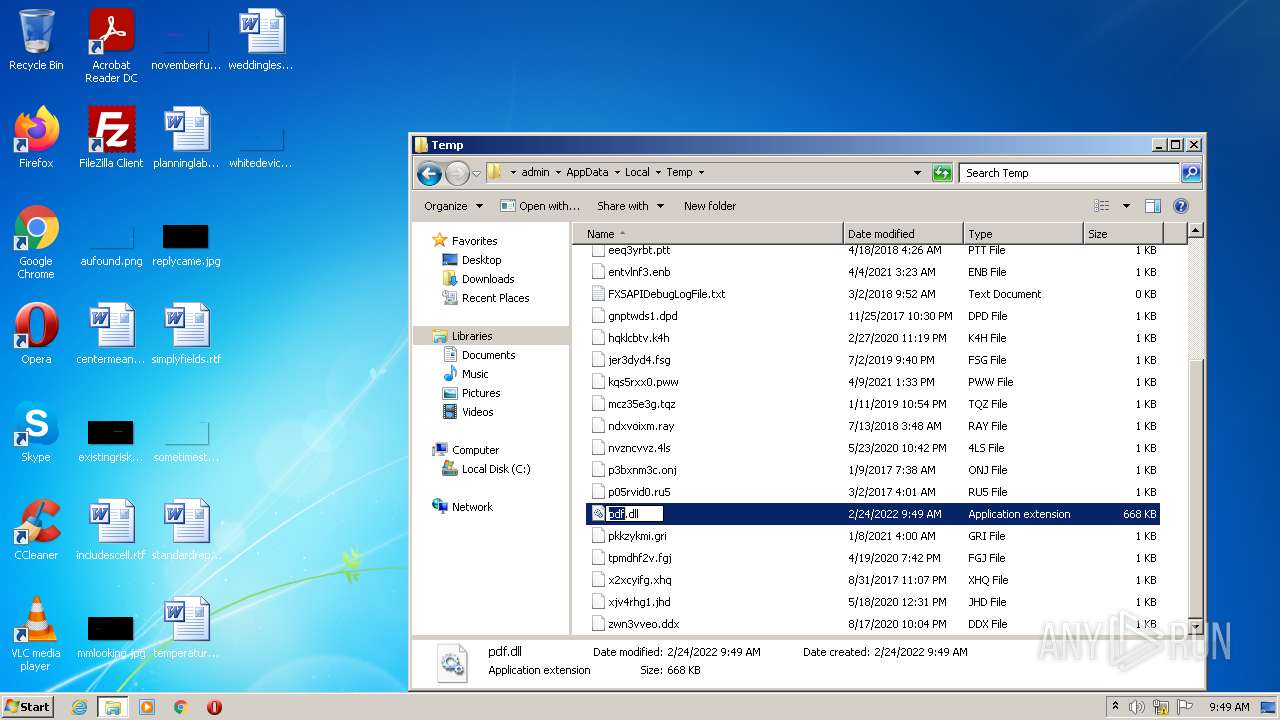
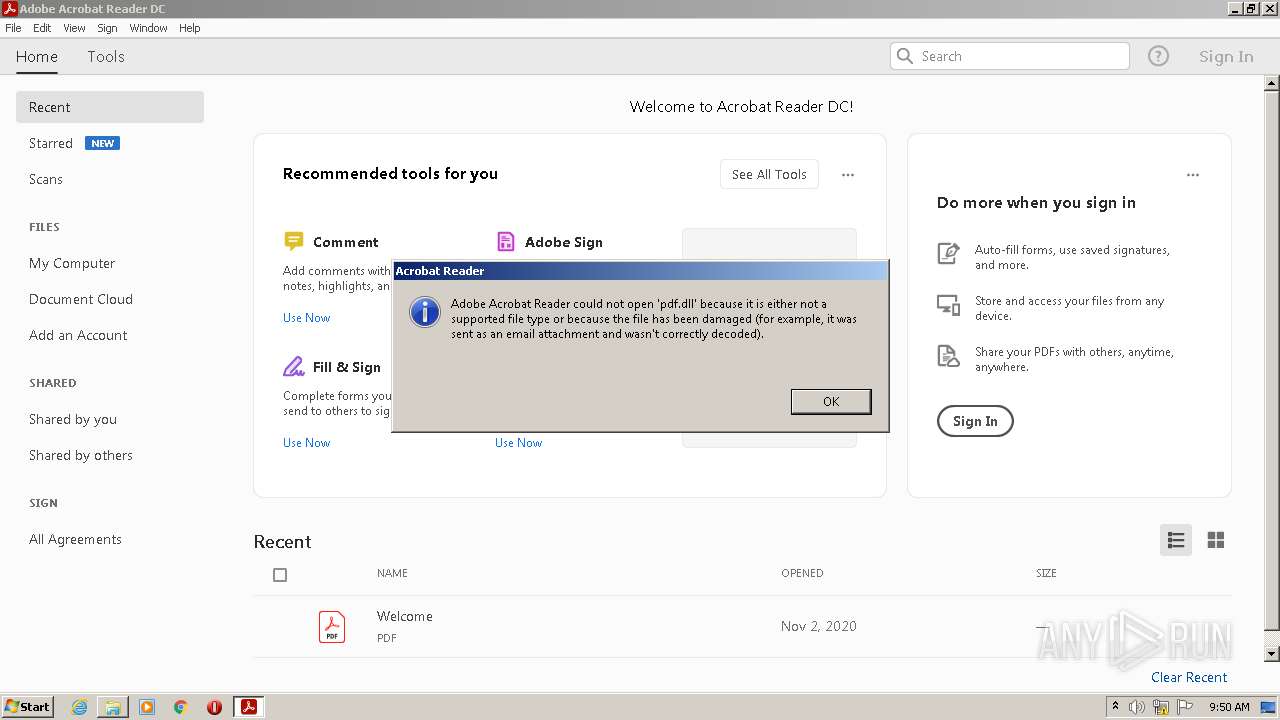
| File name: | pdf.dll |
| Full analysis: | https://app.any.run/tasks/213d913a-d031-47fa-a13e-dd2bcd3c0534 |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2022, 09:48:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | DA5B3014CEACE8E5E161B5219E04ACF5 |
| SHA1: | 15CB2F1E3003EC05340857F1AB3B9A648FDD8187 |
| SHA256: | 0457768F9D8D70FF59275C27BC99D45C1C48CF1E932D29C3F2E9D5E037ACD802 |
| SSDEEP: | 12288:6Ky+46ehnVmcYF7YekzSyjoPipgWOaN6oJt6cptSien3kiFeBNXb0jc/:6J6e5VDYF7Yek/oP+MGrMcpK0iFeB2j |
MALICIOUS
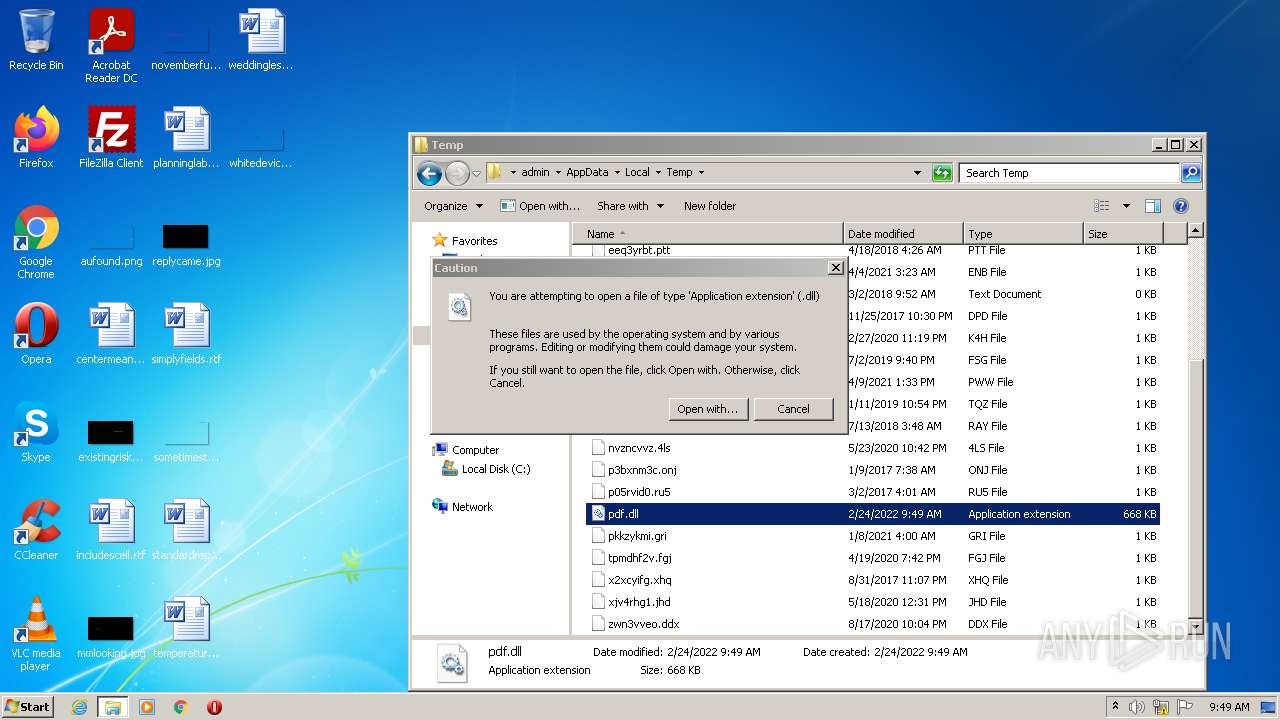
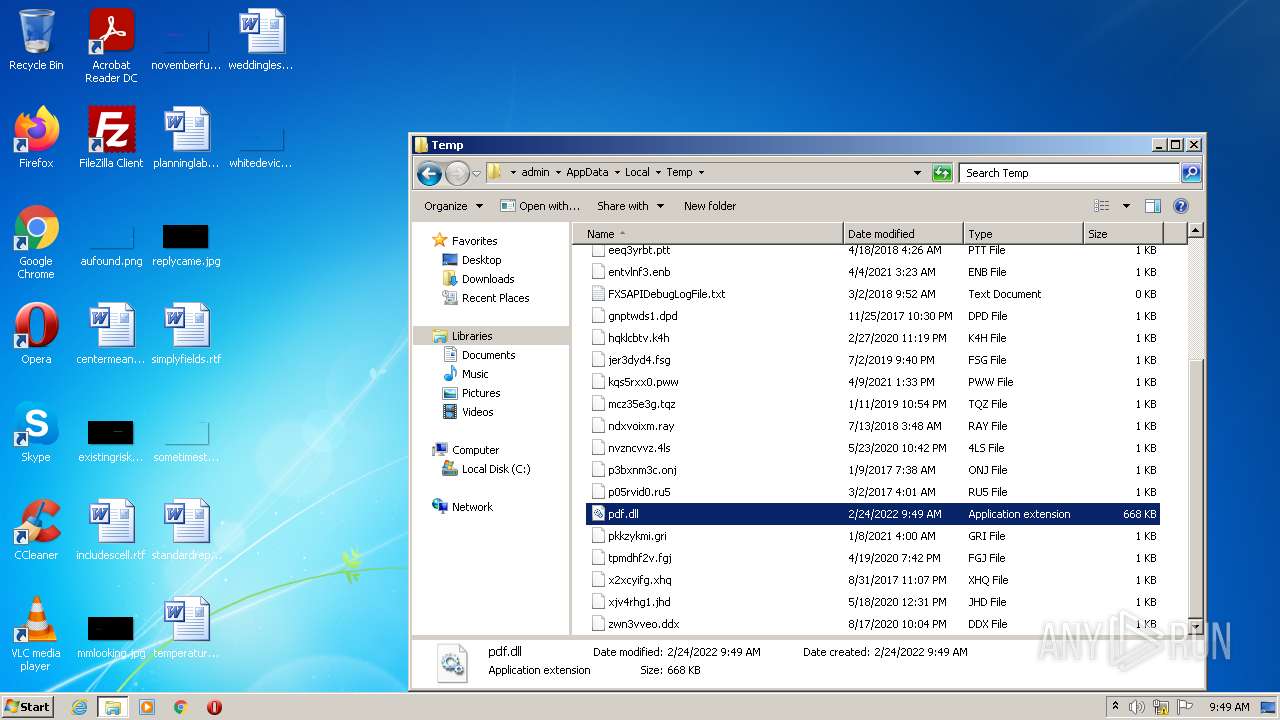
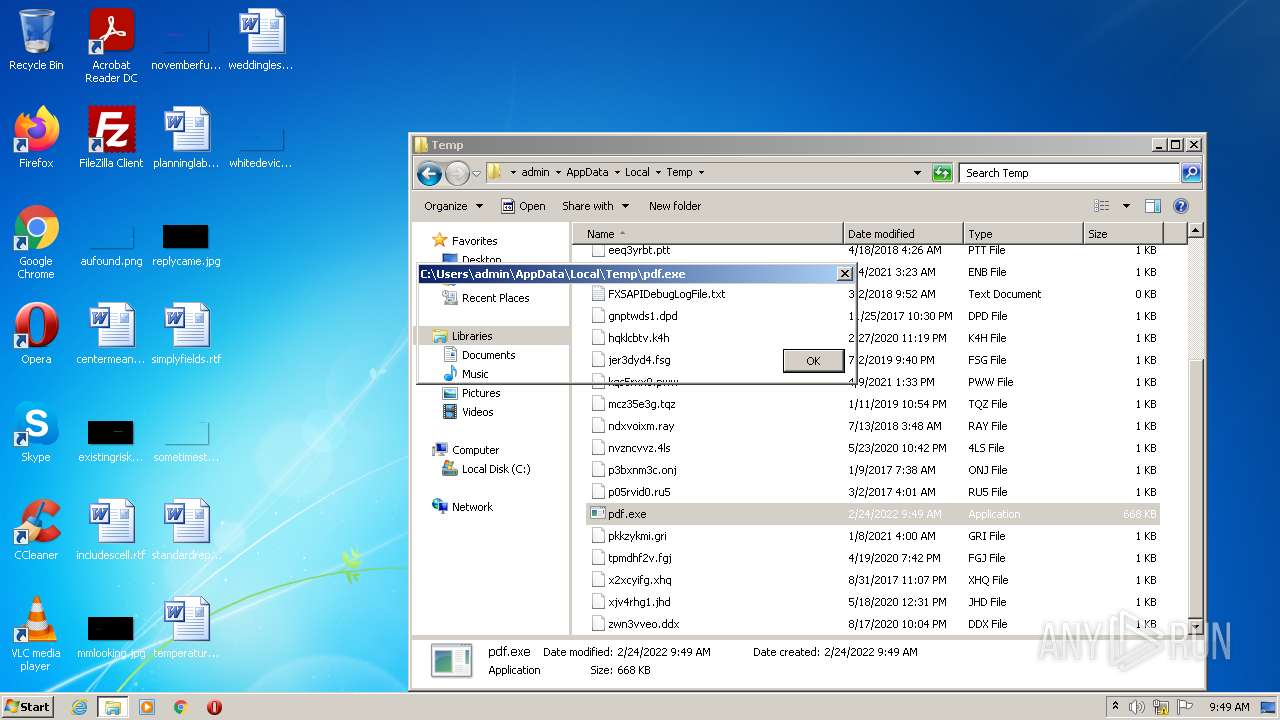
Registers / Runs the DLL via REGSVR32.EXE
- Explorer.EXE (PID: 584)
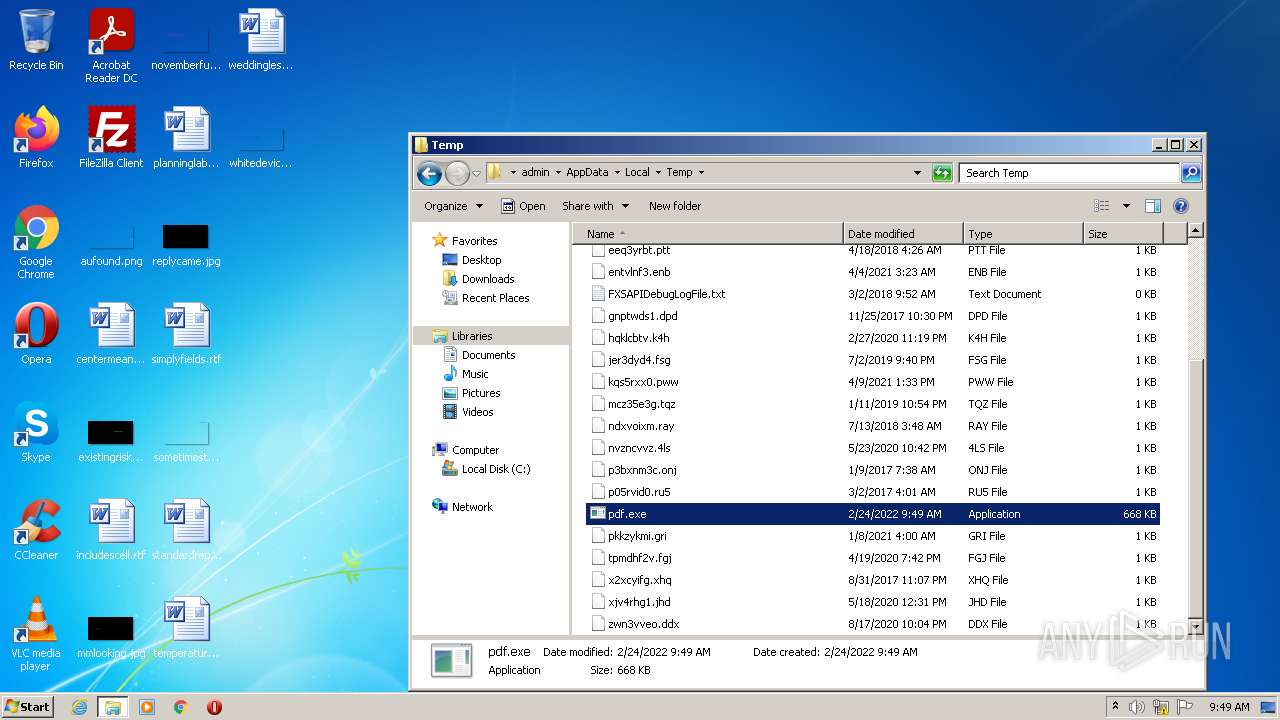
Loads dropped or rewritten executable
- WerFault.exe (PID: 3312)
- Explorer.EXE (PID: 584)
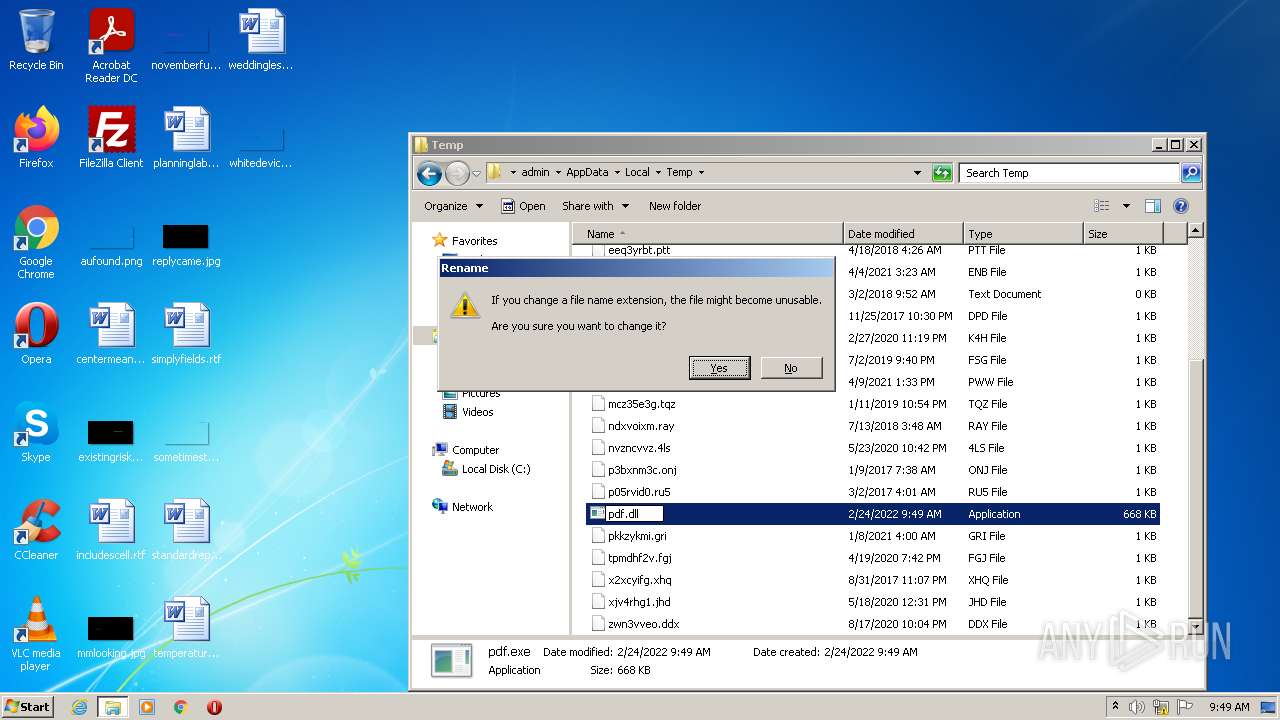
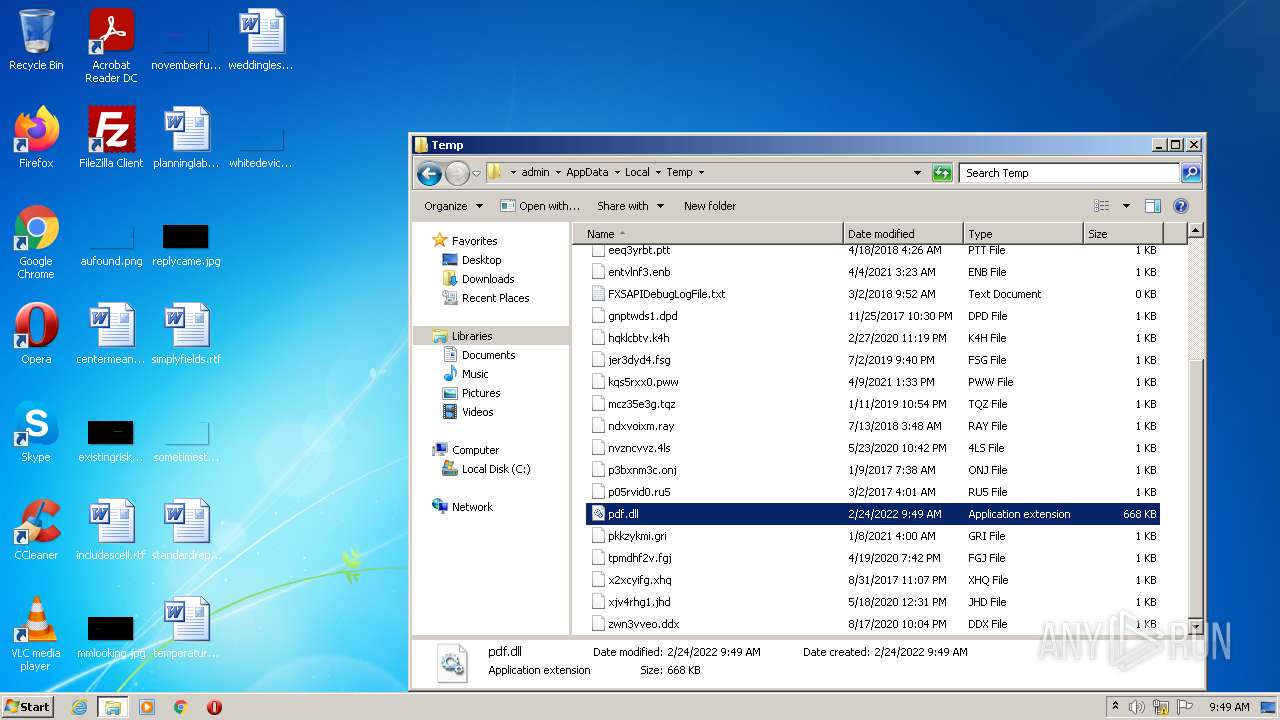
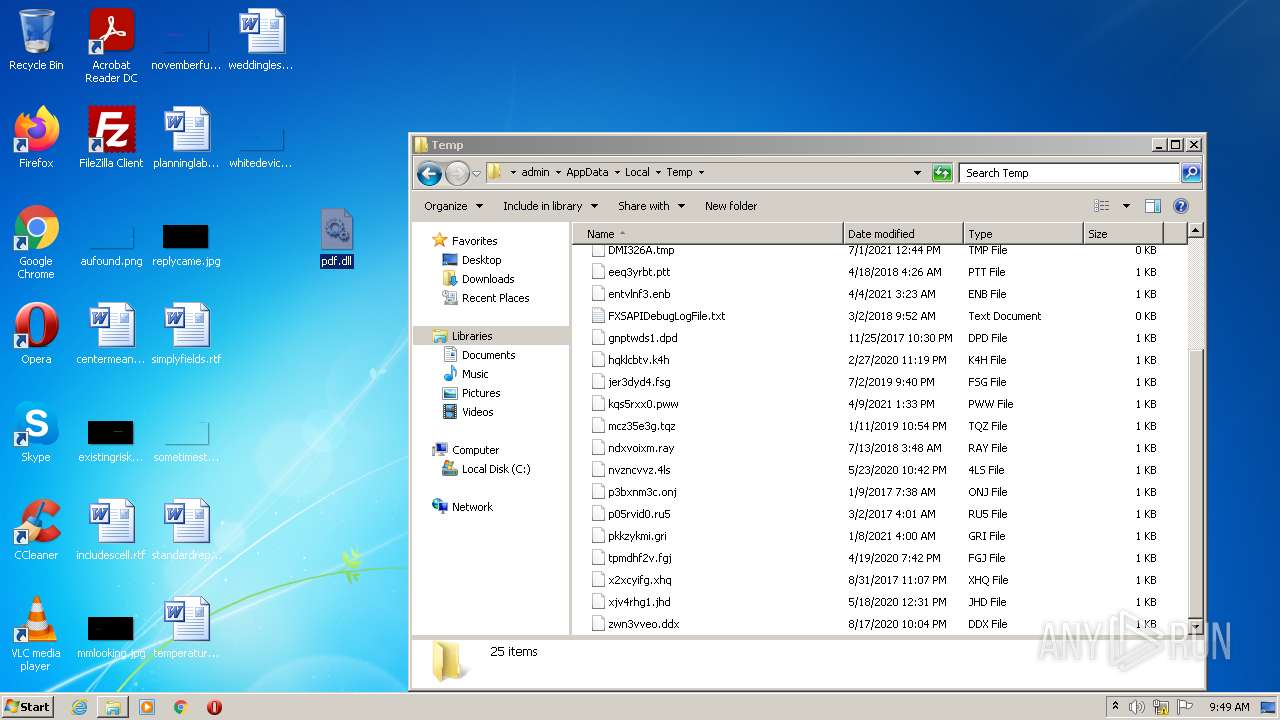
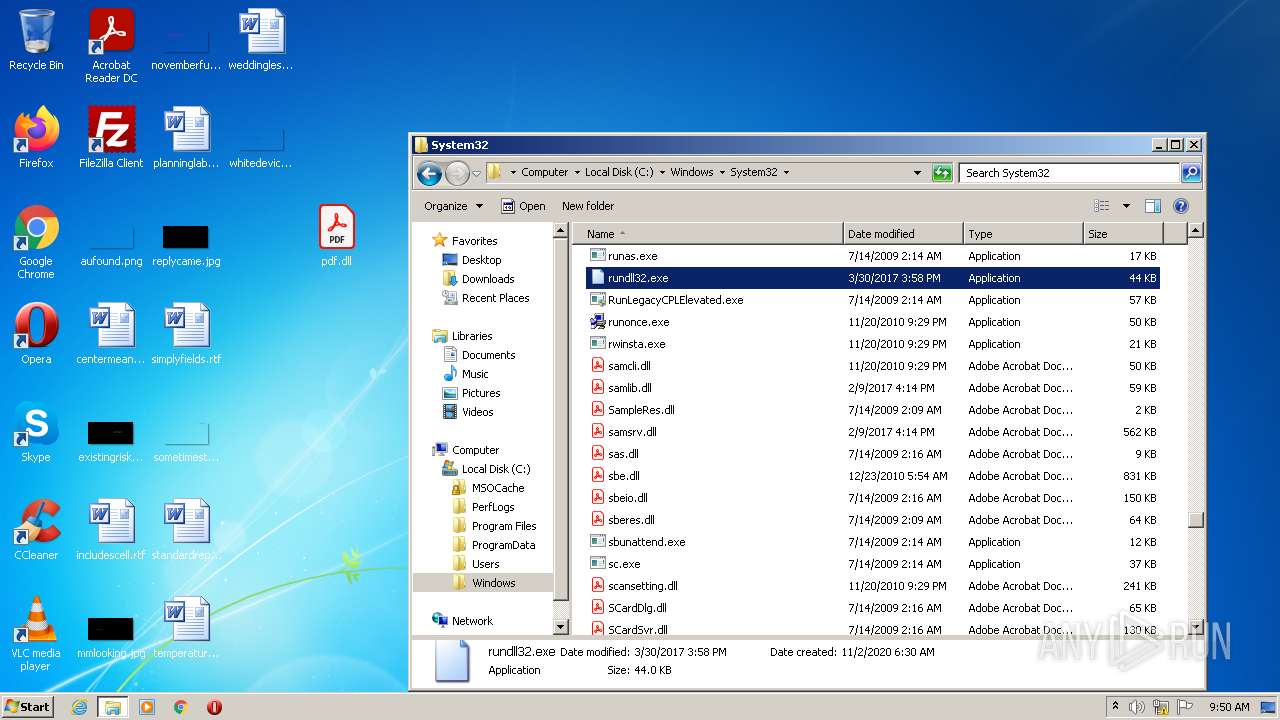
Drops executable file immediately after starts
- Explorer.EXE (PID: 584)
SUSPICIOUS
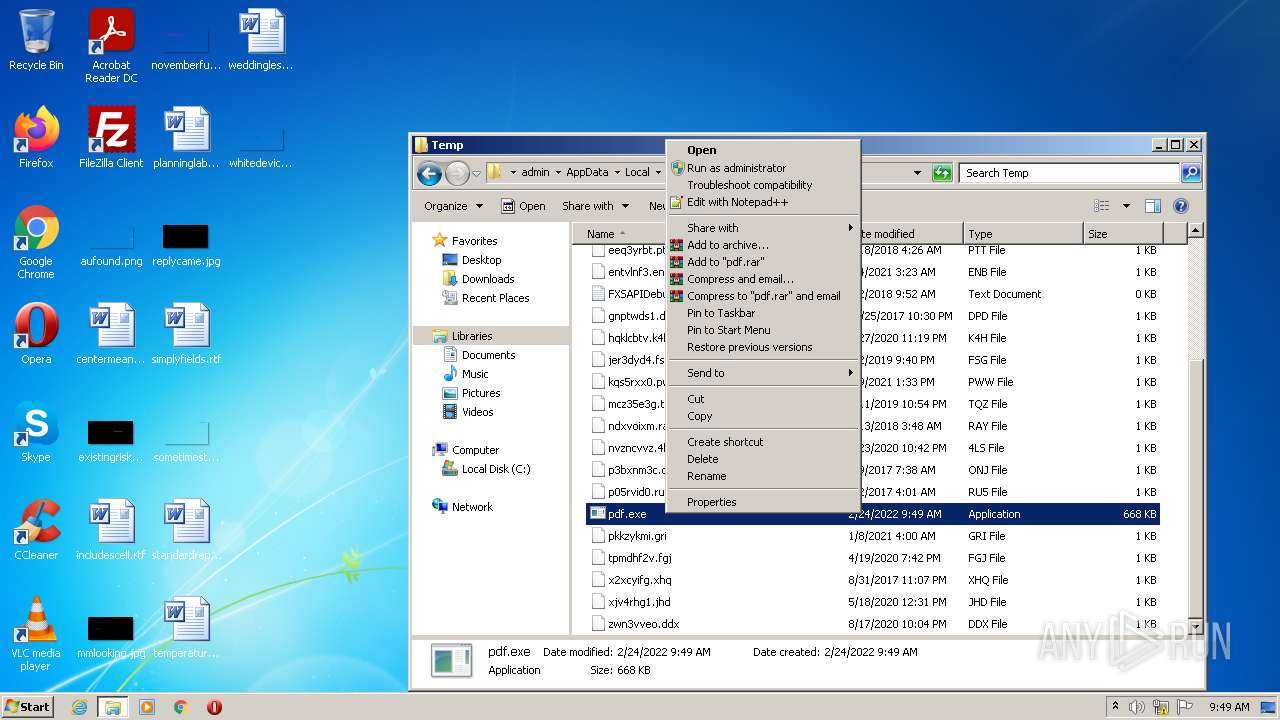
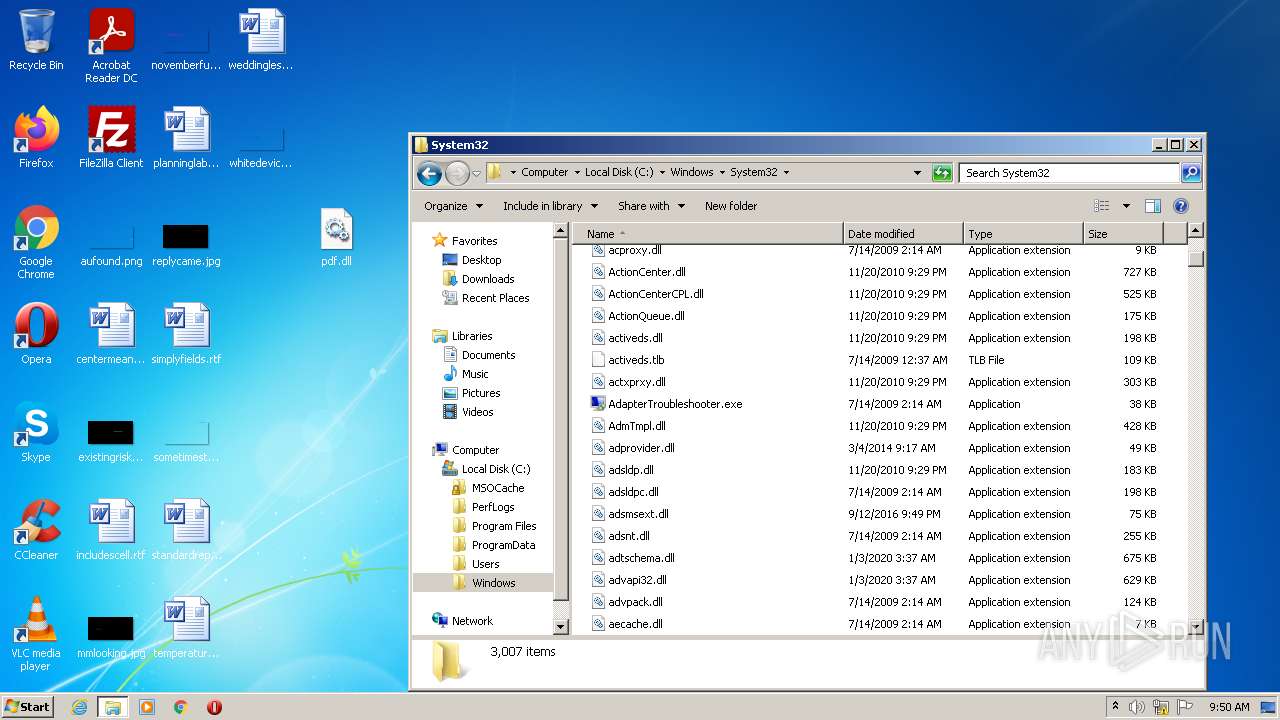
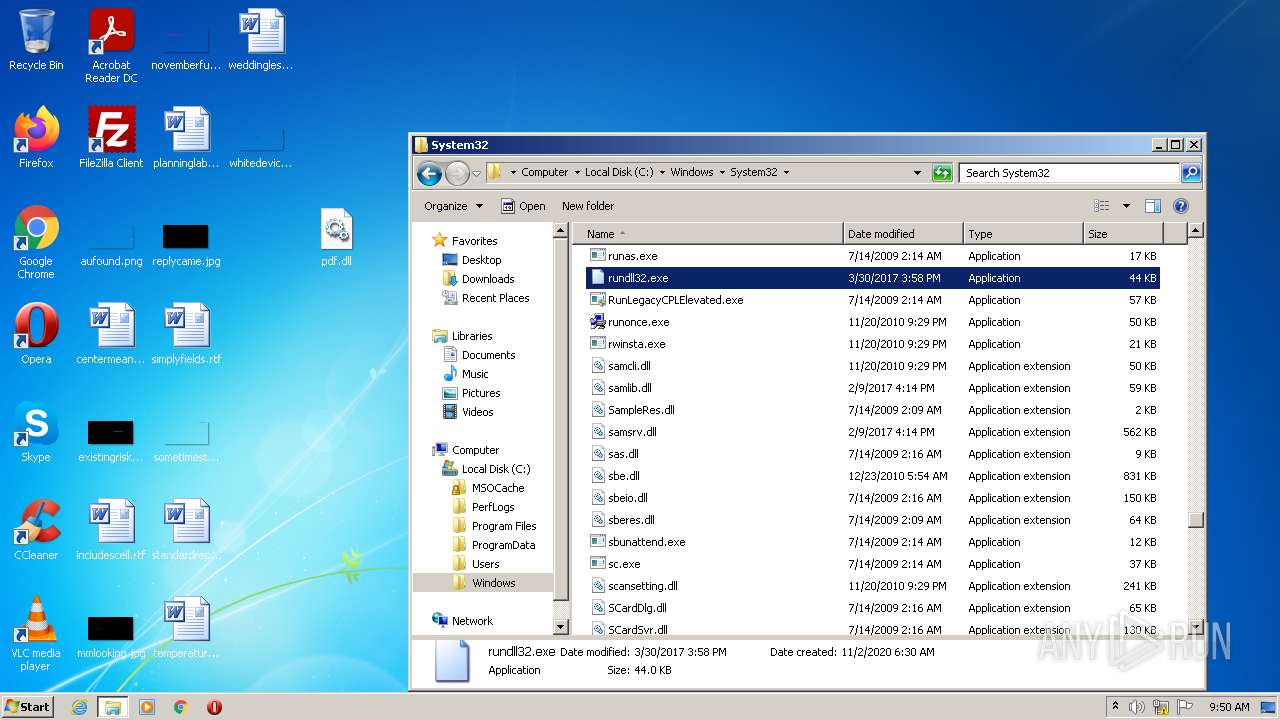
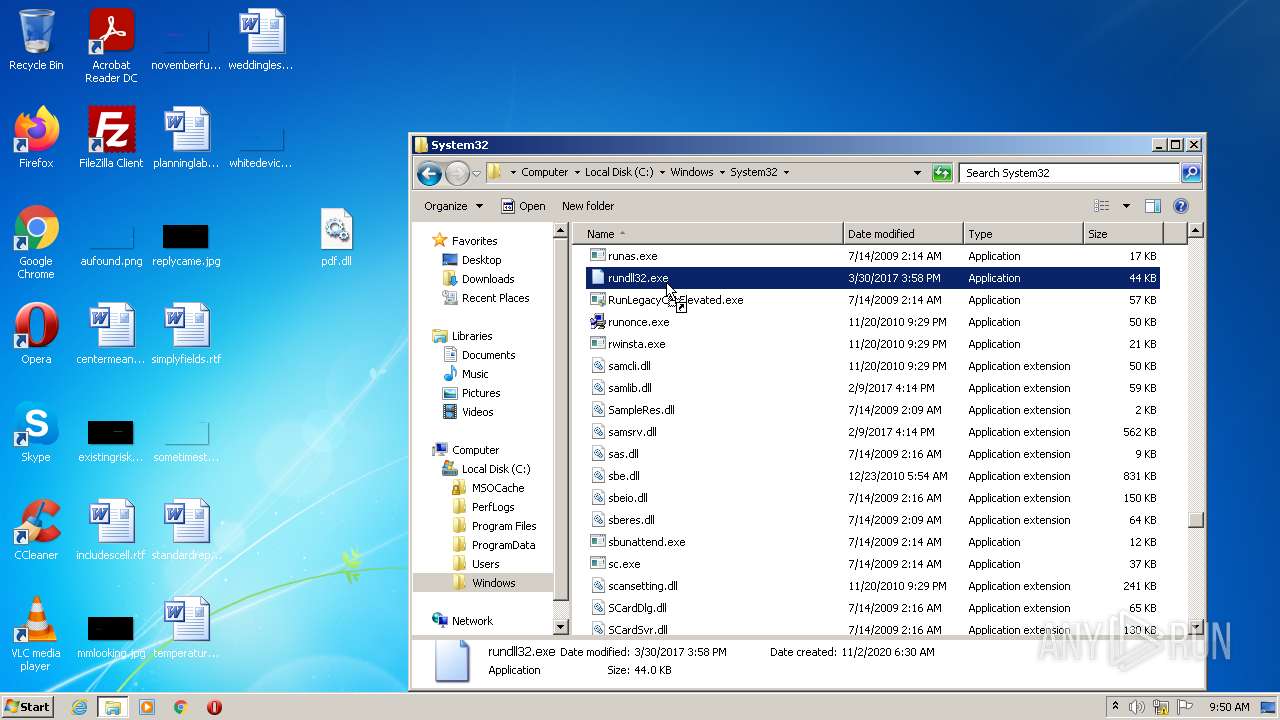
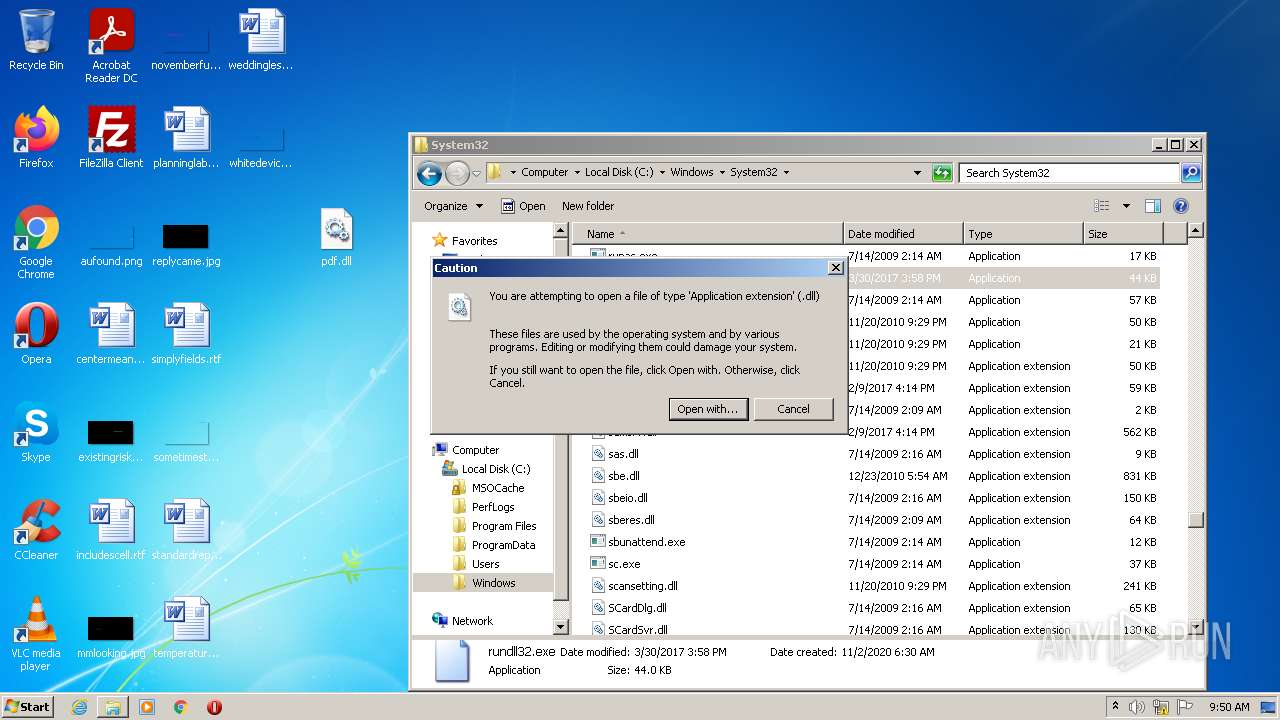
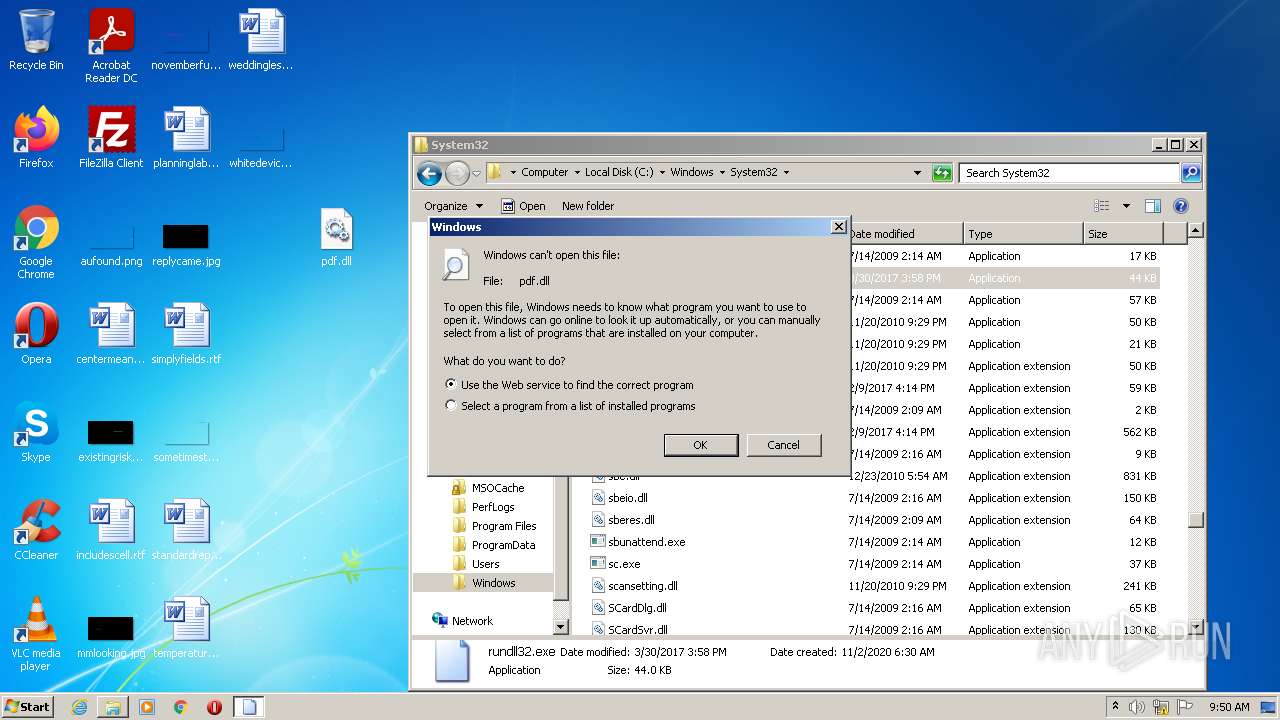
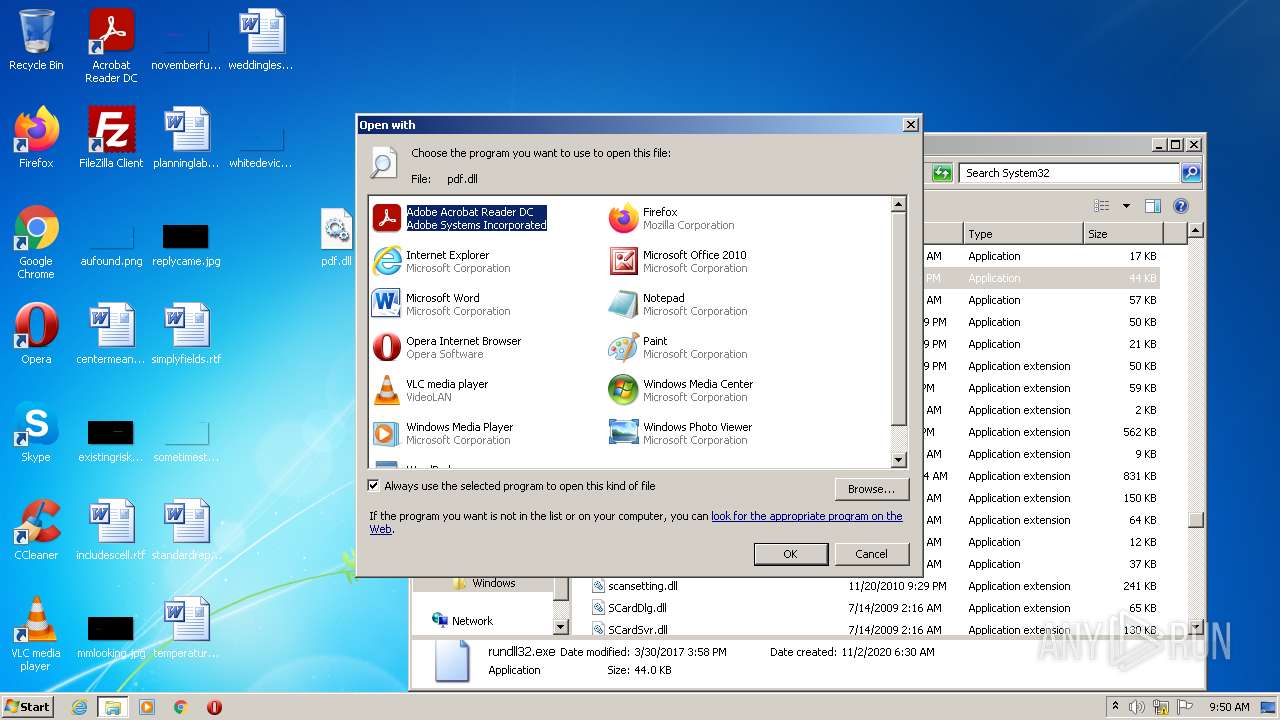
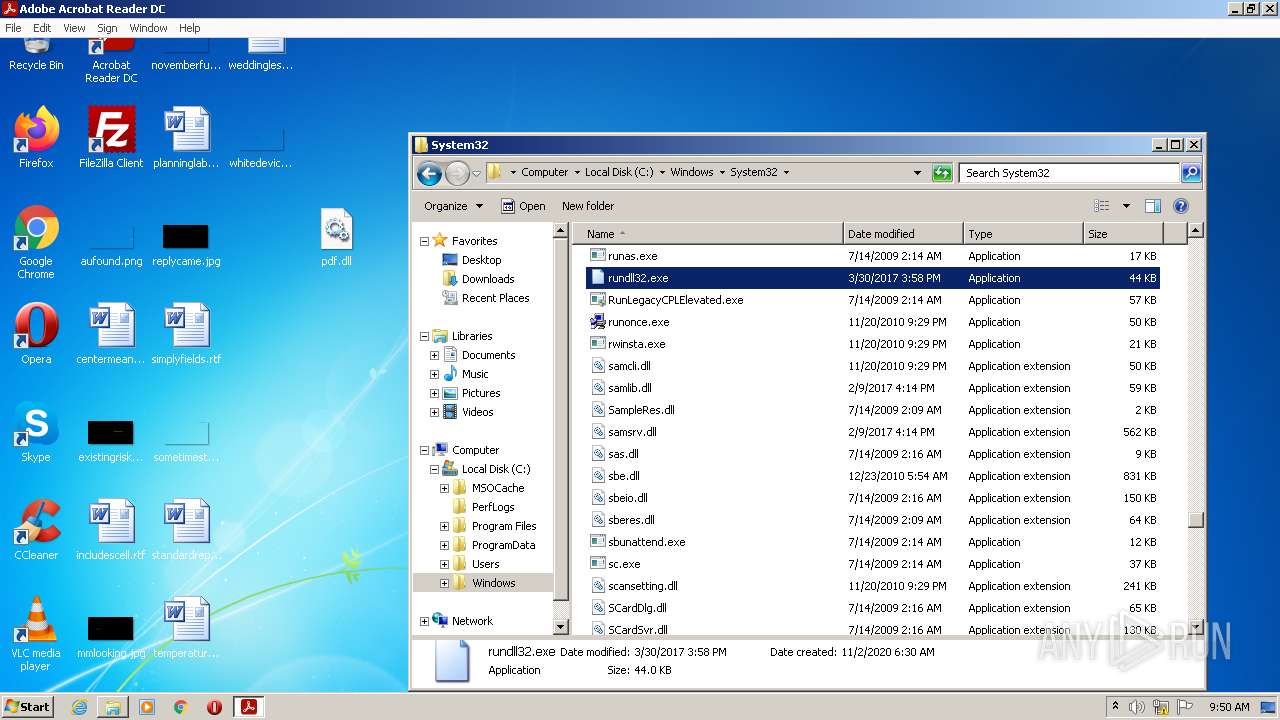
