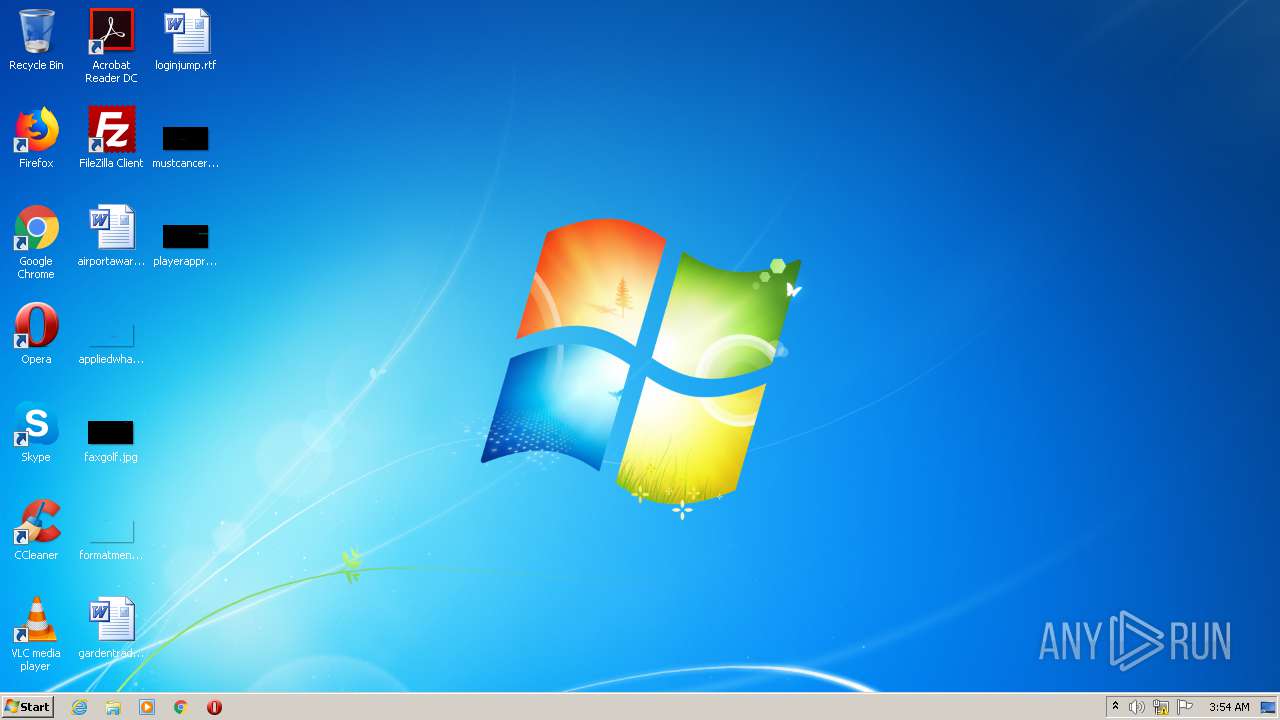
| File name: | Cat mario.exe |
| Full analysis: | https://app.any.run/tasks/024bdb9b-352c-4b45-aa69-6bc66f3fad11 |
| Verdict: | No threats detected |
| Analysis date: | July 18, 2020, 02:54:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 12D20E7F22C8735E4EA9ED13C27FB657 |
| SHA1: | 89A4FC8E4A80AF74CBDECEAACB2D69122CAA037D |
| SHA256: | 044F971C251965E950E147B2C508CA54BB74AD4DA0F6402BD9471054448D2F7E |
| SSDEEP: | 24576:t0LvWQb1FWy33djbjR9FC0brpYGQwflh6h9a9rw2RNkWgWeiT0W:WLvWQXWm39jRC/9atW+1T0W |
MALICIOUS
No malicious indicators.SUSPICIOUS
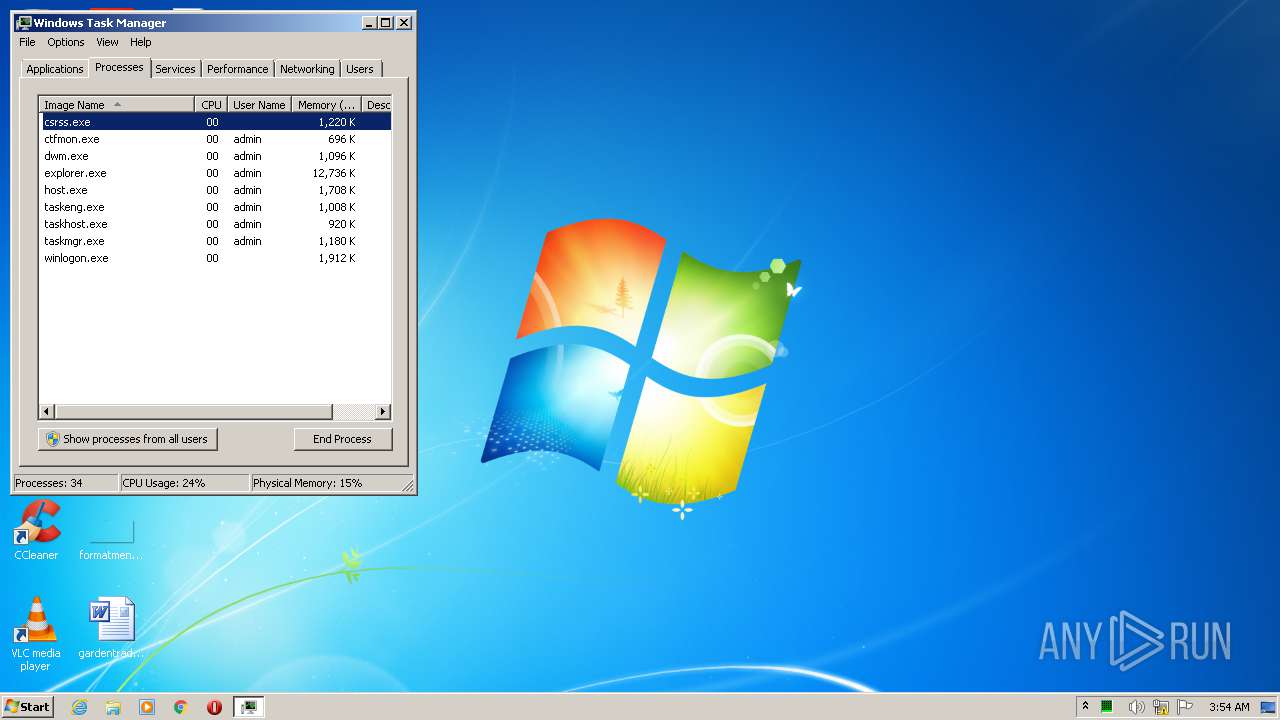
