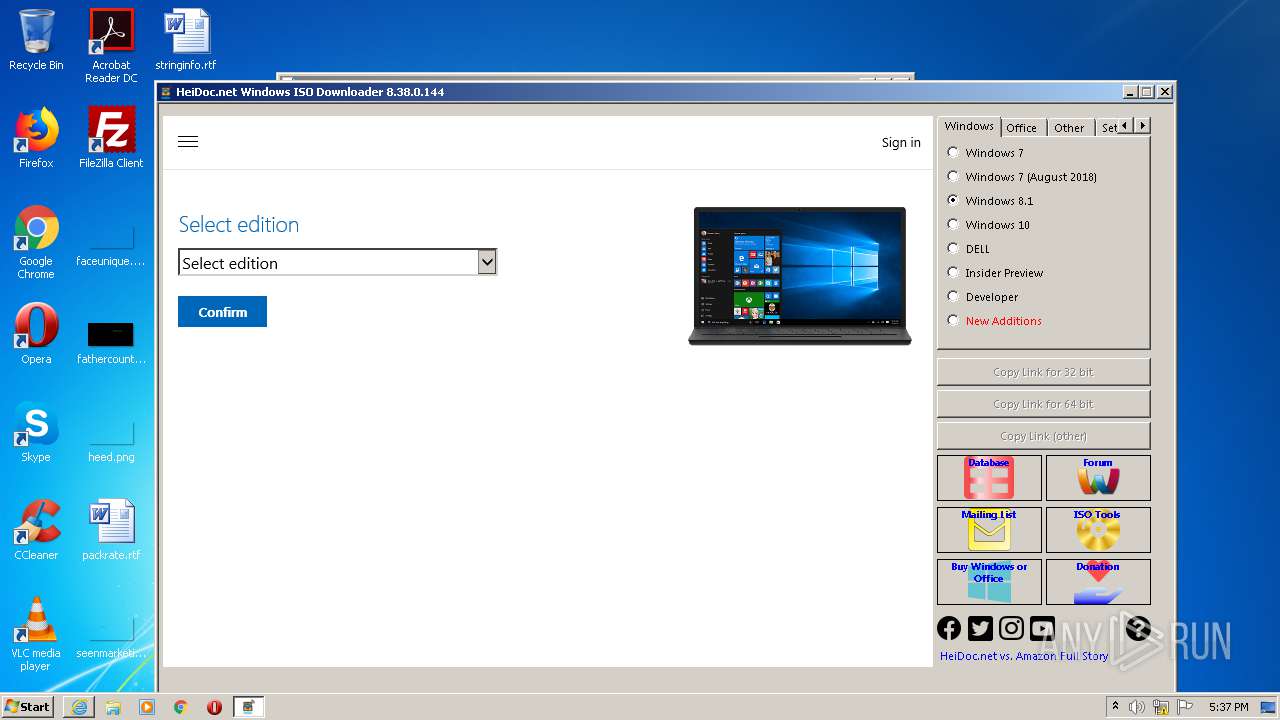
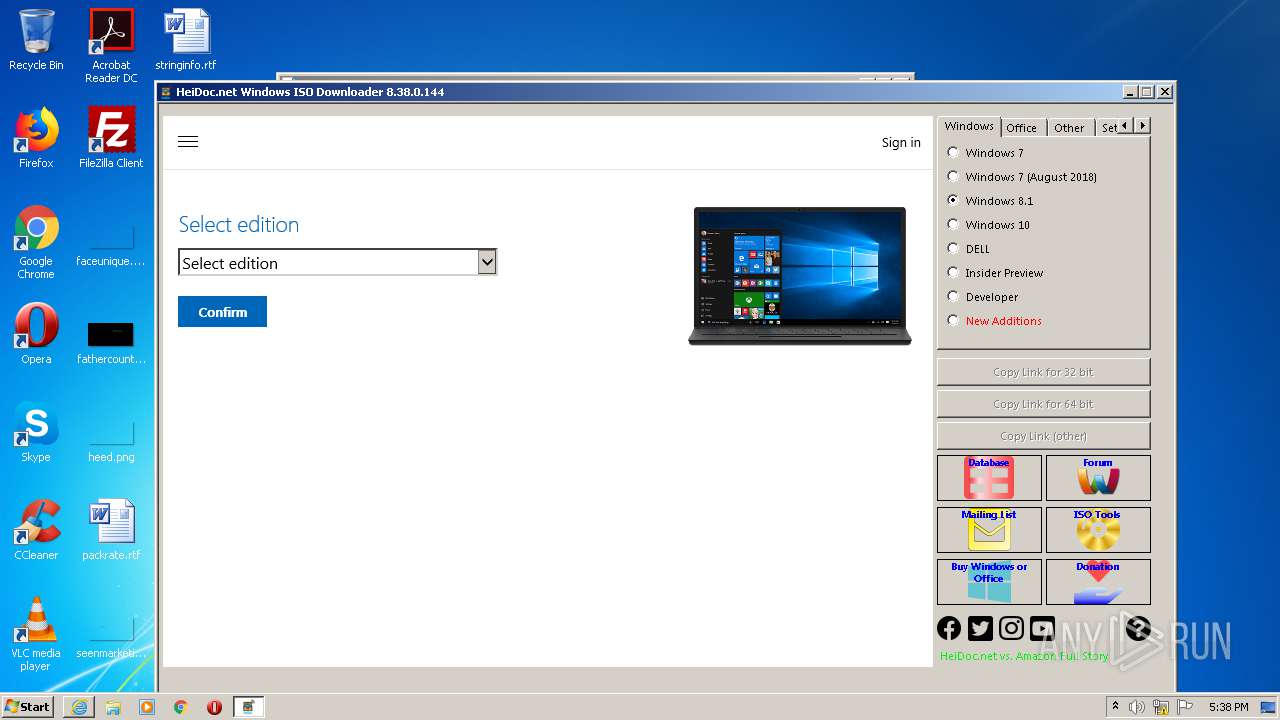
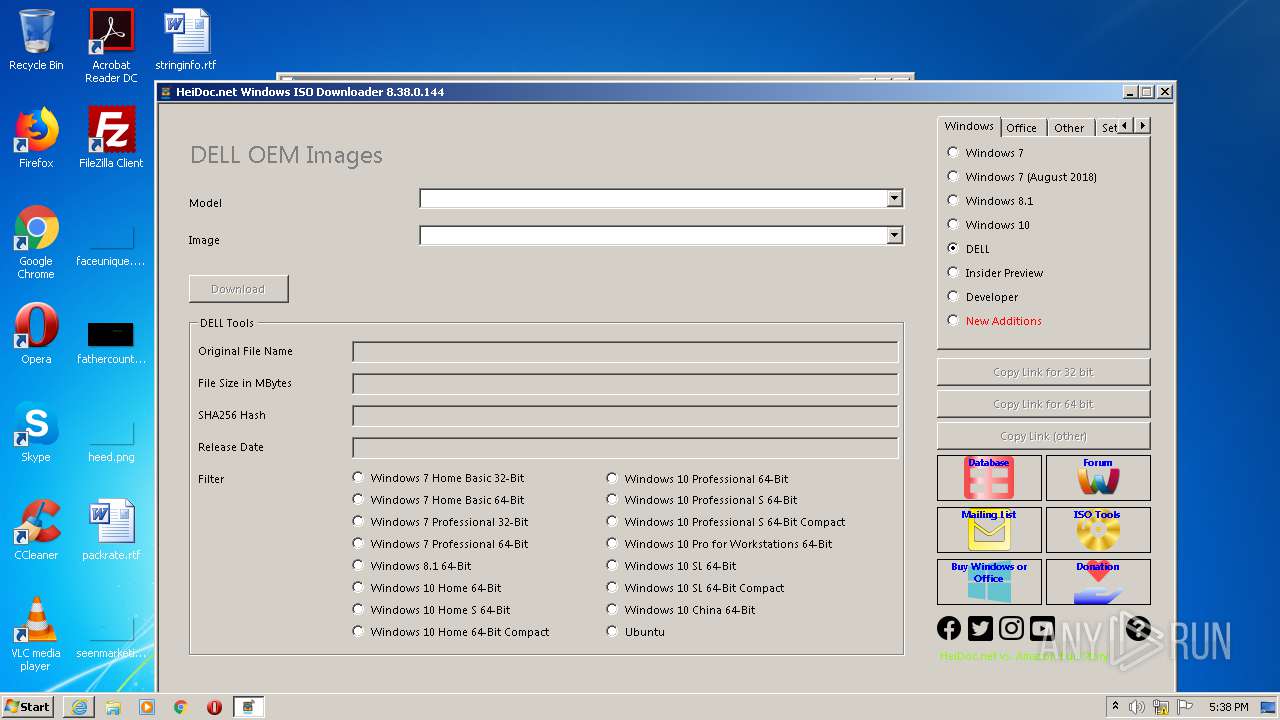
| URL: | https://www.heidoc.net/php/Windows-ISO-Downloader.exe |
| Full analysis: | https://app.any.run/tasks/ceb248e6-cfc7-4d51-926b-37932c021556 |
| Verdict: | Malicious activity |
| Analysis date: | August 15, 2020, 16:36:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A3AB57729AF01C91D81A4E662238532E |
| SHA1: | E9539EE7CD6D02FB25FDB46C664427D2C3FC3312 |
| SHA256: | 0479285C4E4F06ADF00C96F1A812FE0E4F73DAF256564ABE5C6C809B6C102316 |
| SSDEEP: | 3:N8DSLEcoigyaJUhE2X0C:2OLUyaJUS/C |
MALICIOUS
Application was dropped or rewritten from another process
- Windows-ISO-Downloader.exe (PID: 3536)
Changes settings of System certificates
- Windows-ISO-Downloader.exe (PID: 3536)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 1264)
Reads Internet Cache Settings
- Windows-ISO-Downloader.exe (PID: 3536)
Reads internet explorer settings
- Windows-ISO-Downloader.exe (PID: 3536)
Creates files in the user directory