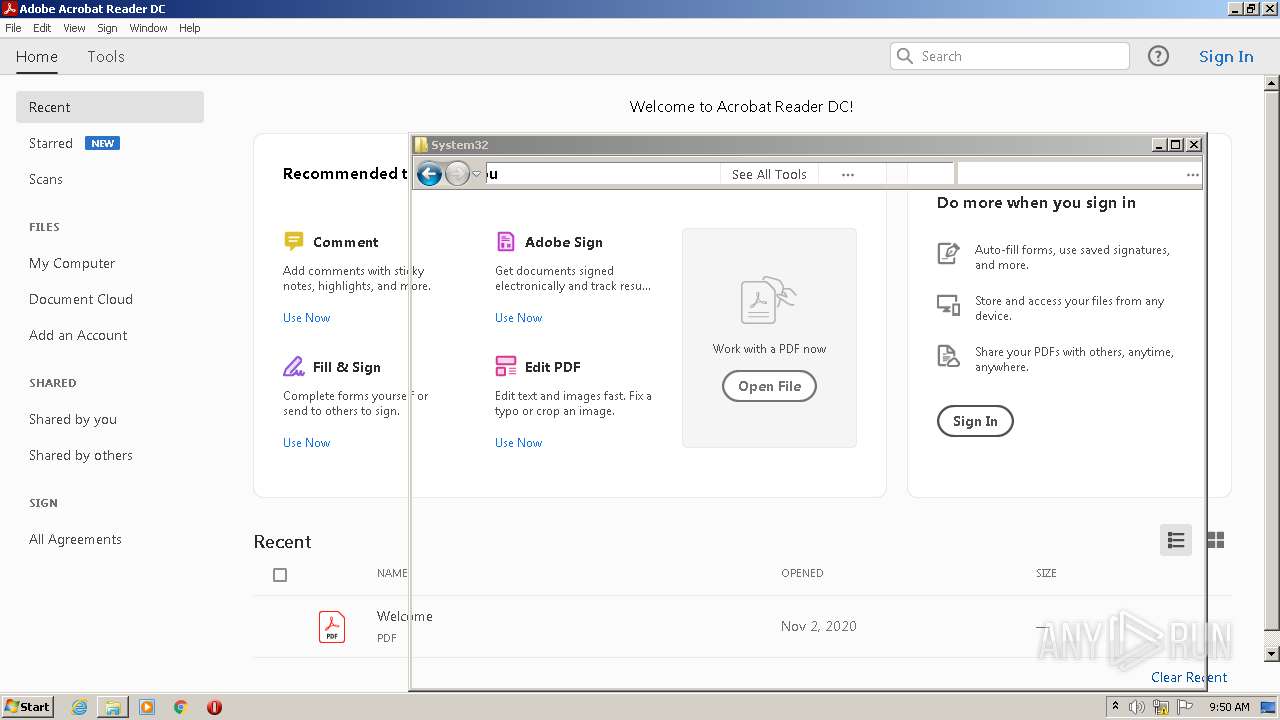
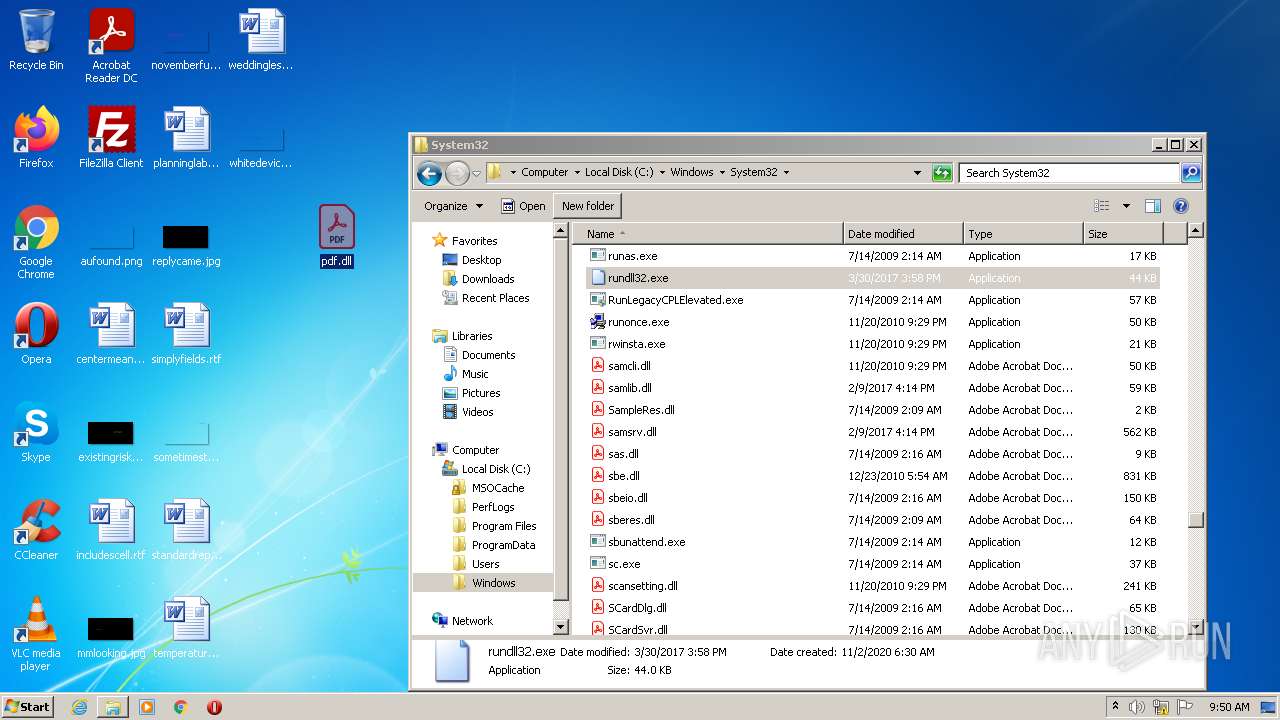
Uses RUNDLL32.EXE to load library
- Explorer.EXE (PID: 584)
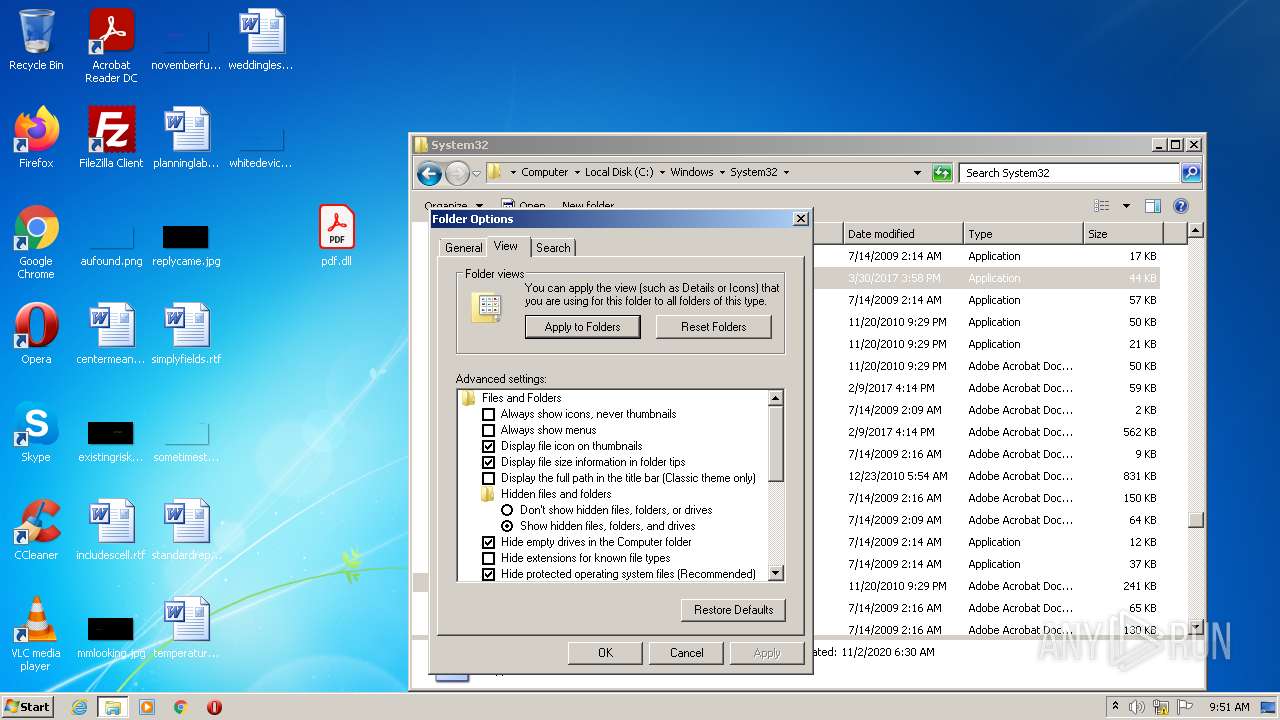
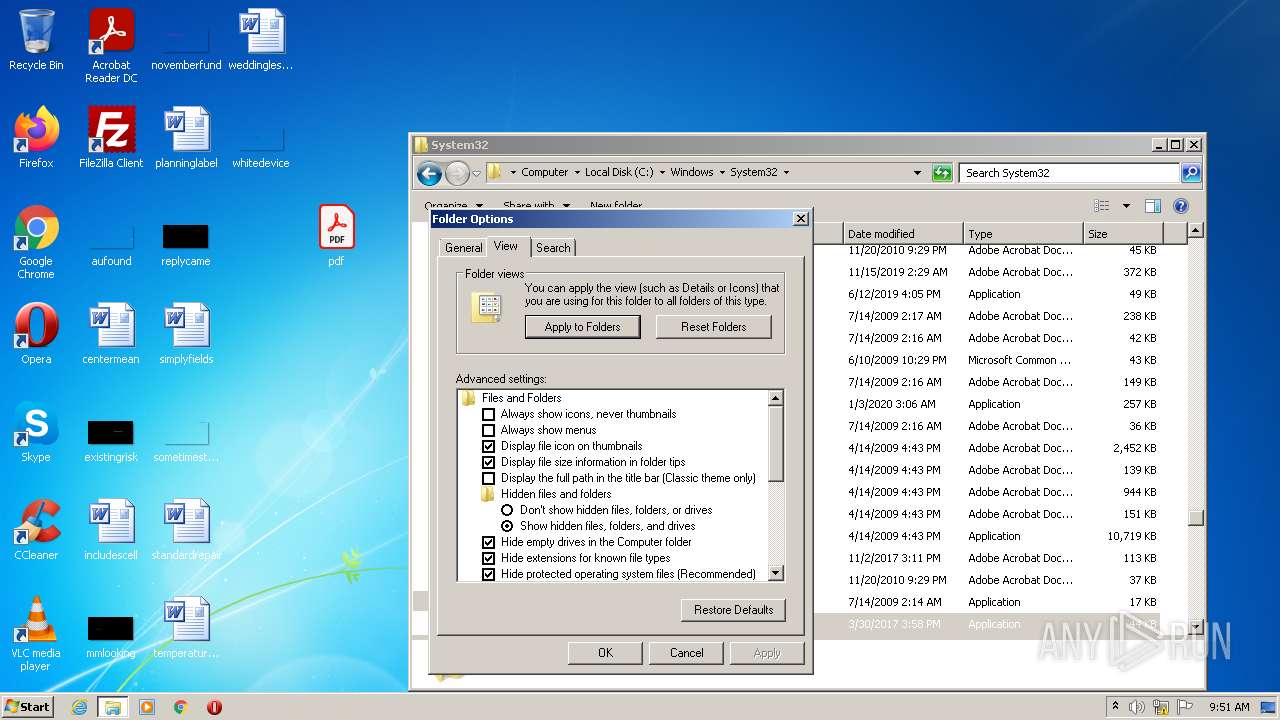
Reads the date of Windows installation
- rundll32.exe (PID: 1628)
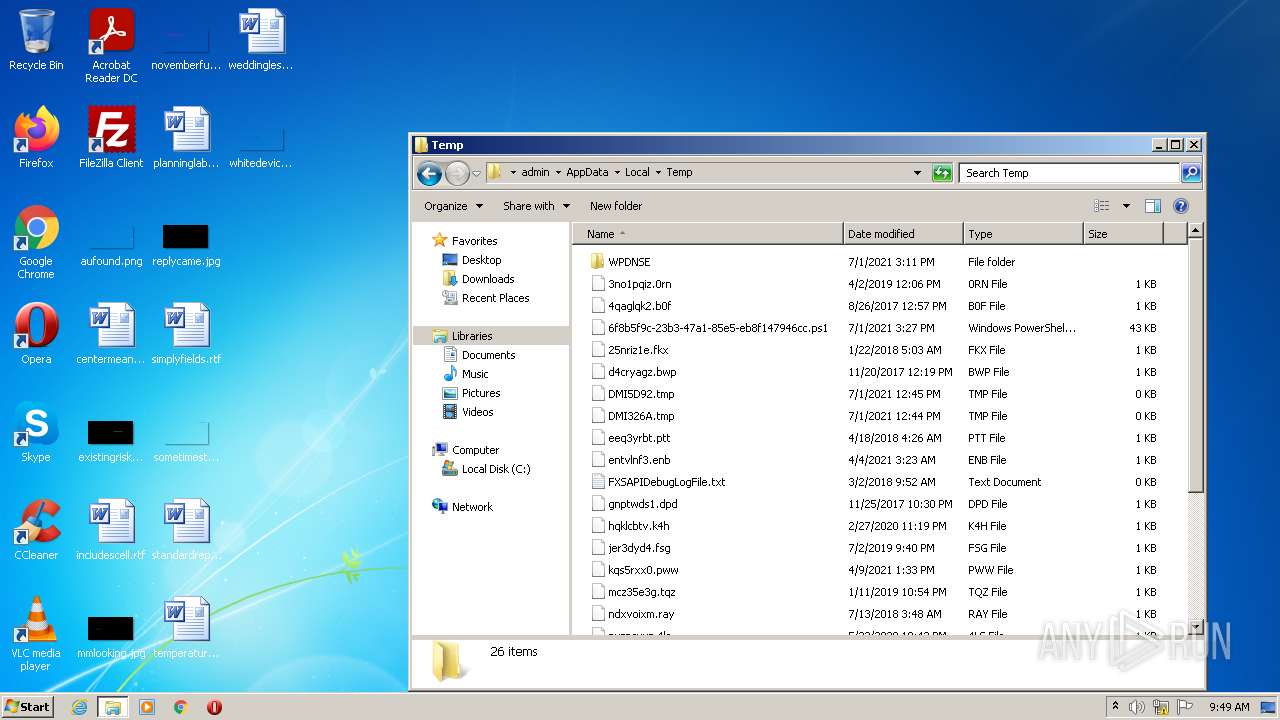
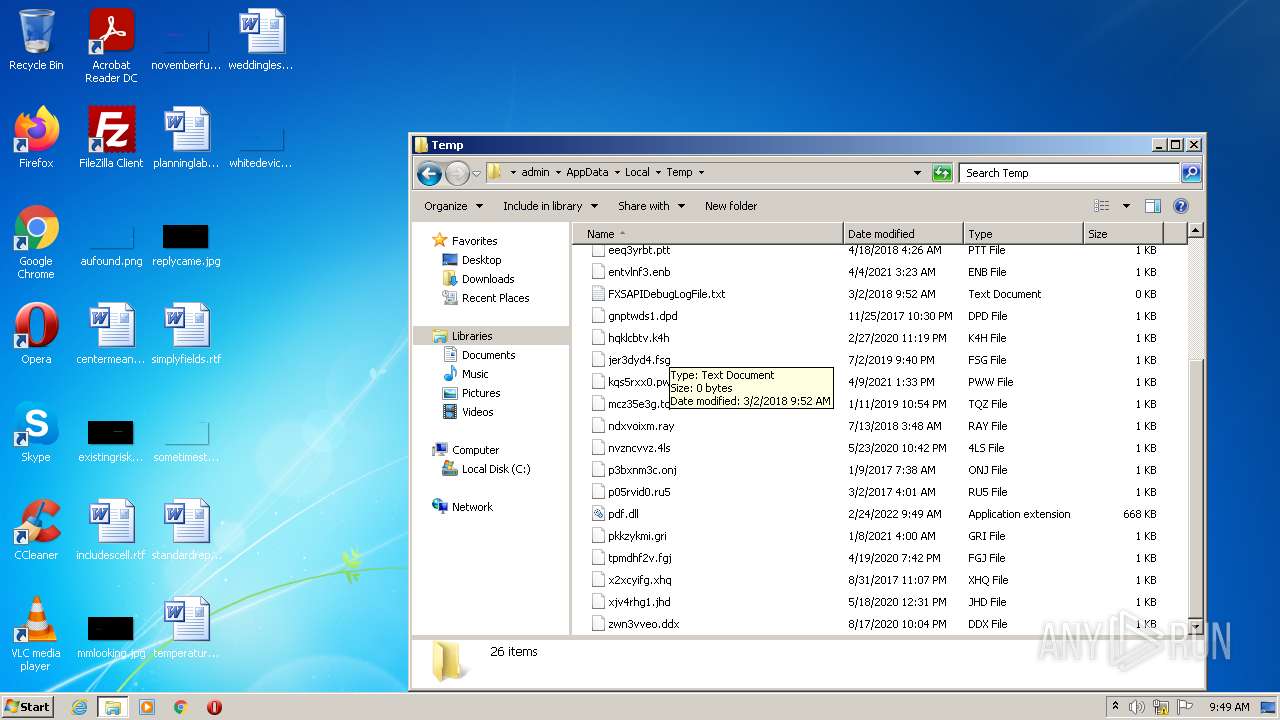
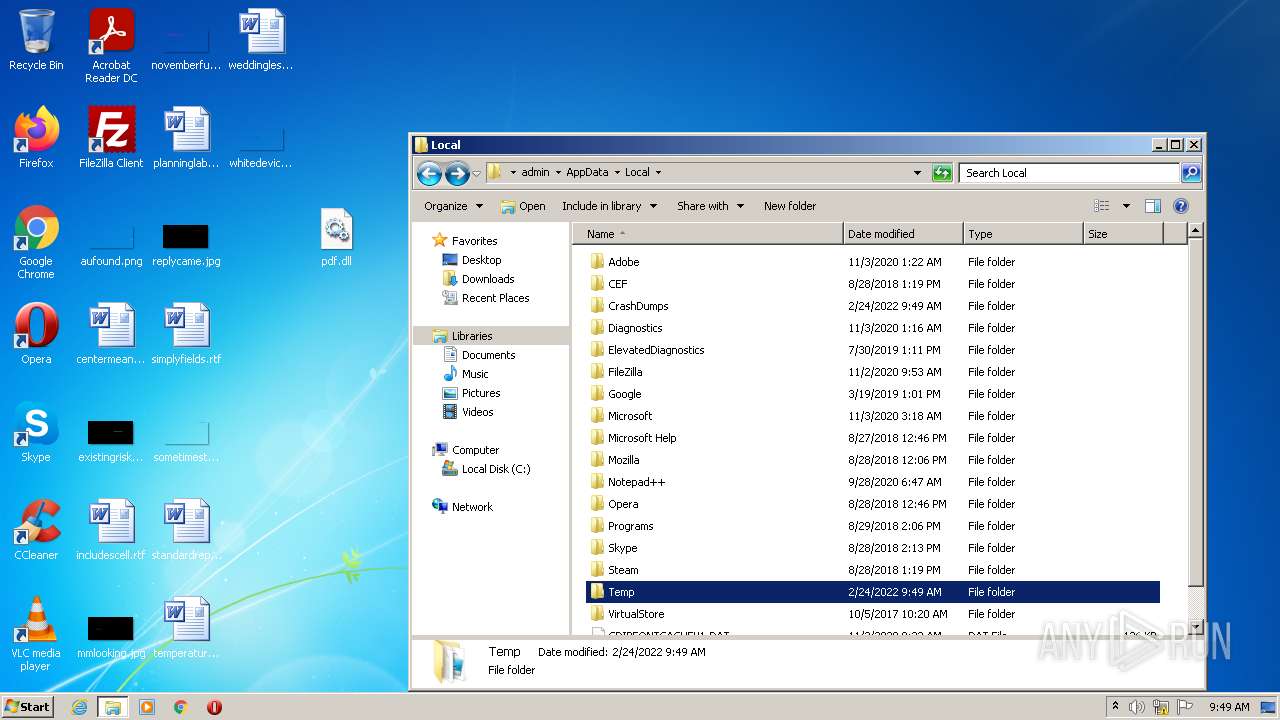
Creates files in the user directory
- Explorer.EXE (PID: 584)
Reads default file associations for system extensions
- Explorer.EXE (PID: 584)
Executable content was dropped or overwritten
- Explorer.EXE (PID: 584)
INFO
Manual execution by user
- explorer.exe (PID: 2156)
Checks supported languages
- WerFault.exe (PID: 3312)
- regsvr32.exe (PID: 2316)
- Explorer.EXE (PID: 584)
- explorer.exe (PID: 2156)
- rundll32.exe (PID: 3896)
- rundll32.exe (PID: 560)
- rundll32.exe (PID: 2844)
- AcroRd32.exe (PID: 3008)
- rundll32.exe (PID: 1628)
- AcroRd32.exe (PID: 3444)
- RdrCEF.exe (PID: 3876)
- RdrCEF.exe (PID: 2720)
- RdrCEF.exe (PID: 2148)
- RdrCEF.exe (PID: 1896)
- RdrCEF.exe (PID: 408)
Loads main object executable
- regsvr32.exe (PID: 2316)
Reads the computer name
- WerFault.exe (PID: 3312)
- explorer.exe (PID: 2156)
- rundll32.exe (PID: 3896)
- rundll32.exe (PID: 560)
- rundll32.exe (PID: 1628)
- AcroRd32.exe (PID: 3444)
- AcroRd32.exe (PID: 3008)
- RdrCEF.exe (PID: 3876)
Reads Microsoft Office registry keys
- Explorer.EXE (PID: 584)
Searches for installed software
- AcroRd32.exe (PID: 3008)