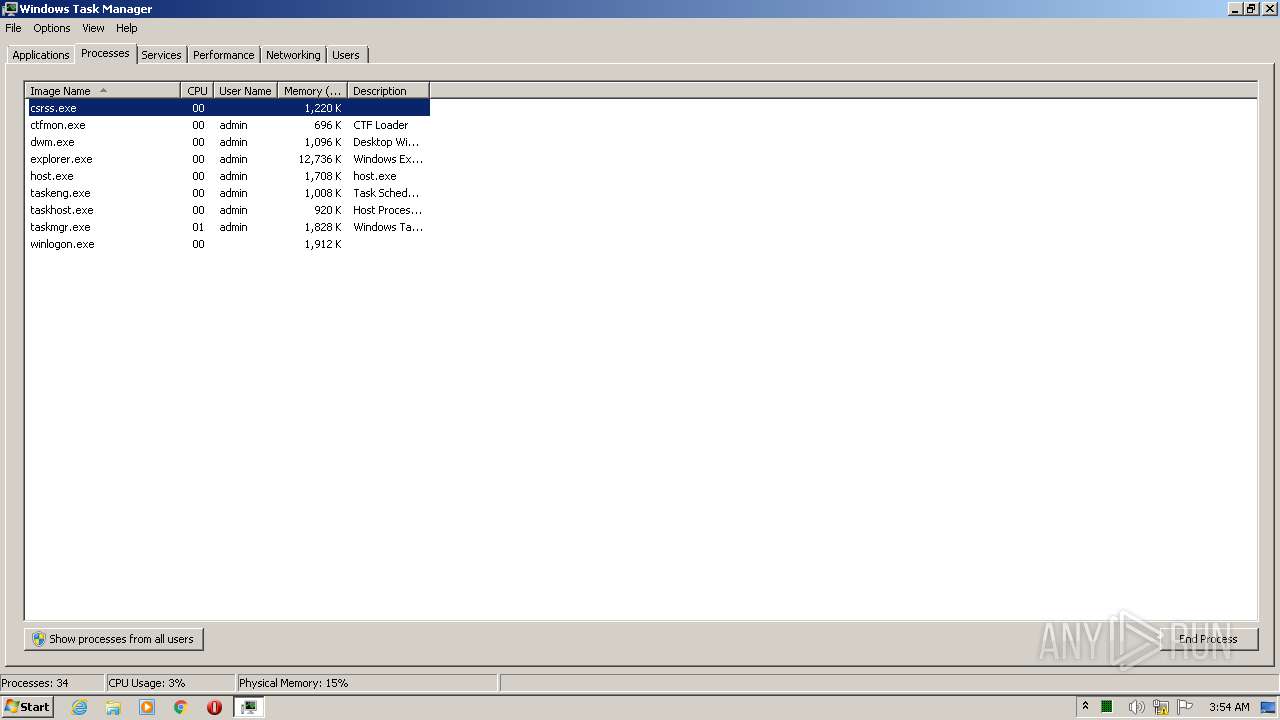
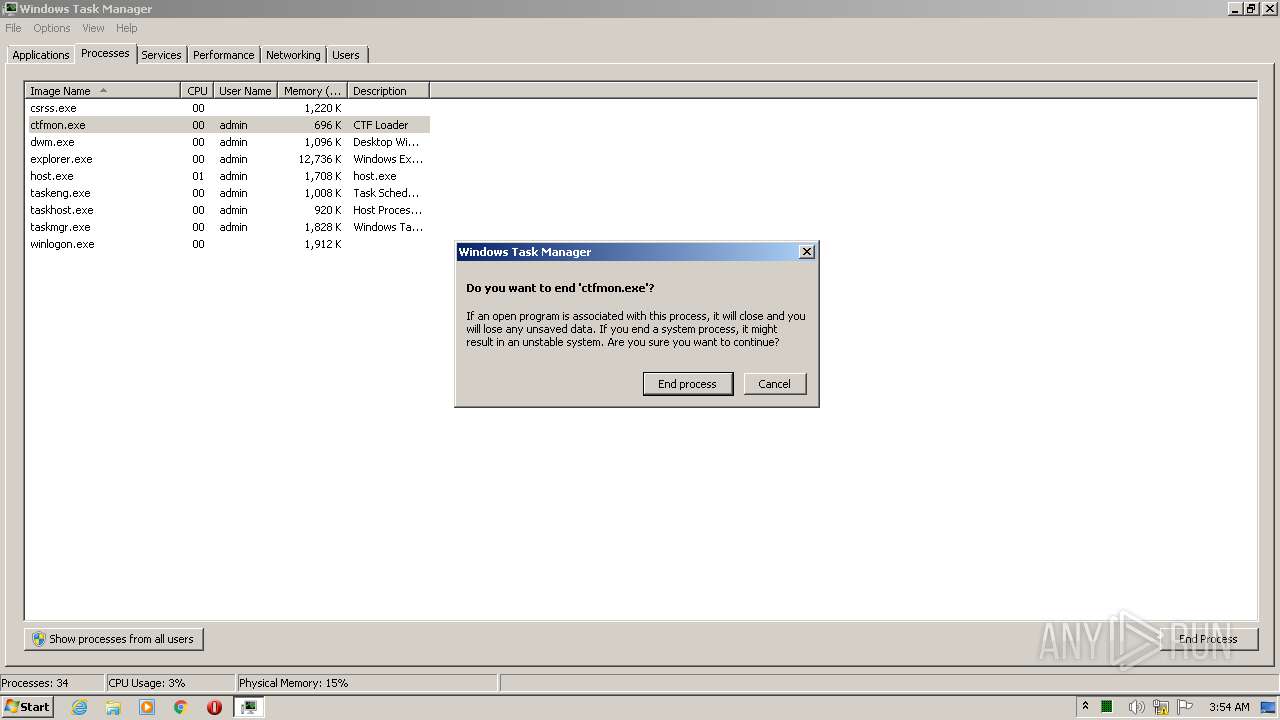
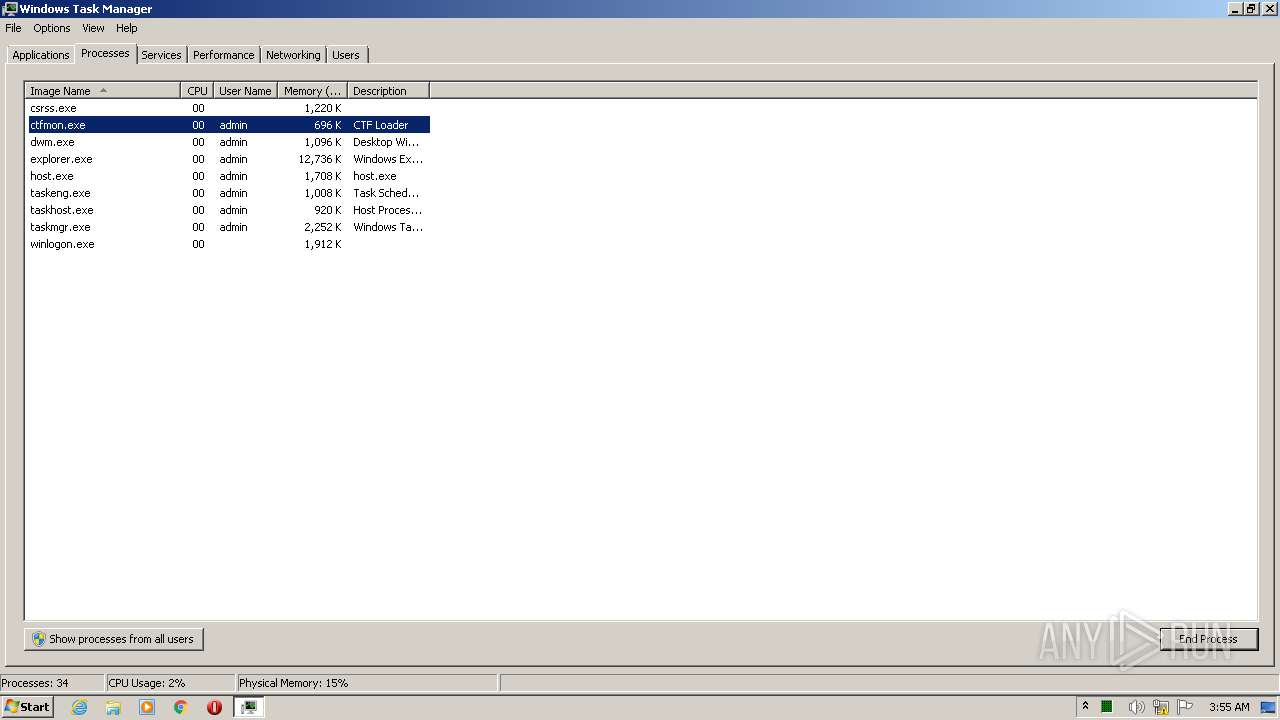
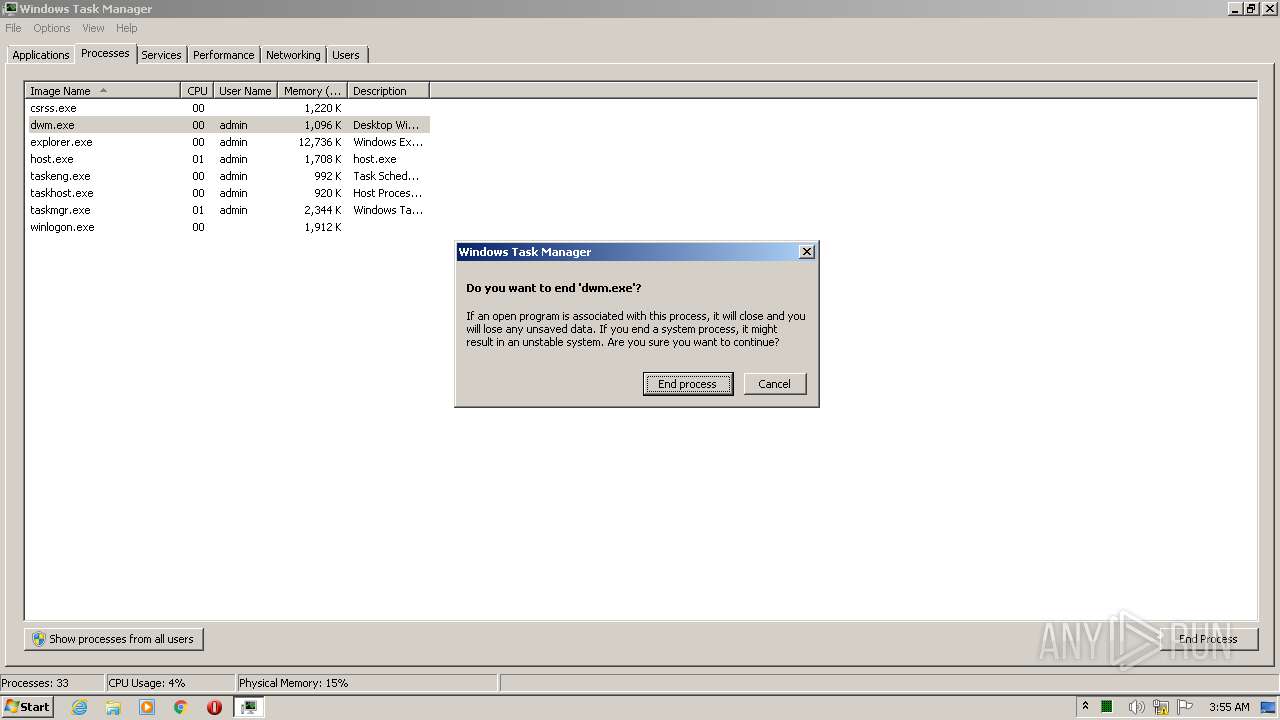
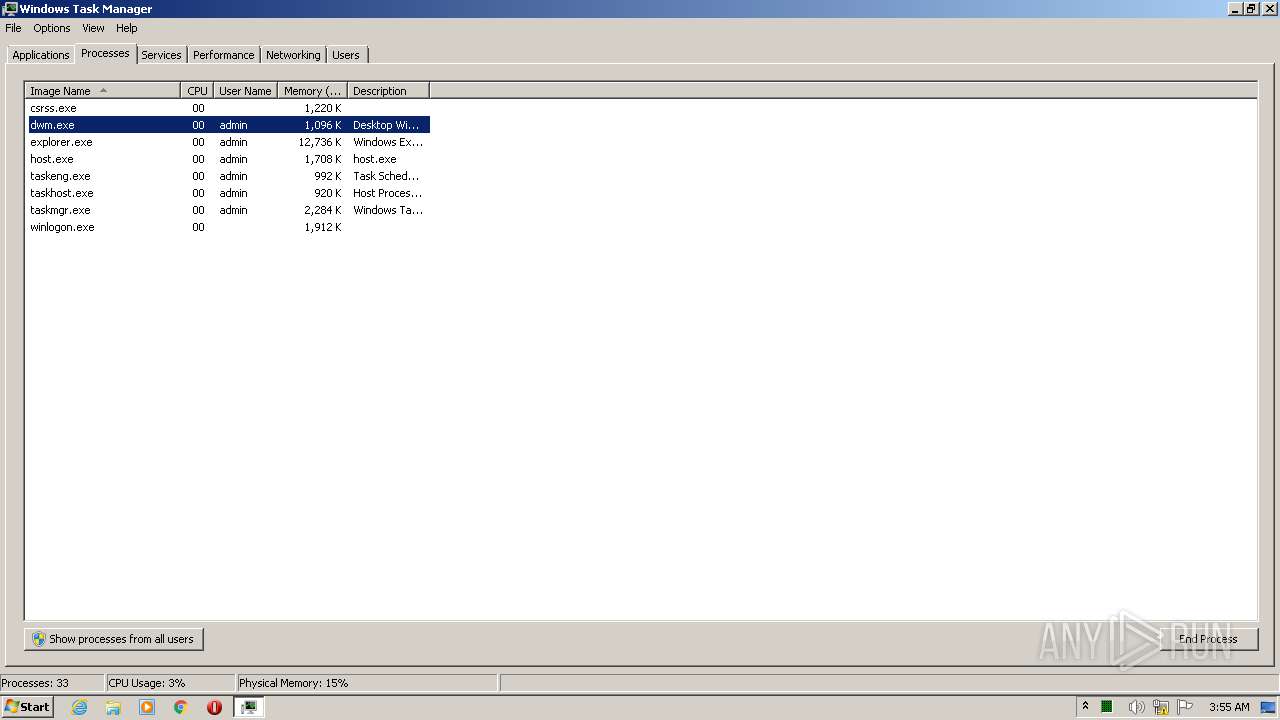
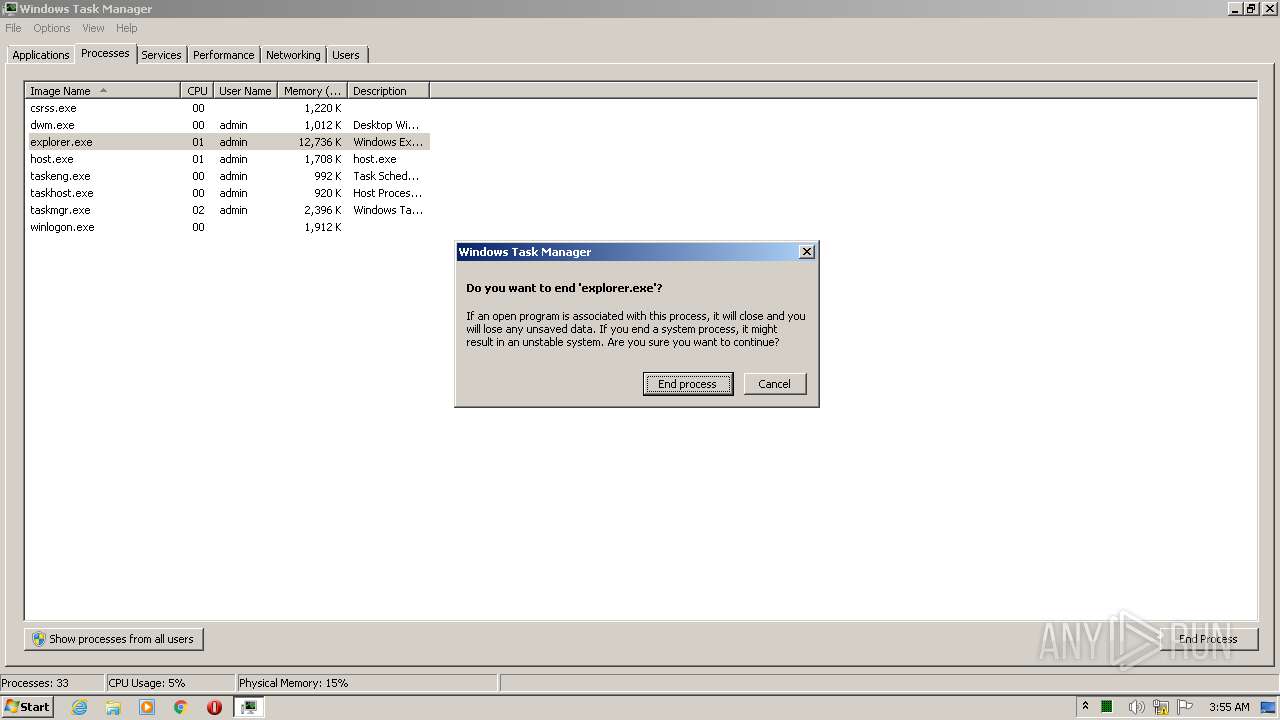
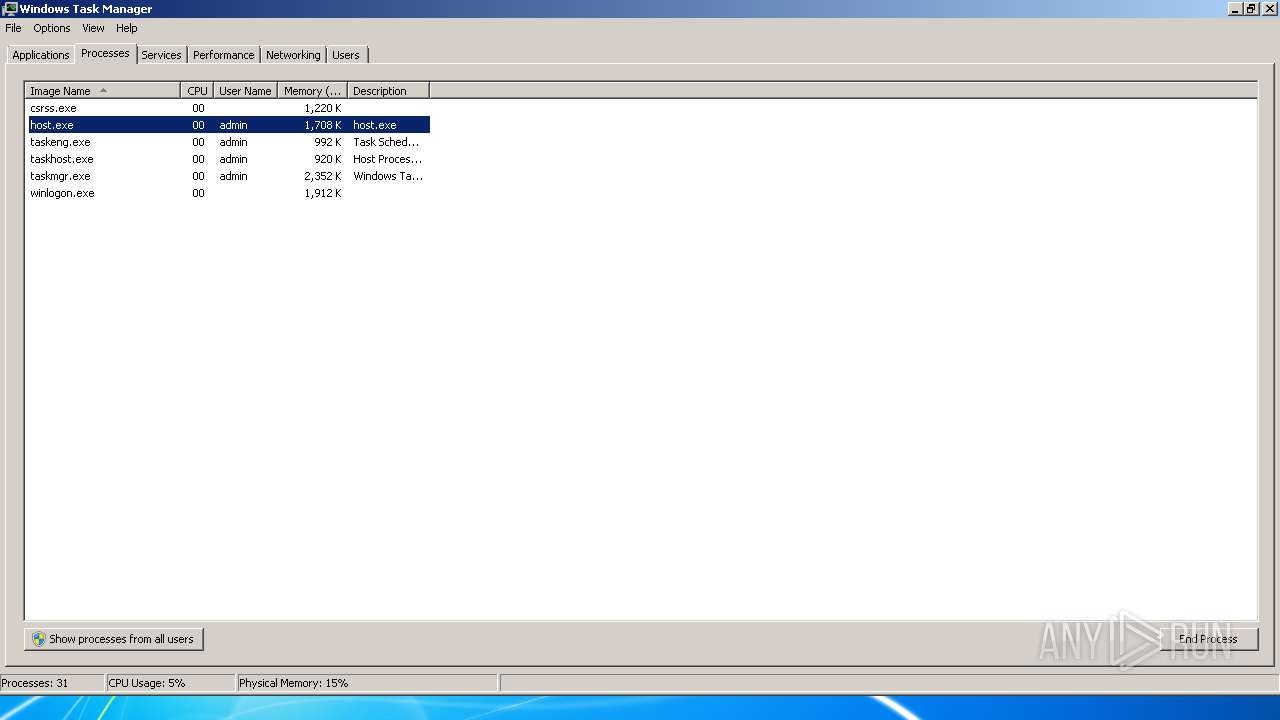
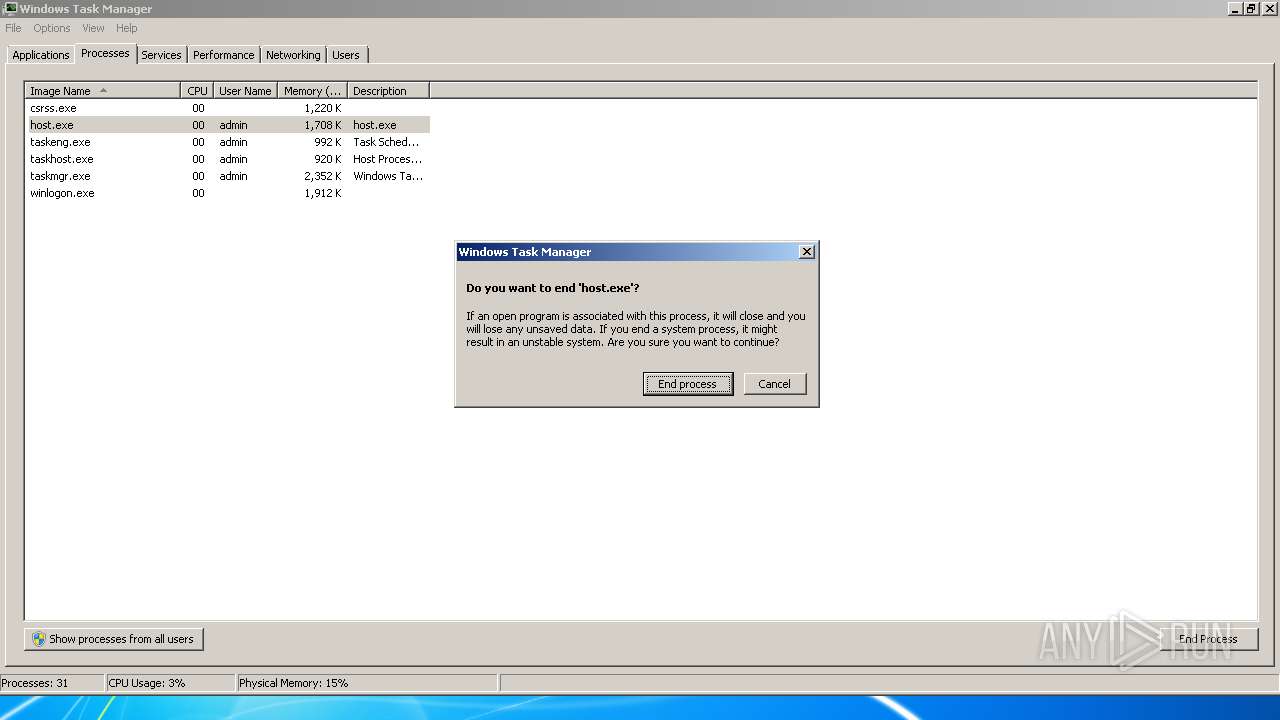
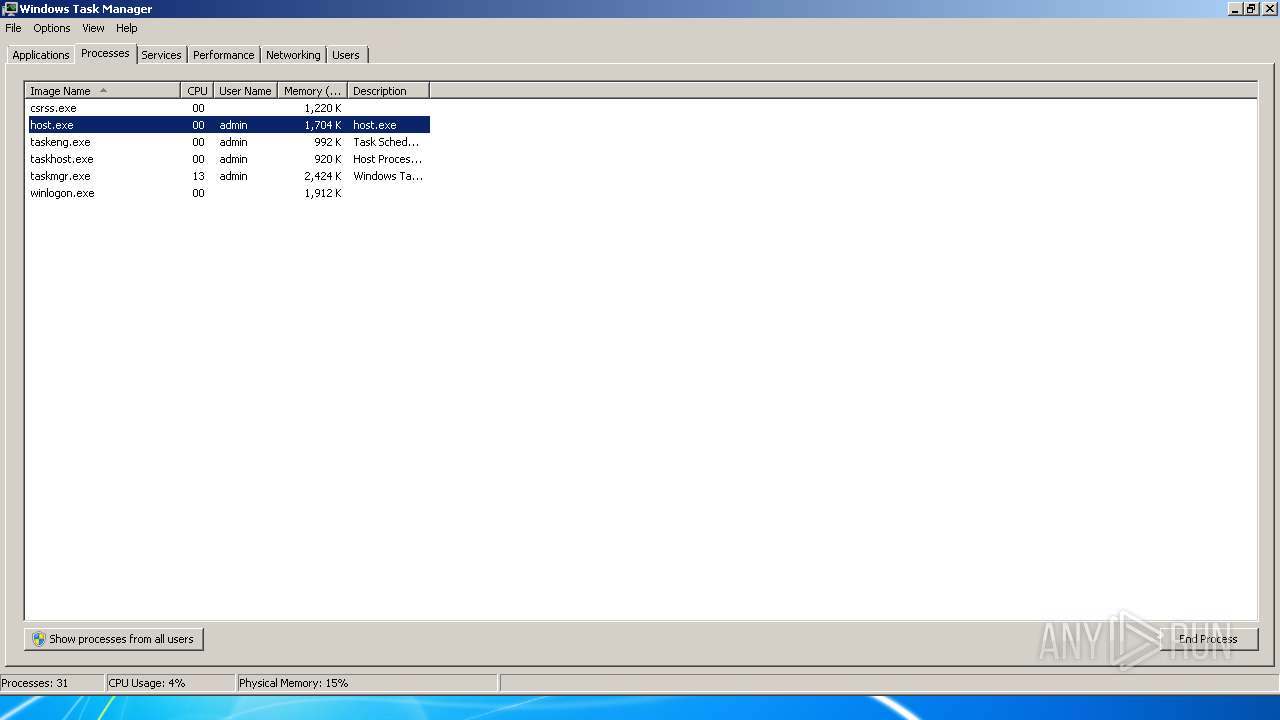
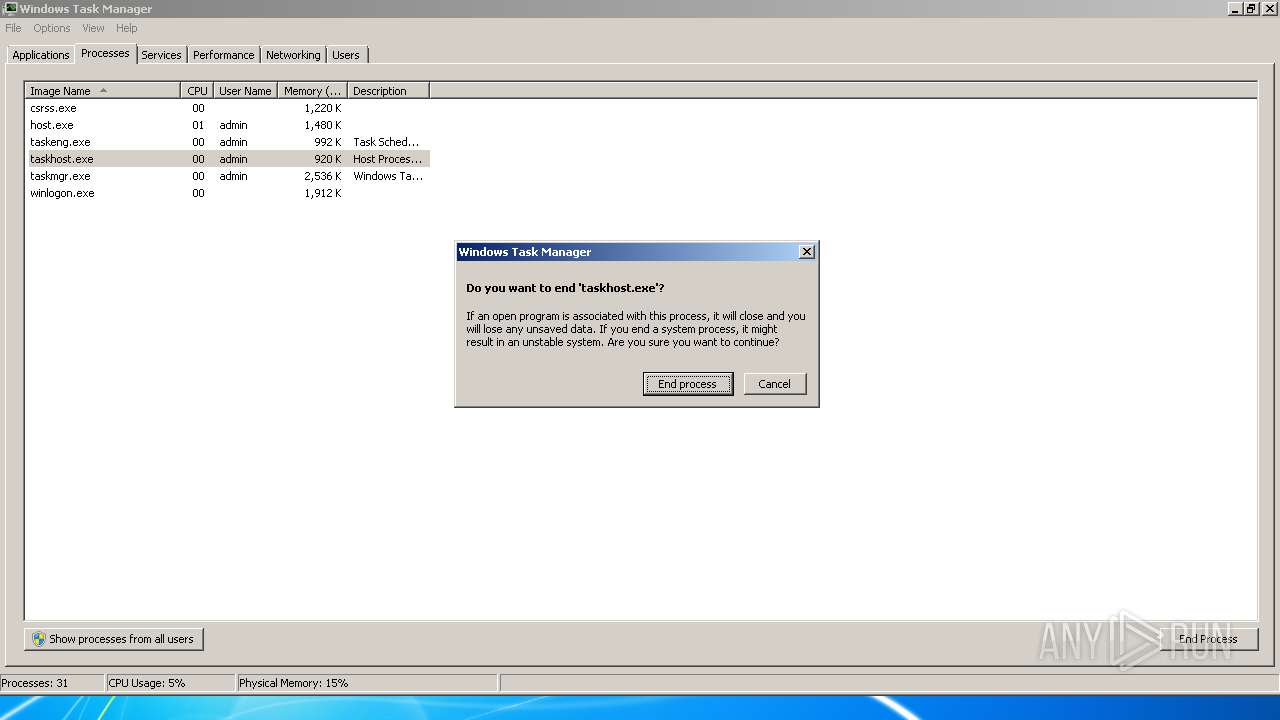
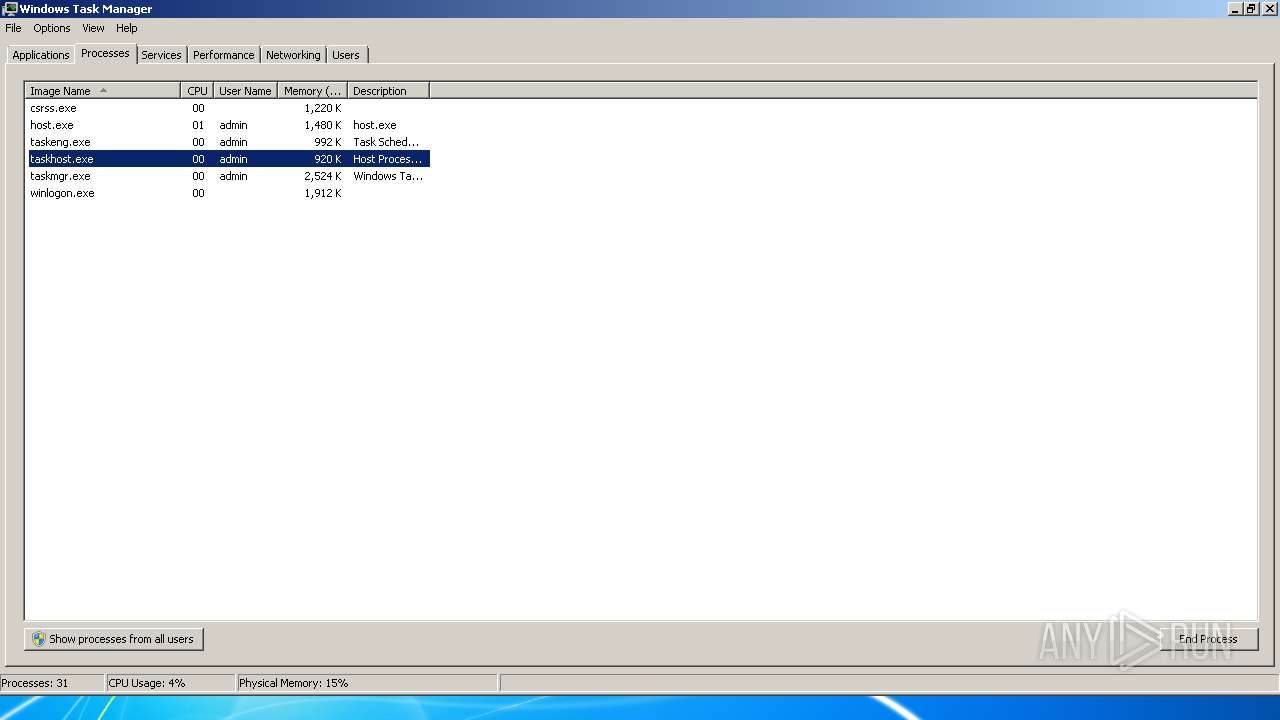
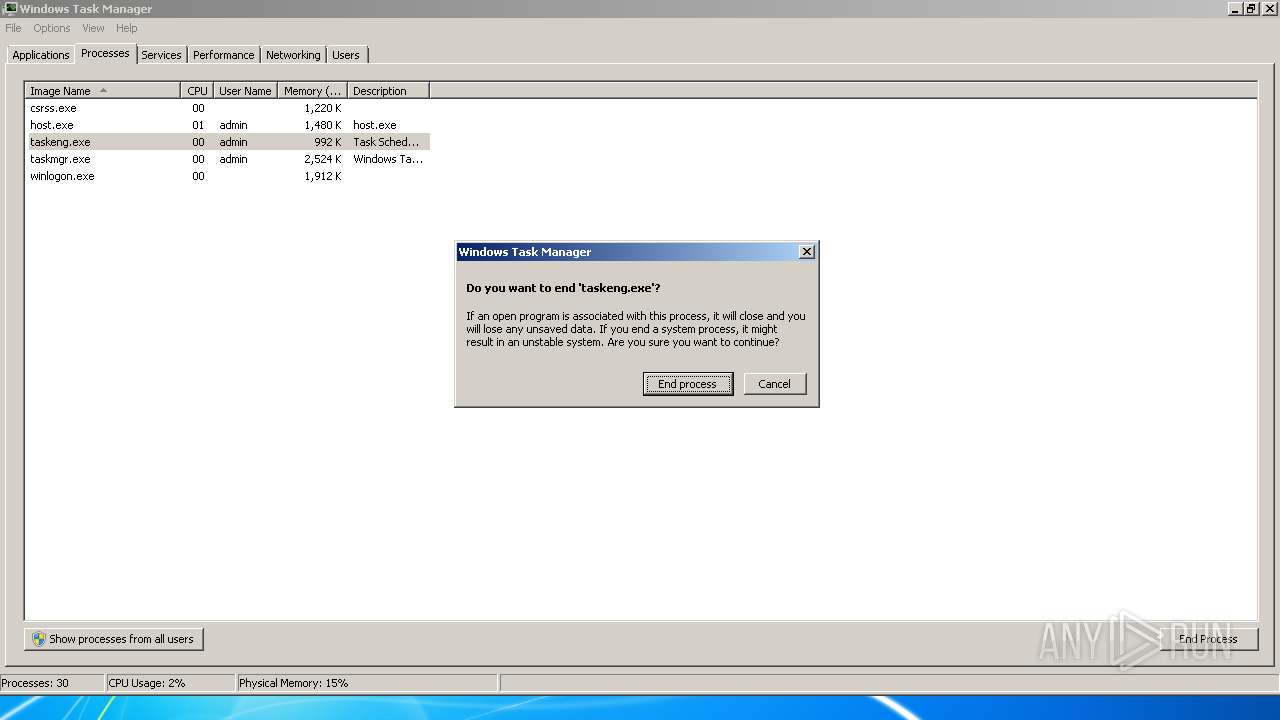
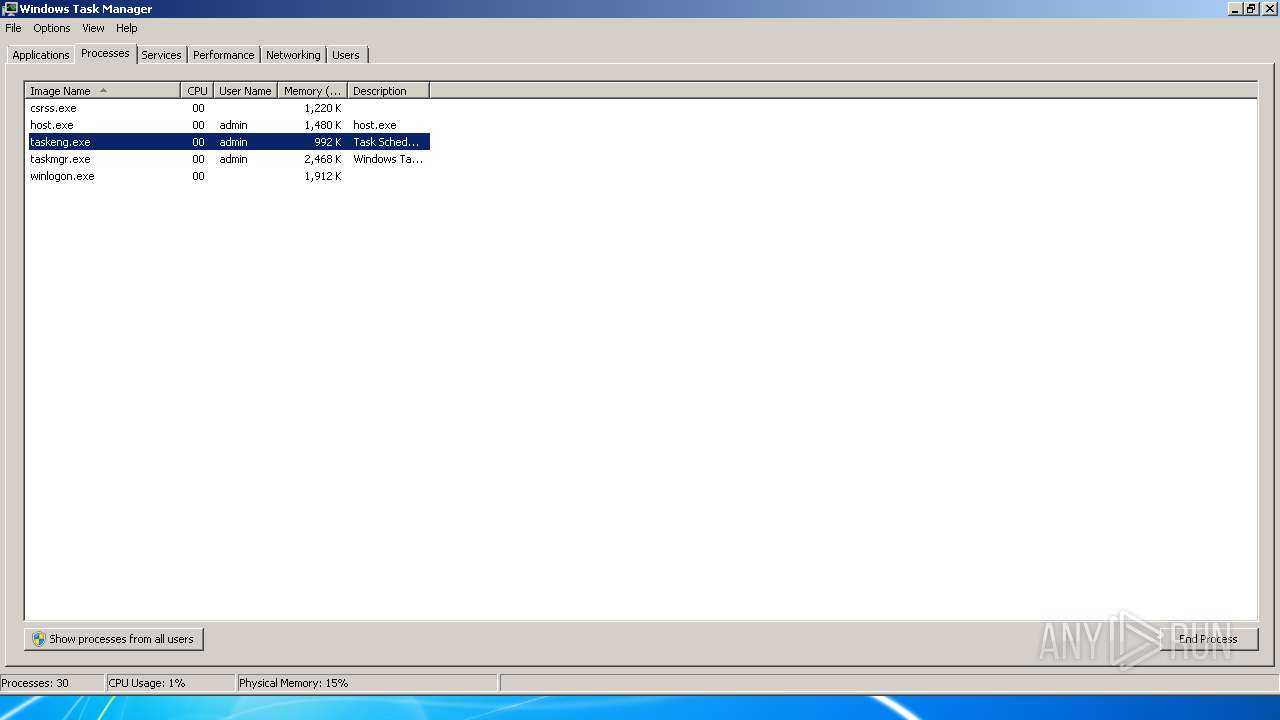
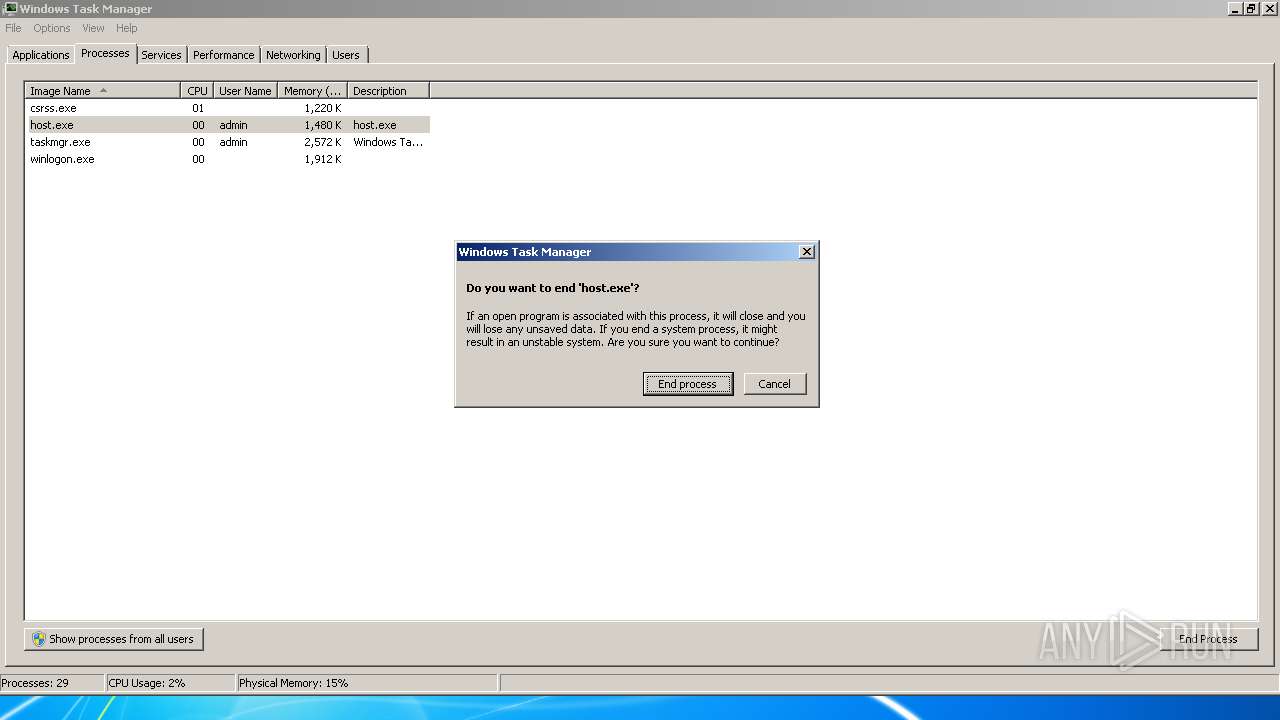
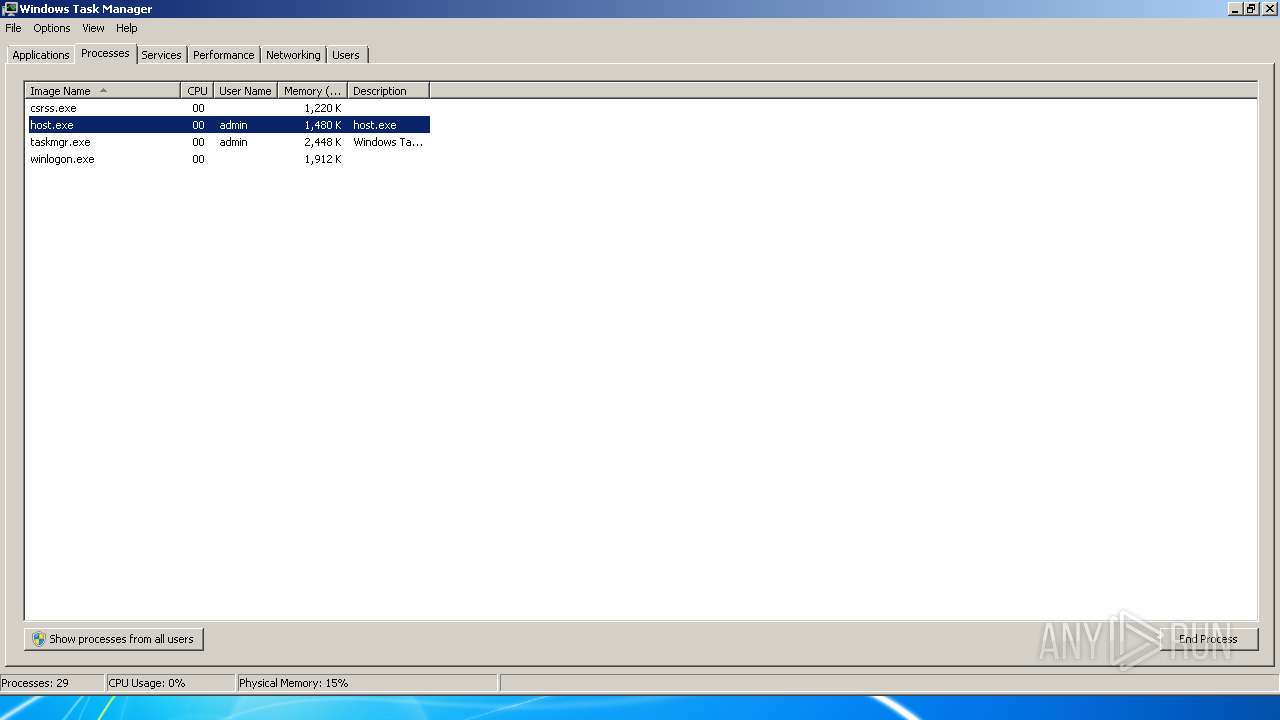
