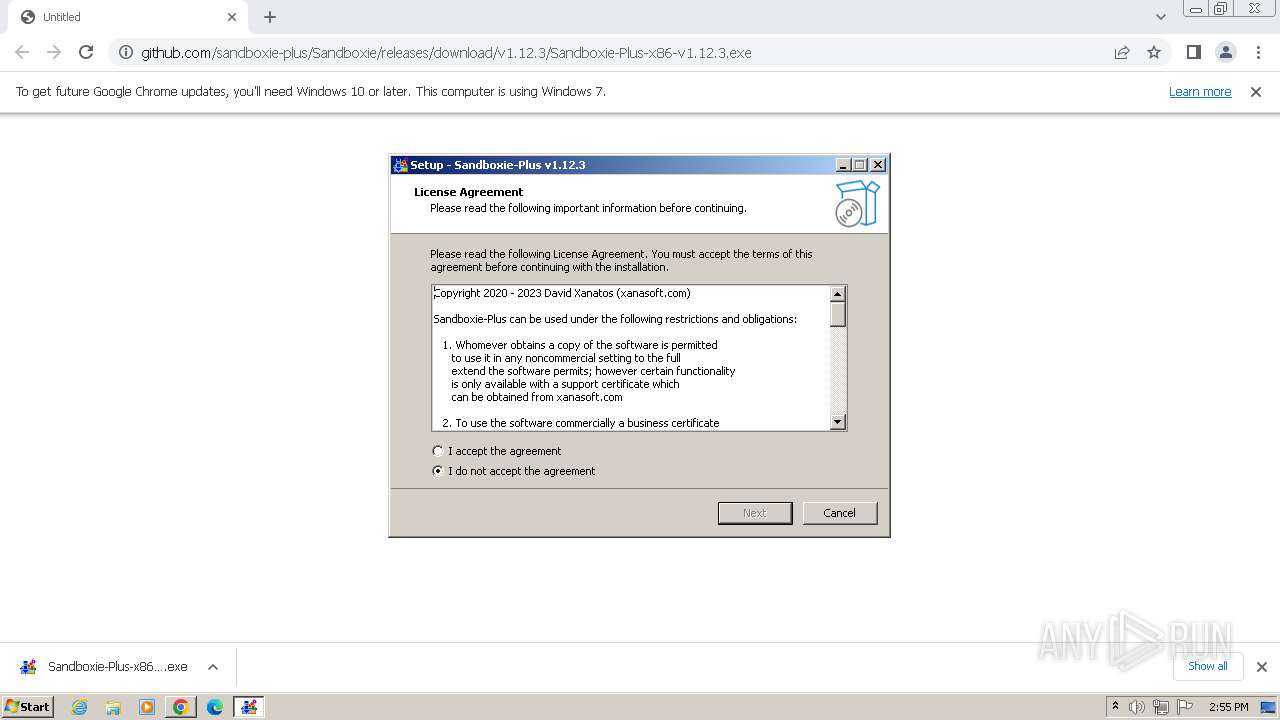
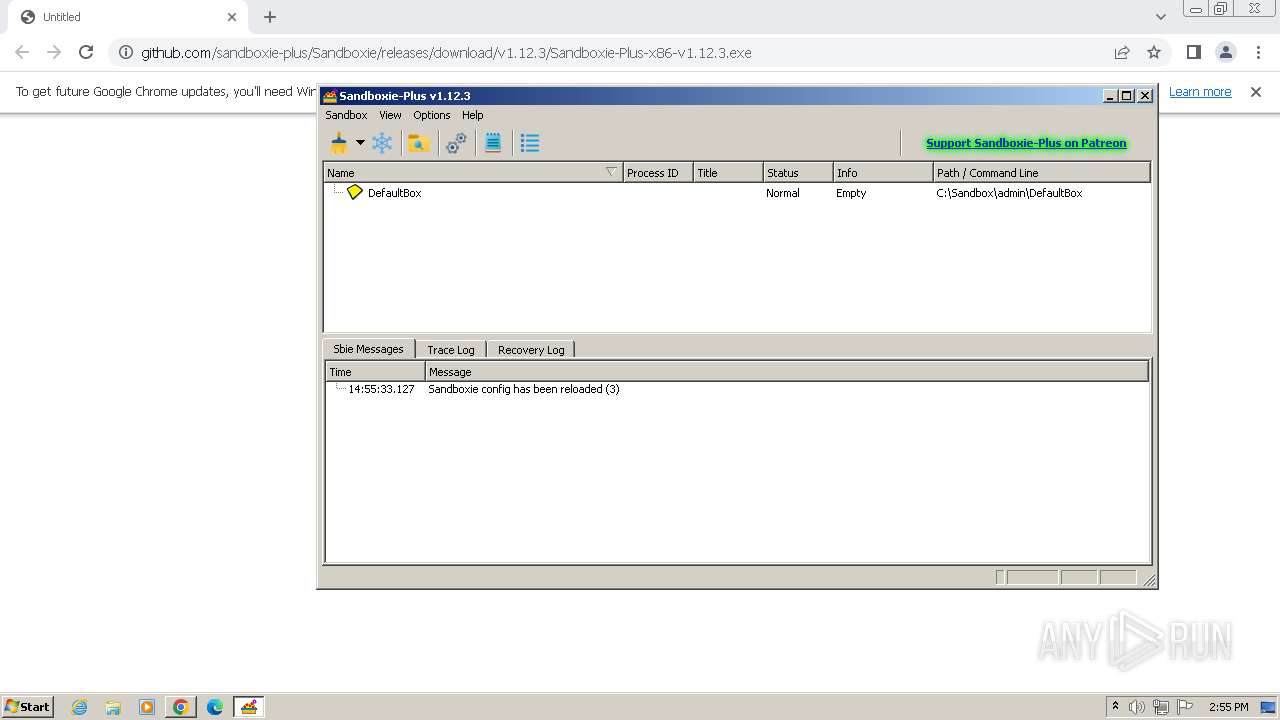
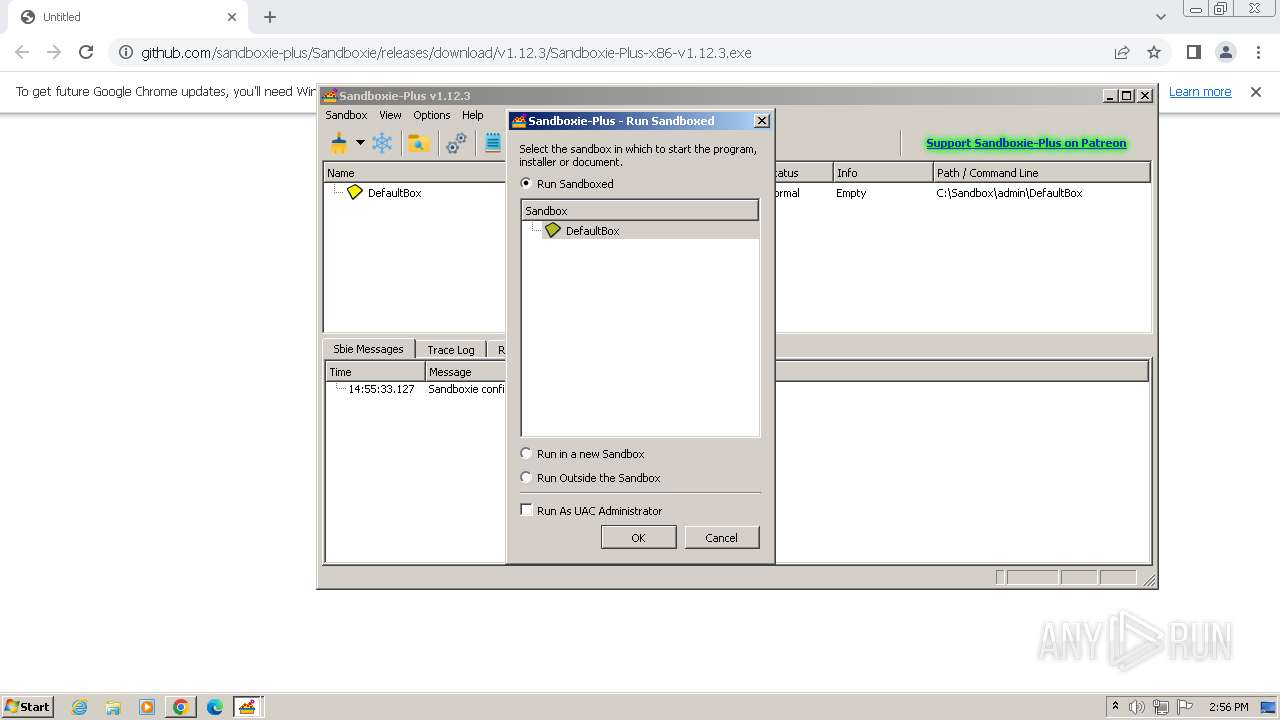
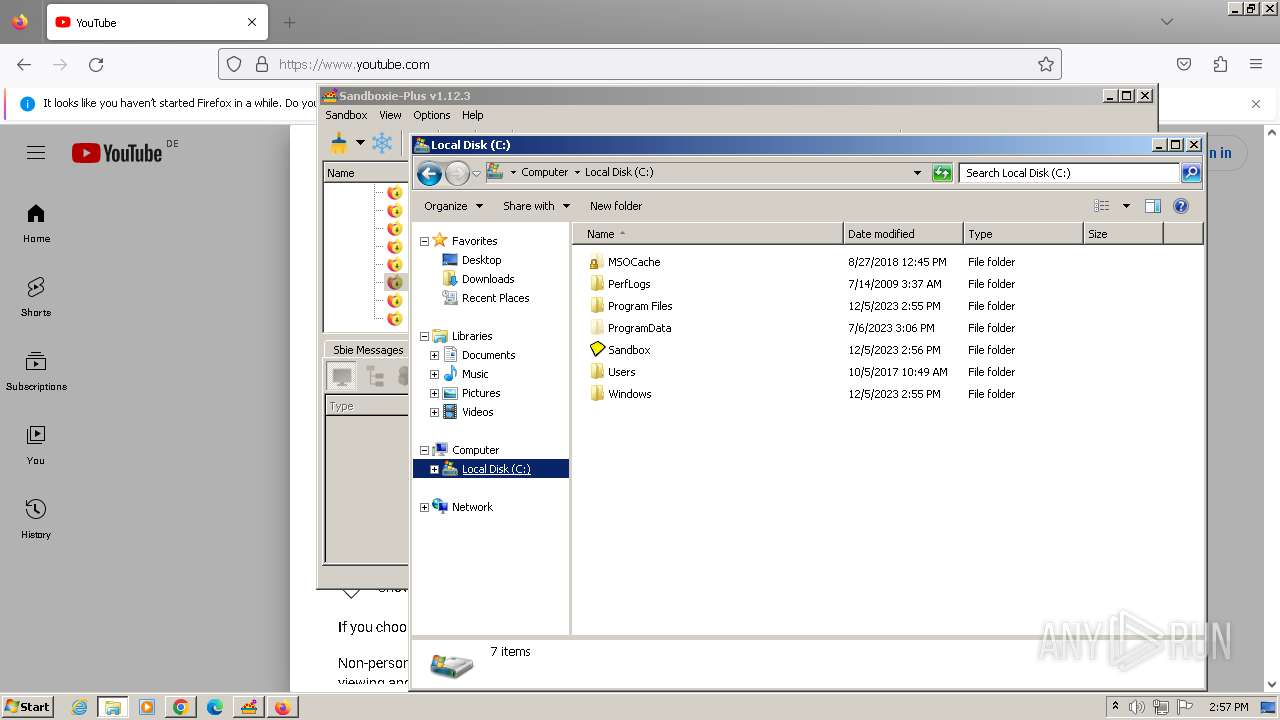
| URL: | https://github.com/sandboxie-plus/Sandboxie/releases/download/v1.12.3/Sandboxie-Plus-x86-v1.12.3.exe |
| Full analysis: | https://app.any.run/tasks/5915603d-de9b-45e3-9012-98c358ee44dd |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2023, 14:54:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D634D0D7F4DA0F6BD8A513F41DF85555 |
| SHA1: | 223E5B936BAD43E96FA33A3333E592DCB32C90E9 |
| SHA256: | 047BB4756C8B00876AE14216758E18BD9C2A241C588A93B8175A2E997EB76E9B |
| SSDEEP: | 3:N8tEdmELxKdM674KkCmOpxHbpEyY4An:2uwi9CFsOnp/YNn |
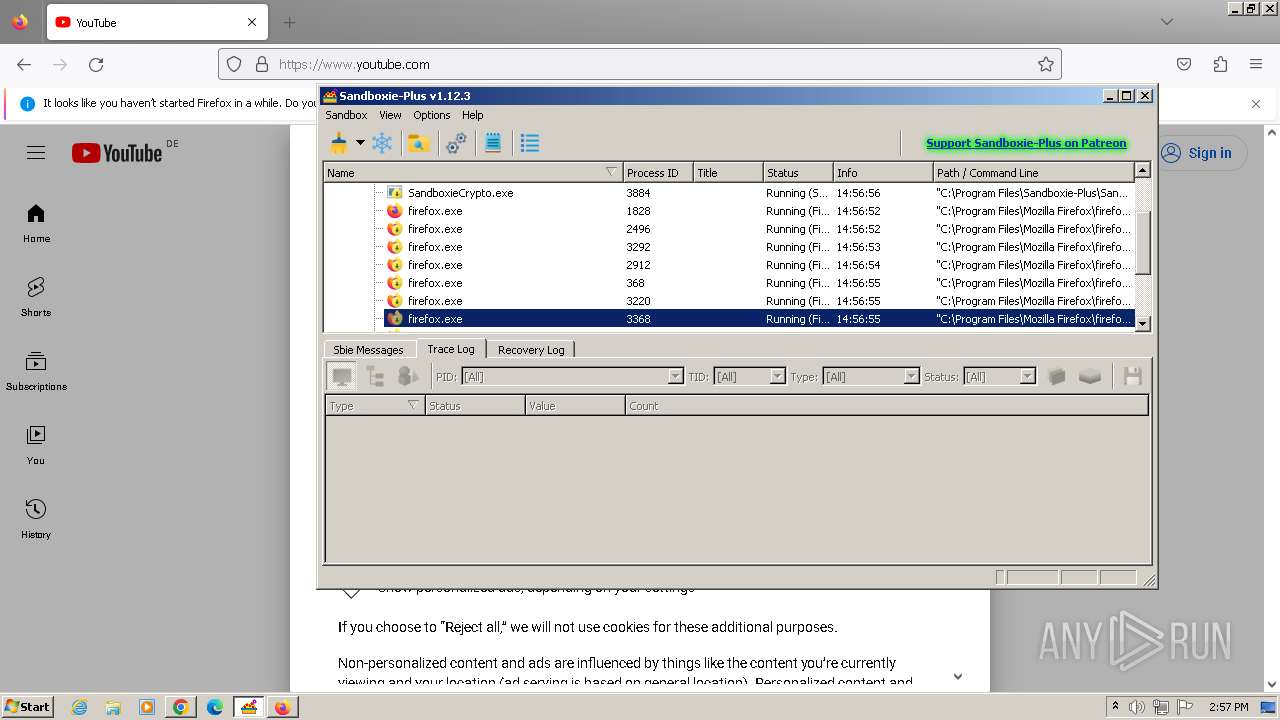
MALICIOUS
Drops the executable file immediately after the start
- Sandboxie-Plus-x86-v1.12.3.exe (PID: 2392)
- Sandboxie-Plus-x86-v1.12.3.exe (PID: 3020)
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
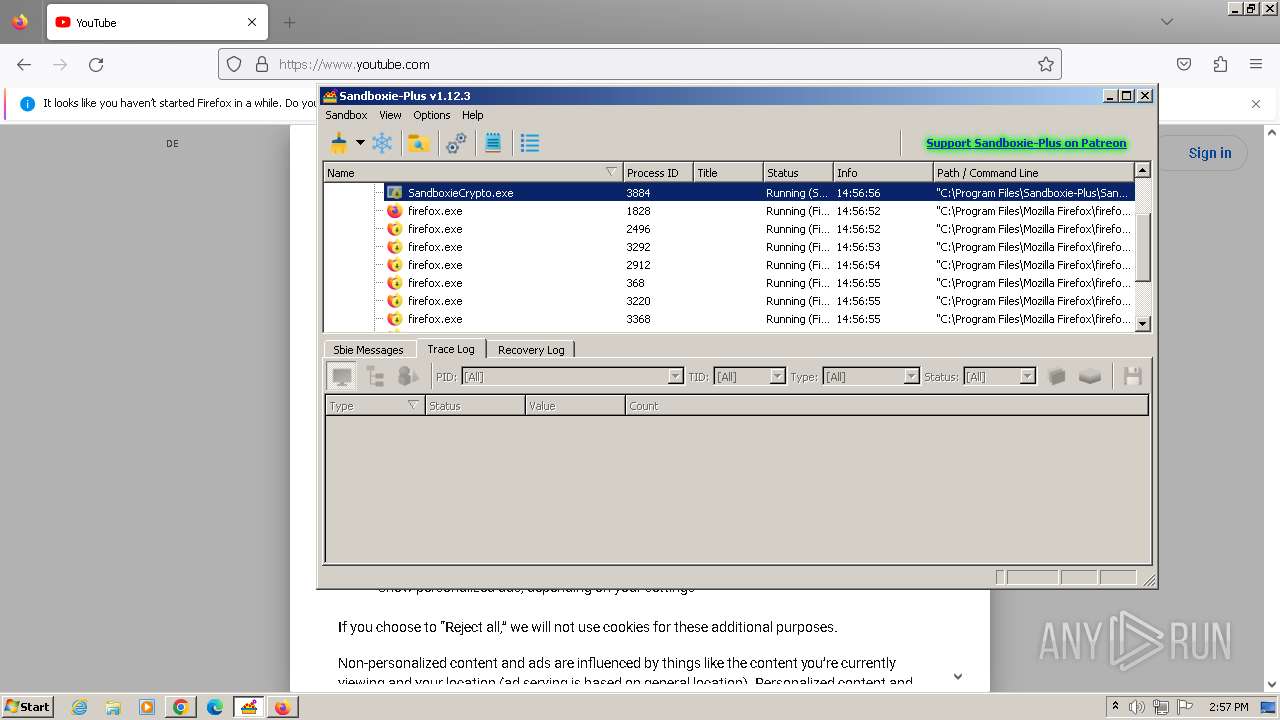
Creates a writable file in the system directory
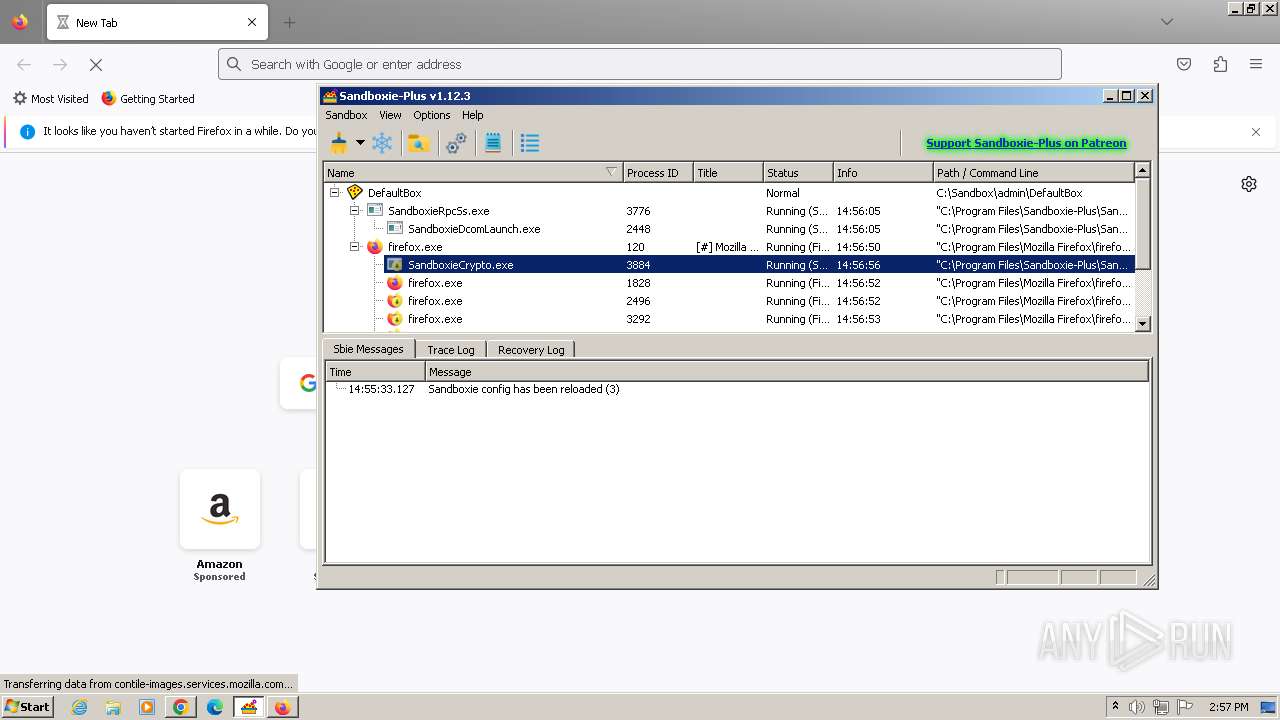
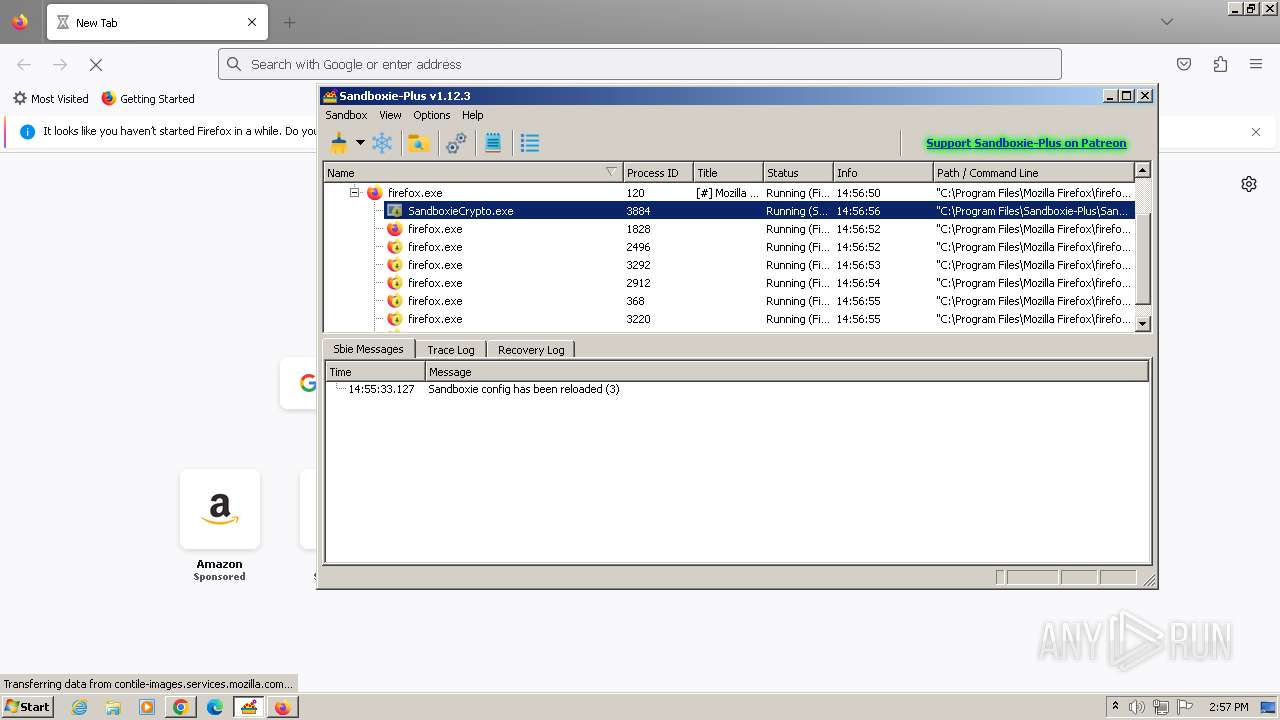
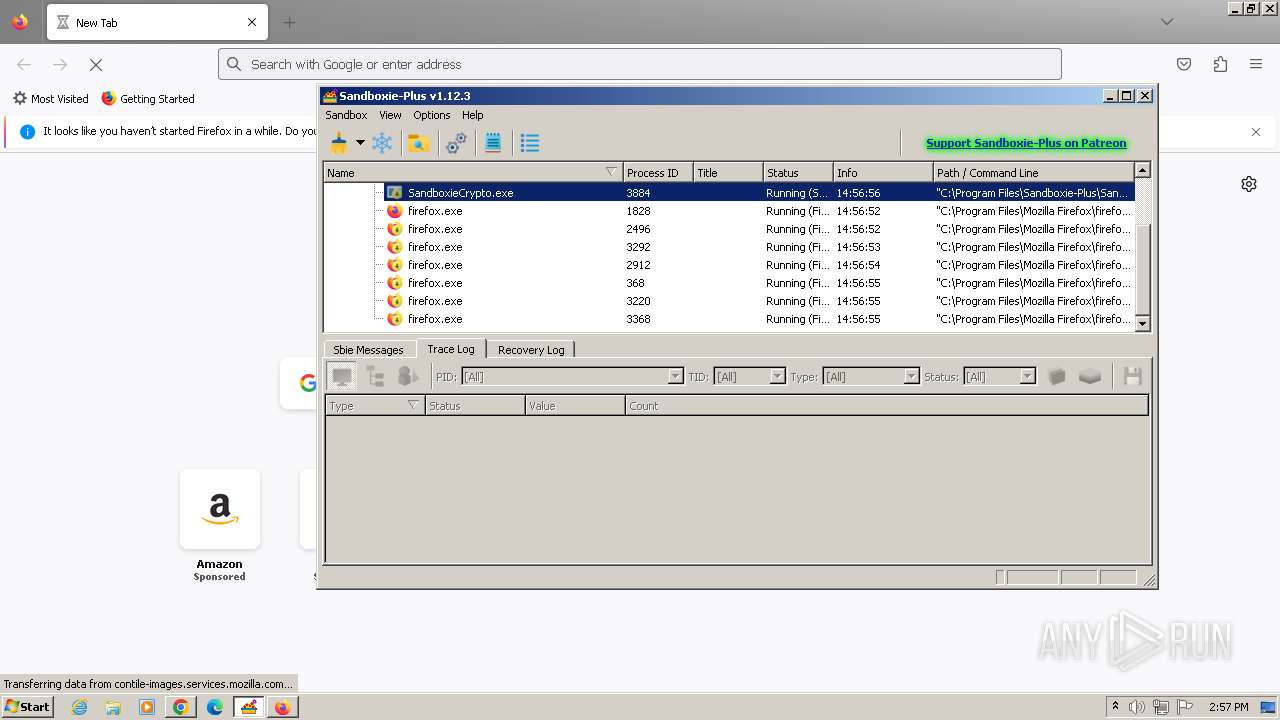
- SandboxieCrypto.exe (PID: 3884)
Actions looks like stealing of personal data
- SbieSvc.exe (PID: 3320)
Changes the autorun value in the registry
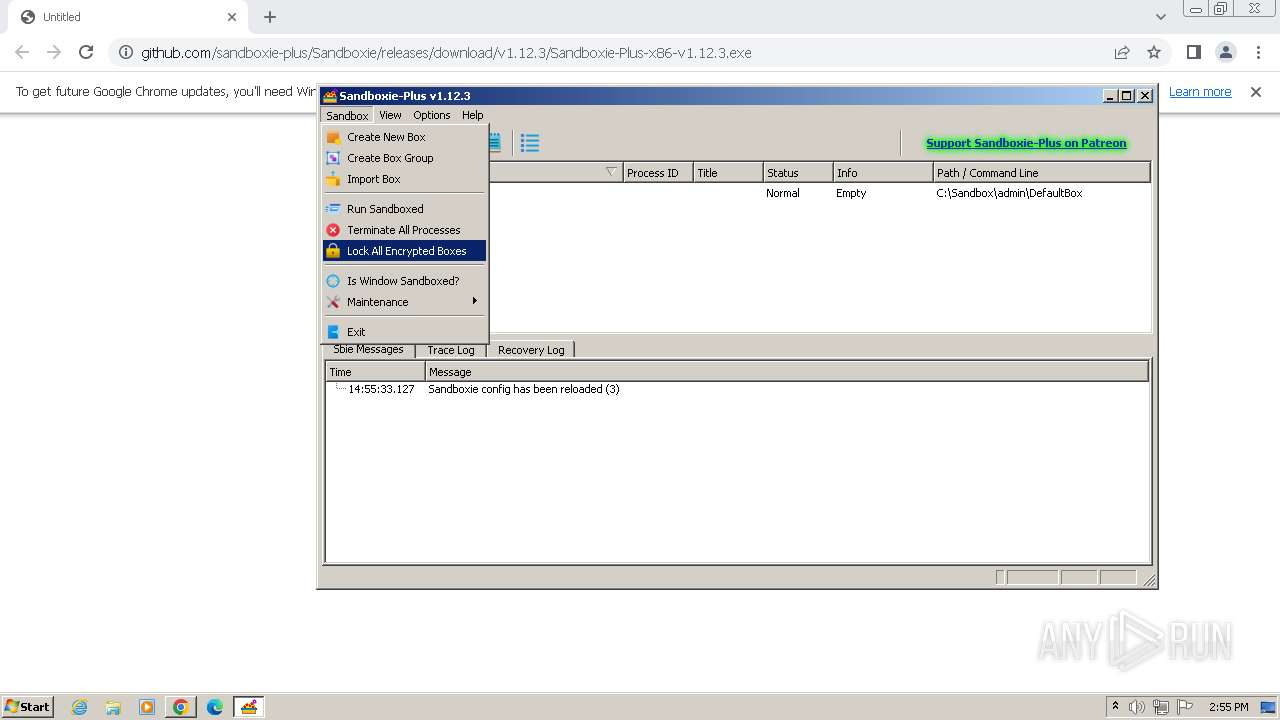
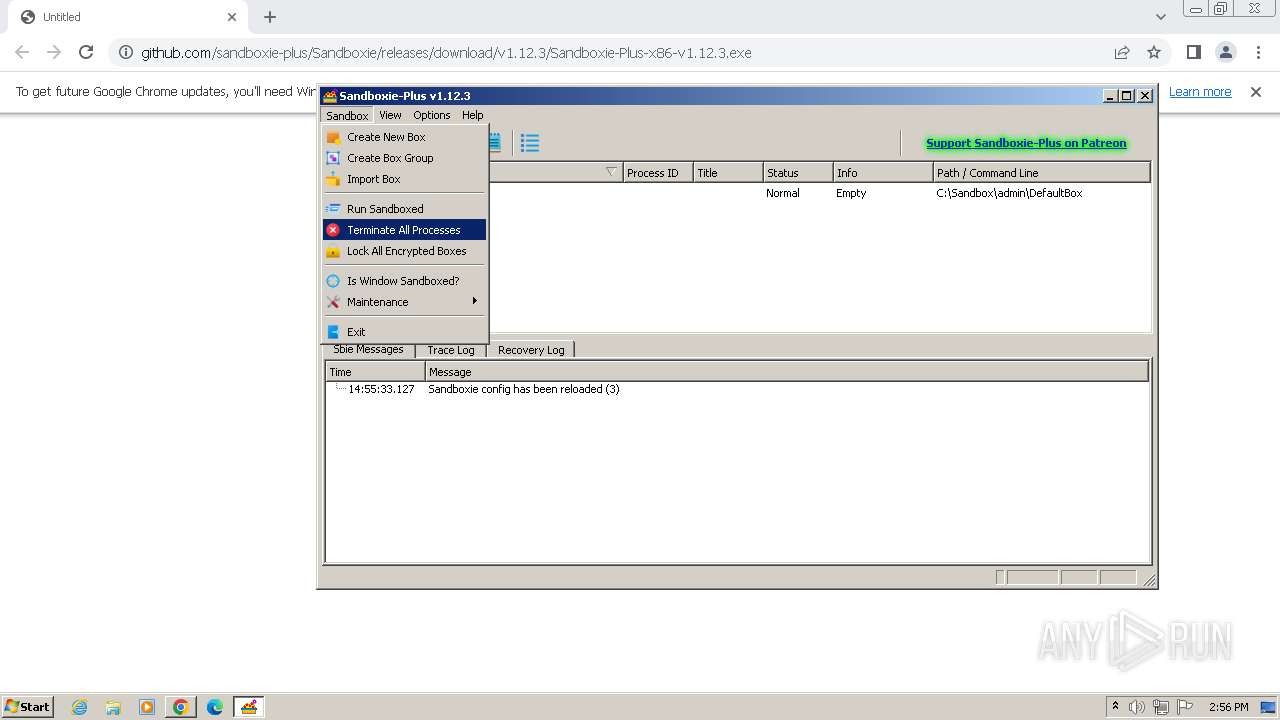