- AcroRd32.exe (PID: 3444)
Reads CPU info
- AcroRd32.exe (PID: 3444)
Checks Windows Trust Settings
- AcroRd32.exe (PID: 3008)
Reads settings of System Certificates
- AcroRd32.exe (PID: 3008)
Reads the hosts file
- RdrCEF.exe (PID: 3876)
Application launched itself
- RdrCEF.exe (PID: 3876)
- AcroRd32.exe (PID: 3008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x0000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 28672 |
| CodeSize: | 223744 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2021:11:27 14:27:21+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Nov-2021 13:27:21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Nov-2021 13:27:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00036842 | 0x00036A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47248 |
.rdata | 0x00038000 | 0x00006482 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.81363 |
.data | 0x0003F000 | 0x00000248 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.21825 |
.reloc | 0x00040000 | 0x0000051C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.24781 |
.data2 | 0x00041000 | 0x0006916D | 0x00069200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99953 |
Imports
KERNEL32.dll |
SHELL32.dll |
ntdll.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
DllCanUnloadNow | 1 | 0x000361A5 |
DllGetClassObject | 2 | 0x00017ACE |
DllRegisterServer | 3 | 0x00022D70 |
DllUnregisterServer | 4 | 0x0001C10D |
GetProxyDllInfo | 5 | 0x00033B0E |
Total processes
58
Monitored processes
15