- Windows-ISO-Downloader.exe (PID: 3536)
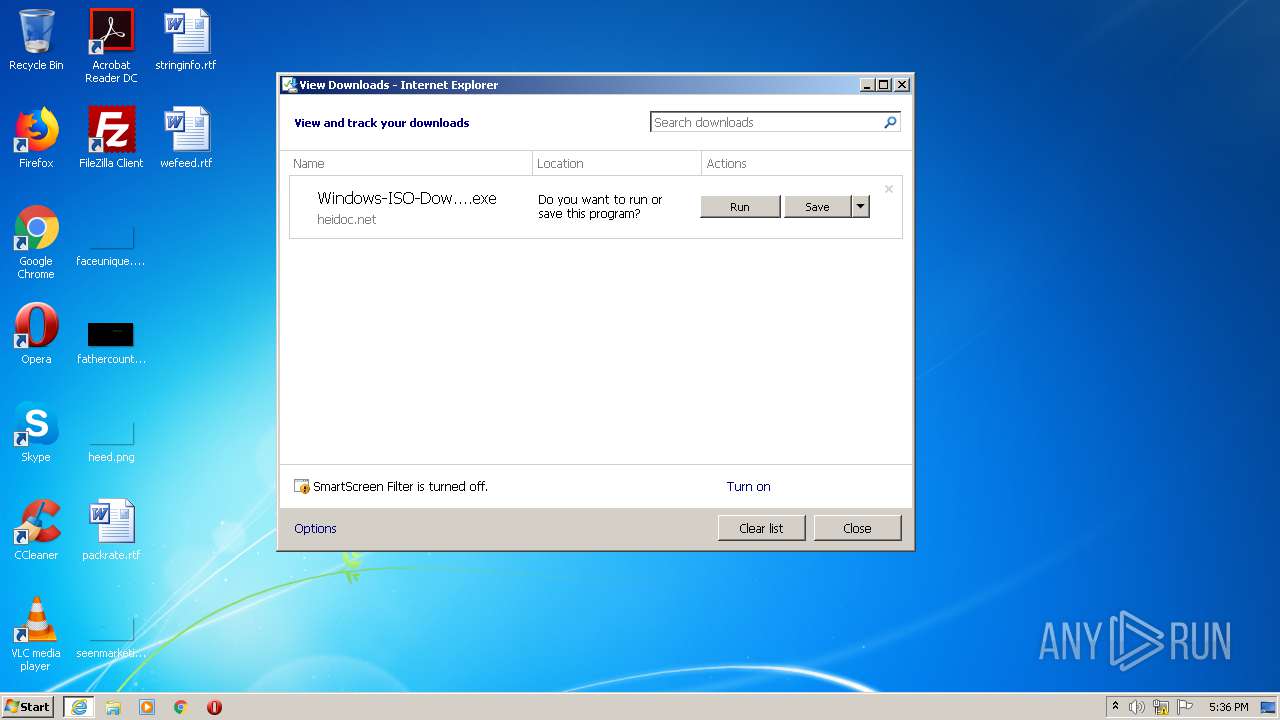
Starts Internet Explorer
- Windows-ISO-Downloader.exe (PID: 3536)
Adds / modifies Windows certificates
- Windows-ISO-Downloader.exe (PID: 3536)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1264)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 1936)
- iexplore.exe (PID: 3292)
Changes internet zones settings
- iexplore.exe (PID: 1264)
- iexplore.exe (PID: 1936)
Reads settings of System Certificates
- iexplore.exe (PID: 1264)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 3140)
- iexplore.exe (PID: 3292)
Application launched itself
- iexplore.exe (PID: 1264)
- iexplore.exe (PID: 1936)
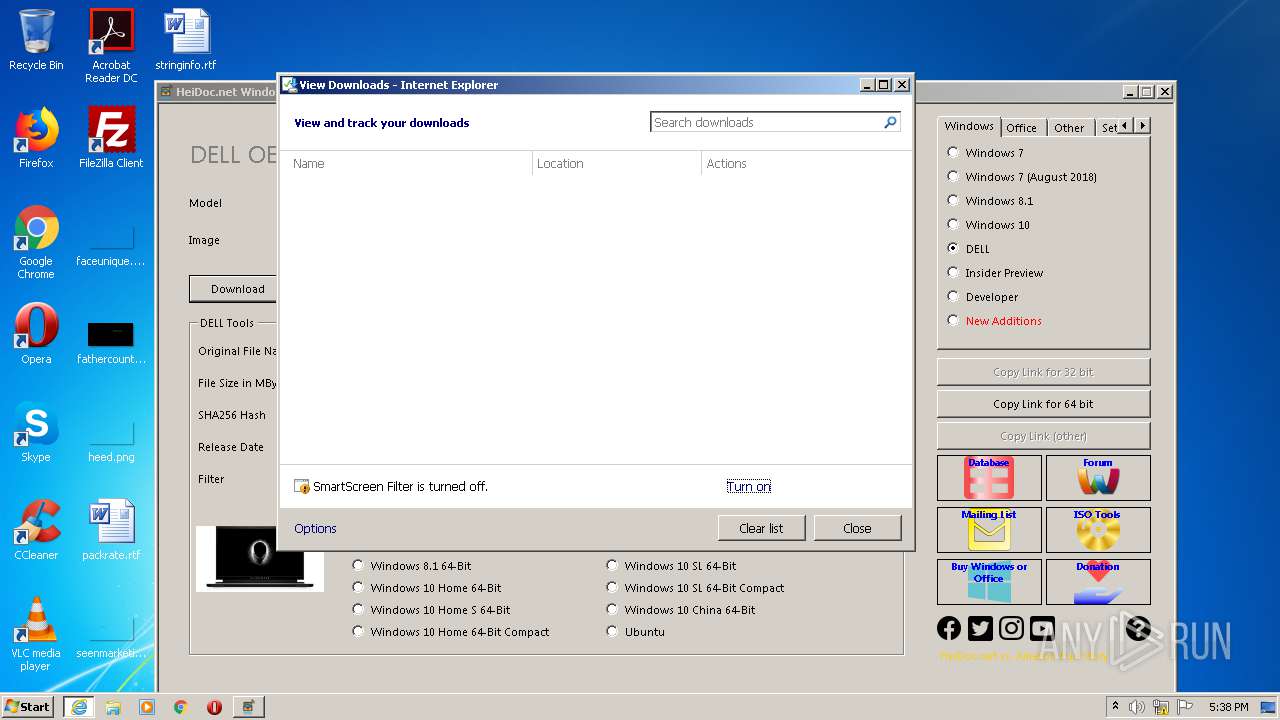
Modifies the phishing filter of IE
- iexplore.exe (PID: 1264)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1264)
Changes settings of System certificates
- iexplore.exe (PID: 1264)
Creates files in the user directory
- iexplore.exe (PID: 1264)
Dropped object may contain Bitcoin addresses