- SandMan.exe (PID: 3000)
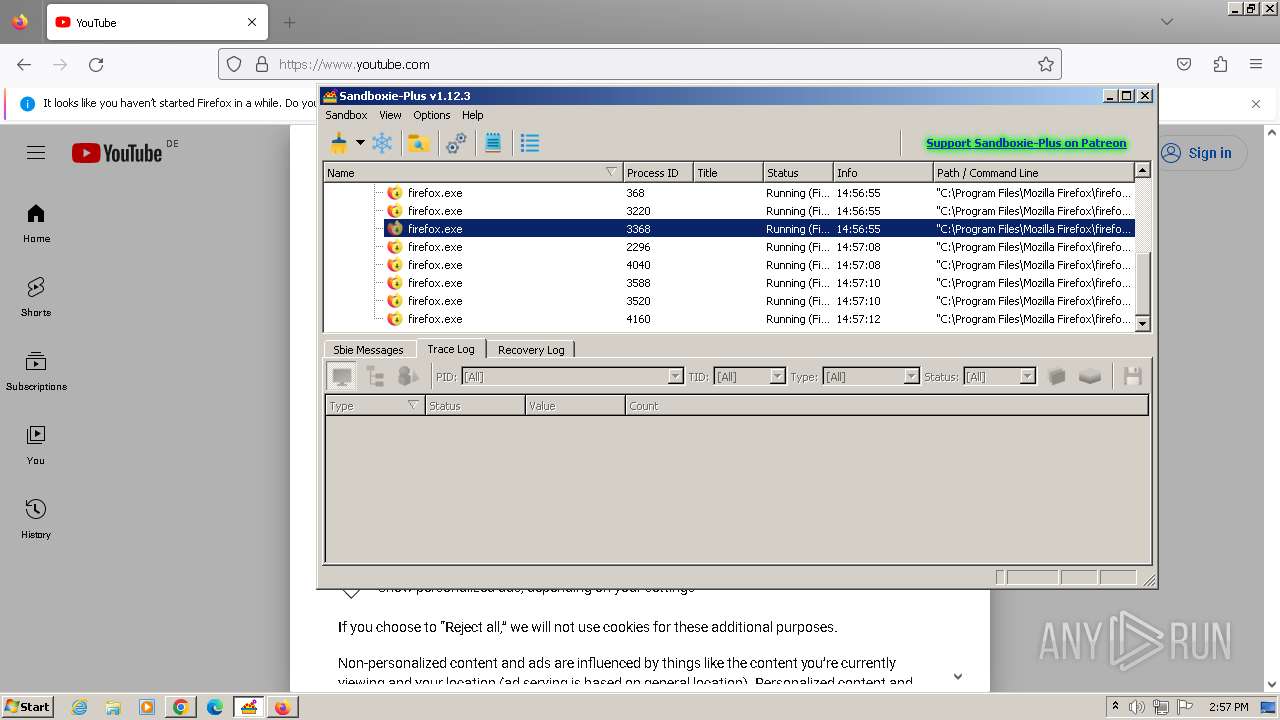
SUSPICIOUS
Reads the Windows owner or organization settings
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
Uses TASKKILL.EXE to kill process
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
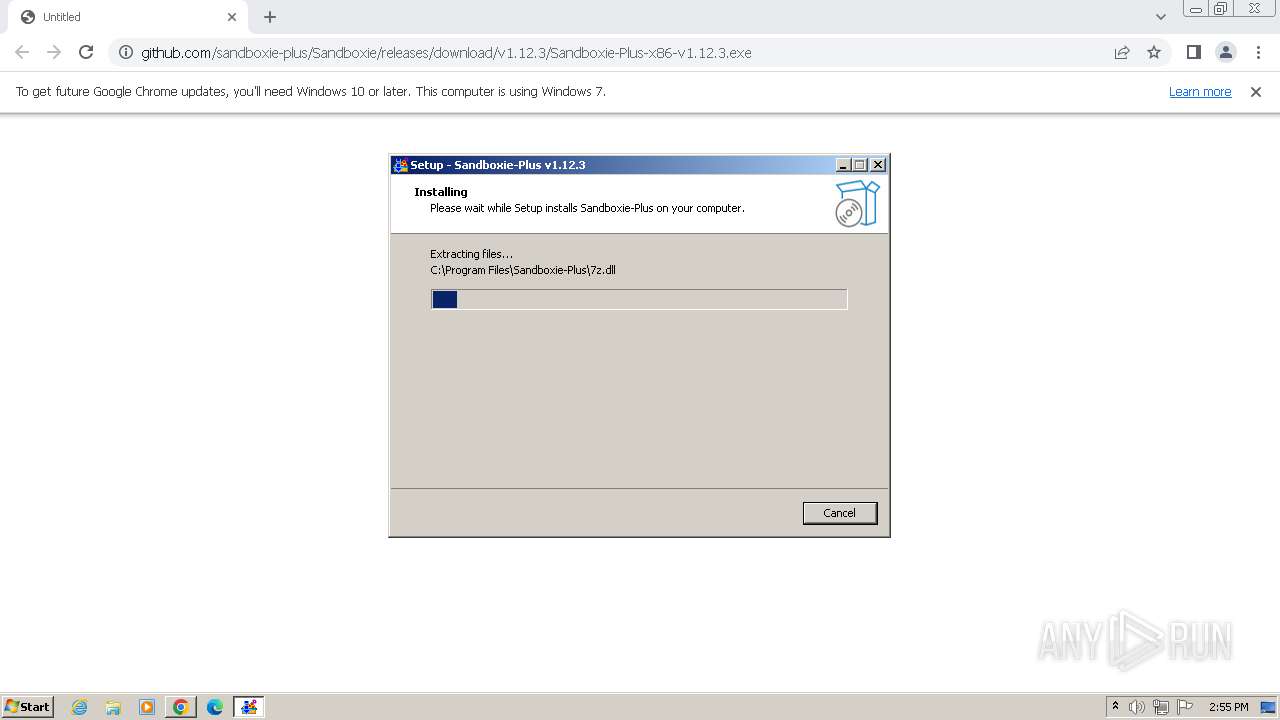
Drops 7-zip archiver for unpacking
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
The process drops C-runtime libraries
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
Process drops legitimate windows executable
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
- chrome.exe (PID: 1864)
Drops a system driver (possible attempt to evade defenses)
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
Reads settings of System Certificates
- UpdUtil.exe (PID: 2708)
- SandMan.exe (PID: 3000)
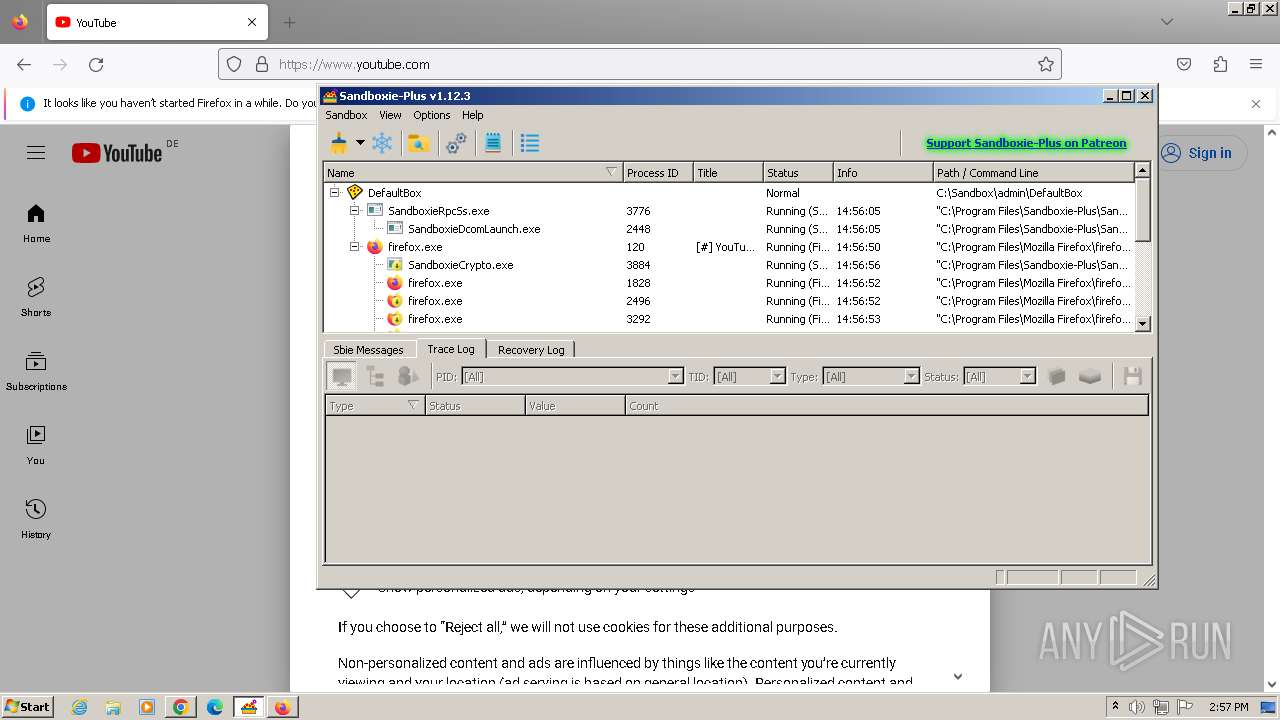
Executes as Windows Service
- SbieSvc.exe (PID: 3320)
Adds/modifies Windows certificates
- UpdUtil.exe (PID: 2708)
Reads the Internet Settings
- SandMan.exe (PID: 3000)
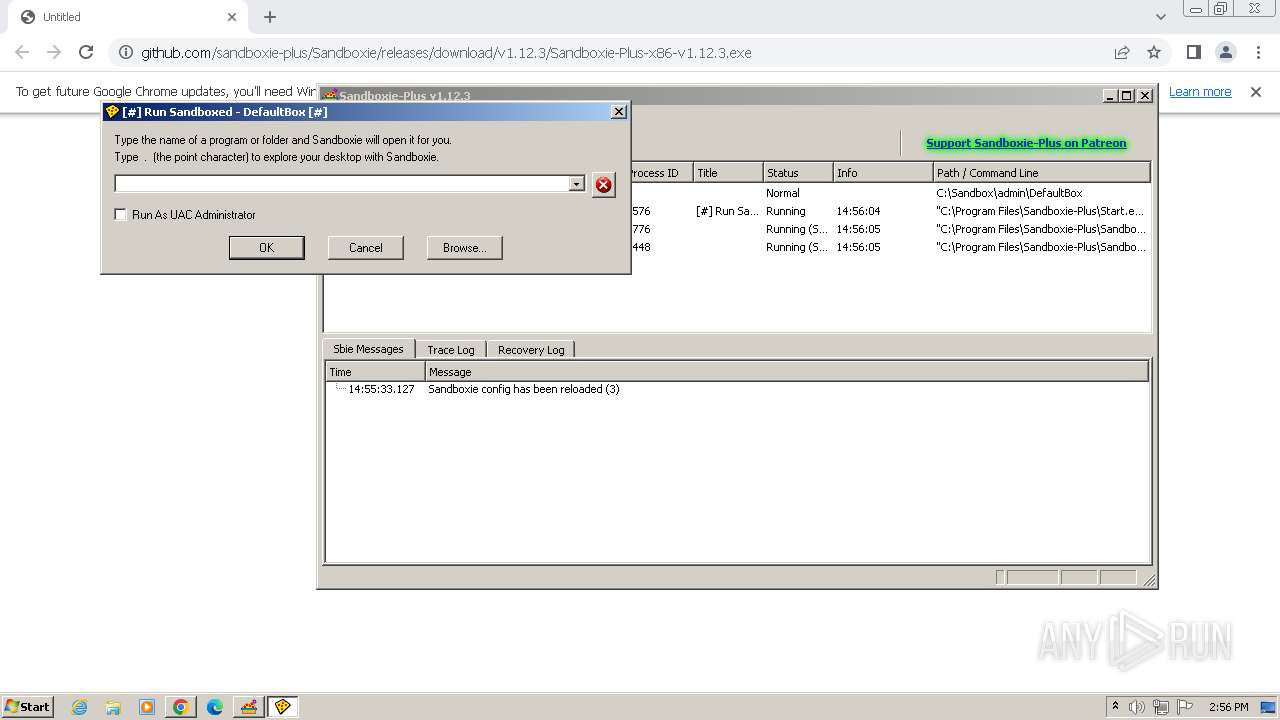
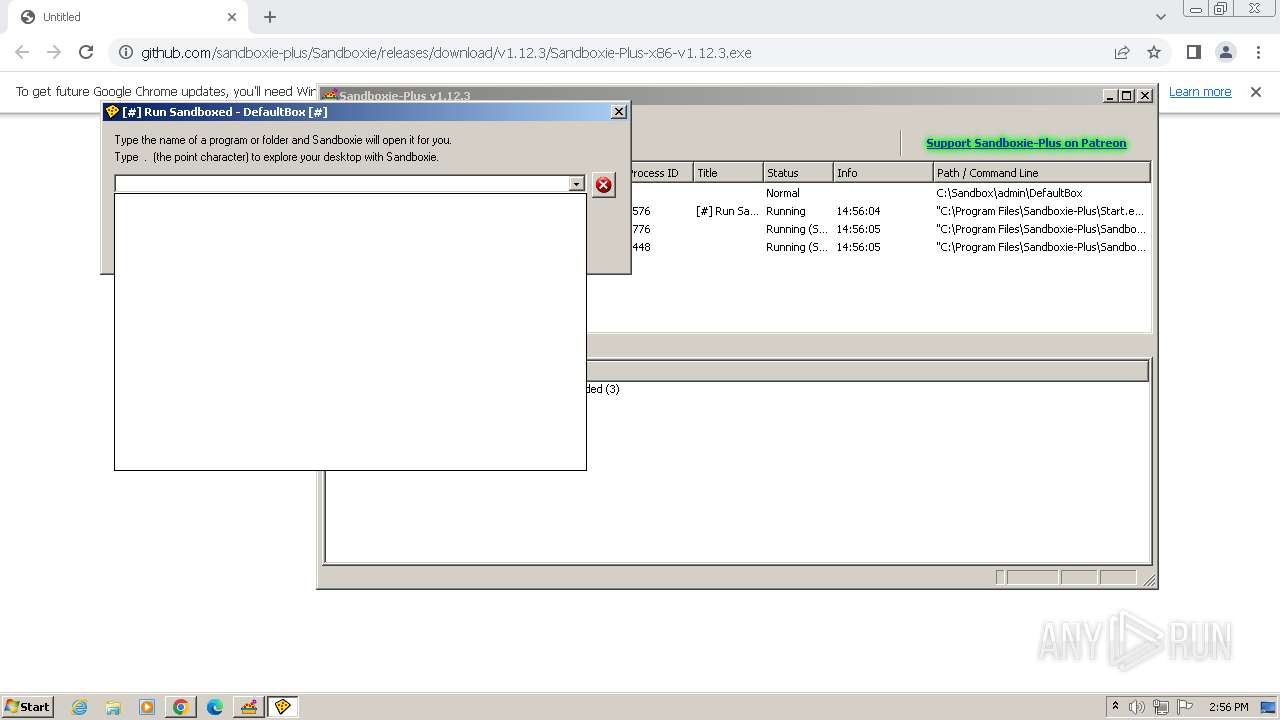
Application launched itself
- SbieSvc.exe (PID: 3320)
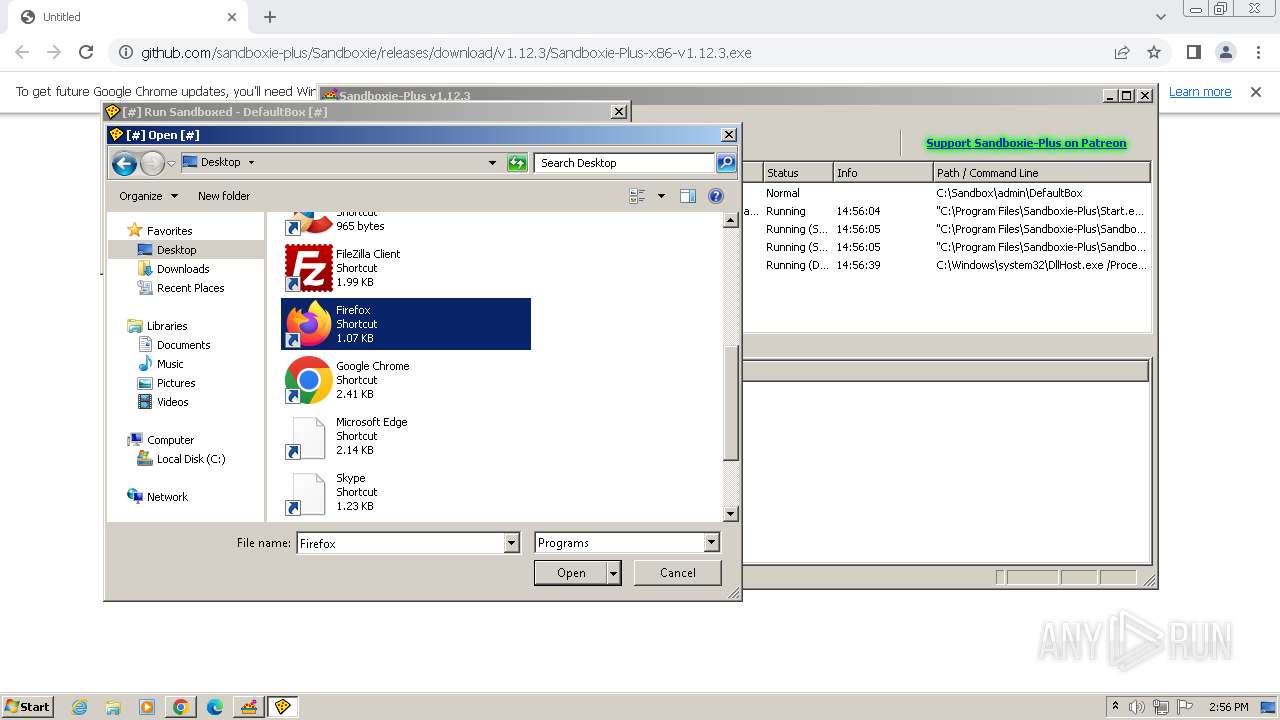
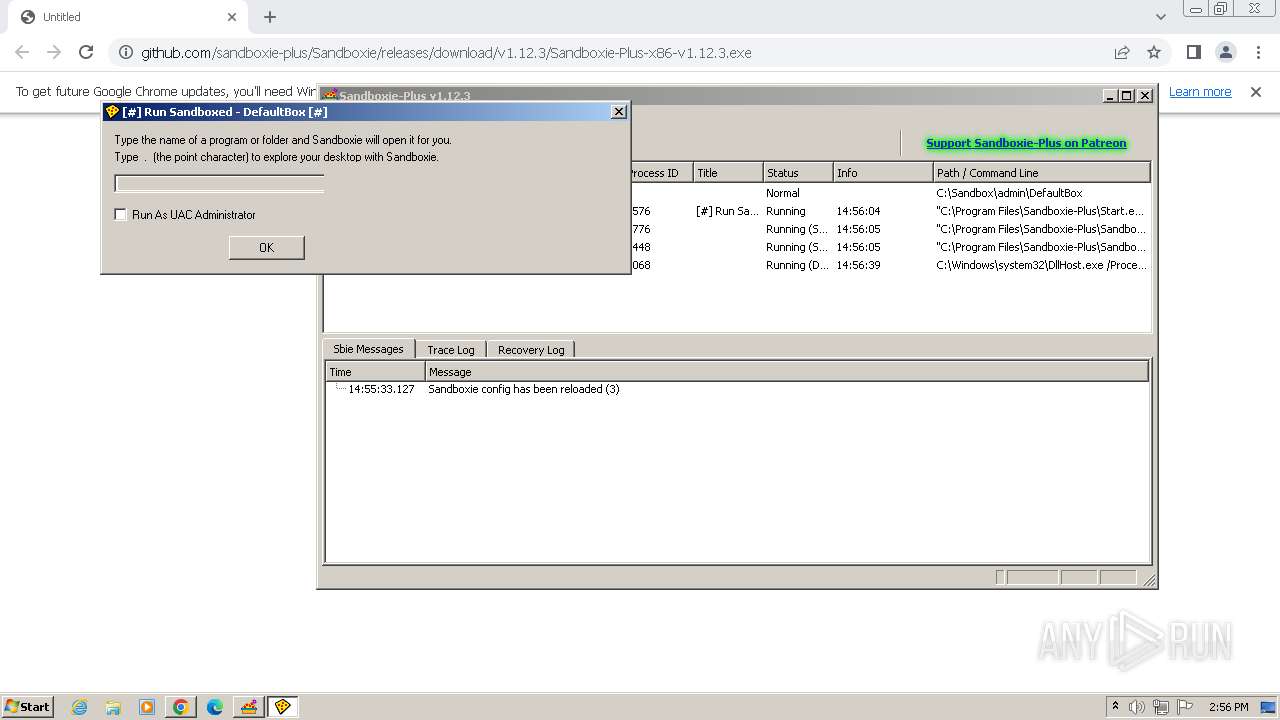
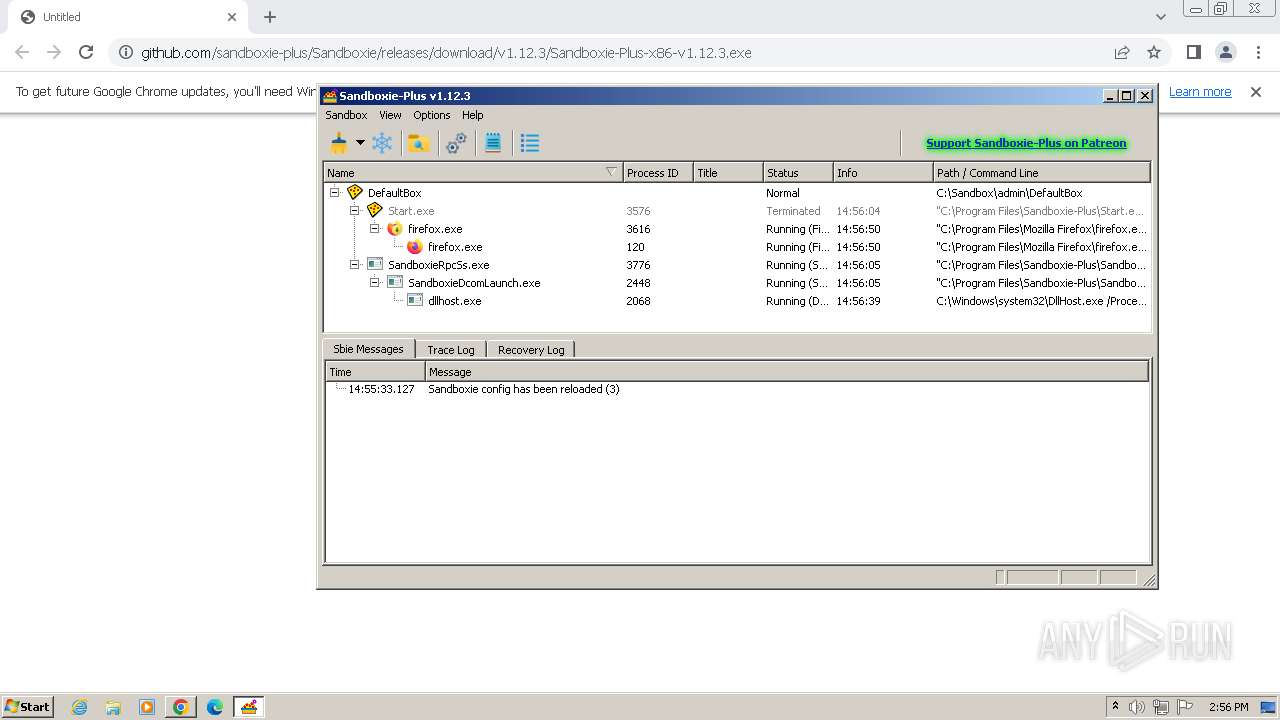
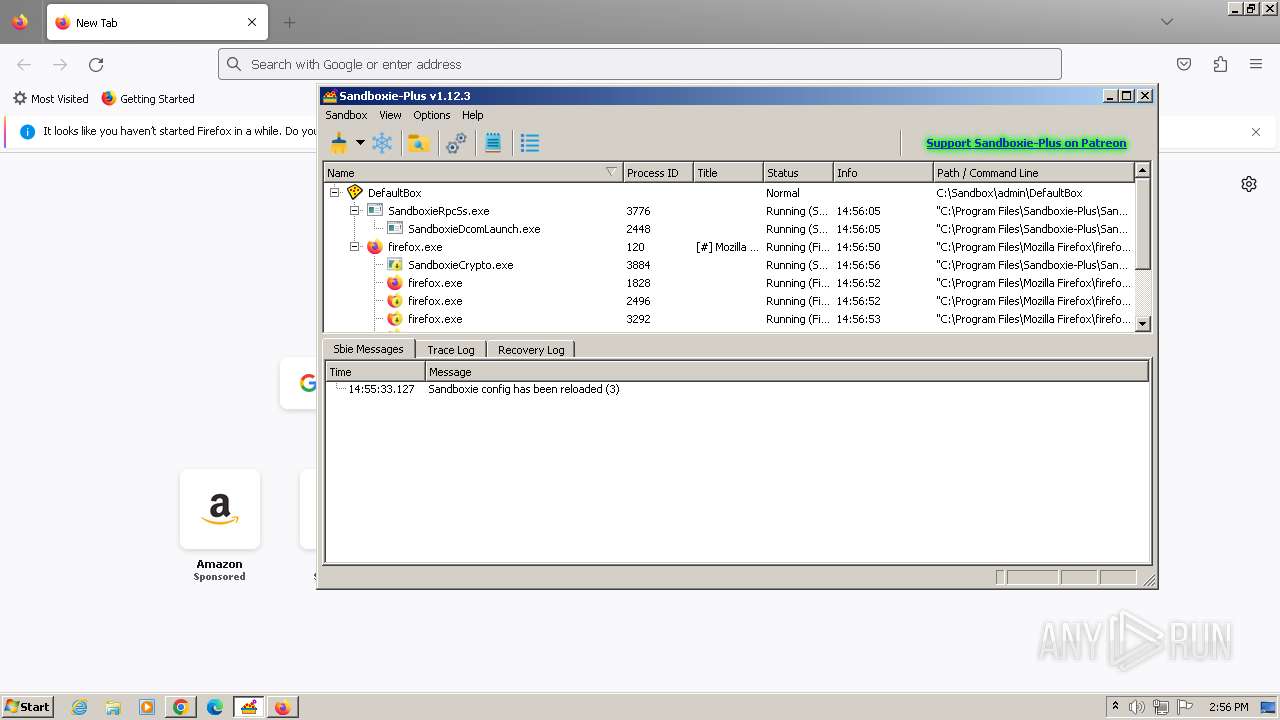
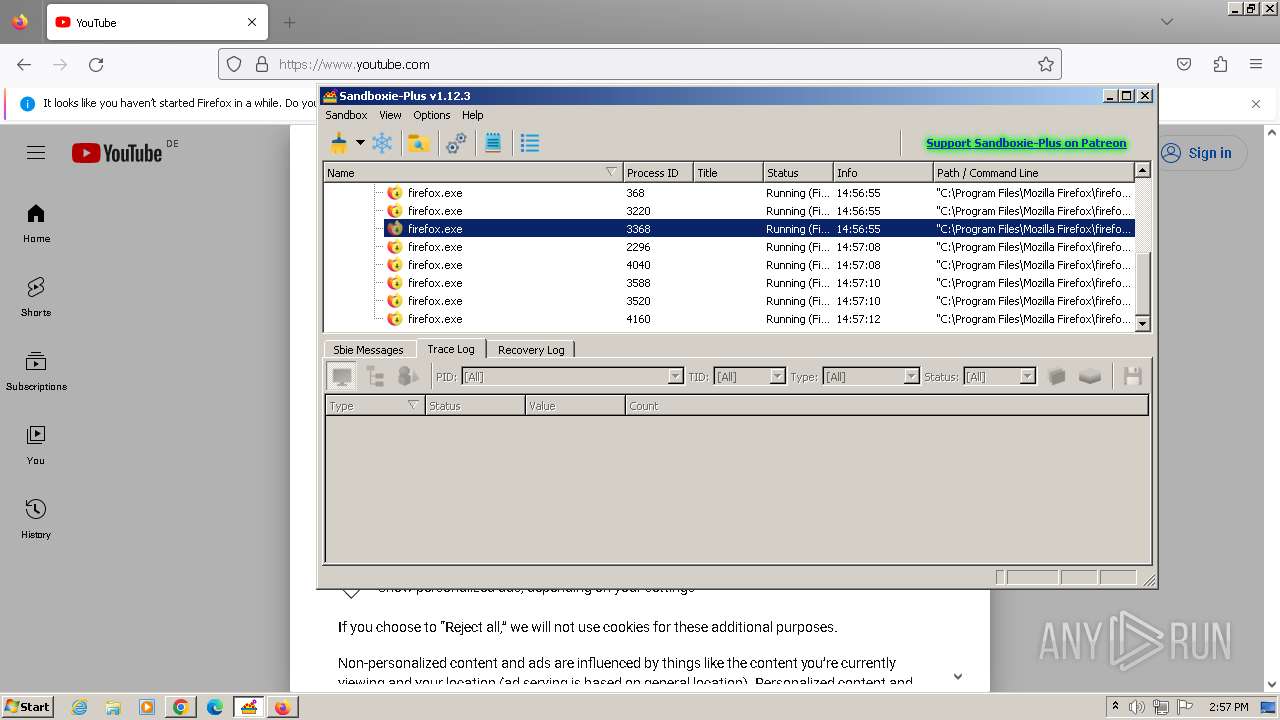
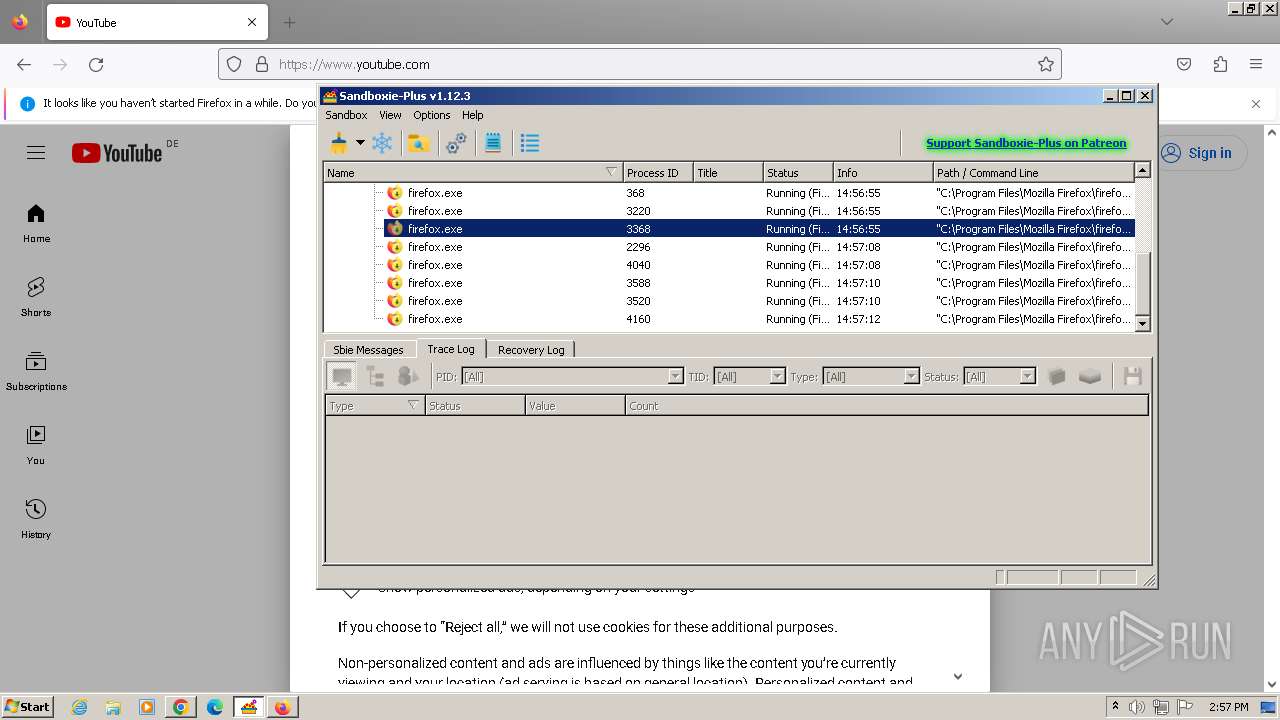