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1064,17970245080642408806,12189011376816108035,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=1130552852400021389 --mojo-platform-channel-handle=1472 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 560 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\pdf.dll | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1628 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\pdf.dll | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1064,17970245080642408806,12189011376816108035,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=6103371467146880601 --mojo-platform-channel-handle=1264 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1064,17970245080642408806,12189011376816108035,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4665303810266547856 --renderer-client-id=2 --mojo-platform-channel-handle=1188 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2156 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
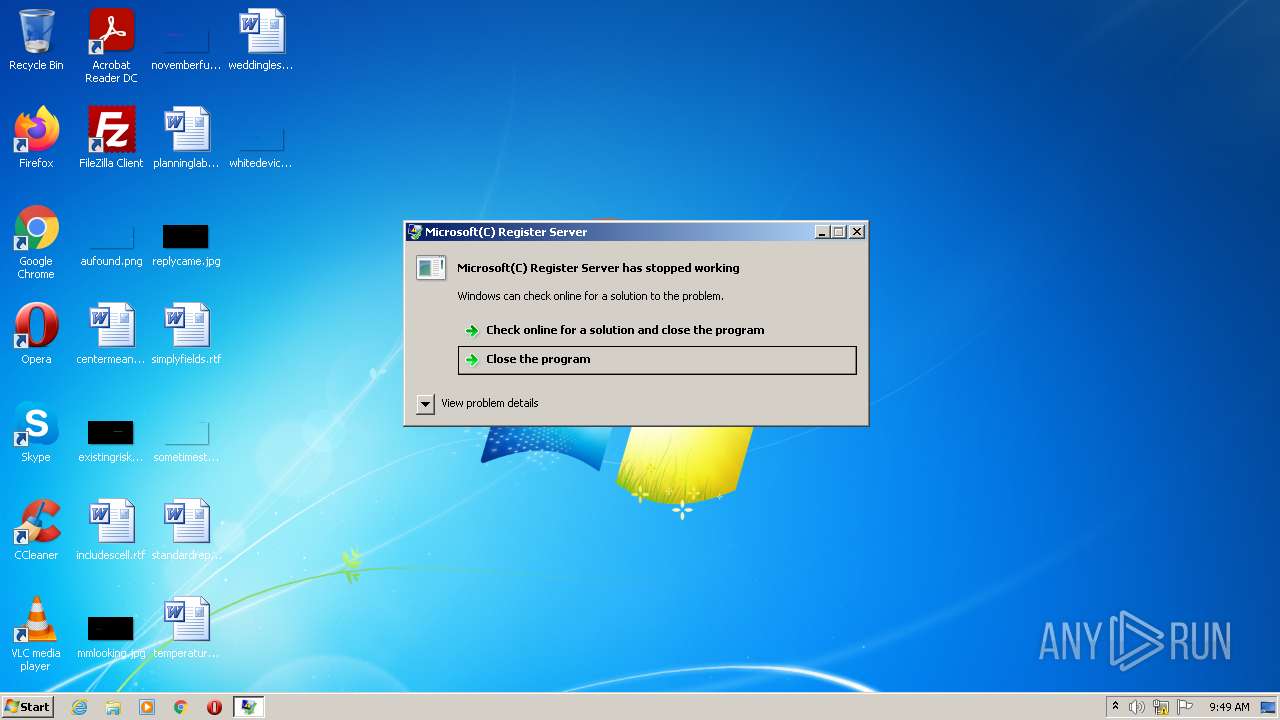
| 2316 | "C:\Windows\System32\regsvr32.exe" C:\Users\admin\AppData\Local\Temp\pdf.dll DllRegisterServer abcdefghij1234567890 | C:\Windows\System32\regsvr32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1064,17970245080642408806,12189011376816108035,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=17648734294061941783 --mojo-platform-channel-handle=1208 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2844 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\Desktop\pdf.dll | C:\Windows\System32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 869