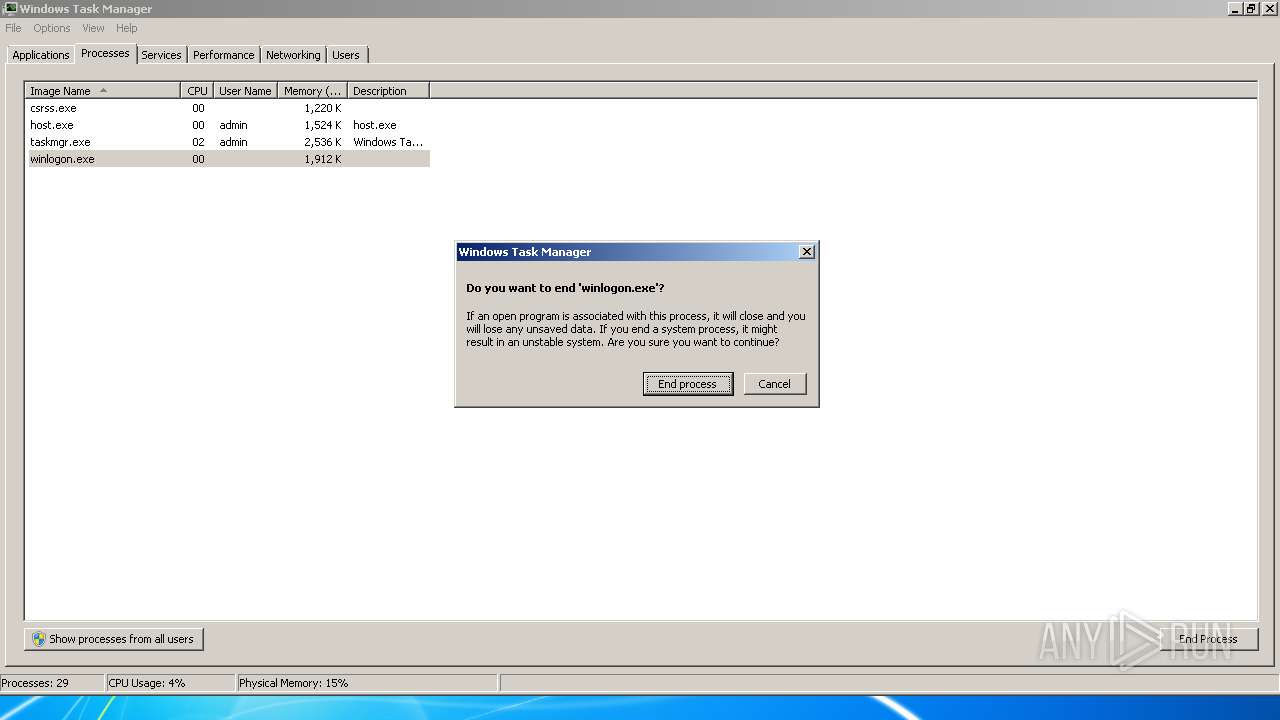
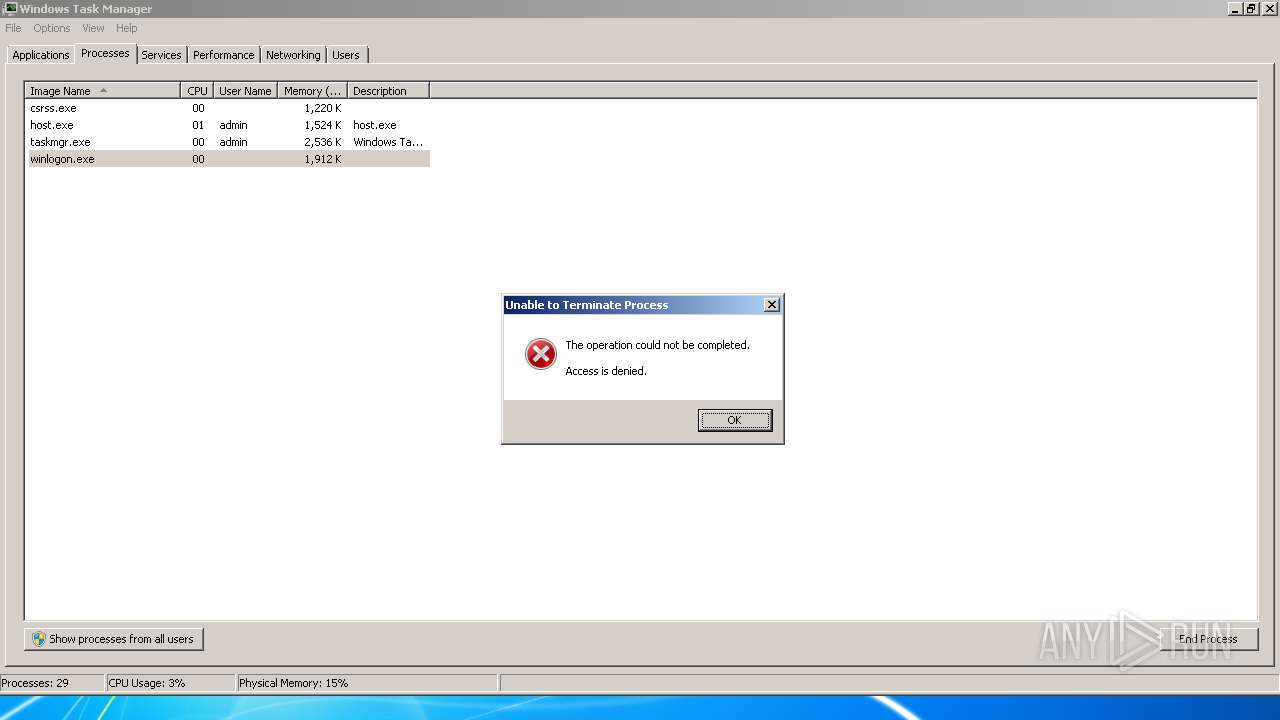
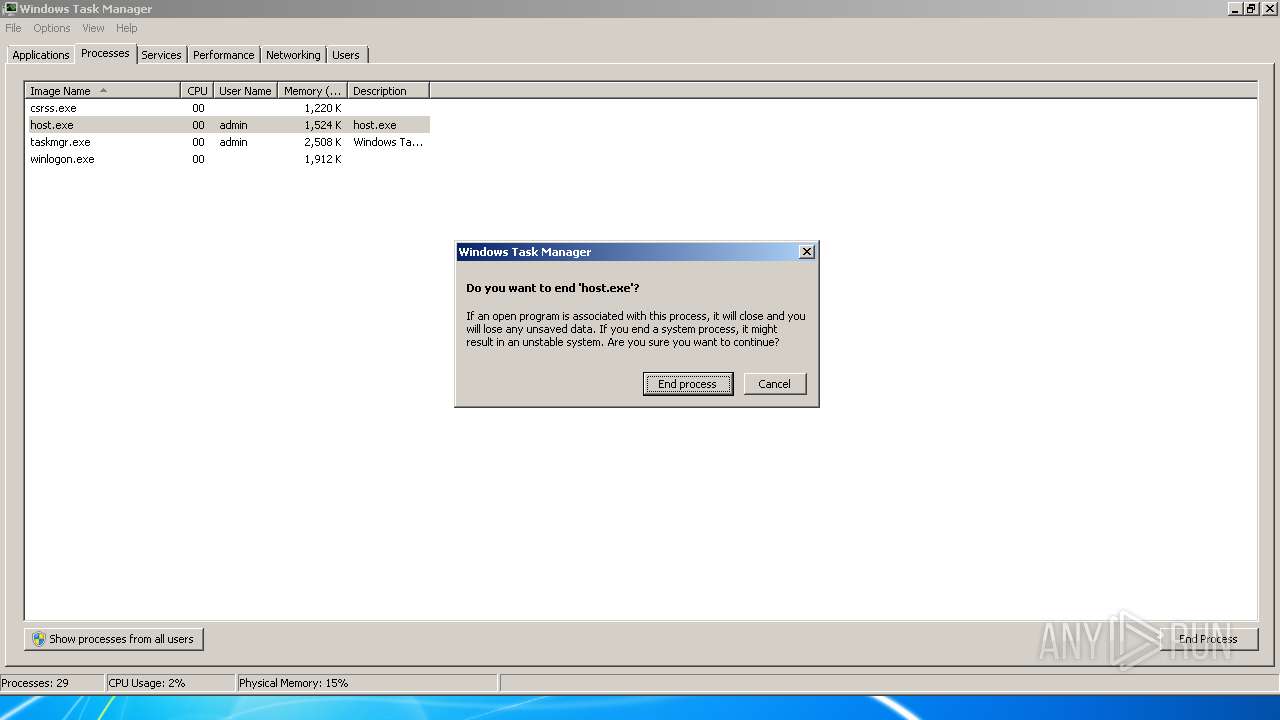
Application launched itself
- taskmgr.exe (PID: 768)
INFO
Manual execution by user
- taskmgr.exe (PID: 768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:12:23 14:06:02+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1536000 |
| InitializedDataSize: | 176128 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x154474 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Dec-2007 13:06:02 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Dec-2007 