Loads DLL from Mozilla Firefox
- SandboxieRpcSs.exe (PID: 3776)
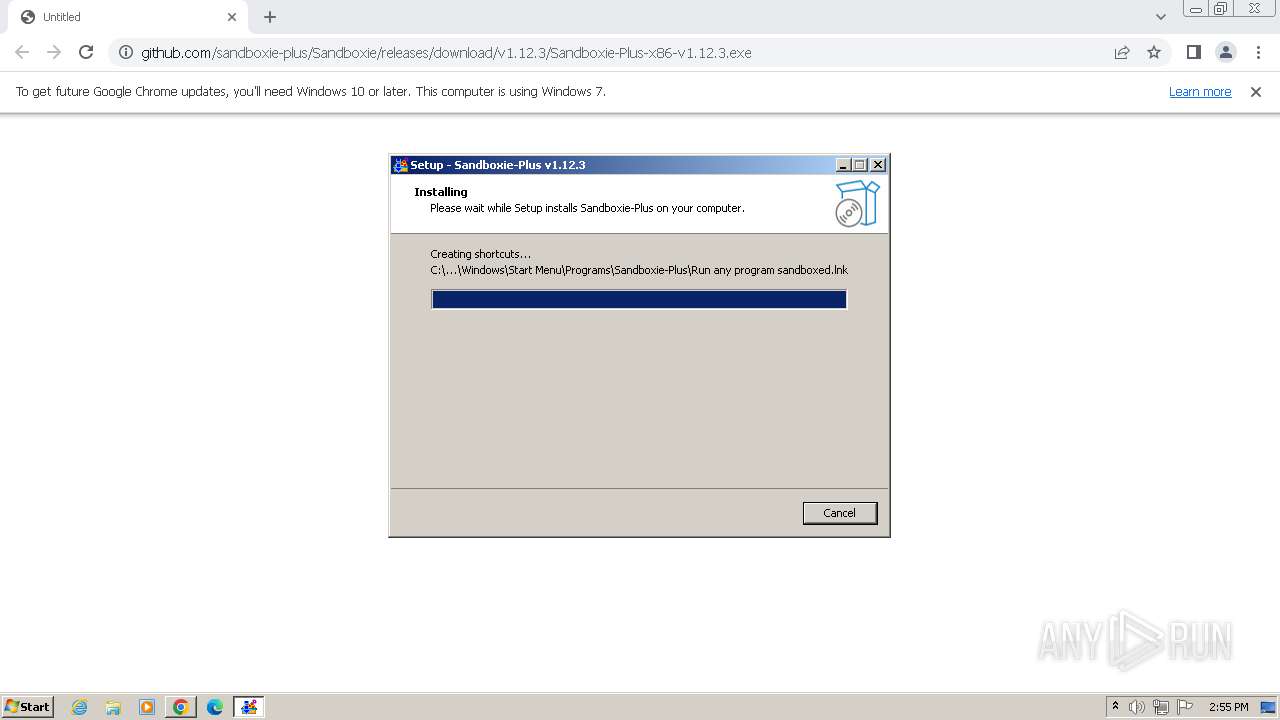
Write to the desktop.ini file (may be used to cloak folders)
- Start.exe (PID: 3576)
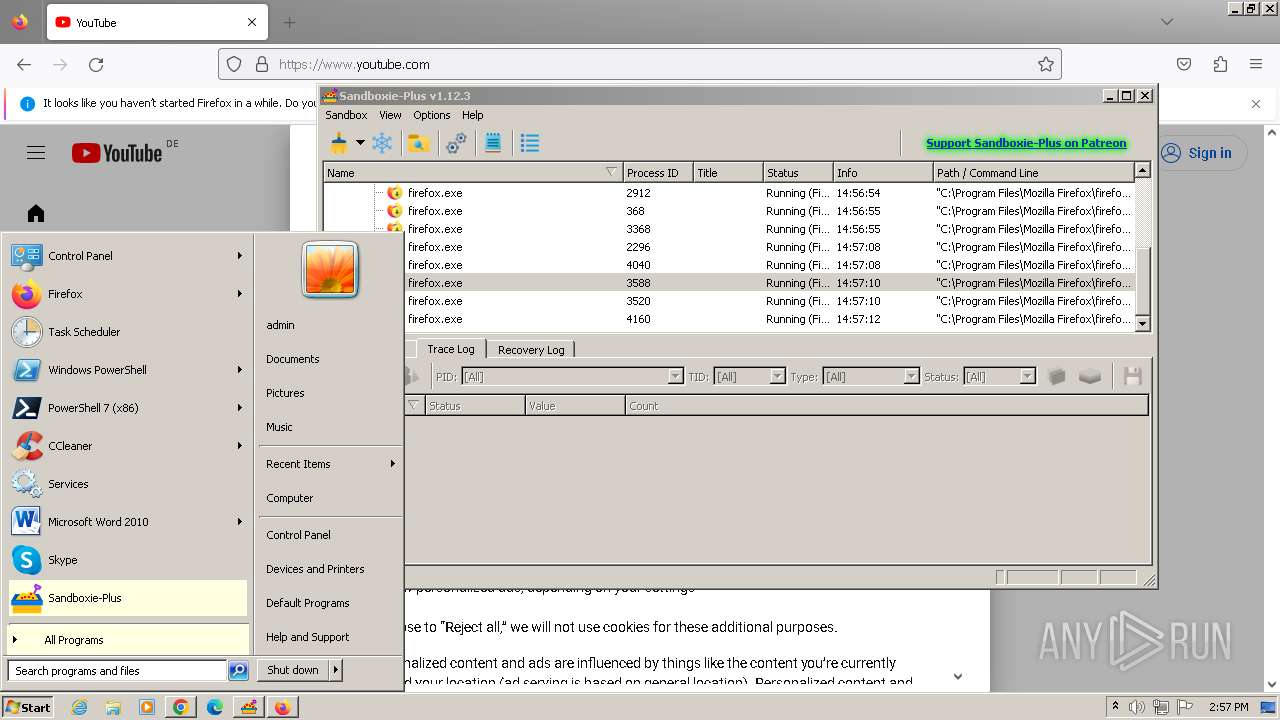
INFO
Application launched itself
- chrome.exe (PID: 1864)
- firefox.exe (PID: 3616)
- firefox.exe (PID: 120)
Reads the computer name
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 2028)
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
- KmdUtil.exe (PID: 788)
- KmdUtil.exe (PID: 448)
- UpdUtil.exe (PID: 2708)
- KmdUtil.exe (PID: 1788)
- SbieSvc.exe (PID: 3320)
- SandMan.exe (PID: 3000)
- wmpnscfg.exe (PID: 3228)
- wmpnscfg.exe (PID: 3736)
- SbieSvc.exe (PID: 3124)
- SandboxieRpcSs.exe (PID: 3776)
- SandboxieDcomLaunch.exe (PID: 2448)
- Start.exe (PID: 3576)
- SbieSvc.exe (PID: 296)
- SandboxieCrypto.exe (PID: 3884)
Checks supported languages
- wmpnscfg.exe (PID: 3736)
- Sandboxie-Plus-x86-v1.12.3.exe (PID: 3020)
- Sandboxie-Plus-x86-v1.12.3.exe (PID: 2392)
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 2028)
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
- KmdUtil.exe (PID: 788)
- KmdUtil.exe (PID: 448)
- KmdUtil.exe (PID: 1788)
- SbieSvc.exe (PID: 3320)
- UpdUtil.exe (PID: 2708)
- Start.exe (PID: 2532)
- SandMan.exe (PID: 3000)
- wmpnscfg.exe (PID: 3228)
- Start.exe (PID: 2584)
- SandboxieRpcSs.exe (PID: 3776)