Read events
15 189
Write events
677
Delete events
3
Modification events
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 0000000032000000670000006F382700000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF50FF33C56329D80100000000 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000480100007B020000FF5A17013F0000004A0000008E0F0D004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000028003E004000A4E75102B8E651020000000000000000000000000000080274E45102000008026CE25102000000000000D26CFFFFFFFF705911750000000000000000A4E251027C900D75000400000000000008E35102FFFFFFFF38EA7000FFFFFFFF080A7400D80E740030EA7000D4E25102F7AF3D7680D0707614F05102081D3E76E4613E766820700008E351020000000071000000BBF2CB00E8E25102A1693E766820700008E351020000000014E551023F613E766820700008E3510200000400000000800400000026E4510298E351025DA5147726E45102D26E147779A51477D6794D7526E4510210E65102000100006400610072E3510226E451026F0061006D0069006E0067005C006D006900630072006F0073006F0066007400CCE351023400000080E35102DE70310033003300350033003800310030003000F8E551025A000000A0E351021DA71477D6610E02D4E351025A00000010E651025C00000011000000104F7000084F7000F8E55102C4E3510220E40000D7F3CB00D0E351025E903E7620E45102D4E3510203943E760000000064561802FCE35102A9933E7664561802A8E45102D8511802BD933E7600000000D8511802A8E4510204E45102000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01000000007200000032AC5D004