13:06:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001769F5 | 0x00177000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48723 |
.rdata | 0x00178000 | 0x00013EE6 | 0x00014000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.78403 |
.data | 0x0018C000 | 0x00302788 | 0x00016000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.13337 |
.rsrc | 0x0048F000 | 0x00000B0C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.06988 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05186 | 338 | Latin 1 / Western European | English - United States | RT_MANIFEST |
MAINICON | 1.81924 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSACM32.dll |
MSVCP80.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WSOCK32.dll |
ole32.dll |
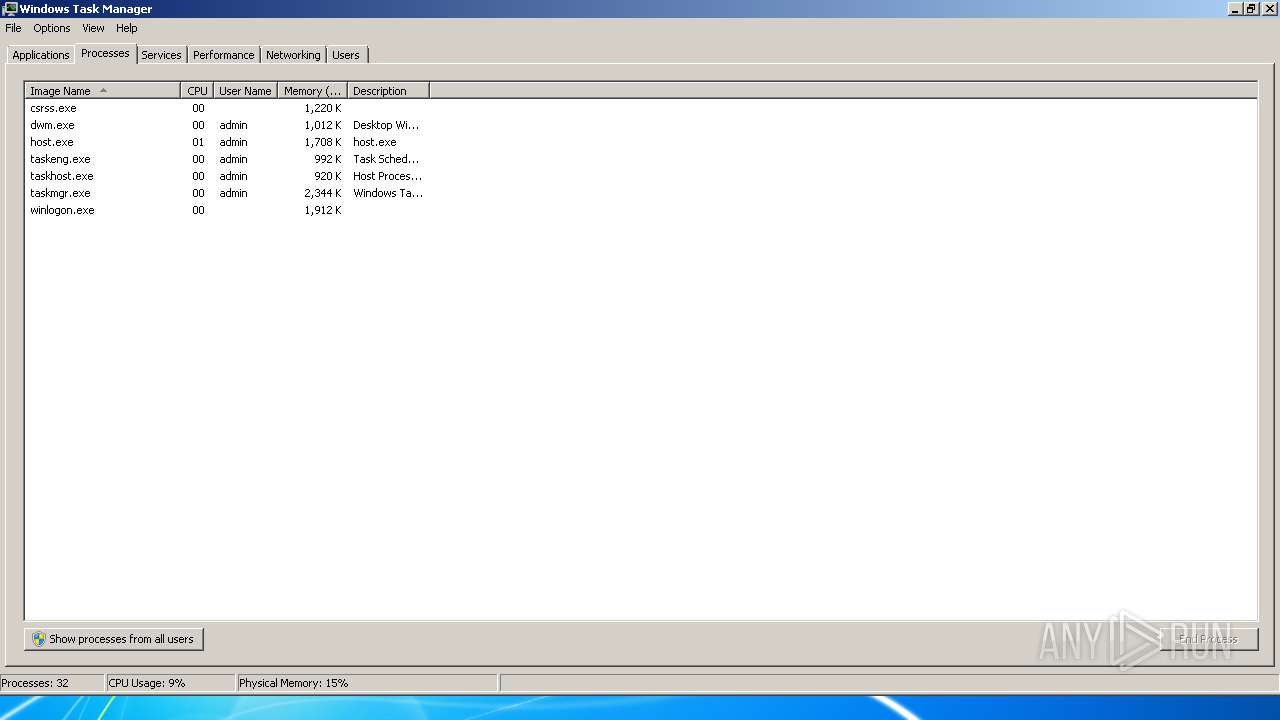
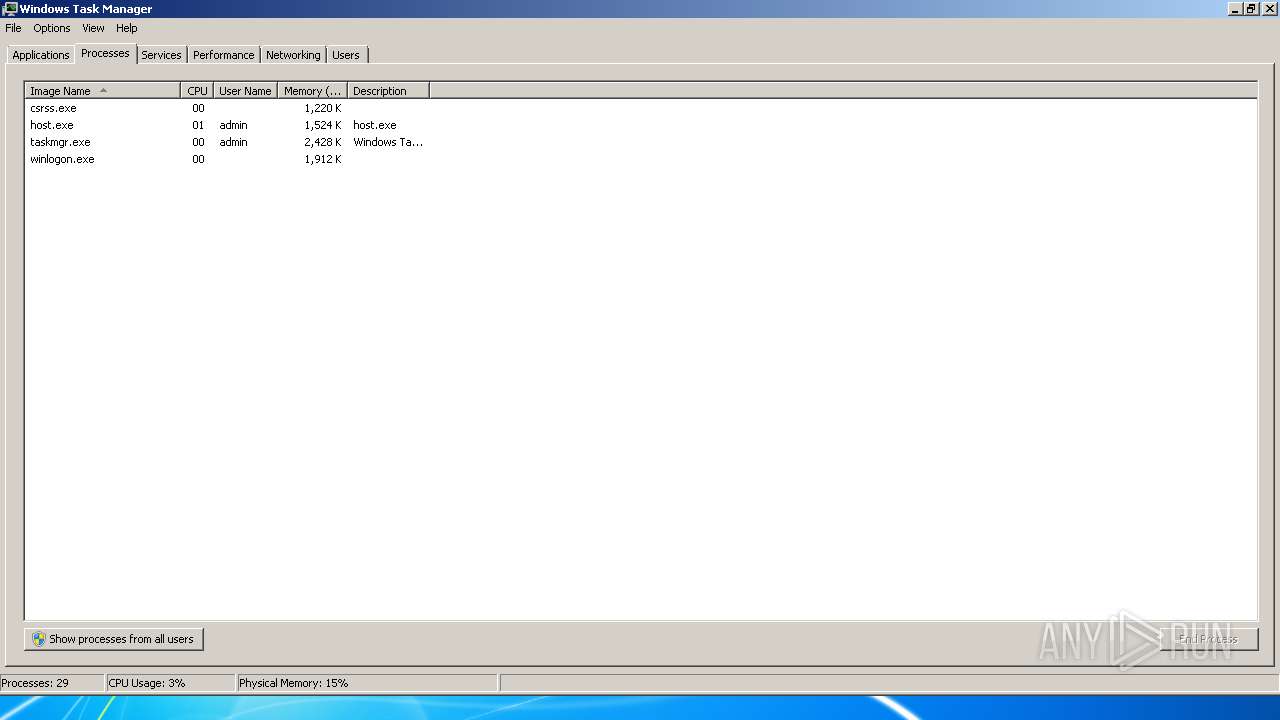
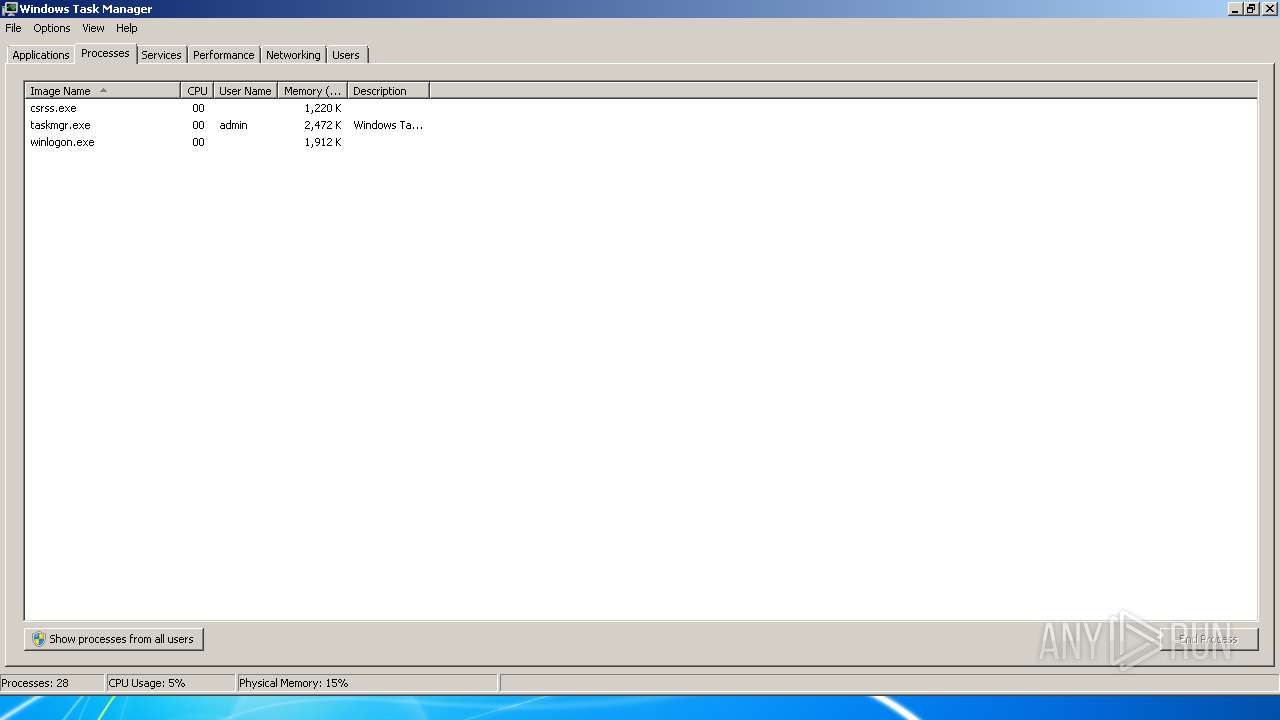
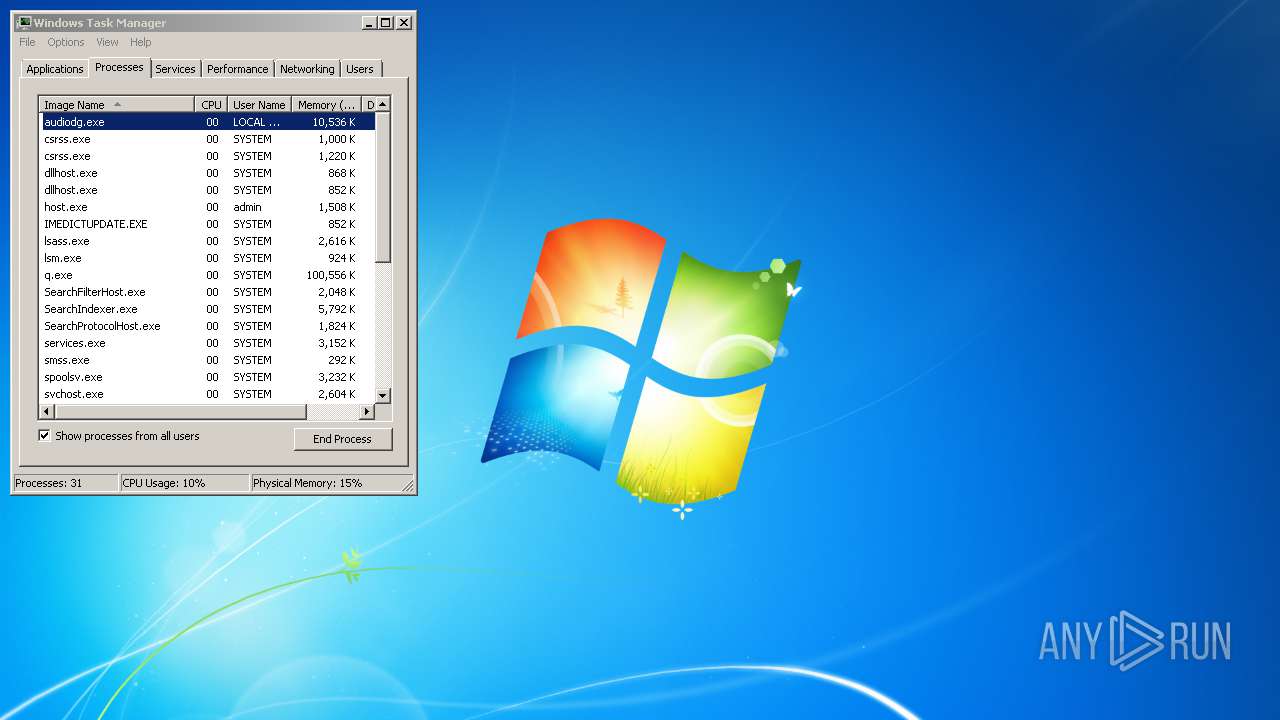
Total processes
45
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 768 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\system32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
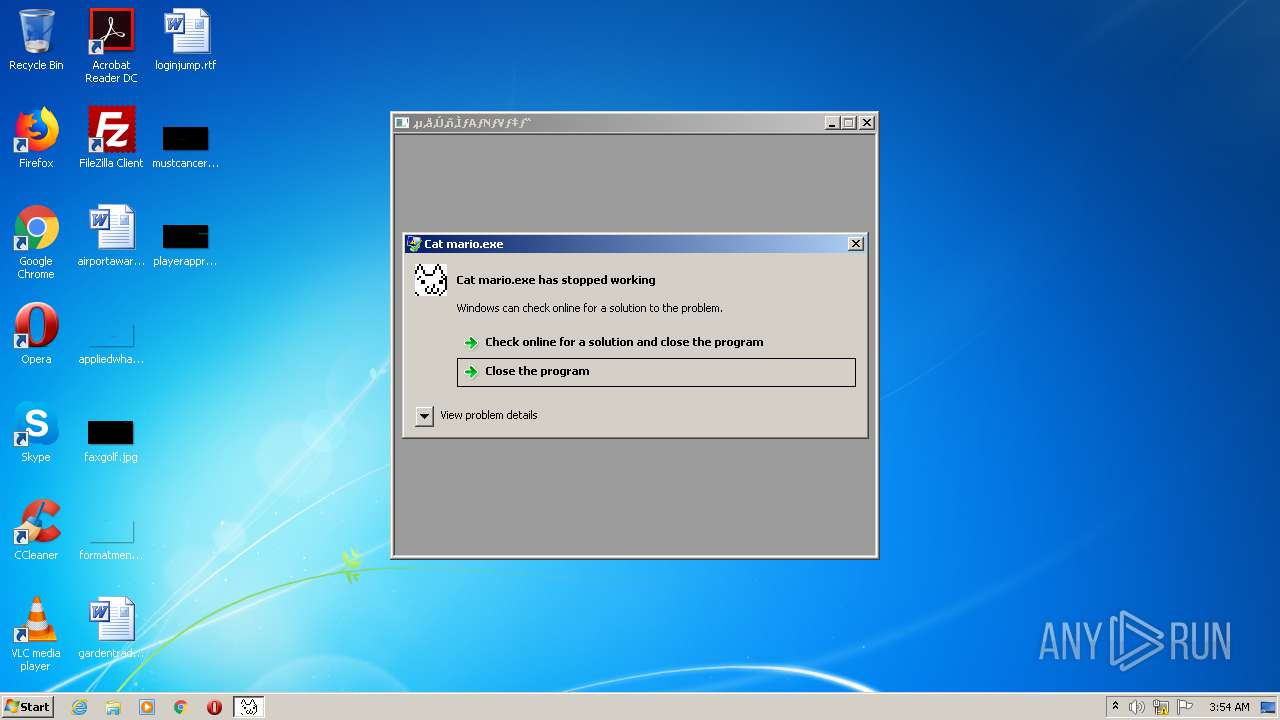
| 2424 | "C:\Users\admin\AppData\Local\Temp\Cat mario.exe" | C:\Users\admin\AppData\Local\Temp\Cat mario.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225620 Modules