- SbieSvc.exe (PID: 3124)
- SandboxieDcomLaunch.exe (PID: 2448)
- Start.exe (PID: 3576)
- SbieSvc.exe (PID: 296)
- SandboxieCrypto.exe (PID: 3884)
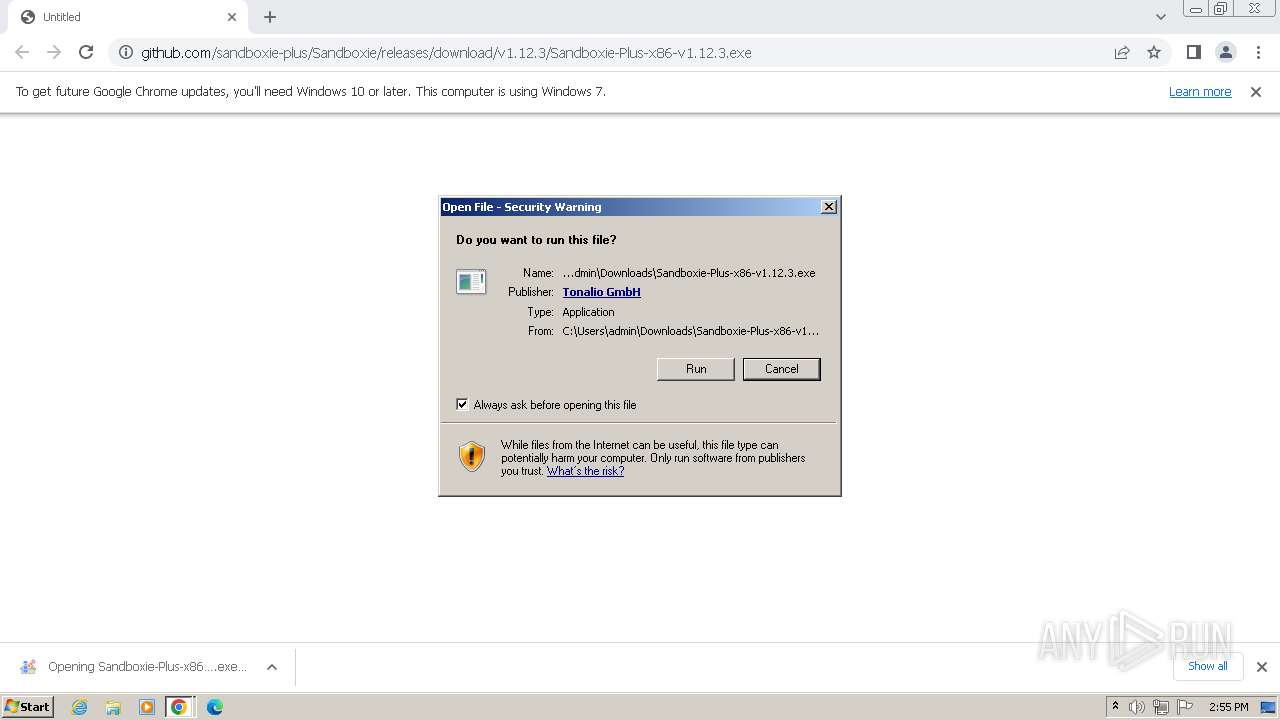
Manual execution by a user
- wmpnscfg.exe (PID: 3736)
- wmpnscfg.exe (PID: 3228)
Drops the executable file immediately after the start
- chrome.exe (PID: 1864)
- chrome.exe (PID: 2888)
Create files in a temporary directory
- Sandboxie-Plus-x86-v1.12.3.exe (PID: 3020)
- Sandboxie-Plus-x86-v1.12.3.exe (PID: 2392)
- SandMan.exe (PID: 3000)
The process uses the downloaded file
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3500)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 1864)
Creates files in the program directory
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
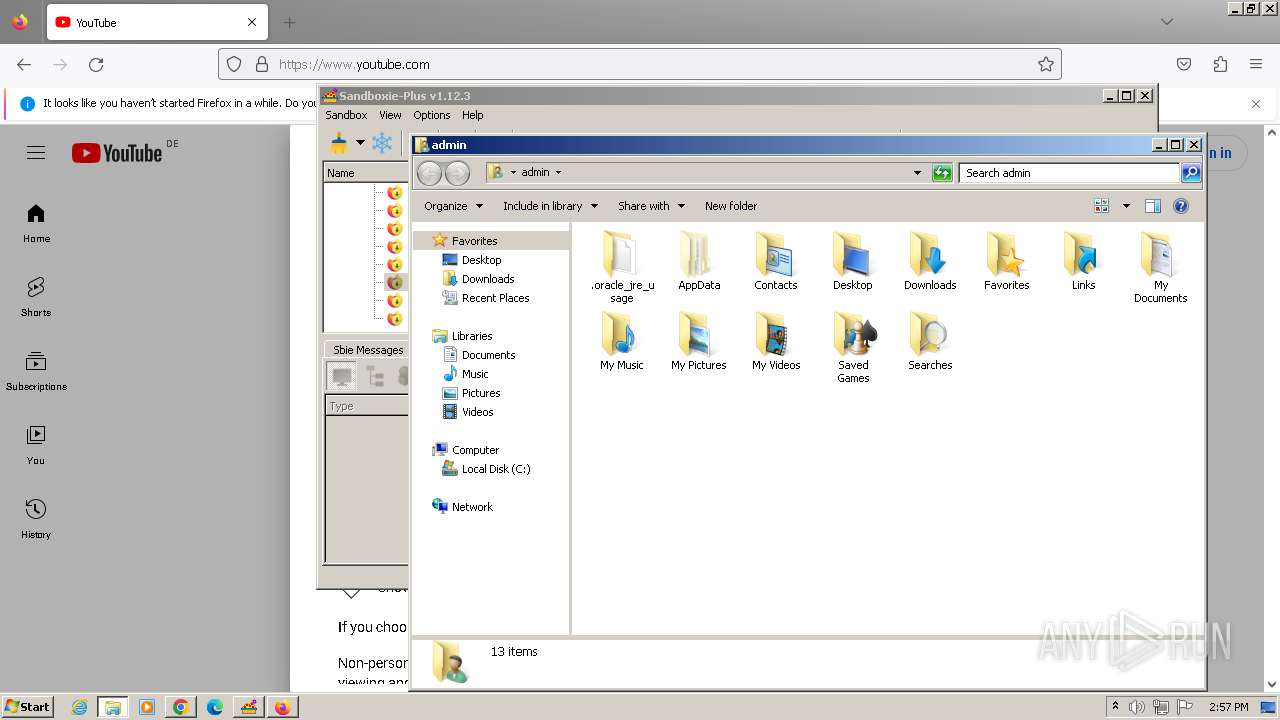
Creates files or folders in the user directory
- Sandboxie-Plus-x86-v1.12.3.tmp (PID: 3700)
- SandMan.exe (PID: 3000)
Reads the machine GUID from the registry
- UpdUtil.exe (PID: 2708)
- SandMan.exe (PID: 3000)
- SandboxieRpcSs.exe (PID: 3776)
- Start.exe (PID: 3576)
- SbieSvc.exe (PID: 296)
- SandboxieCrypto.exe (PID: 3884)
Reads Environment values
- SandMan.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
101
Monitored processes
58
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3888 --field-trial-handle=1192,i,183745071776299084,7905863680723942901,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