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E0043006F006E00740072006F006C00500061006E0065006C00000045003700430036004500410037004400320037007D005C0063006D0064002E0065007800650000000000D45D38760000000005000000D80B3902000000000000000000000000000000000000000000000000CB0501AD000000000000000000000000000000000000000000000000000000000000000030E69D01A8323876B8E59D01C0E59D0154E59D0100000000000000000000000000000000480B39020000000005000000D80B390200000000340C390268E59D01B0E59D010000000000000000E8B93902050000002000000000000000000000000400400000001A0098E59D0100000000000000000000000000000000040000009EE69D0110E69D015DA5B3779EE69D01D26EB37779A5B377114526769EE69D0188E89D0104000000C6E69D0138E69D015DA5B377C6E69D01D26EB37779A5B37739452676C6E69D01B0E89D0100010000E8FE1C0012E69D01C6E69D0168E69D015DA5310033003300350033003800310011000000104F1D00084F1D001AE79D018CE69D015DA5B37774E60000B777588D24E69D015E90D47674E69D0128E69D010394D47600000000D422E60250E69D01A993D476D422E602FCE69D01481EE602BD93D47600000000481EE602FCE69D0158E69D01 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 0000000030000000000000002F000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF50FF33C56329D80100000000 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000B400000000000000B30000003E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D603 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000300000000000000030000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF50FF33C56329D80100000000 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000B400000000000000B40000003E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D6033E000000000000003E0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C0049006E007400650072006E006500740020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000987880574F8C6244BB6371042380B109000000000000000000006D000000000078AB287598117500084B7600981175000000000000000000DE1C0000E0791401C8D4D60313A91477E01D32BD0C0C00001027000002000000FF560200FCD4D603D8A81477FF560200E07914011CD5D603C05C18029CD5D60300000000A40100005CD500009BC44C010CD5D6035E903E765CD5D60310D5D60303943E76000000004C61180238D5D603A9933E764C611802E4D5D603C05C1802BD933E7600000000C05C1802E4D5D60340D5D603 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (584) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
Executable files
3
Suspicious files
41
Text files
1
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3312 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_regsvr32.exe_6d222c5462b9a219dd6dc6b25f73bbce24a92e0_0cfee105\Report.wer | — | |
MD5:— | SHA256:— | |||
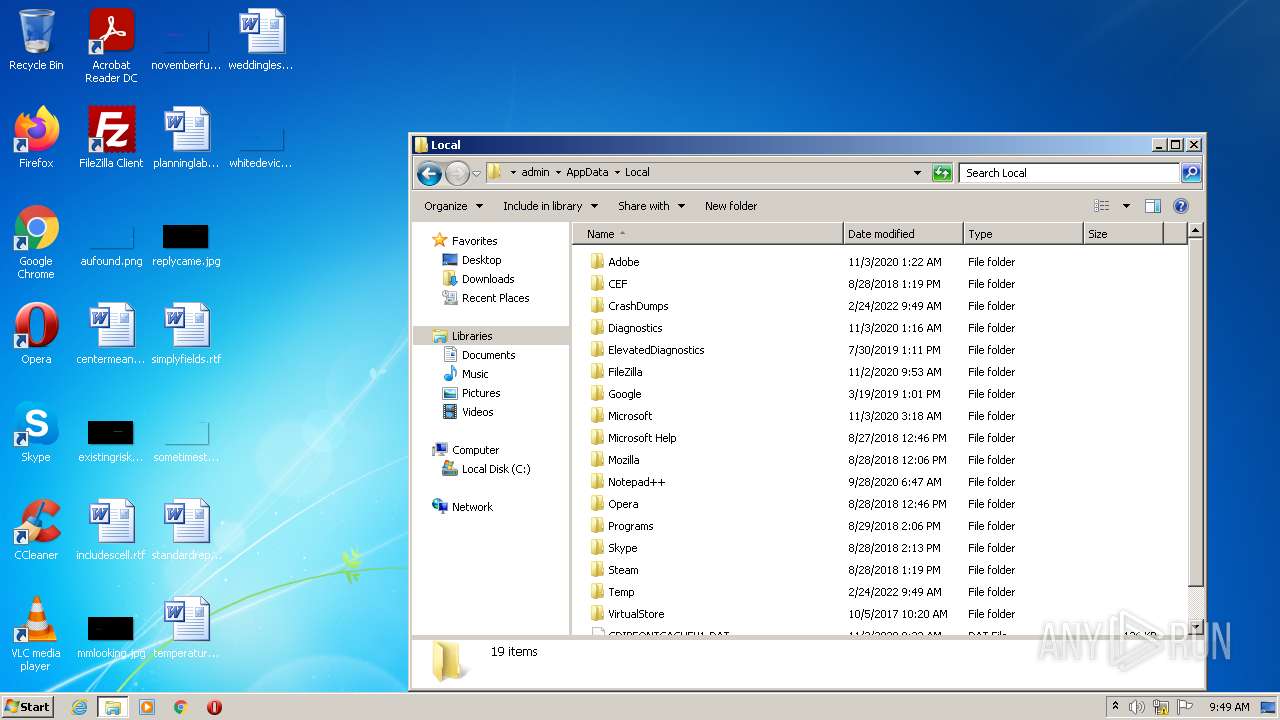
| 3312 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\regsvr32.exe.2316.dmp | dmp | |
MD5:F51453697117D79D2AAD960A29E11D94 | SHA256:FD56E6A3B38CA1322233E048DF97598EE4684D75F8BEE047915419DFBC4FE8FB | |||
| 584 | Explorer.EXE | C:\Users\admin\AppData\Local\Temp\pdf.dll | executable | |
MD5:DA5B3014CEACE8E5E161B5219E04ACF5 | SHA256:0457768F9D8D70FF59275C27BC99D45C1C48CF1E932D29C3F2E9D5E037ACD802 | |||
| 584 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:0381253B5C992548804E6030558E87F7 | SHA256:AAB85A94E727D1F1473119C09FA119C398BDB833662FEAC48864DCD165C2363B | |||
| 3876 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\2a426f11fd8ebe18_0 | binary | |
MD5:2BDB8669C0E3804FA7060B91F963353E | SHA256:328B5BBE1677918402EA754A78548A475BA04FF6E645B5A297F17F3189682D9F | |||
| 584 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\de48a32edcbe79e4.automaticDestinations-ms | automaticdestinations-ms | |
MD5:48221F1393698D387682B6EDDC54A49B | SHA256:1EF39224E33C3ED02DEA5B845637EDCF9991A0825DD986FC12556A7344EA838A | |||
| 584 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\pdf.dll.lnk | lnk | |
MD5:00C3FD63DEA5B8F5B948A464C88928A2 | SHA256:A85A80B8E32D7E8054694715373E0974D3EAAC4C755FACA6129BAD207ACC9246 | |||
| 3876 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\4a0e94571d979b3c_0 | binary | |
MD5:B8F35D97007BE59C4BE56AC2611D5671 | SHA256:1116B217655ABA56532E59BC80B05CE40A80E76BA148F9801644884D7DC3341D | |||
| 3876 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\72d9f526d2e2e7c8_0 | binary | |
MD5:6354A063BBDD88ED519D9C030A41FF0A | SHA256:D1DFAD8EE3950566E4F6E4A7AD5F0C096CA9FE0B251B3AC62920606B96FF352E | |||
| 3876 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\bba29d2e6197e2f4_0 | binary | |
MD5:F1F2BBDFCB3929437610A9C86482F993 | SHA256:566080FA04A3D9FFE039EA2733894AEEAD97431EBB4321C60DBC2BADEEBC6E78 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |