analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
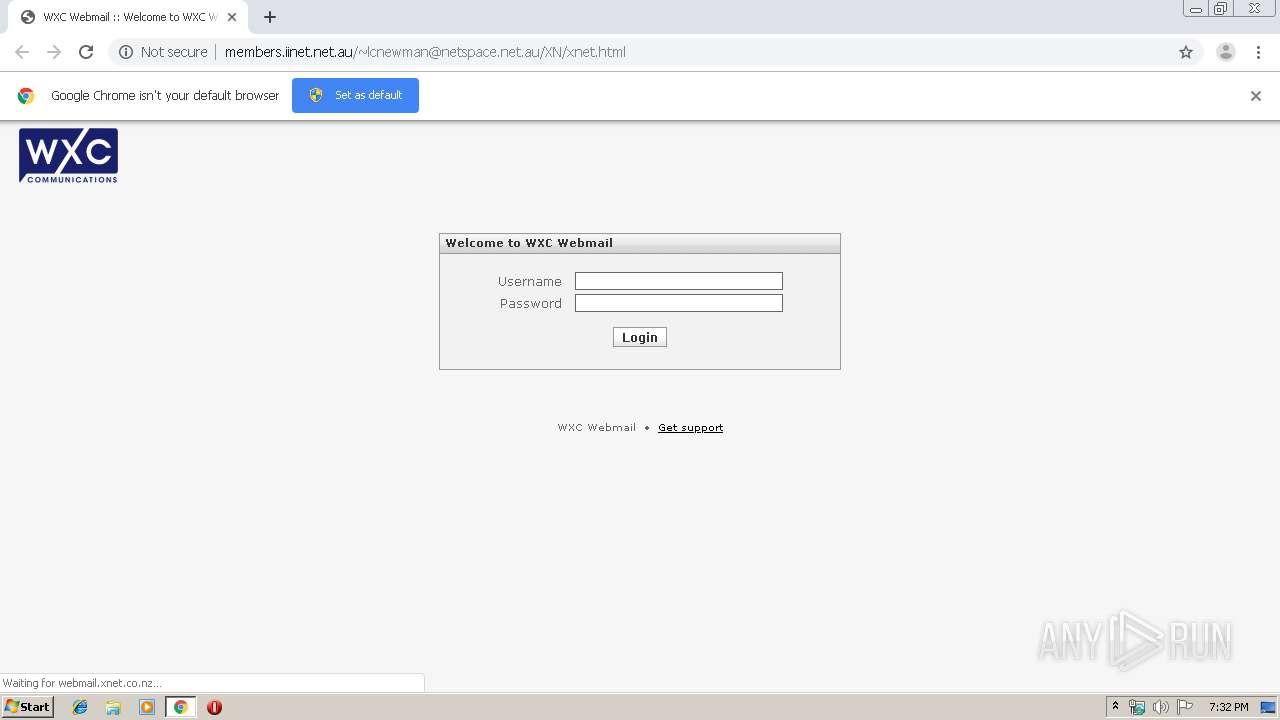
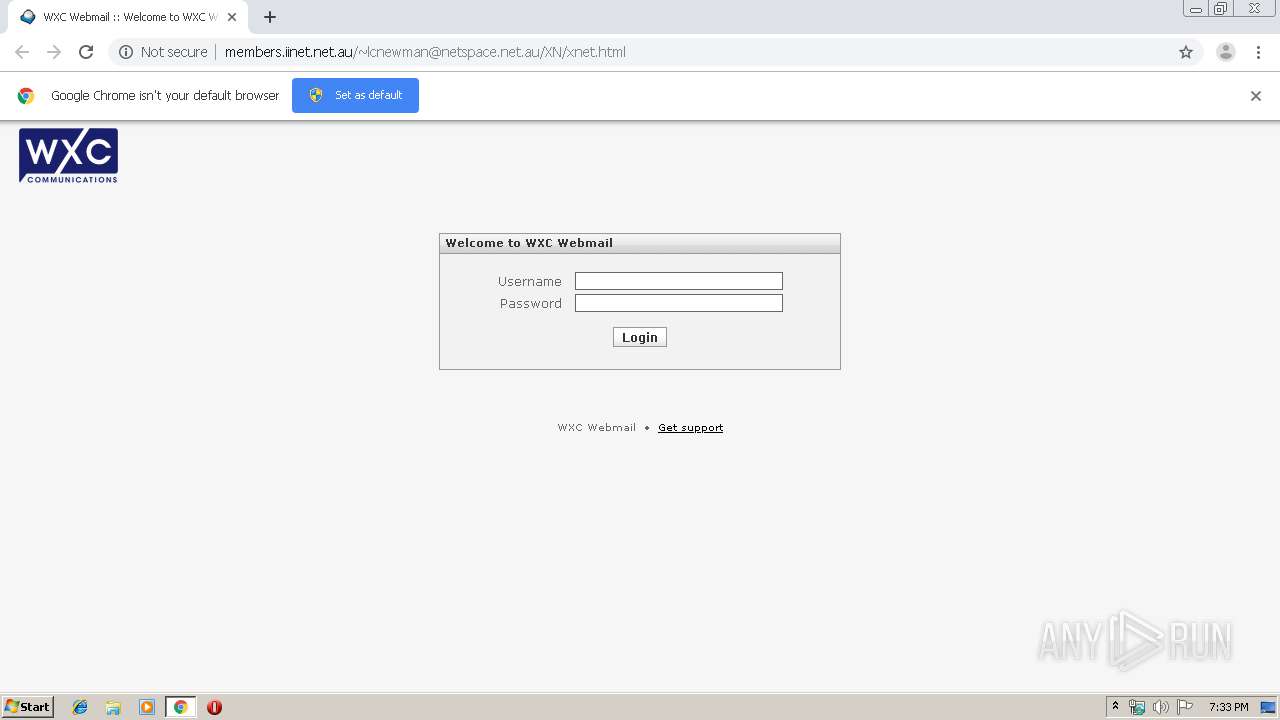
| URL: | http://members.iinet.net.au/[email protected]/XN/xnet.html |
| Full analysis: | https://app.any.run/tasks/a7b2e124-59ee-4643-b4de-746752c61d55 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 19:32:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B866D7F7E31E9BF40896C7FDF59A7091 |
| SHA1: | EEF0C427573D6E917B0B94645E54DC9AB9422DBA |
| SHA256: | 047A778E616AC279AC414997E3160CEB6A5A9DB507399583D5CB4DC9F3443D25 |
| SSDEEP: | 3:N1KTXm0LEQL35tvCARl1A/Gn:CvjCAFeGn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1560)
INFO
Reads the hosts file
- chrome.exe (PID: 4072)
- chrome.exe (PID: 1560)
Application launched itself
- chrome.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
25
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://members.iinet.net.au/[email protected]/XN/xnet.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ed2a9d0,0x6ed2a9e0,0x6ed2a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2108 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7558563487855319700 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 4072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7953914996172316086 --mojo-platform-channel-handle=1628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11198294267237197992 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5654208569192706535 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 4052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13281924392222979665 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5389564396906455274 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 4040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,11730090466670949264,8819684291380496565,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4451598039995468858 --mojo-platform-channel-handle=3516 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
617
Read events
523
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
16
Text files
239
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9712c432-b970-4f64-9f35-407fd7b7617a.tmp | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39abcb.TMP | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DC32343F45B01764B6267AD36548102A | SHA256:A250F5AD57D4BD58AAE92810D50278E3BE2DBF869F126A3A3519691BCDFC2075 | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:213AE3DA120D7862D60B5763B6C9D466 | SHA256:5736534D6EE654C1BF1A8E79E73330AF58F622E8657285330D2C7189A55604F4 | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39ad51.TMP | text | |
MD5:454106CCF080F3E3795C229FC73350D4 | SHA256:9974DC611BE9E20BDFA7B8D939CB913AD23859DEA5F52EBB8D10CEAD9AB5B4FA | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39ac67.TMP | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