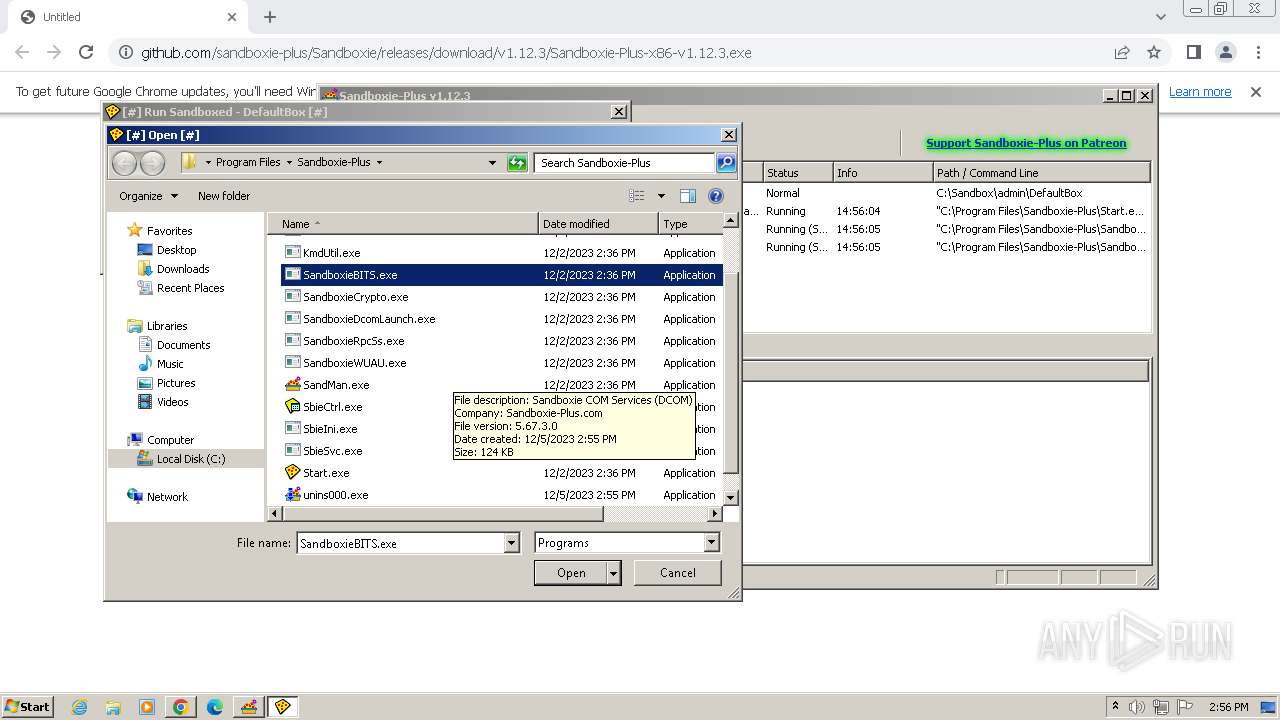
| 296 | "C:\Program Files\Sandboxie-Plus\SbieSvc.exe" Sandboxie_ComProxy_S-1-5-21-1302019708-1500728564-335382590-1000_DefaultBox_1_0_: | C:\Program Files\Sandboxie-Plus\SbieSvc.exe | — | SbieSvc.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: MEDIUM Description: Sandboxie Service Exit code: 0 Version: 5.67.3 Modules
| |||||||||||||||
| 368 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="120.4.67485727\301376833" -childID 3 -isForBrowser -prefsHandle 3840 -prefMapHandle 3688 -prefsLen 29102 -prefMapSize 244195 -jsInitHandle 928 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {3ef17465-3ae6-420f-92f5-2025f01d60ae} 120 "\\.\pipe\gecko-crash-server-pipe.120" 3864 157b7c90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Sandboxie-Plus\KmdUtil.exe" install SbieSvc "C:\Program Files\Sandboxie-Plus\SbieSvc.exe" type=own start=auto msgfile="C:\Program Files\Sandboxie-Plus\SbieMsg.dll" display="Sandboxie Service" group=UIGroup | C:\Program Files\Sandboxie-Plus\KmdUtil.exe | — | Sandboxie-Plus-x86-v1.12.3.tmp | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.67.3 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Sandboxie-Plus\KmdUtil.exe" install SbieDrv "C:\Program Files\Sandboxie-Plus\SbieDrv.sys" type=kernel start=demand msgfile="C:\Program