| |||||||||||||||
Total events
73
Read events
59
Write events
14
Delete events
0
Modification events
| (PID) Process: | (2424) Cat mario.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Version |
Value: 00070000 | |||
| (PID) Process: | (2424) Cat mario.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: CAT MARIO.EXE | |||
| (PID) Process: | (2424) Cat mario.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Id |
Value: CAT MARIO.EXE476E5D3A001A3000 | |||
| (PID) Process: | (2424) Cat mario.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | MostRecentStart |
Value: 46B006CBAE5CD601 | |||
| (PID) Process: | (2424) Cat mario.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Cat mario.exe | |||
| (PID) Process: | (2424) Cat mario.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: 1198415162 | |||
| (PID) Process: | (2424) Cat mario.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Cat mario.exe | |||
| (PID) Process: | (768) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (768) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (768) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000000A0000000A000000A2010000F00100000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
Executable files
0
Suspicious files
0
Text files
88
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2424 | Cat mario.exe | C:\Users\admin\AppData\Local\Temp\Log.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
Cat mario.exe | ‚cF |
Cat mario.exe | WindowsVista ( Build 7601 Service Pack 1 )
|
Cat mario.exe | ‚c‚wƒ‰ƒCƒuƒ‰ƒŠ Ver2.23
|
Cat mario.exe | ‚n‚r |
Cat mario.exe | |
Cat mario.exe | ƒVƒXƒeƒ€‚Ìî•ñ‚ðo—Í‚µ‚Ü‚·
|
Cat mario.exe | Genu |
Cat mario.exe | ineI |
Cat mario.exe | ‚l‚l‚w–½—ß‚ðŽg—p‚µ‚Ü‚·
|
Cat mario.exe | ‚b‚o‚tƒxƒ“ƒ_F |