20
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4072 | chrome.exe | GET | — | 203.0.178.90:80 | http://members.iinet.net.au/[email protected]/XN/program/js/app.min.js?s=1493368164 | AU | — | — | malicious |
4072 | chrome.exe | GET | — | 203.0.178.90:80 | http://members.iinet.net.au/[email protected]/XN/program/js/common.min.js?s=1493368164 | AU | — | — | malicious |
4072 | chrome.exe | GET | 200 | 172.217.132.40:80 | http://r3---sn-5hne6nsk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=192.42.116.16&mm=28&mn=sn-5hne6nsk&ms=nvh&mt=1575315086&mv=m&mvi=2&pl=22&shardbypass=yes | US | crx | 293 Kb | whitelisted |
4072 | chrome.exe | GET | 404 | 203.0.178.90:80 | http://members.iinet.net.au/[email protected]/XN/program/js/jquery.min.js?s=1493368164 | AU | html | 2.35 Kb | malicious |
4072 | chrome.exe | GET | 404 | 203.0.178.90:80 | http://members.iinet.net.au/[email protected]/XN/program/js/jstz.min.js?s=1493368164 | AU | html | 2.35 Kb | malicious |
4072 | chrome.exe | GET | 302 | 216.58.201.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
4072 | chrome.exe | GET | 404 | 203.0.178.90:80 | http://members.iinet.net.au/[email protected]/XN/program/js/common.min.js?s=1493368164 | AU | html | 2.35 Kb | malicious |
4072 | chrome.exe | GET | 200 | 203.0.178.90:80 | http://members.iinet.net.au/[email protected]/XN/xnet.html | AU | html | 2.14 Kb | malicious |
4072 | chrome.exe | GET | 302 | 216.58.201.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
4072 | chrome.exe | GET | 404 | 203.0.178.90:80 | http://members.iinet.net.au/[email protected]/XN/program/js/common.min.js?s=1493368164 | AU | html | 2.35 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4072 | chrome.exe | 204.13.202.71:80 | ssl.trustwave.com | Savvis | US | unknown |
4072 | chrome.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4072 | chrome.exe | 58.28.4.141:443 | webmail.xnet.co.nz | Vodafone Next Generation Services Limited | NZ | unknown |
4072 | chrome.exe | 216.58.215.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 203.0.178.90:80 | members.iinet.net.au | Internode Pty Ltd | AU | malicious |
4072 | chrome.exe | 216.58.213.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.19.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.19.228:443 | www.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 216.58.201.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 216.58.201.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
members.iinet.net.au |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
webmail.xnet.co.nz |
| unknown |
www.google.com |
| whitelisted |
ssl.trustwave.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.wxc.co.nz |
| unknown |