Files\Sandboxie-Plus\SbieMsg.dll" altitude=86900 | C:\Program Files\Sandboxie-Plus\KmdUtil.exe | — | Sandboxie-Plus-x86-v1.12.3.tmp | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.67.3 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1152 --field-trial-handle=1192,i,183745071776299084,7905863680723942901,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Sandboxie-Plus\KmdUtil.exe" start SbieSvc | C:\Program Files\Sandboxie-Plus\KmdUtil.exe | — | Sandboxie-Plus-x86-v1.12.3.tmp | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.67.3 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="120.0.111858011\2143321902" -parentBuildID 20230710165010 -prefsHandle 1188 -prefMapHandle 1184 -prefsLen 28523 -prefMapSize 244195 -appDir "C:\Program Files\Mozilla Firefox\browser" - {96bcb1ea-7065-49a6-b2b6-9eb4263c3395} 120 "\\.\pipe\gecko-crash-server-pipe.120" 1288 cea9360 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://github.com/sandboxie-plus/Sandboxie/releases/download/v1.12.3/Sandboxie-Plus-x86-v1.12.3.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
31 052
Read events
30 821
Write events
224
Delete events
7
Modification events
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
102
Suspicious files
503
Text files
95
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF212143.TMP | — | |
MD5:— | SHA256:— | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8175FB7046E977DAAD01289080C116EF | SHA256:19E403B4BEF7D83DD425AB6A54DE943D244A16E5EA121DEC91C417608AEAACB7 | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF212421.TMP | text | |
MD5:8268A4D53A6A9432A8266584CBD7D624 | SHA256:F785C42945CFE320C52C763837CD41541A8CAAB3E5FD567999EED5343CF0FD7A | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF2126d1.TMP | — | |
MD5:— | SHA256:— | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF2123f2.TMP | text | |
MD5:29B82603A20A26A3F99DB34525AF7448 | SHA256:9601A054A9C6AA6A65CEFAA229046476C1A089989FA6441DAD71D39F6794B980 | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:43550DBA2277BE44F5F842196E084145 | SHA256:D19055342C06316F8B80D0B029BD233A3E48AD4C591953AF7B712ADA7F68F403 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
109
DNS requests
192
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1864 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?97541da0d61824f9 | unknown | compressed | 65.2 Kb | unknown |
1864 | chrome.exe | GET | 200 | 151.101.194.133:80 | http://secure.globalsign.com/cacert/codesigningrootr45.crt | unknown | binary | 1.37 Kb | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 5.94 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 8.57 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.3 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.6 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 341 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 164 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1864 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2108 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
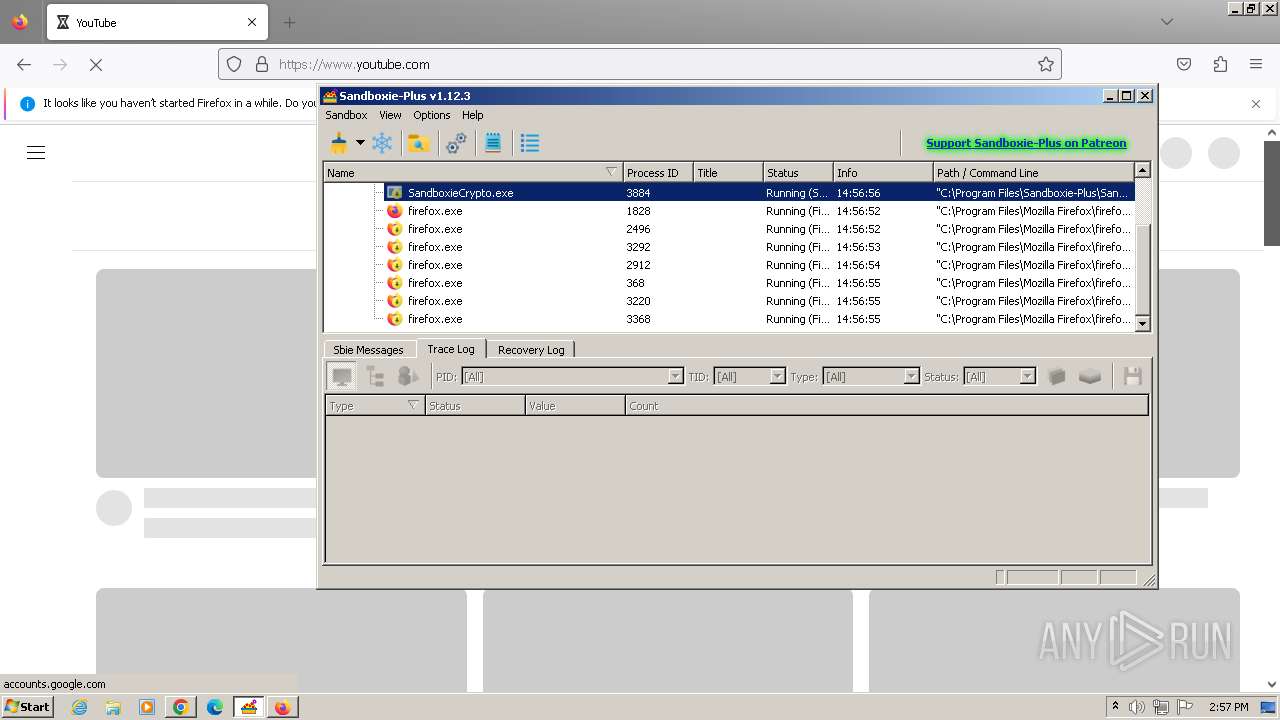
2108 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
2108 | chrome.exe | 185.199.108.133:443 | objects.githubusercontent.com | FASTLY | US | unknown |
1864 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2108 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 23.52.121.156:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
2108 | chrome.exe | 142.250.181.234:443 | optimizationguide-pa.googleapis.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
accounts.google.com |
| shared |
objects.githubusercontent.com |
| shared |
www.google.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
secure.globalsign.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
SandMan.exe | Clear took 2.2e-05 s
|
SandMan.exe | QObject::connect: No such slot CSandMan::OnDismissUpdate()
|
SandMan.exe | QFileSystemWatcher::removePath: path is empty
|
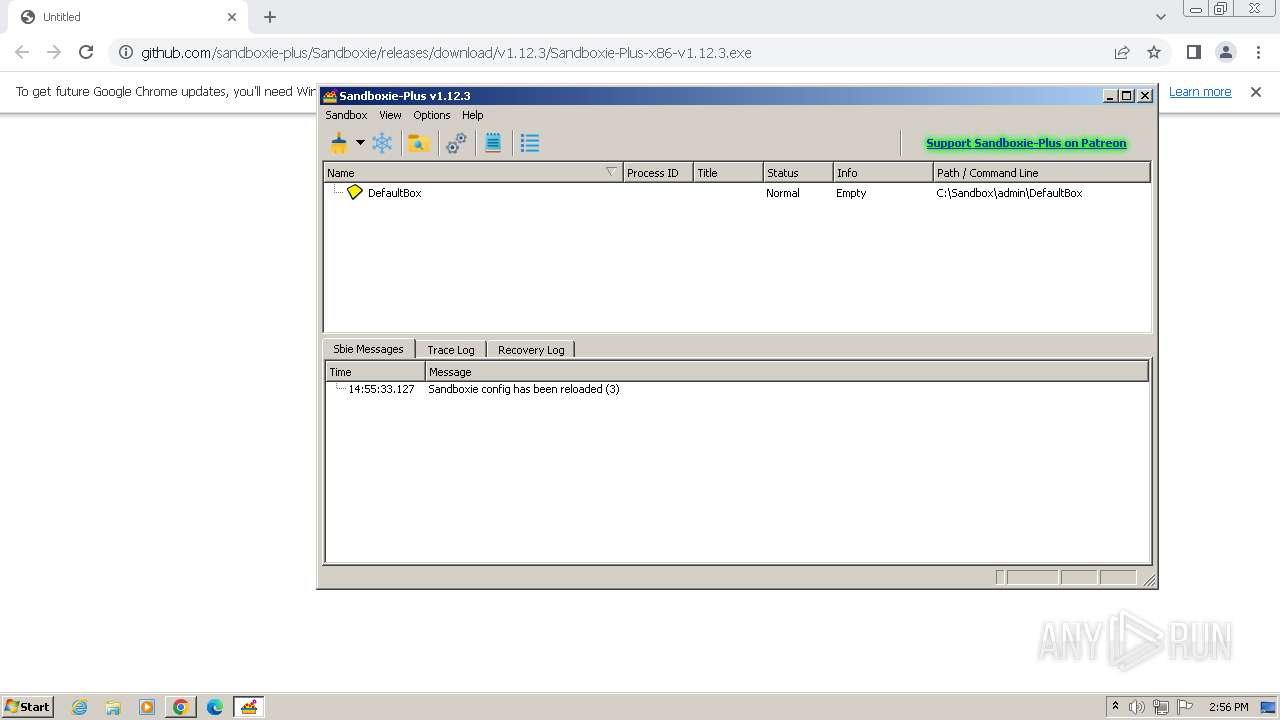
SandMan.exe | Config file: "C:\\Windows\\Sandboxie.ini" (system)
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|
SandMan.exe | QString::arg: Argument missing: Sandboxie config has been reloaded,
|