- Windows-ISO-Downloader.exe (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1264 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.heidoc.net/php/Windows-ISO-Downloader.exe | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
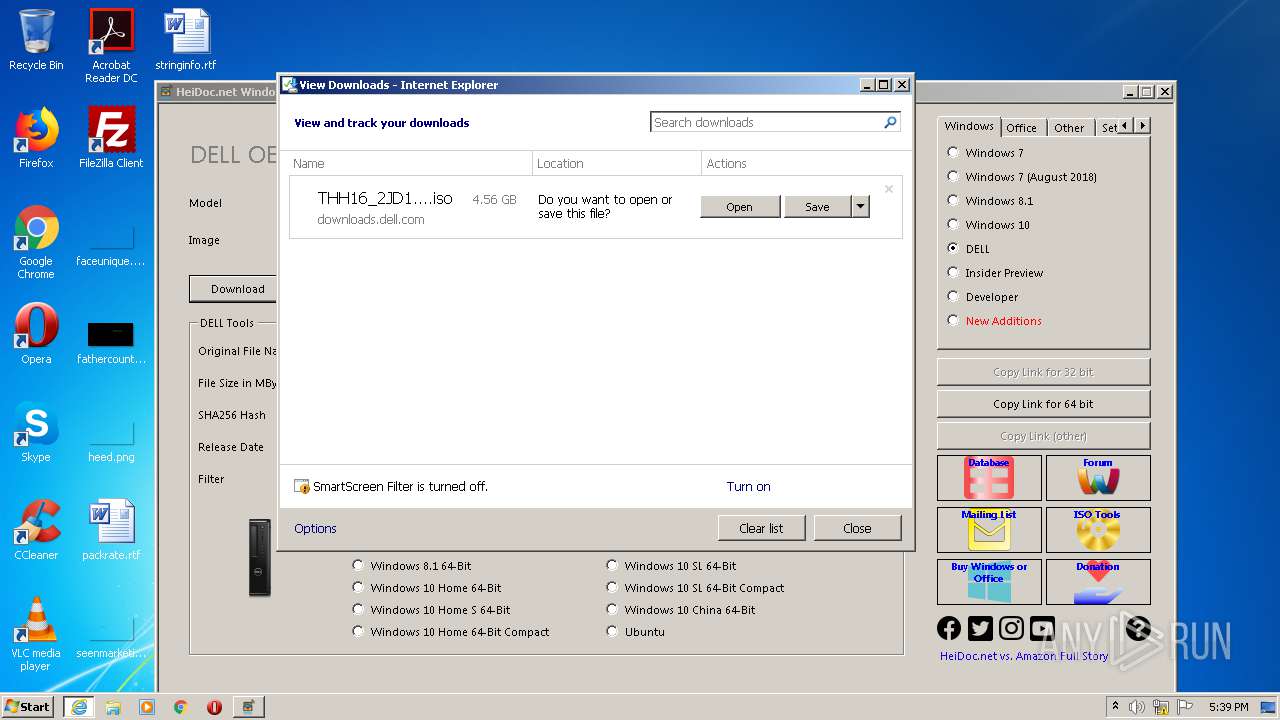
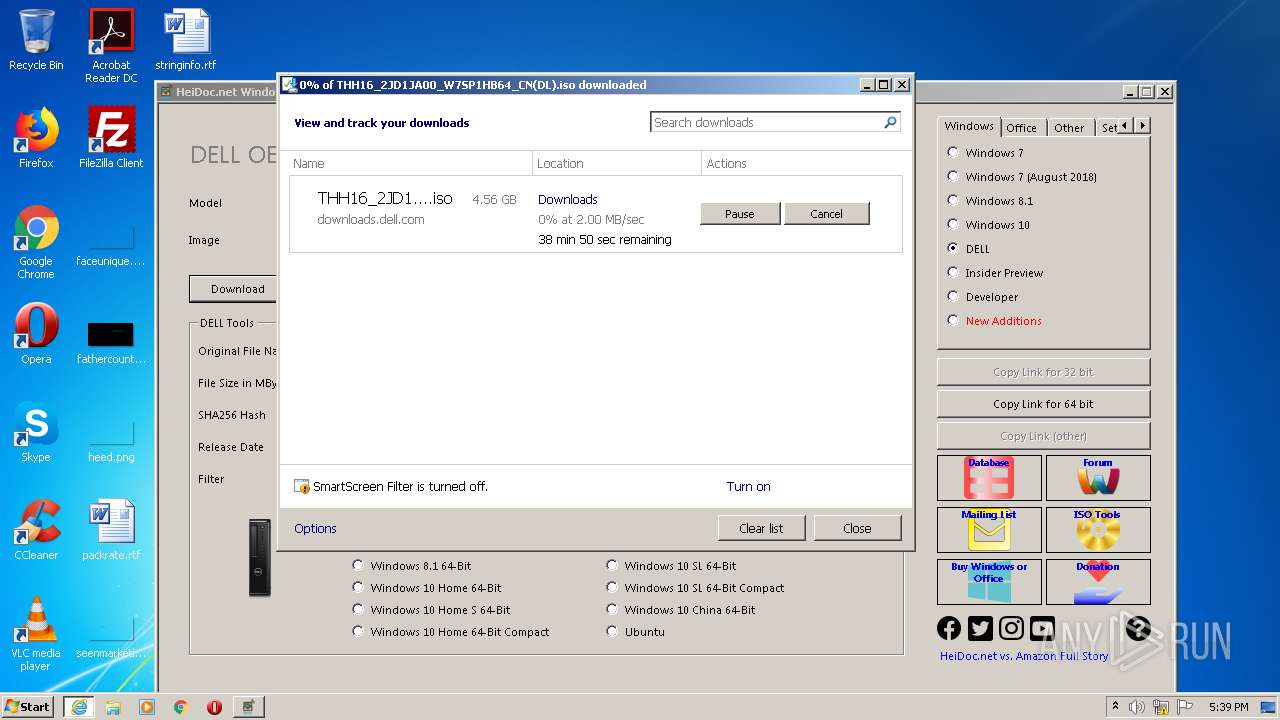
| 1936 | "C:\Program Files\Internet Explorer\iexplore.exe" https://downloads.dell.com/Restricted/FOLDER03656528M/1/THH16_2JD1JA00_W7SP1HB64_CN(DL).iso?authkey=yq0BNIGRI6jIm8rhxo4OHQD0kVMxILwWzMZc51W0v7pTieVY28MtCjkL1UQ8M9deATxVW3uDy4WnNMCkmvitGQ==&__gda__=1597527584_504aa620d854928999db3843fb01dffe&tkn=4jeUdiE_hsIVUlkbU3f10Nem4F9AX0UCuho0z7sSU318gmaurURPVPVVxovzzbGAOY7atcQkNMbyxi9OVq8MaerPjXx1oMajNfSbq6kh9c7vejsoLtWsG4KWuSLmhC4yaR0G0UJmHkuqMbSNt2ruvwhQpA1OkoNQ4ayeQGTRXg&uid=a96f08fe-b954-4305-bdab-578294d1572e | C:\Program Files\Internet Explorer\iexplore.exe | — | Windows-ISO-Downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1264 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
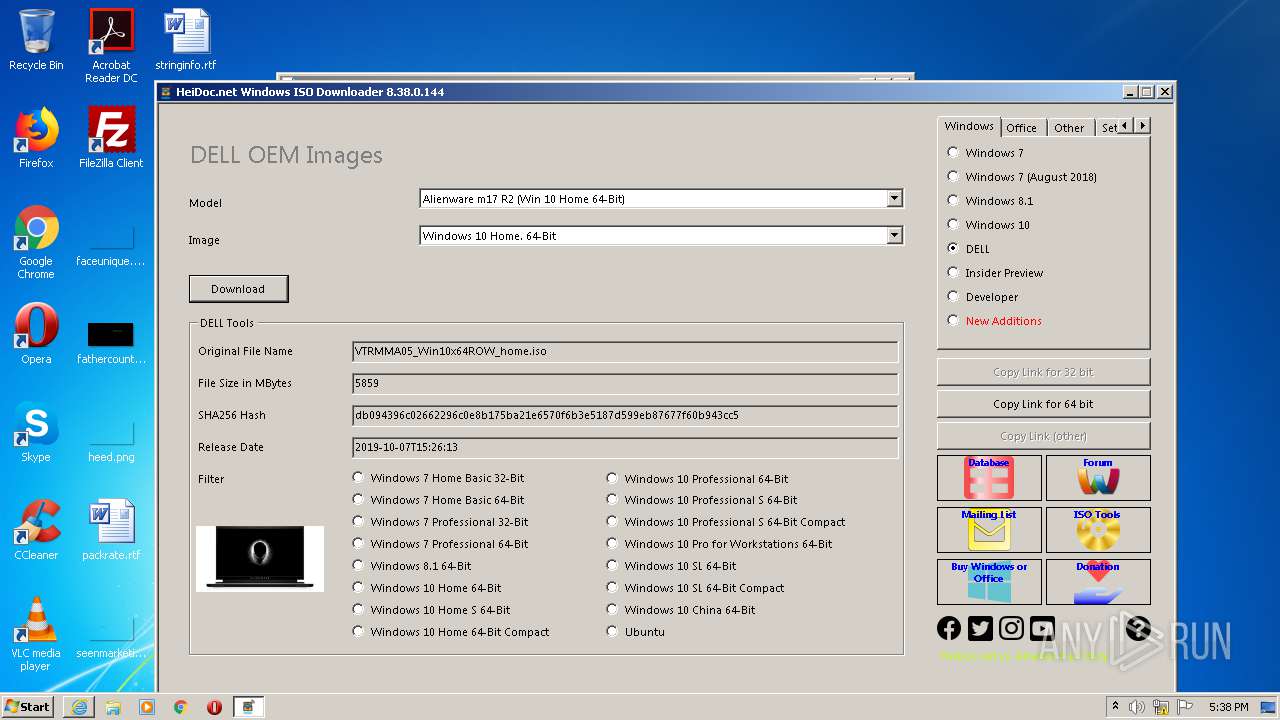
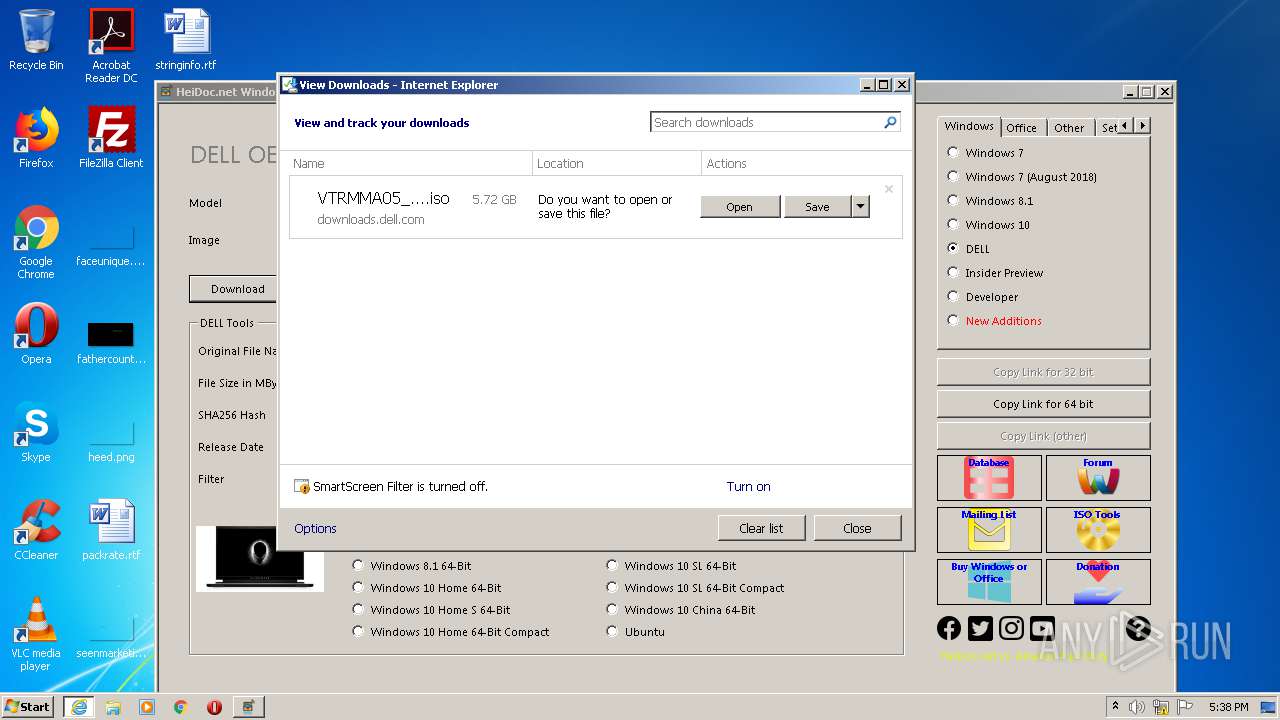
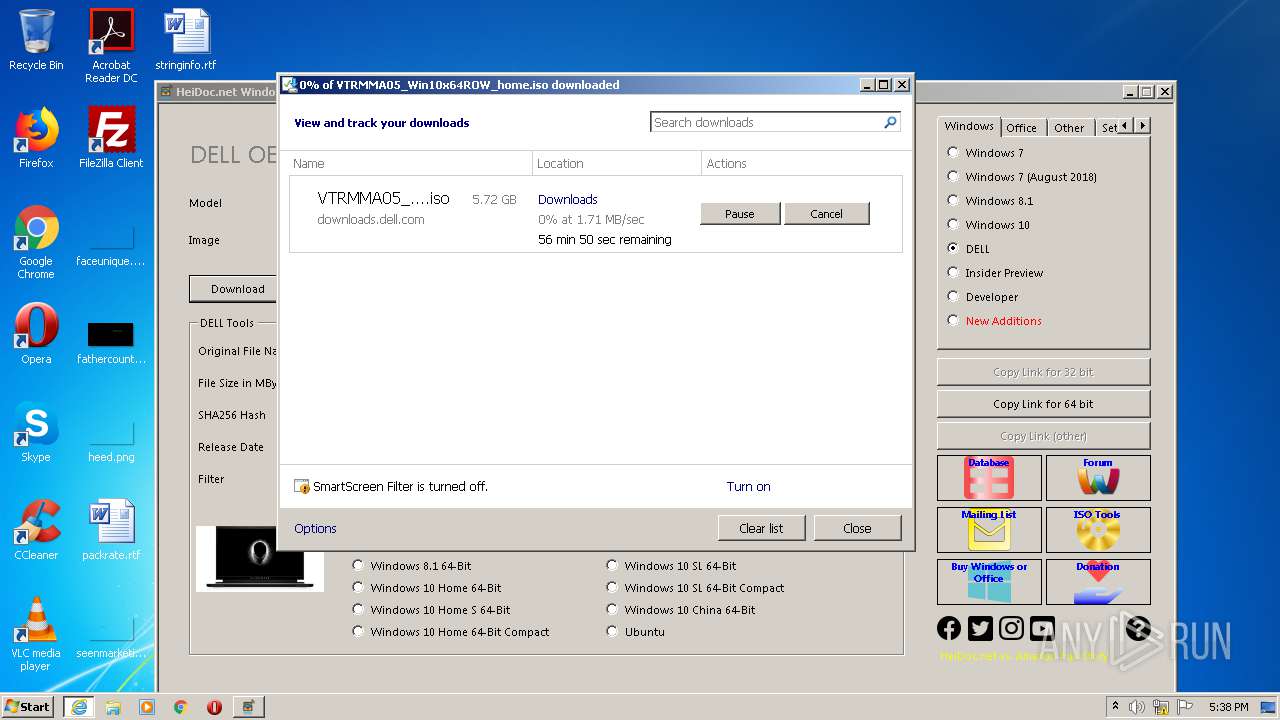
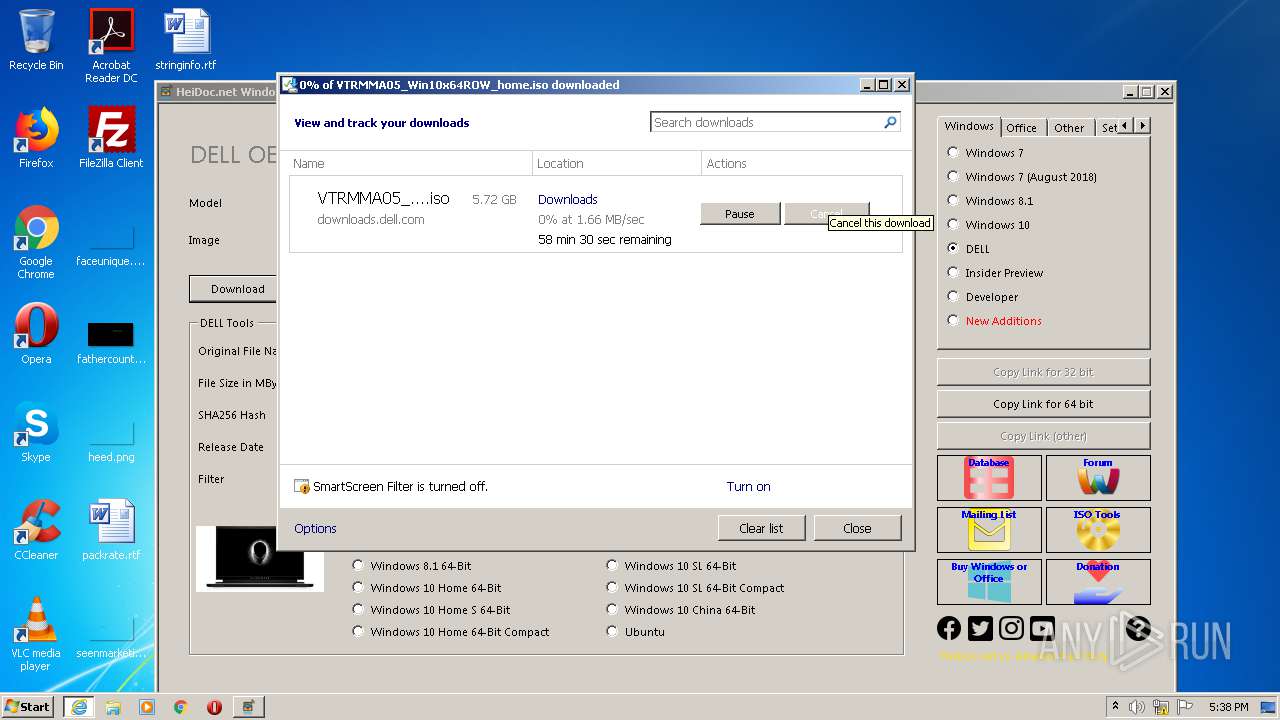
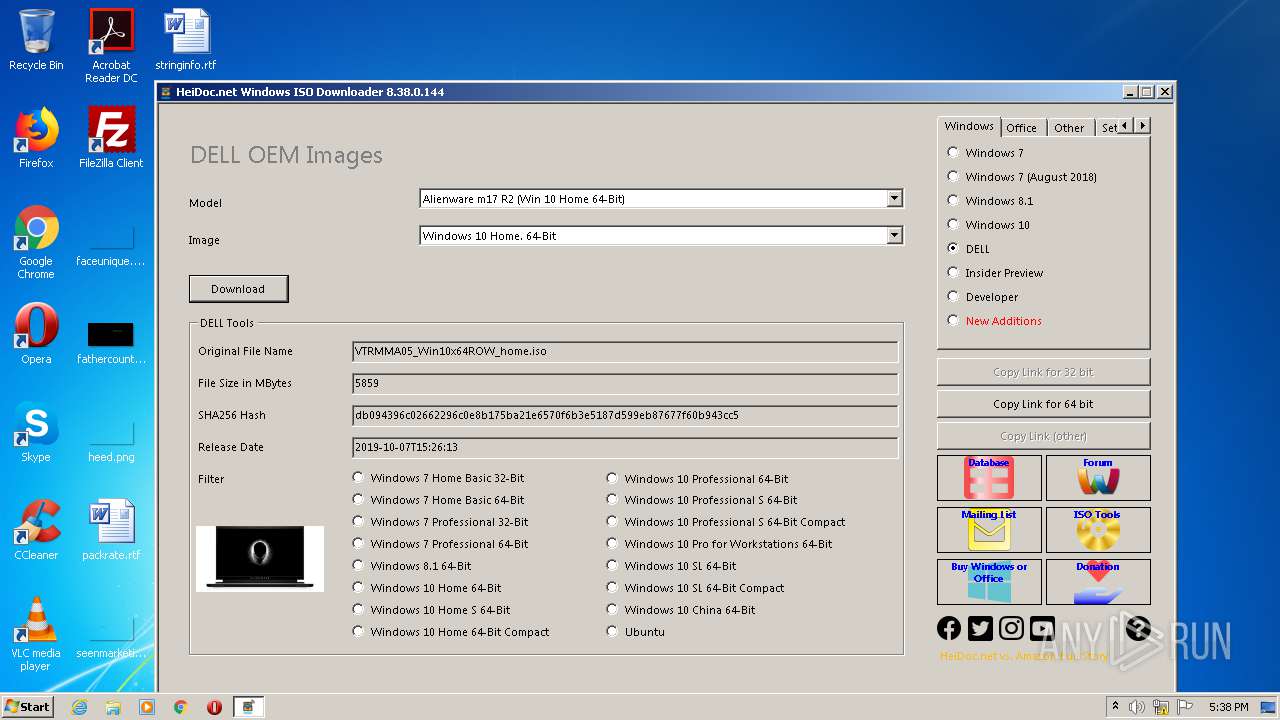
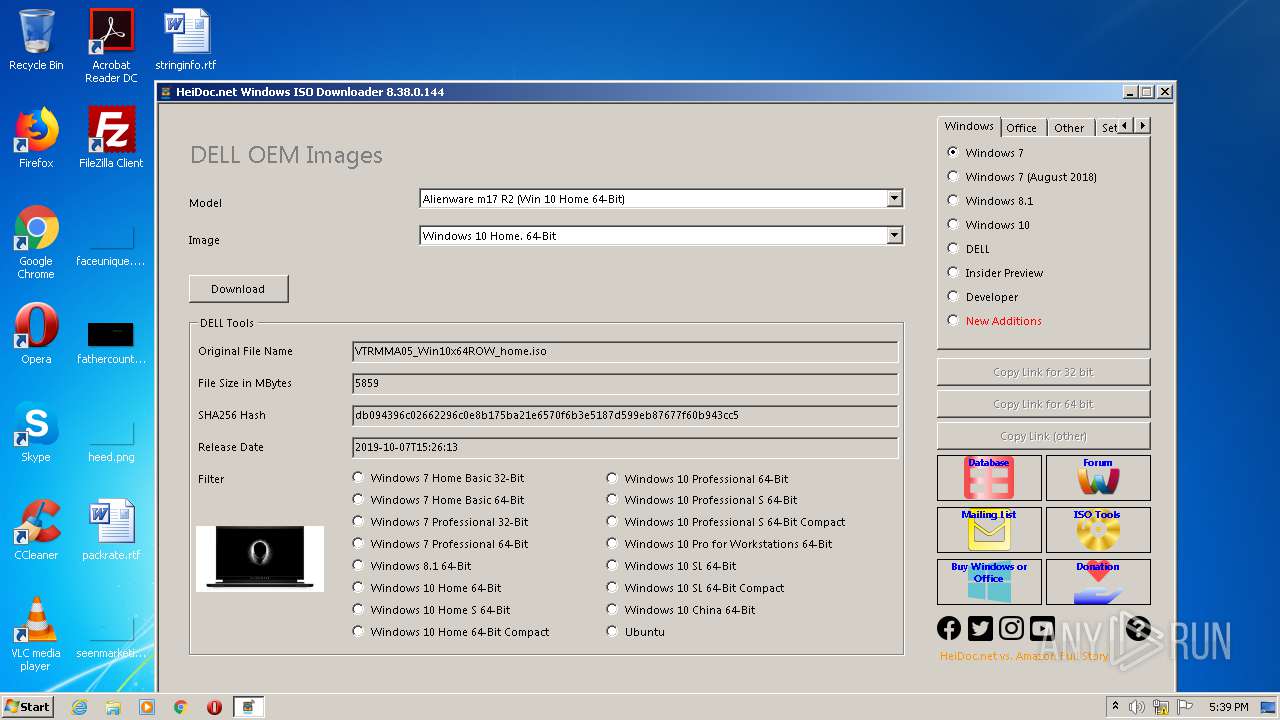
| 2324 | "C:\Program Files\Internet Explorer\iexplore.exe" https://downloads.dell.com/restricted/FOLDER05838541M/1/VTRMMA05_Win10x64ROW_home.iso?authkey=cTicygFUmAd/0e/+a7NVJn91R7PQ6EaWEdpdGWvbffafqkdID/7Upi2NC7h/9ZSx&__gda__=1597527521_93101bb64b86f847ce7b5d2b130d1e22&tkn=TE9cAfSKwI-DgJMtRA1lOHO3kVreKZwtTPQJfkqUq22gF440r8Ujn-V9pBBaGJZyt-2sfFlg9sDbuFhJJMFQHMLywKq_qjave-csUCCImrsq8YszXpiCYXph_6a1AJhSrb-u-9oTYeWZCWFmFQlnInLqw3M09iRrYg&uid=a36e009e-7818-450e-8248-9240f05a22dd | C:\Program Files\Internet Explorer\iexplore.exe | — | Windows-ISO-Downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3140 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1264 CREDAT:3085583 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1936 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
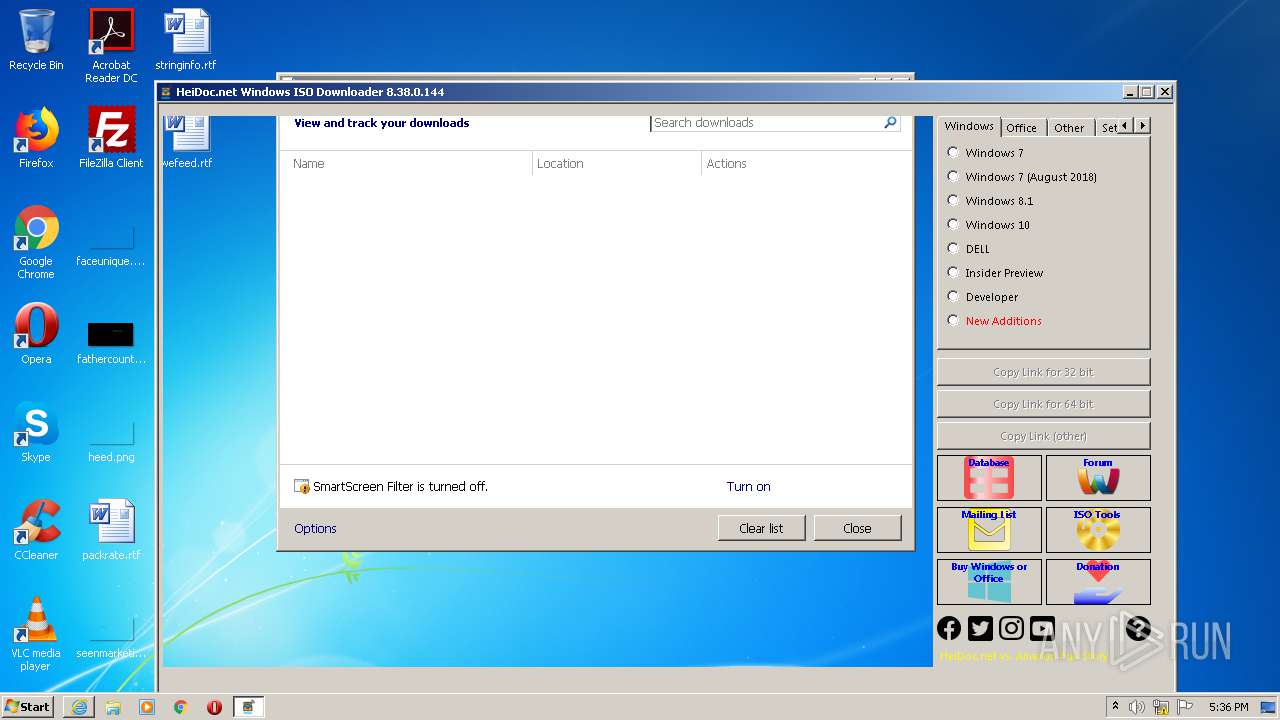
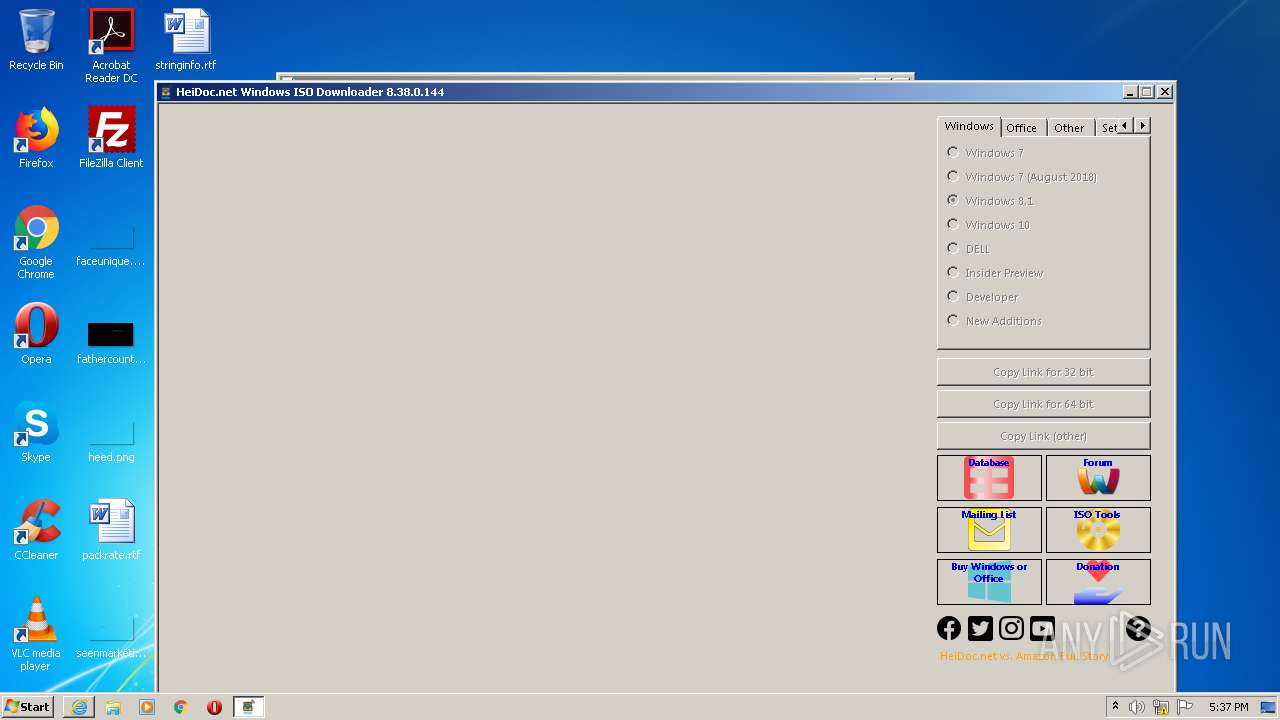
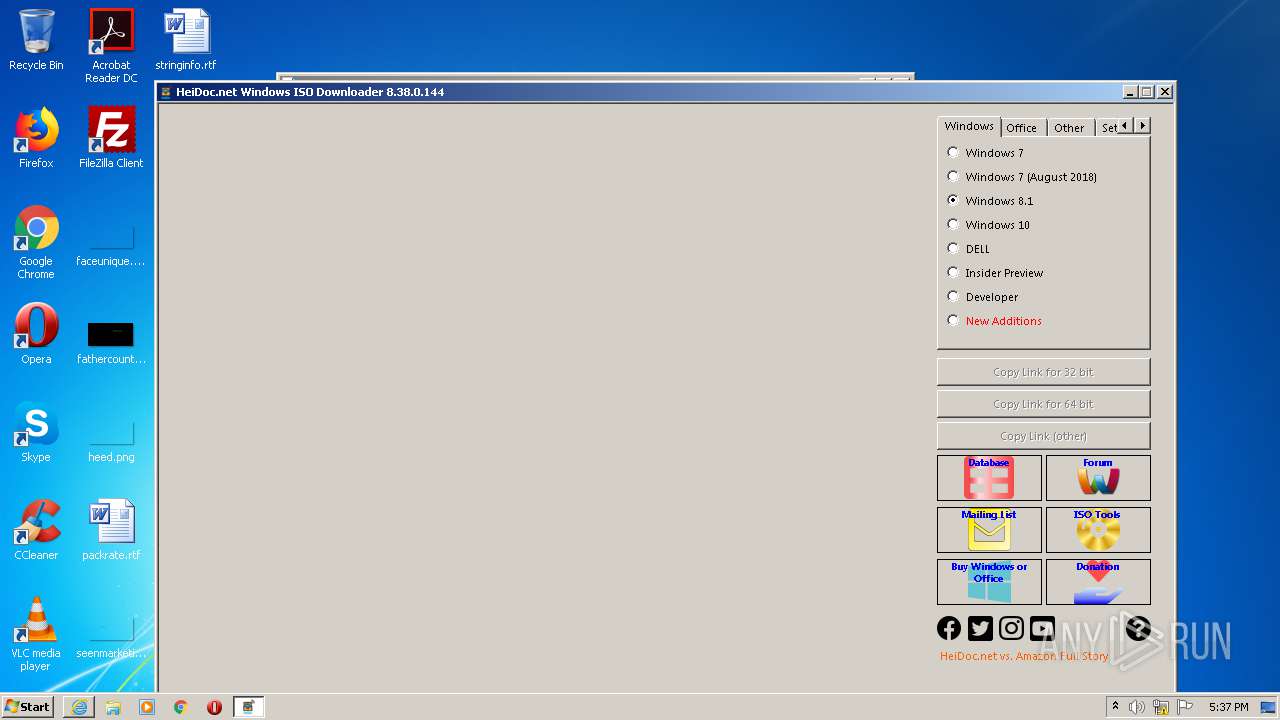
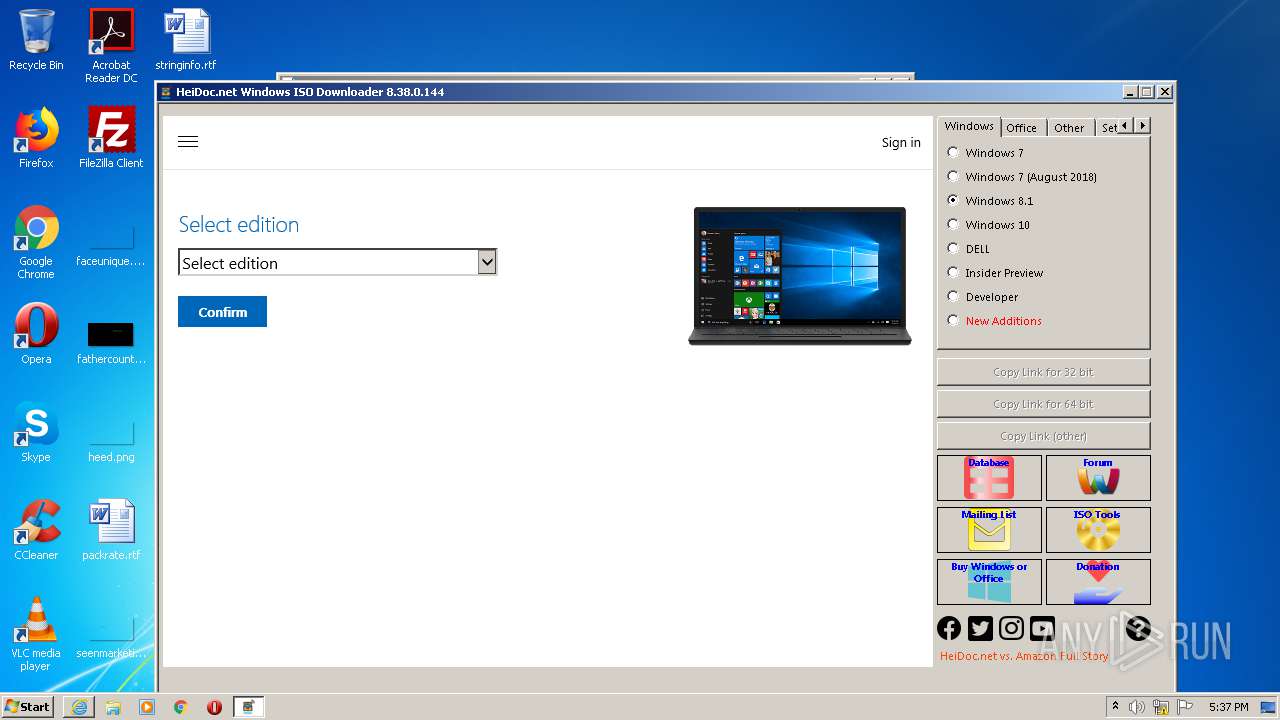
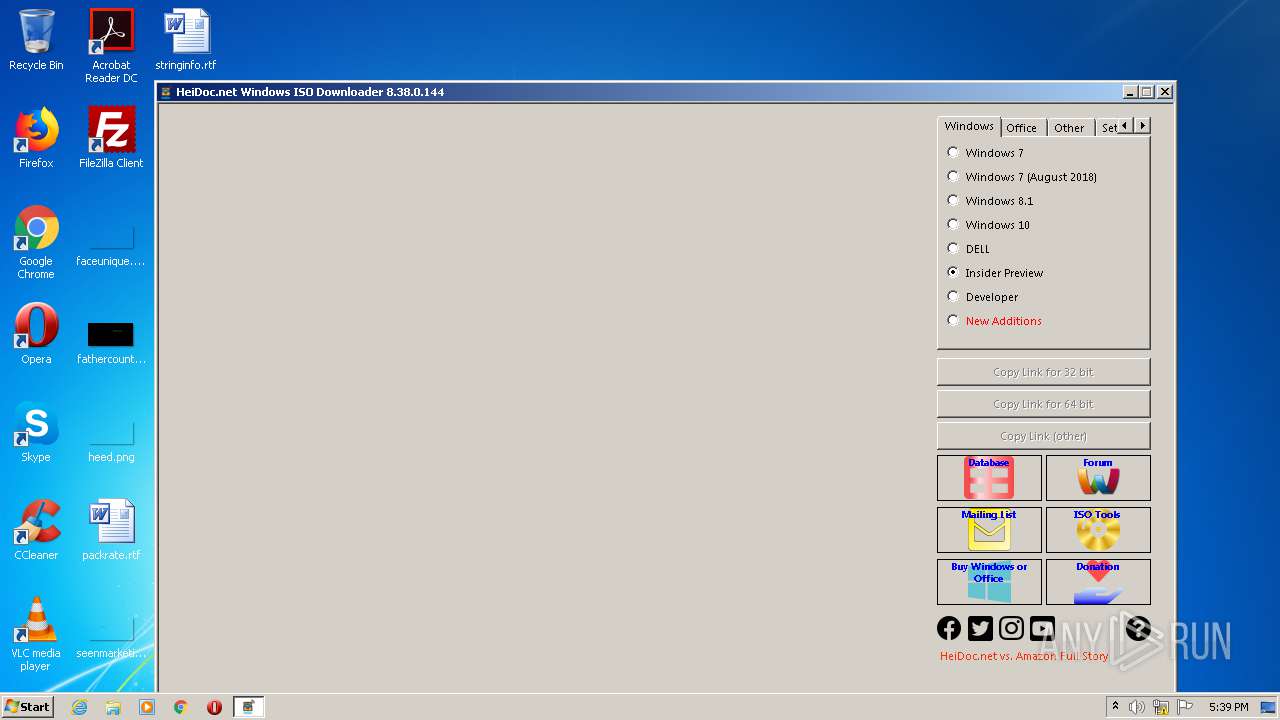
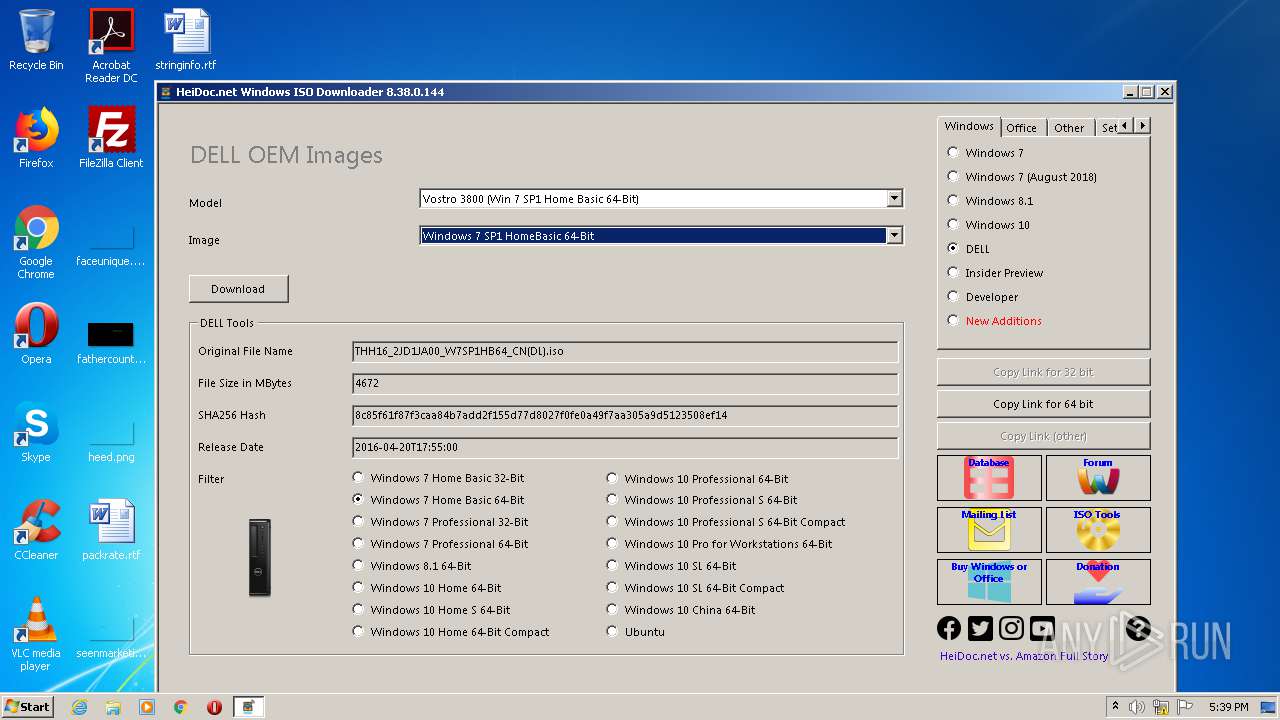
| 3536 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Windows-ISO-Downloader.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Windows-ISO-Downloader.exe | iexplore.exe | ||||||||||||
User: admin Company: HeiDoc V.O.F. Integrity Level: MEDIUM Description: Windows ISO Downloader Exit code: 0 Version: 8.38.0.0144 Modules
| |||||||||||||||
Total events
2 053
Read events
1 797
Write events
239
Delete events
17
Modification events
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1448926876 | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30831394 | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1264) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
60
Text files
72
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab80D2.tmp | — | |
MD5:— | SHA256:— | |||
| 2104 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar80D3.tmp | — | |
MD5:— | SHA256:— | |||
| 1264 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC80E1F63DDA5AE56.TMP | — | |
MD5:— | SHA256:— | |||
| 1264 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Windows-ISO-Downloader.exe.45so91g.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3536 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\Local\Temp\Cab9C49.tmp | — | |
MD5:— | SHA256:— | |||
| 3536 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\Local\Temp\Tar9C4A.tmp | — | |
MD5:— | SHA256:— | |||
| 2104 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | binary | |
MD5:— | SHA256:— | |||
| 1264 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{82171703-DF15-11EA-90BC-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3536 | Windows-ISO-Downloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 1264 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Windows-ISO-Downloader.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
80
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3536 | Windows-ISO-Downloader.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | — | — | whitelisted |
2104 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
3536 | Windows-ISO-Downloader.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCEs0cc0pt0BwIAAAAAc8zc | US | der | 472 b | whitelisted |
3536 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
3536 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
2104 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
3536 | Windows-ISO-Downloader.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDtE0r1Vc%2BgZCAAAAABNnzs%3D | US | der | 471 b | whitelisted |
3536 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3536 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAiIzVJfGSRETRSlgpHeuVI%3D | US | der | 1.47 Kb | whitelisted |
3536 | Windows-ISO-Downloader.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2104 | iexplore.exe | 104.168.147.90:443 | www.heidoc.net | Hostwinds LLC. | US | unknown |
3536 | Windows-ISO-Downloader.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3536 | Windows-ISO-Downloader.exe | 104.168.147.90:443 | www.heidoc.net | Hostwinds LLC. | US | unknown |
3536 | Windows-ISO-Downloader.exe | 172.217.18.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3536 | Windows-ISO-Downloader.exe | 172.217.23.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
3536 | Windows-ISO-Downloader.exe | 172.217.22.78:443 | www.youtube.com | Google Inc. | US | whitelisted |
3536 | Windows-ISO-Downloader.exe | 172.217.22.66:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
3536 | Windows-ISO-Downloader.exe | 172.217.21.230:443 | static.doubleclick.net | Google Inc. | US | whitelisted |
3536 | Windows-ISO-Downloader.exe | 172.217.18.118:443 | i.ytimg.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.heidoc.net |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
aa.online-metrix.net |
| whitelisted |
c.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.youtube.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |